Check answers here:
Modules 24 – 25: Protocols and Log Files Group Exam (Answers)
Quiz-summary
0 of 30 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
Information
Modules 24 - 25: Protocols and Log Files Group Exam - Test online
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 30 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- Answered
- Review
-
Question 1 of 30
1. Question
1 pointsWhich ICMP message type should be stopped inbound?Correct
Incorrect
-
Question 2 of 30
2. Question
1 pointsHow can IMAP be a security threat to a company?Correct
Incorrect
-
Question 3 of 30
3. Question
1 pointsWhich two technologies are primarily used on peer-to-peer networks? (Choose two.)Correct
Incorrect
-
Question 4 of 30
4. Question
1 pointsWhich protocol is exploited by cybercriminals who create malicious iFrames?Correct
Incorrect
-
Question 5 of 30
5. Question
1 pointsWhich method is used by some malware to transfer files from infected hosts to a threat actor host?Correct
Incorrect
-
Question 6 of 30
6. Question
1 pointsWhy does HTTPS technology add complexity to network security monitoring?Correct
Incorrect
-
Question 7 of 30
7. Question
1 pointsWhich approach is intended to prevent exploits that target syslog?Correct
Incorrect
-
Question 8 of 30
8. Question
1 pointsWhich type of attack is carried out by threat actors against a network to determine which IP addresses, protocols, and ports are allowed by ACLs?Correct
Incorrect
-
Question 9 of 30
9. Question
1 pointsWhich two application layer protocols manage the exchange of messages between a client with a web browser and a remote web server? (Choose two.)Correct
Incorrect
-
Question 10 of 30
10. Question
1 pointsWhat is Tor?Correct
Incorrect
-
Question 11 of 30
11. Question
1 pointsWhich protocol is a name resolution protocol often used by malware to communicate with command-and-control (CnC) servers?Correct
Incorrect
-
Question 12 of 30
12. Question
1 pointsWhich technique is necessary to ensure a private transfer of data using a VPN?Correct
Incorrect
-
Question 13 of 30
13. Question
1 pointsWhich technology would be used to create the server logs generated by network devices and reviewed by an entry level network person who works the night shift at a data center?Correct
Incorrect
-
Question 14 of 30
14. Question
1 pointsWhich function is provided by the Sguil application?Correct
Incorrect
-
Question 15 of 30
15. Question
1 pointsWhich statement describes a Cisco Web Security Appliance (WSA)?Correct
Incorrect
-
Question 16 of 30
16. Question
1 pointsWhich statement describes session data in security logs?Correct
Incorrect
-
Question 17 of 30
17. Question
1 pointsWhich two options are network security monitoring approaches that use advanced analytic techniques to analyze network telemetry data? (Choose two.)Correct
Incorrect
-
Question 18 of 30
18. Question
1 pointsHow does a web proxy device provide data loss prevention (DLP) for an enterprise?Correct
Incorrect
-
Question 19 of 30
19. Question
1 pointsWhich information can be provided by the Cisco NetFlow utility?Correct
Incorrect
-
Question 20 of 30
20. Question
1 pointsWhich statement describes statistical data in network security monitoring processes?Correct
Incorrect
-
Question 21 of 30
21. Question
1 pointsMatch the SIEM function with the description.Correct
Incorrect
-
Question 22 of 30
22. Question
1 pointsWhich two tools have a GUI interface and can be used to view and analyze full packet captures? (Choose two.)Correct
Incorrect
-
Question 23 of 30
23. Question
1 pointsWhich Windows log contains information about installations of software, including Windows updates?Correct
Incorrect
-
Question 24 of 30
24. Question
1 pointsMatch the Windows host log to the messages contained in it. (Not all options are used.)Correct
Incorrect
-
Question 25 of 30
25. Question
1 pointsWhich Cisco appliance can be used to filter network traffic contents to report and deny traffic based on the web server reputation?Correct
Incorrect
-
Question 26 of 30
26. Question
1 pointsWhich technique would a threat actor use to disguise traces of an ongoing exploit?Correct
Incorrect
-
Question 27 of 30
27. Question
1 pointsA system administrator runs a file scan utility on a Windows PC and notices a file lsass.exe in the Program Files directory. What should the administrator do?Correct
Incorrect
-
Question 28 of 30
28. Question
1 pointsRefer to the exhibit. A network administrator is viewing some output on the Netflow collector. What can be determined from the output of the traffic flow shown?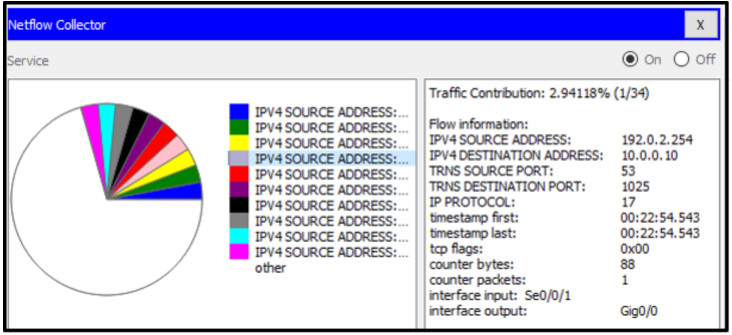 Correct
Correct
Incorrect
-
Question 29 of 30
29. Question
1 pointsIn a Cisco AVC system, in which module is NetFlow deployed?Correct
Incorrect
-
Question 30 of 30
30. Question
1 pointsWhat does it indicate if the timestamp in the HEADER section of a syslog message is preceded by a period or asterisk symbol?Correct
Incorrect
