IT Essentials ( Version 7.00) (Version 8.0) – IT Essentials A+ 220-1002 Certification Practice Exam
IT Essentials ( Version 8.0) – IT Essentials A+ 220-1102 Certification Practice Exam
1. A server administrator needs to set up a new server with disk fault tolerance technology. The administrator decides to deploy RAID 0+1 technology. What is the minimum number of disks needed to deploy the disk array setting?
- 2
- 3
- 4
- 5
- 6
2. A user has detected that one of the virtual machines in a computer is infected with a virus. Which statement about the situation is likely to be true?
- The host operating system is not necessarily infected with a virus.
- The host machine operating system has a bug.
- All of the virtual machines running on the host are infected with a virus.
- The host machine antivirus program requires an update.
3. Which fire protection system would be best for a university computer/electronics lab?
- an overhead sprinkler system
- an electronic ion spreader
- a nonwater based fire extinguisher
- fire suppressing hazmat blankets and supressors
4. Why should a technician avoid opening the casing of a power supply?
- Power supplies must always be replaced, not repaired.
- Hazardous levels of electricity may be present inside the power supply.
- Power supplies are very fragile, expensive, and easy to damage.
- Only the power supply manufacturer can open the casing of a power supply.
5. What is the first step a technician should take when preparing to work on the inside of a computer?
- Remove the power supply.
- Disconnect the computer from power.
- Disconnect the computer from the network.
- Remove external devices such as a mouse.
6. What tool can be used to find and attempt to fix file structural errors on a hard disk in Windows 7?
- Format
- Sfc
- Rd
- Chkdsk
7. A customer asks for a solution to a printer problem that is beyond the knowledge level of the technician. What should the technician do?
- Try to fix the problem anyway.
- Tell the customer to call the printer manufacturer to fix the problem.
- Gather as much information as possible and escalate the problem.
- Ask the customer to call again when another technician can provide a solution to the problem.
8. Which statement that is related to running 64-bit software is correct?
- 64-bit software requires a 64-bit processor but can run on a 32-bit operating system.
- 64-bit software requires a 64-bit processor and a 64-bit operating system.
- 64-bit software can run on a 32-bit processor but requires a 64-bit operating system.
- 64-bit software can run on a 32-bit processor using a 32-bit operating system but the software performance will be slower.
9. Which statement is correct about installing a 32-bit operating system on a x64 architecture?
- The OS will always make use of all the RAM available.
- The OS will run correctly.
- The OS can address more than 128 GB of memory.
- This combination will provide better security.
10. What action should a technician take before upgrading computers from Vista to Windows 7?
- Run Vista Upgrade Analyzer.
- Run Windows 7 Upgrade Advisor.
- Uninstall all programs.
- Upgrade the video card.
11. What is a possible situation when it might be necessary to boot Windows 7 from a USB device, a CD, or a DVD?
- to disable background services
- to delete registry keys
- to partition the hard drive
- to repair the system
12. What type of partition has the ability to create volumes spanning across more than one disk?
- primary
- active
- extended
- dynamic
13. What type of file system allows the use of files larger than 5 GB and is mostly used on internal hard drives?
- FAT32
- FAT64
- NTFS
- CDFS
- exFAT
14. Which user account should be used only to perform system management and not as the account for regular use?
- guest
- standard user
- administrator
- power user
15. Which type of user account is created automatically during a Windows 8.1 installation?
- Administrator
- Guest
- Remote Desktop user
- Standard user
16. A technician is attempting to repair a Windows 7 laptop that has a missing or corrupt OS file that prevents Windows 7 from starting up. The technician reboots the laptop and accesses the WinRE via the F8 key. Which option must the technician choose in the System Recovery menu to locate and fix the missing or corrupt system files?
- Startup Repair
- System Restore
- System Image Recovery
- Windows Memory Diagnostic
17. When would the PXE option be used when repairing a PC?
- The display cannot be seen clearly.
- There is no response from the mouse or keyboard.
- The computer needs a replacement operating system.
- A newly installed application caused the system to perform erratically.
18. A user wants to extend a primary partition formatted with the NTFS file system with the unallocated space on the hard disk. What must the user do after the primary partition is extended to make it usable?
- Convert the disk type to dynamic.
- Ensure that the disk type is basic.
- Format the disk with the FAT64 file system.
- Partition the new space as a basic disk.
19. A user is viewing the Windows Disk Management utility and notices that one of the disks is marked as Foreign. What does this mean?
- This is a basic disk that has just been converted to a dynamic disk.
- This is a dynamic disk whose partition has been deleted.
- This is a dynamic disk from another PC running Windows.
- This is a disk that does not contain a valid signature.
20. What are two file attributes in the Windows environment? (Choose two.)
- details
- archive
- read-only
- security
- general
21. What are two functions of hypervisors? (Choose two.)
- to partition the hard drive to run virtual machines
- to protect the host from malware infection from the virtual machines
- to manage virtual machines
- to allocate physical system resources to virtual machines
- to share the antivirus software across the virtual machines
22. Which Windows utility can be used to schedule a regular backup for preventive maintenance?
- Windows Task Scheduler
- Windows Task Manager
- Disk Cleanup
- System Restore
23. Which statement is correct about applying firmware updates?
- Firmware updates are sometimes irreversible.
- It is possible to use the Roll Back feature to reverse the change.
- The firmware updates can be installed automatically using the Windows Service Pack utility.
- Firmware updates should not be included as part of the preventive maintenance program.
24. What is true about restore points?
- Once System Restore is used to restore a system, the change is irreversible.
- Restore points back up personal data files.
- Restore points recover corrupted or deleted data files.
- Restore points should always be created before making changes to a system.
25. A user has a computer that is infected with spyware. What should be performed before removing the spyware?
- Disable System Restore.
- Run Windows Update.
- Run a disk defragmentation.
- Create a full backup.
26. A technician is troubleshooting a Windows 7 laptop that takes significantly longer than expected when performing a file search. What is the possible cause?
- The file system is corrupt.
- The disk type is basic.
- The disk type is dynamic.
- The file permissions are not set.
- The index service is not running.
27. A user reports that a PC is losing files, not opening some files, and is performing slowly. The technician suspects problems with the hard drive. What should be done to protect the data that is on the PC and to determine the source of the problem, without risking total drive failure?
- Run the format command, then replace the hard drive.
- Run chkdsk, then run format.
- Back up all important files, then replace the hard drive.
- Back up all important files, then run chkdsk .
- Run chkdsk, then back up all important files.
28. A user logs into Active Directory on a workstation and the user home directory does not redirect to a network share on a file server. A technician suspects that the group policy setting is incorrect. Which command can the technician use to verify the group policy settings?
- rstrui
- runas
- tasklist
- gpresult
- gpupdate
29. A company has recently deployed Active Directory and now a workstation cannot connect to a network resource. A technician takes corrective action by modifying group policy settings. Which command should the technician use to make the workstation synchronize with the new settings?
- runas
- rstrui
- tasklist
- gpresult
- gpupdate
30. A wired network is undergoing several changes that could leave it vulnerable to connection by unauthorized devices while the work is in progress. Which two temporary measures would enable the authorized devices to continue to have network access but prevent unauthorized devices from connecting? (Choose two.)
- Disable DNS.
- Disable SSID broadcast.
- Disable DHCP.
- Subnet the network.
- Assign static IP addresses to the authorized devices.
31. Refer to the exhibit. In what situation would a technician use this tab?

- When the device will not be using the Internet.
- When a laptop is used both at work with DHCP and at home with a static IP address.
- When a device is behind a firewall and software is being used that needs access to a remote network.
- When the computer will be using a VPN connection and accessing the Internet while connected through the VPN.
