1. When route redistribution is being configured from another routing protocol into EIGRP, what value is used when no seed metric is configured?
- a value equal to the minimum possible value
- a value equal to the cost of a directly connected segment
- a value equal to the maximum possible value *
- a value equal to the redistributing protocol
2. A network administrator needs to configure a router so that a path to the web server is only added to the routing table if the web server is available on port 8080. Which tool would provide this type of functionality?
- NBAR
- NetFlow
- IP SLA *
- SNMP
3. Refer to the exhibit. A network administrator has noticed that the IP SLA probe did not run as expected. What should the administrator do to correct this problem?
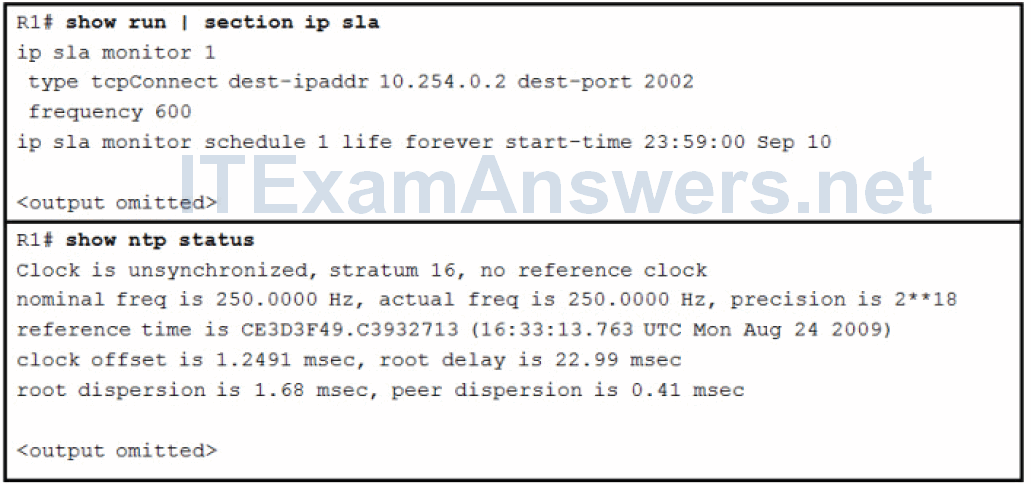
- Remove the forever keyword from the configuration.
- Adjust the clock frequency on R1.
- Configure NTP on the router to point to a different time source.*
- Configure the router as a stratum 1 time source.
4. Refer to the exhibit. A network administrator wants to loadbalance the traffic that is coming from the LAN that is attached to router R1 and going to the 10.10.10.0/24 network. The output from the routing table on R1 reveals that the traffic is flowing through router R3 only. What is the reason for this traffic behavior?
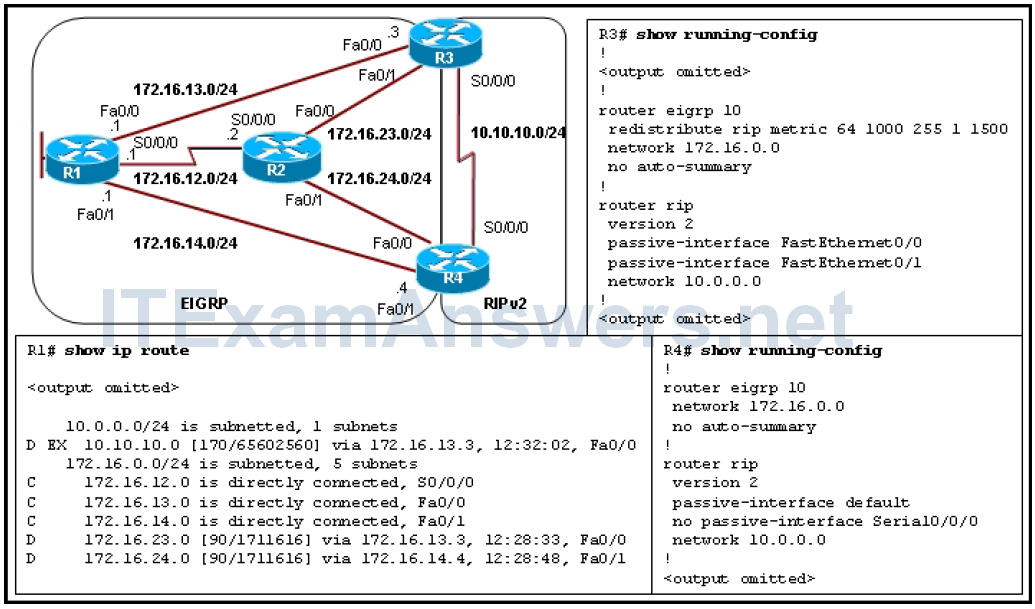
- RIP redistribution into the EIGRP routing process is not performed on R4.*
- The passive-interface default command on R4 is blocking the RIP updates that are being propagated into the EIGRP routing domain.
