IT Essentials (Version 7.00) – IT Essentials 7.0 Chapter 11 exam Answers
IT Essentials v7.0:
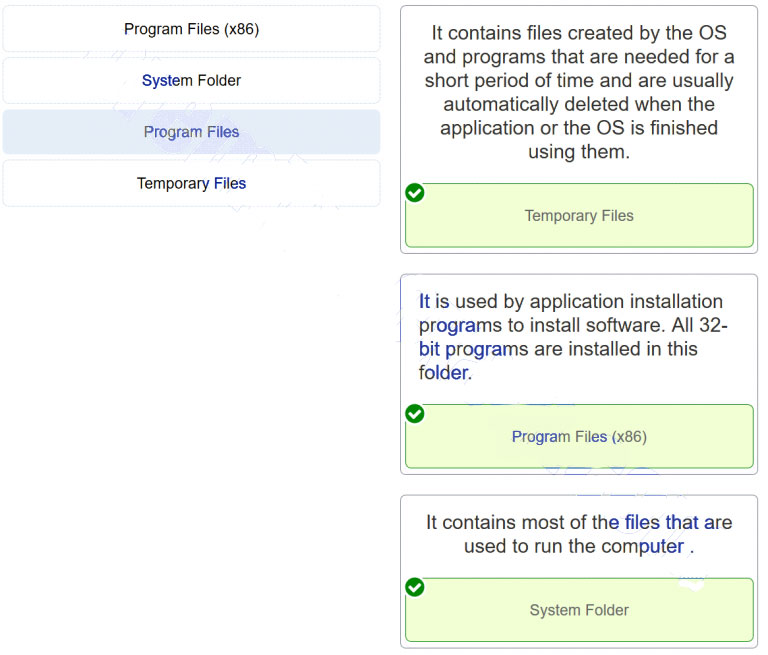
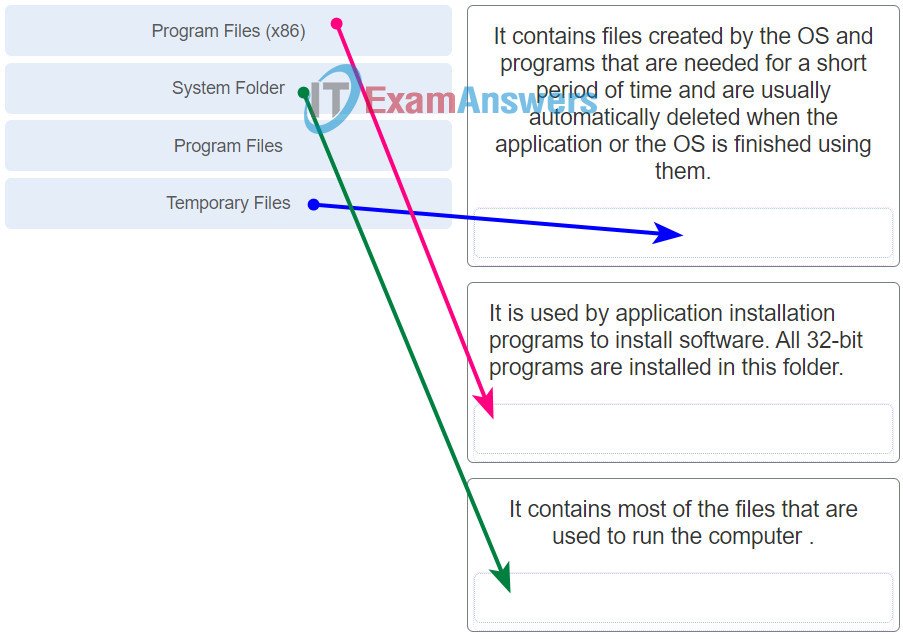
1. Match the folders in a 32-bit Windows 10 PC to their description. (Not all options are used.)
2. Match the categories in the Windows 10 Control Panel to the function.

IT Essentials ( Version 7.0) – IT Essentials 8.0 Chapter 11 exam Q4
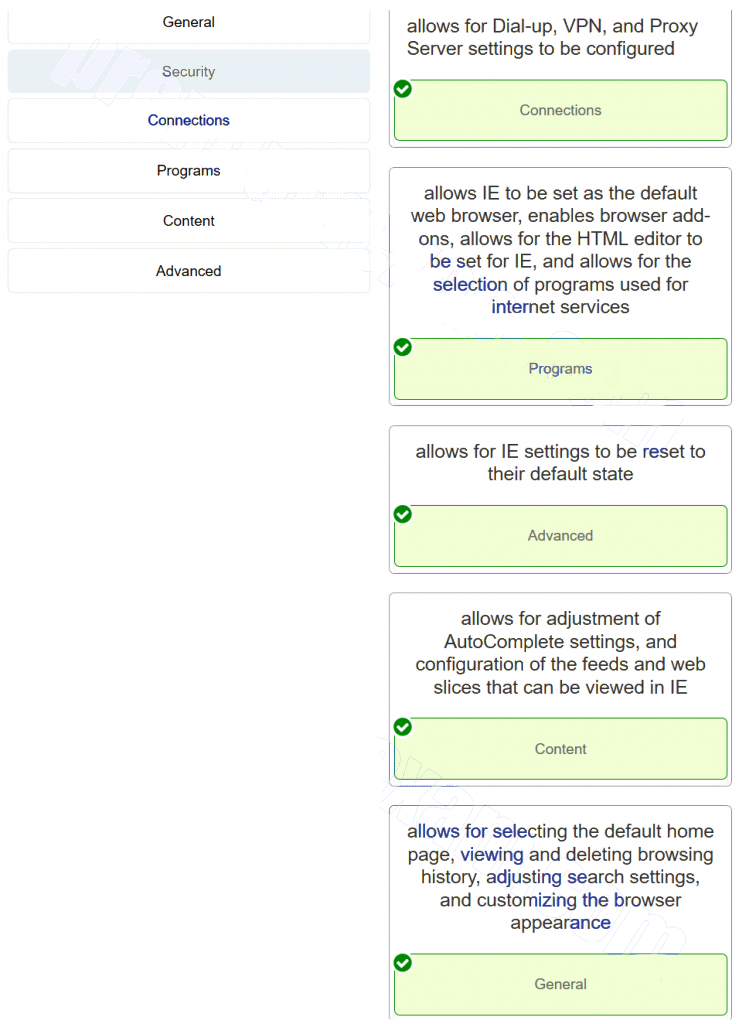
3. Match the Internet Options to the descriptions used to configure Microsoft Internet Explorer. (Not all options are used.)
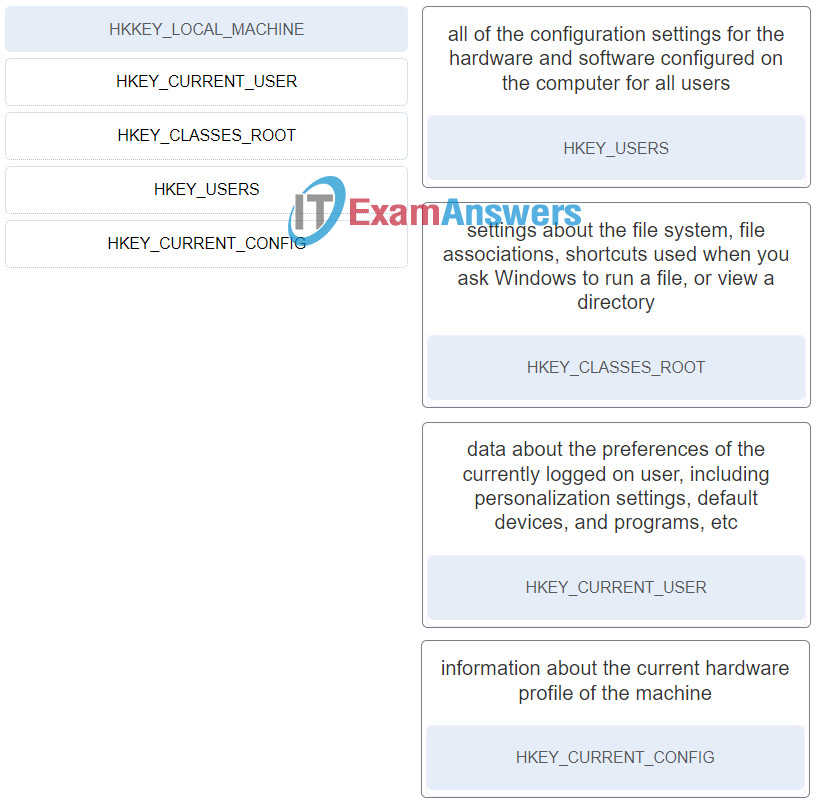
4. Match the Windows 10 Registry key with its description. (Not all options are used.)
IT Essentials ( Version 7.0) – IT Essentials 7.0 Chapter 11 exam Q3
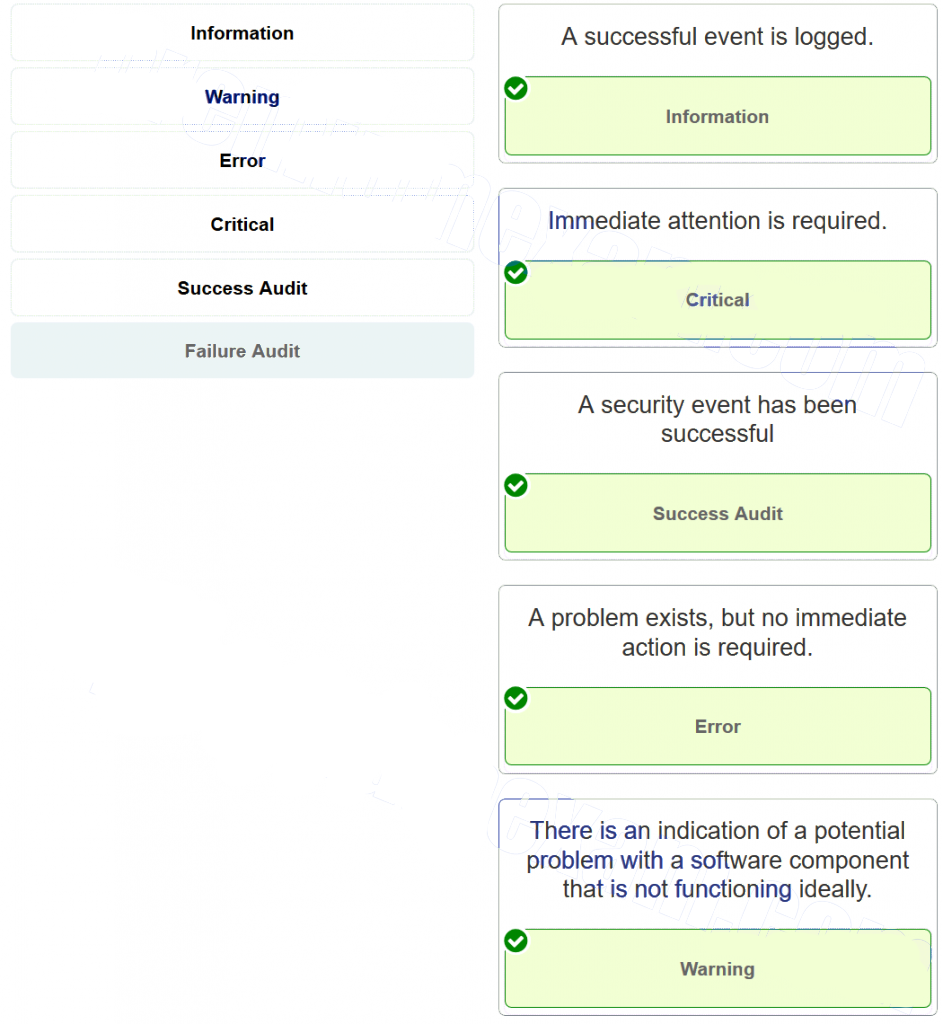
5. Match the message types in the Windows 10 Event Viewer with their description. (Not all options are used.)
6. Which three levels of RAID are supported by Windows 10 Pro? (Choose three.)
- 0
- 1
- 3
- 4
- 5
7. A technician is troubleshooting a PC. The display shows an “Invalid Boot Disk” error after the POST. What is a probable cause?
- The MBR is corrupted.
- A process is using most of the CPU resources.
- The date and time have been changed in the BIOS and do not reflect the correct time and date.
- The PC does not have a floppy drive or the floppy drive is broken.
- The PC has a BIOS password.
8. A technician notices that a program that is listed in the registry of a Windows computer is not found on that computer. What is a possible solution to the problem?
- Run fdisk /mbr from the command prompt.
- Reinstall the application. Then, run the uninstall program.
- Restore the boot.ini file from the installation media.
- Restore the ntdetect.com file from the installation media.
9. Which question is an open ended question that could be used when helping a customer troubleshoot a Windows problem?
- Can you boot the operating system?
- Have you changed your password recently?
- Do you get a login prompt when the computer boots?
- What programs have you installed recently?
10. A technician has been asked to reinstall the OS on a computer that has a corrupted operating system. The technician inserts the installation media in the optical drive. What would be the most likely action the technician should perform next?
- Change the boot sequence in the BIOS.
- Change the BIOS password.
- Flash the BIOS for a firmware upgrade.
- Change clock speeds in the BIOS.
11. A technician has successfully removed malware from a PC and finds that when the system is rebooted error messages are displayed about missing and corrupt system files. What utility can the technician use to replace or fix any corrupted system files?
- ASR
- Fixboot
- Fixmbr
- Regedit
- SFC
12. A technician is troubleshooting a Windows 7 laptop that takes significantly longer than expected when performing a file search. What is the possible cause?
- The file system is corrupt.
- The disk type is basic.
- The disk type is dynamic.
- The file permissions are not set.
- The index service is not running.
13. A Windows 8 computer locks up with a stop error during startup and then automatically reboots. The automatic restart setting is making it difficult to see any error messages. What can be done so that the error messages can be viewed?
