Check answers here:
IT Essentials (Version 8.0) Final Exam – Composite (Chapters 1-14) Answers
Quiz-summary
0 of 350 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- 143
- 144
- 145
- 146
- 147
- 148
- 149
- 150
- 151
- 152
- 153
- 154
- 155
- 156
- 157
- 158
- 159
- 160
- 161
- 162
- 163
- 164
- 165
- 166
- 167
- 168
- 169
- 170
- 171
- 172
- 173
- 174
- 175
- 176
- 177
- 178
- 179
- 180
- 181
- 182
- 183
- 184
- 185
- 186
- 187
- 188
- 189
- 190
- 191
- 192
- 193
- 194
- 195
- 196
- 197
- 198
- 199
- 200
- 201
- 202
- 203
- 204
- 205
- 206
- 207
- 208
- 209
- 210
- 211
- 212
- 213
- 214
- 215
- 216
- 217
- 218
- 219
- 220
- 221
- 222
- 223
- 224
- 225
- 226
- 227
- 228
- 229
- 230
- 231
- 232
- 233
- 234
- 235
- 236
- 237
- 238
- 239
- 240
- 241
- 242
- 243
- 244
- 245
- 246
- 247
- 248
- 249
- 250
- 251
- 252
- 253
- 254
- 255
- 256
- 257
- 258
- 259
- 260
- 261
- 262
- 263
- 264
- 265
- 266
- 267
- 268
- 269
- 270
- 271
- 272
- 273
- 274
- 275
- 276
- 277
- 278
- 279
- 280
- 281
- 282
- 283
- 284
- 285
- 286
- 287
- 288
- 289
- 290
- 291
- 292
- 293
- 294
- 295
- 296
- 297
- 298
- 299
- 300
- 301
- 302
- 303
- 304
- 305
- 306
- 307
- 308
- 309
- 310
- 311
- 312
- 313
- 314
- 315
- 316
- 317
- 318
- 319
- 320
- 321
- 322
- 323
- 324
- 325
- 326
- 327
- 328
- 329
- 330
- 331
- 332
- 333
- 334
- 335
- 336
- 337
- 338
- 339
- 340
- 341
- 342
- 343
- 344
- 345
- 346
- 347
- 348
- 349
- 350
Information
IT Essentials 7.0 8.0 Final Exam – Composite (Chapters 1-14) Test Online
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 350 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- 143
- 144
- 145
- 146
- 147
- 148
- 149
- 150
- 151
- 152
- 153
- 154
- 155
- 156
- 157
- 158
- 159
- 160
- 161
- 162
- 163
- 164
- 165
- 166
- 167
- 168
- 169
- 170
- 171
- 172
- 173
- 174
- 175
- 176
- 177
- 178
- 179
- 180
- 181
- 182
- 183
- 184
- 185
- 186
- 187
- 188
- 189
- 190
- 191
- 192
- 193
- 194
- 195
- 196
- 197
- 198
- 199
- 200
- 201
- 202
- 203
- 204
- 205
- 206
- 207
- 208
- 209
- 210
- 211
- 212
- 213
- 214
- 215
- 216
- 217
- 218
- 219
- 220
- 221
- 222
- 223
- 224
- 225
- 226
- 227
- 228
- 229
- 230
- 231
- 232
- 233
- 234
- 235
- 236
- 237
- 238
- 239
- 240
- 241
- 242
- 243
- 244
- 245
- 246
- 247
- 248
- 249
- 250
- 251
- 252
- 253
- 254
- 255
- 256
- 257
- 258
- 259
- 260
- 261
- 262
- 263
- 264
- 265
- 266
- 267
- 268
- 269
- 270
- 271
- 272
- 273
- 274
- 275
- 276
- 277
- 278
- 279
- 280
- 281
- 282
- 283
- 284
- 285
- 286
- 287
- 288
- 289
- 290
- 291
- 292
- 293
- 294
- 295
- 296
- 297
- 298
- 299
- 300
- 301
- 302
- 303
- 304
- 305
- 306
- 307
- 308
- 309
- 310
- 311
- 312
- 313
- 314
- 315
- 316
- 317
- 318
- 319
- 320
- 321
- 322
- 323
- 324
- 325
- 326
- 327
- 328
- 329
- 330
- 331
- 332
- 333
- 334
- 335
- 336
- 337
- 338
- 339
- 340
- 341
- 342
- 343
- 344
- 345
- 346
- 347
- 348
- 349
- 350
- Answered
- Review
-
Question 1 of 350
1. Question
1 pointsIn which situation would an ESD strike potentially cause harm to the PC?Correct
Incorrect
Hint
Minimize the risk of electrostatic discharge. Whenever 2 things touch, there is always an exchange of electrons at the atomic level. Most of the time, this exchange is so negligible that you don’t notice it, but even tiny bolts of static electricity can fry your RAM modules. In fact, any electrical component in your computer has a chance to be damaged by static electricity. -
Question 2 of 350
2. Question
1 pointsA person has started a new technical job. In which situation would ESD be an issue?Correct
Incorrect
-
Question 3 of 350
3. Question
1 pointsA technician is about to begin preventive maintenance on a company PC. In which situation would ESD be an issue?Correct
Incorrect
-
Question 4 of 350
4. Question
1 pointsAn instructor has given a student an assignment to assemble a PC. In which situation should the student be aware that ESD is an issue?Correct
Incorrect
-
Question 5 of 350
5. Question
1 pointsWhat two motherboard components control the system boot operations? (Choose two.)Correct
Incorrect
Hint
System boot services are provided by the motherboard BIOS and UEFI chips. -
Question 6 of 350
6. Question
1 pointsA technician is upgrading an ATX motherboard with another ATX motherboard. Which component might be affected by this and need to be upgraded and bought as an additional purchase?Correct
Incorrect
Hint
The motherboard, CPU, and power supply must be compatible. -
Question 7 of 350
7. Question
1 pointsA customer has requested that a PC be built that will support eSATA. Which component should be checked to be sure that this feature is supported?Correct
Incorrect
Hint
The chipset on a motherboard consists of integrated circuits that control how system hardware interacts with the CPU and motherboard. It also provides the capability and features needed, such as the maximum memory supported on the motherboard, multiple USB ports, eSATA connections, surround sound, and video. -
Question 8 of 350
8. Question
1 pointsWhich memory module used to hold instructions for booting a PC and loading the OS, but is still used on adapters even though the memory contents cannot be changed?Correct
Incorrect
Hint
ROM stands for read-only memory. -
Question 9 of 350
9. Question
1 pointsWhat is a characteristic of DDR SDRAM?Correct
Incorrect
Hint
DDR SDRAM transfers data twice per clock cycle, whereas SDRAM transfers data once each clock cycle. Both DDR SDRAM and SDRAM are forms of dynamic memory. The difference in data transfer rate between DDR SDRAM and SDRAM is not determined by the number of pins, nor the operating voltage. -
Question 10 of 350
10. Question
1 pointsWhat are two safety hazards when dealing with laser printers? (Choose two.)Correct
Incorrect
Hint
Laser printers require high voltage when initially powered on and to charge the drum in preparation for writing data to the drum. This high voltage requirement is why most laser printers are not normally connected to a UPS. A laser printer also has a fuser assembly used to apply heat and pressure to the toner to permanently attach it to the paper. The laser printer must be unplugged and the fuser assembly must be allowed to cool before working inside the printer. -
Question 11 of 350
11. Question
1 pointsWhich component requires a technician to install screws externally through the PC case?Correct
Incorrect
Hint
The power supply commonly has four screws that attach from outside the case through case holes into screw holes on the power supply. -
Question 12 of 350
12. Question
1 pointsA technician is installing an internal HDD. To which motherboard connector will the technician connect the data cable?Correct
Incorrect
Hint
Internal hard drives are commonly SATA drives that have a data cable that extends from the drive to a motherboard SATA connector. -
Question 13 of 350
13. Question
1 pointsRefer to the exhibit. A technician has been asked to install a video card. Which section of the motherboard will the technician use to install the card?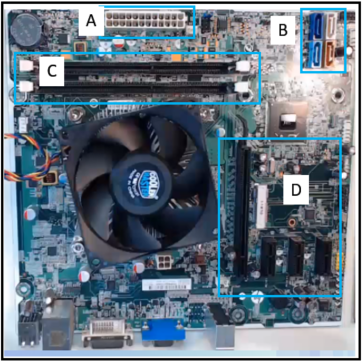 Correct
Correct
Incorrect
Hint
Graphics cards, also known as video cards, are installed into a PCIe x16 expansion slot. The expansion slots on a motherboard are located near the motherboard ports. -
Question 14 of 350
14. Question
1 pointsWhen a PC is being assembled, what component is connected to the motherboard with a SATA cable?Correct
Incorrect
Hint
SATA cables, or serial ATA cables, are used to carry data from drives to the motherboard. -
Question 15 of 350
15. Question
1 pointsA technician is troubleshooting a computer that is experiencing hardware failure detected by the BIOS. What is one way this failure is indicated?Correct
Incorrect
Hint
Beep codes are a result of POST and these vary between computer vendors based on what BIOS is installed. -
Question 16 of 350
16. Question
1 pointsWhich three features can be configured in the BIOS settings to secure a computer? (Choose three.)Correct
Incorrect
Hint
Passwords, drive encryption, and TPM are BIOS configurable security features. File encryption, TKIP key, and MAC filtering are security features not configured within BIOS. -
Question 17 of 350
17. Question
1 pointsWhat is the purpose of RAID adapters?Correct
Incorrect
Hint
RAID 0 allows “striping” or writing data across two hard drives, but provides no redundancy. The other RAID versions provide redundancy. -
Question 18 of 350
18. Question
1 pointsWhen a new motherboard is being installed, between which two components must thermal compound be applied? (Choose two.)Correct
Incorrect
Hint
You must apply thermal compound between the new CPU and the heat sink/fan assembly to avoid overheating the CPU. The thermal paste helps to conduct heat from the CPU to the heat sink. -
Question 19 of 350
19. Question
1 pointsWhat is the purpose of a Safety Data Sheet?Correct
Incorrect
Hint
A Safety Data Sheet is a fact sheet that summarizes information about material identification, including hazardous ingredients that can affect personal health, fire hazards, and first-aid requirements. The SDS explains how to dispose of potentially hazardous materials in the safest manner. -
Question 20 of 350
20. Question
1 pointsWhich negative environmental factor does cleaning the inside of a computer reduce?Correct
Incorrect
Hint
Accumulated dust inside the computer can prevent the flow of air and can hinder cooling. -
Question 21 of 350
21. Question
1 pointsWhat is a recommended procedure to follow when cleaning computer components?Correct
Incorrect
Hint
When using compressed air, keep the can upright to prevent the fluid from leaking onto computer components. -
Question 22 of 350
22. Question
1 pointsOn the production floor, a furniture plant has laptops for process monitoring and reporting. The production floor environment is around 80 degrees Fahrenheit (27 degrees Celsius). The humidity level is fairly high around 70 percent. Fans are mounted in the ceiling for air circulation. Wood dust is prevalent. Which condition is most likely to adversely affect a laptop that is used in this environment?Correct
Incorrect
Hint
Most laptops are created to be tolerant of a wide range of humidity levels and room temperatures. Dust, however, can cause overheating and failures. -
Question 23 of 350
23. Question
1 pointsAfter a technician tests a theory of probable causes, what two actions should the technician take if the testing did not identify an exact cause? (Choose two.)Correct
Incorrect
Hint
If the exact cause of the problem has not been determined after you have tested all your theories, establish a new theory of probable causes and test it. -
Question 24 of 350
24. Question
1 pointsWhat would happen if a PC that contains a power supply that does not automatically adjust for input voltage is set to 230 volts and attaches to an outlet in the United States?Correct
Incorrect
Hint
In the United States, the wall outlet electrical power is standardized at 120 volts AC. -
Question 25 of 350
25. Question
1 pointsWhich type of network spans a single building or campus and provides services and applications to people within a common organizational structure?Correct
Incorrect
Hint
A LAN is smaller or more contained than a WAN, which can span several cities. A MAN is usually contained in one city. A PAN is a very small network of devices that are located in close proximity to one another, usually within range of a single person. -
Question 26 of 350
26. Question
1 pointsWhat are two types of wired high-speed Internet connections? (Choose two.)Correct
Incorrect
Hint
Cable and DSL Internet technologies both use physical cabling to provide an Internet connection to a residence or a small business. Although dial-up is a wired technology, it does not provide a high-speed Internet connection. Satellite and cellular connections provide a wireless Internet connection. -
Question 27 of 350
27. Question
1 pointsIn what two situations would UDP be better than TCP as the preferred transport protocol? (Choose two.)Correct
Incorrect
Hint
UDP is a very simple transport layer protocol that does not guarantee delivery. Devices on both ends of the conversation are not required to keep track of the conversation. UDP is used as the transport protocol for applications that need a speedy, best-effort delivery. -
Question 28 of 350
28. Question
1 pointsThe current IP configuration of a small company is done manually and is time-consuming. Because of increased network growth, a technician needs a simpler way for IP configuration of workstations. Which service would simplify the workstation IP configuration task?Correct
Incorrect
Hint
In networks with more than a few hosts, DHCP simplifies the addressing process. A DHCP server automatically assigns host IP addresses. -
Question 29 of 350
29. Question
1 pointsA company is looking for a next-generation firewall that provides VPN functionality, IDS/IPS functionality, and DoS/DDoS protection. Which device would be best suited for this task?Correct
Incorrect
Hint
A universal threat management (UTM) device is a security device that can provide firewall, IDS/IPS, and proxy server functionality as well as email filtering and DoS/DDoS protection. -
Question 30 of 350
30. Question
1 pointsA student is helping a friend with a home computer that can no longer access the Internet. Upon investigation, the student discovers that the computer has been assigned the IP address 169.254.100.88. What could cause a computer to get such an IP address?Correct
Incorrect
Hint
When a PC does not have a static IP address or cannot pick one up from a DHCP server, Windows will automatically assign the PC an IP address using APIPA, that uses the range of addresses 169.254.0.0 to 169.254.255.255. -
Question 31 of 350
31. Question
1 pointsWhat three values must be added to the IPv4 properties of a NIC in order for a computer to have basic connectivity with the network? (Choose three.)Correct
Incorrect
Hint
The IP address, subnet mask, and default gateway address values should be added to the NIC properties in order for the computer to have basic network connectivity. This can be done either statically or dynamically with DHCP. An additional value that should be present if the computer is to be used to connect to the Internet is the DNS server value. A computer automatically attempts to locate a DHCP server if configured to do so. A DHCP server address is not used. Finally, NAT is configured on a router, not on a computer host, and speed and duplex settings are NIC hardware settings and not IPv4 properties of the NIC. -
Question 32 of 350
32. Question
1 pointsA device has an IPv6 address of 2001:0DB8:75a3:0214:0607:1234:aa10:ba01 /64. What is the host identifier of the device?Correct
Incorrect
Hint
