CCNPv8 ENCOR (Version 8.0) – Wireless Security and Connectivity Exam
1. Which term describes the role of a Cisco switch in the 802.1X port-based access control?
- authentication server
- authenticator
- supplicant
- agent
2. What method of wireless authentication is dependent on a RADIUS authentication server?
- WPA2 Enterprise
- WPA Personal
- WEP
- WPA2 Personal
3. Which wireless encryption method is the most secure?
- WPA2 with AES
- WEP
- WPA2 with TKIP
- WPA
4. A network administrator is configuring a RADIUS server connection on a Cisco 3500 series WLC. The configuration requires a shared secret password. What is the purpose for the shared secret password?
- It is used to authenticate and encrypt user data on the WLAN.
- It allows users to authenticate and access the WLAN.
- It is used by the RADIUS server to authenticate WLAN users.
- It is used to encrypt the messages between the WLC and the RADIUS server.
5. Which WLAN security protocol avoids attacks by strengthening the key exchange between clients and APs using a method known as Simultaneous Authentication of Equals?
- WEP
- WPA3-Personal
- WPA-Personal
- WPA2-Personal
6. Which configuration is supported as the authentication server for implementation of 802.1X on Cisco devices?
- TACACS+ security system with EAP extensions
- RADIUS security system with EAP extensions
- RADIUS security system with 3DES extensions
- TACACS+ security system
7. A network administrator of a small advertising company is configuring WLAN security on a Cisco WLC. The administrator decides to use the WPA2 PSK authentication method. On which OSI layer does WPA2 PSK provide security?
- Layer 1
- Layer 2
- Layer 3
- Layer 7
8. Which WLAN security measure requires a special backend authentication server?
- EAP
- WPA
- WEP
- pre-shared key
9. What advantage does WPA2 have over WPA?
- WPA2 uses a 32-bit WEP key for encryption.
- WPA2 allows the caching of key information.
- WPA2 uses static key management.
- WPA2 uses AES instead of TKIP.
10. Match the wireless security settings to the description. (Not all options are used.)
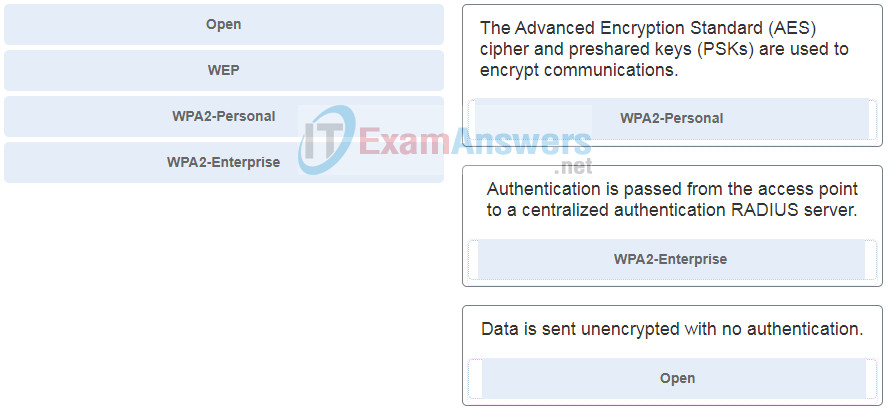
- WPA2-Personal – The Advanced Encryption Standard (AES) cipher and preshared keys (PSKs) are used to encrypt communications.
- WPA2-Enterprise – Authentication is passed from the access point to a centralized authentication RADIUS server.
- Open – Data is sent unencrypted with no authentication.
11. A network administrator of a small advertising company is configuring WLAN security by using the WPA2 PSK method. Which credential do office users need in order to connect their laptops to the WLAN?
- the company username and password through Active Directory service
- a user passphrase
- a key that matches the key on the AP
- a username and password configured on the AP
12. A network administrator is configuring a WLAN with WPA2 Enterprise on a Cisco 3500 series WLC. Client authentications will be handled by a RADIUS server. Which tab should the administrator use to add the RADIUS server information?
- SECURITY
- WLANs
- WIRELESS
- MANAGEMENT
13. Which situation is an example of EAP deployment?
- when both the AP and client are configured with the same key or secret word for authentication by the AP
- when a wireless client sends its MAC address to the AP for authentication after being validated by the internal database of the AP
- when unauthenticated clients associate with the AP
- when a client communicates with a RADIUS server for authenticated access to the network through the AP
14. Which three statements concerning wireless network security are accurate? (Choose three.)
- A wireless client first associates with an AP and then authenticates for network access.
- WPA2-Personal prevents attackers from being able to use a key to unencrypt data that was already transmitted over the air.
- Every device using the WLAN must be configured with an identical pre-shared key, unless PSK with ISE is used.
- WPA versions use a three-way handshake procedure to exchange a pre-shared key between a client and an AP.
- Open authentication uses no client or AP verification.
- WPA1, WPA2, and WPA3 support both PSK or 802.1x client authentication modes.
15. A network administrator is configuring security for new WLANs on a Cisco WLC. Which client authentication mode should the administrator use for a large scale deployment?
- WPA2
- 802.1x
- 802.11
- AES
16. A network administrator is adding a new WLAN with Open Authentication on a Cisco 3500 series WLC. Which tab should the administrator use to create it?
- General
- QoS
- Security
- Advanced
17. A recently hired network engineer is new to the Cisco lightweight APs that the company uses. Which tool should the engineer use for managing and monitoring the wireless network?
- debug output from the lightweight AP prompt
- Layer 2 switch configuration for the switches to which the APs connect
- WLC GUI
- Wireshark
18. A network technician has received complaints from users in a particular area. Upon investigation, the technician notices a poor air quality value for the AP in that area. Which WLC GUI tab should the technician use next to determine if there are any neighbor or rogue APs interfering with the one AP?
- EVENT LOG
- TOOLS
- RF TROUBLESHOOT
- CLIENTS
19. Users are complaining about the wireless connectivity in a particular area for a company that uses lightweight APs and wireless LAN controllers. The technician that handles the wireless networks notices that the particular AP has a poor air quality value. The technician uses the CLEAN AIR tab to further investigate and notices that there is an active interferer listed that has a duty cycle of 100%. What should the technician do next?
- Reboot the AP.
- Track down the offending device that is using the particular frequency causing the interference.
- Use the EVENT LOG tab to monitor clients as they attempt to join the wireless network.
- Use a different VLAN for that particular AP.
20. A company uses lightweight APs. Which criterion must be in place before an AP can successfully accept clients for a particular WLAN?
- The AP must be physically connected to the WLC.
- The AP must have wireless connectivity with a distribution layer switch.
- The AP must have connectivity to an access layer switch.
- The AP must have wireless connectivity with an AAA server.
21. In addition to signal-to-noise ratio, what is used by a Cisco wireless LAN controller to determine which AP will respond to a client request to associate?
- security protocol
- LAP
- client MAC
- WEP version
- RSSI
22. What are two common issues that could cause a specific user to have problems when trying to connect to the wireless network within a company that uses lightweight APs? (Choose two.)
- interference from cellular carriers
- AP to WLC connectivity
- distance from the AP
- authentication
- interference from FM radio stations
23. What is the function provided by CAPWAP protocol in a corporate wireless network?
- CAPWAP provides connectivity between an access point using IPv6 addressing and a wireless client using IPv4 addressing.
- CAPWAP provides the encryption of wireless user traffic between an access point and a wireless client.
- CAPWAP provides the encapsulation and forwarding of wireless user traffic between an access point and a wireless LAN controller.
- CAPWAP creates a tunnel on Transmission Control Protocol (TCP) ports in order to allow a WLC to configure an autonomous access point.
24. Several users from the same area cannot connect to the wireless network. The company uses lightweight APs and WLCs. What is one of the first things that the technician should check?
- client authentication
- authentication server issues
- sources of RF interference
- the AP
25. A network engineer is working with a user to troubleshoot connectivity of a laptop to a lightweight AP. The user has rebooted the laptop, and the network engineer is checking the connection status of the client from the WLC GUI. The client connection status dot is showing black on the DHCP step, just as it did before the reboot. What can the network engineer learn from this output?
- The DHCP server is down.
- The laptop has successfully received IP addressing information or has been statically configured.
- The WLC controller has not received client IP addressing information from the DHCP server.
- The switch to which the AP connects needs an IP helper address configured.
- The client is configured for a static IP address.
26. A network administrator is configuring a WLC to provide WLAN access to users in an office building. When testing the newly created WLAN, the administrator does not see the SSID from a wireless device. What is a possible cause?
- The APs have not been configured for the new WLAN.
- The new WLAN needs to be enabled.
- The RADIUS server is not operational.
- The WLAN security setting is incorrect.
27. A network technician is checking the status of a live AP on the WLC. On the Access Point View screen, the technician notices that the AP is using channel 11 and the channel utilization is 35%. However, the technician notices that there is no wireless client associated with the AP. What is a possible explanation for the channel utilization?
- The CAPWAP tunnel between the AP and the WLC is down.
- Nearby APs and clients are also using channel 11.
- The AP is operating in FlexConnect mode.
- The radio has malfunctioned and is preventing clients from association to the AP.
28. A network technician is checking the status of a live AP on the WLC. On the Access Point View screen, the technician notices that the AP is using channel 11 and the noise level is -30 dBm. Which conclusion can be drawn with the information?
- The radio is malfunctioning.
- Too many wireless clients are connected to the AP.
- There are some non-802.11 devices around that interfere with the WLAN signal.
- Wireless clients are transmitting a large amount of media data through the AP.
29. Users report that accesses to the wireless network inside a meeting room are not successful even after repeated attempts. A network technician verifies that the meeting room space is served by a lightweight AP and the radio is working. What is a likely cause of the problem?
- The AP is operating in FlexConnect mode.
- The AP has lost connectivity to the WLC.
- The radio signal is too weak.
- Too many users are trying to connect to the AP.
30. A network administrator opens the Client View screen on the WLC to review the performance data of a wireless client. The administrator notices that the client has a connection score value of 78%. What can the administrator conclude from this information?
- The client has a received signal strength of 78% at the AP.
- The client is using its wireless connection only 78% of the time.
- The client is currently using a data rate that is 78% of its maximum capability.
- The client is currently in the bottom 78% of all wireless clients in data usage.
31. A network administrator receives a complaint from a laptop user of slow web accesses through the wireless network. The administrator reviews the information in the Client View screen of the WLC and finds that the connection speed of the client is 30 Mbps and it has a connection score of 21%. What is likely the problem?
- Other APs on the network are over utilizing the channel.
- The AP has a defective radio.
- There are too many wireless users on the network.
- The client is too far from the AP.
32. A network administrator of a college is configuring WLAN security with WPA2 Enterprise authentication. Which server is required when deploying this type of authentication?
- AAA
- DHCP
- RADIUS
- SNMP
33. Which two hybrid modes can cause compatibility issues when configured on a WLAN controller? (Choose two.)
- WPA with AES
- WPA3 with CCMK
- WPA2 with CCMK
- WPA2 with AES
- WPA2 with TKIP

Which two hybrid modes can cause compatibility issues when configured on a WLAN controller? (Choose two.)
Added, many thanks for your sharing!