- EIGRP does not loadbalance automatically over equal-cost paths.
- A variance command is missing under the EIGRP configuration on R3 and R4.
- The seed metrics should be configured with the default metrics command under the EIGRP process on R3.
5. Refer to the exhibit. A network technician has just configured router East to establish a tunnel to router West. After the configuration is applied, tunnel 1 is flapping. What needs to be done to stop this flapping?
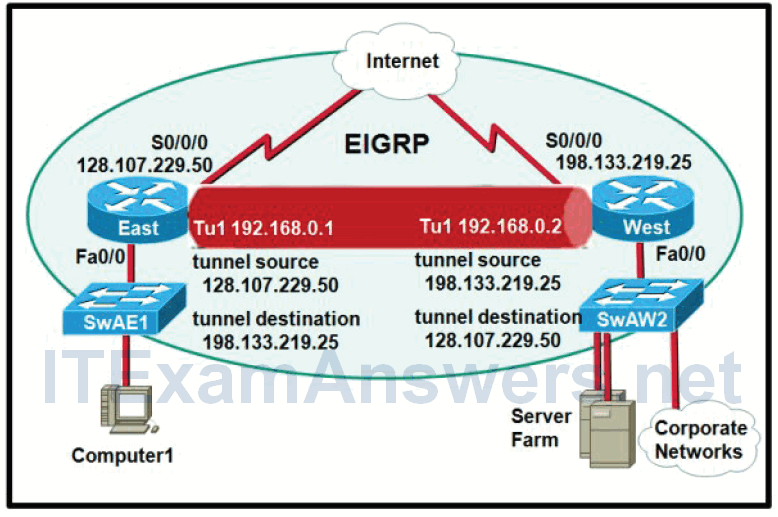
- Add a static route on router East out S0/0/0 to 198.133.219.25.*
- Set the default gateway of Computer1 to 128.107.229.50.
- Change the configuration on router East such that the destination of tunnel 1 is 192.168.0.2.
- Make tunnel 1 on router East an EIGRP passive interface.
6. Refer to the exhibit. A new system administrator is unable to obtain access to the EXEC shell. Based on the exhibited output of the debug aaa authorization command, what is the reason the administrator is unable to access the shell?
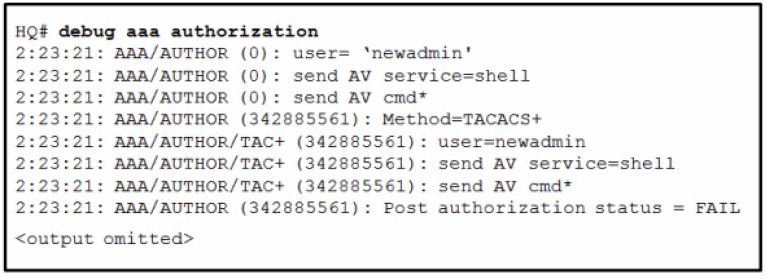
- The command has not been properly configured to require authorization.
- The user ‘newadmin’ is not authorized to perform this task.*
- The command has been entered in the wrong configuration mode.
- The TACACS+ server cannot be found.
7. Refer to the exhibit. A network administrator is attempting to connect a branch office to headquarters through a VPN tunnel. The tunnel is reported as being active at both ends, but the 10.2.2.0/24 network is not appearing in the routing table at the branch end. The administrator has determined that the problem is with the branch office configuration. Based on the output as shown, why is the 10.2.2.0/24 network not appearing in the routing table?
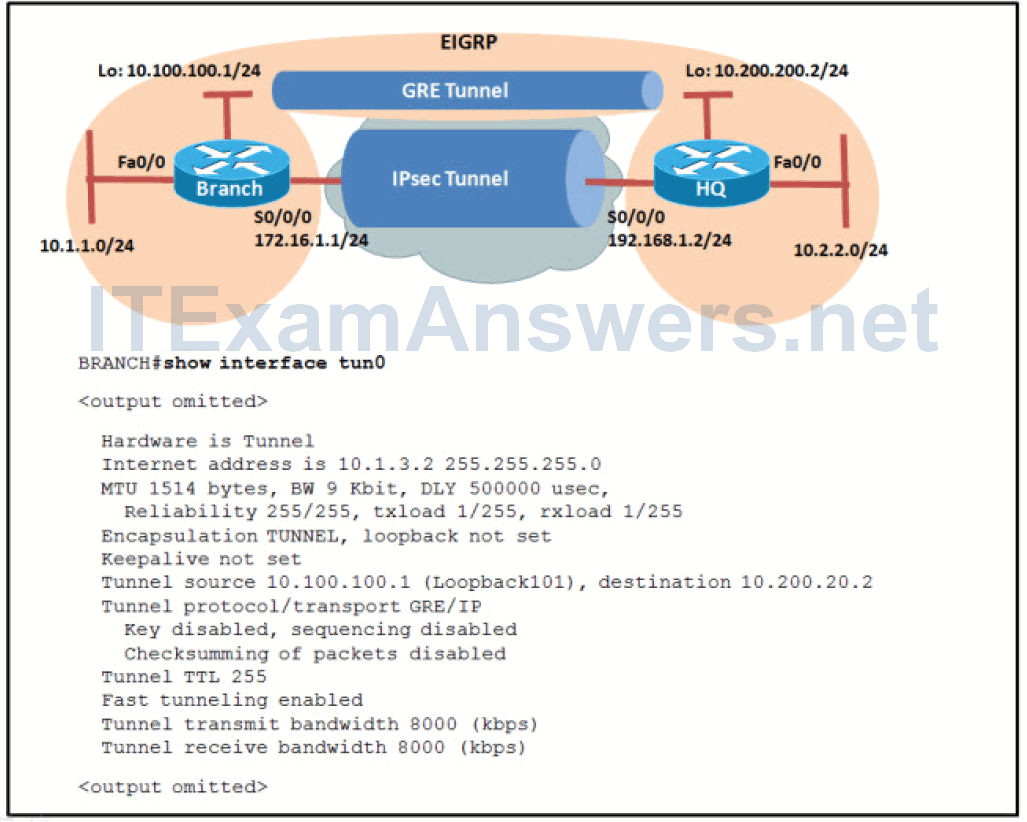
- The tunnel bandwidth is insufficient for EIGRP updates.
- The tunnel destination end point has been improperly configured.*
- The tunnel key has been improperly configured.
- The tunnel encapsulation is improperly configured.
- The tunnel protocol is improperly set.
8. Refer to the exhibit. A network administrator has recently implemented a GRE tunnel between the HQ router and a branch site. Whenever the GRE tunnel is activated, the indicated console messages are generated. Which two actions could fix this problem? (Choose two.)
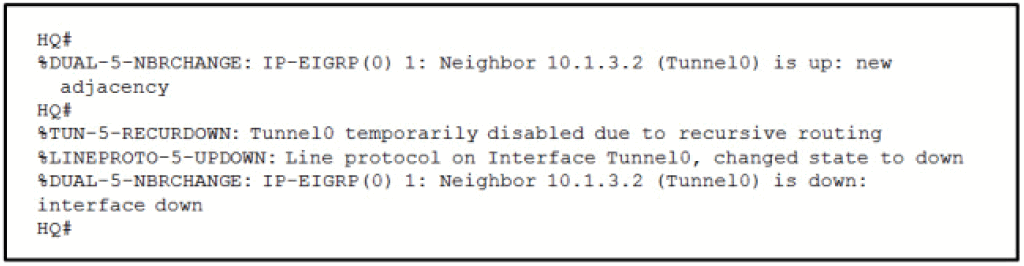
- Change the network routing protocol to OSPF.
- Apply a filter to stop EIGRP from advertising the tunnel destination through the tunnel interface.*
- Use the ip hello-interval eigrp command to increase the hello interval time.
- On both the HQ and branch routers, enter static routes to the tunnel destination that will be preferred over the one through the tunnel.*
- Use the bandwidth command to increase the bandwidth available for EIGRP updates.
9. Refer to the exhibit. Which statement about the debug radius authentication output is correct?
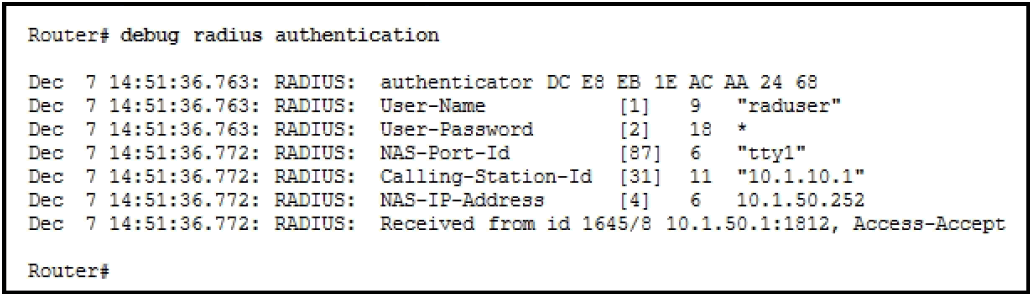
- The user raduser is on a device with the IP address of 10.1.50.1.
