12.3.1.5 Lab – Configure the Firewall in Windows 8 (Answers)
Introduction
In this lab, you will explore the Windows Firewall and configure some advanced settings.
Recommended Equipment
- Two computers directly connected or connected over the network
- Windows 8 installed on both computers
- Computers must be in the same workgroup and share the same subnet mask
Answers Note: Set the following computer configurations:
- Turn on Network Discovery is on both computers.
- Create User accounts on PC-1 and PC-2 and add them both to the Administrators group. For example: on PC-1 and PC-2 create ITEuser accounts on both PCs. Make sure to assign a password to the accounts.
- On PC-2, turn off Use Sharing Wizard (Recommended). Click Start > Computer > Tools > Folder Options > View, and then uncheck Use Sharing Wizard (Recommended) > OK.
Step 1: Create and share a folder on PC-1.
a. Log on to PC-1 as a member of the administrator group. Ask your instructor for the user name and password.
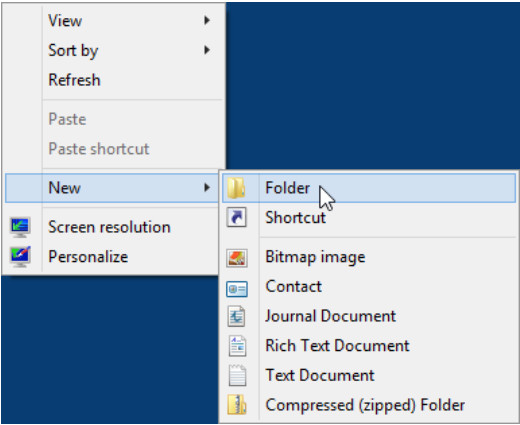
b. On PC-1, right-click the desktop, select New > Folder. Name the folder Cisco.
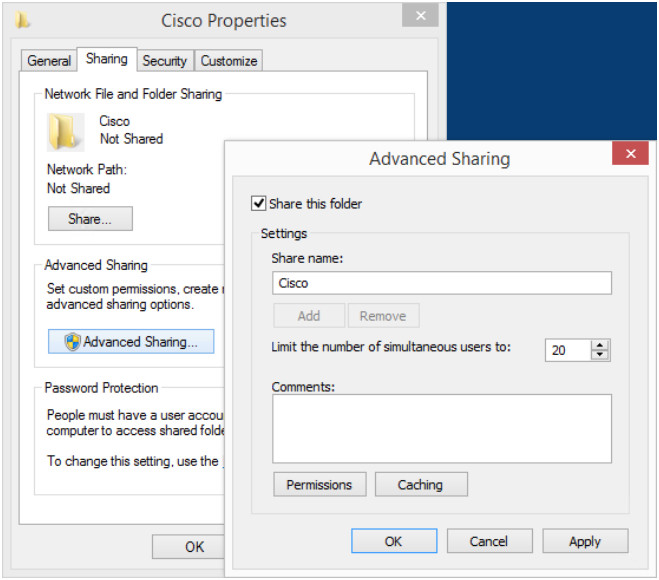
c. Right-click the Cisco folder, and then select Properties > Sharing > Advanced Sharing. The Advanced Sharing window opens. Click Share this folder and use the default name Cisco. Click OK. Close the Cisco Properties window.
Step 2: Use File Explorer to view PC-1’s shared folder.
a. Log on to PC-2 as a member of the administrator group. Ask your instructor for the user name and password.
b. Open File Explorer window. In the left pane, under Network, expand PC-1.
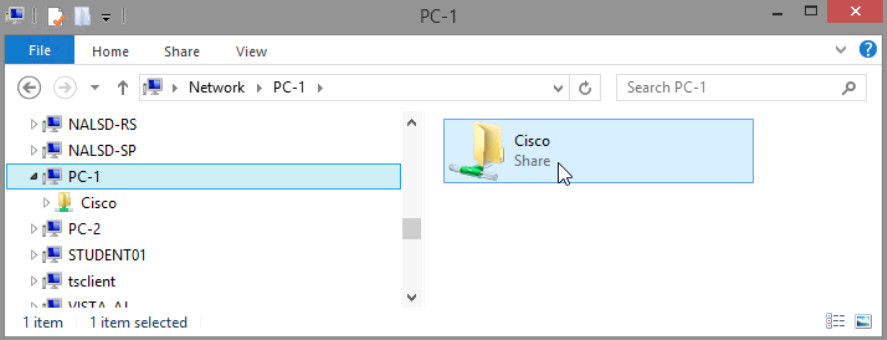
Under PC-1, Are you able to see the shared folder Cisco?
