1. Refer to the exhibit. A network administrator used an extended ping to verify connectivity to a remote location. The ping indicated a 50 percent packet loss. What could be the cause of the problem?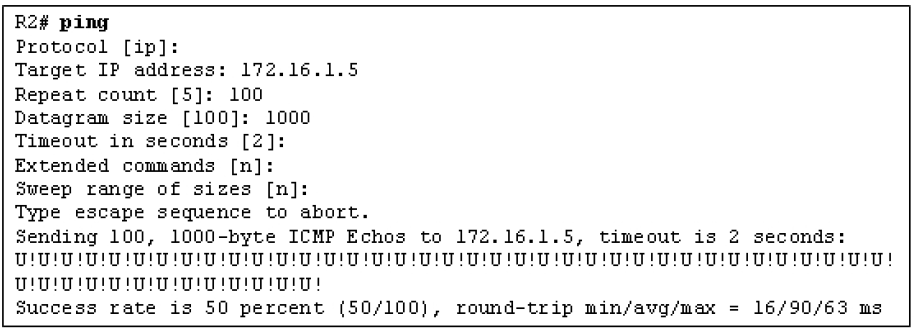
- NAT is filtering the echo reply packets.
- The packet size is exceeding the MTU.
- An ACL is blocking the echo reply packets.
- An ACL is blocking the echo request packets.
- Load balancing is occurring with packet loss on one path.*
2. Refer to the exhibit. A network administrator uses ping commands to verify connectivity to the remote 172.16.1.0/24 network . On the basis of the exhibited output, what could be a possible cause for the failure of the second ping?
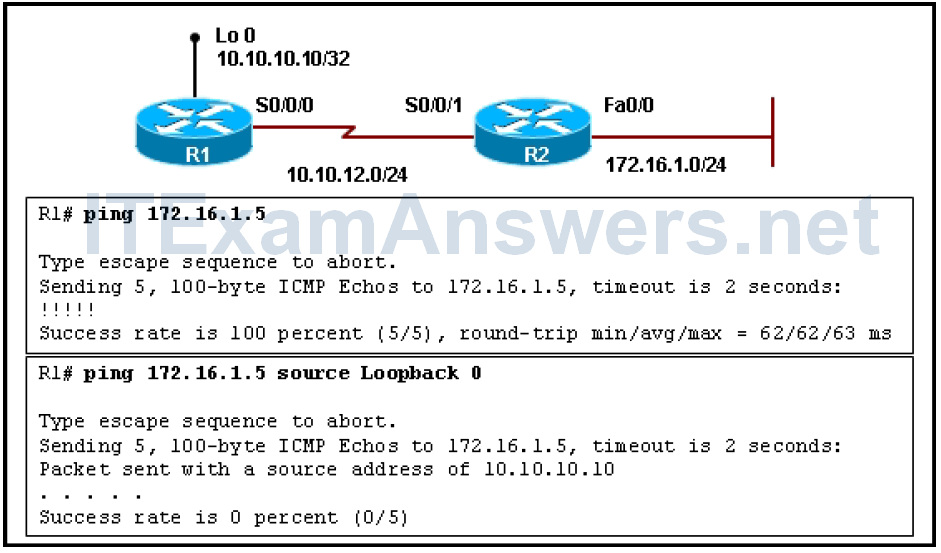
- The destination 172.16.1.0/24 network is unreachable.
- An ACL blocks all TCP traffic along the path to network 172.16.1.0/24.
- R2 does not have a return path to the source address that is used in the second ping.*
- An ACL blocks all ICMP traffic from 172.16.1.0/24 to all connected networks to R1.