An IPv6 address is made up of 128 bits that are represented as eight blocks of four hexadecimal digits that are called hextets. Because each hexadecimal digit represents four bits, each hextet represents 16 bits. The /64 network prefix indicates that the first 64 bits, or first four hextets, represent the network portion of the address. Because there are 128 bits in an IPv6 address, this leaves the last 64 bits, or last four hextets, to represent the host identifier. The value for the last four hextets is 0607:1234:aa10:ba01. -
Question 33 of 350
33. Question
1 pointsHow can a user prevent specific applications from accessing a Windows computer over a network?Correct
Incorrect
Hint
Network applications have specific TCP or UDP ports that can be left open or blocked in Windows Firewall. Disabling automatic IP address assignment may result in the computer not being able to connect to the network at all. Enabling MAC address filtering is not possible in Windows and would only block specific network hosts, not applications. Changing default usernames and passwords will secure the computer from unauthorized users, not from applications. -
Question 34 of 350
34. Question
1 pointsPlace the six stages of the troubleshooting process in the correct order.Correct
Incorrect
-
Question 35 of 350
35. Question
1 pointsA technician has been asked to configure Wi-Fi calling on a corporate mobile device. In which situation would this feature be most advantageous?Correct
Incorrect
Hint
Wi-Fi calling is not supported on all mobile devices, but when enabled, it uses a Wi-Fi network to make voice calls. It is very useful in areas with poor cellular coverage. -
Question 36 of 350
36. Question
1 pointsWhich statement is true about laptops?Correct
Incorrect
Hint
Laptop internal components are designed with a small form factor and are proprietary. Although a laptop CPU uses less power, it needs a cooling device (heat sink and fan). -
Question 37 of 350
37. Question
1 pointsWhich standard provides a bridge between laptop hardware and the operating system and a way for technicians to configure power management schemes to get the best performance?Correct
Incorrect
Hint
The Advanced Configuration and Power Interface (ACPI) standard has specific sleep states that can be assigned to a device in order to conserve power. PCIe is a motherboard interface. Bluetooth and 802.11 are wireless standards. -
Question 38 of 350
38. Question
1 pointsWhich two laptop components are considered replaceable by the customer. (Choose two.)Correct
Incorrect
Hint
Customer-replaceable units (CRUs) do not typically require a lot of technical skill to replace. RAM and a battery are two examples of a CRU. In contrast, a field-replaceable unit (FRU), such as a display, motherboard, keyboard, or touchpad, commonly requires a technician to install. -
Question 39 of 350
39. Question
1 pointsA user wants to synchronize some apps, movies, music, and ebooks between mobile devices. What are the two types of connections used to synchronize this type of data? (Choose two.)Correct
Incorrect
Hint
Because of the amount of data transferred during video synchronization, synchronization occurs through either a Wi-Fi connection or a wired USB connection. -
Question 40 of 350
40. Question
1 pointsA technician is explaining the differences between inkjet printers and laser printers to a customer. Which two comparisons should the technician make? (Choose two.)Correct
Incorrect
Hint
Inkjet printers are easy to use and usually less expensive than laser printers. Some advantages of an inkjet printer are initial low cost, high resolution, and they are quick to warm up. Some disadvantages of an inkjet printer are that the nozzles are prone to clogging, ink cartridges can be expensive, and the ink is wet for a few seconds after printing. A laser printer is a high-quality, fast printer that uses a laser beam to create an image. Some advantages of a laser printer are low cost per page, high ppm, high capacity, and prints come out dry. Some disadvantages of a laser printer are high cost of startup, and that toner cartridges can be expensive. -
Question 41 of 350
41. Question
1 pointsA user chooses the collate option and prints two copies of a three-page document. What is the order in which the pages are printed?Correct
Incorrect
Hint
The collate feature enables a printer to sort multiple copies of a document with the proper page order for each copy. -
Question 42 of 350
42. Question
1 pointsA color laser printer is used to print documents with graphics and photographs. Users are complaining that printing takes too long. Which component of the printer should be upgraded in order to improve printing performance?Correct
Incorrect
Hint
Because documents with graphics and photographs generate much larger print jobs, the printing process will run more efficiently if the printer memory is adequate to store the entire job before the job starts. -
Question 43 of 350
43. Question
1 pointsWhat service is available for Windows to provide software print server services to MAC OS clients?Correct
Incorrect
Hint
Bonjour Printer Server from Apple comes with MAC OS X and is a free download for Windows users to be used as a software print server. Airport Extreme, a dedicated print server, and a PC with a printer attached serving as a print server are all hardware print sharing solutions. -
Question 44 of 350
44. Question
1 pointsWhich three components are typically found in laser printer maintenance kits? (Choose three.)Correct
Incorrect
Hint
Laser printer maintenance kits typically contain components that wear and can be installed with minimal disassembly of the printer. Corona wires are internal components that would require a trained technician to replace. Paper trays are components that are not typically replaced during maintenance, but would be replaced any time if damaged. -
Question 45 of 350
45. Question
1 pointsA technician is installing a new printer in a cool, damp environment. After the printer cabling is done, and the software and print driver are installed, the printer test page jams. What is the most likely cause of the print failure?Correct
Incorrect
Hint
Paper jams are commonly caused when the paper being used is dirty, affected by humidity, or is the wrong type of paper for the printer. -
Question 46 of 350
46. Question
1 pointsA data center has recently updated a physical server to host multiple operating systems on a single CPU. The data center can now provide each customer with a separate web server without having to allocate an actual discrete server for each customer. What is the networking trend that is being implemented by the data center in this situation?Correct
Incorrect
Hint
Virtualization technology can run several different operating systems in parallel on a single CPU. -
Question 47 of 350
47. Question
1 pointsHow does virtualization help with disaster recovery within a data center?Correct
Incorrect
Hint
Disaster recovery is how a company goes about accessing applications, data, and the hardware that might be affected during a disaster. Virtualization provides hardware independence which means the disaster recovery site does not have to have the exact equipment as the equipment in production. Server provisioning is relevant when a server is built for the first time. Although data centers do have backup generators, the entire data center is designed for disaster recovery. One particular data center could never guarantee that the data center itself would never be without power. -
Question 48 of 350
48. Question
1 pointsWhich two hypervisors are suitable to support virtual machines in a data center? (Choose two.)Correct
Incorrect
Hint
VMware ESX/ESXi and Microsoft Hyper-V 2012 are Type 1 hypervisors that have direct access to the hardware resources. Type 1 hypervisors are more efficient than hosted architectures, and enable greater scalability, performance, and robustness. They are used to support enterprise VMs in data centers. Oracle VM VirtualBox, VMware Fusion, and Microsoft Virtual PC are host based Type 2 hypervisors. -
Question 49 of 350
49. Question
1 pointsA web designer accesses a company Windows 10 computer remotely. The designer often needs to simultaneously open multiple applications, such as a web page editor and a graphics editor. Rather than opening them in multiple windows, the designer opens them in different virtual desktops. What technology is being used by the designer?Correct
Incorrect
Hint
Windows 10 has a feature called Windows Virtual Desktop (WVD). A user can create multiple virtual desktops and navigate among them easily. This feature reduces the clutter on a desktop of Windows caused by opening multiple applications. With WVD, a user can have each application open in a separate desktop. -
Question 50 of 350
50. Question
1 pointsWhich Cloud computing service would be best for an organization that needs to collaboratively create applications and deliver them over the web?Correct
Incorrect
Hint
Platform as a service (PaaS) provides a collaborative environment where multiple developers can create software and host an application through a Cloud provider. -
Question 51 of 350
51. Question
1 pointsWhich statement describes a feature of SDRAM?Correct
Incorrect
Hint
SDRAM ( Synchronous Dynamic RAM) works in synchronization with the memory bus and has higher transfer rates because it can process overlapping instructions in parallel. -
Question 52 of 350
52. Question
1 pointsMatch the memory type to the feature. (Not all options are used.)Correct
Incorrect
-
Question 53 of 350
53. Question
1 pointsA technician is troubleshooting a server that displays the error message “RAID not found” after a power outage over the weekend. What is a possible cause for this?Correct
Incorrect
Hint
The loss of the RAID controller can be caused by the external RAID controller not receiving power, incorrect BIOS settings, failure of the RAID controller or incorrect drivers for the RAID controller. -
Question 54 of 350
54. Question
1 pointsA customer brings in a laptop with a touch screen that is not working correctly. The touch screen either does not respond at all or provides unusual or inaccurate responses. What is a possible cause for such behavior?Correct
Incorrect
Hint
A touch screen that is unresponsive or inaccurate can be caused by dirt or grease on the screen, the screen protector, or apps consuming too many resources. -
Question 55 of 350
55. Question
1 pointsWhat are two security risks associated with sharing printers in a corporate environment? (Choose two.)Correct
Incorrect
Hint
Three security concerns related to shared printers include (1) cached print files could contain sensitive data; (2) user authentication is needed to control access to the printer; and (3) print jobs could be read by others, intercepted, copied, or modified. Although the names of documents can be viewed in the print queue, document viewing is not possible. Dumpster diving and shoulder surfing are security concerns whether the printer is shared or not. -
Question 56 of 350
56. Question
1 pointsWhich change management process component is concerned with the business processes that are affected by changes?Correct
Incorrect
Hint
There are several change management process components that help changes, installations, and upgrades go more easily. The assessment component identifies the business processes that are affected and the costs and resources required. -
Question 57 of 350
57. Question
1 pointsMatch the problem to the possible solution. (Not all options are used.)Correct
Incorrect
-
Question 58 of 350
58. Question
1 pointsA computer technician is installing a RAID. If the RAID uses mirroring and striping, which RAID level is the technician using?Correct
Incorrect
Hint
RAID Levels:RAID Level Minimum Number of Drives Features 0 2 Striping 1 2 Mirroring 5 3 Striping with parity 6 3 Striping with double parity 10 (0+1) 4 Mirroring and Striping -
Question 59 of 350
59. Question
1 pointsA computer technician is installing a RAID. If the RAID uses mirroring, which RAID level is the technician using?Correct
Incorrect
Hint
RAID Levels:RAID Level Minimum Number of Drives Features 0 2 Striping 1 2 Mirroring 5 3 Striping with parity 6 3 Striping with double parity 10 (0+1) 4 Mirroring and Striping -
Question 60 of 350
60. Question
1 pointsA computer technician is installing a RAID. If the RAID uses striping with parity, which RAID level is the technician using?Correct
Incorrect
Hint
RAID Levels:RAID Level Minimum Number of Drives Features 0 2 Striping 1 2 Mirroring 5 3 Striping with parity 6 3 Striping with double parity 10 (0+1) 4 Mirroring and Striping -
Question 61 of 350
61. Question
1 pointsA computer technician is installing a RAID. If the RAID uses striping, which RAID level is the technician using?Correct
Incorrect
Hint
RAID Levels:RAID Level Minimum Number of Drives Features 0 2 Striping 1 2 Mirroring 5 3 Striping with parity 6 3 Striping with double parity 10 (0+1) 4 Mirroring and Striping -
Question 62 of 350
62. Question
1 pointsA computer technician is installing a RAID. If the RAID uses striping with double parity, which RAID level is the technician using?Correct
Incorrect
Hint
RAID Levels:RAID Level Minimum Number of Drives Features 0 2 Striping 1 2 Mirroring 5 3 Striping with parity 6 3 Striping with double parity 10 (0+1) 4 Mirroring and Striping -
Question 63 of 350
63. Question
1 pointsA technician is upgrading many PCs used within the company. How should the technician dispose of an old battery?Correct
Incorrect
-
Question 64 of 350
64. Question
1 pointsA technician is upgrading many PCs used within the company. How should the technician dispose of a broken monitor?Correct
Incorrect
-
Question 65 of 350
65. Question
1 pointsA technician is upgrading many PCs used within the company. How should the technician dispose of an old power supply?Correct
Incorrect
-
Question 66 of 350
66. Question
1 pointsA technician is upgrading many PCs used within the company. How should the technician dispose of old RAM?Correct
Incorrect
-
Question 67 of 350
67. Question
1 pointsA technician is upgrading many PCs used within the company. How should the technician dispose of an old motherboard?Correct
Incorrect
-
Question 68 of 350
68. Question
1 pointsA technician is upgrading many PCs used within the company. How should the technician dispose of an old hard drive?Correct
Incorrect
-
Question 69 of 350
69. Question
1 pointsAfter continuous morning use, a computer suddenly reboots without the intervention of the user. What are the two most likely hardware parts that could cause this problem? (Choose two.)Correct
Incorrect
-
Question 70 of 350
70. Question
1 pointsA technician has been called in to investigate a problem with the computer rebooting randomly throughout the day. What two pieces of hardware could cause this problem? (Choose two.)Correct
Incorrect
-
Question 71 of 350
71. Question
