2.0 Introduction
2.0.1 Why Should I Take this Module?
If you are taking this course, you may be considering a career in CyberOps security. What technologies do you need to be aware of? What types of jobs are available? Where can you find those jobs? Keep reading to find out!
2.0.2 What Will I Learn in this Module?
Module Title: Fighters in the War Against Cybercrime
Module Objective: Explain how to prepare for a career in cybersecurity operations.
| Topic Title | Topic Objective |
|---|---|
| The Modern SOC | Explain the mission of the security operations center (SOC). |
| Becoming a Defender | Describe resources available to prepare for a career in cybersecurity operations. |
2.1 The Modern Security Operations Center
2.1.1 Elements of a SOC
Defending against today’s threats requires a formalized, structured, and disciplined approach. Organizations typically use the services of professionals in a Security Operations Center (SOC). SOCs provide a broad range of services, from monitoring and management, to comprehensive threat solutions and hosted security that can be customized to meet customer needs. SOCs can be wholly in-house, owned and operated by a business, or elements of a SOC can be contracted out to security vendors, such as Cisco’s Managed Security Services.
As illustrated in the figure, the major elements of a SOC, are people, processes, and technologies.
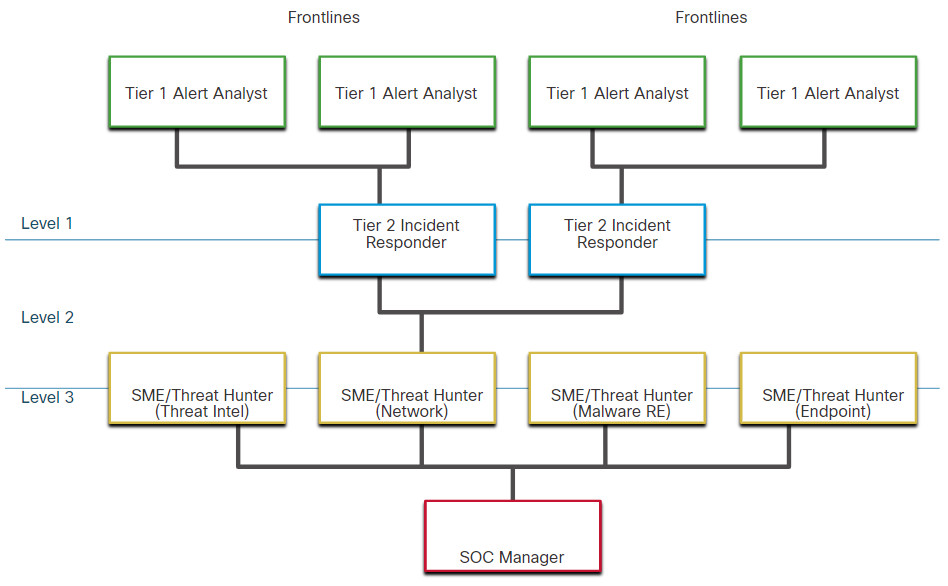
2.1.2 People in the SOC
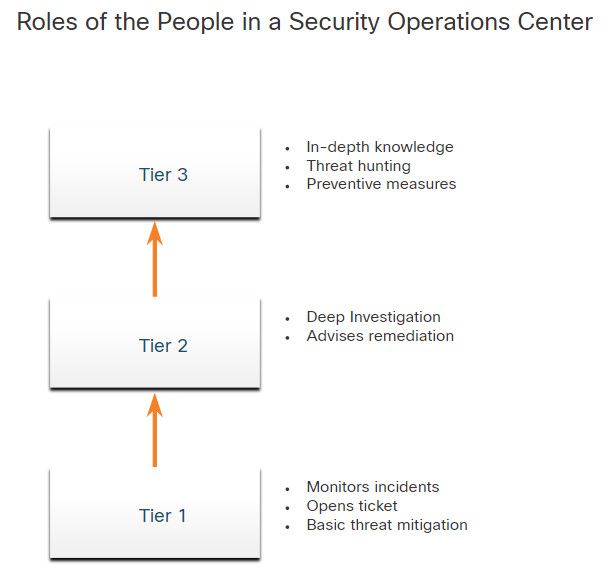
Job roles in a SOC are rapidly evolving. Traditionally, SOCs assign job roles by tiers, according to the expertise and responsibilities required for each. First tier jobs are more entry level, while third tier jobs require extensive expertise.