- The user raduser has been authenticated.*
- The IP address of the RADIUS server is 10.1.50.252.
- The RADIUS server is unreachable.
10. Refer to the exhibit. A legitimate user experienced a problem while attempting to gain access to the router EXEC shell. To investigate the situation, a network administrator issued debug tacacs and debug aaa authentication commands on the router. Based on the provided output, what could be the problem?
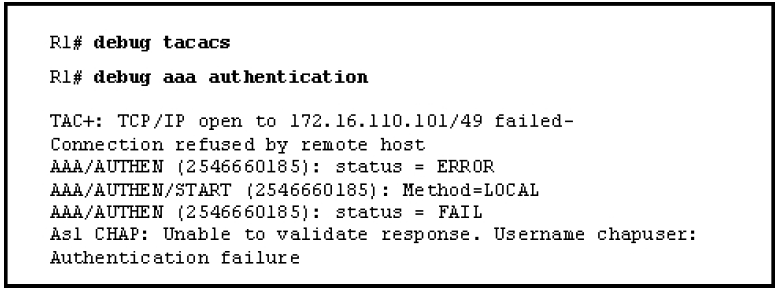
- The user credentials are rejected by the TACACS+ server.
- The user credentials stored in the local database do not match the credentials on the TACACS+ server.
- The user fails the authentication because router R1 cannot connect to the TACACS+ server.*
- The user fails the authentication because the TACAS+ server does not have a profile set up to authorize CHAP.
11. Refer to the exhibit. Based on the debug aaa authentication and debug tacacs outputs, which statement is true?
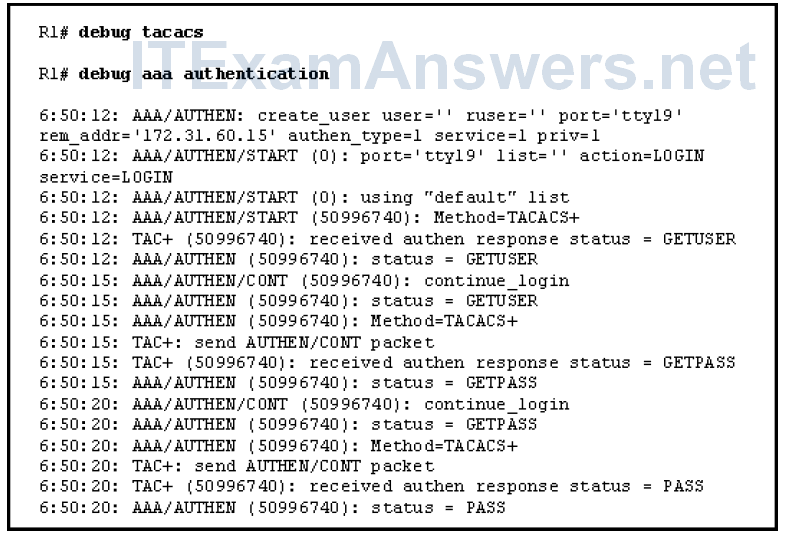
- The attempt of a remote user with the IP address 172.31.60.15 to log in to the router is unsuccessful.
- The authentication process verifies the user credentials to the local database.
- The user with the IP address 172.31.60.15 has been authorized to use privileged EXEC mode.
- The first method defined by the default authentication method list is TACACS+.*
12. Refer to the exhibit. Based on the provided debug aaa authorization and debug tacacs command output, which statement is true?
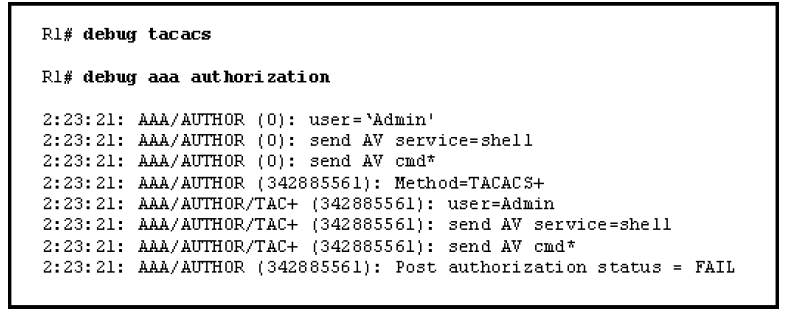
- The AAA security server has authorized the user Admin to use privilege level 15 EXEC commands.
- The authorization method used for user Admin was TACACS+.*
- The user Admin attempted to gain Telnet access to the device.
- The AAA security server authorized the user Admin to perform the requested command.
13. Which two types of information can be extracted from the output of the show ip protocols command? (Choose two.)
- reachability information
- all known networks and subnetworks
- networks used for traffic load balancing
- routing timers *
- local networks advertised by the routing protocol *
Download PDF File below:
