Assessment – ROUTE Chapter 7 – CCNP ROUTE (Version 6.0) Exam Answers
1. Refer to the exhibit. A network administrator has configured a GRE tunnel between R1 and R2 as shown. After completing the tunnel configurations, the administrator notices that the tunnel interfaces on both routers are down. All other interfaces are up and the pings through the ISP to the serial interface of each router are successful. What is the cause of the problem?
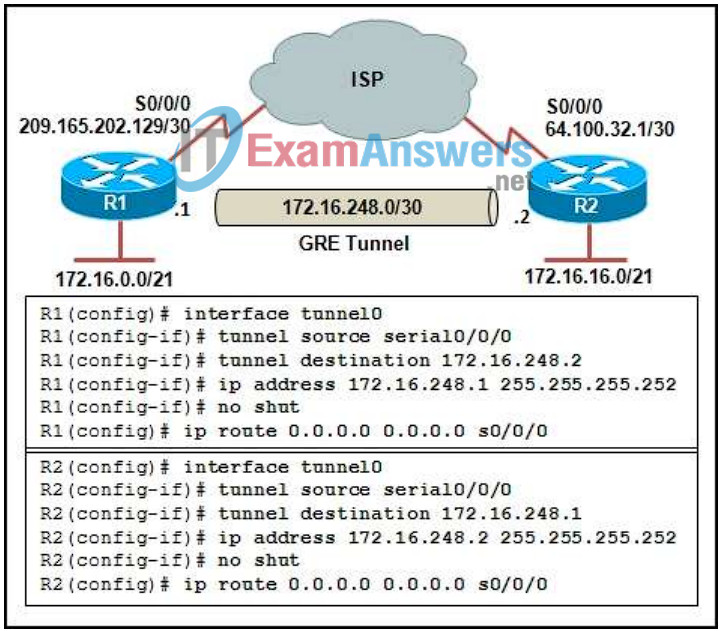
- Tunnel source configurations are incorrect.
- Tunnel destination configurations are incorrect.
- The MTU size has not been increased to 1492.
- GRE IP encapsulation has not been configured.
2. Which three protocols are involved in the establishment of an IPsec VPN tunnel? (Choose three.)
- Tunnel Profile (TCP port 604)
- Authentication Header (protocol 51)
- Generic Routing Encapsulation (protocol 47)
- Encapsulating Security Protocol (protocol 50)
- Internet Security Association and Key Management Protocol (TCP port 500)
- Internet Security Association and Key Management Protocol (UDP port 500)
3. Refer to the exhibit. Based on the partial configuration that is shown, which static route would be the primary default path?
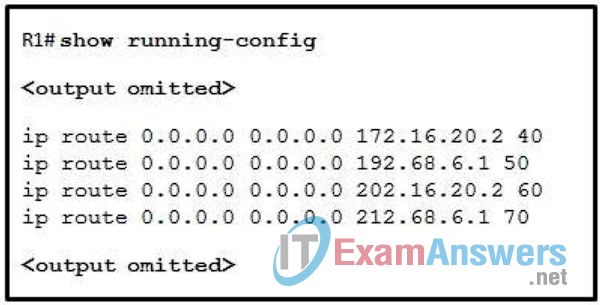
- ip route 0.0.0.0 0.0.0.0 172.16.20.2 40
- ip route 0.0.0.0 0.0.0.0 192.68.6.1 50
- ip route 0.0.0.0 0.0.0.0 202.16.20.2 60
- ip route 0.0.0.0 0.0.0.0 212.68.6.1 70
4. Which is a clientless VPN solution for mobile workers?
- GRE
- IPsec
- SSH
- SSL
5. Which two statements are correct about IPsec crypto maps? (Choose two.)
- The crypto map defines the IPsec tunnel endpoint or peer.
- Packets that do not meet the criteria as specified in the crypto map are dropped.
- The crypto map is applied to the outbound interface that the router is peering with.
- A crypto map is used to negotiate and exchange authentication and encryption parameters with its peer.
- The crypto map is applied to the inbound interface that receives the packets before being transmitted over the VPN tunnel.
6. What is a limitation of IPsec by design?
- IPsec only forwards unicast traffic.
- IPsec does not support encryption for traffic over a GRE tunnel.
- IPsec forwards unicast and multicast traffic, but not broadcast traffic.
- IPsec tunneling does not support the encapsulation of RFC 1918 addresses.
7. Refer to the exhibit. Which two statements are true about the exhibited static routes? (Choose two.)
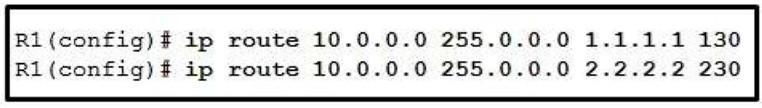
- If a route to 10.0.0.0/8 is received via RIP, R1 will prefer the dynamic route over both configured static routes.
- If no dynamic route to 10.0.0.0/8 exists, both static routes will appear in the R1 routing table.
- If no dynamic route to 10.0.0.0/8 exists, R1 will use 2.2.2.2 as the next hop because it has a higher preference.
- If a route to 10.0.0.0/8 is received via RIP, both static routes will appear in the routing table.
- The static route to 10.0.0.0/8 via 1.1.1.1 will be preferred to the route via 2.2.2.2.
8. Refer to the exhibit. A network administrator is configuring NAT on router Remote. The configuration should allow users on network 172.16.16.0/21 to access Internet sites as well as resources on the HQ LAN network 172.16.0.0/21 through the VPN tunnel. How should the administrator configure access list 101 to accomplish this task?
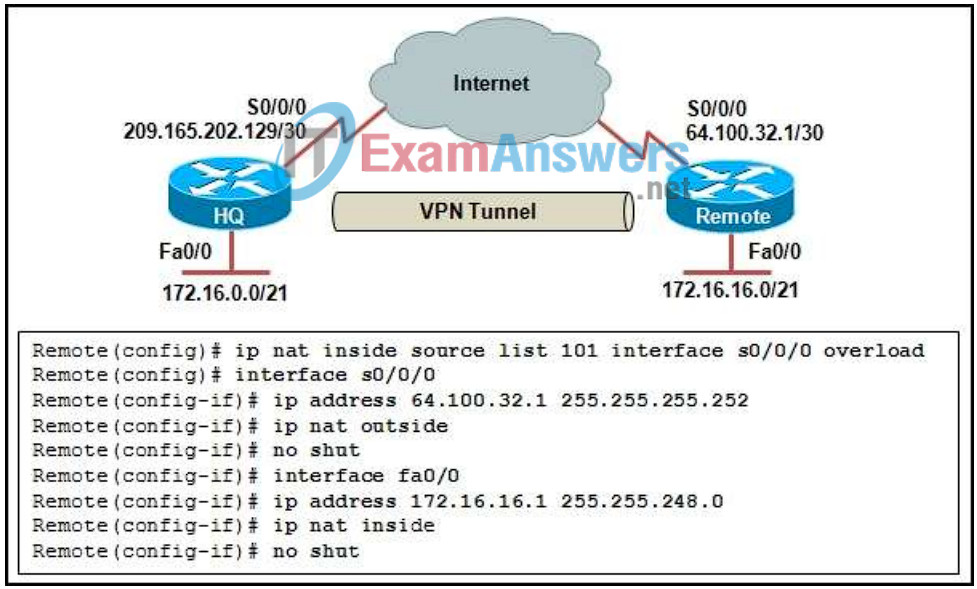
- Remote(config)# access-list 101 deny 172.16.16.0 0.0.7.255 172.16.0.0 0.0.7.255
Remote(config)# access-list 101 permit ip 172.16.16.0 0.0.7.255 any - Remote(config)# access-list 101 permit ip 172.16.16.0 0.0.7.255 any
Remote(config)# access-list 101 deny 172.16.16.0 0.0.7.255 172.16.0.0 0.0.7.255 - Remote(config)# access-list 101 deny 172.16.16.0 0.0.7.255 any
Remote(config)# access-list 101 permit ip 172.16.16.0 0.0.7.255 any - Remote(config)# access-list 101 deny 172.16.16.0 0.0.7.255 209.165.202.129 0.0.0.3
Remote(config)# access-list 101 permit ip 172.16.16.0 0.0.7.255 any - Remote(config)# access-list 101 permit ip 172.16.16.0 0.0.7.255 any
Remote(config)# access-list 101 deny 172.16.0.0 0.0.7.255 172.16.16.0 0.0.7.255
9. How is NAT tuned to handle traffic that is sent through a VPN tunnel between a mobile worker and internal corporate resources?
- Translation is allowed by a permit access list statement or route map.
- Translation is allowed by a deny access list statement or route map.
- Traffic should bypass translation with a permit access list statement or route-map.
- Traffic should bypass translation with a deny access list statement or route-map.
10. Branch office network design faces several challenges. Which of these challenges has the goal of obtaining centralized control of network security and management?
- bandwidth and network requirements
- consolidated data centers
- deployment plan
- management costs
- mobility
11. Which three statements would help an end user develop a better understanding of DSL technology? (Choose three.)
- ADSL typically has a higher download bandwidth than available upload bandwidth.
- All varieties of DSL provide the same bandwidth, although they use different technologies to achieve upload and download.
- DSL data subscribers are connected to a network segment, all sharing the upstream and downstream bandwidth.
- DSL is available in any location that has a telephone.
- DSL speeds can exceed the speeds available with a typical T1 line.
- Transfer rates vary by the length of the local loop.
12. What are three characteristics of broadband access? (Choose three.)
- always on
- built-in security
- enhanced voice and video services
- guaranteed quality of service (QoS)
- high-speed access
- wide area of coverage
13. Which three items can be specified by ISAKMP policy parameters? (Choose three.)
- the hashing method to be used
- the encryption method to be used
- the encapsulation method to be used
- the authentication method to be used
- the ACL that is used to identify interesting traffic
- the amount of time the crypto interface should be active before being renegotiated
14. Refer to the exhibit. A network administrator is tuning IPsec to encapsulate the GRE tunnel between R1 and R2. Assuming all other IPsec configurations are correct, which two crypto map access lists will complete this task? (Choose two.)
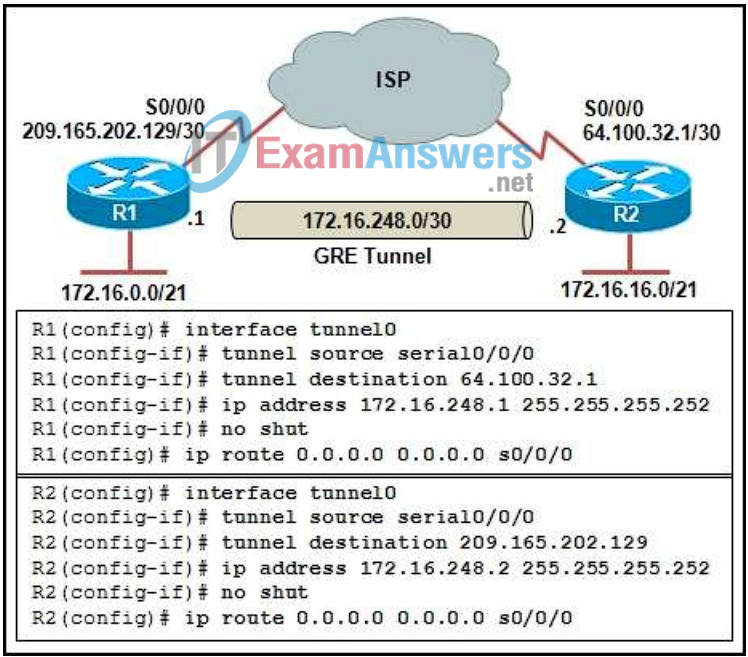
- R1(config-ext-nacl)# permit gre host 172.16.248.1 host 172.16.248.2
- R1(config-ext-nacl)# permit gre host 209.165.202.129 host 64.100.32.1
- R1(config-ext-nacl)# permit gre host 64.100.32.1 host 209.165.202.129
- R2(config-ext-nacl)# permit gre host 172.16.248.2 host 172.16.248.1
- R2(config-ext-nacl)# permit gre host 209.165.202.129 host 64.100.32.1
- R2(config-ext-nacl)# permit gre host 64.100.32.1 host 209.165.202.129
15. Which statement is true about the deployment of Context-Based Access Control (CBAC) and Zone-Based Firewall (ZBF)?
- They cannot be deployed on the same router.
- They can be deployed on the same router but not on the same interface.
- They can be deployed on the same interface but not in the same direction.
- They can be deployed on the same interface but cannot filter the same protocol.
16. Which two solutions can a hybrid fiber cable service provider apply when there is constant congestion on the line? (Choose two.)
- Allocate less bandwidth to affected customers.
- Allocate another downstream channel.
- Allocate another upstream channel.
- Run fiber deeper into the neighborhood.
- Run fiber to each home.
17. Which is a Cisco IOS firewall solution that relies on access control lists?
- Cisco Easy VPN server
- Cisco Security Manager
- Zone-Based Firewall (ZBF)
- Context-Based Access Control (CBAC)
18. In the routing design for a branch office, which area will have an affect on convergence, load balancing, and scalability?
- connectivity technologies
- mobility requirements
- resiliency
- routing protocols
- service mix
- security and compliance
19. Which IPsec service verifies that the data was not altered during transmission?
- authorization
- confidentiality
- encapsulation
- encryption
- integrity
20. Which two UDP ports must be permitted inbound through the Internet-facing interface on a firewall to establish an IPsec tunnel and NAT-T? (Choose two.)
- 22
- 50
- 51
- 500
- 4500