- Tier 1 Alert Analyst – These professionals monitor incoming alerts, verify that a true incident has occurred, and forward tickets to Tier 2, if necessary.
- Tier 2 Incident Responder– These professionals are responsible for deep investigation of incidents and advise remediation or action to be taken.
- Tier 3 Threat Hunter – These professionals have expert-level skill in network, endpoint, threat intelligence, and malware reverse engineering. They are experts at tracing the processes of the malware to determine its impact and how it can be removed. They are also deeply involved in hunting for potential threats and implementing threat detection tools. Threat hunters search for cyber threats that are present in the network but have not yet been detected.
- SOC Manager – This professional manages all the resources of the SOC and serves as the point of contact for the larger organization or customer.
This course offers preparation for a certification suitable for the position of Tier 1 Alert Analyst, also known as Cybersecurity Analyst or CyberOps Associate.
The figure, which is originally from the SANS Institute, graphically represents how these roles interact with each other.
2.1.3 Process in the SOC
The day of a Cybersecurity Analyst typically begins with monitoring security alert queues. A ticketing system is frequently used to assign alerts to a queue for an analyst to investigate. Because the software that generates alerts can trigger false alarms, one job of the Cybersecurity Analyst might be to verify that an alert represents a true security incident. When verification is established, the incident can be forwarded to investigators or other security personnel to be acted upon. Otherwise, the alert may be dismissed as a false alarm.
If a ticket cannot be resolved, the Cybersecurity Analyst will forward the ticket to a Tier 2 Incident Responder for deeper investigation and remediation. If the Incident Responder cannot resolve the ticket, it will be forwarded it to Tier 3 personnel with in-depth knowledge and threat hunting skills.
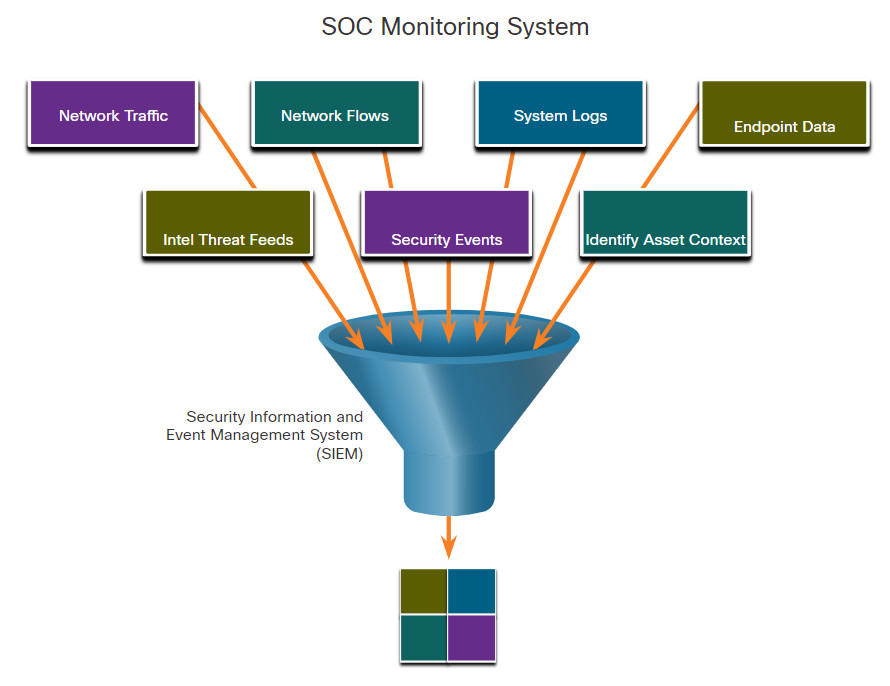
2.1.4 Technologies in the SOC: SIEM
As shown in the figure, a SOC needs a security information and event management system (SIEM), or its equivalent. SIEM makes sense of all the data that firewalls, network appliances, intrusion detection systems, and other devices generate.
SIEM systems are used for collecting and filtering data, detecting and classifying threats, and analyzing and investigating threats. SIEM systems may also and manage resources to implement preventive measures and address future threats. SOC technologies include one or more of the following:
- Event collection, correlation, and analysis
- Security monitoring
- Security control
- Log management
- Vulnerability assessment
- Vulnerability tracking
- Threat intelligence
2.1.5 Technologies in the SOC: SOAR
SIEM and security orchestration, automation and response (SOAR) are often paired together as they have capabilities that complement each other.
Large security operations (SecOps) teams use both technologies to optimize their SOC. It is estimated that 15% of organizations with a security team of larger than five people will utilize SOAR by the end of 2020.
SOAR platforms are similar to SIEMs in that they aggregate, correlate, and analyze alerts. However, SOAR technology goes a step further by integrating threat intelligence and automating incident investigation and response workflows based on playbooks developed by the security team.
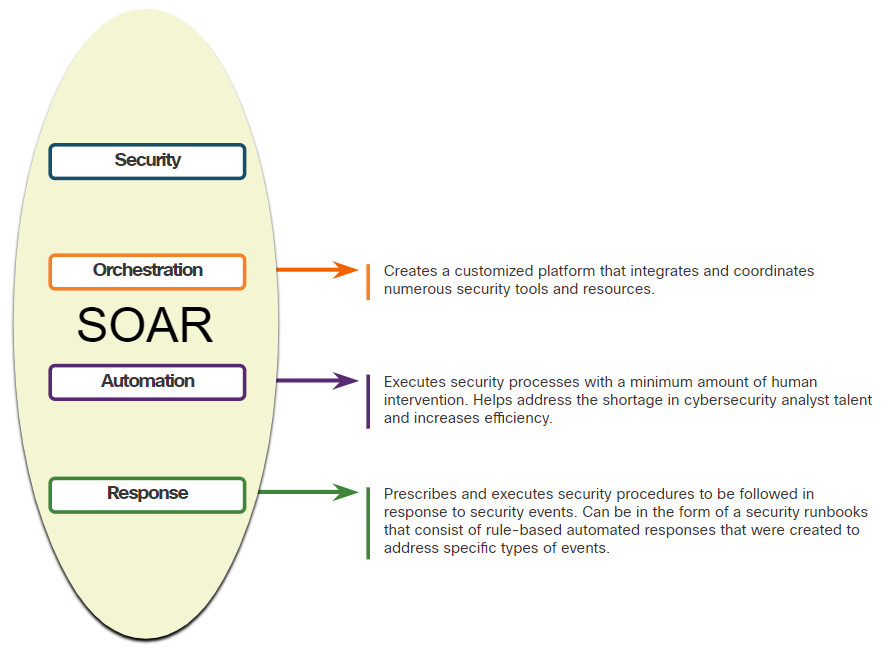
SOAR security platforms:
- Gather alarm data from each component of the system.
- Provide tools that enable cases to be researched, assessed, and investigated.
- Emphasize integration as a means of automating complex incident response workflows that enable more rapid response and adaptive defense strategies.
- Include pre-defined playbooks that enable automatic response to specific threats. Playbooks can be initiated automatically based on predefined rules or may be triggered by security personnel.
SOAR emphasizes integration tools and automation of SOC workflows. It orchestrates many manual processes such as investigation of security alerts only requiring human intervention when necessary. This frees security personnel to address more pressing matters and high-end investigation and threat remediation. The future adoption of sophisticated SOAR platforms will remake SOC operations and job roles.
SIEM systems necessarily produce more alerts than most SecOps teams can realistically investigate in order to conservatively capture as many potential exploits as possible. SOAR will process many of these alerts automatically and will enable security personnel to focus on more complex and potentially damaging exploits.
2.1.6 SOC Metrics
A SOC is critically important to the security of an organization. Whether the SOC is internal to an organization, or providing services to multiple organizations, it is important to understand how well the SOC is functioning in order so that improvements can be made to the people, processes, and technologies that comprise the SOC.
Many metrics, or key performance indicators (KPI) can be devised to measure different specific aspects of SOC performance. However, five metrics are commonly used as SOC metrics. Note however, that metrics that describe blanket performance frequently do not paint an accurate picture of SOC operation due to the diversity of cybersecurity threats. Several common metrics compiled by SOC managers are:
- Dwell Time – the length of time that threat actors have access to a network before they are detected, and their access is stopped.
- Mean Time to Detect (MTTD) – the average time that it takes for the SOC personnel to identify valid security incidents have occurred in the network.
