Author: ITExamAnswers
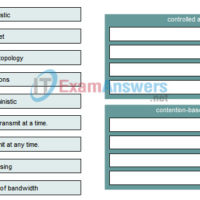
1. Drag the Ethernet frame fields on the left and drop them onto their function on the right. 2. What is a primary function of CSMA/CD in an Ethernet network? assigns MAC addresses to hosts defines the area in which collisions can occur identifies the start and end …
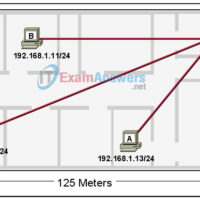
1. Match the colors to the numbers that represent the wiring pinouts for 568B patch cables. 2. Place each pin on the left onto the correct pin on the right to properly create a RJ-45 connector for a router console cable. 3. What kind of connection is represented …
1. Which frame field is created by a source node and used by a destination node to ensure that a transmitted data signal has not been altered by interference, distortion, or signal loss? transport layer error check field frame check sequence field User Datagram Protocol field error correction …
1. What are the differences between binary and decimal numbers? (Choose two.) Decimal numbers are based on powers of 1 and binary numbers are based on powers of 2. Binary numbers are based on powers of 2 and decimal numbers are based on powers of 10. Computers use …
1. Which protocol provides connectionless network layer services? IP TCP UDP OSI 2. Which protocol is connectionless? TCP UDP FTP SMTP 3. Which part of a network layer address does the router use during path determination? The host address The router address The server address The network address …
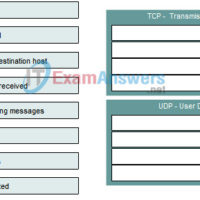
1. Match the TCP port numbers with the correct protocol by dragging the options on the left to the targets on the right. (Not all options are used.) 2. Categorize the options based on whether they describe TCP or UDP. Answer 3. At the transport layer, which of …
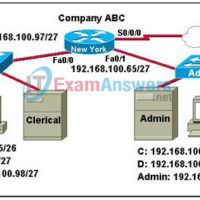
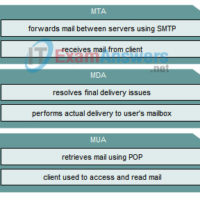
1. Which three Layers of the OSI model make up the Application layer of the TCP/IP model? (Choose three.) data link network transport session presentation application 2. What protocol is used to transfer web pages from server to client? HTML SMTP HTTP SSH Telnet POP 3. Refer to …
1. Which OSI layer is associated with IP addressing? 1 2 3 4 2. Which type of addressing is found at the OSI Layer 2? (Choose two.) logical physical MAC IP port 3. When a server responds to a web request, what occurs next in the encapsulation process …
CCNA Security 2.0 Study Material – Chapter 1: Modern Network Security Threats 1.0 Introduction 1.0.1 Welcome 1.0.1.1 1.0.1.1 Chapter 1: Modern Network Security Threats Network security is now an integral part of computer networking. Network security involves protocols, technologies, devices, tools, and techniques to secure data and mitigate …
CCNA Security 2.0 Study Material – Chapter 2: Securing Network Devices 2.0 Introduction 2.0.1 Welcome 2.0.1.1 Securing Network Devices Configure a Network Operating System Every computer requires an operating system to function, including computer-based network devices such as switches, routers, access points, and firewalls. These network devices use …