IT Essentials Practice Final Exam Modules 10-14 Answers
IT Essentials (Version 8.0) – ITE 8.0 Practice Final Exam Modules 10-14 (Ch 10 – 14)
IT Essentials (Version 7.00) – IT Essentials 7.0 Practice Final Ch 10 – 14
1. What two motherboard components control the system boot operations? (Choose two.)
- BIOS chip
- UEFI chip
- Northbridge chip
- Southbridge chip
- CPU
2. What motherboard chip controls high speed CPU communication to RAM and the video card?
- Northbridge
- Southbridge
- BIOS
- UEFI
3. Which two procedures can help protect against ESD when working on a computer system? (Choose two.)
- the use of an antistatic wrist strap
- the use of magnetized tools
- the use of an antistatic mat
- the use of safety glasses
- the use of polyester clothing
4. Which software tool will protect against viruses and spyware on a Windows PC?
- Windows 8 Action Center
- Scandisk
- Windows Defender
- System File Checker
5. Which cleaning material should be used to clean component contacts?
- isopropyl alcohol
- compressed air
- cotton swabs and cloths
- dishwashing liquid and water
6. A technician is troubleshooting a problem where many websites return a “certificate not valid” error. The technician notices that the date and time are not current and resets these to the correct settings. The previously inaccessible websites are now accessible. However, when the computer is restarted the same problem reoccurs. What can the technician do to prevent the date and time from resetting?
- Reinstall the OS.
- Upgrade the BIOS.
- Change the power settings in the BIOS.
- Replace the CMOS battery.
7. When a new motherboard is being installed, between which two components must thermal compound be applied? (Choose two.)
- CPU
- RAM
- chassis
- heat sink
- chipset
- motherboard
8. A specific computer has an issue that could not be resolved by the help desk technician. The on-site technician finds that Windows updates have been disabled. The technician re-enables the update service, configures the computer for automatic updates, downloads and installs all missing updates, ensures the computer boots successfully, and verifies with the customer that the issue has been resolved. Which step, if any, is next?
- Document the findings, actions, and outcomes.
- No further action is needed.
- Establish a plan of action to resolve the problem and implement the solution.
- Verify full system functionality and, if applicable, implement preventive measures.
- Test the theory to determine the cause.
9. What should a technician do before beginning any troubleshooting steps on a customer computer?
- Perform a data backup.
- Document the findings.
- Identify the problem.
- Establish a plan of action.
10. Which document can be signed by both a user and a computer repair shop to release the shop from backing up user data?
- preventive maintenance plan
- work order
- liability release form
- warranty form
11. A technician is troubleshooting a 4-year-old computer that takes a long time to boot, and identifies that the BIOS rediscovers all the hardware at every boot. What action would fix this problem?
- Replace the CMOS battery.
- Launch Device Manager to discover new hardware.
- Reset the BIOS using the CMOS jumper.
- Start the computer with the last known good configuration.
12. Which location on a hard disk is used by the BIOS to search for operating system instructions in order to boot a PC?
- the logical drive
- the active partition
- the Windows partition
- the extended partition
13. A technician is asked to set up one hard drive that will support two operating systems and will store data files in three separate drive locations. Which partition settings will support these requirements?
- 1 primary, 3 active, 1 extended, 2 logical
- 2 logical, 2 active, 3 extended
- 2 primary, 1 active, 1 extended, 3 logical
- 3 primary, 1 active, 2 extended
14. A user installs a new sound card driver in a computer that is working properly. After the installation of the drivers for the new sound card, the computer fails to boot. Which quick fix can the user implement to return to the previous working state?
- Boot to Emergency Recovery State.
- Boot to Last Known Good Configuration.
- Boot to Recovery Console.
- Boot to Start Windows Normally.
15. A technician uses the shrink volume feature of the disk management utility and splits the partition. What must the technician do next in order to make use of the new space?
- Partition the unallocated space.
- Format the existing partition.
- Delete all partitions and reinitialize the disk.
- Convert the unallocated space into a dynamic disk.
16. A technician is using the six troubleshooting steps in an attempt to repair a PC. After completing the steps needed to test a theory and determine the cause, the technician still has not solved the problem. Which two steps are likely to be taken next by the technician to establish a plan of action and resolve the problem? (Choose two.)
- Perform an Internet search.
- Ask other users in the area.
- Access helpdesk repair logs.
- Speak with the supervisor of the user.
- Call the helpdesk to log the problem.
17. On a computer that will not boot, which two actions are recommended in the troubleshooting process after verifying the obvious issues such as power to the computer and display, non-bootable media, and the BIOS boot order options? (Choose two.)
- Remove unnecessary peripherals.
- Reinstall the operating system.
- Reset the BIOS settings to factory default.
- Use the Last Known Good Configuration.
- Replace computer components one at a time until the problem is solved.
- Reinstall the user applications.
18. What is the distance limitation of a single data run for UTP cabling without adding networking devices?
- 33 ft (10 m)
- 100 ft (31 m)
- 330 ft (100 m)
- 500 ft (154 m)
19. What is the default subnet mask for a Class A network?
- 0.0.0.255
- 0.0.255.255
- 0.255.255.255
- 255.0.0.0
- 255.255.0.0
- 255.255.255.0
20. Which network protocol is used to automatically assign an IP address to a computer on a network?
- FTP
- DHCP
- ICMP
- SMTP
- APIPA
21. Which open standards-based wireless security mode supports the highest level of security?
- WEP
- WPA2
- WPA
- LEAP
22. What are two network requirements necessary to establish a VPN connection between a remote computer and a private company LAN? (Choose two.)
- low latency network connection
- secure web server
- Internet access
- PSTN access
- VPN client
23. The corporate security policy states that all remote connections use only secure tunnels for data communications. Which encryption technique secures data traveling across the public Internet as if it were traveling across the corporate LAN?
- MD5
- VPN
- WEP
- WPA
24. What type of WAN connection would use 3G or 4G?
- DSL
- satellite
- cable
- POTS
- cellular
25. True or False?
An intrusion detection system works inline and has the ability to drop malicious traffic.
- true
- false
26. Where can a technician enable ACPI mode on a laptop?
- BIOS
- Task Manager
- Device Manager
- Personalization
27. Which two actions must be performed before installing RAM into a laptop? (Choose two.)
- Use thermal compound to attach the memory to the motherboard.
- Before installing the RAM, update the saved CMOS settings to the newly configured amount of RAM.
- Remove the battery.
- Disconnect the display from the bottom of the laptop.
- Disconnect AC power.
- Remove the memory module retaining clips from the slots where the new RAM will insert.
28. Which two items would be part of a laptop preventive maintenance kit? (Choose two.)
- compressed air
- plastic scribe
- soft cloth
- antistatic wrist strap
- flat-head screwdriver
29. What is the purpose of running mobile device apps in a sandbox?
- to enable the phone to run multiple operating systems
- to prevent malicious programs from infecting the device
- to enable separate app icons to be displayed on the home screen
- to bypass phone carrier restrictions that prevent access to unauthorized apps
30. A user has installed a new printer. Which two pieces of information about the printer operation are provided by printing a test page from the computer? (Choose two.)
- confirmation that the color calibration is optimized
- verification of print spool settings
- confirmation that duplex (double-sided) printing is working correctly
- verification that driver software is working correctly
- confirmation that printer and computer are communicating
31. A technician wants to add a new shared network printer to a computer. The printer is not shown in the list of available printers. What two actions can the technician take to add the printer? (Choose two.)
- Enter the printer model.
- Enter the printer IP address.
- Access a command prompt and use the net use command to locate the printer and printer path.
- Browse for the printer on the network.
- Enter the name of the computer used to share the printer.
32. A technician is installing a new printer in a cool, damp environment. After the printer cabling is done, and the software and print driver are installed, the printer test page jams. What is the most likely cause of the print failure?