Yes
Note: If you answered no, ask the instructor for help.
c. Close File Explorer.
Step 3: Open Windows Firewall on PC-1.
Note: Use PC-1 for the rest of the lab unless otherwise stated.
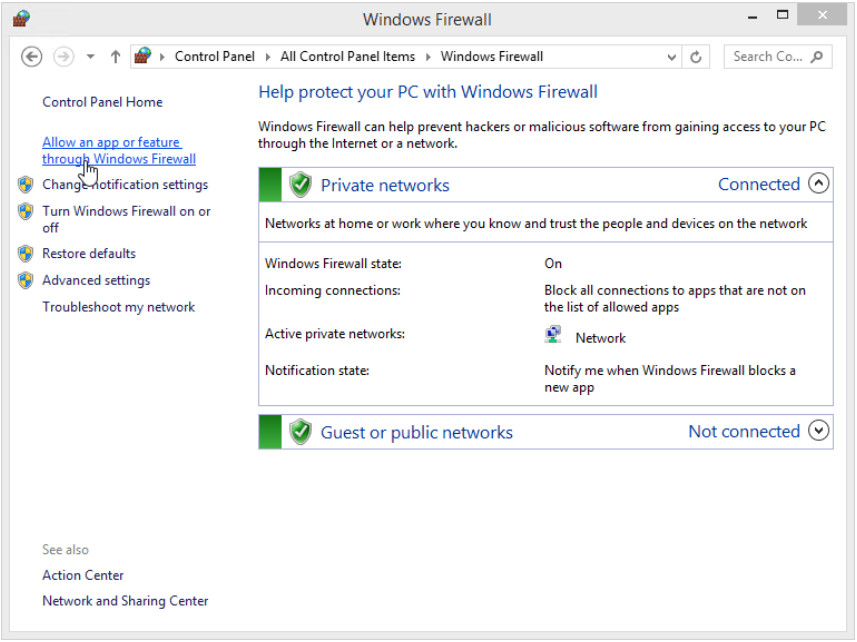
a. To open the Windows Firewall window, click Control Panel > Windows Firewall.
b. The normal state for the Windows Firewall is On.
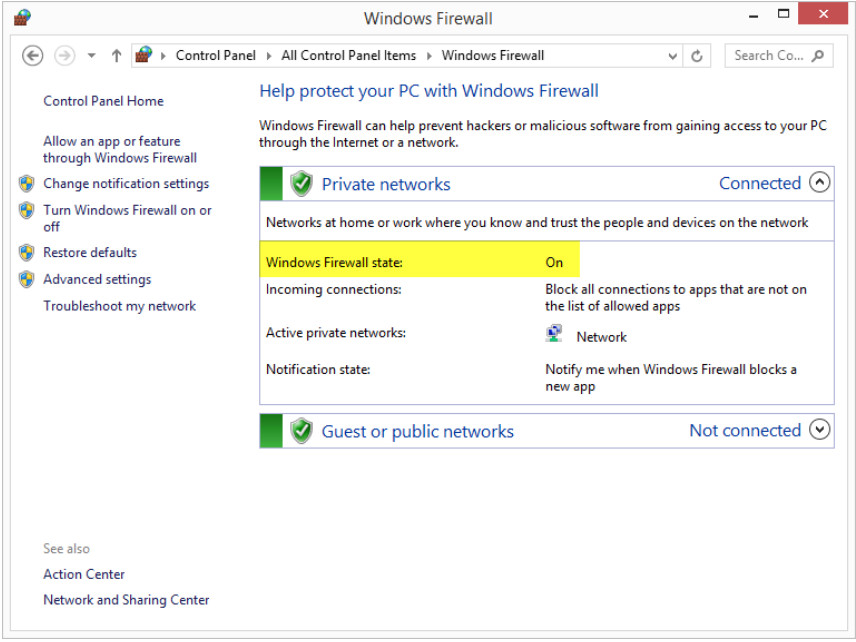
c. What are the benefits of Windows Firewall?
Windows Firewall can help prevent hackers or malicious software from gaining access to your computer through the Internet or a network.
Step 4: Investigate the Windows Firewall Allowed Programs feature.