1 pointsFor two days in a row, a user has noticed that the computer reboots several times before it eventually starts. What are two suspect components? (Choose two.)Correct
Incorrect
-
Question 72 of 350
72. Question
1 pointsWhile a user is working on a spreadsheet, the computer reboots. What are two components that could cause this issue? (Choose two.)Correct
Incorrect
-
Question 73 of 350
73. Question
1 pointsA client packet is received by a server. The packet has a destination port number of 137. What service application is the client requesting?Correct
Incorrect
-
Question 74 of 350
74. Question
1 pointsA client packet is received by a server. The packet has a destination port number of 22. What service application is the client requesting?Correct
Incorrect
-
Question 75 of 350
75. Question
1 pointsA client packet is received by a server. The packet has a destination port number of 143. What service application is the client requesting?Correct
Incorrect
-
Question 76 of 350
76. Question
1 pointsA client packet is received by a server. The packet has a destination port number of 23. What service application is the client requesting?Correct
Incorrect
-
Question 77 of 350
77. Question
1 pointsA client packet is received by a server. The packet has a destination port number of 161. What service application is the client requesting?Correct
Incorrect
-
Question 78 of 350
78. Question
1 pointsA client packet is received by a server. The packet has a destination port number of 389. What service application is the client requesting?Correct
Incorrect
-
Question 79 of 350
79. Question
1 pointsA client packet is received by a server. The packet has a destination port number of 25. What service application is the client requesting?Correct
Incorrect
-
Question 80 of 350
80. Question
1 pointsA client packet is received by a server. The packet has a destination port number of 427. What service application is the client requesting?Correct
Incorrect
-
Question 81 of 350
81. Question
1 pointsA client packet is received by a server. The packet has a destination port number of 53. What service application is the client requesting?Correct
Incorrect
-
Question 82 of 350
82. Question
1 pointsWhich is the compressed format of the IPv6 address 2001:0db8:0000:0000:0000:a0b0:0008:0001?Correct
Incorrect
-
Question 83 of 350
83. Question
1 pointsWhich is the compressed format of the IPv6 address fe80:09ea:0000:2200:0000:0000:0fe0:0290?Correct
Incorrect
-
Question 84 of 350
84. Question
1 pointsWhich is the compressed format of the IPv6 address 2002:0042:0010:c400:0000:0000:0000:0909?Correct
Incorrect
-
Question 85 of 350
85. Question
1 pointsWhich is the compressed format of the IPv6 address 2002:0420:00c4:1008:0025:0190:0000:0990?Correct
Incorrect
-
Question 86 of 350
86. Question
1 pointsWhich is the compressed format of the IPv6 address 2001:0db8:0000:0000:0ab8:0001:0000:1000?Correct
Incorrect
-
Question 87 of 350
87. Question
1 pointsWhich is the compressed format of the IPv6 address fe80:0000:0000:0000:0220:0b3f:f0e0:0029?Correct
Incorrect
-
Question 88 of 350
88. Question
1 pointsWhich is the compressed format of the IPv6 address fe80:9ea0:0000:2020:0000:00bf:00e0:9290?Correct
Incorrect
-
Question 89 of 350
89. Question
1 pointsWhat ACPI power state describes when the CPU and RAM are off and the contents of RAM have been saved to a temporary file on the hard drive?Correct
Incorrect
-
Question 90 of 350
90. Question
1 pointsWhat ACPI power state describes when the CPU and RAM are still receiving power but unused devices are powered down?Correct
Incorrect
-
Question 91 of 350
91. Question
1 pointsWhat ACPI power state describes when the CPU is off, but the RAM is refreshed?Correct
Incorrect
-
Question 92 of 350
92. Question
1 pointsWhat ACPI power state describes when the computer is off?Correct
Incorrect
-
Question 93 of 350
93. Question
1 pointsWhat ACPI power state describes when the CPU is off and the RAM is set to a slow refresh rate, often called suspend mode?Correct
Incorrect
-
Question 94 of 350
94. Question
1 pointsWhat ACPI power state describes when the computer is on and the CPU is running?Correct
Incorrect
-
Question 95 of 350
95. Question
1 pointsA reporter is trying to print several high resolution photographs but the color laser printer is going extremely slowly. What should the technician do to resolve the issue?Correct
Incorrect
-
Question 96 of 350
96. Question
1 pointsA new printer has just been installed deep in a mine. When test pages are printed, the paper constantly jams. What should the technician do to resolve the issue?Correct
Incorrect
-
Question 97 of 350
97. Question
1 pointsA user complains that recently every printed document has vertical lines and streaks on the paper. What should the technician do to resolve the issue?Correct
Incorrect
-
Question 98 of 350
98. Question
1 pointsA school is installing a new shared printer but the printer is not showing up on the list of available printers. What should the technician do to resolve the issue?Correct
Incorrect
-
Question 99 of 350
99. Question
1 pointsEmployees are complaining that they send print jobs to a newly installed printer but the print jobs never print. What should the technician do to resolve the issue?Correct
Incorrect
-
Question 100 of 350
100. Question
1 pointsUsers have noticed that the colors on their printed documents are different from the colors that they see on their computer screens. What should the technician do to resolve the issue?Correct
Incorrect
-
Question 101 of 350
101. Question
1 pointsA technician has just completed a preventive maintenance on the department printer. Users are now complaining that the printer is no longer available. What should the technician do to resolve the issue?Correct
Incorrect
-
Question 102 of 350
102. Question
1 pointsEmployees of a small business are complaining that the printer is printing faded images. What should the technician do to resolve the issue?Correct
Incorrect
-
Question 103 of 350
103. Question
1 pointsA photographer is complaining about the following printer issue: The printer issues a “Document failed to print” message. What are two possible causes of this issue? (Choose two.)Correct
Incorrect
-
Question 104 of 350
104. Question
1 pointsA reporter is complaining about the following printer issue: The printer is printing unknown characters. What are two possible causes of this issue? (Choose two.)Correct
Incorrect
-
Question 105 of 350
105. Question
1 pointsA manager is complaining about the following printer issue: The printer is printing incorrect colors. What are two possible causes of this issue? (Choose two.)Correct
Incorrect
-
Question 106 of 350
106. Question
1 pointsA technician is complaining about the following printer issue: The print appears faded on the paper. What are two possible causes of this issue? (Choose two.)Correct
Incorrect
-
Question 107 of 350
107. Question
1 pointsA librarian is complaining about the following printer issue: The printer control panel displays no image. What are two possible causes of this issue? (Choose two.)Correct
Incorrect
-
Question 108 of 350
108. Question
1 pointsA teacher is complaining about the following printer issue: The paper is creased after printing. What are two possible causes of this issue? (Choose two.)Correct
Incorrect
-
Question 109 of 350
109. Question
1 pointsA receptionist is complaining about the following printer issue: My impact printer produces faded or light characters. What are two possible causes of this issue? (Choose two.)Correct
Incorrect
-
Question 110 of 350
110. Question
1 pointsA photographer is complaining about the following printer issue: The paper is not being fed into the printer. What are two possible causes of this issue? (Choose two.)Correct
Incorrect
-
Question 111 of 350
111. Question
1 pointsA laptop has an NVMe drive (C:) and a mechanical hard drive (D:). When the user tries to save a spreadsheet to the D: drive, the user notices that the D: drive is not there. What should the technician do to see if the drive is recognized by the operating system?Correct
Incorrect
-
Question 112 of 350
112. Question
1 pointsA computer has two mechanical hard drives. The second drive (D:) is used for data storage. When trying to save an email attachment to the local hard drive, the user notices that the D: drive is not an option. What should the technician do to see if the drive is recognized by the operating system?Correct
Incorrect
-
Question 113 of 350
113. Question
1 pointsA user reports that a drive is no longer there. The technician asks the user to demonstrate the problem. Within the application, the user demonstrates that the drive, that was present in the save options yesterday, is now no longer an option. What should the technician do to see if the drive is recognized by the operating system?Correct
Incorrect
-
Question 114 of 350
114. Question
1 pointsA computer has an SSD for the operating system and applications and uses another mechanical hard drive for data storage. The user reports that data can no longer be saved to the mechanical hard drive. What should the technician do to see if the drive is recognized by the operating system?Correct
Incorrect
-
Question 115 of 350
115. Question
1 pointsA technician is working on a laptop and the GPS is not functioning. What is a probable cause for this situation?Correct
Incorrect
-
Question 116 of 350
116. Question
1 pointsA technician is working on a laptop and an app is not loading. What is a probable cause for this situation?Correct
Incorrect
-
Question 117 of 350
117. Question
1 pointsA technician is working on a laptop and an app is not responding. What is a probable cause for this situation?Correct
Incorrect
-
Question 118 of 350
118. Question
1 pointsA technician is working on a laptop and an error message about decryption appears when opening an email. What is a probable cause for this situation?Correct
Incorrect
-
Question 119 of 350
119. Question
1 pointsA PC technician has been asked by a supervisor to recommend a security solution for a small company that wants stateful firewall services. Which security technique should the technician recommend?Correct
Incorrect
-
Question 120 of 350
120. Question
1 pointsA gamer is booting a desktop that has Windows 10 installed on dynamic drives. The boot process is currently working on the following step: WinLoad reads the registry files, chooses a hardware profile, and loads the device drivers. What is the next step that will happen in the boot process?Correct
Incorrect
Hint
Boot Sequence for Windows: – Power on Self Test (POST) – POST for each adapter card that has a BIOS – BIOS reads the MBR – MBR takes over control of the boot process and starts BOOTMGR – BOOTMGR reads the Boot Configuration Data file to know which OS to load and where to find the OS on the boot partition – BOOTMGR invokes WINLOAD.EXE in order to load the NTOSKRNL.EXE file and HAL.DLL – BOOTMGR reads the registry files and loads device drivers – NTOSKRNL.EXE starts the WINLOGON.EXE program and displays the Windows login screen At this point, the NT kernel takes over. The NT kernel is the heart of all Windows operating systems. The name of this file is NTOSKRNL.EXE. It starts the login file called WINLOGON.EXE and displays the Windows Welcome screen. -
Question 121 of 350
121. Question
1 pointsA technician is working on a laptop and an error message about decryption appears when opening an email. What is a possible solution for this situation?Correct
Incorrect
-
Question 122 of 350
122. Question
1 pointsUsers in the sales department want to be able to print from laptops and tablets. Which two wireless technologies should the IT technician look for when researching new printers for the sales department? (Choose two.)Correct
Incorrect
Hint
Many printers come with built-in wireless capability which enables them to be connected to a WiFi network (802.11 standard). Some come equipped with the ability to connect to devices through Bluetooth pairing. -
Question 123 of 350
123. Question
1 pointsWhat are three factors to consider when purchasing a replacement motherboard? (Choose three.)Correct
Incorrect
Hint
Because you have to match the motherboard with the parts like power supply form factor, case form factor, cpu socket/chipset, RAM that will remain the same. You replace only the motherboard in this case. -
Question 124 of 350
124. Question
1 pointsWhat are two features of protocols used within the TCP/IP protocol stack? (Choose two.)Correct
Incorrect
Hint
Application programmers make decisions about which protocols to use to transport the data to and from their applications based on whether the application can tolerate any lost data. Live streaming and voice transmissions can use UDP because if a few data packets are lost, the quality of the video and audio is not seriously impacted. TCP is used when all data must be complete and accurate. -
Question 125 of 350
125. Question
1 pointsA technician is working on a laptop and a key on the keyboard is not responding as it should. What is a possible solution for this situation?Correct
Incorrect
-
Question 126 of 350
126. Question
1 pointsWhat two effects might suggest that an incorrect printer driver is loaded on the Windows PC? (Choose two.)Correct
Incorrect
-
Question 127 of 350
127. Question
1 pointsWhy would a network technician change the wireless router IP address to a different private IP address during initial installation?Correct
Incorrect
-
Question 128 of 350
128. Question
1 pointsA technician is working on a laptop and GPS is not functioning. What is a possible solution for this situation?Correct
Incorrect
-
Question 129 of 350
129. Question
1 pointsWhich factor can limit the amount of data that the CPU can receive and process at one time?Correct
Incorrect
-
Question 130 of 350
130. Question
1 pointsWhich type of optical drive supports the greatest amount of storage and is able to read and write CDs, DVDs, and Blu-Ray media?Correct
Incorrect
Hint
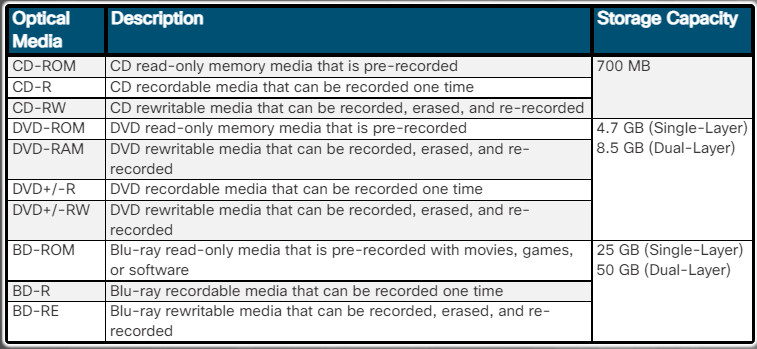
-
Question 131 of 350
131. Question
1 pointsA technician is working on a laptop and GPS is not functioning. What is a possible solution for this situation?Correct
Incorrect
-
Question 132 of 350
132. Question
1 pointsWhy would a manager need to use the sfc command?Correct
Incorrect
-
Question 133 of 350
133. Question
1 pointsWhy would a technician need to use the DISM command?Correct
Incorrect
-
Question 134 of 350
134. Question
1 pointsWhy would a technician need to use the tasklist command?Correct
Incorrect
-
Question 135 of 350
135. Question
1 pointsWhy would an analyst need to use the taskkill command?Correct
Incorrect
-
Question 136 of 350
136. Question
1 pointsWhy would an analyst need to use the msconfig command?Correct
Incorrect
-
Question 137 of 350
137. Question
1 pointsWhy would an analyst need to use the dir command?Correct
Incorrect
-
Question 138 of 350
138. Question
1 pointsWhy would a bank manager need to use the gpupdate command?Correct
Incorrect
-
Question 139 of 350
139. Question
1 pointsWhy would a bank manager need to use the gpresult command?Correct
Incorrect
-
Question 140 of 350
140. Question
1 pointsWhy would a lawyer need to use the cd command?Correct
Incorrect
-
Question 141 of 350
141. Question
1 pointsWhich two activities are normally controlled by the Northbridge part of the chipset? (Choose two.)Correct
Incorrect
Hint
The Northbridge chipset generally controls access to the RAM, video card, and the speeds at which the CPU can communicate with them. -
Question 142 of 350
142. Question
1 pointsA manager is booting a tablet that has Windows 8 installed. The boot process is currently working on the following step: WINLOGON.EXE displays the Windows Welcome screen What is the next step that will happen in the boot process?Correct
Incorrect
Hint
Boot Sequence for Windows: – Power on Self Test (POST) – POST for each adapter card that has a BIOS – BIOS reads the MBR – MBR takes over control of the boot process and starts BOOTMGR – BOOTMGR reads the Boot Configuration Data file to know which OS to load and where to find the OS on the boot partition – BOOTMGR invokes WINLOAD.EXE in order to load the NTOSKRNL.EXE file and HAL.DLL – BOOTMGR reads the registry files and loads device drivers – NTOSKRNL.EXE starts the WINLOGON.EXE program and displays the Windows login screen At this point, the NT kernel takes over. The NT kernel is the heart of all Windows operating systems. The name of this file is NTOSKRNL.EXE. It starts the login file called WINLOGON.EXE and displays the Windows Welcome screen. -
Question 143 of 350
143. Question
1 pointsAn analyst is booting a tablet that has Windows 7 installed with media card reader. The boot process is currently working on the following step: WINLOGON.EXE displays the Windows Welcome screen What is the next step that will happen in the boot process?Correct
Incorrect
-
Question 144 of 350
144. Question
1 pointsMatch the function performed by an OS to its description.Correct
Incorrect
-
Question 145 of 350
145. Question
1 pointsBefore installing the latest version of printer management software, an IT technician creates a restore point on the Windows 10 computer. The installation fails before it is complete, and now the printer shows as unavailable. Which Windows option should the technician use to reverse the software installation and return the system to its prior state without affecting users files and settings?Correct
Incorrect
-
Question 146 of 350
146. Question
1 pointsA new customer asks if all of its older company computers, which are still running Windows XP, can be immediately upgraded to Windows 10. What are two important concerns that the IT technician must discuss with the customer in order to determine if the OS upgrade can be done? (Choose two.)Correct
Incorrect
-
Question 147 of 350
147. Question
1 pointsWhich three wireless router settings should be disabled as a security best practice? (Choose three.)Correct
Incorrect
-
Question 148 of 350
148. Question
1 pointsMatch the Android or Apple element to its description.Correct
Incorrect
-
Question 149 of 350
149. Question
1 pointsWhat are two symptoms that indicate that a computer system may be a victim of DNS spoofing? (Choose two.)Correct
Incorrect
-
Question 150 of 350
150. Question
1 pointsA PC technician has been asked by a supervisor to recommend a security solution for preventing tailgating. Which security technique should the technician recommend?Correct
Incorrect
-
Question 151 of 350
151. Question
1 pointsMatch the computer or peripheral problem with a probable cause of the issue.Correct
Incorrect
-
Question 152 of 350
152. Question
1 pointsA company contracts with a service provider to obtain IaaS and ITaaS services. What are two advantages of these types of cloud service implementation? (Choose two.)Correct
Incorrect
Hint
Cloud service providers have extended the IaaS model to also provide IT as a service (ITaaS). ITaaS can extend the capability of IT without requiring investment in new infrastructure, training new personnel, or licensing new software. These services are available on demand and delivered economically to any device anywhere in the world without compromising security or function. -
Question 153 of 350
153. Question
1 pointsWhat are two methods of disabling cellular data when located in an area where it is limited or expensive? (Choose two.)Correct
Incorrect
-
Question 154 of 350
154. Question
1 pointsRefer to the exhibit. A computer technician creates a bootable USB hard drive and loads a Linux operating system on it. When the technician reboots the computer, it does not boot to the Linux OS. Instead, the light on the optical drive flashes and then the computer loads Windows. What needs to be done to ensure that the computer automatically boots from the USB hard drive if it is connected?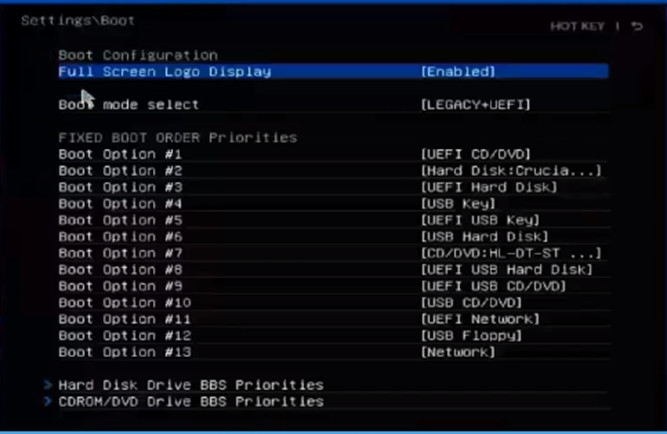 Correct
Correct
Incorrect
-
Question 155 of 350
155. Question
1 pointsA help desk technician receives a call from a user describing an issue with a computer. The user states that the computer will not power on, that it only makes a beeping sound. Why does the technician ask the user to restart the system and count how many beeps the computer makes?Correct
Incorrect
-
Question 156 of 350
156. Question
1 pointsA college uses Microsoft 365 Office and email services for its faculty, staff, and students. Data storage, custom applications, and Microsoft Active Directory services are delivered by virtual servers leased from a local data center. Single sign-on is implemented for both environments for authentication and authorization. Access control is managed locally. What type of cloud service implementation is the college using?Correct
Incorrect
-
Question 157 of 350
157. Question
1 pointsThe help desk receives a call from a customer who reports a computer issue that occurs after trying to install Windows 10 with a disc that the IT department provided. When the customer reboots the computer, instead of loading Windows, the computer displays the Windows installation program screen again. Which probable cause should the IT technician place at the top of the list of most obvious reasons for the error?Correct
Incorrect
-
Question 158 of 350
158. Question
1 pointsOffice workers in a software company are being temporarily relocated to a different area of the building while their previous office space is being reconfigured. Which type of network device should be installed to make it easy for the users to connect to the company network from all of their devices, including smart phones, tablets, and laptops?Correct
Incorrect
-
Question 159 of 350
159. Question
1 pointsWhat is an example of an active cooling solution for a desktop PC?Correct
Incorrect
-
Question 160 of 350
160. Question
1 pointsWhat is a consequence of a computer not having enough RAM memory installed?Correct
Incorrect
-
Question 161 of 350
161. Question
1 pointsRefer to the exhibit. A payroll department employee has shared a locally attached HP Officejet Pro 8110 printer over the network in Windows 10. What do the other Windows 10 users in the payroll department have to do in order to print to the shared printer?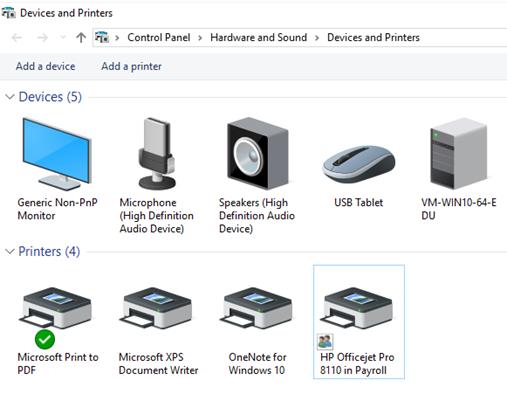 Correct
Correct
Incorrect
-
Question 162 of 350
162. Question
1 pointsWhich type of power supply is the most commonly used and provides a separate power connection in order to directly power the CPU?Correct
Incorrect
-
Question 163 of 350
163. Question
1 pointsRefer to the exhibit. A user calls the help desk to report a printer issue. The user explains that when selecting the print option from the menu bar, a dialog box pops up requesting a file name. After entering the filename, nothing prints on the attached HP printer. What is the cause of the issue that the user is experiencing?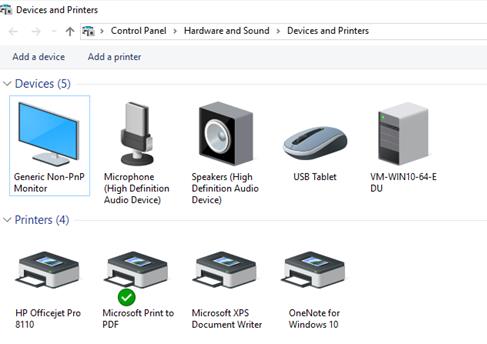 Correct
Correct
Incorrect
-
Question 164 of 350
164. Question
1 pointsWhich function is incorporated into some Intel CPUs that enables a single CPU to perform as though two CPUs are installed?Correct
Incorrect
Hint
Various CPU manufacturers complement their CPU with performance-enhancing features. For instance, Intel incorporates Hyper-Threading to enhance the performance of some of their CPUs. With Hyper-Threading, multiple pieces of code (threads) are executed simultaneously in the CPU. To an operating system, a single CPU with Hyper-Threading performs as though there are two CPUs when multiple threads are being processed. AMD processors use HyperTransport to enhance CPU performance. HyperTransport is a high-speed connection between the CPU and the Northbridge chip. -
Question 165 of 350
165. Question
1 pointsWhich cloud computing characteristic enables multiple tenants to share the same storage, processing, and network bandwidth?Correct
Incorrect
Hint
Resource pooling, the provider’s computing resources are pooled to serve multiple consumers using a multi-tenant model. Each model, each tenant (i.e., customer) shares the different physical and virtual resources dynamically assigned and reassigned according to consumer demand. Examples of resources that can be pooled and shared include storage, processing, memory, and network bandwidth. -
Question 166 of 350
166. Question
1 pointsWhich three types of external ports can be used to connect an external storage device to a computer? (Choose three.)Correct
Incorrect
-
Question 167 of 350
167. Question
1 pointsWhich three computer components require separate cabling for power? (Choose three.)Correct
Incorrect
-
Question 168 of 350
168. Question
1 pointsIn which two situations would thin clients be a good choice to meet the end-user computing needs? (Choose two.)Correct
Incorrect
-
Question 169 of 350
169. Question
1 pointsRefer to the exhibit. Which two hypervisor software products are suitable for the virtualization environment shown in the exhibit? (Choose two.)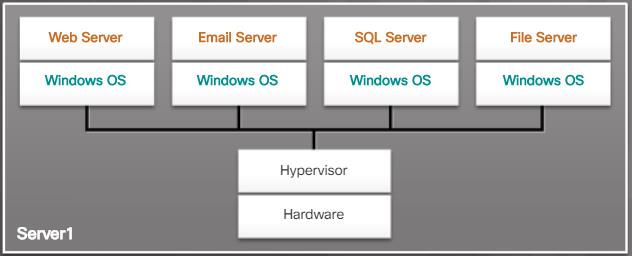 Correct
Correct
Incorrect
-
Question 170 of 350
170. Question
1 pointsRefer to the exhibit. The help desk is receiving numerous calls from employees in the payroll department. It appears that their computers can print to the local network printer, but cannot access the cloud-based payroll service. One employee sends a screen print showing the result of issuing an ipconfig /all command. What is the cause of the issue being experienced by the users?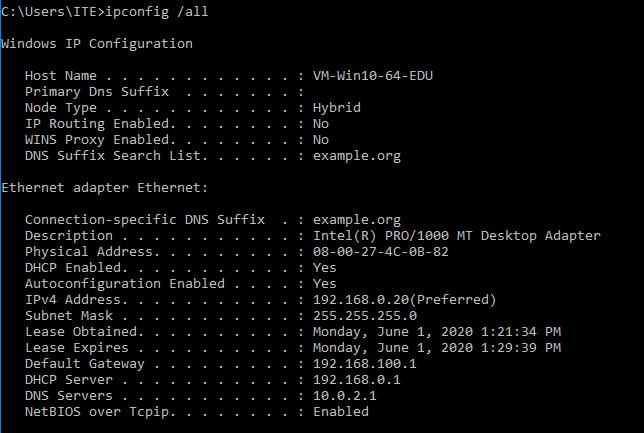 Correct
Correct
Incorrect
-
Question 171 of 350
171. Question
1 pointsAn employee recently purchased a smartwatch. Following the instructions from the watch manufacturer, the employee downloads the wearable app and installs it on an Android phone. The smartwatch shows that it is in discoverable mode, but the app cannot connect to the watch. What is one issue that might cause this problem?Correct
Incorrect
-
Question 172 of 350
172. Question
1 pointsWhich member of the DDR SDRAM family has the fastest clock rate and consumes the least amount of power?Correct
Incorrect
-
Question 173 of 350
173. Question
1 pointsRefer to the exhibit. What is one function that a technician can accomplish using this graphical interface? Correct
Correct
Incorrect
-
Question 174 of 350
174. Question
1 pointsA network technician suspects that there may be a short or a termination error in the wiring that connects an Ethernet switch to the network. Which tool would be the best choice for the technician to use to identify the issue?Correct
Incorrect
-
Question 175 of 350
175. Question
1 pointsA client packet is received by a server. The packet has a destination port number of 110. What service application is the client requesting?Correct
Incorrect
-
Question 176 of 350
176. Question
1 pointsWhy would a university student need to use the taskkill command?Correct
Incorrect
-
Question 177 of 350
177. Question
1 pointsWhich term describes a partition scheme that supports storing a backup of a partition table?Correct
Incorrect
-
Question 178 of 350
178. Question
1 pointsHow can a hard drive that is using an MBR be partitioned in order to support additional logical drives?Correct
Incorrect
-
Question 179 of 350
179. Question
1 pointsA computer technician uses Windows tools to gather information such as system components, operating system, users, and disk drives on multiple systems within the company. Another technician suggests that the tasks would take less time if they were automated. Which two built-in scripting capabilities in Windows enable a technician to run a simple text file, created in Notepad, which contains the necessary commands and variables? (Choose two.)Correct
Incorrect
-
Question 180 of 350
180. Question
1 pointsMatch the IT policy type with its description.Correct
Incorrect
-
Question 181 of 350
181. Question
1 pointsRefer to the exhibit. Examine both the output and the source code of the Linux shell script sample.sh. Which two statements describe the variables contained in the sample.sh script? (Choose two.)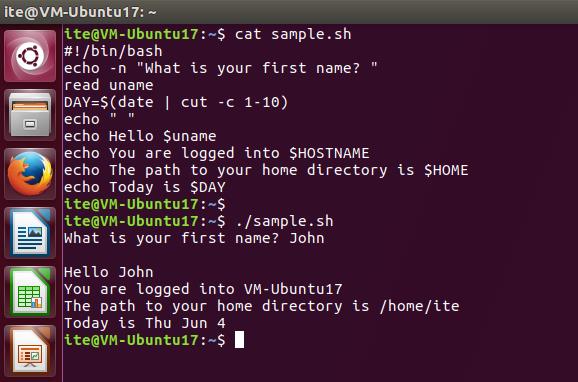 Correct
Correct
Incorrect
-
Question 182 of 350
182. Question
1 pointsWhy would a lawyer need to use the tracert command?Correct
Incorrect
Hint
tracert – The command traces the route that packets take from your computer to a destination host. At the command prompt, enter tracerthostname. The first listing in the results is your default gateway. Each listing after that is the router that packets are traveling through to reach the destination. Tracert shows you where packets are stopping, indicating where the problem is occurring. -
Question 183 of 350
183. Question
1 pointsA network analyst is booting a laptop that has Windows 7 installed with cellular SIM slot. The boot process is currently working on the following step: The Windows kernel takes over the boot process. What is thenext step that will happen in the boot process?Correct
Incorrect
Hint
Boot Sequence for Windows: – Power on Self Test (POST) – POST for each adapter card that has a BIOS – BIOS reads the MBR – MBR takes over control of the boot process and starts BOOTMGR – BOOTMGR reads the Boot Configuration Data file to know which OS to load and where to find the OS on the boot partition – BOOTMGR invokes WINLOAD.EXE in order to load the NTOSKRNL.EXE file and HAL.DLL – BOOTMGR reads the registry files and loads device drivers – NTOSKRNL.EXE starts the WINLOGON.EXE program and displays the Windows login screen At this point, the NT kernel takes over. The NT kernel is the heart of all Windows operating systems. The name of this file is NTOSKRNL.EXE. It starts the login file called WINLOGON.EXE and displays the Windows Welcome screen. -
Question 184 of 350
184. Question