- incorrect printer driver
- too much humidity
- not enough printer memory
- loose printer cables
33. What type of security attack is being launched when a hacker calls a company to obtain computer login information and pretends to be an employee?
- spyware
- phishing
- adware
- Trojan
- social engineering
34. Which two aspects of a computer can be protected by setting the BIOS password? (Choose two.)
- network address assignment method
- hard drive settings
- operating system login
- operating system booting
- file system management
- firewall settings
35. After logging into a computer, a user can view files but is unable to download the files. What action can the administrator take to allow the user to download the files while preventing deletion of the files?
- Set the folder permissions to Read.
- Set the file permissions to Modify.
- Set the file permissions to Full Control
- Set the file permissions to Read and Execute.
36. The PC support person has heard of an instance where departmental secretaries go to lunch and leave their computers unlocked and remain logged into their account. Which Windows feature would the technician use to help in this situation?
- AutoRun
- BIOS/UEFI password
- idle timeout and screen lock
- Windows firewall
37. A customer is angry and calls to complain that the service scheduled on the computer took longer than expected. The technician reviews the work order and notices that the service was performed by a new employee. How should the technician respond?
- Verify that the computer is working properly now.
- Listen to the complaint and then apologize for any inconvenience caused by the lengthy service on the computer.
- Explain that the repair technician sent to perform the service is inexperienced.
- Put the customer on hold until a supervisor is available.
38. Refer to the exhibit. During the troubleshooting of software that is installed on a computer system, a level one technician requires help from a level two technician. The file shown in the exhibit must be sent to the level two technician. How should the level one technician deliver this file?
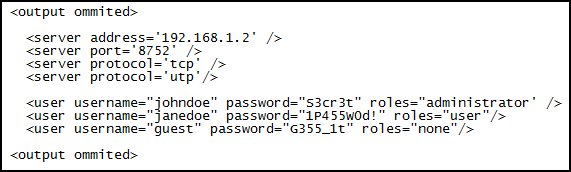
- This file should not be shared with the level two technician.
- Replace all passwords in the file with <password omitted> before emailing the file and then supply the passwords by secure means, if required.
- Send the file as it is to the level two technician.
- Deliver the file in printed format only.
39. What determines the level of support that a call center technician will provide to an individual customer?
- Support is based on the SLA for that customer.
- All customers receive the same level of support by the call center.
- A level one technician will provide a higher level of support than a level two technician.
- An individual call center technician chooses the level of support based on the time available to assist the customer.