- Mean Time to Respond (MTTR) – the average time that it takes to stop and remediate a security incident.
- Mean Time to Contain (MTTC) – the time required to stop the incident from causing further damage to systems or data.
- Time to Control – the time required to stop the spread of malware in the network.
2.1.7 Enterprise and Managed Security
For medium and large networks, the organization will benefit from implementing an enterprise-level SOC. The SOC can be a complete in-house solution. However, many larger organizations will outsource at least part of the SOC operations to a security solutions provider.
Cisco has a team of experts who help ensure timely and accurate incident resolution. Cisco offers a wide range of incident response, preparedness, and management capabilities including:
- Cisco Smart Net Total Care Service for Rapid Problem Resolution
- Cisco Product Security Incident Response Team (PSIRT)
- Cisco Computer Security Incident Response Team (CSIRT)
- Cisco Managed ServicesCisco Tactical Operations (TacOps)
- Cisco’s Safety and Physical Security Program
2.1.8 Security vs. Availability
Most enterprise networks must be up and running at all times. Security personnel understand that for the organization to accomplish its priorities, network availability must be preserved.
Each business or industry has a limited tolerance for network downtime. That tolerance is usually based upon a comparison of the cost of the downtime in relation to the cost of ensuring against downtime. For example, in a small retail business with only one location, it may be tolerable to have a router as a single point of failure. However, if a large portion of that business’s sales are from online shoppers, then the owner may decide to provide a level of redundancy to ensure that a connection is always available.
Preferred uptime is often measured in the number of down minutes in a year, as shown in the table. For example, a “five nines” uptime means that the network is up 99.999% of the time or down for no more than 5 minutes a year. “Four nines” would be a downtime of 53 minutes a year.
| Availability % | Downtime |
|---|---|
| 99.8% | 17.52 hours |
| 99.9% (“three nines”) | 8.76 hours |
| 99.99% (“ four nines” ) | 52.56 minutes |
| 99.999% (“five nines”) | 5.256 minutes |
| 99.9999% (“six nines“ ) | 31.56 seconds |
| 99.99999% (“seven nines“ ) | 3.16 seconds |
However, security cannot be so strong that it interferes with the needs of employees or business functions. It is always a tradeoff between strong security and permitting efficient business functioning.
2.2 Becoming a Defender
2.2.1 Certifications
A variety of cybersecurity certifications that are relevant to careers in SOCs are available from several different organizations.
Cisco Certified CyberOps Associate
The Cisco Certified CyberOps Associate certification provides a valuable first step in acquiring the knowledge and skills needed to work with a SOC team. It can be a valuable part of a career in the exciting and growing field of cybersecurity operations.
CompTIA Cybersecurity Analyst Certification
The CompTIA Cybersecurity Analyst (CySA+) certification is a vendor-neutral IT professional certification. It validates knowledge and skills required to configure and use threat detection tools, perform data analysis, interpret the results to identify vulnerabilities, threats and risks to an organization. The end goal is the ability to secure and protect applications and systems within an organization.
(ISC)² Information Security Certifications
(ISC)² is an international non-profit organization that offers the highly-acclaimed CISSP certification. They offer a range of other certifications for various specialties in cybersecurity.
Global Information Assurance Certification (GIAC)
GIAC, which was founded in 1999, is one of the oldest security certification organizations. It offers a wide range of certifications in seven categories.
Other Security-Related Certifications
Search for “cybersecurity certifications” on the internet to find information about other vendor and vendor-neutral certifications.
2.2.2 Further Education
Degrees
Anyone considering a career in the cybersecurity field, should seriously consider pursuing a technical degree or bachelor’s degree in computer science, electrical engineering, information technology, or information security. Many educational institutions offer security-related specialized tracks and certifications.
Python Programming
Computer programming is an essential skill for anyone who wishes to pursue a career in cybersecurity. If you have never learned how to program, then Python might be the first language to learn. Python is an open-source, object-oriented language that is routinely used by cybersecurity analysts. It is also a popular programming language for Linux-based systems and software-defined networking (SDN).
Linux Skills
Linux is widely used in SOCs and other networking and security environments. Linux skills are a valuable addition to your skillset as you work to develop a career in cybersecurity.

2.2.3 Sources of Career Information
A variety of websites and mobile applications advertise information technology jobs. Each site targets a variety of job applicants and provides different tools for candidates to research their ideal job position. Many sites are job site aggregators. Job site aggregators gather listings from other job boards and company career sites and display them in a single location.
Indeed.com
Advertised as the world’s #1 job site, Indeed.com attracts over 180 million unique visitors every month from over 50 different countries. Indeed.com is truly a worldwide job site. It helps companies of all sizes hire the best talent and offers the best opportunity for job seekers.
CareerBuilder.com
CareerBuilder serves many large and prestigious companies. As a result, this site attracts specific candidates that typically have more education and higher credentials. The employers posting on CareerBuilder commonly get more candidates with college degrees, advanced credentials, and industry certifications.
USAJobs.gov
The United States federal government posts any openings on the USAJobs website.
Glassdoor
The website glassdoor.com provides salary information for different job types, companies, and locations. Search for “cyber security analyst” to see salaries and requirements for current job openings.
LinkedIn is a professional network of more the 630 million users in more than 150 countries with the mission of helping people be more productive and successful. LinkedIn is also a great source for career information and job opportunities.

2.2.4 Getting Experience
Internships
Internships are an excellent method for entering the cybersecurity field. Sometimes, internships turn into an offer of full time employment. However, even a temporary internship allows you the opportunity to gain experience in the inner workings of a cybersecurity organization. The contacts you make during an internship can also prove to be a valuable resource as you continue your career. Search the internet for the best websites to locate network security internships.
Scholarships and Awards
To help close the security skills gap, organizations like Cisco and INFOSEC have introduced scholarship and awards programs that provide money to students who meet qualification requirements. Search the internet to discover opportunities that are currently offered.
Temporary Agencies
If you are having difficulty finding your first job, a temporary agency can be a great place to start. Most temporary agencies will help you polish your resume and make recommendations on additional skills you may need to obtain to make yourself more attractive to potential employers.
Many organizations use temporary agencies to fill job openings for the first 90 days. Then, if the employee is a good match, the organization may offer to buy the contract from the temporary agency, converting the employee to a full-time, permanent position.
Your First Job
If you have no experience in the cybersecurity field, then you will most likely look for a company that is willing to train you for a position similar to a Tier 1 Analyst. Working for a call center or support desk may be your first step into gaining the experience you need to move ahead in your career.
How long should you stay in your first job? Generally, you want to make it through a full review cycle before leaving a company. That is, you typically want to make it past 18 months. Potential employers will normally want to know if you met or exceeded expectations in your current or past jobs.

2.2.5 Lab – Becoming a Defender
In this lab, you will research and analyze what it takes to become a network defender.
2.2.5 Lab – Becoming a Defender
2.3 Fighters in the War Against Cybercrime Summary
2.3.1 What Did I Learn in this Module?
The Modern Security Operations Center
Major elements of the SOC include people, processes, and technologies. Job roles are rapidly evolving and include tiers based on expertise and experience. These roles include a Tier 1 Alert Analyst, a Tier 2 Incident Responder, a Tier 3 Threat hunter, and an SOC Manager. A Tier 1 Analyst will monitor incidents, open tickets, and perform basic threat mitigation.
SEIM systems are used for collecting and filtering data, detecting and classifying threats, and analyzing and investigating threats. SEIM and SOAR are often paired together. SOAR is similar to SIEM. SOAR goes a step further by integrating threat intelligence and automating incident investigation and response workflows based on playbooks developed by the security team. Key Performance Indicators (KPI) are devised to measure different aspects of SOC performance. Common metrics include Dwell Time, Meant Time to Detect (MTTD), Mean Time to Respond (MTTR), Mean Time to Contain (MTTC), and Time to Control.
There must be a balance between security and availability of the networks. Security cannot be so strong that it interferes with employees or business functions.
Becoming a Defender
A variety of cybersecurity certifications that are relevant to careers in SOCs are available from different organizations. They include Cisco Certified CyberOps Associate, CompTIA Cybersecurity Analyst Certification, (ISC)2 Information Security Certifications, Global Information Assurance Certification (GIAC), and others. Job sites include Indeed.com, CareerBuilder.com, USAJobs.gov, Glassdoor, and LinkedIn. You may also want to consider internships and temporary agencies to gain experience and begin your career. In addition, Linux and Python programming skills will add to your desirability in the job market.