1 pointsA company purchases 15 USB flash drives to use for data analysis training for company accountants. The data analysis training requires that actual company data be stored on the drives, so a secure method of erasing the data is needed before the flash drives can be reused for other training classes. What method should the IT technicians use to ensure that the data on the USB flash drives cannot be recovered?Correct
Incorrect
-
Question 185 of 350
185. Question
1 pointsRefer to the exhibit. What can be determined about the contents of the ite_user home directory?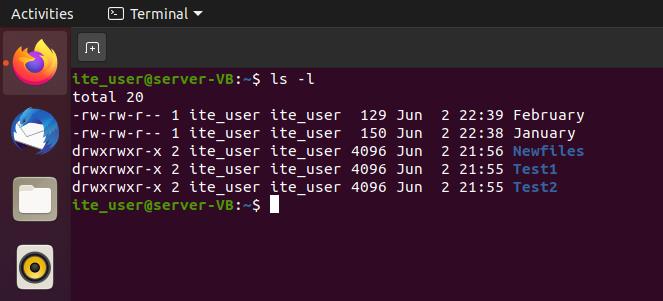 Correct
Correct
Incorrect
-
Question 186 of 350
186. Question
1 pointsRefer to the exhibit. What is true of this mobile device screen? Correct
Correct
Incorrect
Hint
The Windows Phone interface uses tiles to represent apps. Tiles are rectangular areas of a screen that identify the app and may also contain active content such as text messages, news feeds, and photos. -
Question 187 of 350
187. Question
1 pointsAn on-site IT technician needs to work on systems installed in a small health clinic located in New York state. When the technician arrives, the office manager asks if the technician is aware of HIPAA regulations. Which two situations are breaches of PHI and could possibly lead to severe penalties under HIPAA? (Choose two.)Correct
Incorrect
-
Question 188 of 350
188. Question
1 pointsWhy would a manager need to use the del command?Correct
Incorrect
-
Question 189 of 350
189. Question
1 pointsA technician is working on a laptop and an app is not responding. What is a possible solution for this situation?Correct
Incorrect
-
Question 190 of 350
190. Question
1 pointsAn end user wants to be able to recover an older version of a document that was created earlier in the day. Assuming that Windows Backup is enabled, which Windows 10 function can provide a user access to recover specific versions of a file?Correct
Incorrect
-
Question 191 of 350
191. Question
1 pointsAn IT technician attempts to copy a large file to a USB flash drive that contains other data but the copy fails. The technician checks the properties of the flash drive and finds that it was formatted using FAT32. Which method can the technician use to easily change the file system to NTFS without losing the data files currently stored on the disk?Correct
Incorrect
-
Question 192 of 350
192. Question
1 pointsAn employee wants to keep a local backup of iPhone data on a Windows laptop. What type of software does the employee need on the laptop to create this backup?Correct
Incorrect
-
Question 193 of 350
193. Question
1 pointsWhat can an IT technician accomplish using the Manage Storage Spaces feature in Windows 8 and 10?Correct
Incorrect
-
Question 194 of 350
194. Question
1 pointsWhile troubleshooting an issue on a customer computer, an on-site technician believes that the problem can be resolved by using Windows Restore. What type of information is not restored when using Windows Restore with a recent restore point snapshot?Correct
Incorrect
-
Question 195 of 350
195. Question
1 pointsA technician is booting a PC that has Windows 10 installed on dynamic drives. The boot process is currently working on the following step: POST. What is the next step that will happen in the boot process?Correct
Incorrect
Hint
Boot Sequence for Windows: – Power on Self Test (POST) – POST for each adapter card that has a BIOS – BIOS reads the MBR – MBR takes over control of the boot process and starts BOOTMGR – BOOTMGR reads the Boot Configuration Data file to know which OS to load and where to find the OS on the boot partition – BOOTMGR invokes WINLOAD.EXE in order to load the NTOSKRNL.EXE file and HAL.DLL – BOOTMGR reads the registry files and loads device drivers – NTOSKRNL.EXE starts the WINLOGON.EXE program and displays the Windows login screen At this point, the NT kernel takes over. The NT kernel is the heart of all Windows operating systems. The name of this file is NTOSKRNL.EXE. It starts the login file called WINLOGON.EXE and displays the Windows Welcome screen. -
Question 196 of 350
196. Question
1 pointsWhat are two features of multicore processors? (Choose two.)Correct
Incorrect
-
Question 197 of 350
197. Question
1 pointsWhich two statements describe characteristics of network addresses? (Choose two.)Correct
Incorrect
Hint
Knowing how network addressing works can speed configuration and troubleshooting tasks. MAC addresses are assigned by the NIC manufacturer and remain the same as long as the NIC is not replaced. MAC addresses are used to communicate between devices connected to the same local Ethernet network. Valid IPv4 and IPv6 addresses are necessary for communications to be routed over the internet. All IP addresses are valid only on a network that has the same network prefix bits and the same subnet mask. -
Question 198 of 350
198. Question
1 pointsAn on-site technician is asked to check a laptop used by an executive who occasionally works from home. The technician observes that the image on the laptop screen flickers and appears dull, even though the same image displayed on another monitor attached to the laptop docking station is normal. What are two issues that could cause the symptoms the technician observed? (Choose two.)Correct
Incorrect
-
Question 199 of 350
199. Question
1 pointsA technician must replace a power supply. Which two features should the technician consider when selecting the replacement? (Choose two.)Correct
Incorrect
-
Question 200 of 350
200. Question
1 pointsWhy is unbuffered memory a better choice than buffered memory for gaming or general use computers?Correct
Incorrect
-
Question 201 of 350
201. Question
1 pointsA UTM appliance, such as a Cisco ASA 5506-X, includes the functionality of which two standalone devices? (Choose two.)Correct
Incorrect
-
Question 202 of 350
202. Question
1 pointsAn on-site IT technician is attempting to resolve an issue with application performance on a customer laptop. The technician backs up the customer data and then replaces the memory in the laptop with known good memory. It does not resolve the performance issue. What are the next two actions the technician should take? (Choose two.)Correct
Incorrect
Hint
If you cannot determine the exact cause of the problem after testing all your theories, establish a new theory of probable cause and test it. If necessary, escalate the problem to a technician with more experience. Before you escalate, document each test that you tried -
Question 203 of 350
203. Question
1 pointsA user wants VirtualBox to run automatically when Windows 10 starts up. Which action will enable VirtualBox to load and run on system startup?Correct
Incorrect
-
Question 204 of 350
204. Question
1 pointsAn on-site IT technician finished the removal of malware from a customer computer and installed new virus protection software. An hour after the technician left the site, the customer called the help desk to report that a critical web-based application was no longer functioning properly. Which step in the troubleshooting process did the IT technician fail to properly complete?Correct
Incorrect
-
Question 205 of 350
205. Question
1 pointsWhat are two characteristics of the hotend nozzle on a 3D printer? (Choose two.)Correct
Incorrect
-
Question 206 of 350
206. Question
1 pointsRefer to the exhibit. What can be determined from the output of this command? Correct
Correct
Incorrect
-
Question 207 of 350
207. Question
1 pointsWhich type of disk drive can provide a very fast boot experience and also provide high capacity storage?Correct
Incorrect
Hint
Solid-state drives (SSD) store data as electrical charges in semiconductor flash memory. This makes SSDs much faster than magnetic HDDs. SSD storage capacity ranges from around 120 GBs to many TBs. -
Question 208 of 350
208. Question
1 pointsRefer to the exhibit. Which type of adapter card may require the width of two slots in order to accommodate additional cooling, even though it only has one PCIe x16 connector? Correct
Correct
Incorrect
Hint
PCIe x16 slots are generally intended for use with Graphics Cards. Capture devices usually use PCIe 1x slots -
Question 209 of 350
209. Question
1 pointsA technician follows the instruction manual that came with a new Bluetooth speaker to place the speaker in discoverable mode. In this mode, what type of information will the speaker transmit to the laptop in order to start the pairing process?Correct
Incorrect
-
Question 210 of 350
210. Question
1 pointsA technician is booting a PC that has Windows 10 installed on dynamic drives. The boot process is currently working on the following step: BIOS locates and reads the configuration settings that are stored in the CMOS memory. What is the next step that will happen in the boot process?Correct
Incorrect
Hint
After POST, the BIOS locates and reads the configuration settings that are stored in the CMOS memory. The boot device priority, the boot device priority is set in the BIOS and can be arranged in any order. The BIOS boots the computer using the first drive that contains an operating system. -
Question 211 of 350
211. Question
1 pointsA network analyst is booting a laptop that has Windows 7 installed with cellular SIM slot. The boot process is currently working on the following step: The Windows kernel takes over the boot process. What is the next step that will happen in the boot process?Correct
Incorrect
Hint
Boot Sequence for Windows: – Power on Self Test (POST) – POST for each adapter card that has a BIOS – BIOS reads the MBR – MBR takes over control of the boot process and starts BOOTMGR – BOOTMGR reads the Boot Configuration Data file to know which OS to load and where to find the OS on the boot partition – BOOTMGR invokes WINLOAD.EXE in order to load the NTOSKRNL.EXE file and HAL.DLL – BOOTMGR reads the registry files and loads device drivers – NTOSKRNL.EXE starts the WINLOGON.EXE program and displays the Windows login screen At this point, the NT kernel takes over. The NT kernel is the heart of all Windows operating systems. The name of this file is NTOSKRNL.EXE. It starts the login file called WINLOGON.EXE and displays the Windows Welcome screen. -
Question 212 of 350
212. Question
1 pointsWhy would a bank manager need to use the bootrec command?Correct
Incorrect
-
Question 213 of 350
213. Question
1 pointsA gamer is booting a tablet that has Windows 7 installed with 4 GB RAM. The boot process is currently working on the following step: The Windows kernel takes over the boot process. What is the next step that will happen in the boot process?Correct
Incorrect
-
Question 214 of 350
214. Question
1 pointsWhy would a user need to use the gpresult command?Correct
Incorrect
-
Question 215 of 350
215. Question
1 pointsAn accountant is booting a desktop that has Windows 8 installed. The boot process is currently working on the following step: WinLoad loads two files that make up the core of Windows: NTOSKRNL.EXE and HAL.DLL. What is the next step that will happen in the boot process?Correct
Incorrect
-
Question 216 of 350
216. Question
1 pointsA user is booting a desktop that has Windows 10 installed that also uses an extended partition. The boot process is currently working on the following step: The code in the boot sector is executed and the control of the boot process is given to Windows Boot Manager. What is the next step that will happen in the boot process?Correct
Incorrect
-
Question 217 of 350
217. Question
1 pointsA technician is working on a laptop and an app is not loading. What is a possible solution for this situation?Correct
Incorrect
-
Question 218 of 350
218. Question
1 pointsWhich term describes a file system that supports a partition size up to 2 TB?Correct
Incorrect
Hint
File Allocation Table, 32 bit (FAT32) – Supports partition sizes up to 2 TB or 2,048 GB. The FAT32 file system is used by Windows XP and earlier OS versions. -
Question 219 of 350
219. Question
1 pointsWhy would a technician need to use the copy command?Correct
Incorrect
-
Question 220 of 350
220. Question
1 pointsMatch the Windows 10 boot sequence after the boot manager (bootmgr.exe) loads.Correct
Incorrect
-
Question 221 of 350
221. Question
1 pointsMatch the correct API with its function within the Windows 10 environment.Correct
Incorrect
-
Question 222 of 350
222. Question
1 pointsWhich two tools are available to transfer user data and settings from an old Windows computer to a Windows operating system on a new computer? (Choose two.)Correct
Incorrect
Hint
When a new operating system is being installed, existing user data and settings need to be migrated from the old to the new operating system. The User State Migration Tool and the Windows Easy Transfer Tool are available to perform this task on the Windows Vista, 7, and 8 operating systems. -
Question 223 of 350
223. Question
1 pointsA user wants to extend a primary partition formatted with the NTFS file system with the unallocated space on the hard disk. What must the user do after the primary partition is extended to make it usable?Correct
Incorrect
Hint
A partition must be formatted with the NTFS file system in order to extend it by using the unallocated space on the disk. Once the partition has been extended, the disk type must be converted to a dynamic disk in order for the new partition to be accessible. -
Question 224 of 350
224. Question
1 pointsWhy is a full format more beneficial than a quick format when preparing for a clean OS installation?Correct
Incorrect
Hint
A full format removes files from a partition while scanning the disk for bad sectors. A quick format will remove files from a partition but does not scan a disk for bad sectors. -
Question 225 of 350
225. Question
1 pointsA technician wishes to prepare the computers in the network for disaster recovery. The network consists of a variety of desktops and laptops from different vendors. All the computers are running either a 32-bit version of Windows 10 Pro or a 64-bit version of Windows 10 Pro. How would the technician prepare the recovery media?Correct
Incorrect
Hint
All the PCs are from different vendors and thus have dissimilar hardware configurations. Furthermore, all the PCs have a variety of 32-bit Windows 10 and 64-bit Windows 10. Because the PCs have different versions of the OS and dissimilar hardware, you cannot use the same image on all the PCs . In order to use a single image, Sysprep must be used to strip out machine specific information like the SID, and all PCs must have the same hardware configuration and the same version of the Windows operating system. -
Question 226 of 350
226. Question
1 pointsA technician wishes to deploy Windows 10 Pro to multiple PCs through the remote network installation process. The technician begins by connecting the new PCs to the network and booting them up. However, the deployment fails because the target PCs are unable to communicate with the deployment server. What is the possible cause?Correct
Incorrect
Hint
The NIC cards on the new PCs have to be PXE-enabled in order for them to communicate with the remote installation services on the server. -
Question 227 of 350
227. Question
1 pointsWhich condition is required when planning to install Windows on a GPT disk?Correct
Incorrect
Hint
The globally unique identifier (GUID) partition table (GPT) makes use of a number of modern techniques to expand on the older MBR partitioning scheme. GPT is commonly used in computers with UEFI firmware. For Windows 10 to be installed on, and boot, from a GPT disk UEFI must be used. -
Question 228 of 350
228. Question
1 pointsA technician wishes to perform a customized unattended network installation of Windows 10 on a PC. The requirements include the installation of specific applications and device drivers through the use of an answer file. What would the technician use to create the answer file?Correct
Incorrect
Hint
To perform a custom Windows Unattended installation, setup.exe must be run with the user options found in the answer file. Additional packages, such as applications or drivers, can be added to the answer file. The Windows System Image Manager (SIM) is used to create the setup answer file. -
Question 229 of 350
229. Question
1 pointsAn organization has purchased a custom application for the sales staff that can only be installed on a 64-bit Windows operating system. Each member of the sales staff has a Windows 8.1 32-bit PC. What must the IT department do in order to install and run the application on the sales staff computers?Correct
Incorrect
Hint
A 32-bit OS cannot be upgraded to a 64-bit OS. In this case a clean install of Windows 64-bit would be the only option because the application requires a 64-bit Windows environment to work. -
Question 230 of 350
230. Question
1 pointsMatch the tabs of the Windows 10 Task Manager to their functions. (Not all options are used.)Correct
Incorrect
-
Question 231 of 350
231. Question
1 pointsMatch the drive status indicators in the Disk Management utility with their description. (Not all options are used.)Correct
Incorrect
-
Question 232 of 350
232. Question
1 pointsMatch the wireless security settings to the description. (Not all options are used.)Correct
Incorrect
-
Question 233 of 350
233. Question
1 pointsWhat are two possible solutions to any Windows computer restarting continuously and never displaying the desktop? (Choose two.)Correct
Incorrect
Hint
Upgrading the processor, upgrading the video card, or resetting the hard drive jumper would not fix this problem. Boot order settings cannot cause the system to reboot continuously. -
Question 234 of 350
234. Question
1 pointsA technician uses Microsoft Deployment Image Servicing and Management (DISM) tool to create a Windows image file on one of the workstations running Windows 10. When the technician tries to clone another workstation with the image file, the workstation exhibits network connectivity issues on completion. What could cause this?Correct
Incorrect
Hint
The technician must use Sysprep to clean up the local specific configuration, such as the SID, otherwise the cloned systems will not work properly. -
Question 235 of 350
235. Question
1 pointsA user complains that user files cannot be synced with the network file server while the user is traveling out of the office. The user had access to the internet but no access to the company network server. How can this be addressed?Correct
Incorrect
Hint
Because the user has access to the internet, access to the Microsoft OneDrive cloud based service is possible and thus the user can sync with Microsoft OneDrive, which in turn can sync with the company network server from across the internet. -
Question 236 of 350
236. Question
1 pointsA technician has connected a new internal hard drive to a Windows 10 PC. What must be done in order for Windows 10 to use the new hard drive?Correct
Incorrect
Hint
The new hard drive needs to be initialized before it can be used in Windows. This will involve formatting the disk which will erase any existing data on the drive. -
Question 237 of 350
237. Question
1 pointsWhat service does PRINT$ provide?Correct
Incorrect
Hint
PRINT$ is a hidden share for printer drivers. It is shared by default and used to access remote shared printers or provide drivers to clients when sharing a printer. -
Question 238 of 350
238. Question
1 pointsA technician is troubleshooting a Windows 10 laptop infected with a virus that has damaged the master boot record. The technician has booted the laptop using the installation media and is attempting to repair the laptop from the command line interface. Which command can the technician use to repair the corrupt master boot record?Correct
Incorrect
Hint
The sfc /scannow command is used to check the integristy of the system files. The msconfig command allows for viewing the startup configuration mode, while the chkdsk command is used to repair the Windows file system. The bootrec /fixmbr command is used to repair a corrupt master boot record in a Windows 10 environment. -
Question 239 of 350
239. Question
1 pointsA user reports that a Windows 10 PC displays the error message “Invalid Boot Disk” during the boot process. The IT technician attempts to boot the computer and finds that the error message occurs immediately after the POST. What could be the possible cause?Correct
Incorrect
Hint
The message “invalid Boot Disk” could be a symptom of a missing or damaged MBR/GPT, a missing or damaged Boot Configuration Data file, a boot sector virus, a boot order not set correctly in BIOS, media without an operating system being in a drive, a hard drive not detected or damaged, or the absence of an installed operating system. -
Question 240 of 350
240. Question
1 pointsWhich port number is used by Virtual Network Computing (VNC) to provide remote screen sharing between devices?Correct
Incorrect
Hint
Virtual Network Computing (VNC) is a freeware product that is similar in functionality to RDP and works over port 5900. -
Question 241 of 350
241. Question
1 pointsWhich feature is included with macOS and provides the ability for a remote user to view and change files, folders, and applications on the local computer?Correct
Incorrect
Hint
In macOS, remote access functionality is provided by the Screen Sharing feature, which is based on Virtual Network Computing (VNC). VNC is a freeware product that is similar in functionality to RDP and works over port 5900. -
Question 242 of 350
242. Question
1 pointsWhich area of concern falls under the operations and planning category in IT documentation?Correct
Incorrect
Hint
There are four broad categories of IT documentation: Policies, Operations, Projects, and User documentation. Operations is concerned with inventory management. -
Question 243 of 350
243. Question
1 pointsMatch the individual languages with their corresponding classification.Correct
Incorrect
Hint
Scripting languages include Windows batch files, PowerShell, Linux shell script, VBScript, JavaScript, and Python. Compiled languages include C, C++, C#, and Java. -
Question 244 of 350
244. Question
1 pointsWhich two actions should a technician take if illegal content, such as child pornography, is discovered on the hard drive of a customer computer? (Choose two.)Correct
Incorrect
Hint
If illegal content is found, begin documentation to build a chain of custody and contact a first responder immediately. -
Question 245 of 350
245. Question
1 pointsWhat are three pieces of information a level one technician should gather from a customer? (Choose three.)Correct
Incorrect
Hint
A level one technician should gather information from the customer and solve simple problems. For more advanced diagnostics, opening the computer case, running diagnostics software, and performing remote connections, the problem should be escalated to a level two technician. -
Question 246 of 350
246. Question
1 pointsWhat two actions are appropriate for a support desk technician to take when assisting customers? (Choose two.)Correct
Incorrect
Hint
When dealing with customers, a technician should show professionalism in all aspects. A technician should observe the process before putting a customer on hold. First, let the customer finish speaking. Then, explain that there is need to put the customer on hold for a short period, and ask the customer for permission to do so. Tell the customer that it will be only a few minutes and explain what you will do during the period. When the customer agrees to be put on hold, thank the customer. -
Question 247 of 350
247. Question
1 pointsA support desk technician is dealing with an angry customer. Which two approaches should the technician take in dealing with the customer? (Choose two.)Correct
Incorrect
Hint
Angry customers should be allowed to explain the problem, then be redirected to discussing how the problem can be solved. Transferring the customer, replying in a rude tone, and asking unrelated questions will usually increase, not ease, the anger being expressed by the customer. -
Question 248 of 350
248. Question
1 pointsWhat two kinds of problems should be escalated from a level one technician to a level two technician? (Choose two.)Correct
Incorrect
Hint
A problem should be escalated to a level two technician when the problem is going to take a long time to fix, is affecting a large number of users, or requires knowledge or expertise that the level one technician does not possess. -
Question 249 of 350
249. Question
1 pointsAn IT technician in a service company has provided extensive remote IT support with product deployment for a customer. After the completion of the contract, a complaint is filed against the IT technician for not following company policy by sending unsolicited emails about services and products that are not related to the contract. What two things should the IT support technician have done differently? (Choose two.)Correct
Incorrect
Hint
While working with customers both briefly and over an extended period of time, it is possible to form friendly relationships. It is important to always follow company policy and never send unsolicited messages to a customer. Also do not send unsolicited mass mailings or chain letters to customers from a company email address. Any personal relationships should be kept via personal email accounts and should not reflect the IT organization of the employer. -
Question 250 of 350
250. Question
1 pointsA third-party security firm is performing a security audit of a company and recommends the company utilize the Remote Desktop Protocol. What are two characteristics of the Microsoft Remote Desktop Protocol (RDP)? (Choose two.)Correct
Incorrect
Hint
The Remote Desktop protocol (RDP) is used to remotely access a Windows OS. It is a client/server protocol.The port number for RDP is TCP port 3389 and it uses encryption. -
Question 251 of 350
251. Question
1 pointsWhich subject area describes collecting and analyzing data from computer systems, networks, and storage devices, as part of an investigation of alleged illegal activity?Correct
Incorrect
Hint
The field of computer forensics involves collecting and analyzing data from computer systems, networks, wireless communications, and storage devices. -
Question 252 of 350
252. Question
1 pointsIn a computer forensics investigation, which type of data is considered volatile data and can be lost if power is removed from the computer?Correct
Incorrect
Hint
Volatile data is a data that is lost when power is turned off, and is located in temporary storage such as RAM, cache, CPU or in transit between them. -
Question 253 of 350
253. Question
1 pointsRefer to the exhibit. During the troubleshooting of software that is installed on a computer system, a level one technician requires help from a level two technician. The file shown in the exhibit must be sent to the level two technician. How should the level one technician deliver this file?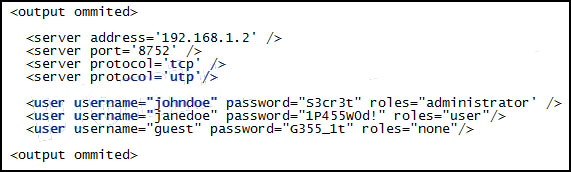 Correct
Correct
Incorrect
Hint
Customer privacy should be maintained. The easiest way to preserve it is removing any occurrence of passwords from the documentation that is being sent to another technician. If a client password is required to solve the problem, it should be sent to another technician through a specific document. -
Question 254 of 350
254. Question
1 pointsWhat skill is essential for a level one technician to have?Correct
Incorrect
Hint
The level one technician must be able to translate the description of a customer problem into a succinct sentence or two that is entered into the work order. -
Question 255 of 350
255. Question
1 pointsWhat is used to control illegal use of software and content?Correct
Incorrect
Hint
Digital rights management, or DRM, is software that is designed to prevent illegal access to digital content. -
Question 256 of 350
256. Question
1 pointsWhat determines the level of support that a call center technician will provide to an individual customer?Correct
Incorrect
Hint
A call center technician must provide the level of support that is outlined in the SLA for that individual customer. -
Question 257 of 350
257. Question
1 pointsA bench technician enters the server room and finds the backup server computer case open. The hard drives containing patient medical data are all physically disconnected from the motherboard and the SATA data cables are hanging outside the case. Which step should the technician immediately take?Correct
Incorrect
Hint
When a potential crime scene is found, a chain of custody must be observed and followed. The technician should immediately locate another employee who is qualified to collect evidence. Disconnecting or reconnecting the drives or attempting to move data may adversely affect the chain of custody. -
Question 258 of 350
258. Question
1 pointsWhat is the difference between a scripting language and a compiled language?Correct
Incorrect
Hint
A scripting language is different than a compiled language because each line is interpreted and then executed when the script is run. Compiled languages need to be converted into executable code using a compiler. Another difference between the two types of languages is that compiled languages are executed by the CPU while scripting languages are executed by a command interpreter or by the operating system. -
Question 259 of 350
259. Question
1 pointsWhich methods can be used to implement multifactor authentication?Correct
Incorrect
Hint
A cybersecurity specialist must be aware of the technologies available that support the CIA triad. -
Question 260 of 350
260. Question
1 pointsWhen responding to a call from a customer who is experiencing problems with a computer, the technician notices that a number of system files on the computer have been renamed. Which two possible solutions could the technician implement to resolve the problem? (Choose two.)Correct
Incorrect
Hint
Renamed system files are usually the result of a virus on the computer. Removing the virus and restoring the computer from a backup are the only two possible solutions in this case. -
Question 261 of 350
261. Question
1 pointsA technician suspects that a security issue is causing problems with a computer. What two actions could be performed to test theories of probable cause when troubleshooting the PC? (Choose two.)Correct
Incorrect
Hint
Several actions can be taken by a technician when security issues are suspected as the possible cause of a problem with a computer. Logging in as a different user or disconnecting the PC from the network to isolate the cause of the problem are two possible actions. -
Question 262 of 350
262. Question
1 pointsThe CIO wants to secure data on company laptops by implementing file encryption. The technician determines the best method is to encrypt each hard drive using Windows BitLocker. Which two things are needed to implement this solution? (Choose two.)Correct
Incorrect
Hint
Windows provides a method to encrypt files, folders, or entire hard drives depending on need. However, certain BIOS settings and configurations are necessary to implement encryption on an entire hard disk. -
Question 263 of 350
263. Question
1 pointsWhat is an accurate description of asymmetric encryption technology?Correct
Incorrect
-
Question 264 of 350
264. Question
1 pointsWhich type of security threat can be transferred through email and is used to gain sensitive information by recording the keystrokes of the email recipient?Correct
Incorrect
Hint
Adware does not record keystrokes. A worm self-replicates across the network. A Trojan appears to be a legitimate program while carrying malware, and grayware is a general term for software that may be malware. -
Question 265 of 350
265. Question
1 pointsA manager reports that unusual things are happening on a Windows computer. The technician determines that malware is the culprit. What can the technician do to remove stubborn malware?Correct
Incorrect
Hint
Booting the computer in Safe Mode prevents most drivers from loading. Additional antimalware software can then be installed to remove or quarantine malware. Sometimes the storage drive must be wiped, the operating system reinstalled, and data restored from a backup. -
Question 266 of 350
266. Question
1 pointsAn employee that has worked at the company for many years has started a home-based business selling crafts. While leaving an office meeting, a company supervisor notices the employee buying supplies for the personal crafting business of the employee. What section of the security policy should the supervisor review when determining how to handle this situation?Correct
Incorrect
Hint
The acceptable use policies section of a security policy commonly identifies network resources and usages that are acceptable to the organization. They might also state the ramifications that can occur if this security policy is violated. -
Question 267 of 350
267. Question
1 pointsWhat Windows utility should be used to configure password rules and account lockout policies on a system that is not part of a domain?Correct
Incorrect
Hint
A technician must be aware of the technologies and measures that are used as countermeasures to protect the organization from threats and vulnerabilities. A Windows Domain Security Policy is used and applied when a user logs in to a computer that is on a corporate network. A Windows Local Security Policy is used for stand-alone computers to enforce security settings. -
Question 268 of 350
268. Question
1 pointsA customer brings in a computer that is asking for a password as soon as it powers on, even before the operating system boots. Which type of password is enabled?Correct
Incorrect
Hint
A BIOS password is configured by entering the BIOS Setup program. If unknown, it can be removed by placing a jumper over two motherboard pins. Some motherboards support BIOS password removal by removing the CMOS battery, but if this is done, all BIOS settings will be reset to the default values. -
Question 269 of 350
269. Question
1 pointsWhen attempting to improve system performance for Linux computers with a limited amount of memory, why is increasing the size of the swap file system not considered the best solution?Correct
Incorrect
Hint
The swap file system is used by Linux when it runs out of physical memory. When needed, the kernel moves inactive RAM content to the swap partition on the hard disk. Storing and retrieving content in the swap partition is much slower than RAM is, and therefore using the swap partition should not be considered the best solution to improving system performance. -
Question 270 of 350
270. Question
1 pointsWhat are three features of GPS on mobile devices? (Choose three.)Correct
Incorrect
Hint
Navigation, specialized search results, and device tracking are features of GPS on mobile devices. Remote wipe may be a feature on some mobile devices, but is not related to GPS. Phone number lookup and gas mileage calculations are not GPS features. -
Question 271 of 350
271. Question
1 pointsWhich three components are used to assign file and directory permissions in Linux systems? (Choose three.)Correct
Incorrect
In Linux, file and directory permissions are assigned as follows:
- Owner – the owner user of the file or directory
- Group – the user group that has been assigned to the file or directory
- All users – all other users on the system
-
Question 272 of 350
272. Question
1 pointsA user downloads a widget onto his Android phone but is puzzled to see that when the widget is touched an app is launched. What is a possible cause?Correct
Incorrect
Hint
Widgets are programs that when installed associate with the application they were built for. This will cause the application to launch when the widget icon is touched on the touchscreen of the Android device. -
Question 273 of 350
273. Question
1 pointsWhat is the purpose of running mobile device apps in a sandbox?Correct
Incorrect
Hint
Mobile device apps are run in a sandbox that isolates them from other resources. Bypassing the phone carrier from preventing access to unauthorized apps is jailbreaking or rooting the device. -
Question 274 of 350
274. Question
1 pointsWhich built-in tool is available on a Mac OS X machine to perform disk backups?Correct
Incorrect
Hint
Time Machine is an automatic backup utility in the Mac OS. The Mac Disk Utility allows an administrator to configure disk backups. The Deja Dup tool is a tool built into the Linux OS for backing up data. Finder is similar to the Windows File Explorer tool and is used to navigate the Mac OS file system. -
Question 275 of 350
275. Question
1 pointsA user calls the help desk reporting that a laptop with Linux freezes on startup and displays kernel panic. What could cause this problem?Correct
Incorrect
Hint
A corrupted driver or failing hardware could cause kernel panic for Linux or Mac OS. The laptop will not be able to boot successfully. Either GRUB or LILO corruption or GRUB or LILO deletion would cause the stop screen to display a “Missing GRUB” or “Missing LILO” message. A resource unavailable to an application will cause the application to stop responding, but not prevent a laptop from starting up. -
Question 276 of 350
276. Question
1 pointsA user calls the help desk to report that a mobile device exhibits very slow performance. What could cause this problem?Correct
Incorrect
Hint
A power-intensive app that is running in the background could consume most of the CPU cycles and thus the device would exhibit very slow performance for other apps. If an app is not compatible with the device, the device operating system would freeze. If the operating system has encountered an error, the device will fail to respond. -
Question 277 of 350
277. Question
1 pointsWhich term describes a partition that is used to store and boot an operating system by default?Correct
Incorrect
-
Question 278 of 350
278. Question
1 pointsWhich term describes a file system that supports a partition size up to 16 exabytes?Correct
Incorrect
-
Question 279 of 350
279. Question
1 pointsWhich term describes a file system for USB flash drives that supports files larger than 4 GB?Correct
Incorrect
-
Question 280 of 350
280. Question
1 pointsWhich term describes a partition that supports up to 23 logical drives?Correct
Incorrect
-
Question 281 of 350
281. Question
1 pointsWhich term describes a file system for optical disk media?Correct
Incorrect
-
Question 282 of 350
282. Question
1 pointsWhich term describes a type of partition that would only exist on a hard disk that has an MBR?Correct
Incorrect
-
Question 283 of 350
283. Question
1 pointsWhich term describes a type of storage device that supports a partition to be extended into adjacent unallocated space as long as it is contiguous?Correct
Incorrect
-
Question 284 of 350
284. Question
1 pointsWhich term describes a general name for physical areas on a hard drive?Correct
Incorrect
-
Question 285 of 350
285. Question
1 pointsWhich term describes a partition scheme that takes a portion of disk space of 512 bytes long and that contains the boot loader?Correct
Incorrect
-
Question 286 of 350
286. Question
1 pointsWhich term describes a type of storage device that supports a volume that can span across more than one disk?Correct
Incorrect
-
Question 287 of 350
287. Question
1 pointsA technician is booting a laptop that has Windows 10 installed with 2 GB RAM. The boot process is currently working on the following step: NTOSKRNL.EXE starts the login file called WINLOGON.EXE. What is the next step that will happen in the boot process?Correct
Incorrect
-
Question 288 of 350
288. Question
1 pointsA user is booting a tablet that has Windows 10 installed. The boot process is currently working on the following step: WINLOGON.EXE displays the Windows Welcome screen What is the next step that will happen in the boot process?Correct
Incorrect
-
Question 289 of 350
289. Question
1 pointsA manager is booting a tablet that has Windows 8 installed. The boot process is currently working on the following step: POST. What is the next step that will happen in the boot process?Correct
Incorrect
-
Question 290 of 350
290. Question
1 pointsAn accountant is booting a PC that has Windows 8 installed. The boot process is currently working on the following step: BIOS locates and reads the configuration settings that are stored in the CMOS memory. What is the next step that will happen in the boot process?Correct
Incorrect
-
Question 291 of 350
291. Question
1 pointsA network analyst is booting a PC that has Windows 7 installed with 2 GB RAM. The boot process is currently working on the following step: The code in the boot sector is executed and the control of the boot process is given to Windows Boot Manager. What is the next step that will happen in the boot process?Correct
Incorrect
-
Question 292 of 350
292. Question
1 pointsAn analyst is booting a desktop that has Windows 7 installed with 4 GB RAM. The boot process is currently working on the following step: Winload uses the path specified in BOOTMGR to find the boot partition. What is the next step that will happen in the boot process?Correct
Incorrect
-
Question 293 of 350
293. Question
1 pointsA gamer is booting a desktop that has Windows 7 installed on dynamic drives. The boot process is currently working on the following step: WinLoad reads the registry files, chooses a hardware profile, and loads the device drivers. What is the next step that will happen in the boot process?Correct
Incorrect
-
Question 294 of 350
294. Question
1 pointsA technician is booting a laptop that has Windows 10 installed with 2 GB RAM. The boot process is currently working on the following step: The Windows kernel takes over the boot process. What is the next step that will happen in the boot process?Correct
Incorrect
-
Question 295 of 350
295. Question
1 pointsA user is booting a laptop that has Windows 10 installed. The boot process is currently working on the following step: WINLOGON.EXE displays the Windows Welcome screen What is the next step that will happen in the boot process?Correct
Incorrect
-
Question 296 of 350
296. Question
1 pointsA manager is booting a tablet that has Windows 8 installed. The boot process is currently working on the following step: The Windows kernel takes over the boot process. What is the next step that will happen in the boot process?Correct
Incorrect
-
Question 297 of 350
297. Question
1 pointsUsers in a company have complained about network performance. After investigation, the IT staff has determined that the attacker was using a specific technique that affected the TCP three-way handshake. What is the type of network attack?Correct
Incorrect
-
Question 298 of 350
298. Question
1 pointsUsers in a company have complained about network performance. After investigation, the IT staff has determined that the attacker is using a technique that compares hashed passwords to potential hashes the hacker has. What is the type of network attack?Correct
Incorrect
-
Question 299 of 350
299. Question
1 pointsUsers in a company have complained about network performance. After investigation, the IT staff has determined that the DNS server was sent with an enormous amount of false requests, thus overwhelming the server. What is the type of network attack?Correct
Incorrect
-
Question 300 of 350
300. Question
1 pointsUsers in a company have complained about network performance. After investigation, the IT staff has determined that the attacker is using a vulnerability that is known to the software vendor, but not patched yet. What is the type of network attack?Correct
Incorrect
-
Question 301 of 350
301. Question
1 pointsUsers in a company have complained about network performance. After investigation, the IT staff has determined that zombies were used to attack the firewall. What is the type of network attack?Correct
Incorrect
-
Question 302 of 350
302. Question
1 pointsUsers in a company have complained about network performance. After investigation, the IT staff has determined that zombies were used to attack the firewall. What is the type of network attack?Correct
Incorrect
-
Question 303 of 350
303. Question
1 pointsUsers in a company have complained about network performance. After investigation, the IT staff has determined that the attacker is using a table of words that potentially could be used as passwords. What is the type of network attack?Correct
Incorrect
-
Question 304 of 350
304. Question
1 pointsUsers in a company have complained about network performance. After investigation, the IT staff has determined that the attacker injected false records on the server that translates IP addresses to domain names. What is the type of network attack?Correct
Incorrect
-
Question 305 of 350
305. Question
1 pointsWhat is required as an additional verification mechanism on iOS mobile devices when setting up biometric screen locks, such as Touch ID or Face ID?Correct
Incorrect
-
Question 306 of 350
306. Question
1 pointsWhich situation can be prevented by creating a UEFI password?Correct
Incorrect
-
Question 307 of 350
307. Question
1 pointsA PC technician has been asked by a supervisor to recommend a security solution for a company that wants a device to monitor incoming and outgoing traffic and stop any malicious activity. Which security technique should the technician recommend?Correct
Incorrect
-
Question 308 of 350
308. Question
1 pointsA PC technician has been asked by a supervisor to recommend a security solution for a machine where the antimalware software cannot remove all of the malware. Which security technique should the technician recommend?Correct
Incorrect
-
Question 309 of 350
309. Question
1 pointsA PC technician has been asked by a supervisor to recommend a security solution for preventing tailgating. Which security technique should the technician recommend?Correct
Incorrect
-
Question 310 of 350
310. Question
1 pointsA PC technician has been asked by a supervisor to recommend a security solution for drive redundancy. Which security technique should the technician recommend?Correct
Incorrect
-
Question 311 of 350
311. Question
1 pointsA PC technician has been asked by a supervisor to recommend a security solution for phishing. Which security technique should the technician recommend?Correct
Incorrect
-
Question 312 of 350
312. Question
1 pointsA PC technician has been asked by a supervisor to recommend a security solution for protecting a computer used to log in at a dental clinic from someone using a bootable disk containing hacking tools. Which security technique should the technician recommend?Correct
Incorrect
-
Question 313 of 350
313. Question
1 pointsA PC technician has been asked by a supervisor to recommend a security solution for a manager traveling who needs access to internal corporate resources. Which security technique should the technician recommend?Correct
Incorrect
-
Question 314 of 350
314. Question
1 pointsWhy would a gamer need to use the move command?Correct
Incorrect
-
Question 315 of 350
315. Question
1 pointsWhy would a gamer need to use the copy command?Correct
Incorrect
-
Question 316 of 350
316. Question
1 pointsWhy would a university student need to use the robocopy command?Correct
Incorrect
-
Question 317 of 350
317. Question
1 pointsWhy would a university student need to use the xcopy command?Correct
Incorrect
-
Question 318 of 350
318. Question
1 pointsWhy would a technical support representative need to use the format command?Correct
Incorrect
-
Question 319 of 350
319. Question
1 pointsWhy would a technical support representative need to use the bootrec command?Correct
Incorrect
-
Question 320 of 350
320. Question
1 pointsWhy would a technical support representative need to use the ipconfig command?Correct
Incorrect
-
Question 321 of 350
321. Question
1 pointsWhy would a user need to use the netstat command?Correct
Incorrect
-
Question 322 of 350
322. Question
1 pointsWhy would a user need to use the nslookup command?Correct
Incorrect
-
Question 323 of 350
323. Question
1 pointsWhy would a manager need to use the ping command?Correct
Incorrect
-
Question 324 of 350
324. Question
1 pointsWhat are two probable causes of a user unable to access local resources such as file shares or printers on a wired network? (Choose two.)Correct
Incorrect
Hint
There are many issues which can cause local resources to be unavailable. These include bad cabling, a switch or router not functioning, a firewall blocking traffic, DNS name resolution not working, or failed services. -
Question 325 of 350
325. Question
1 pointsThe IT department has just purchased 15 wireless access points in order to provide full wireless coverage for all 100 employees within the company and is looking to deploy the most secure and scalable wireless implementation. Which open source authentication method would perform authentication on behalf of all 15 wireless network devices?Correct
Incorrect
Hint
RADIUS and TACACS+ both use a separate server that performs authentication on behalf of network devices. However, RADIUS is an open standard and provides greater compatibility. -
Question 326 of 350
326. Question
1 pointsA technician is upgrading many PCs used within the company. How should the technician dispose of an old inkjet printer cartridge?Correct
Incorrect
-
Question 327 of 350
327. Question
1 pointsA technician is about to begin preventive maintenance on a company PC. In which situation would ESD be an issue?Correct
Incorrect
-
Question 328 of 350
328. Question
1 pointsA client packet is received by a server. The packet has a destination port number of 67. What service application is the client requesting?Correct
Incorrect
-
Question 329 of 350
329. Question
1 pointsA client packet is received by a server. The packet has a destination port number of 443. What service application is the client requesting?Correct
Incorrect
-
Question 330 of 350
330. Question
1 pointsA client packet is received by a server. The packet has a destination port number of 69. What service application is the client requesting?Correct
Incorrect
-
Question 331 of 350
331. Question
1 pointsA client packet is received by a server. The packet has a destination port number of 445. What service application is the client requesting?Correct
Incorrect
-
Question 332 of 350
332. Question
1 pointsA client packet is received by a server. The packet has a destination port number of 548. What service application is the client requesting?Correct
Incorrect
-
Question 333 of 350
333. Question
1 pointsA client packet is received by a server. The packet has a destination port number of 80. What service application is the client requesting?Correct
Incorrect
-
Question 334 of 350
334. Question
1 pointsA client packet is received by a server. The packet has a destination port number of 3389. What service application is the client requesting?Correct
Incorrect
-
Question 335 of 350
335. Question
1 pointsWhy would a user need to use the gpupdate command?Correct
Incorrect
-
Question 336 of 350
336. Question
1 pointsWhich protocol is used by Windows for file and printer sharing?Correct
Incorrect
Hint
SMB (Server Message Block) is the protocol used for file and printer sharing by Windows. SMTP and IMAP are protocols used in email services. HTTPS is the protocol used for secure web browsing. -
Question 337 of 350
337. Question
1 pointsWhich laptop LCD technology uses tilting crystals to provide a much higher contrast ratio than other types?Correct
Incorrect
Hint
Vertical alignment (VA) laptop display technology uses tilting crystals to provide a much higher contrast ratio than other types. In-Plane switching (IPS) and Twisted Nematic (TN) do not have this feature. Organic light-emitting diode (OLED) displays are not used in laptops. -
Question 338 of 350
338. Question
1 pointsWhich two statements are true regarding GPT partitions? (Choose two.)Correct
Incorrect
Hint
GPT partitions are commonly used in computers with UEFI firmware. They store a backup of the partition table and can support up to 128 partitions. The maximum partition size is 9.4ZB. -
Question 339 of 350
339. Question
1 pointsA technician wishes to use the reset option to repair a Windows 10 installation and chooses the option that will retain the user’s personal files. Which statement is true based on using this option?Correct
Incorrect
Hint
By using the reset process from within the recovery area, it will remove all apps and programs, change the computer’s settings back to their defaults, and reinstall Windows 10 without removing any user personal data files. -
Question 340 of 350
340. Question
1 pointsA user is trying to execute a file using elevated permission. The user right-clicks the file, chooses Run as Administrator, and chooses Yes in the User Account Control (UAC) window. The operation fails. What is the reason?Correct
Incorrect
Hint
An administrator password is required to open or execute a file using elevated permission, or the current user must belong to the Administrator group. -
Question 341 of 350
341. Question
1 pointsWhat is a possible situation when it might be necessary to boot Windows 10 from a bootable recovery USB device?Correct
Incorrect
Hint
You can boot Windows 10 from a repair boot USB drive and repair your computer with corresponding recovery tools, such as bootrec commands. A Windows 10 repair boot USB is a bootable recovery drive made with USB. -
Question 342 of 350
342. Question
1 pointsAn accountant is booting a PC that has Windows 10 installed. The boot process is currently working on the following step: BIOS locates and reads the configuration settings that are stored in the CMOS memory. What is the next step that will happen in the boot process?Correct
Incorrect
Hint
The Windows 10 boot process is as follows: 1 . PreBoot: POST or Power-On Self-Test loads firmware settings. It checks for a valid disk system, and if the system is good to go for the next phase. If the computer has a valid MBR, i.e. Master Boot Record, the boot process moves further and loads Windows Boot Manager. 2 . Windows Boot Manager: This step determines if you have multiple OS installed on your computer. If yes, then it offers a menu with the names of the OSs. When you select the OS, it will load the right program, i.e. Winload.exe to boot you into the correct OS. 3 . Windows OS Loader: WinLoad.exe loads important drivers to kick start the Windows Kernel. The kernel uses the drivers to talk to the hardware and do rest of the things required for the boot process to continue. 4 . Windows NT OS Kernel: This is the last stage which picks up the Registry settings, additional drivers, etc. Once that has been read, the control is taken by the system manager process. It loads up the UI, the rest of the hardware and software. That’s when you finally get to see your Windows 10 Login screen. -
Question 343 of 350
343. Question
1 pointsA manager is booting a tablet that has Windows 10 installed. The boot process is currently working on the following step: The Windows kernel takes over the boot process. What is the next step that will happen in the boot process?Correct
Incorrect
Hint
The Windows 10 boot process is as follows: 1. PreBoot: POST or Power-On Self-Test loads firmware settings. It checks for a valid disk system, and if the system is good to go for the next phase. If the computer has a valid MBR, i.e. Master Boot Record, the boot process moves further and loads Windows Boot Manager. 2. Windows Boot Manager: This step determines if you have multiple OS installed on your computer. If yes, then it offers a menu with the names of the OSs. When you select the OS, it will load the right program, i.e. Winload.exe to boot you into the correct OS. 3. Windows OS Loader: WinLoad.exe loads important drivers to kick start the Windows Kernel. The kernel uses the drivers to talk to the hardware and do rest of the things required for the boot process to continue. 4. Windows NT OS Kernel: This is the last stage which picks up the Registry settings, additional drivers, etc. Once that has been read, the control is taken by the system manager process. It loads up the UI, the rest of the hardware and software. That’s when you finally get to see your Windows 10 Login screen. -
Question 344 of 350
344. Question
1 pointsAn analyst is booting a desktop that has Windows 10 installed with 4 GB RAM. The boot process is currently working on the following step: Winload uses the path specified in BOOTMGR to find the boot partition. What is the next step that will happen in the boot process?Correct
Incorrect
Hint
The Windows 10 boot process is as follows: 1. PreBoot: POST or Power-On Self-Test loads firmware settings. It checks for a valid disk system, and if the system is good to go for the next phase. If the computer has a valid MBR, i.e. Master Boot Record, the boot process moves further and loads Windows Boot Manager. 2. Windows Boot Manager: This step determines if you have multiple OS installed on your computer. If yes, then it offers a menu with the names of the OSs. When you select the OS, it will load the right program, i.e. Winload.exe to boot you into the correct OS. 3. Windows OS Loader: WinLoad.exe loads important drivers to kick start the Windows Kernel. The kernel uses the drivers to talk to the hardware and do rest of the things required for the boot process to continue. 4. Windows NT OS Kernel: This is the last stage which picks up the Registry settings, additional drivers, etc. Once that has been read, the control is taken by the system manager process. It loads up the UI, the rest of the hardware and software. That’s when you finally get to see your Windows 10 Login screen -
Question 345 of 350
345. Question
1 pointsA user notes that the username and password are automatically populated in the Microsoft Edge browser when logging into a secure site. When the user tries to log into the same site using Google Chrome, the username and password do not save automatically. Why is this occurring?Correct
Incorrect
Hint
Web credentials do not save for sites accessed by browsers other than Internet Explorer and Edge. Credentials created with other browsers must be managed from within that browser. -
Question 346 of 350
346. Question
1 pointsWhich statement is true regarding libraries in Windows 10?Correct
Incorrect
Hint
Libraries in Windows 10 allow multiple different directories to be linked together in one location. -
Question 347 of 350
347. Question
1 pointsMatch the steps that will lead to the loading of bootmgr.exe in a 32 bit Windows 10 environment.Correct
Incorrect
-
Question 348 of 350
348. Question
1 pointsSelect the Windows 10 version that best meets the described use.Correct
Incorrect
-
Question 349 of 350
349. Question
1 pointsMatch the file system with the respective description.Correct
Incorrect
-
Question 350 of 350
350. Question
1 pointsA corporation would like to use three or more factors for the password authentication policy. How can this be achieved?Correct
Incorrect
Hint
MFA (Multi-Factor Authentication) requires users to present at least two, if not more, types of authentication. 2FA (Two-Factor authentication), also sometimes referred to as 2-step verification, is a security approach requiring users to present two factors for authentication for accessing an account. SFA (Single-Factor Authentication) requires users to authenticate with only one type of evidence for authentication, usually a password. Bitlocker encrypts drives.