40. After resolving an intermittent CD-ROM drive fault by firmly reconnecting a loose cable, the technician then decides to inspect all other cable connections to prevent other faults from occurring. Which two conditions will help to prevent future cable and connector faults? (Choose two.)
- There are no missing or bent connector pins.
- Cables are stretched tight between connectors.
- Cables are not bent sharply around adapter cards.
- Device data cables exceed manufacturer specifications.
- The connector retaining screws have been over tightened with a screwdriver.
41. A technician has been asked to reinstall the OS on a computer that has a corrupted operating system. The technician inserts the installation media in the optical drive. What would be the most likely action the technician should perform next?
- Change the boot sequence in the BIOS.
- Change the BIOS password.
- Flash the BIOS for a firmware upgrade.
- Change clock speeds in the BIOS.
42. What are three common causes of operating systems problems? (Choose three.)
- a corrupted registry
- incorrect IP addressing information
- loose cable connections
- failed service pack installation
- CMOS battery problem
- virus infection
43. Which built-in BIOS diagnostic test would a technician run to check a computer boot problem?
- memory test
- POST test
- start test
- battery test
44. What are three features of GPS on mobile devices? (Choose three.)
- phone number lookup
- navigation
- specialized search results
- device tracking
- remote wipe
- gas mileage calculations
45. In Windows 7, which path will give access to parental control?
- Start > Control Panel > Network and Internet > Internet Options > Security tab
- Start > Control Panel > User Accounts and Family Safety > Parental Controls
- Start > Control Panel > User Accounts and Family Safety > User Accounts > Change User Account Control settings
- Start > Control Panel > Network and Internet > Internet Options > Parental Control link
46. A user calls the help desk reporting that a laptop with Linux freezes on startup and displays kernel panic. What could cause this problem?
- A driver has become corrupted.
- GRUB or LILO has been deleted.
- GRUB or LILO has been corrupted.
- An application is using a resource that has become unavailable.
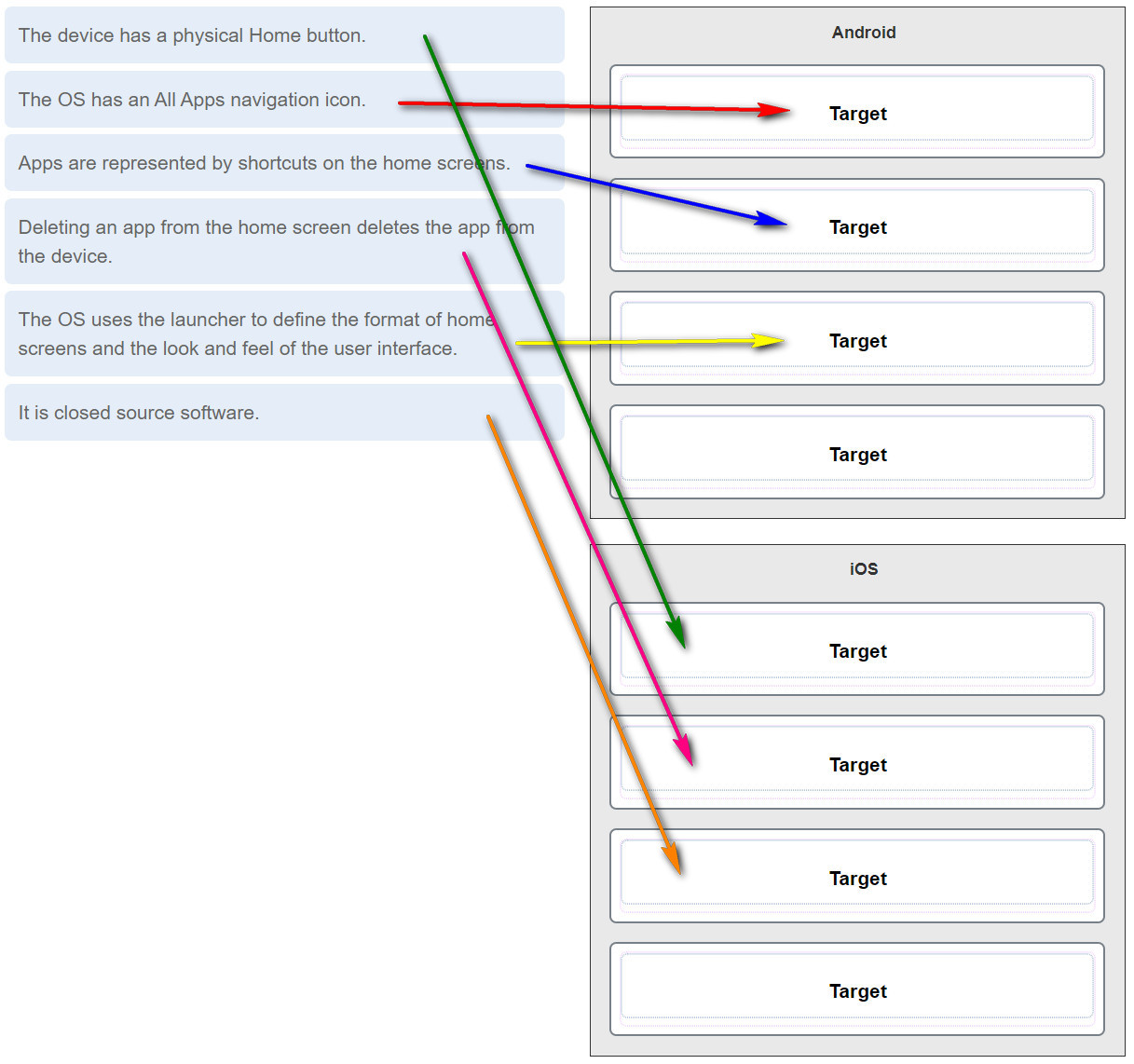
47. Drag the statements on the left to the mobile OS that they describe on the right. (Not all targets are used.) Question
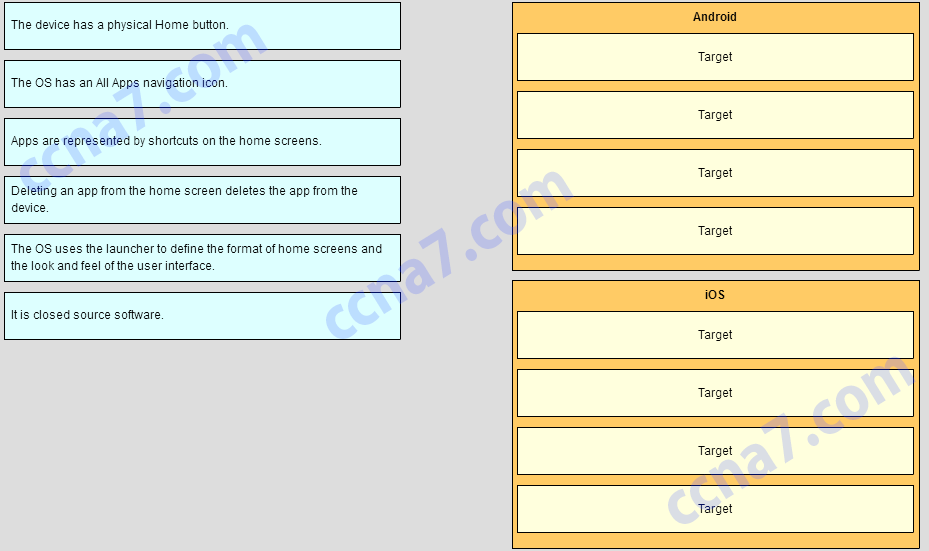
Answer
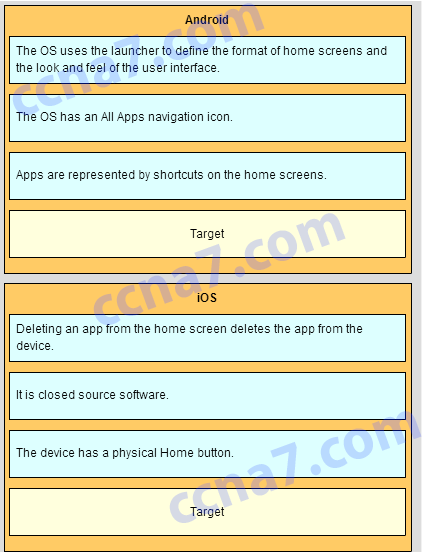
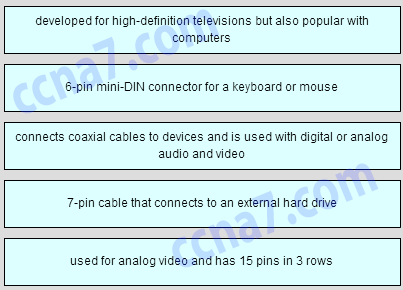
48. Drag the description to its matching cable type. Question
Answer
49. Match the computer problem with the area of the system affected by the problem. Question
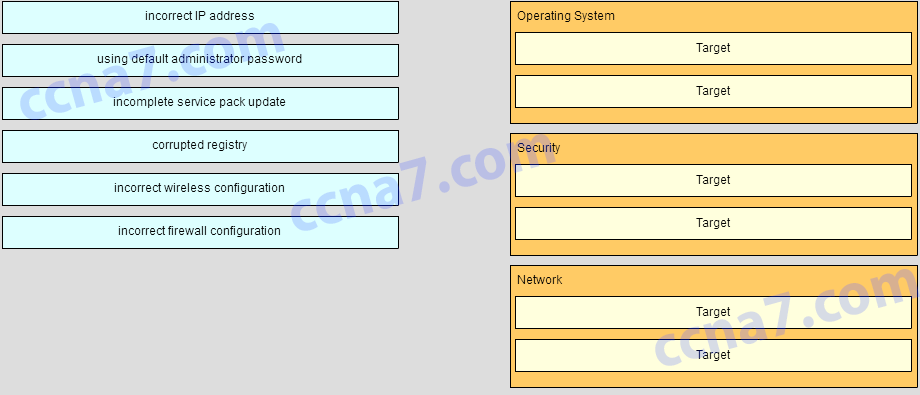
Answer
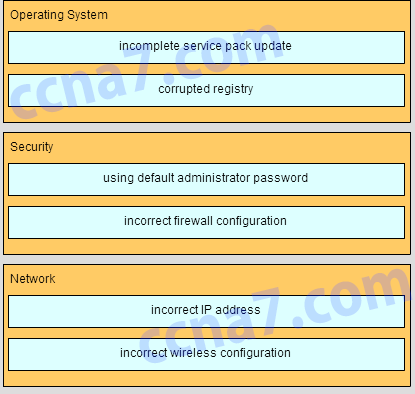
50. Drag the statments on the left to the mobile OS that they describe on the right. (Not all targets are used.)
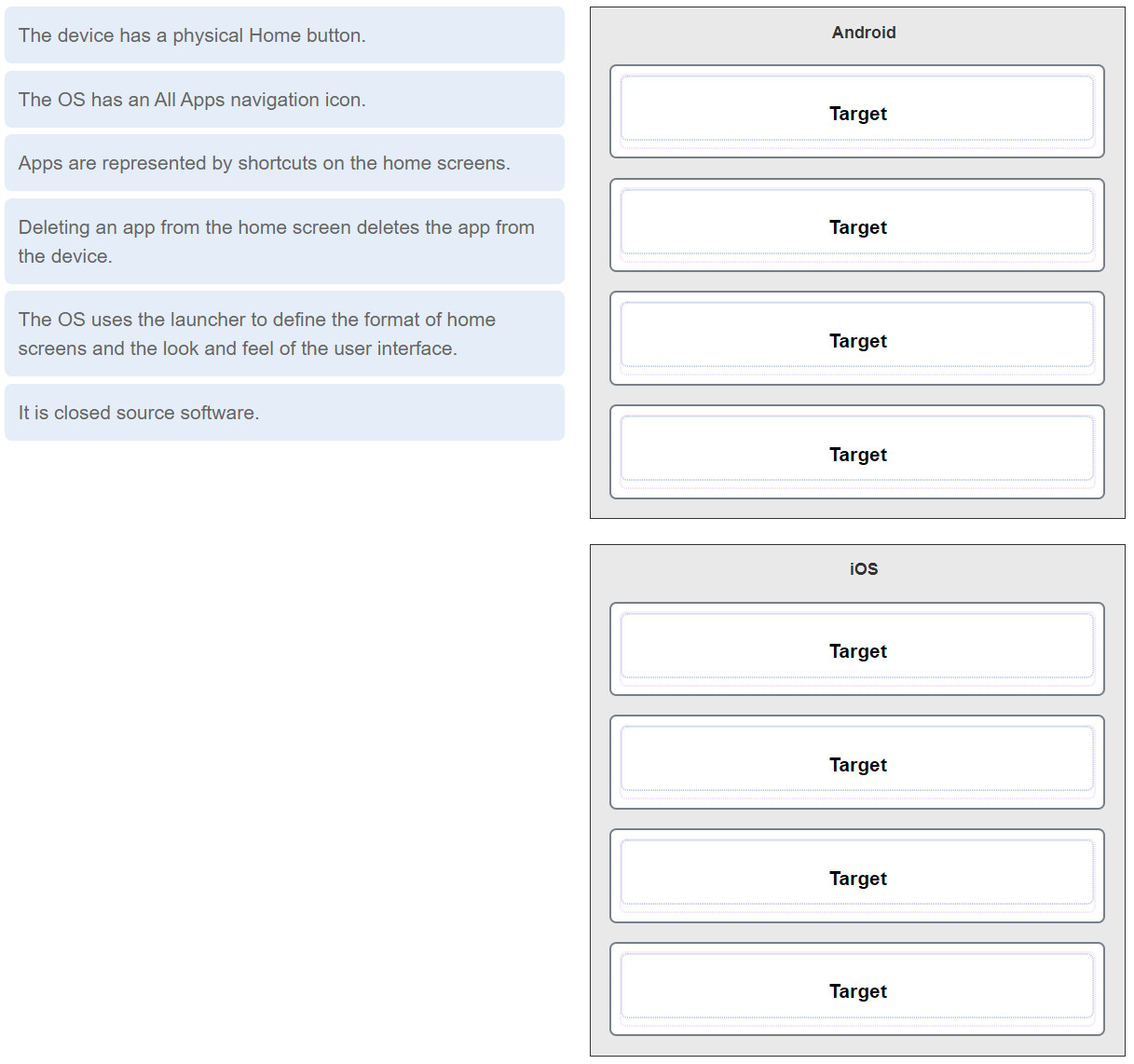
Answer
51. Refer to the exhibit. A user issues the command ls -l in a Linux system. Match the description to the result of the command output. (Not all options are used.)
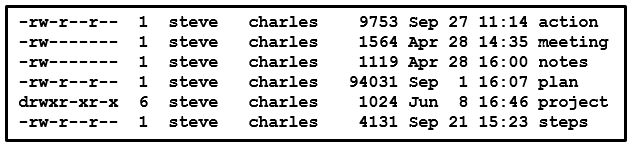
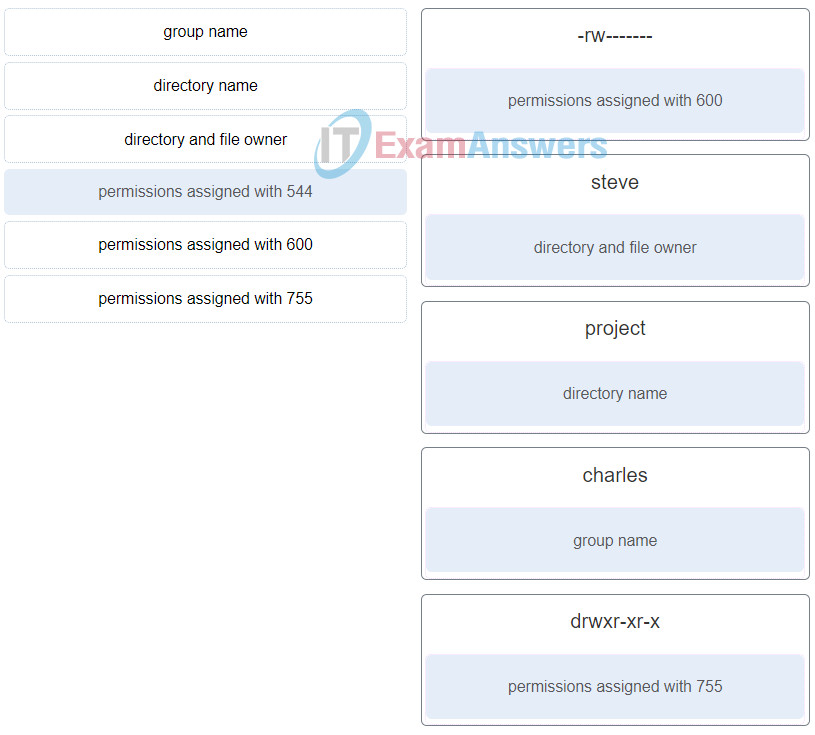
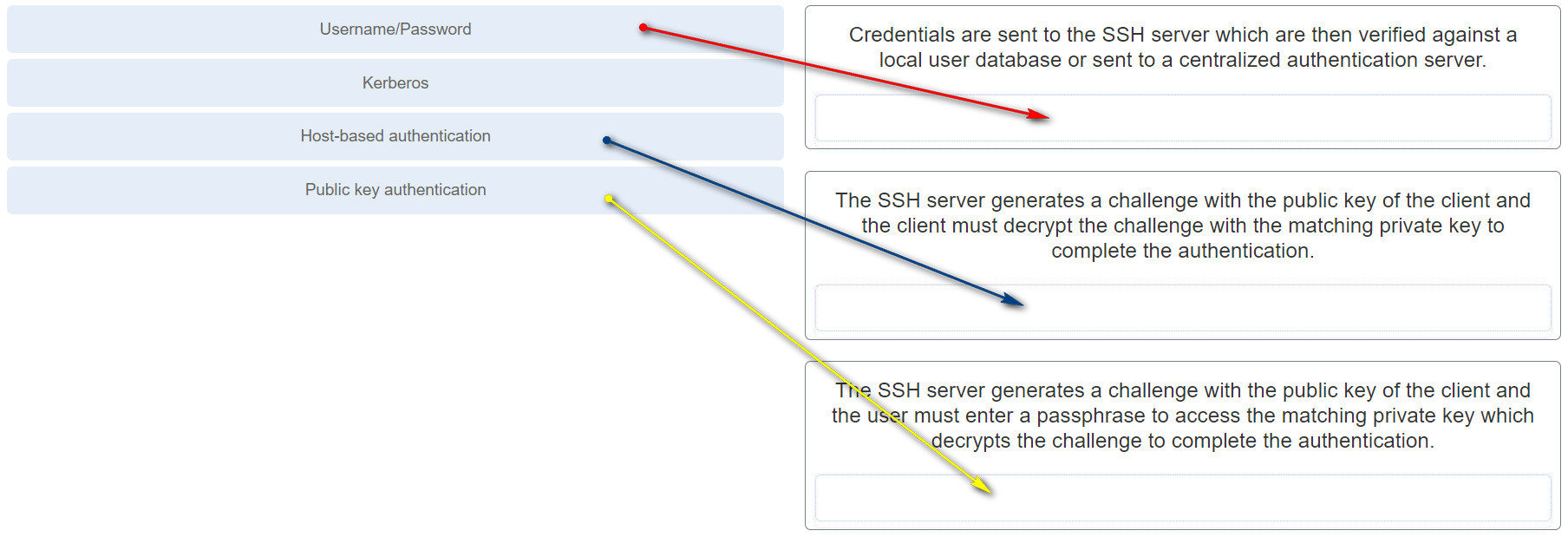
52. Match remote access authentication methods to the description. (Not all options are used.)
Answer
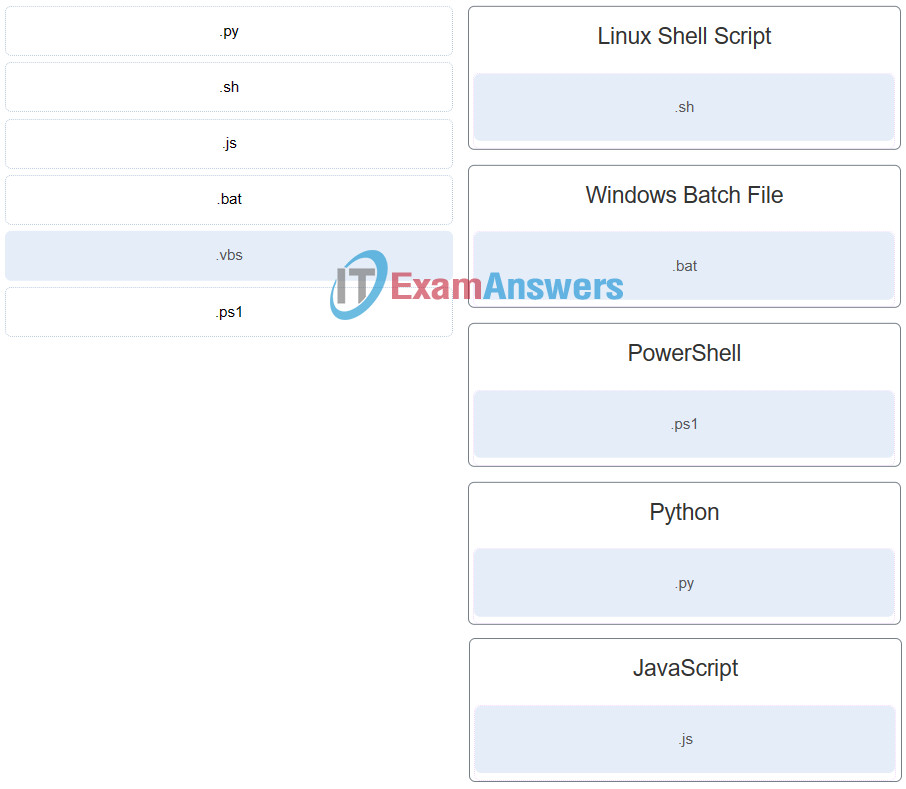
53. Match the scripting language with the script file name extension. (Not all options are used.)
54. What are two potential risks that could result from rooting or jailbreaking a mobile device? (Choose two.)
- improving device performance
- not properly creating or maintaining sandboxing features
- enabling app access to the root directory
- allowing the user interface to be extensively customized
- enabling features that are disabled by a cellular carrier
55. What two tasks should be done regularly to preserve the security and integrity of data and applications on mobile devices. (Choose two.)
- Password protect iTunes or Google Play accounts.
- Use airplane mode if you are accessing the Internet at an open Wi-Fi site.
- Ensure that the operating system software and applications contain the latest updates.
- Unmount all unused disk partitions.
- Back up user data on a regular basis.
- Execute a factory reset once a month to remove all unidentified malicious software.
56. A user notices that a mobile device is draining power faster than is normal. What are three causes of quick battery drain? (Choose three.)
- The display is set to a high level of brightness.
- The airplane mode is turned on.
- The device is connecting over a VPN.
- An app is not compatible with the device.
- An app is using too many resources.
- The device is roaming between call towers.
57. Which two operations can help prevent a mobile device from being tracked without permission? (Choose two.)
- Disable or remove apps that allow connections to the GPS.
- Set the device to connect only to known WiFi networks.
- Use a VPN connection whenever possible.
- Turn off the GPS when not in use.
- Set the device to not store credentials.
58. Which component uses the greatest amount of power on most mobile devices?
- camera
- CPU
- media player
- LCD screen
59. What tool is included in the Mac OS X for backing up disks to image files and recovering disk images?
- System Restore
- Deja Dup
- Disk Error-Checking
- Disk Utility
60. When a user tries to run a program a missing or corrupt DLL message is displayed. What are two possible solutions to this problem? (Choose two.)
- Run sfc/scannow in Safe Mode.
- Use the msconfig command to adjust the startup settings for the program.
- Run Windows Startup Repair.
- Reinstall the correct drivers.
- Register the DLL file using the regsvr32 command.
61. A computer repeatedly locks without any error message. Which two conditions may be the cause of the problem? (Choose two.)
- The computer has a virus.
- The UAC has been turned off.
- The CPU needs to be upgraded.
- An update has corrupted the operating system.
- The index service is not running.
- The user has breached the user security policy.
62. A user has submitted a trouble ticket stating that their computer is showing the error “BOOTMGR is missing”. The IT technician replicates the error and finds that it occurs after the POST of this Windows 10 machine. What are two possible solutions for this problem? (Choose two.)
- Run the bootrec /fixboot command.
- Run chkdsk /F /R from the recovery console.
- Restore BOOTMGR using the Windows Recovery Environment.
- Run virus removal software.
- Use the last known good configuration to boot the computer.
63. A user calls the help desk and reports that invalid system disk or invalid boot disk error messages display on the workstation when it is powered on. When a technician comes to the office, the user mentions that the workstation was working well the day before. The technician suspects that the MBR is corrupted. Which process can the technician use to check and repair the MBR?
- Run the bootrec command.
- Run the sfc command.
- Run the chkdsk command.
- Boot the workstation in Safe Mode.
64. A technician is visiting a website and is using Google Chrome on a Windows 10 PC. The technician is trying to view the password for the website. The technician uses the Credential Manager to view the password but cannot see it. What could be the cause?
- The browser had crashed after accessing the website.