3. Refer to the exhibit. What conclusion can be drawn from the exhibited output?
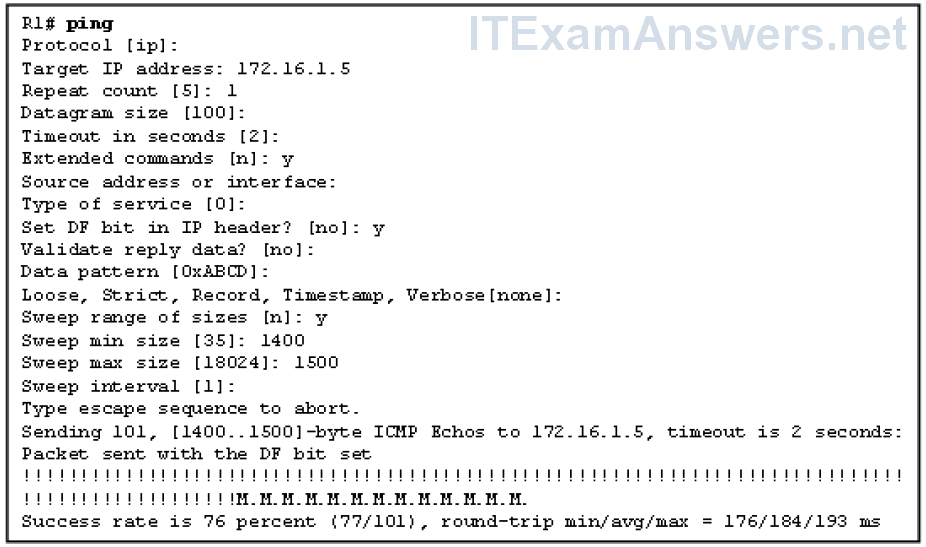
- The last host along the path is unreachable.
- Only the last 24 packets are sent with the DF bit set.
- The destination network became unreachable after two seconds.
- An interface on a device along the path cannot accommodate the larger packets.*
4. Refer to the exhibit. An administrator issues the show interfaces serial2/0 command. What are two possible causes of an increase in the number of input errors? (Choose two.)
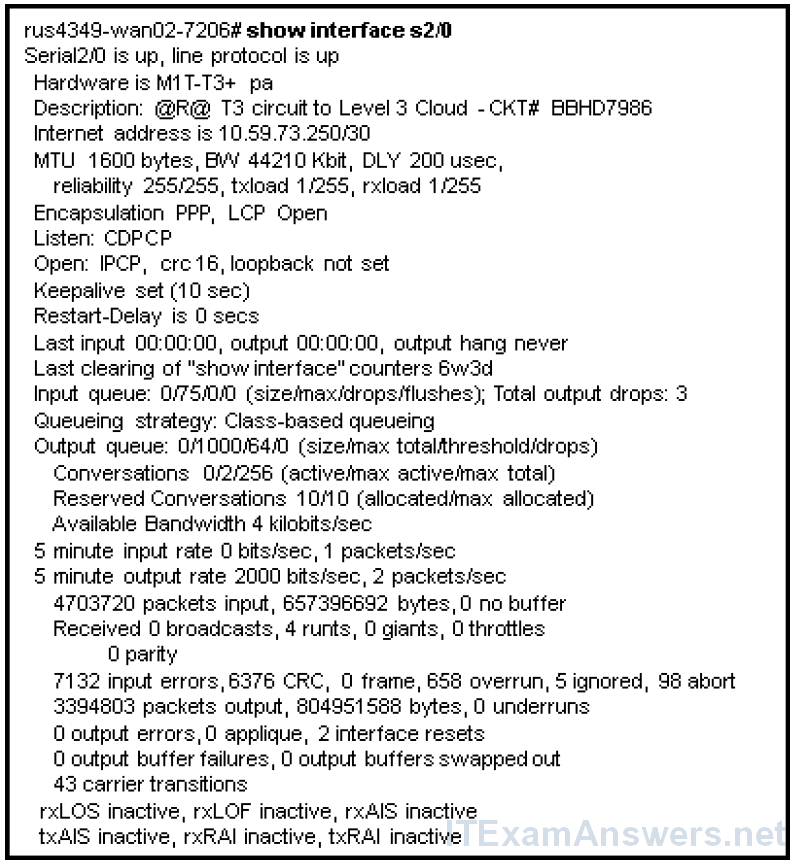
- There could be Layer 3 addressing problems.
- There could be a problem with the cabling.*
- The router hardware could be defective.*
- There is an incorrectly configured encapsulation on the interface.
5. Which two symptoms would the show processes cpu command be helpful in troubleshooting? (Choose two.)
- no link lights
- failed Telnet sessions to router *
- output queue drops
- input queue drops *
- excessive collisions
6. The administrator would like to see the commands that are associated with the serial1/0 interface. The administrator enters the command show running-config | section interface serial1/0 but does not receive a response. What could be the problem?
- The interface is down.
- The interface does not have any commands associated with it.
- The interface serial1/0 keyword looks for an exact match and should specify interface Serial1/0.*
- The administrator should have entered the command show run | i interface serial1/0.
7. The command show ip cef displays the contents of which table?
- Address Resolution Protocol (ARP)
- IP routing
- Forwarding Information Base (FIB)*
- adjacency
- Routing Information Base (RIB)
8. About which process can detailed information be found from the output of the show platform forward command on the Catalyst 3560, 3750, and 4500 platforms?