- Use the System Recovery options to restart the operating system.
- Use the Command Prompt option to research the stop error messages.
- View the error messages and recover the system using the System Image Recovery tool.
- Access the Advanced Startup options menu before the OS loads to disable the auto restart function.
14. A user reports that a PC is losing files, not opening some files, and is performing slowly. The technician suspects problems with the hard drive. What should be done to protect the data that is on the PC and to determine the source of the problem, without risking total drive failure?
- Run the format command, then replace the hard drive.
- Run chkdsk, then run format.
- Back up all important files, then replace the hard drive.
- Back up all important files, then run chkdsk.
- Run chkdsk, then back up all important files.
15. A company has recently deployed Active Directory and now a workstation cannot connect to a network resource. A technician takes corrective action by modifying group policy settings. Which command should the technician use to make the workstation synchronize with the new settings?
- runas
- rstrui
- tasklist
- gpresult
- gpupdate
16. A user is reporting that a file has been shared specifically with another user on the network, but the other user opens the file and is unable to save it once edited. What is the probable cause?
- The user shared the document with Read permissions.
- The user forgot to share the parent folder.
- The file has the Archive attribute enabled.
- The file has been deleted.
17. A user calls the help desk and reports that the workstation, when powering up, displays error messages about an invalid system disk or invalid boot disk. When a technician comes to the office, the user mentions that the workstation was working well the day before. The technician checks the workstation and makes sure that the cable is firmly connected between the hard drive and the motherboard. What is another likely cause of the problem?
- The MBR/GPT is corrupted.
- The boot service fails to start.
- Some of the operating system files may be corrupted.
- A recently installed device driver is incompatible with the boot.
18. A technician is attempting to diagnose and rectify a common boot problem on a Windows 10 installation. Which Windows 10 advanced recovery option should the technician use?
- System Restore
- System Image Recovery
- Reset
- Startup Repair
19. A user of a Windows 10 PC wants to automatically sync the user profile across various Windows 10 devices that the user owns. How can the user accomplish this?
- Have the user sign into all devices with the Microsoft account of the user.
- Ensure that the user is in the proper group so that the group policy will be applied.
- Use gpupdate to propagate the group policy to other devices.
- Make sure that OneDrive file sync is disabled.
20. A technician is troubleshooting a Windows 10 PC with a frozen Internet Explorer window. Which command can the technician run, as an administrator at a command prompt, to terminate the Internet Explorer process that has hung?
- taskkill /fi iexplorer.exe
- taskkill /pid iexplorer.exe
- taskkill /f /im iexplorer.exe
- taskkill /f /im explorer.exe
21. A technician wishes to create a dynamic volume on a Windows 10 PC that has two physical hard drives. The technician wants to achieve maximum write performance with data fault tolerance. What type of dynamic volume should be created to achieve this?
- RAID 5 volume
- RAID 1 volume
- RAID 2 volume
- RAID 6 volume
22. A user wishes to view an ISO disk image file on a Windows 10 Pro PC. How can this be done?
- Convert a Dynamic disk to a Basic disk and open the ISO image.
- Use the built-in Unzip utility to open the ISO file and extract the contents into a directory.
- Use File Explorer to locate the ISO file and mount the file using the Disk Image tools.
- Copy the ISO image to a Dynamic disk and double click it.
23. Which file sharing mechanism is included with Microsoft Windows 10 to provide simple file sharing via Wi-Fi and Bluetooth?
- AirDrop
- Nearby Sharing
- Homegroup
- NFC
- Workgroup
24. Which feature is included with both macOS and Apple iOS to establish a Wi-Fi direct connection between devices to simplify file transfer?
- Nearby sharing
- Workgroup
- Homegroup
- AirDrop
25. A computer technician is attempting to modify settings in the Network Adapter > Properties > Advanced tab > Speed and Duplex . What is a possible effect (or impact) if this option is configured incorrectly?
- The network connection may experience issues.
- The NIC cannot be set to wake up with network activity.
- The NIC cannot be set to shutdown while the computer is idle.
- The NIC loses VLAN support.
26. A company is implementing a wireless network and using wireless devices as part of the corporate environment. Which two server-based authentication methods should the company consider in the wireless network design? (Choose two.)
- AES
- RADIUS
- TACACS
- TKIP
- WPA2-PSK
27. A user tries to install an application on a Windows 10 Pro PC but it fails. The user tries to uninstall the application but it fails to uninstall. What option can be used to address this issue without loss of data or applications?
- Use Restore Point.
- Use Advanced Start-up.
- Uninstall and reinstall the device using device manager.
- Restart the Windows Update services.
29. A technician is troubleshooting a Windows 10 PC that will not do any windows updates automatically or manually. What option can be used to address this issue without loss of data or applications?
- Delete all the files in C:\Windows\SoftwareDistribution folder and restart the PC.
- Restore using Sysprep.
- Uninstall and reinstall the device using device manager.
- Restart the Windows Update services.
30. A Windows 10 computer suddenly started experiencing network connectivity issues after the latest Windows updates completed a week ago. What option can be used to address this issue without loss of data or applications?
- Reset this PC.
- Restore using Sysprep.
- Restart the Windows Update services.
- Uninstall and reinstall the device using device manager.
31. A client installed a new driver for a device three weeks ago; however, this driver is causing the system to freeze occasionally and the client wishes to revert back to the old driver. What option can be used to address this issue without loss of data or applications?
- Reset this PC.
- Restart the Windows Update services.
- Restore using Sysprep.
- Uninstall and reinstall the device using device manager.
32. A technician is working on a Windows 10 PC that keeps freezing occasionally after a driver update. System restore has been turned off. What option can be used to address this issue without loss of data or applications?
- Reset this PC.
- Uninstall and reinstall the device using device manager.
- Restore using Sysprep.
- Restart the Windows Update services.
33. A technician is working on a Windows 10 PC that keeps freezing occasionally after a driver update. System restore has been turned off. What option can be used to address this issue without loss of data or applications?
- Reset this PC.
- Go back to the initial Windows build.
- Restart the Windows Update services.
- Uninstall and reinstall the device using device manager.
34. A technician is working on a Windows 10 PC that keeps freezing occasionally after a driver update. System restore has been turned off. What option can be used to address this issue without loss of data or applications?
- Reset this PC.
- Go back to the initial Windows build.
- Use Advanced Start-up.
- Perform a repair of Windows using Installation media.
35. A technician is troubleshooting a Windows 10 PC that will not do any windows updates automatically or manually. What option can be used to address this issue without loss of data or applications?
- Delete all the files in C:\Windows\SoftwareDistribution folder and restart the PC.
- Use Advanced Start-up.
- Go back to the initial Windows build.
- Perform a repair of Windows using Installation media.
36. A user is trying to create a new Windows directory for storing files related to a new project. What is the best Windows command to select to do the job?
- md
- ping
- tracert
- nslookup
- help
37. A user has to shutdown several remote computers one at a time. What is the best Windows command to select to do the job?
- shutdown
- nslookup
- ping
- netstat
- recover
38. A user has an important file that is used in many projects and needs to move that file to a different Windows directory while maintaining it in the current location. What is the best Windows command to select to do the job?
- copy
- bootrec
- ipconfig
- diskpart
- history
39. A user needs to display a list of current processes running on a local or a remote computer. What is the best Windows command to select to do the job?
- tasklist
- diskpart
- bootrec
- format
- path
40. A user has just installed a new hard drive into the PC and needs to prepare it to store Windows files. What is the best Windows command to select to do the job?
- format
- bootrec
- ipconfig
- diskpart
- net user
41. A user is experiencing issues with system startup and with failing to open some files. The user wants to determine the source of any hard drive issues. What is the best Windows command to select to do the job?
- chkdsk
- bootrec
- ipconfig
- diskpart
- cls
42. A user suspects someone has hacked into the PC and wants to verify activity on the PC by displaying all active TCP connections to the PC. What is the best Windows command to select to do the job?
- netstat
- diskpart
- bootrec
- format
- regsrv32
43. A user is looking for a file but can not find it in the Document folder. The user wants to move to the Download directory to check there. What is the best Windows command to select to do the job?
- cd
- bootrec
- ipconfig
- diskpart
- help
44. A user is troubleshooting a connectivity issue from the PC to a web server and wants to see a list of the traffic stops between the PC and the web server. What is the best Windows command to select to do the job?
- tracert
- diskpart
- bootrec
- tasklist
- recover
45. A user is reorganizing files within different directories to accommodate new projects and needs to relocate a file from one Windows directory to another one. What is the best Windows command to select to do the job?
- move
- tasklist
- DISM
- sfc
- history
46. Match the folders in a 64-bit Windows 10 PC to their description. (Not all options are used.)
47. A user notes that the username and password are automatically populated in the Microsoft Edge browser when logging into a secure site. When the user tries to log into the same site using Google Chrome, the username and password do not save automatically. Why is this occurring?
- The certificate for that site has not been authenticated.
- The Google Chrome browser is corrupt.
- Google Chrome does not support that secure site.
- Google Chrome does not automatically save web credentials.
48. Where are 32-bit program files located in a 64-bit version of Windows 10 Pro?
- c:\Program files (x86)
- c:\Program files
- c:\users
- c:\Windows\system32
49. What is the purpose of Windows 10 ReadyBoost?
- It enables the quadruple channels on a 64-bit processor.
- It enables Windows to treat an external flash device, such as a USB drive, as a hard drive cache.
- It enables the UEFI bios to boot faster.
- It speeds up the Windows 10 start time
50. Which statement is true regarding libraries in Windows 10?
- Libraries allow Windows 10 to index files faster.
- Libraries allow Windows 10 to link mutiple different directories.
- Libraries allow Windows 10 to enforce the EFS file system.
- Libraries allow Windows 10 to support file names longer than 20 characters
IT Essentials v6.0:
1. Which factor affects the speed of an inkjet printer?
- the desired quality of the image
- the size of printer power supply
- the quality of the paper
- the cost of the inkjet cartridges
2. What are two cables that are used to connect a computer to a printer? (Choose two.)
- serial
- FireWire
- PS/2
- HDMI
- eSATA
3. What type of connection would be used to connect a printer directly to the network?
- Ethernet
- serial
- USB
- Firewire
4. What is a characteristic of thermal inkjet nozzles?
- The heat creates a bubble of steam in the chamber.
- Heat is applied to the ink reservoir of each nozzle.
- The vibration of the crystal controls the flow of ink.
- A charge is applied to the printhead.
5. In laser printing, what is the name of the process of applying toner to the latent image on the drum?
- developing
- charging
- transferring
- fusing
6. What mechanism is used in a laser printer to permanently fuse the toner to the paper?
- heat
- electrical charge
- pressure
- light
7. Which statement describes a printer driver?
- It is the interface in Windows that identifies a unique printer attached to the workstation.
- It is cache inside a printer that stores documents to be printed in a queue.
- It is software that converts a document into the format that a printer can understand.
- It is the configuration code that is sent to a printer to identify the operating system of the workstation.
8. A technician is installing a printer that will be directly connected to a computer. Why does the technician not connect the printer initially during the installation process?
- The printer needs to be configured first.
- The OS of the workstation needs to be updated first.
- The printer driver might need to be installed first before the printer is connected.
- The Microsoft download site needs to be searched first for the printer driver.
9. A Windows 7 computer has several printers configured in the Control Panel Devices and Printers window. Which printer will the computer choose to be the first option for printing?
- the printer that is set as the default printer
- the software-based printer that is used to create PDF files
- the software-based printer that is used to create XPS files
- a manual selection, which is always needed
10. What is a characteristic of global and per-document options in print settings?
- Per-document options override global options.
- Global options take precedence over per-document options.
- It is not possible to configure per-document options.
- It is not possible to configure global options.
11. A user discovers that an inkjet color printer is printing different colors from those that are shown on the screen. What can be done to solve this problem?
- Calibrate the printer.
- Adjust the printer spool.
- Replace the fuser.
- Replace the drum.
12. The users on a LAN are reporting that computers respond slowly whenever high resolution photographs are being printed on the color laser printer. What would be the cause of this problem?
- The printer does not have enough memory to buffer an entire photograph.
- The printer is not configured for duplex printing.
- The paper is not adequate for photograph printing.
- The printer is not configured for the proper paper orientation.
13. What is the purpose of the Additional Drivers button in the Sharing tab of the Printer Properties?
- to add additional drivers for other operating systems
- to add additional drivers for other printers in the network
- to add additional drivers for duplex printing
- to add additional drivers for other printers connected to the computer
14. What are two methods to connect to a printer wirelessly? (Choose two.)
- IEEE 802.11 standards
- Bluetooth
- WiMax
- satellite
- microwave
15. In Windows 8, what must be configured to enable one user to share a USB-connected printer with another user on the same network?
- Windows firewall
- Windows Defender
- IEEE 802.11
- File and printer sharing
- virtualization option in BIOS
16. Which type of print server provides the most functions and capabilities?
- a dedicated PC print server
- a computer-shared print server
- a hardware print server
- a print server that is implemented in software
17. What are two functions of a print server? (Choose two.)
- provide print resources to all connected client computers
- store print jobs in a queue until the printer is ready
- ensure that the connected client computers have up-to-date printer drivers
- store backups of documents sent to the printer
- provide uninterrupted power to the printer
18. Which action supports an effective printer preventive maintenance program?
- Reset the printer page counters if available.
- Replace laser printer toner at set predetermined time intervals.
- Clean inkjet print heads when they stop working.
- Disconnect the printer from the power source when it is not in use.
19. How can the life of a thermal printer be extended?
- Clean the heating element regularly with isopropyl alcohol.
- Clean the inside of the printer with a vacuum cleaner with a HEPA filter.
- Keep the paper dry in a low humidity environment.
- Wipe the outside of the printer with a damp cloth.
20. After applying a solution to a printer problem, a technician restarts the printer and prints a test page. Which step of the troubleshooting process is the technician applying?
- verifying the solution and system functionality
- identifying the problem
- testing a theory to determine the cause of the problem
- documenting findings, actions, and outcomes
21. A technician recorded that a new fuser roller unit was installed in a laser printer to solve a printing problem. Which step in the troubleshooting process did the technician just perform?
- documenting findings, actions, and outcomes
- verifying the solution and system functionality
- identifying the problem
- testing a theory to determine the cause of the problem
22. What are two probable causes for printer paper jams?
- high humidity
- the wrong type of paper
- a defective print cartridge
- misaligned print heads
- an incorrect print driver
23. What corrective action should be taken if a printer is printing faded images?
- secure loose printer cables
- update the print driver
- clean the printer
- replace the toner cartridge
24. What corrective action would a technician take in response to a print spooler error?
- reboot the printer
- restart the print spooler
- update the printer driver
- clean the printer
25. What would cause an inkjet printer to fail to print any pages?
- The printer software is set to toner save.
- The printer ribbon is worn out.
- The ink cartridge is empty.
- The printer is loaded with a paper type other than photo paper.
26. A user tells a technician that the printer does not respond to attempts to print a document. The technician attempts to print a document and the printer does not output any pages. The technician notices that the printer LCD display is blank and unlit. What is most likely the problem?
- The screen contrast is too low.
- The printer is not turned on.
- The printer is out of ink.
- The print head is clogged.
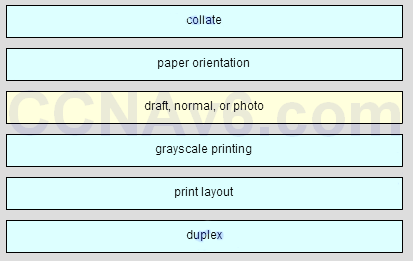
27. Match the common printer configuration options to the correct descriptions. (Not all options are used.)
Question
Answer
Older Version
28. Which two actions should a technician take if illegal content, such as child pornography, is discovered on the hard drive of a customer computer? (Choose two.)
- Contact a first responder.
- Confront the customer immediately.
- Shut down the computer until authorities arrive.
- Document as much information as possible.
- Remove and destroy the hard drive.
29. What is the definition of cyber law?
- a single law defining criminal acts that are committed online
- a contract that defines expectations between and organization and IT service vendors for an agreed upon level of support
- the process of collecting and analyzing data from computer systems, networks, wireless communications, and storage devices
- the collection of international, country, and local laws that affect computer security professionals
30. When performing computer forensics, what can be prevented with a properly and carefully documented chain of custody?
- identity theft
- copying of copyrighted materials
- evidence tampering
- cyber crime
31. During the process of troubleshooting, a technician gains access to customer private information. What is expected that the technician do with this information?
- Send this information to the manager of the customer.
- Back up the information just in case the customer needs it some day.
- Document all information in a log file.
- Send this information to the technician manager.
- Keep it confidential.

32. During the troubleshooting of software that is installed on a computer system, a level one technician requires help from a level two technician. The file shown in the exhibit must be sent to the level two technician. How should the level one technician deliver this file?
- Send the file as it is to the level two technician.
- Deliver the file in printed format only.
- Replace all passwords in the file with before emailing the file and then supply the passwords by secure means, if required.
- This file should not be shared with the level two technician.
33. What are two sections that are usually included in an SLA? (Choose two.)
- supported equipment and software
- home contact information of the technician
- service provider part suppliers
- time of service availability
- contact information of other clients
34. Which two rules pertain to the general daily activities of employees in a call center environment? (Choose two.)
- The technician should contact the customer if the technician is going to be late for a follow-up appointment.
- The technician should adjust the work chair to a height that is high enough so that wrists angle downwards toward the keyboard.
- The technician should be sure to treat all customers equally.
- If a customer complains about another technician, the technician who is taking the call should agree with opinion of the customer.
- If a technician takes a call from a customer the technician does not like, the technician should pass the call to another technician.
35. Which statement describes a best practice related to time management?
- The technician can take the call of another technician, even without permission to do so.
- The technician should give better service to a customer for whom the technician feels more sympathy.
- The technician should take the easier calls first, regardless of the urgency.
- The technician should make sure to call the customer back as close to the callback time as possible.
36. Which two statements are correct about level one and level two technicians? (Choose two.)
- Level two technicians usually respond to the “down calls” as they may be able to resolve them faster.
- Level one technicians usually work on the problems that require opening up the computer case.
- Level two technicians are often referred to as “incident screeners,” and level one technicians are often referred to as “product specialists.”
- Level two technicians are usually more knowledgeable about technology than the level one technicians are.
- Level two technicians prepare a work order and escalate it to a level one technician if a problem cannot be resolved within ten minutes.
37. What should a level two technician do immediately after receiving an escalated work order from a level one technician?
- Call the customer back to ask any additional questions and resolve the problem.
- Call the level one technician and ask questions about the problem.
- Document suggestions to solve the problem in the work order and return it to the level one technician.
- Send the work order to a level three technician and ask for support.
38. A customer calls to report a computer problem. Which two actions can the technician take to establish a good rapport with the customer? (Choose two.)
- Use technical terms to determine the level of knowledge the customer possesses.
- Allow the customer to speak without interruption.
- Personalize the call by periodically asking questions unrelated to the computer problem.
- Refer to the customer by name whenever possible.
- Ask only closed-ended questions.
39. What is the correct way to conduct a telephone call to troubleshoot a computer problem?
- Always gather information from the customer and escalate the problem.
- Ask personal questions to get better acquainted with the customer.
- Explain each step to help the customer understand the troubleshooting process.
- Maintain professional behavior at all times.
40. A technician receives a call from a customer who is too talkative. How should the technician handle the call?
- Politely step in and gain control of the call by asking the customer social questions.
- Allow the customer to speak without interruption and then try to use closed-ended questions to gather data.
- Use open-ended questions and repeat all the information back to the customer to politely show that unnecessary information is being given.
- Talk over the customer and quickly gather the necessary information to be of help.
41. What are two examples of displaying professional communication skills while talking to a customer? (Choose two.)
- focusing on what you cannot do to give customers an idea of the magnitude of the problem
- clarifying what customers say after they have finished their explanations
- interrupting customers with a question to gather more information
- asking customers to paraphrase their explanations
- the use of active listening, with occasional interjections such as “I see” or “I understand”
42. What are three pieces of information a level one technician should gather from a customer? (Choose three.)
- details of any recent changes to the computer
- description of the problem
- output from diagnostic software
- output from a remote connection to the customer computer
- current CMOS settings
- contact information
43. Which situation would require that a support desk call be given the highest priority?
- A couple of computers have operating system errors.
- The company cannot operate because of a system failure.
- Some computers cannot log in to the network.
- Two users are requesting an application enhancement.
- A user is requesting a RAM memory upgrade.
44. Which two data storage locations contain persistent data that can be used by computer forensics specialists? (Choose two.)
- solid state drives
- CPU registers
- RAM
- hard disk drives
- cache
45. In a computer forensics investigation, which type of data is considered volatile data and can be lost if power is removed from the computer?
- data in transit between RAM and the CPU
- data stored on an internal drive
- data stored on an external drive
- data stored on magnetic disks
46. What customer support procedure would likely cause an upset customer to become more upset?
- Ask the customer to do obvious or unnecessary steps.
- Reiterate that you want to solve the problem.
- Follow a step-by-step approach to solving the problem.
- Apologize for the wait time if there has been no wait time.
47. What name is given to a certain set of general rules that apply to written communication over the Internet?
- flame wars
- online interactions
- Internet slang
- netiquette
48. When performing computer forensics what is required to prove a chain of custody?
- an admission of guilt
- collected evidence
- proper documentation procedures
- expert testimony
49. What is a reason to escalate a problem from a level one technician to a level two technician?
- when the equipment needs to be rebooted
- when the screen resolution of a customer PC needs to be adjusted
- when drivers, applications, or operating systems need to be installed
- when a peripheral device needs to be replaced

A user notes that the username and password are automatically populated in the Microsoft Edge browser when logging into a secure site. When the user tries to log into the same site using Google Chrome, the username and password do not save automatically. Why is this occurring?
The certificate for that site has not been authenticated.
The Google Chrome browser is corrupt.
Google Chrome does not support that secure site.
Google Chrome does not automatically save web credentials. ✅✅✅
Where are 32-bit program files located in a 64-bit version of Windows 10 Pro?
c:\Program files (x86) ✅✅
c:\Program files
c:\users
c:\Windows\system32
What is the purpose of Windows 10 ReadyBoost?
Which statement is true regarding libraries in Windows 10?
Match the folders in a 64-bit Windows 10 PC to their description. (Not all options are used.)
Thank you for sharing.
In the online test, in the question about HKEY’s, there are two “HKEY_CURRENT_USER” options and one of them goes to “for all users”. It should be “HKEY_USERS” instead.
I will fix it, thank you
Q31- Resetting your pc does not give the option of saving applications only files
A user has to shutdown several remote computers one at a time. What is the best Windows command to select to do the job? ( 1 mark) a) shutdown b) nslookup c) ping d) netstat e) recover
Why Q.no 1 is missing bro??
Hier das Bild was fehlt…
don’t do a hundred percent
схуяли