- The Credential Manager will only store system passwords.
- The website visited placed a cookie disallowing the storage of the password.
- Web credentials are not saved for sites accessed by browsers other than Explorer and Edge.
65. A technician is troubleshooting an employee laptop that has a wired network connectivity issue. The laptop can connect to the internet when used inside the office but cannot connect to the network when used in a research lab. The company uses DHCP in the office but does not use DHCP in the research lab. How can the technician address this issue?
- Implement an Alternate Configuration IPv4 address on the laptop.
- Modify the DNS server IPv4 address on the laptop.
- Modify the proxy settings used on the laptop.
- Adjust the default gateway IPv4 address on the laptop.
66. Which two statements are correct about level one and level two technicians? (Choose two.)
- Level two technicians prepare a work order and escalate it to a level one technician if a problem cannot be resolved within ten minutes.
- Level two technicians are often referred to as “incident screeners,” and level one technicians are often referred to as “product specialists.”
- Level two technicians are usually more knowledgeable about technology than the level one technicians are.
- Level two technicians usually respond to the “down calls” as they may be able to resolve them faster.
- Level one technicians usually work on the problems that require opening up the computer case.
67. What two roles or tasks are associated with level two technicians? (Choose two.)
- escalating a trouble ticket to a higher level technician
- gathering customer information to initiate a work order
- remotely updating drivers and software on customer computers
- gathering diagnostic information from a customer computer
- prioritizing incoming calls according to their severity
68. When performing computer forensics what is required to prove a chain of custody?
- an admission of guilt
- proper documentation procedures
- expert testimony
- collected evidence
69. A technician has copied several commercial movies to a company server to be shared with colleagues. How would this behavior be classified?
- acceptable
- ethically wrong and illegal
- illegal but ethical
- ethically wrong but legal
70. A call center technician answers a call from a frequent customer who is known to be impatient and lacks experience with computers. The customer has an issue with an application that the call center supports. The customer informs the technician that the problem had been reported before but the original technician was rude, did not listen, and did not fix the problem. If the technician is confident that the problem can be resolved by increasing the amount of memory in the computer, what should the technician do?
- Suggest that the customer purchase a new computer.
- Tell the customer to install 2 GB of DDR3 PC3-10600 RAM.
- Confirm the issues and give detailed instructions to solve the problem.
- Explain that the original technician is no good and the supervisor will be told.
71. A call center technician has asked a customer to perform a simple operation to fix a problem on a computer. The customer seems unable to perform the task. What should the technician do?
- Determine whether the customer would prefer to receive the instructions in another form, such as emailed, illustrated written instructions.
- Explain to the customer that it is a simple task and ask the customer to try it again.
- Tell the customer that another technician will explain the task .
- Ask the customer to find someone with more experience to perform the task.
72. An IT technician is troubleshooting a file error on an employee laptop. While working in the system files directory, the technician notices that the User Account Control (UAC) box appears requesting a password. What should the IT technician do next?
- Call the employee and apologize for the delay in repairs and request the administrator password over the phone.
- Call the employee and ask the employee to come to the IT department to enter the necessary credentials.
- Shutdown the laptop and email the employee with a request for the administrator account password of the supervisor.
- Shutdown the laptop, boot it from a bootable CD/USB, and modify the system files to complete the repair.
73. Which two Windows operating systems cannot be upgraded to Windows 8.1 64-bit? (Choose two.)
- Windows 7 64-bit
- Windows 7 32-bit
- Windows 8 64-bit
- Windows XP 64-bit
- Windows Vista 64-bit
74. A user wishes to upgrade a PC to Windows 10 from a PC that is running a 32-bit version of Windows 7. Which two editions of Windows 10 will support this upgrade? (Choose two).
- 64-bit version of Windows 10 Pro
- 32-bit Windows Home
- 32-bit version of Windows 10 Pro
- 64-bit version of Windows 10 Enterprise
- 64-bit version of Windows Home
75. After a computer is powered on, Windows 7 fails to start. What initial procedure would a technician use to deal with this failure?
- Press the F12 key during the boot process and start the computer in Safe Mode.
- Boot from a Windows 7 installation media and access the System Restore utility.
- Access the Control Panel and choose Restore Files from Backup from the System and Security menu.
- Create a System Repair Disc and restore the image.
76. Which statement is correct about installing a 32-bit operating system on a x64 architecture?
- This combination will provide better security.
- The OS can address more than 128 GB of memory.
- The OS will run correctly.
- The OS will always make use of all the RAM available.
77. A technician is attempting to create multiple partitions on a hard disk that is using the boot sector standard that supports a maximum partition size of 2TB. What is the maximum number of primary partitions allowed per hard drive?
- 128
- 32
- 4
- 2
- 16
- 1
78. A network administrator is tasked with deployment of Windows 10 Pro for a large number of new PCs in the company. The administrator uses a PC to perform a base installation together with standard company applications. The PC is tested to be fully functional. Which tool must the administrator use to remove all computer and user specific information before building a deployable image from the disk?
- Unattended.bat
- Ntoskrnl.exe
- Windows Easy Transfer
- Sysprep.exe
79. A network analyst is booting a PC that has Windows 8 installed. The boot process is currently working on the following step: The BIOS boots the computer using the first drive that contains a valid boot sector. What is the next step that will happen in the boot process?
- WINLOGON.EXE displays the Windows Welcome screen
- NTOSKRNL.EXE starts the login file called WINLOGON.EXE.
- The code in the boot sector is executed and the control of the boot process is given to Windows Boot Manager.
- The Windows kernal takes over the boot process.
80. A help desk technician notices an increased number of calls relating to the performance of computers located at the manufacturing plant. The technician believes that botnets are causing the issue. What are two purposes of botnets? (Choose two.)
- to gain access to the restricted part of the operating system
- to transmit viruses or spam to computers on the same network
- to withhold access to a computer or files until money has been paid
- to record any and all keystrokes
- to attack other computers
81. A company has a security policy that permits the reuse of wiped drives in other computers. The wiped drives are often used for additional storage or as a replacement drive. What are two methods that could be used to wipe data? (Choose two.)
- EFS encryption
- degaussing equipment
- data wiping software
- multifactor erasure
- biometric scanner
82. A technician is configuring a SOHO computer. The technician wants to create a local account that requires a password and wants a screen saver to appear if the person using the computer steps away for a period of time. Which two Windows Control Panels will the technician use to accomplish these tasks? (Choose two.)
- Programs
- Hardware and Sound
- Personalization
- Ease of Access
- Network and Internet
- User Accounts
83. After confirming the removal of a virus from a computer, how should the technician ensure and verify the full functionality of the system?
- Talk with the user to determine the cause of the problem.
- Check for the latest OS patches and updates.
- Gather information from a number of sources to clearly identify the problem.
- Document the problem and the procedures performed to solve it.
84. What is the next troubleshooting step after a theory of probable cause has been established?
- Document findings and outcomes.
- Identify the exact problem.
- Test the theory to determine cause.
- Establish a plan of action.
85. A technician has been notified of a problem on the network. After investigation, the technician determines that a specific internal company computer is launching an attack on other company computers. Which type of malware is being used?
- rootkit
- Trojan
- spoofing
- DoS
86. What is a recommended best practice for a technician who must perform tasks that require administrative access?
- Ask the current user to log off, restart the computer, and then log in with the administrator account.
- Prevent the computer from contacting the network authentication server by disabling the network card and then log in with an administrator account.
- Log off the computer and then log in with an account with administrator privileges.
- Use a standard account with limited permissions, and then use the Run as Administrator option to perform the task that requires elevated privileges.
87. A technician is troubleshooting a Windows 10 PC that has a .dll file for an application that has not been registered. Which administrative command-line tool or command can be used to address this?
- robocopy
- type
- regsvr32
- net user
88. A technician has been asked by a manager to recommend a security solution for protecting a computer against boot sector viruses. Which security technique should the technician recommend?
- encryption
- antimalware
- TPM
- dual authentication
89. True or False? When a user is working on a system that uses a network file system, there is no difference between accessing a file stored locally or on another computer on the network.
- False
- True
90. An instructor is discussing facts about different mobile device operating software. The instructor states: “To synchronize a mobile device to a PC, iTunes must be installed on the PC.” To which OS does this relate: iOS, Android, or both?
- both
- Android
- iOS
91. A client installed a new driver for a device three weeks ago; however, this driver is causing the system to freeze occasionally and the client wishes to revert back to the old driver. What option can be used to address this issue without loss of data or applications?
- Reset this PC.
- Use Advanced Start-up.
- Go back to the initial Windows build.
- Uninstall and reinstall the device using device manager.
92. When a security audit is performed at a company, the auditor reports that new users have access to network resources beyond their normal job roles. Additionally, users who move to different positions retain their prior permissions. What kind of violation is occurring?
- least privilege
- password
- audit
- network policy
93. An instructor is discussing facts about different mobile device operating software. The instructor states: “To help prevent malicious programs from infecting the device, mobile device apps are run in a sandbox that isolates them from other resources.” To which OS does this relate?
- iOS
- Android
- or both
94. True or False? Hard drives partitioned with a master boot record (MBR) cannot have an extended partition or logical drives.
- True
- False
95. A technician is troubleshooting a Windows 10 computer that displays an “Invalid Boot Disk” error message. What should be the first action the technician should take to troubleshoot the issue?
- Change the boot order in the UEFI/BIOS settings to select the drive that has the operating system installed as the first boot device.
- Boot the computer in Safe Mode and run sfc / scanno w .
- Use the last known good configuration to boot the computer.
- Run the command chkdsk .
96. A technician is troubleshooting a Windows 10 PC. The PC has an application that displays an error message about a missing DLL. The technician has located the DLL file on the PC and wants to register it. Which command line tool can the technician use for the task?
- regsvr32
- dism
- sfc
- regedit
97. A technician wants to split a large partition on a drive in a Windows 10 PC without loss of any data. How can this be accomplished?
- Shrink the existing partition and create a new partition from the unallocated space.
- Delete the existing partition and format the disk with two new partitions.
- Reinitialize the disk and create new partitions.
- Delete the existing partition and create two new partitions.
98. A network technician is troubleshooting a DHCP issue for a user and has requested assistance from a senior technician. The senior technician provides the graphic to illustrate configuration options. What is the purpose of the Alternate Configuration feature?
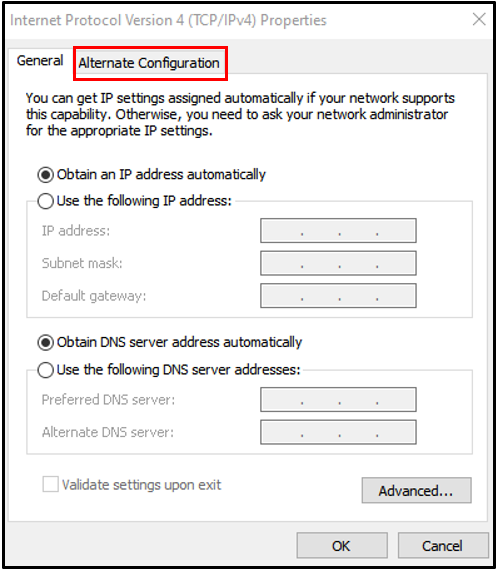
- It allows an administrator to choose a secondary network interface card (NIC) for the PC to use if it is having difficulty contacting a DHCP server.
- It allows an administrator to specify the IP address of a DHCP server when a PC is having trouble receiving an IP address dynamically.
- It allows an administrator to configure an alternative IP address for the PC to use if it is unable to contact a DHCP server.
- It allows an administrator to change the MAC address of the PC in order to receive another IP address from a DHCP server.
99. Which two data storage locations contain persistent data that can be used by computer forensics specialists? (Choose two.)
- RAM
- CPU registers
- hard disk drives
- cache
- solid state drives
100. Chad, a level one call center technician, receives a customer phone call. The customer has an issue that Chad does not have the knowledge to answer. The customer is irritated that Chad cannot provide immediate assistance. Which two things should Chad do next? (Choose two.)
- Inform the customer of the need to call back later.
- Document the reason the customer called and create a support ticket.
- Escalate the customer to a level two technician.
- Ask the customer further questions to diagnose and attempt to fix the problem.
- Place the customer on hold until the customer has time to cool down.
101. What is the best definition of personally identifiable information (PII)?
- Data that is collected by businesses to track the digital behavior of consumers.
- Data that is collected from servers and web browsers using cookies in order to track a consumer.
- Data that is collected from servers and websites for anonymous browsing.
- Data that is collected by businesses to distinguish identities of individuals.
102. An instructor is discussing facts about different mobile device operating software. The instructor states: “Remote backups are a cloud-enabled service for mobile devices.” To which OS does this relate: iOS, Android, or both?
- iOS
- both
- Android
103. A Windows 10 computer suddenly started experiencing network connectivity issues after the latest Windows updates completed a week ago. What option can be used to address this issue without loss of data or applications?
- Use Advanced Start-up.
- Reset this PC.
- Restore using Sysprep.
- Go back to the initial Windows build.
104. A user wants to display and change information about computer users. Which administrative command-line tool or command can be used to address this?
- diskpart
- net user
- mstsc
- chkdsk
105. A user wants to display the contents of a text file in a command interpreter. Which administrative command-line tool or command can be used to address this?
- type
- net user
- chkdsk
- robocopy
106. True or False? Modern operating systems boot the computer, manage the file system, and support only one user, task, or CPU.
- True
- False
107. A user tries to install an application on a Windows 10 Pro PC but it fails. The user tries to uninstall the application but it fails to uninstall. What option can be used to address this issue without loss of data or applications?
- Use Advanced Start-up.
- Use Restore Point.
- Uninstall and reinstall the device using device manager.
- Restart the Windows Update services.
108. True or False? Multitasking describes a computer operating system that is capable of running multiple applications at the same time.
- True
- False
109. A technician is working on a Windows 10 PC that keeps freezing occasionally after a driver update. System restore has been turned off. What option can be used to address this issue without loss of data or applications?
- Reset this PC.
- Uninstall and reinstall the device using device manager.
- Restart the Windows Update services.
- Restore using Sysprep.
110. A technician is troubleshooting a Windows 10 PC that will not do any windows updates automatically or manually. What option can be used to address this issue without loss of data or applications?
- Delete all the files in C:\Windows\SoftwareDistribution folder and restart the PC.
- Perform a repair of Windows using Installation media.
- Restart the Windows Update services.
- Uninstall and reinstall the device using device manager.
111. A user wants to check a file system for errors, including errors with physical media. Which administrative command-line tool or command can be used to address this?
- chkdsk
- type
- net user
- robocopy
112. A technician wants to create customized system image files that will be installed on computers in the network. Which administrative command-line tool or command can be used to address this?
- dism
- robocopy
- type
- chkdsk
113. A user wants to terminate a running process on a computer. Which administrative command-line tool or command can be used to address this?
- taskkill
- robocopy
- type
- chkdsk
114. A technician wants to copy files and entire directory trees from one volume to another volume on a Windows 10 PC. Which administrative command-line tool or command can be used to address this?
- robocopy
- type
- net user
- chkdsk
115. A technician is troubleshooting a Windows 10 PC that has corrupted system files. Which administrative command-line tool or command can be used to address this?
- sfc
- chkdsk
- robocopy
- diskpart
116. A user wishes to see a summary of software information and system components, including hardware components, on a Windows 10 PC. Which administrative command-line tool or command can be used to address this?
- msinfo32
- chkdsk
- robocopy
- diskpart
117. A technician has just configured the security policy on a Windows 10 PC and wants to ensure the policy is implemented immediately. Which administrative command-line tool or command can be used to address this?
- gpupdate
- diskpart
- chkdsk
- mstsc
118. A technician has been asked by a manager to recommend a security solution for protecting a computer against keyloggers. Which security technique should the technician recommend?
- antimalware
- IPS
- encryption
- SSL
119. A technician has been asked by a manager to recommend a security solution for protecting a computer against adware programs. Which security technique should the technician recommend?
- antimalware
- ping sweep
- encryption
- SSL
120. A technician has been asked by a manager to recommend a security solution for protecting a computer against rootkits. Which security technique should the technician recommend?
- antimalware
- port scan
- encryption
- SSL
121. A technician has been asked by a manager to recommend a security solution for protecting a computer against Trojans. Which security technique should the technician recommend?
- antimalware
- RAID
- dual authentication
- encryption
122. A technician has been asked by a manager to recommend a security solution for protecting a computer against firmware viruses. Which security technique should the technician recommend?
- antimalware
- TPM
- dual authentication
- encryption
123. True or False? Smartphones require an operating system before they can be operated.
- True
- False
124. True or False? When a hardware device is installed, the operating system needs to use a device driver to access and use that hardware.
- True
- False
125. True or False? Windows 10 64-bit version can be installed on as little as 1GB of hard drive space.
- False
- True
126. True or False? DirectX is a collection of APIs related to multimedia tasks for Microsoft Windows.
- True
- False
127. True or False? The registry is a database that only contains information about the device drivers on a computer.
- False
- True
128. True or False? Multithreading describes an operating system that can support two or more CPUs.
- False
- True
129. An instructor is discussing facts about different mobile device operating software. The instructor states: “The start voice control function can be performed with the home button.” To which OS does this relate: iOS, Android, or both?
- iOS
- both
- Android
130. An instructor is discussing facts about different mobile device operating software. The instructor states: “The mobile devices have a feature called Spotlight that is a search tool that provides information from many sources.” To which OS does this relate: iOS, Android, or both?
- iOS
- both
- Android
131. An instructor is discussing facts about different mobile device operating software. The instructor states: “This OS can be used by programmers to operate devices like laptops, smart TVs, and e-book readers.” To which OS does this relate: iOS, Android, or both?
- Android
- both
- iOS
132. An instructor is discussing facts about different mobile device operating software. The instructor states: “The icon on the Home screen is a shortcut to the app.” To which OS does this relate: iOS, Android, or both?
- Android
- both
- iOS
133. An instructor is discussing facts about different mobile device operating software. The instructor states: “To help prevent malicious programs from infecting the device, mobile device apps are run in a sandbox that isolates them from other resources.” To which OS does this relate: iOS, Android, or both?
- both
- Android
- iOS
134. An instructor is discussing facts about different mobile device operating software. The instructor states: “WIFI hotspots are a location data source that can be used by locator apps to determine the position of a mobile device.” To which OS does this relate: iOS, Android, or both?
- both
- Android
- iOS
135. An instructor is discussing facts about different mobile device operating software. The instructor states: “GPS signals are used to enable geocaching, geotagging and device tracking on these mobile devices.” To which OS does this relate: iOS, Android, or both?
- both
- iOS
- Android
136. An instructor is discussing facts about different mobile device operating software. The instructor states: “The user interface can be extensively customized using rooting or jailbreaking into a mobile device.” To which OS does this relate: iOS, Android, or both?
- both
- Android
- iOS
137. What is the purpose of “branching” in high-level programming languages?
- to add programming code that links to another application
- to have a series of control flow statements
- to add a different programming language to existing code
- to add sequential programming code
138. Which statement is true regarding mobile devices using the Wireless Wide Area Network (WWAN)?
- The bandwidth available over WWAN connections is fixed and is independent of the technologies supported by the adapter and the transmitter.
- They require a 64-bit operating system.
- They can only be connected through external WWAN USB adapters.
- They require an adapter to link to a cellular provider’s network through the nearest base station or transmitter.
139. A user is trying to execute a file using elevated permission. The user right-clicks the file, chooses Run as Administrator, and chooses Yes in the User Account Control (UAC) window. The operation fails. What is the reason?
- The UAC does not have the elevated privileges option.
- The directory housing the file is read-only.
- The user is not a member of the administrator group.
- The login password of the user is invalid.
140. A technician has just purchased a new Windows 10 PC and wants to transfer selected files, folders, profiles, and applications from the old Windows PC. What tool or utility does Microsoft recommend to do this?
- Upgrade Assistant
- PCmover Express
- User State Migration Tool
- Windows Task Manager
141. Which tool is available to transfer user data and settings from an old Windows 10 PC to a new Windows 10 PC?
- Windows Upgrade Assistant
- Windows User Manager
- User State Migration tool
- Windows Easy Transfer
- Windows Upgrade Advisor
142. What is the default file system used during a fresh installation of Windows 10?
- HPFS
- FAT16
- NTFS
- FAT32
143. What is a possible situation when it might be necessary to boot Windows 10 from a bootable recovery USB device?
- to delete registry keys
- to disable background services
- to partition the hard drive
- to repair the operating system
144. A manager is booting a tablet that has Windows 10 installed. The boot process is currently working on the following step: The Windows kernel takes over the boot process. What is the next step that will happen in the boot process?
- NTOSKRNL.EXE starts the login file called WINLOGON.EXE.
- The code in the boot sector is executed and the control of the boot process is given to Windows Boot Manager.
- WinLoad loads two files that make up the core of Windows: NTOSKRNL.EXE and HAL.DLL.
- Winload uses the path specified in BOOTMGR to find the boot partition.
145. An accountant is booting a PC that has Windows 10 installed. The boot process is currently working on the following step: BIOS locates and reads the configuration settings that are stored in the CMOS memory. What is the next step that will happen in the boot process?
- The code in the boot sector is executed and the control of the boot process is given to Windows Boot Manager.
- The BIOS boots the computer using the first drive that contains a valid boot sector.
- WinLoad loads two files that make up the core of Windows: NTOSKRNL.EXE and HAL.DLL.
- Winload uses the path specified in BOOTMGR to find the boot partition.
146. What is the name of the Windows Phone 10 digital, or virtual, assistant?
- Bing
- Spotlight
- Cortana
- Nova Launcher
147. What are two possible solutions to any Windows computer restarting continuously and never displaying the desktop? (Choose two.)
- Run chkdsk /F /R from the recovery console.
- Reset the hard drive jumpers.
- Open Control Panel and navigate to System and Security and disable automatic restart.
- Upgrade the processor.
- Upgrade the video card.
- Access the BIOS and change the boot order options.
148. Where are 32-bit program files located in a 64-bit version of Windows 10 Pro?
- c:\Windows\system32
- c:\users
- c:\Program files
- c:\Program files (x86)
149. A corporate office is considering using an MDM policy to enhance its security parameters. What is achieved through the implementation of the MDM policy?
- It can be used to inventory all corporate assets.
- Sets policies for the applications that are allowed on a device.
- Blocks and tracks all incoming TCP connections.
- It can be used to log the onboarding of BYOD devices.
150. A technician receives a trouble ticket from a user reporting that a website is no longer accessible. What two questions would the technician ask to narrow down the potential problem? (Choose two.)
- Can you access other web sites from this computer browser?
- What operating system is installed on your computer?
- Could you access this web site previously from this device?
- What model computer are you using to access this site?
- Do you remember your password to this web site?

Where are 32-bit program files located in a 64-bit version of Windows 10 Pro?
I added. Thank you.
I encountered this question and it could possibly help new people
A corporate office is considering using an MDM policy to enhance its security parameters. What is achieved through the implementation of the MDM policy?
A. It can be used to inventory all corporate assets.
B. Sets policies for the applications that are allowed on a device.
C. Blocks and tracks all incoming TCP connections.
D. It can be used to log the onboarding of BYOD devices.
I added. Thank you.
A technician receives a trouble ticket from a user reporting that a website is no longer accessible. What two questions would the technician ask to narrow down the potential problem? (Choose two.)
Can you access other web sites from this computer browser?
What operating system is installed on your computer?
Could you access this web site previously from this device?
What model computer are you using to access this site?
Do you remember your password to this web site?
Thank you for sharing.
Question 96: A computer repeatedly locks without any error message. Which two conditions may be the cause of the problem?
The correct answers should be:
What is a recommended best practice for a technician who must perform tasks that require administrative access?
In addition to nontechnical users having a standard user account, it is also a best practice to make technical staff use a limited account. Then when an administrative task is needed, the technician uses the Run as Administrator option and provides the appropriate credentials of an account that has elevated credentials for the one task.
Fixed! Thanks for sharing!!
Hi, I would like if CCNA Questions Answers would respond to this,and anyone using this website for this particular exam to read this, not all of the answers on this page are correct. I have done the exam 5 times using the answers from this website and still get around 10 wrong. There is a website called infraexam.com which has this same exam and has all the correct answers except for two questions. The first one is:\
What is a recommended best practice for a technician who must perform tasks that require administrative access?
The correct answer is Using a standard account with limited permissions, use the Run as Administrator option to perform the task that requires elevated privileges.
The other question is has the correct answer on this page but not on infraexam.com
A user calls the help desk and reports that invalid system disk or invalid boot disk error messages display on the workstation when it is powered on. When a technician comes to the office, the user mentions that the workstation was working well the day before. The technician suspects that the MBR is corrupted. Which process can the technician use to check and repair the MBR?
I would like the author CCNA Question Answers I assume, to try and fix the answers on this page to match the ones on infraexam.com with the questions i listed above as exceptions. I really like this website and I know a lot of people rely on it so I would really appreciate it if you put the correct answers. I mean this in the nicest way possible. Thanks, Have a nice day!
Fixed. I will review all other question, many thanks for your report!
True or False? Multitasking describes a computer operating system that is capable of running multiple applications at the same time.
Thanks for sharing!
True or False? Modern operating systems boot the computer, manage the file system, and support only one user, task, or CPU.
added, thanks you
A user tries to install an application on a Windows 10 Pro PC but it fails. The user tries to uninstall the application but it fails to uninstall. What option can be used to address this issue without loss of data or applications?
105 Answers should be
Ensure that the operating system software and applications contain the latest updates.
Back up user data on a regular basis.
57
Turn off the GPS when not in use
Disable or remove apps that allow connections to the GPS
A user wants to display the contents of a text file in a command interpreter. Which administrative command-line tool or command can be used to address this?
a. type
b. net user
c. chkdsk
d. robocopy
type
107. Disk Utility
q48. sSATA is 7 pins connector used for external hard disk and the DB-15 is 15 pins in 3 raws
Hello well using this to help with answers and check answers there are several questions that are the same but have different answers
True or False? DirectX is a collection of APIs related to multimedia tasks for Microsoft Windows.
True
1 True or False? Hard drives partitioned with a master boot record (MBR) cannot have an extended partition or logical drives.
True
False
false
An instructor is discussing facts about different mobile device operating software. The instructor states: “To help prevent malicious programs from infecting the device, mobile device apps are run in a sandbox that isolates them from other resources.” To which OS does this relate: iOS, Android, or both?
Both
ios ritardato