- errors
- forwarding *
- counters
- buffering
- queuing
9. What is common between Layer 3 switches and routers?
- the supported features
- the packet forwarding processes
- the Layer 2 protocols on the interfaces
- the commands for troubleshooting the control plane*
10. An attacker has started a program that fills the MAC address table of the local switch with false information. What will happen to an inbound frame when the switch MAC address table is full and does not contain information about the destination MAC address?
- The inbound frame will be dropped.
- The frame will be flooded out all ports except the one on which it is received.*
- The source MAC address will be added to the MAC address table, displacing the oldest entry.
- The MAC address table will be immediately flushed and the source MAC address entered in the table.
- The inbound frame will be buffered until an entry in the MAC address table times out and is replaced with the source MAC address of the frame.
11. What is one of the first indications that spanning tree has failed and a broadcast storm may be underway?
- Access ports move into blocking state.
- All 802.1Q trunks shut down unexpectedly.
- MAC address tables rapidly fill and prevent data frame forwarding.
- Routers or Layer 3 switches run at a very high CPU utilization load.*
12. A network administrator received several complaints from end users that they are unable to access any resources on the Layer 2 switched network. The administrator unplugs one of the redundant links that is running to the affected area of the network, and the users report that the problem disappears. When the cable is reconnected, the problem reappears. What is the most likely cause of the problem?
- The network cable is faulty.
- The immediately upstream switch is faulty.
- Spanning tree has failed or has been disabled.*
- The link cable is connected to an incorrect VLAN.
- The switch port is improperly configured as an access port.
13. A network administrator issued the show ip cef command to verify the routing operations on the device. Which table entries will be present in the output?
- the topology table entries
- the routing table entries
- the Routing Information Base (RIB) entries
- the Forwarding Information Base (FIB) entries *
14. Refer to the exhibit. A network administrator uses the output of the show ip cef exact-route command to verify the routing operations. Which statement represents the information that the network administrator will gather from the output?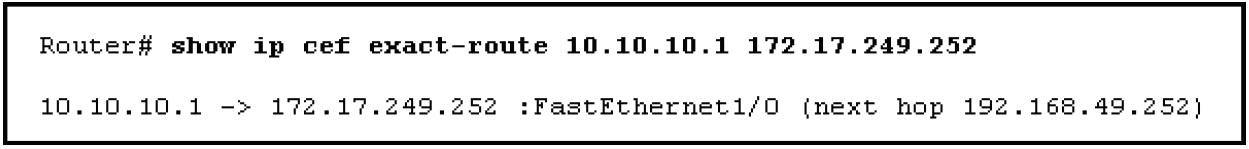
- Traffic that is sourced from 172.17.249.252 will use 192.168.49.252 as a next hop.
- The destination 172.17.249.252 can be reached via the next hop address 10.10.10.1.
- The destination 10.10.10.1 can be reached via the next hop address 172.17.249.252.
- Traffic that is sourced from 10.10.10.1 and destined to 172.17.249.252 will go out the FastEthernet1/0 interface.*
15. Refer to the exhibit. A network administrator first issued the show ip route command and then decided to filter the output of the routing table via the show ip route 128.0.0.0 128.0.0.0 longer-prefixes command. Which prefixes will be displayed in the output?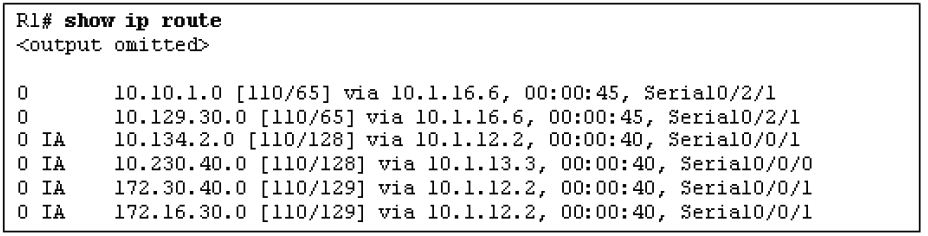
- all IP prefixes
- IP prefixes 10.10.1.0 and 10.134.2.0
- IP prefixes 172.16.30.0 and 172.30.40.0 *
- IP prefixes 10.10.1.0, 10.129.30.0, 10.134.2.0, and 10.230.40.0
16. Which data structure provides the best information when troubleshooting problems that are related to the data plane?
- the routing table
- the adjacency table
- the Routing Information Base (RIB) table
- the Forwarding Information Base (FIB) table *
17. What occurs immediately following the encapsulation of data into IP packets during the transmission of data between source and destination hosts?