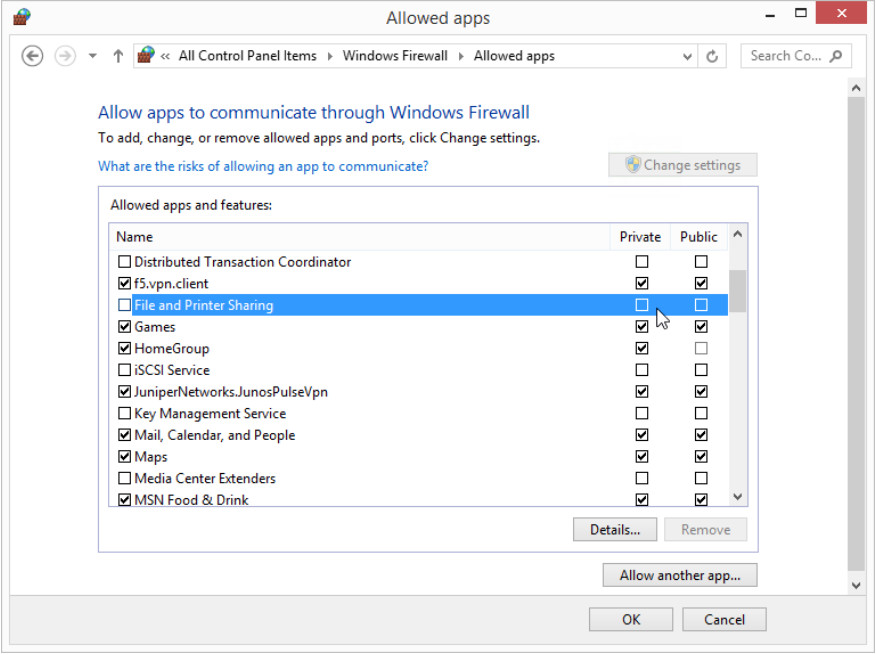
a. Click Allow an app or feature through Windows Firewall.
b. The Allowed apps window opens. Programs and services that Windows Firewall is not blocking will be listed with a check mark. Click What are the risks of allowing an app to communicate?
Note: You can add applications to this list. This may be necessary if you have an application that requires outside communications but for some reason the Windows Firewall cannot perform the configuration automatically.
Creating too many exceptions in your Programs and Services file can have negative consequences.
Describe a negative consequence of having too many exceptions.
Answers will vary. Exceptions for a program to communicate through the Windows Firewall are like opening a hole in the firewall. Attackers use software that scans the Internet looking for computers with many exceptions and open ports.
c. Close Windows Help and Support window.
Step 5: Configure the Windows Firewall Allowed apps feature.
a. Click the Allowed apps window so it is active. Click Change settings. Remove the check mark from File and Printer Sharing. Click OK.
b. On PC-2, using File Explorer, attempt to open the network connect to PC-1.
Can you connect to PC-1 and view the Cisco shared folder?
No
Did you receive an error message on PC-2? If so, what was the Error message?
Yes. Windows cannot access \\PC-1.
c. Close all open windows on PC-2.
d. On PC-1, add a check mark to File and Printer Sharing. Click OK.
Note: You should be able to add the check mark without needing to click Change settings.
e. On PC-2, re-open File Explorer and attempt to connect to PC-1.
Can you connect to computer 1? Why?
Yes, because PC-1’s File and Printer Sharing is not being blocked by the firewall any longer.
f. Close all open windows on PC-2 and Log off .
g. Close all windows on PC-1.
Step 6: Configure Advanced Security features in Windows Firewall.
Note: Use PC-1 for the rest of this lab.
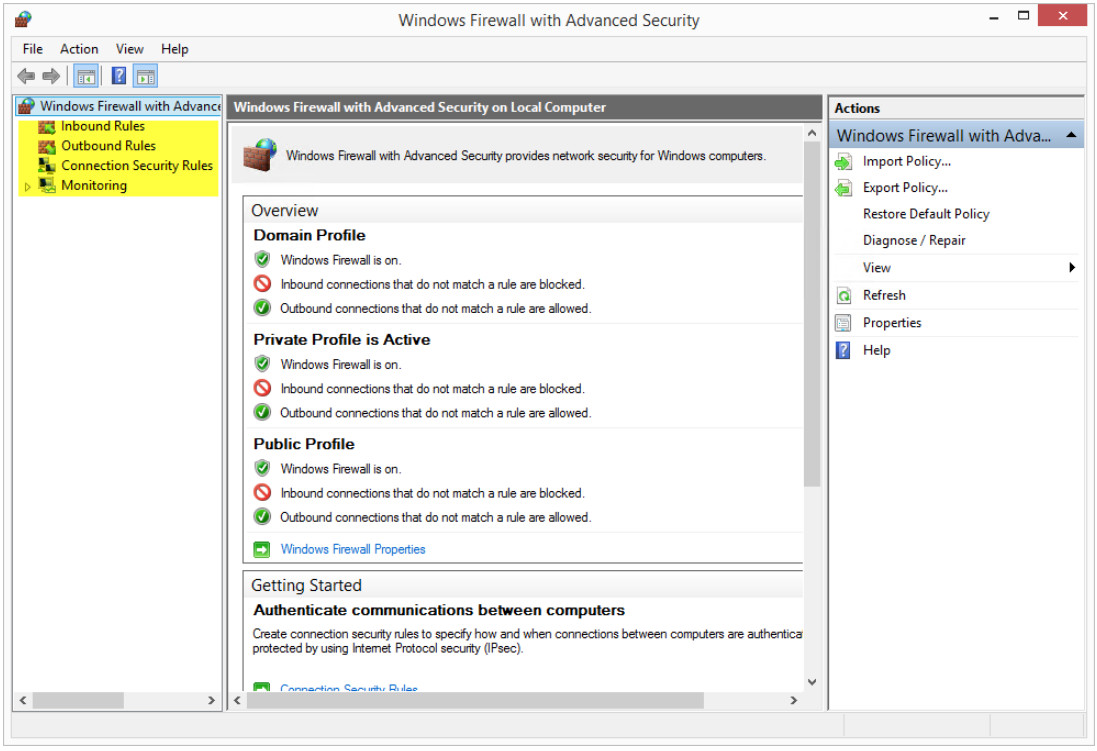
a. Click Control Panel > Administrative Tools > Windows Firewall with Advanced Security
b. The Windows Firewall with Advanced Security window opens. In the panel on the left, you can select items to configure Inbound Rules, Outbound Rules, or Connection Security Rules. You can also click Monitoring to view the status of configured rules. Click Inbound Rules.
c. In the middle panel, scroll down until you find the inbound rule named Files and Printer Sharing (Echo Request – ICMPv4-In). Right-click the rule and select Properties, then select the Advanced tab.
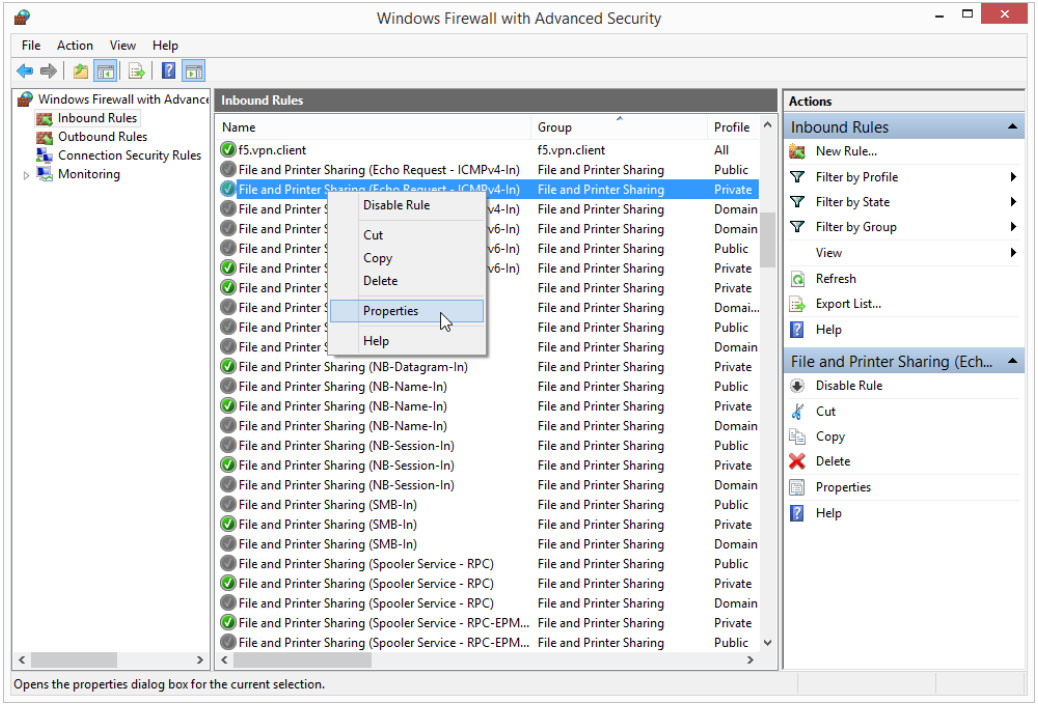
d. The Advanced tab displays the profile(s) used by the computer. Click Customize in the Interface Types area of the window.
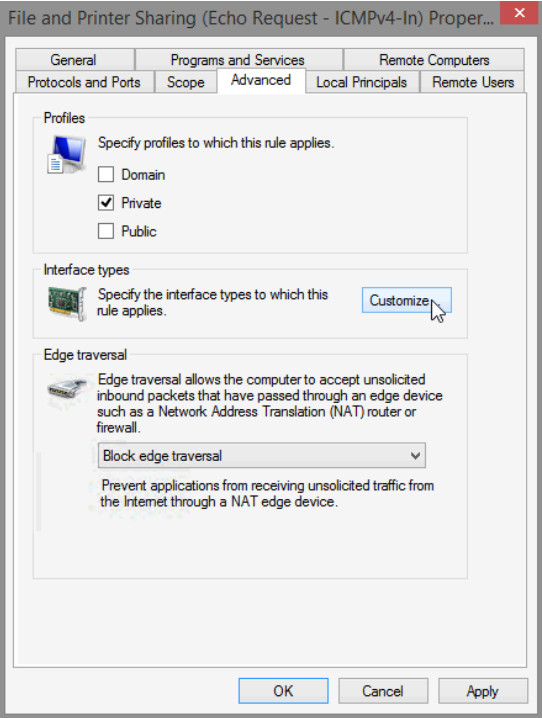
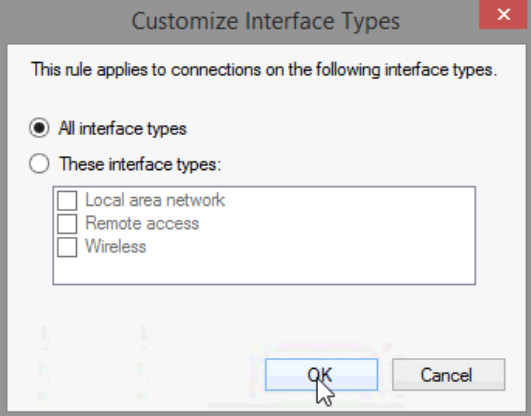
e. The Customize Interface Types window opens. It displays the different connections configured for your computer. Leave All interface types selected, then click OK.
f. Click the Programs and Services tab. In the Services section, click Settings….
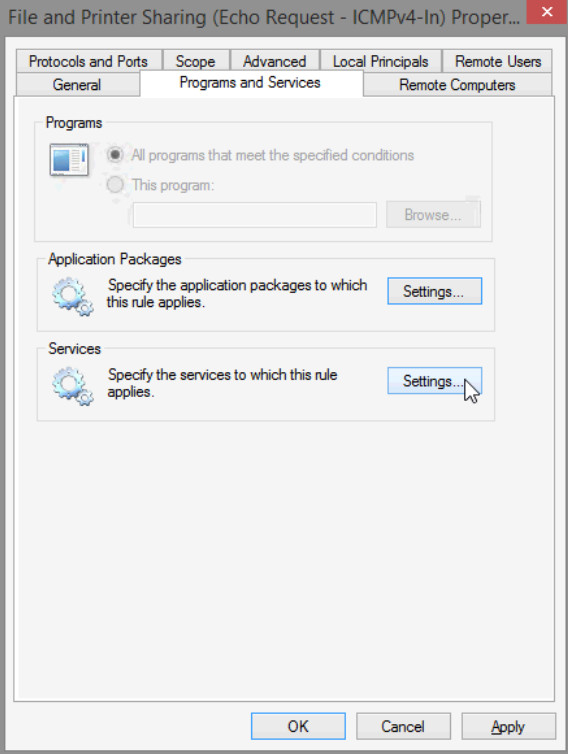
g. The Customize Service Settings window opens.
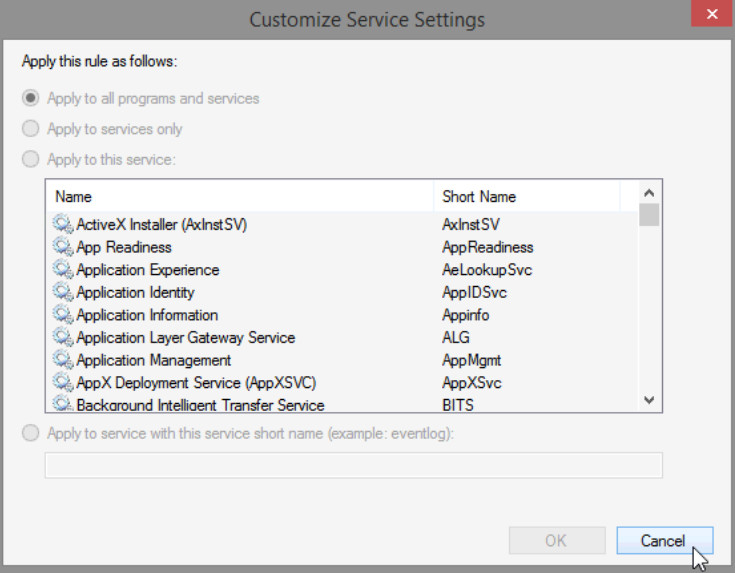
h. List the short name of four services that are available.
Answer will vary. AeLookupSvc, Appinfo, ALG, AppMgmt, etc.
i. Click Cancel to close the Customize Service Settings window.
j. Click the Protocols and Ports tab.
Note: There are many applications that users do not normally see that also need to get through the Windows Firewall to access your computer. These are the network level programs that direct traffic on the network and the Internet.
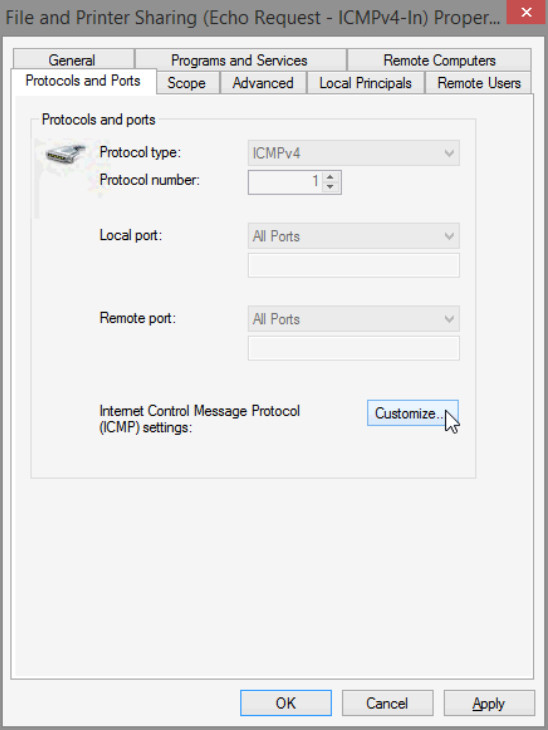
k. For the ICMP settings, click the Customize button.
l. The Customize ICMP Settings window opens. Allowing incoming echo requests is what allows network users to ping your computer to determine if it is present on the network.
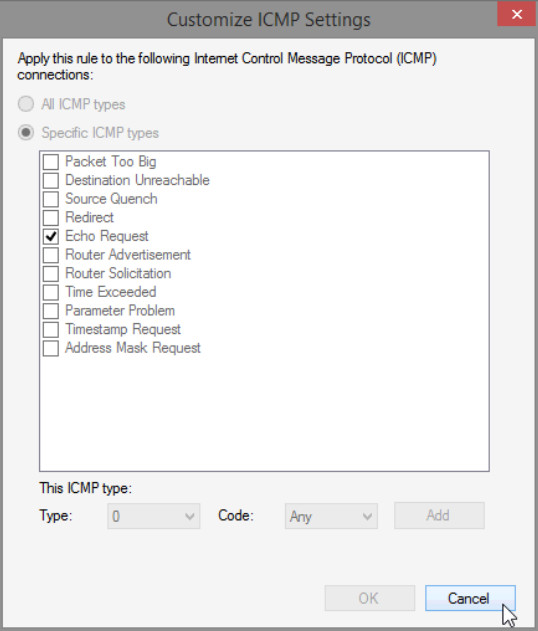
List four of the Specific ICMP types.
Answers will vary. Packet Too Big, Destination Unreachable, Source Quench, Redirect, etc.
m. Close all open windows on PC-1.
n. Right-click the Cisco folder on the Desktop, then select Delete.
Reflection
What are some possible reasons you may need to make firewall changes?
Answers will vary. By default, most apps are blocked by Windows Firewall. You may be required to make firewall changes to allow some apps to function correctly. Other times, you might need to open a specific port to get an app to function correctly. For example, to play a multiplayer game with friends online, you might need to open a port for the game to that the firewall allows the game information to reach your PC.