32. On a PC that is running Windows 7 Ultimate, a user sets up a home entertainment system and creates a homegroup. The user then joins two other PCs to the workgroup, one PC running Windows 7 Starter and the other running Windows 7 Home Basic. What else must the user do in order to have the user accounts on the Windows 7 Home Basic and Windows 7 Starter PCs access the shares on the home entertainment system?
- Users have to be added to the user accounts on the home entertainment PC.
- Users on the PC that is running Windows Starter cannot join the homegroup.
- Users on the PC that is running Windows Home Basic will have to be manually added to the homegroup.
- User accounts on all three PCs have to be added to the homegroup.
- Nothing has to be done. All users accounts on all the PCs will automatically be added to the homegroup.
33. A user is reporting that a file has been shared specifically with another user on the network, but the other user opens the file and is unable to save it once edited. What is the probable cause?
- The user shared the document with Read permissions.
- The user forgot to share the parent folder.
- The file has the Archive attribute enabled.
- The file has been deleted.
34. Which character of the Cloud model provides easy monitoring, controlling, reporting, and billing for both the provider and customers?
- rapid elasticity
- resource pooling
- measured service
- broad network access
- on-demand self-service
35. A business organization is configuring security on the mobile devices that are used in the organization. The security policy states that business data on mobile devices should only ever be accessed by employees. Which mobile device security feature can be used to best ensure that business data is rendered completely inaccessible if the device is lost or stolen?
- remote lock
- remote wipe
- passcode lock
- sandbox
36. An administrative assistant tries to link a Bluetooth keyboard and mouse to a computer. The keyboard does not work, but the mouse works fine. What are two issues that could cause this situation? (Choose two.)
- Wi-Fi is turned off.
- The keyboard battery is dead.
- Bluetooth is turned off.
- The Num Lock key has been inadvertently pressed.
- The keyboard is too far from the computer.
37. What is needed from Apple and Google in order for individual programmers to develop apps for iOS and Android devices?
- SLA
- SDK
- firmware
- iOS or Android device
38. Which type of malware is disguised as a legitimate program?
- adware
- worm
- Trojan
- spyware
39. After complaints from users, a technician identifies that the college web server is running very slowly. A check of the server reveals that there are an unusually large number of TCP requests coming from multiple locations on the Internet. What is the source of the problem?
- A DDoS attack is in progress.
- The server is infected with a virus.
- There is insufficient bandwidth to connect to the server.
- There is a replay attack in progress.
40. Which security threat hides the resources that it uses from antivirus programs?
- worm
- Trojan
- rootkit
- spyware
41. A user receives an email requesting verification of the password that is used to access bank files. What type of security threat is this?
- virus
- social engineering
- phishing
- malware
42. A cleaner attempts to enter a computer lab but is denied entry by the receptionist because there is no scheduled cleaning for that day. What type of attack was just prevented?
- Trojan
- shoulder surfing
- war driving
- social engineering
- phishing
43. Which two precautions can help prevent social engineering? (Choose two.)
- Always ask for the ID of unknown persons.
- Escort all visitors.
- Keep your password securely under your keyboard.
- Do not allow any customers into the workplace.
- Always require a user name and password to be configured.
44. A company has replaced five desktop computers in the accounting and finance department with new computers. The plan is to donate the recovered computers in a fully functional state to a not-for-profit community organization. How can the company ensure that sensitive financial data cannot be accessed once the computers are donated?
- Data wipe the hard drives by using specialized software.
- Perform a high-level format on the hard drives.
- Drill holes through the hard drive platters.
- Delete all the files and directories on the hard drives.
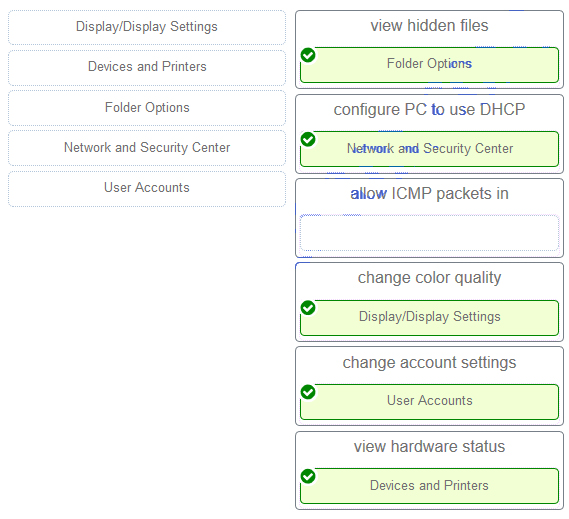
45. Match the task to the Windows Control Panel utility. (Not all options are used.)
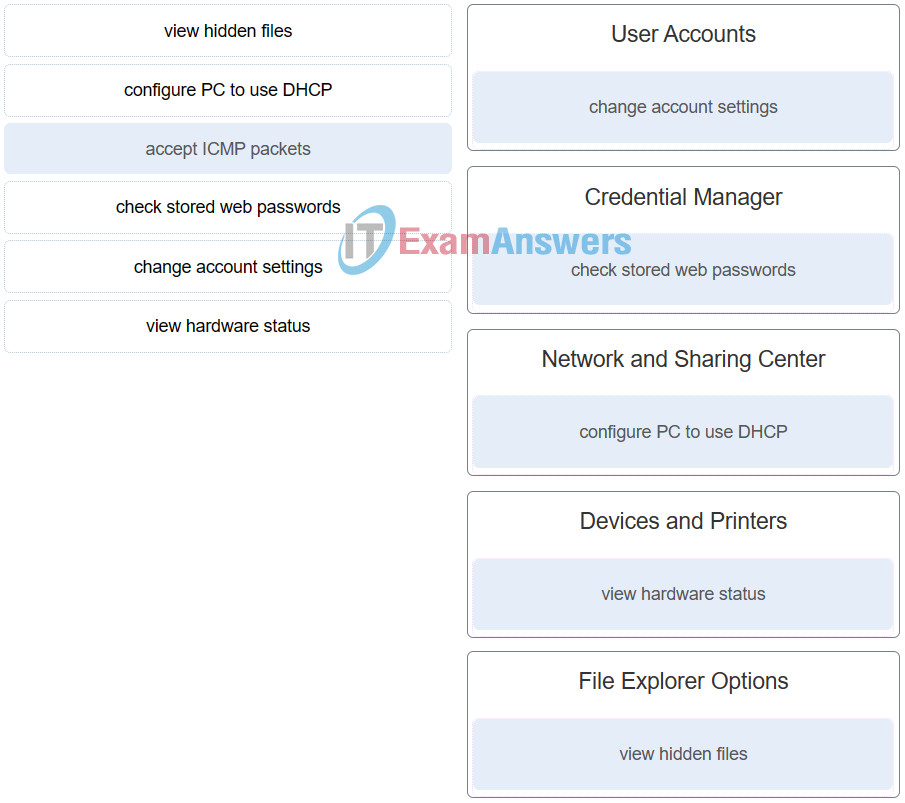
46. Match the task to the Windows 10 Control Panel utility. (Not all options are used.)
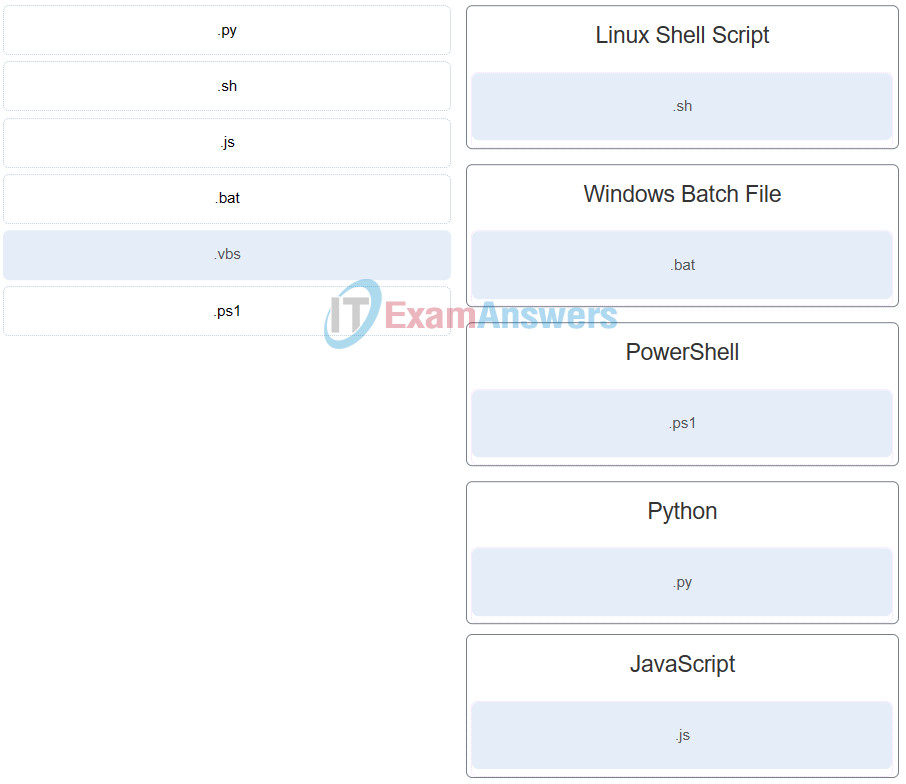
47. Match the scripting language with the script file name extension. (Not all options are used.)
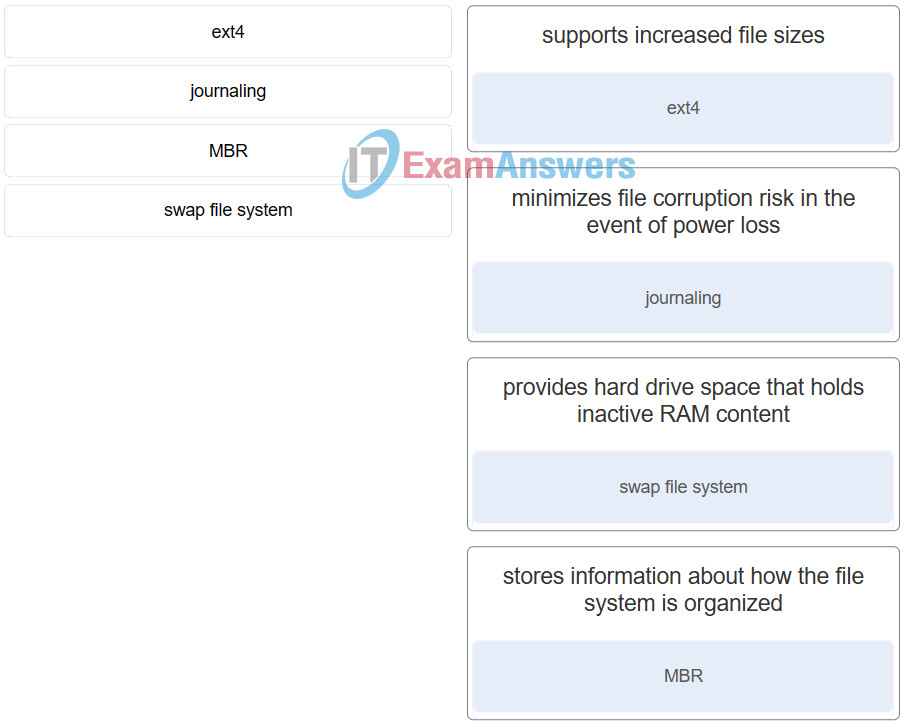
48. Match the file system term used in Linux to the function.
49. Which two data storage locations contain persistent data that can be used by computer forensics specialists? (Choose two.)
- cache
- RAM
- CPU registers
- hard disk drives
- solid state drives
50. On which two occasions is it most likely that a technician will have to perform a clean operating system installation if a backup has not been performed? (Choose two.)
- The existing operating system is corrupted.
- The computer is being moved to a different network.
- A user requires access to a new printer.
- The existing security software requires upgrading.
- A new replacement hard drive is installed in a computer.
51. Which three items are biometric security devices? (Choose three.)
- smart card
- fingerprint reader
- password
- key fob
- voice recognition
- retina scanner
52. Which two guidelines are appropriate for creating strong passwords? (Choose two.)
- Include letters, numbers, and symbols.
- Passwords should contain symbols only.
- Change the password once each year.
- Use at least eight characters.
- Use only upper case and numeric values in passwords.
53. A support desk technician is dealing with an angry customer. Which two approaches should the technician take in dealing with the customer? (Choose two.)
- Ask socially related questions to direct the customer away from the problem.
- Let the customer explain the problem without interrupting.
- Immediately transfer the customer to a higher level technician.
- Work to redirect the conversation to solving the problem.
- Reply to the customer with the same level of anger.
54. A technician working on a computer discovers what is suspected to be illegal activity. Which three pieces of information should be immediately documented? (Choose three.)
- evidence of the suspected illegal activity
- technical specifications of the computer
- why the computer was accessed by the technician
- location of the computer
- details of all past users of the computer
- duration of the suspected illegal activity
55. What two roles or tasks are associated with level two technicians? (Choose two.)
- prioritizing incoming calls according to their severity
- remotely updating drivers and software on customer computers
- escalating a trouble ticket to a higher level technician
- gathering diagnostic information from a customer computer
- gathering customer information to initiate a work order
56. A store in a shopping center uses a wireless network to provide internet access for three tablet computers. The authentication to the wireless router has been configured as 128-bit WEP. Recently the store employees notice that the internet connection is getting slower. The network administrator of the shopping center reviews the logs of the wireless router and notices many non-store devices are associated with the router. Which two actions can the network administrator do to improve the security of the wireless network access? (Choose two.)
- Use the MAC address filtering feature.
- Change WEP to WPA2 protocol.
- Ensure that the shared key is randomly generated.
- Use a 32-character long SSID.
- Change to the 152-bit WEP protocol.
57. A user is hiking in a city park. The user wants to make a call home but cannot get a reliable cellular signal. What are two possible causes for the bad cellular coverage? (Choose two.)
- The distance to the nearest Wi-Fi access point is too far.
- The user is located between coverage areas of the carrier.
- The location service is turned off.
- The Bluetooth headset is unpaired.
- There are not enough cell towers in the area.
58. A user purchases a new smartphone and is trying to use a high quality Bluetooth headset on the new device. However, the headset is not connected to the smartphone. What are three settings that the user needs to check to troubleshoot the problem? (Choose three.)
- The battery capacity on the smartphone is above 50%.
- The USB port on the headset is working.
- The authentication service is turned on.
- The Bluetooth connection is enabled on the smartphone.
- The headset is turned on.
- The pin code is entered correctly.
59. A third-party security firm is performing a security audit of a company and recommends the company utilize the Remote Desktop Protocol. What are two characteristics of the Microsoft Remote Desktop Protocol (RDP)? (Choose two.)
- RDP uses an encrypted session.
- RDP connects on TCP port 3389.
- RDP requires a Windows client.
- RDP is a command-line network virtual terminal protocol.
- RDP connects on TCP port 22.
60. A computer can successfully ping outside the local network, but cannot access any World Wide Web services. What is the most probable cause of this problem?
- Windows Firewall blocks port 23 by default.
- The computer network interface card is faulty.
- The BIOS or CMOS settings are blocking web access.
- Windows Firewall is blocking port 80.
61. Which question would be an example of an open-ended question that a technician might ask when troubleshooting a security issue?
- Have you scanned your computer recently for viruses?
- Is your security software up to date?
- Did you open any attachments from a suspicious email message?
- What symptoms are you experiencing?
62. A technician is troubleshooting a computer security issue. The computer was compromised by an attacker as a result of the user having a weak password. Which action should the technician take as a preventive measure against this type of attack happening in the future?
- Ensure the security policy is being enforced.
- Verify the physical security of all offices.
- Scan the computer with protection software.
- Check the computer for the latest OS patches and updates.
63. A user notices that some of the programs that are installed before upgrading to Windows 7 no longer function properly. What can the user do to fix this problem?
- Lower the UAC setting in the Change User Account Control settings dialog box of the User Accounts control.
- Reinstall the programs in Compatibility Mode.
- Update the driver for the graphics card.
- Change the file system to FAT16.
64. In which folder are application files for 32-bit programs typically located on a computer that is running a 64-bit edition of Windows 7?
- C:\Users
- C:\Program Files (x86)
- C:\Application Data
- C:\Program Files
65. What is required in order to connect a Wi-Fi enabled laptop to a WPA secured wireless network?
- a security encryption key
- a MAC address
- a username and password
- an updated wireless driver
66. What is a feature that can be used by an administrator to prevent unauthorized users from connecting to a wireless access point?
- MAC filtering
- WPA encryption
- software firewall
- proxy server
67. A user is configuring a wireless access point and wants to prevent any neighbors from discovering the network. What action does the user need to take?
- Configure a DNS server.
- Disable SSID broadcast.
- Enable WPA encryption.
- Configure DMZ settings.
68. Which setting must be turned on in order to share a printer in Windows 7?
- Sharing
- Share this Printer
- Windows Firewall
- File and Printer Sharing
69. A user is able to only access files required to perform a specific task. What type of security practice is being applied?
- principle of least privilege
- principle of most privilege
- principle of privileges
- principle of necessary privilege
70. A technician is troubleshooting a workstation in a domain that has been infected with a virus. What is the first step the technician should take to clean the infected workstation?
- Run the antivirus software.
- Turn off system restore.
- Disconnect the workstation from the network.
- Update the antivirus software.
71. A technician is about to install and configure a wireless network at a small branch office. What is the first security measure the technician should apply immediately upon powering up the wireless router?
- Disable the wireless network SSID broadcast.
- Configure encryption on the wireless router and the connected wireless devices.
- Change the default user-name and password of the wireless router.
- Enable MAC address filtering on the wireless router.
72. A company has a preventive maintenance policy that requires every computer have a new restore point created every six months. For computers using the Windows 7 operating system, how can a technician create the restore point?
- From the CLI enter the command restore /cn.
- Choose Start > Control Panel > Accessories > System Tools > System Restore > Create a restore point.
- Choose Start > All Programs > Accessories > System Tools > System Restore > Next.
- Right-click My Computer and then choose Properties > Restore > Create Restore Point.
73. What does virtual memory provide to an operating system?
- the creation of virtual partitions on the hard drive
- an increase in data storage
- an increase in the speed of accessing RAM
- a temporary storage of data until enough RAM is available to process it
74. Why would an administrator use Windows Remote Desktop and Windows Remote Assistant?
- to provide secure remote access to resources on another network
- to connect to a remote computer over the network to control its applications and data
- to connect to an enterprise network across an unsecured connection and act as a local client of that network
- to enable sharing of files and presentations with a group of users over the Internet
75. A technician needs to check the system settings on a remote computer to make sure it will be compatible with a new software update that will be sent out. The technician will use an administrator account to log in and start a user session on the remote PC. Which Windows tool will the technician use to accomplish this?
- Windows file sharing services
- Windows VPN remote access client
- Windows Remote Desktop
- Windows Update Assistant
76. A business traveler connects to a wireless network with open authentication. What should the traveler do to secure confidential data when connecting to the business services?
- Connect with a VPN.
- Change the network location profile to public.
- Change the Windows firewall settings.
- Manually configure an IP address, subnet mask, and default gateway.
77. What determines the level of support that a call center technician will provide to an individual customer?
- A level one technician will provide a higher level of support than a level two technician.
- Support is based on the SLA for that customer.
- An individual call center technician chooses the level of support based on the time available to assist the customer.
- All customers receive the same level of support by the call center.
78. A corporation has expanded to include multiple remote offices around the globe. Which technology should be used to allow the remote offices to communicate and share network resources privately?
- VPN
- Remote Desktop
- Remote Assistance
- administrative share
79. A user has been using a smartphone for several hours, but now the applications on the device have become unresponsive. What action should the user take?
- Restore the mobile operating system from a backup.
- Reconfigure settings.
- Restart the device.
- Reset the device to factory defaults.
80. A security audit for the human resources office finds that most employees leave confidential information on the screen when they are out of office for a short period of time. Which Windows control panel link should be used to make the monitor show a screen saver after a few minutes of inactivity and require that the user re-authenticate?
- Windows Firewall
- Device Manager
- Network and Sharing Center
- Personalization
81. Which statement describes most enterprise software licenses?
- Developers are allowed to modify and share the source code of the software.
- A company is allowed to use the software campus wide.
- A user is allowed to share the software with friends.
- A user is allowed to install the software on only one computer.
82. In a Linux operating system, which component interprets user commands and forwards them to the OS?
- shell
- CLI
- application program
- kernel
83. In Linux and OS X, which CLI command can be used to display the name of the current directory?
- pwd
- ps
- chmod
- sudo
84. When installing application software on a Windows 7 workstation, the user sees an error message indicating that the installation is unsuccessful. What should the user try next?
- Run the chkdsk /R command.
- Restart the installation process with the services.msc utility.
- Use the bootrec /fixmbr command from the System Recovery option.
- Run the installation under compatibility mode.
85. A virus has infected several computers in a small office. It is determined that the virus was spread by a USB drive that was shared by users. What can be done to prevent this problem?
- Destroy the USB drive.
- Set the antivirus software to scan removable media.
- Activate Windows Firewall.
- Change the passwords on the computers.
86. Which wireless encryption method is the least secure?
- TKIP
- AES
- WEP
- WPA
87. A customer is explaining a problem with a computer to a technician. The technician recognizes the problem prior to the customer finishing the explanation. What should the technician do?
- Interrupt the customer and let the customer know that the technician knows what the problem is.
- Ask the customer to repeat the problem so that the technician can document it and verify all the facts.
- Wait politely for the customer to finish explaining the problem.
- Start working on the PC while listening to the customer at the same time.
88. The Windows PC of a user was shutdown abruptly due to a sudden loss of power. The user then reports that the workstation has lost several files. A help desk technician suspects that part of the hard disk might be damaged. Which Windows utility can the technician use to scan the hard disk and make repairs if necessary?
- Disk Cleanup
- Disk Defragmenter
- Chkdsk
- System File Check
89. A user calls the help desk and reports that the workstation, when powering up, displays error messages about an invalid system disk or invalid boot disk. When a technician comes to the office, the user mentions that the workstation was working well the day before. The technician checks the workstation and makes sure that the cable is firmly connected between the hard drive and the motherboard. What is another likely cause of the problem?
- The boot service fails to start.
- The MBR/GPT is corrupted.
- Some of the operating system files may be corrupted.
- A recently installed device driver is incompatible with the boot.
90. A user calls the help desk and reports that invalid system disk or invalid boot disk error messages display on the workstation when it is powered on. When a technician comes to the office, the user mentions that the workstation was working well the day before. The technician suspects that the MBR is corrupted. Which process can the technician use to check and repair the MBR?
- Run the sfc command.
- Run the bootrec command.
- Boot the workstation in Safe Mode.
- Run the chkdsk command.
91. A student tells a teacher that many junk emails are appearing on a new personal laptop. What is a possible cause of the problem?
- The laptop needs to be updated to the latest OS version.
- The student has spent too much time surfing the web.
- The school email server is not functioning properly.
- The new laptop does not have antivirus or anti-spam software installed.
92. A sales representative is driving to visit several customer sites in the city. The representative notices that the smartphone is draining battery power more quickly than normal. What is a possible cause of the issue?
- The battery charger is malfunctioning.
- The smartphone was not fully charged.
- There are not enough Wi-Fi access points in the area.
- The smartphone is roaming among cell towers.
93. A user attended the wedding of a coworker and took pictures using a smartphone. The user receives phone calls from several coworkers the next day and is shocked to learn that these pictures now appear on multiple web pages. What is a possible cause for the incident?
- The smartphone is set to automatically upload files to the coworker group folder.
- The passcode for the smartphone has been hacked.
- The smartphone sent the pictures to the websites by mistake.
- The user account for the cloud service has been hacked.
94. A student is jogging in a city park. The student has an app on the smartphone that tracks exercise activities. The student receives a notification that a new email has been received and stops to read the email message. However, the email app is slow to respond. What is a reason for the slowness of the app to open?
- The smartphone OS is frozen.
- The smartphone is unable to decrypt the email message.
- The exercise tracking app is using the GPS service.
- The email app requires a large amount of RAM.
95. A user reports that the PC displays a warning message. The warning message indicates that the PC is infected by a virus. A technician comes with a USB drive that contains a malware detection and removal program. What should the technician do before running the program?
- Disconnect the hard drive.
- Change the BIOS setting to make the USB drive bootable.
- Boot the PC in Safe Mode.
- Make a backup of the data.
96. A user reports that a Windows 10 PC displays a warning message. The warning message indicates that the PC is infected by malware. A technician comes to the office and makes sure that the PC is disconnected from all wired and wireless networks. What should the technician do next to further investigate the incident?
- Boot the PC in Safe Mode.
- Save log files to removable media.
- Disconnect the hard drive.
- Move the malware to the Quarantined Items folder.
97. All Windows 10 computers in a small advertising company are configured with the System Restore service. One of the PCs was infected by malware when an employee was doing research on the internet. The IT administrator scans the system and deletes the malware from the Quarantined Items folder. What should the administrator do next to complete the remediation process?
- Delete all restore points.
- Disable the System Restore service.
- Create a restore point.
- Restore the system from a backup.
98. A mobile user downloads and installs an app. Once the app is installed, the Android mobile device is frozen. What is a cause for the issue?
- The mobile OS needs to be replaced.
- Additional apps are needed for the app to function correctly.
- The app is not compatible with the device.
- The app needs an update.
99. When a user tries to run a program, a missing or corrupt DLL message is displayed. What is a solution to fix the problem?
- Use the msconfig command to adjust the startup settings for the program.
- Run Windows Startup Repair.
- Run sfc /scannow in Safe Mode.
- Reinstall the correct drivers.
100. A programmer needs to automate processes and tasks in an operating system. Which tool would the programmer use to build a script file?
- a text editor
- a compiler
- a comparison operator
- an executable automation tool
101. A company has a guest wireless network available for visitors while on the company premises. A technician has noted that unauthorized users are connecting to this wireless network from outside the premises. Which action can be taken to reduce unauthorized connections to the guest wireless network while enabling visitors to still connect quickly and easily without assistance while on the company premises?
- Enable MAC address filtering.
- Configure WPA encryption.
- Reduce the radio power level.
- Disable SSID broadcast.
102. What is an example of a web application using multifactor authentication?
- A user logs on to an online shopping website and uses a credit card to make an order.
- Teleworkers are required to establish a VPN connection to the company before logging into the company internal web server.
- A user attends a large conference and tries to access Google Gmail at the conference site. The Gmail service sends a verification code to the smartphone of the user.
- A network administrator needs to swipe a card in order to access the corporate server room.
103. A user calls the help desk with the following situation. “I added a new PC to my LAN. I can ping other devices on my LAN but not any remote devices.” What advice should the help desk agent give to the caller?
- Set the file permissions to read and execute.
- If using Windows, set the idle timeout and screen lock.
- Check the IP address configuration on the new PC, because the default gateway may be incorrect.
- Create a virtual machine with an OS that supports the application.
104. Which statement describes the active partition?
- It is a physical section of a hard disk. It can contain an operating system to boot the system and cannot be subdivided.
- It is used to boot an operating system by default.
- It is often used to organize data storage by subdividing it into as many as 23 logical sections.
- It is a section of an extended partition on an MBR. It can be used to separate information for administrative purposes.
105. A technician has just purchased a new Windows 10 PC and wants to transfer selected files, folders, profiles, and applications from the old Windows PC. What tool or utility would be the best choice for the user?
- Upgrade Assistant
- User State Migration Tool
- Windows Task Manager
- PCmover Express
106. A user wants to copy a group of files from one Windows directory to another. What is the best Windows command to select to do the job?
- regsrv32
- sfc
- DISM
- robocopy
- tasklist
107. A technician wants to create customized system image files that will be installed on computers in the network. Which administrative command-line tool or command can be used to address this?
- msinfo32
- mstsc
- dism
- diskpart
108. A user finds that when launching a downloaded Windows update file, Windows Update fails. What are two possible causes for this? (Choose two.)
- The downloaded update file is corrupted.
- A previous update that is required for the current update is not installed.
- The Windows Firewall is turned off.
- The virus definitions are out of date.
- The hard disk is failing.
109. Which key or key sequence pressed during the boot process will allow a user to start a Windows PC using the last known good configuration?
- F8
- F12
- Windows key
- Alt-Z
- F1
110. A technician notices that an application is not responding to commands and that the computer seems to respond slowly when applications are opened. What is the best administrative tool to force the release of system resources from the unresponsive application?
- Add or Remove Programs
- Task Manager
- Event Viewer
- System Restore
111. A technician has successfully removed malware from a PC and finds that when the system is rebooted error messages are displayed about missing and corrupt system files. What utility can the technician use to replace or fix any corrupted system files?
- Regedit
- ASR
- Fixboot
- Fixmbr
- SFC
112. Which disk management tool scans the critical files of an operating system and replaces the corrupt files?
- Optimize Drives
- Disk Cleanup
- Chkdsk
- Scandisk
- System File Checker
113. A computer technician is notified by a user that there are no automated backups being created on an Apple computer. What is the first thing the technician should check?
- if space is available on the local drive
- whether Remote Disc is enabled
- whether Time Machine is turned on
- correct date and time configuration
114. A user reports that an application crashed. The technician tries a few other applications on the PC and finds that none of them start normally or that they crash soon after being launched. What is a possible cause of the problem?
- The applications need updates from the software vendors.
- The Windows Firewall is turned off for the Private networks profile.
- The PC is infected by a virus.
- The hard disk is failing.
115. A user calls the help desk and reports that a security alert appears on the screen about a malware attempt to enter the PC. What should the technician instruct the user to do?
- Stop wired or wireless network connection immediately.
- Close the email client software.
- Turn on the Windows Firewall.
- Scan the PC to remove any malware.
116. A user is shopping in a mall and gets a notification that a new email is received on the smartphone. The user is wondering how the email message was delivered because the data usage feature is turned off. The user notices that the smartphone is connected to the coffee shop inside the mall using Wi-Fi. What caused this connection?
- The Wi-Fi access point in the coffee shop uses WPA2 Personal settings.
- The smartphone is set to automatically connect to available Wi-Fi networks.
- The service carrier of the smartphone provides Wi-Fi connections inside the mall.
- The Wi-Fi access point in the coffee shop uses the same channel as the user smartphone uses.
117. A programmer is building a script that will test a condition of either true or false. Which data type would the programmer use?
- float
- Bool
- int
- char
118. A user has a computer that is infected with spyware. What should be performed after the spyware is completely cleaned?
- Run Windows Update.
- Run a disk defragmentation.
- Delete system restore files.
- Create a full backup.
119. A technician calls the help desk with the following situation. “I am trying to save a file to my RAID drive but my system cannot find it.” What advice should the help desk agent give to the caller?
- Check the permissions for this file.
- Set the file permissions to read and execute.
- Check the RAID controller, because it may need to be replaced.
- Create a virtual machine with an OS that supports the application.
120. Which statement describes a primary partition?
- It is a section of an extended partition on an MBR. It can be used to separate information for administrative purposes.
- It is a physical section of a hard disk. It can contain an operating system to boot the system and cannot be subdivided.
- It is used to boot an operating system by default.
- It is often used to organize data storage by subdividing it into as many as 23 logical sections.
121. A support technician wants to upgrade a system to Windows 10 but is unsure whether the hardware and software on the existing system are compatible. What tool or utility would be the best choice for the user?
- Windows Easy Transfer
- Get Windows 10 app
- Cortana Virtual Assistant
- PCmover Express
122. A user is deleting old files and wants to see all files in the current directory. What is the best Windows command to select to do the job?
- dir
- exit
- bootrec
- ipconfig
- diskpart
123. A technician is troubleshooting a Windows 10 PC that has a .dll file for an application that has not been registered. Which administrative command-line tool or command can be used to address this?
- regsvr32
- net user
- type
- gpupdate
124. An IT technician in a service company has provided extensive remote IT support with product deployment for a customer. After the completion of the contract, a complaint is filed against the IT technician for not following company policy by sending unsolicited emails about services and products that are not related to the contract. What two things should the IT support technician have done differently? (Choose two.)
- The IT technician should have added the customer to a chain letter with many recipients instead.
- The IT technician should have used encryption to hide the purpose of the emails.
- The IT technician should have researched the company policy about personal communication with customers on company time.
- The IT technician should have asked the customer if the customer was interested in receiving information regarding other new services and products.
- The IT technician should have requested permission from a supervisor to send the customer emails.
125. A user finds that when launching a downloaded Windows update file, Windows Update fails. What are two possible causes for this? (Choose two.)
- The downloaded update file is corrupted.
- The virus definitions are out of date.
- The Windows Firewall is turned off.
- A previous update that is required for the current update is not installed.
- The hard disk is failing.
126. A server administrator needs to remotely configure a legacy network device. The legacy network device only supports a plain-text session connection. Which remote access tool should be used?
- SSH client
- Windows Remote Assistance client
- Telnet client
- Windows Remote Desktop client
127. Which statement describes a logical drive?
- It takes the first 512 bytes on the disk and contains the boot loader, an executable program that allows a user to choose from multiple operating systems.
- It is a standard for the layout of the hard drive partition table using globally unique identifiers. All partitions are primary.
- It is a section of an extended partition on an MBR. It can be used to separate information for administrative purposes.
- It is a physical section of a hard disk. It can contain an operating system to boot the system and cannot be subdivided.
128. A technician wants to open a remote desktop utility to connect to a remote computer on a Windows 10 PC. Which administrative command-line tool or command can be used to address this?
- diskpart
- mstsc
- msinfo32
- chkdsk
129. A technician needs to capture the company user accounts, files, operating system settings, and application settings for migration into the new Windows 10 installation. What tool or utility would be the best choice for the user?
- User State Migration Tool
- Upgrade Assistant
- Windows Easy Transfer
- WinLoad
130. Which technology allows a mobile device to automatically rotate what is being displayed on the screen as the physical orientation of the device is changed?
- Time Machine
- accelerometer
- screen calibration
- geocaching
131. After questioning a user about the problems being experienced with a PC operating system, the support technician suspects that a recent service pack installation has failed. Which step of the troubleshooting process has the technician just concluded?
- Test the theory to determine the cause of the problem.
- Establish a plan of action to resolve the problem.
- Establish a theory of probable cause.
- Document findings, actions, and outcomes.
132. A new computer workstation has been installed in a small office. The user of the workstation can print a document using a network printer on the LAN, but cannot access the Internet. What is a possible cause of the problem?
- The TCP/IP stack is not functional.
- The gateway IP address is misconfigured.
- The DHCP server IP address is misconfigured.
- The workstation is configured with a static IP address.
133. A customer is explaining a problem with a computer to a technician. The technician recognizes the problem prior to the customer finishing the explanation. What should the technician do?
- Interrupt the customer and let the customer know that the technician knows what the problem is.
- Start working on the PC while listening to the customer at the same time.
- Ask the customer to repeat the problem so that the technician can document it and verify all the facts.
- Wait politely for the customer to finish explaining the problem.
134. A technician needs to permanently destroy data on some drives before disposing of them. What is the best way to do this?
- Shatter the drive platters with a hammer.
- Overwrite the drives
- Partition the hard drives.
- Perform a full format.
135. A user notices errors for some Windows operations and suspects that some system files might be corrupted. The user wants to scan and verify the integrity of all system files and replace corrupted files with correct versions. What is the best Windows command to select to do the job?
- DISM
- tasklist
- sfc
- shutdown
- path
136. An analyst is running Windows 7 on the PC and is planning to migrate to Windows 8.1. The analyst wants help migrating the personal files and settings into the newer version. What tool or utility would be the best choice for the user?
- PCmover Express
- Windows Easy Transfer
- Application manager
- User State Migration Tool
137. Which statement describes a recovery partition?
- It is a section of the disk, that is inaccessible to the user, containing an image that can be used to restore the computer to its original configuration.
- It is often used to organize data storage by subdividing it into as many as 23 logical sections.
- It is used to boot an operating system by default.
- It is a physical section of a hard disk. It can contain an operating system to boot the system and cannot be subdivided.
138. An administrator calls the help desk with the following situation. “I need to make changes to a file. I can open it but I am unable to make changes.” What advice should the help desk agent give to the caller?
- Create a virtual machine with an OS that supports the application.
- If using Windows, set the idle timeout and screen lock.
- Set the file permissions to read and execute.
- Check the permissions for this file.
139. What three technologies enable virtual assistants to interact with end users via voice commands? (Choose three.)
- VoIP
- multi-threading
- machine learning
- voice recognition
- data fault tolerance
- artificial intelligence
140. How can a user prevent specific applications from accessing a Windows computer over a network?
- Enable MAC address filtering.
- Disable automatic IP address assignment.
- Block specific TCP or UDP ports in Windows Firewall.
- Change default usernames and passwords.
141. What is the most commonly used method to close an application that appears to be frozen on an OS X-based computer?
- Use Force Quit.
- Use Task Manager.
- Access the Status menu.
- Access the Notification Center.
142. In the context of a Linux operating system, which command can be used to display the syntax and parameters for a specific command?
- cat
- man
- grep
- crontab
143. A system administrator issues the apt-get command on a laptop that has Ubuntu installed. What is the function provided by the command?
- to display or configure a wireless NIC
- to install, configure, and remove packages
- to list the applications currently running in the system
- to allow a user to login as another user or to become a super user
144. After consulting the manufacturer manuals, a technician applies a series of recommended solutions that resolve a problem with a workstation computer. What is the next step in the troubleshooting process that the technician should perform?
- Verify the solution and confirm full system functionality.
- Document the findings, actions, and outcomes.
- Test the theory of probable cause.
- Determine the next steps to resolve the problem.
145. When a user tries to run a program a missing or corrupt DLL message is displayed. What are two possible solutions to this problem? (Choose two.)
- Reinstall the correct drivers.
- Use the msconfig command to adjust the startup settings for the program.
- Run Windows Startup Repair.
- Run sfc/scannow in Safe Mode.
- Register the DLL file using the regsvr32 command.
146. A support desk technician is asking a customer a series of questions about a problem connecting to the network. Which step of the troubleshooting process is the technician applying?
- Identify the problem.
- Establish a theory of probable cause.
- Establish a plan of action to resolve the problem.
- Test the theory to determine cause.
147. A computer technician has successfully returned a laptop to full operation and verified system functionality. Actions the technician performed included modifying the registry and applying patches to the operating systems. What is the next step in the troubleshooting process that the technician should do?
- Reboot the computer.
- Document the solution.
- Consult manufacturer manuals and repair logs.
- Re-attach and test all peripherals.
148. A user reports that a computer is unable to print on an inkjet printer. The technician has determined that there is no paper in the paper bin. What is the next step in the troubleshooting process?
- Establish a plan of action.
- Determine the exact cause.
- Verify system functionality.
- Document the findings.
149. A Windows PC that was formatted with the NTFS file system displays a missing or corrupt DLL error message when a certain program is run. What is the cause of this?
- The DLL file was not installed with the program.
- The NTFS file system does not support DLLs.
- The OS must be 64 bit in order to support the DLL.
- The DLL file was not registered during installation of the program.
150. What are two possible symptoms of MBR/GPT corruption in a workstation? (Choose two.)
- The workstation continually restarts.
- The workstation displays an “Invalid Boot Disk” error.
- The workstation displays a black or blue screen of death.
- The workstation displays a “BOOTMGR is missing” error.
- The workstation displays an “Inaccessible Boot Device” error.
151. What is a result when the DHCP servers are not operational in a network?
- Workstations are assigned with the IP address 0.0.0.0.
- Workstations are assigned with the IP address 127.0.0.1.
- Workstations are assigned with IP addresses in the 10.0.0.0/8 network.
- Workstations are assigned with IP addresses in the 169.254.0.0/16 network.
152. A user reports that during the boot up process of a Windows 7 workstation, the message “MBR has been changed or modified” appears. What is the most probable cause of the message?
- A virus has damaged the MBR.
- A virus has damaged the boot sector.
- A boot sector virus has changed the MBR.
- A virus damaged the Windows system files.
153. A user has completed a project and wants to erase or delete one or more files from a Windows directory. What is the best Windows command to select to do the job?
- bootrec
- del
- history
- diskpart
- ipconfig
154. A user calls the help desk with the following situation. “My Windows operating system is slowing down more and more each day and it now takes ages to load an application.” What advice should the help desk agent give to the caller?
- Set the file permissions to read and execute.
- Create a virtual machine with an OS that supports the application.
- If using Windows, set the idle timeout and screen lock.
- Use the Disk Defragmenter to remedy the problem.
155. A user wants to display the contents of a text file in a command interpreter. Which administrative command-line tool or command can be used to address this?
- type
- net user
- robocopy
- gpupdate
156. A manager wants to install Windows 10 directly onto a computer and needs help with the setup process. What tool or utility would be the best choice for the user?
- Upgrade Assistant
- User State Migration Tool
- Windows Easy Transfer
- Windows Boot Manager
157. A user cannot reach a familiar web server and wants to verify connectivity by sending echo-request messages to the server in the hope that the server will respond to confirm connectivity. What is the best Windows command to select to do the job?
- sfc
- DISM
- recover
- tasklist
- ping
158. Which statement describes the globally unique identifier (GUID) partition table (GPT)?
- It is a section of an extended partition on an MBR. It can be used to separate information for administrative purposes.
- It is a standard for the layout of the hard drive partition table using globally unique identifiers. All partitions are primary.
- It is often used to organize data storage by subdividing it into as many as 23 logical sections.
- It is used to boot an operating system by default.
159. A user is trying to repair, prepare, and fix Windows images and the recovery image within an installation of the operating system. What is the best Windows command to select to do the job?
- path
- format
- DISM
- bootrec
- diskpart
160. A technician calls the help desk with the following situation. “I installed a new sound card but it is not working correctly.” What advice should the help desk agent give to the caller?
- Set the file permissions to read and execute.
- Use Device Manager to look for any driver issues or problems.
- Check the permissions for this file.
- Create a virtual machine with an OS that supports the application.
161. Which statement describes formatting?
- It is a process to create a file system in a partition or volume for file storage.
- It is often used to organize data storage by subdividing it into as many as 23 logical sections.
- It is a section of an extended partition on an MBR. It can be used to separate information for administrative purposes.
- It is a section of the disk, that is inaccessible to the user, containing an image that can be used to restore the computer to its original configuration.
162. Which two statements are true regarding GPT partitions? (Choose two.)
- They are commonly used in computers with UEFI firmware.
- They are commonly used in computers with BIOS based firmware.
- They store a backup of the partition table.
- They have a maximum partition size of 2TB.
- They store the partition and boot data in one place.
163. A technician wants to open up a separate command interpreter with commands for working with disk partitions. Which administrative command-line tool or command can be used to address this?
- chkdsk
- mstsc
- diskpart
- msinfo32
164. Which statement describes a dynamic disk?
- It is a standard for the layout of the hard drive partition table using globally unique identifiers. All partitions are primary.
- It is often used to organize data storage by subdividing it into as many as 23 logical sections.
- It is a type of disk with the ability to create volumes that span across more than one disk even if the unallocated space is noncontiguous.
- It takes the first 512 bytes on the disk and contains the boot loader, an executable program that allows a user to choose from multiple operating systems.
165. An administrator calls the help desk with the following situation. “I need to use an application that is not supported by Windows on my PC.” What advice should the help desk agent give to the caller?
- Create a virtual machine with an OS that supports the application.
- Check the permissions for this file.
- If using Windows, set the idle timeout and screen lock.
- Set the file permissions to read and execute.
166. A user wants to check a file system for errors, including errors with physical media. Which administrative command-line tool or command can be used to address this?
- chkdsk
- type
- net user
- robocopy
167. An administrator calls the help desk with the following situation. “An application on my computer is not responding and it is slowing down other applications. What should I do?” What advice should the help desk agent give to the caller?
- Create a virtual machine with an OS that supports the application.
- Check the permissions for this file.
- Use Task Manager to release system resources from the unresponsive application.
- Set the file permissions to read and execute.
168. A user suspects issues with the MBR and is trying to repair it. What is the best Windows command to select to do the job?
- net user
- format
- diskpart
- bootrec
- ipconfig
169. A technician wants to copy files and entire directory trees from one volume to another volume on a Windows 10 PC. Which administrative command-line tool or command can be used to address this?
- type
- gpupdate
- net user
- robocopy
170. A user wants to display the Group Policy settings that are in effect for a currently logged in user. Which administrative command-line tool or command can be used to address this?
- msinfo32
- mstsc
- diskpart
- gpresult
171. A user calls the help desk with the following situation. “I was updating my operating system software and the power went out before it finished. My PC terminates before the boot process is complete.” What advice should the help desk agent give to the caller?
- Set the file permissions to read and execute.
- Press F8 during the boot process to use the last known good configuration.
- If using Windows, set the idle timeout and screen lock.
- Create a virtual machine with an OS that supports the application.
172. A user wants to copy a directory with all files and a subdirectory in it from one Windows directory to another. What is the best Windows command to select to do the job?
- ipconfig
- net use
- diskpart
- xcopy
- bootrec
173. What does the activation of the Offline Files feature in the Sync Center do in Windows 10?
- It sets up manual synchronization.
- It sets up synchronization to occur automatically.
- It sets up a sync partnership with the networked file location.
- It sets up a local file location that will store the files to be synchronized.
174. What is the default file system used during a fresh installation of Windows 10?
- HPFS
- NTFS
- FAT16
- FAT32
175. A user visits a trusted website. The website sends the user a link via email to the default browser window. When the user clicks on the link, a message appears stating that there is a problem with the website’s security certificate. Why has this occurred?
- the browser has identified it as a malware
- the CRLs of the browser have not been updated
- the antivirus has flagged this as a known virus
- the pop-up windows on the browser have been disabled
176. Match the Windows 10 drive management condition with the respective description.

177. What are two advantages of SD-WAN technologies over traditional WAN? (Choose two.)
- network consistency and reliability
- independently configured devices instead of centrally
- required to activate platform as a service (PaaS)
- network monitoring and management is not required
- integrated and automated network security features
178. A technician has just purchased a new Windows 10 PC and wants to transfer selected files, folders, profiles, and applications from the old Windows PC. What tool or utility does Microsoft recommend to do this?
- Upgrade Assistant
- PCmover Express
- User State Migration Tool
- Windows Task Manager
179. A technician wishes to start Windows 10 in safe mode to troubleshoot it. What key or key combination would begin this process?
- ctrl + F6 and restart
- hold the Shift key and select the Restart option in the Power menu
- recycle power and hold down the del key
- recycle power and hold down the F8 key
180. A user signs up on an application that requires multifactor authentication. The user chooses to register the phone number for the authentication system. Which three items must the user provide in order to authenticate? (Choose three.)
- answer to secret question
- IP address
- account username
- OTP
- email address
- password
181. Which two statements are true regarding 64-bit processor architecture? (Choose two.)
- It has additional registers for 64-bit address space.
- It only supports 64-bit operating systems.
- It supports a maximum of 4GB RAM memory.
- It supports both 32-bit and 64-bit operating systems.
- It has only 64-bit registers.
182. Which process in Windows 10 is responsible for assigning system resources and driver installation?
- winlogon
- PnP
- services
- explorer
183. What is the purpose of Windows 10 ReadyBoost?
- It speeds up the Windows 10 start time.
- It enables the quadruple channels on a 64-bit processor.
- It enables the UEFI bios to boot faster.
- It enables Windows to treat an external flash device, such as a USB drive, as a hard drive cache.
184. A technician calls the help desk with the following situation. “I added a new PC to my LAN. I can ping other devices on my LAN but not any remote devices.” What advice should the help desk agent give to the caller?
- Check the IP address configuration on the new PC, because the default gateway may be incorrect.
- Create a virtual machine with an OS that supports the application.
- Set the file permissions to read and execute.
- If using Windows, set the idle timeout and screen lock.
185. Where are 32-bit program files located in a 64-bit version of Windows 10 Pro?
- c:\Program files
- c:\Program files (x86)
- c:\users
- c:\Windows\system32
186. A technician wishes to use the reset option to repair a Windows 10 installation and chooses the option that will retain the user’s personal files. Which statement is true based on using this option?
- All user files and applications will be restored together with the complete reinstallation of Windows 10.
- All user files and applications will be deleted, and a complete reinstallation of Windows 10 will occur.
- Only corrupt files of the Windows 10 installation will be replaced and repaired.
- Only user files will be restored together with the complete reinstallation of Windows 10.
187. A user notices that the PC behaves a bit differently from the organization group policies. The user believes that the group policy settings may have been applied incorrectly and wants to verify the settings. What is the best Windows command to select to do the job?
- sfc
- cls
- gpresult
- DISM
- tasklist

if I study with this site do I get 100% on the exam?
I have only 1 attempt left to take this exam
i have the exam tomorrow
Thank you
new question
What does the activation of the Offline Files feature in the Sync Center do in Windows 10?
A user wants to copy a directory with all files and a subdirectory in it from one Windows directory to another. What is the best Windows command to select to do the job?
Added, thanks for sharing!
A user calls the help desk with the following situation. “I was updating my operating system software and the power went out before it finished. My PC terminates before the boot process is complete.” What advice should the help desk agent give to the caller?
added, thanks for sharing
An administrator calls the help desk with the following situation. “I need to use an application that is not supported by Windows on my PC.” What advice should the help desk agent give to the caller?
A user wants to check a file system for errors, including errors with physical media. Which administrative command-line tool or command can be used to address this?
*chkdsk
An administrator calls the help desk with the following situation. “An application on my computer is not responding and it is slowing down other applications. What should I do?” What advice should the help desk agent give to the caller?
A user suspects issues with the MBR and is trying to repair it. What is the best Windows command to select to do the job?
Which statement describes a dynamic disk?
A technician wants to copy files and entire directory trees from one volume to another volume on a Windows 10 PC. Which administrative command-line tool or command can be used to address this?
A user has been using a smartphone for several hours, but now the applications on the device have become unresponsive. What action should the user take?
Thanks for your sharing!
A technician wants to open up a separate command interpreter with commands for working with disk partitions. Which administrative command-line tool or command can be used to address this?
IT Essential course final exam/ Where can I find answers for oral examination ? And Final certification exam/
Which statement describes formatting?
Thanks for your sharing!!
A technician calls the help desk with the following situation. “I installed a new sound card but it is not working correctly.” What advice should the help desk agent give to the caller?
Added, thanks for sharing
Which statement describes a dynamic disk?
A user is trying to repair, prepare, and fix Windows images and the recovery image within an installation of the operating system. What is the best Windows command to select to do the job?
Correct answer: DISM
Thanks for your sharing!
A user cannot reach a familiar web server and wants to verify connectivity by sending echo-request messages to the server in the hope that the server will respond to confirm connectivity. What is the best Windows command to select to do the job?
Added all, many thanks for your sharing! :)
Which statement describes the globally unique identifier (GUID) partition table (GPT)?
A user cannot reach a familiar web server and wants to verify connectivity by sending echo-request messages to the server in the hope that the server will respond to confirm connectivity. What is the best Windows command to select to do the job?
NEW QUESTION
A manager wants to install Windows 10 directly onto a computer and needs help with the setup process. What tool or utility would be the best choice for the user?
Get Windows 10 app
Windows Boot Manager
Upgrade Assistant
PCmover Express
Added, thanks for your sharing!
A user wants to display the contents of a text file in a command interpreter. Which administrative command-line tool or command can be used to address this?
Added, thanks for sharing!
A user calls the help desk with the following situation. “My Windows operating system is slowing down more and more each day and it now takes ages to load an application.” What advice should the help desk agent give to the caller?
Thanks for sharing!
A user has completed a project and wants to erase or delete one or more files from a Windows directory. What is the best Windows command to select to do the job?
A technician needs to permanently destroy data on some drives before disposing of them. What is the best way to do this?
****Shatter the drive platters with a hammer is the real response
Added! Many thanks
A user notices errors for some Windows operations and suspects that some system files might be corrupted. The user wants to scan and verify the integrity of all system files and replace corrupted files with correct versions. What is the best Windows command to select to do the job?
An analyst is running Windows 7 on the PC and is planning to migrate to Windows 8.1. The analyst wants help migrating the personal files and settings into the newer version. What tool or utility would be the best choice for the user?
Which statement describes a recovery partition?
An administrator calls the help desk with the following situation. “I need to make changes to a file. I can open it but I am unable to make changes.” What advice should the help desk agent give to the caller?
A technician needs to permanently destroy data on some drives before disposing of them. What is the best way to do this?
correct answer is shatter the drive plates with a hammer
Wiping the drives (multiple writes of zeros, or magnetically wipe), and then mechanical shredding (destruction) of the hard drives. Opinion: if you break first, data is still on the hard drives.
https://www.whitecanyon.com/articles/the-risks-of-shredding-drives-internally
ANOTHER 1
A technician needs to capture the company user accounts, files, operating system settings, and application settings for migration into the new Windows 10 installation. What tool or utility would be the best choice for the user
user state migration
NEW QUESTION
A user notices that the PC behaves a bit differently from the organization group policies. The user believes that the group policy settings may have been applied incorrectly and wants to verify the settings. What is the best Windows command to select to do the job
I think true answer is: gpedit.msc
Can you share answers multiple choose? Thank you!
Need to update the policy. Look for command gdupdate;
Reference:
https://docs.microsoft.com/en-us/windows-server/administration/windows-commands/gpupdate
Ok
NEW QUESTION
An administrator calls the help desk with the following situation. “An application on my computer is not responding and it is slowing down other applications. What should I do?” What advice should the help desk agent give to the caller
can you post the choice of answers for this question please
Can somone repost the question diagrams for 31, 46, 47 and 48? They’re blank.