- The source host sends the packet to the default gateway address.
- An ARP request is made to determine the MAC address of the destination host.
- The source host determines if the destination network is the same or different from its own local subnet.*
- The sending host encapsulates the data into a frame addressed to the MAC address of the destination host.
- The routing table is consulted to determine which interface to forward the packet through based on the longest prefix match.
18. Which two events happen when the Time to Live (TTL) field in the IP header of a packet is reduced to zero? (Choose two.)
- The packet is discarded.*
- The packet is returned to the source device.
- The packet is flooded out all active interfaces.
- The packet is forwarded to the next hop IP address.
- An ICMP “time exceeded” message is sent to the source.*
- The ARP process is invoked to determine where to forward the packet.
19. Which two data structures are used by Cisco Express Forwarding to improve the performance of IP packet switching processes on routers? (Choose two.)
- adjacency table *
- Forwarding Information Base *
- interface table
- neighbor table
- routing table
- topology table
20. A network administrator wishes to use debug commands to observe how a router processes each individual packet on an interface. Which packet switching solution should be implemented on the interface to accomplish this task?
- Enable Cisco Express Forwarding (CEF) using the ip cef comand.
- Enable Cisco Express Forwarding (CEF) using the no ip cef command.
- Enable fast switching using the ip route-cache command.
- Enable fast switching using the no ip route-cache command.
- Enable process switching using the ip route-cache command.
- Enable process switching using the no ip route-cache command.*
21. Refer to the exhibit. A network administrator issues a ping command as shown. What could be the reason for the failure of the ping to host 172.16.1.5?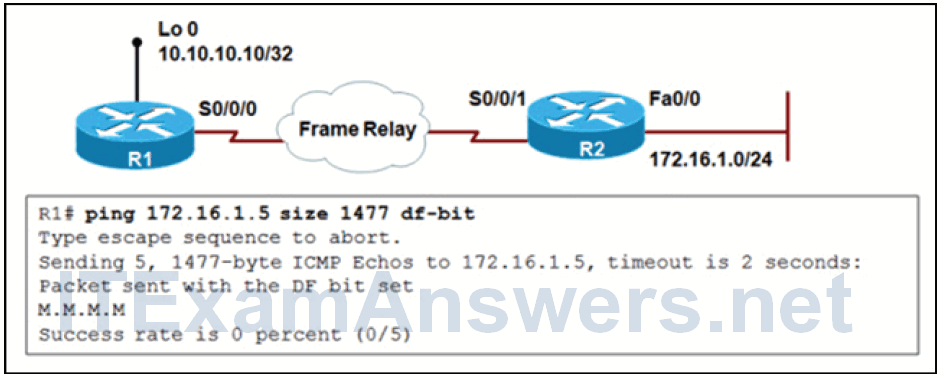
- Host 172.16.1.5 is not reachable.
- Ping packets are being blocked by an ACL somewhere along the path to 172.16.1.5.
- Packets with the DF bit set cannot be transported over a Frame Relay network.
- An interface of the device along the path to the destination cannot accommodate the large packets.*
22. Refer to the exhibit. A network administrator is testing connectivity to a remote host. Based on the command output, what conclusion can be made?
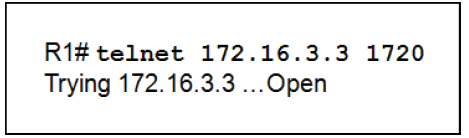
- A problem exists with Layer 3 connectivity.
- A connection can be established to all TCP ports on the remote host.
- The Open response on R1 indicates that the port (application) is active.*
- A Telnet connection to the specified host port is unsuccessful.
23. A network administrator has just issued this command:
R1# debug ip packet 5 detail
Why would the network administrator issue the debug ip packet 5 detail command?
- to limit the output to five lines
- to limit the output to every fifth packet and include all details that are associated with the packet
- to limit output to packets that are matched by an ACL *
- to increase the amount of given output to include the first five fields of the IP header
- to increase the amount of given output by including more detailed information
24. A newly established branch office is reporting connectivity issues with the server farm that is located at the main office. The network administrator suggests that the problem could be with the path MTU. How could the network administrator verify that this is the problem?
- Consult the network documentation to determine the MTU.
- Use the traceroute command to determine where packets are being lost.
- Adjust the MTU parameter on the router in the server farm to determine the acceptable path MTU.
- Use the extended ping option to send packets of increasing size to the destination to determine the path MTU.*
Download PDF File below:
