Version 6.0:
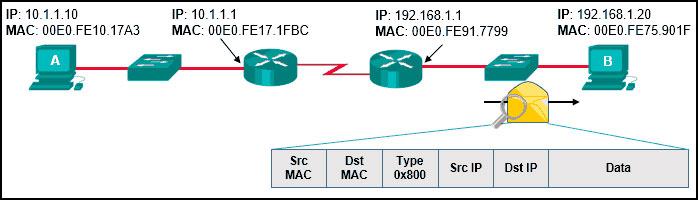
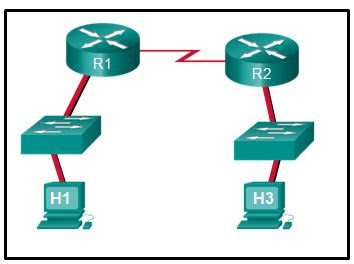
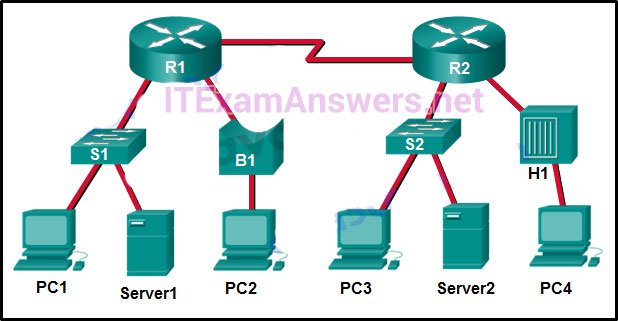
1. Refer to the exhibit. Assuming that the routing tables are up to date and no ARP messages are needed, after a packet leaves H1, how many times is the L2 header rewritten in the path to H2?
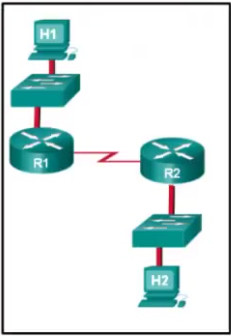
- 1
- 2
- 3
- 4
- 5
- 6
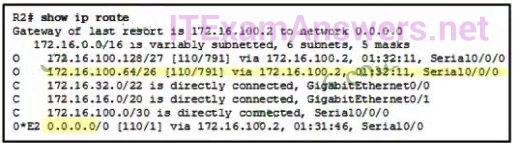
2. Refer to the exhibit. Which highlighted value represents a specific destination network in the routing table?
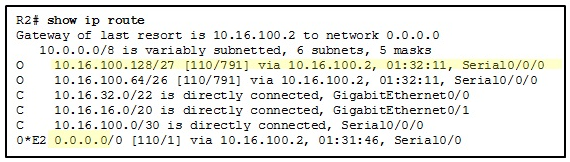
- 0.0.0.0
- 10.16.100.128
- 10.16.100.2
- 110
- 791
3. Which type of static route is configured with a greater administrative distance to provide a backup route to a route learned from a dynamic routing protocol?
- floating static route
- default static route
- summary static route
- standard static route
4. Refer to the exhibit. Which route was configured as a static route to a specific network using the next-hop address?
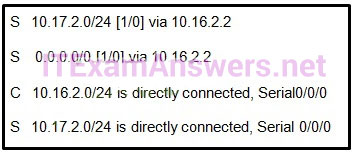
- S 10.17.2.0/24 [1/0] via 10.16.2.2
- S 0.0.0.0/0 [1/0] via 10.16.2.2
- C 10.16.2.0/24 is directly connected, Serial0/0/0
- S 10.17.2.0/24 is directly connected, Serial 0/0/0
5. What network prefix and prefix-length combination is used to create a default static route that will match any IPv6 destination?
- :/128
- FFFF:/128
- ::1/64
- ::/0
6. A router has used the OSPF protocol to learn a route to the 172.16.32.0/19 network. Which command will implement a backup floating static route to this network?
- ip route 172.16.0.0 255.255.240.0 S0/0/0 200
- ip route 172.16.32.0 255.255.224.0 S0/0/0 200
- ip route 172.16.0.0 255.255.224.0 S0/0/0 100
- ip route 172.16.32.0 255.255.0.0 S0/0/0 100
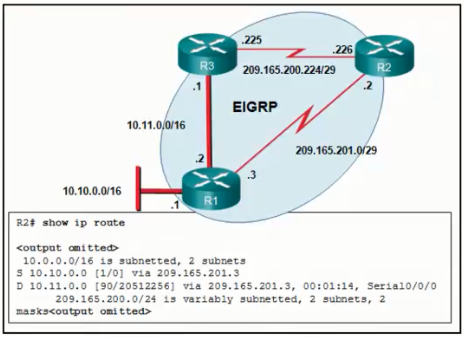
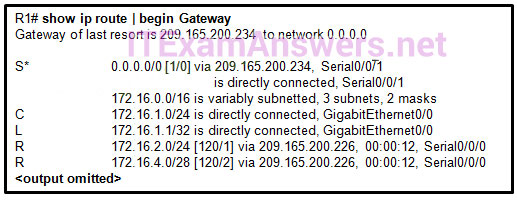
7. Refer to the exhibit. Currently router R1 uses an EIGRP route learned from Branch2 to reach the 10.10.0.0/16 network. Which floating static route would create a backup route to the 10.10.0.0/16 network in the event that the link between R1 and Branch2 goes down?
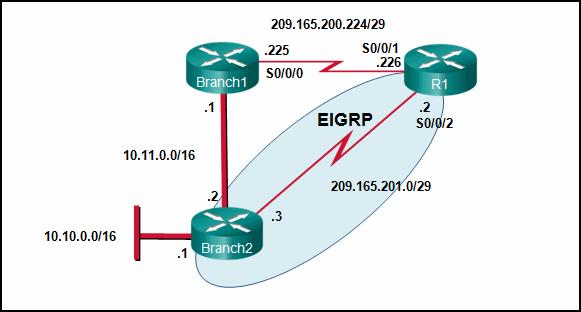
CCNA 2 v6 RSE Final Exam Answers Form A 2019-2020
- ip route 10.10.0.0 255.255.0.0 Serial 00/0 100
- ip route 10.10.0.0 255.255.0.0 209.165.200.226 100
- ip route 10.10.0.0 255.255.0.0 209.165.200.225 100
- ip route 10.10.0.0 255.255.0.0 209.165.200.225 50
8. Which statement describes a route that has been learned dynamically?
- It is automatically updated and maintained by routing protocols.
- It is unaffected by changes in the topology of the network.
- It has an administrative distance of 1.
- It is identified by the prefix C in the routing table.
9. Compared with dynamic routes, what are two advantages of using static routes on a router? (Choose two.)
- They automatically switch the path to the destination network when the topology changes
- They Improve network security
- They take less time to converge when the network topology changes
- They use fewer router resources
- They improve the efficiency of discovering neighboring networks.
10. To enable RIPv1 routing for a specific subnet, the configuration command network 172.16.64.32 was entered by the network administrator. What address, if any, appears in the running configuration file to identify this network?
- 172.16.64.32
- 172.16.64.0
- 172.16.0.0
- No address is displayed.
11. A network administrator adds the default-information originate command to the configuration of a router that uses RIP as the routing protocol. What will result from adding this command?
- The router will only forward packets that originate on directly connected networks.
- The router will propagate a static default route in its RIP updates, if one is present
- The router will be reset to the default factory information
- The router will not forward routing information that is learned from other routers
12. Refer to the exhibit. What is the administrative distance value that indicates the route for R2 to reach the 10.10.0.0/16 network?
- 1
- 0
- 90
- 20512256
13. Which route will a router use to forward an IPv4 packet after examining its routing table for the best match with the destination address?
- a level 1 child route
- a level 1 parent route
- a level 1 ultimate route
- a level 2 supernet route
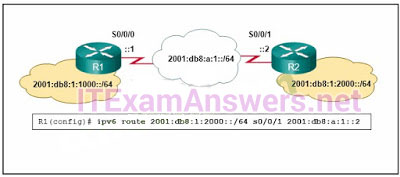
14. Refer to the exhibit. An administrator is attempting to install an IPv6 static route on router R1 to reach the network attached to router R2. After the static route command is entered, connectivity to the network is still failing. What error has been made in the static route configuration?
- The network prefix is incorrect.
- The destination network is incorrect.
- The interface is incorrect
- The next hop address is incorrect.
15. A network administrator reviews the routing table on the router and sees a route to the destination network 172.16.64.0/18 with a next-hop IP address of 192.168.1.1. What are two descriptions of this route? (Choose two.)
- parent route
- default route
- level 2 child route
- ultimate route
- supernet route
16. Which two factors are important when deciding which interior gateway routing protocol to use? (Choose two.)
- scalability
- ISP selection
- speed of convergence
- the autonomous system that is used
- campus backbone architecture
17. Employees of a company connect their wireless laptop computers to the enterprise LAN via wireless access points that are cabled to the Ethernet ports of switches. At which layer of the three-layer hierarchical network design model do these switches operate?
- physical
- access
- core
- data link
- distribution
18. What is a basic function of the Cisco Borderless Architecture access layer?
- aggregates Layer 2 broadcast domains
- aggregates Layer 3 routing boundaries
- provides access to the user
- provides fault isolation
19. What is a characteristic of the distribution layer in the three layer hierarchical model?
- provides access to the rest of the network through switching, routing, and network access policies
- distributes access to end users
- represents the network edge
- acts as the backbone for the network, aggregating and distributing network traffic throughout the campus
20. Which information does a switch use to populate the MAC address table?
- the destination MAC address and the incoming port
- the destination MAC address and the outgoing port
- the source and destination MAC addresses and the incoming port
- the source and destination MAC addresses and the outgoing port
- the source MAC address and the incoming port
- the source MAC address and the outgoing port
21. Which statement is correct about Ethernet switch frame forwarding decisions?
- Unicast frames are always forwarded regardless of the destination MAC address
- Frame forwarding decisions are based on MAC address and port mappings in the CAM table
- Cut-through frame forwarding ensures that invalid frames are always dropped
- Only frames with a broadcast destination address are forwarded out all active switch ports
22. What is the name of the layer in the Cisco borderless switched network design that would have more switches deployed than other layers in the network design of a large organization?
- access
- core
- data link
- network
- network access
23. Which switching method drops frames that fail the FCS check?
- borderless switching
- cut-through switching
- ingress port buffering
- store-and-forward switching
24. In what situation would a Layer 2 switch have an IP address configured?
- when the Layer 2 switch is using a routed port
- when the Layer 2 switch needs to be remotely managed
- when the Layer 2 switch is the default gateway of user traffic
- when the Layer 2 switch needs to forward user traffic to another device
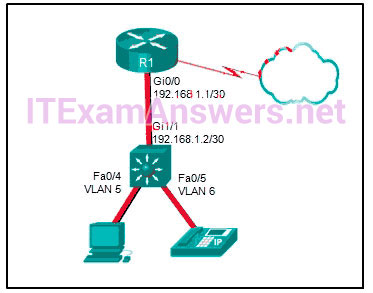
25. Refer to the exhibit. A network engineer is examining a configuration implemented by a new intern who attached an IP phone to a switch port and configured the switch. Identify the issue, if any, with the configuration.
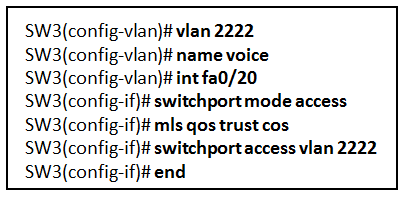
- The voice VLAN should be 150.
- The configuration is correct.
- There must be a data VLAN added.
- The spanning-tree BPDU guard feature is missing.
- The switch port is not configured as a trunk.
26. A network administrator is configuring a new Cisco switch for remote management access. Which three items must be configured on the switch for the task? (Choose three.)
- vty lines
- VTP domain
- loopback address
- default VLAN
- default gateway
- IP address
27. A network technician has been asked to secure all switches in the campus network. The security requirements are for each switch to automatically learn and add MAC addresses to both the address table and the running configuration. Which port security configuration will meet these requirements?
- auto secure MAC addresses
- dynamic secure MAC addresses
- static secure MAC addresses
- sticky secure MAC addresses
28. A network administrator is configuring port security on a Cisco switch. When a violation occurs, which violation mode that is configured on an interface will cause packets with an unknown source address to be dropped with no notification sent?
- off
- restrict
- protect
- shutdown
29. Two employees in the Sales department work different shifts with their laptop computers and share the same Ethernet port in the office. Which set of commands would allow only these two laptops to use the Ethernet port and create violation log entry without shutting down the port if a violation occurs?
- switchport mode access
switchport port-security - switchport mode access
switchport port-security
switchport port-security maximum 2
switchport port-security mac-address sticky
switchport port-security violation restrict - switchport mode access
switchport port-security maximum 2
switchport port-security mac-address sticky - switchport mode access
switchport port-security maximum 2
switchport port-security mac-address sticky
switchport port-security violation protect
30. Refer to the exhibit. What protocol should be configured on SW-A Port 0/1 if it is to send traffic from multiple VLANs to switch SW-B?
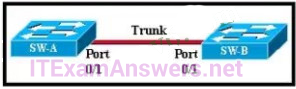
- RIP v2
- IEEE 802.1Q
- Spanning Tree
- ARP
- Rapid Spanning Tree
31. A Cisco Catalyst switch has been added to support the use of multiple VLANs as part of an enterprise network. The network technician finds it necessary to clear all VLAN information from the switch in order to incorporate a new network design. What should the technician do to accomplish this task?
- Erase the startup configuration and reboot the switch
- Erase the running configuration and reboot the switch
- Delete the startup configuration and the vlan.dat file in the flash memory of the switch and reboot the switch
- Delete the IP address that is assigned to the management VLAN and reboot the switch.
32. What will a Cisco LAN switch do if it receives an incoming frame and the destination MAC address is not listed in the MAC address table?
- Drop the frame.
- Send the frame to the default gateway address.
- Use ARP to resolve the port that is related to the frame.
- Forward the frame out all ports except the port where the frame is received.
33. What VLANs are allowed across a trunk when the range of allowed VLANs is set to the default value?
- The switches will negotiate via VTP which VLANs to allow across the trunk
- Only VLAN 1 will be allowed across the trunk.
- Only the native VLAN will be allowed across the trunk
- All VLANs will be allowed across the trunk
34. Refer to the exhibit. A network administrator is configuring inter-VLAN routing on a network. For now, only one VLAN is being used, but more will be added soon. What is the missing parameter that is shown as the highlighted question mark in the graphic?
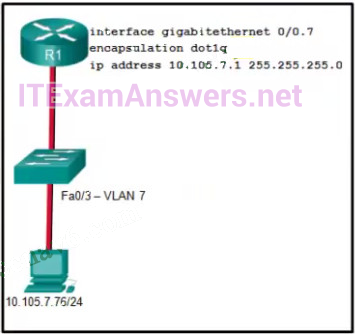
- It identifies the type of encapsulation that is used
- It identifies the VLAN number
- It identifies the subinterface
- It identifies the number of hosts that are allowed on the interface
- It identifies the native VLAN number
35. A network administrator is designing an ACL. The networks 192.168.1.0/25, 192.168.0.0/25, 192.168.0.128/25, 192.168.1.128/26, and 192.168.1.192/26 are affected by the ACL. Which wildcard mask, if any, is the most efficient to use when specifying all of these networks in a single ACL permit entry?
- 0.0.0.127
- 0.0.0.255
- 0.0.1.255
- 0.0.255.255
- A single ACL command and wildcard mask should not be used to specify these particular networks or other traffic will be permitted or denied and present a security risk.
36. The computers used by the network administrators for a school are on the 10.7.0.0/27 network. Which two commands are needed at a minimum to apply an ACL that will ensure that only devices that are used by the network administrators will be allowed Telnet access to the routers? (Choose two.)
- access-class 5 in
- access-list 5 deny any
- access-list standard VTY
- permit 10.7.0.0 0.0.0.127
- access-list 5 permit 10.7.0.0 0.0.0.31
- ip access-group 5 out
- ip access-group 5 in
37. A network engineer has created a standard ACL to control SSH access to a router. Which command will apply the ACL to the VTY lines?
- access-group 11 in
- access-class 11 in
- access-list 11 in
- access-list 110 in
38. What is the reason why the DHCPREQUEST message is sent as a broadcast during the DHCPv4 process?
- for hosts on other subnets to receive the information
- to notify other hosts not to request the same IP address
- for routers to fill their routing tables with this new information
- to notify other DHCP servers on the subnet that the IP address was leased
39. Which set of commands will configure a router as a DHCP server that will assign IPv4 addresses to the 192.168.100.0/23 LAN while reserving the first 10 and the last addresses for static assignment?
- ip dhcp excluded-address 192.168.100.1 192.168.100.10
ip dhcp excluded-address 192.168.100.254
ip dhcp pool LAN POOL-100
network 192.168.100.0 255.255.255.0
ip default gateway 192.168.100.1 - ip dhcp excluded-address 192.168.100.1 192.168.100.9
ip dhcp excluded-address 192.168.101.254
ip dhcp pool LAN POOL-100 ip
network 192.168.100.0 255.255.254.0
ip default-gateway 192.168.100.1 - ip dhcp excluded-address 192.168.100.1 192.168.100.10
ip dhcp excluded-address 192.168.101.254
ip dhcp pool LAN POOL-100
network 192.168.100.0 255.255.254.0
default-router 192.168.100.1 - dhcp pool LAN-POOL 100
ip dhcp excluded-address 192.168.100.1 192.168.100.9
ip dhcp excluded-address 192.168.100.254
network 192.168.100.0 255.255.254.0
default-router 192.168.101.1
40. Which command, when issued in the interface configuration mode of a router, enables the interface to acquire an IPv4 address automatically from an ISP, when that link to the ISP is enabled?
- ip dhcp pool
- ip address dhcp
- service dhcp
- ip helper-address
41. Refer to the exhibit. A network administrator is configuring a router as a DHCPv6 server. The administrator issues a show ipv6 dhcp pool command to verify the configuration. Which statement explains the reason that the number of active clients is 0?
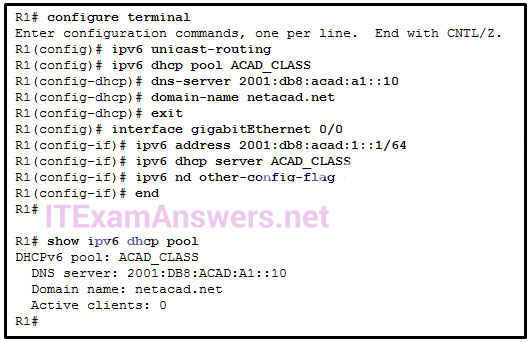
- The default gateway address is not provided in the pool.
- No clients have communicated with the DHCPv6 server yet.
- The IPv6 DHCP pool configuration has no IPv6 address range specified.
- The state is not maintained by the DHCPv6 server under stateless DHCPv6 operation.
42. Refer to the exhibit. R1 has been configured as shown. However, PC1 is not able to receive an IPv4 address. What is the problem?
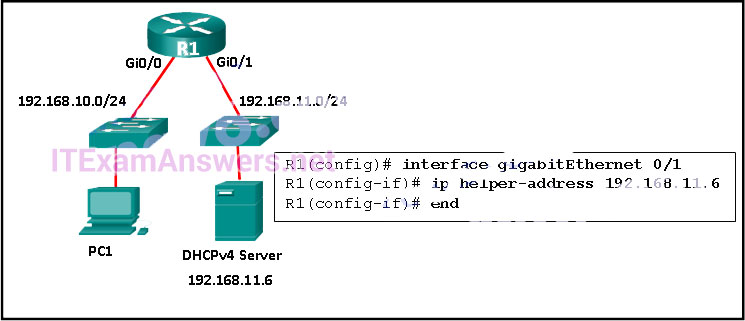
- A DHCP server must be installed on the same LAN as the host that is receiving the IP address.
- R1 is not configured as a DHCPv4 server.
- The ip address dhcp command was not issued on the interface Gi0/1.
- The ip helper-address command was applied on the wrong interface.
43. Refer to the exhibit. Which statement shown in the output allows router R1 to respond to stateless DHCPv6 requests?
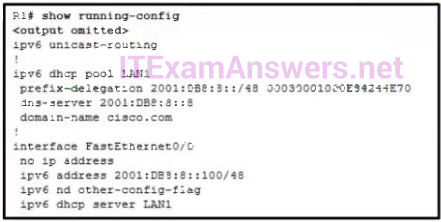
- ipv6 unicast-routing
- ipv6 nd other-config-flag
- ipv6 dhcp server LAN1
- prefix-delegation 2001:DB8:8::/48 00030001000E84244E70
- dns-server 2001:DB8:8::8
44. Refer to the exhibit. NAT is configured on Remote and Main. The PC is sending a request to the web server. What IPv4 address is the source IP address in the packet between Main and the web server?

- 10.130.5.76
- 209.165.200.245
- 203.0.113.5
- 172.16.1.10
- 192.0.2.1
- 209.165.200.226
45. Which type of traffic would most likely have problems when passing through a NAT device?
- Telnet
- IPsec
- HTTP
- ICMP
- DNS
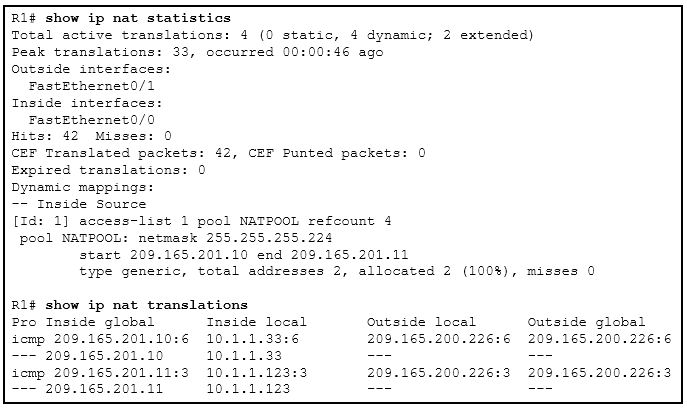
46. Refer to the exhibit. Which two statements are correct based on the output as shown in the exhibit? (Choose two.)
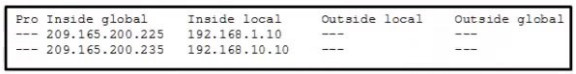
- The host with the address 209.165.200.235 will respond to requests by using a source address of 209.165.200.235
- The output is the result of the show ip nat translations command
- Traffic with the destination address of a public web server will be sourced from the IP of 192.168.1.10.
- The host with the address 209.165.200.235 will respond to requests by using a source address of 192.168.10.10.
- The output is the result of the show ip nat statistics command
47. Refer to the exhibit. A network administrator has configured R2 for PAT. Why is the configuration incorrect?
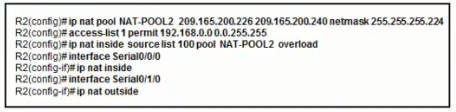
- NAT-POOL2 is bound to the wrong ACL
- The ACL does not define the list of addresses to be translated.
- The overload keyword should not have been applied.
- The static NAT entry is missing
48. A small company has a web server in the office that is accessible from the Internet. The IP address 192.168.10.15 is assigned to the web server. The network administrator is configuring the router so that external clients can access the web server over the Internet. Which item is required in the NAT configuration?
- an IPv4 address pool
- an ACL to identify the local IPv4 address of the web server
- the keyword overload for the ip nat inside source command
- the ip nat inside source command to link the inside local and inside global addresses
49. A college marketing department has a networked storage device that uses the IP address 10.18.7.5, TCP port 443 for encryption, and UDP port 4365 for video streaming. The college already uses PAT on the router that connects to the Internet. The router interface has the public IP address of 209.165.200.225/30. The IP NAT pool currently uses the IP addresses ranging from 209.165.200.228-236. Which configuration would the network administrator add to allow this device to be accessed by the marketing personnel from home?
- ip nat inside source static tcp 209.165.200.225 443 10.18.7.5 443
ip nat inside source static udp 209.165.200.225 4365 10.18.7.5 4365 - No additional configuration is necessary
- ip nat pool mktv 10.18.7.5 10.18.7.5
- ip nat inside source static tcp 10.18.7.5 443 209.165.200.225 443
ip nat inside source static udp 10.18.7.5 4365 209.165.200.225 4365 - ip nat outside source static 10.18.7.5 209.165.200.225
50. Refer to the exhibit. Based on the output that is shown, what type of NAT has been implemented?
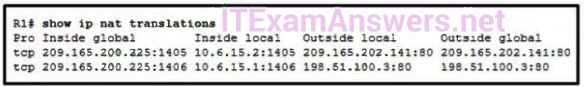
- static NAT with a NAT pool
- static NAT with one entry
- dynamic NAT with a pool of two public IP addresses
- PAT using an external interface
51. Refer to the exhibit. An administrator is trying to configure PAT on R1, but PC-A is unable to access the Internet. The administrator tries to ping a server on the Internet from PC-A and collects the debugs that are shown in the exhibit. Based on this output, what is most likely the cause of the problem?
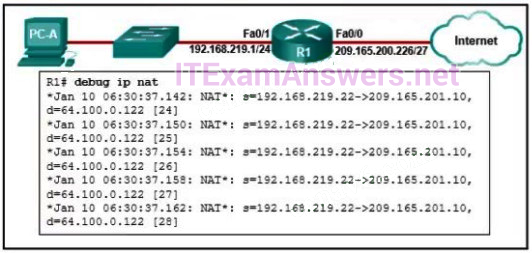
- The inside and outside NAT interlaces have been configured backwards
- The inside global address is not on the same subnet as the ISP
- The address on Fa0/0 should be 64.100.0.1.
- The NAT source access list matches the wrong address range.
52. A network engineer is interested in obtaining specific information relevant to the operation of both distribution and access layer Cisco devices. Which command provides common information relevant to both types of devices?
- show port-security
- show ip interface
- show ip protocols
- show mac-address-table
- show cdp neighbors
53. Which two statements are correct if a configured NTP master on a network cannot reach any clock with a lower stratum number? (Choose two.)
- The NTP master will claim to be synchronized at the configured stratum number.
- An NTP server with a higher stratum number will become the master.
- Other systems will be willing to synchronize to that master using NTP.
- The NTP master will be the clock with 1 as its stratum number.
- The NTP master will lower its stratum number.
54. What are three functions provided by the syslog service? (Choose three.)
- to specify the destinations of captured messages
- to periodically poll agents for data
- to select the type of logging information that is captured
- to gather logging information for monitoring and troubleshooting
- to provide traffic analysis
- to provide statistics on packets that are flowing through a Cisco device
55. Refer to the exhibit. Which three hosts will receive ARP requests from host A, assuming that port Fa0/4 on both switches is configured to carry traffic for multiple VLANs? (Choose three.)
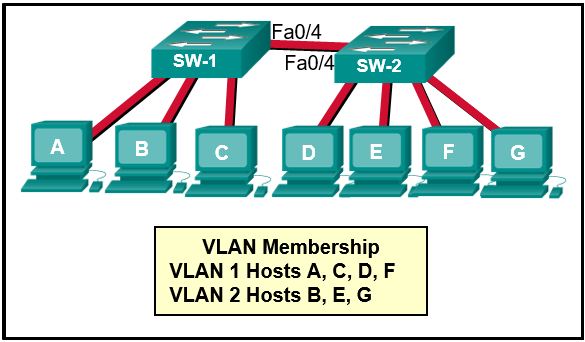
- host B
- host C
- host D
- host E
- host F
- host G
56. Refer to the exhibit. An administrator is examining the message in a syslog server. What can be determined from the message?

- This is an error message that indicates the system is unusable.
- This is an alert message for which immediate action is needed
- This is an error message for which warning conditions exist
- This is a notification message for a normal but significant condition
57. When a customer purchases a Cisco IOS 15.0 software package, what serves as the receipt for that customer and is used to obtain the license as well?
- Software Claim Certificate
- Unique Device Identifier
- End User License Agreement
- Product Activation Key
58. Refer to the exhibit. The network administrator enters these commands into the R1 router:
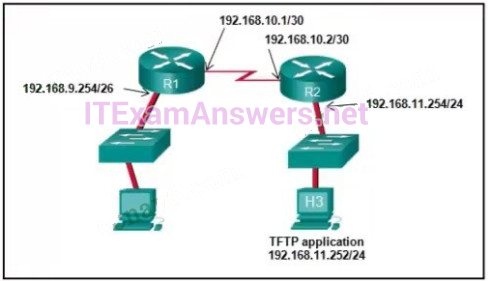
R1# copy running-config tftp Address or name of remote host [ ]
When the router prompts for an address or remote host name, what IP address should the administrator enter at the prompt?
- 192.168.10.2
- 192.168.11.252
- 192.168.11.254
- 192.168.9.254
- 192.168.10.1
59. Which configuration would be appropriate for a small business that has the public IP address of 209.165.200.225/30 assigned to the external interface on the router that connects to the Internet?
- access-list 1 permit 10.0.0.0 0.255.255.255
ip nat inside source list 1 interface serial 0/0/0 overload - access-list 1 permit 10.0.0.0 0.255.255.255
ip nat pool comp 192.168.2.1 192.168.2.8 netmask 255.255.255.240
ip nat inside source list 1 pool comp - access-list 1 permit 10.0.0.0 0.255.255.255
ip nat pool comp 192.168.2.1 192.168.2.8 netmask 255.255.255.240
ip nat inside source list 1 pool comp overload - access-list 1 permit 10.0.0.0 0.255.255.255
ip nat pool comp 192.168.2.1 192.168.2.8 netmask 255.255.255.240
ip nat inside source list 1 pool comp overload
ip nat inside source static 10.0.0.5 209.165.200.225
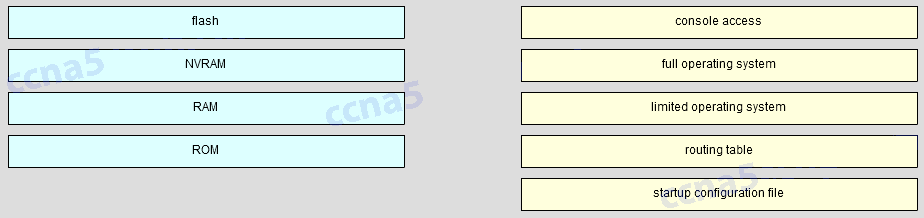
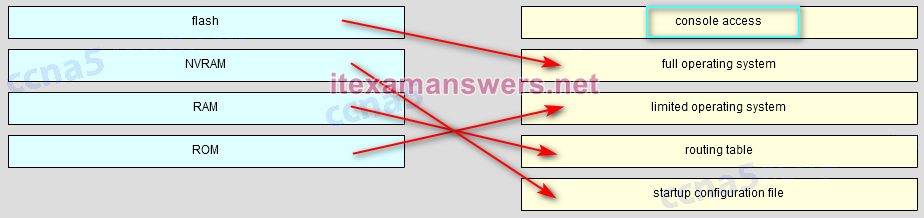
60. Match the router memory type that provides the primary storage for the router feature. (Not all options are used.)
61. Match each borderless switched network principle to its description. (Not all options are used)
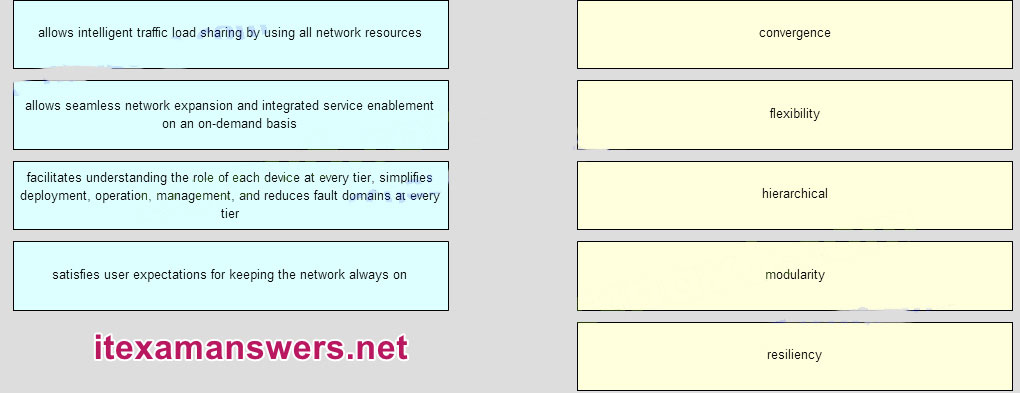
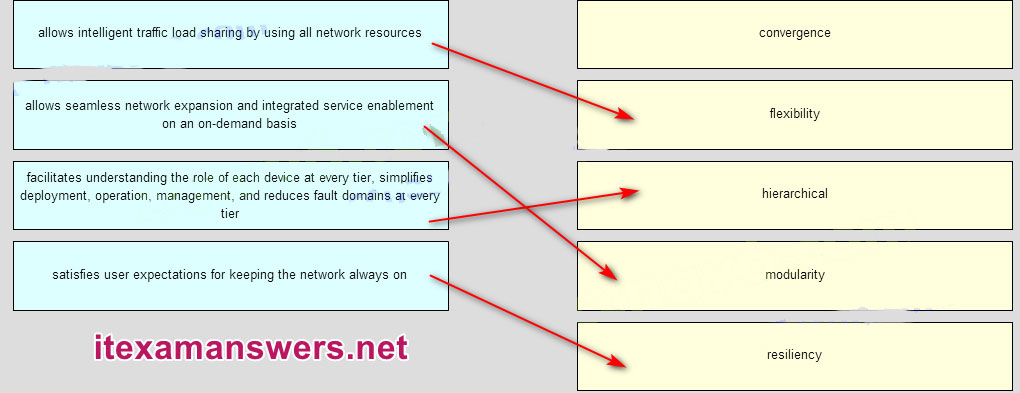
resiliency -> This provides “always-on” dependability
hierarchical -> Layers minimize the number of devices on any one tier that share a single point of failure
modularity -> Each layer has specific roles and functions that can scale easily
flexibility -> This shares the network traffic load across all network resources
none -> This provides quality of service and additional security
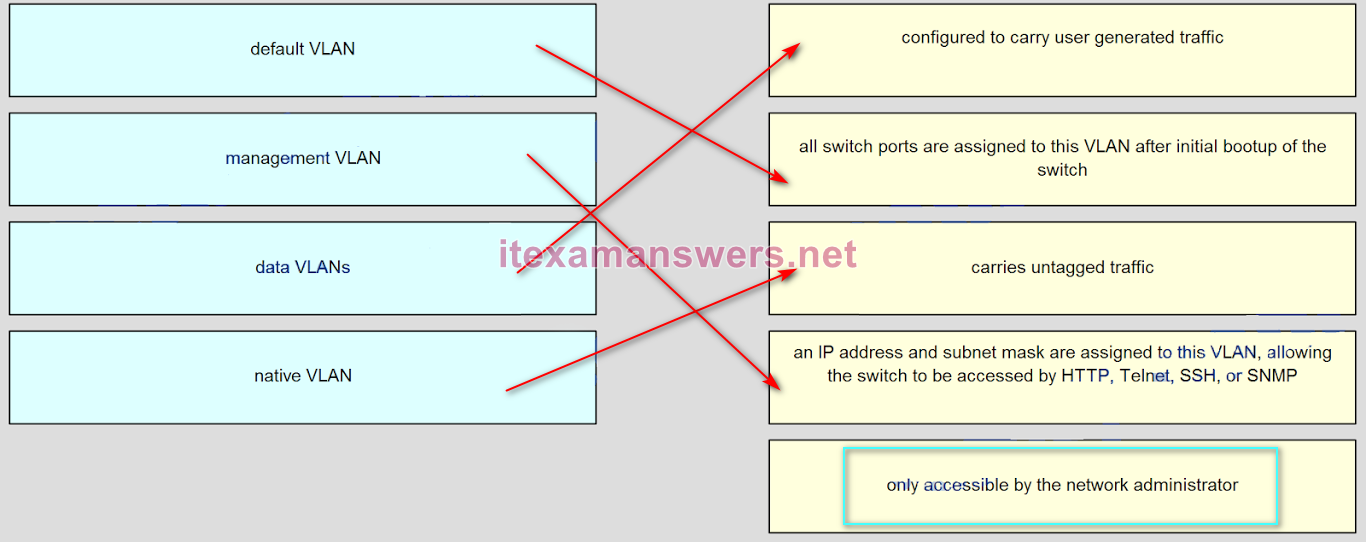
62. Match the description to the correct VLAN type. (Not all options are used )
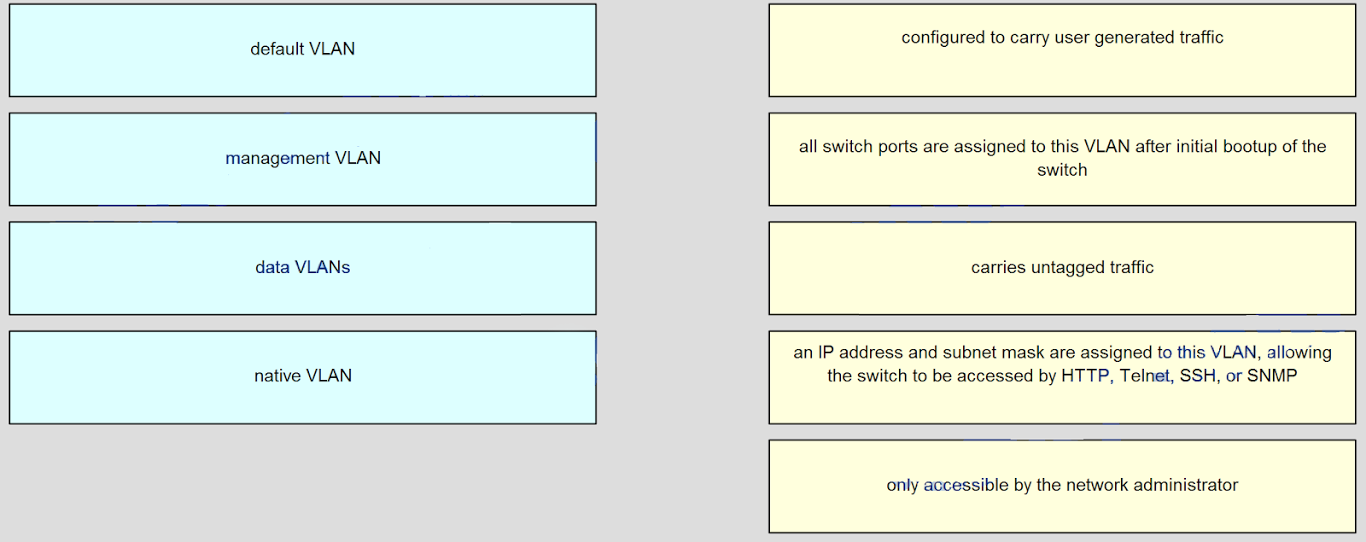
Answers:
63. Refer to the exhibit. Host A has sent a packet to host B. What will be the source MAC and IP addresses on the packet when it arrives at host B?
- Source MAC: 00E0.FE91.7799
Source IP: 192.168.1.1 - Source MAC: 00E0.FE10.17A3
Source IP: 10.1.1.10 - Source MAC: 00E0.FE91.7799
Source IP: 10.1.1.10 - Source MAC: 00E0.FE10.17A3
Source IP: 192.168.1.1 - Source MAC: 00E0.FE91.7799
Source IP: 10.1.1.1
64. What benefit does NAT64 provide?
- It allows sites to use private IPv6 addresses and translates them to global IPv6 addresses.
- It allows sites to connect multiple IPv4 hosts to the Internet via the use of a single public IPv4 address.
- It allows sites to connect IPv6 hosts to an IPv4 network by translating the IPv6 addresses to IPv4 addresses.
- It allows sites to use private IPv4 addresses, and thus hides the internal addressing structure from hosts on public IPv4 networks.
65. What is the effect of configuring the ipv6 unicast-routing command on a router?
- to assign the router to the all-nodes multicast group
- to enable the router as an IPv6 router
- to permit only unicast packets on the router
- to prevent the router from joining the all-routers multicast group
66. What is a characteristic of a static route that creates a gateway of last resort?
- It backs up a route already discovered by a dynamic routing protocol.
- It uses a single network address to send multiple static routes to one destination address.
- It identifies the gateway IP address to which the router sends all IP packets for which it does not have a learned or static route
- It is configured with a higher administrative distance than the original dynamic routing protocol has.
67. Match each borderless switched network principle to its description. (Not all options are used.)
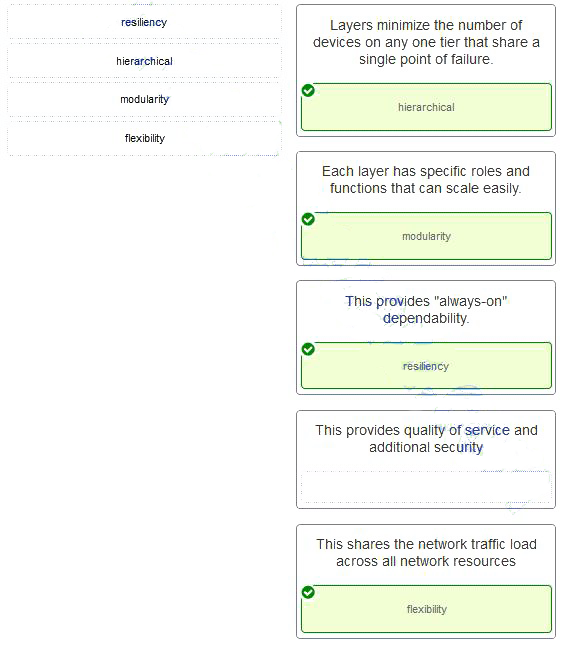
- Layers minimize the number of devices on any one tier that share a single point of failure. –> hierarchical
- Each layer has specific roles and functions that can scale easily. –> modularity
- This provides “always-on” dependability –> resiliency
- This provides quality of service and additional security –> (empty)
- This shares the network traffic load across all network resources –> flexibility
68. Refer to the exhibit. Which command will properly configure an IPv6 static route on R2 that will allow traffic from PC2 to reach PC1 without any recursive lookups by router R2?
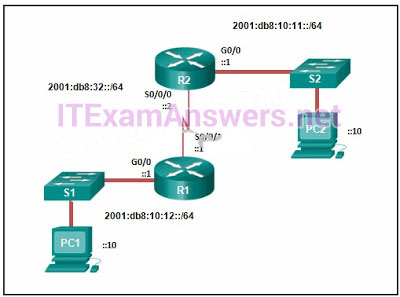
- R2(config)# ipv6 route 2001:db8:10:12::/64 2001:db8:32::1
- R2(config)# ipv6 route 2001:db8:10:12::/64 S0/0/0
- R2(config)# ipv6 route ::/0 2001:db8:32::1
- R2(config)# ipv6 route 2001:db8:10:12::/64 S0/0/1
69. Which network design may be recommended for a small campus site that consists of a single building with a few users?
- a network design where the access and distribution layers are collapsed into a single layer
- a network design where the access and core layers are collapsed into a single layer
- a collapsed core network design
- a three-tier campus network design where the access, distribution, and core are all separate layers, each one with very specific functions
70. Which information does a switch use to keep the MAC address table information current?
- the destination MAC address and the incoming port
- the destination MAC address and the outgoing port
- the source and destination MAC addresses and the incoming port
- the source and destination MAC addresses and the outgoing port
- the source MAC address and the incoming port
- the source MAC address and the outgoing port
71. Which advantage does the store-and-forward switching method have compared with the cut-through switching method?
- collision detecting
- frame error checking
- faster frame forwarding
- frame forwarding using IPv4 Layer 3 and 4 information
72. Which characteristic describes cut-through switching?
- Frames are forwarded without any error checking.
- Error-free fragments are forwarded, so switching accurs with lower latency.
- Buffering is used to support different Ethernet speeds.
- Only outgoing frames are checked for errors.
73. What is a result of connecting two or more switches together?
- The number of broadcast domains is increased.
- The size of the broadcast domain is increased.
- The number of collision domains is reduced.
- The size of the collision domain is increased.
74. Which commands are used to re-enable a port that has been disabled as a result of a port security violation?
- shutdown
no shutdown - shutdown
no switchport port-security - shutdown
no switchport port-security violation shutdown - shutdown
no switchport port-security maximum
75. Which two characteristics describe the native VLAN? (Choose two.)
- Designed to carry traffic that is generated by users, this type of VLAN is also known as the default VLAN.
- The native VLAN traffic will be untagged across the trunk link.
- This VLAN is necessary for remote management of a switch.
- High priority traffic, such as voice traffic, uses the native VLAN.
- The native VLAN provides a common identifier to both ends of a trunk.
76. Which type of traffic is designed for a native VLAN?
- management
- user-generated
- tagged
- untagged
77. An administrator is trying to remove configurations from a switch. After using the command erase startup-config and reloading the switch, the administrator finds that VLANs 10 and 100 still exist on the switch. Why were these VLANs not removed?
- These VLANs are default VLANs that cannot be removed.
- These VLANs cannot be deleted unless the switch is in VTP client mode.
- These VLANs can only be removed from the switch by using the no vlan 10 and no vlan 100 commands.
- Because these VLANs are stored in a file that is called vlan.dat that is located in flash memory, this file must be manually deleted.
78. Refer to the exhibit. Inter-VLAN communication between VLAN 10, VLAN 20, and VLAN 30 is not successful. What is the problem?
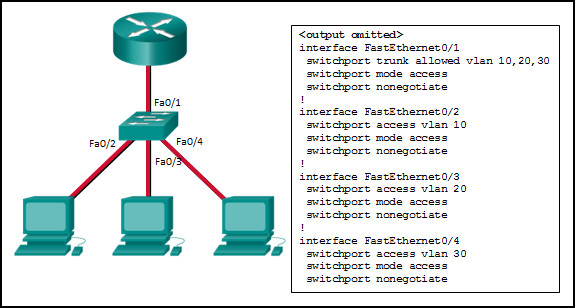
- The access interfaces do not have IP addresses and each should be configured with an IP address.
- The switch interface FastEthernet0/1 is configured as an access interface and should be configured as a trunk interface.
- The switch interface FastEthernet0/1 is configured to not negotiate and should be configured to negotiate.
- The switch interfaces FastEthernet0/2, FastEthernet0/3, and FastEthernet0/4 are configured to not negotiate and should be configured to negotiate.
79. A network administrator is configuring an ACL with the command access-list 10 permit 172.16.32.0 0.0.15.255. Which IPv4 address matches the ACE?
- 172.16.20.2
- 172.16.26.254
- 172.16.36.255
- 172.16.47.254
- 172.16.48.5
80. Refer to the exhibit. A PC at address 10.1.1.45 is unable to access the Internet. What is the most likely cause of the problem?
- The NAT pool has been exhausted.
- The wrong netmask was used on the NAT pool.
- Access-list 1 has not been configured properly.
- The inside and outside interfaces have been configured backwards.
81. A network administrator is verifying a configuration that involves network monitoring. What is the purpose of the global configuration command logging trap 4?
- System messages will be forwarded to the number following the logging trap argument.
- System messages that exist in levels 4-7 must be forwarded to a specific logging server.
- System messages that match logging levels 0-4 will be forwarded to a specified logging device.
- System messages will be forwarded using a SNMP version that matches the argument that follows the logging trap command.
82. What is indicated by the M in the Cisco IOS image name c1900-universalk9-mz.SPA.153-3.M.bin?
- a maintenance deployment release
- a minor release
- a mainline release
- an extended maintenance release
83. Refer to the exhibit. A network engineer is preparing to upgrade the IOS system image on a Cisco 2901 router. Based on the output shown, how much space is available for the new image?
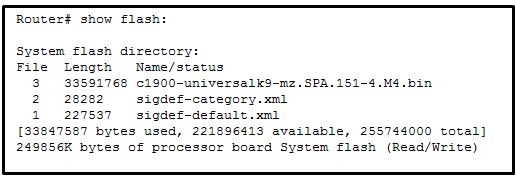
- 25574400 bytes
- 249856000 bytes
- 221896413 bytes
- 33591768 bytes
84. Refer to the exhibit. Based on the exhibited configuration and output, what are two reasons VLAN 99 missing? (Choose two.)
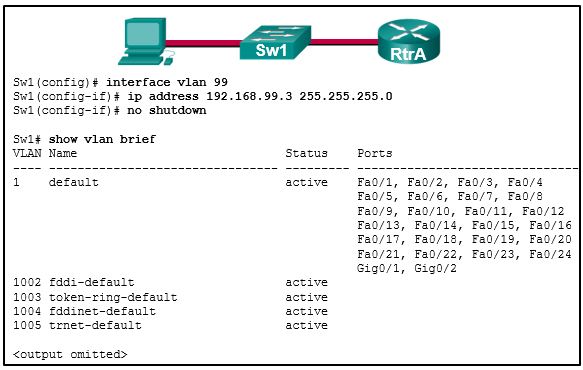
- because there is a cabling problem on VLAN 99
- because VLAN 99 is not a valid management VLAN
- because VLAN 1 is up and there can only be one management VLAN on the switch
- because VLAN 99 needs to be entered as a VLAN under an interface before it can become an active interface
- because the VLAN 99 has not been manually entered into the VLAN database with the vlan 99 command
85. Order the DHCP process steps. (Not all options are used.)
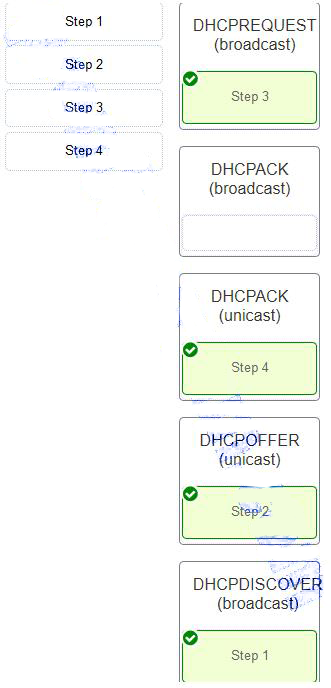
- DHCPREQUEST (broadcast) –> Step 3
- DHCPACK (broadcast) –> (empty)
- DHCPACK (unicast) –> Step 4
- DHCPOFFER (unicast) –> Step 2
- DHCPDISCOVER (broadcast) –> Step 1
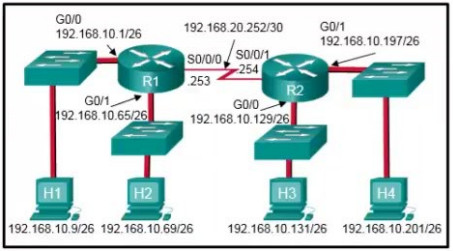
86. Refer to the exhibit. Assuming that the routing tables are up to date and no ARP messages are needed, after a packet leaves H1, how many times is the L2 header rewritten in the path to H3?
- 1
- 2
- 3
- 4
- 5
- 6
87. Refer to the exhibit. Which highlighted value represents a specific destination network in the routing table?
- 0.0.0.0
- 172.16.100.64
- 172.16.100.2
- 110
- 791
88. On which two routers would a default static route be configured? (Choose two.)
- stub router connection to the rest of the corporate or campus network
- any router where a backup route to dynamic routing is needed for reliability
- edge router connection to the ISP
- any router running an IOS prior to 12.0
- the router that serves as the gateway of last resort
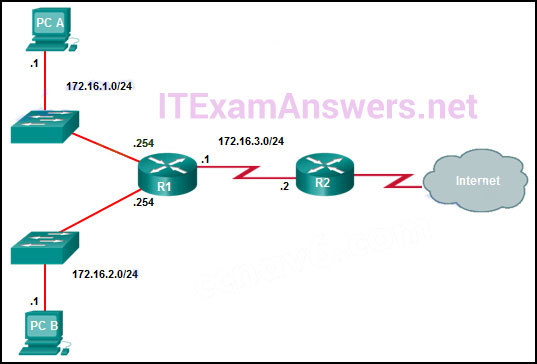
89. The exhibit shows two PCs called PC A and PC B, two routes called R1 and R2, and two switches. PC A has the address 172.16.1.1/24 and is connected to a switch and into an interface on R1 that has the IP address 172.16.1.254. PC B has the address 172.16.2.1/24 and is connected to a switch that is connected to another interface on R1 with the IP address 172.16.2.254. The serial interface on R1 has the address 172.16.3.1 and is connected to the serial interface on R2 that has the address 172.16.3.2/24. R2 is connected to the internet cloud. Which command will create a static route on R2 in order to reach PC B?
- R2(config)# ip route 172.16.2.1 255.255.255.0 172.16.3.1
- R2(config)# ip route 172.16.2.0 255.255.255.0 172.16.2.254
- R2(config)# ip route 172.16.2.0 255.255.255.0 172.16.3.1
- R2(config)# ip route 172.16.3.0 255.255.255.0 172.16.2.254
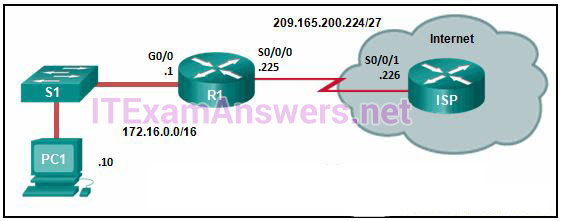
90. Refer to the exhibit. R1 was configured with the static route command ip route 209.165.200.224 255.255.255.224 S0/0/0 and consequently users on network 172.16.0.0/16 are unable to reach resources on the Internet. How should this static route be changed to allow user traffic from the LAN to reach the Internet?
- Add an administrative distance of 254.
- Change the destination network and mask to 0.0.0.0 0.0.0.0
- Change the exit interface to S0/0/1.
- Add the next-hop neighbor address of 209.165.200.226.
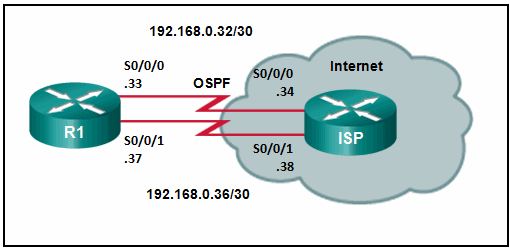
91. Refer to the exhibit. Router R1 has an OSPF neighbor relationship with the ISP router over the 192.168.0.32 network. The 192.168.0.36 network link should serve as a backup when the OSPF link goes down. The floating static route command ip route 0.0.0.0 0.0.0.0 S0/0/1 100 was issued on R1 and now traffic is using the backup link even when the OSPF link is up and functioning. Which change should be made to the static route command so that traffic will only use the OSPF link when it is up?
- Add the next hop neighbor address of 192.168.0.36.
- Change the administrative distance to 1.
- Change the destination network to 192.168.0.34.
- Change the administrative distance to 120.
92. Refer to the exhibit. All hosts and router interfaces are configured correctly. Pings to the server from both H1 and H2 and pings between H1 and H2 are not successful. What is causing this problem?
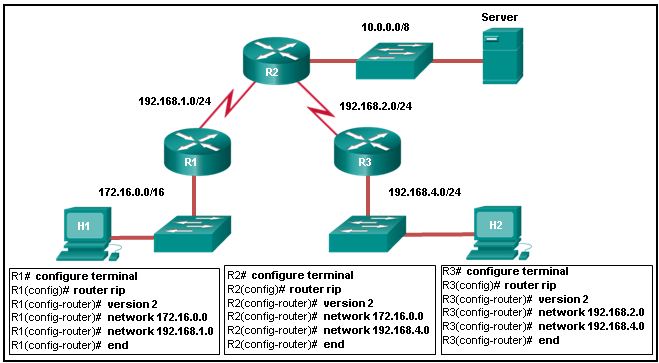
- RIPv2 does not support VLSM.
- RIPv2 is misconfigured on router R1.
- RIPv2 is misconfigured on router R2.
- RIPv2 is misconfigured on router R3.
- RIPv2 does not support discontiguous networks.
93. What caused the following error message to appear?01:11:12: %PM-4-ERR_DISABLE: psecure-violation error detected on Fa0/8, putting Fa0/8 in err-disable state01:11:12: %PORT_SECURITY-2-PSECURE_VIOLATION: Security violation occurred, caused by MAC address 0011.a0d4.12a0 on port FastEthernet0/8.01:11:13: %LINEPROTO-5-UPDOWN: Line protocol on Interface FastEthernet0/8, changed state to down01:11:14: %LINK-3-UPDOWN: Interface FastEthernet0/8, changed state to down
- Another switch was connected to this switch port with the wrong cable.
- An unauthorized user tried to telnet to the switch through switch port Fa0/8.
- NAT was enabled on a router, and a private IP address arrived on switch port Fa0/8.
- A host with an invalid IP address was connected to a switch port that was previously unused.
- Port security was enabled on the switch port, and an unauthorized connection was made on switch port Fa0/8.
94. Refer to the exhibit. A small business uses VLANs 2, 3, 4, and 5 between two switches that have a trunk link between them. What native VLAN should be used on the trunk if Cisco best practices are being implemented?
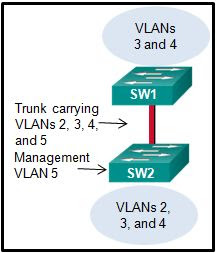
- 1
- 2
- 3
- 4
- 5
- 6
- 11
95. Which statement describes a characteristic of the extended range VLANs that are created on a Cisco 2960 switch?
- They are numbered VLANs 1002 to 1005.
- They cannot be used across multiple switches.
- They are reserved to support Token Ring VLANs.
- They are not stored in the vlan.dat file.
96. A network administrator is using the router-on-a-stick method to configure inter-VLAN routing. Switch port Gi1/1 is used to connect to the router. Which command should be entered to prepare this port for the task?
- Switch(config)# interface gigabitethernet 1/1
Switch(config-if)# spanning-tree vlan 1 - Switch(config)# interface gigabitethernet 1/1
Switch(config-if)# spanning-tree portfast - Switch(config)# interface gigabitethernet 1/1
Switch(config-if)# switchport mode trunk - Switch(config)# interface gigabitethernet 1/1
Switch(config-if)# switchport access vlan 1
97. What will be the result of adding the command ip dhcp excluded-address 172.16.4.1 172.16.4.5 to the configuration of a local router that has been configured as a DHCP server?
- Traffic that is destined for 172.16.4.1 and 172.16.4.5 will be dropped by the router.
- Traffic will not be routed from clients with addresses between 172.16.4.1 and 172.16.4.5.
- The DHCP server function of the router will not issue the addresses from 172.16.4.1through 172.16.4.5 inclusive.
- The router will ignore all traffic that comes from the DHCP servers with addresses 172.16.4.1 and 172.16.4.5.
98. A host on the 10.10.100.0/24 LAN is not being assigned an IPv4 address by an enterprise DHCP server with the address 10.10.200.10/24. What is the best way for the network engineer to resolve this problem?
- Issue the command ip helper-address 10.10.200.10 on the router interface that is the 10.10.100.0/24 gateway.
- Issue the command default-router 10.10.200.10 at the DHCP configuration prompt on the 10.10.100.0/24 LAN gateway router.
- Issue the command ip helper-address 10.10.100.0 on the router interface that is the 10.10.200.0/24 gateway.
- Issue the command network 10.10.200.0 255.255.255.0 at the DHCP configuration prompt on the 10.10.100.0/24 LAN gateway router.
99. What is used in the EUI-64 process to create an IPv6 interface ID on an IPv6 enabled interface?
- the MAC address of the IPv6 enabled interface
- a randomly generated 64-bit hexadecimal address
- an IPv6 address that is provided by a DHCPv6 server
- an IPv4 address that is configured on the interface
100. Refer to the exhibit. NAT is configured on RT1 and RT2. The PC is sending a request to the web server. What IPv4 address is the source IP address in the packet between RT2 and the web server?
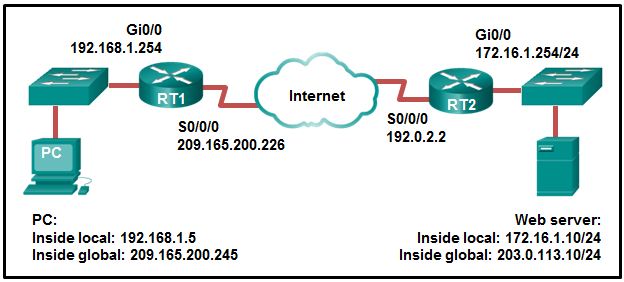
- 192.0.2.2
- 172.16.1.10
- 203.0.113.10
- 172.16.1.254
- 192.168.1.5
- 209.165.200.245
101. Refer to the exhibit. A company has an internal network of 172.16.25.0/24 for their employee workstations and a DMZ network of 172.16.12.0/24 to host servers. The company uses NAT when inside hosts connect to outside network. A network administrator issues the show ip nat translations command to check the NAT configurations. Which one of source IPv4 addresses is translated by R1 with PAT?
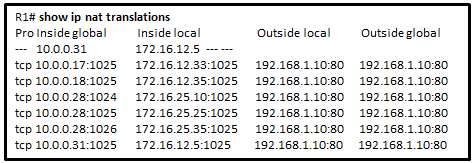
- 10.0.0.31
- 172.16.12.5
- 172.16.12.33
- 192.168.1.10
- 172.16.25.35
102. What is the purpose of the Cisco PAK?
- It is a key for enabling an IOS feature set.
- It is a proprietary encryption algorithm.
- It is a compression file type used when installing IOS 15 or an IOS upgrade.
- It is a way to compress an existing IOS so that a newer IOS version can be co-installed on a router.
103. As part of the new security policy, all switches on the network are configured to automatically learn MAC addresses for each port. All running configurations are saved at the start and close of every business day. A severe thunderstorm causes an extended power outage several hours after the close of business. When the switches are brought back online, the dynamically learned MAC addresses are retained. Which port security configuration enabled this?
- auto secure MAC addresses
- dynamic secure MAC addresses
- static secure MAC addresses
- sticky secure MAC addresses
104. A network administrator is configuring port security on a Cisco switch. The company security policy specifies that when a violation occurs, packets with unknown source addresses should be dropped and no notification should be sent. Which violation mode should be configured on the interfaces?
- off
- restrict
- protect
- shutdown
Version 5:
103. What is the major release number in the IOS image name c1900-universalk9-mz.SPA.152-3.T.bin?
- 2
- 15
- 3
- 52
- 1900
- 17
104. What is the reason that an ISP commonly assigns a DHCP address to a wireless router in a SOHO environment?
- better connectivity
- easy IP address management
- better network performance
- easy configuration on ISP firewall
105. Refer to the exhibit. What does the number 17:46:26:143 represent?
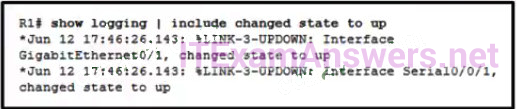
- The time passed since the syslog server has been started
- the time when the syslog massage was issued
- the time on the router when the show logging command was issued
- the time pass since the interfaces have been up
106. What statement describes a Cisco IOS image with the “universalk9_npe” designation for Cisco ISR G2 routers?
- It is an IOS version that provides only the IPBase feature set.
- It is an IOS version that, at the request of some countries, removes any strong cryptographic functionality.
- It is an IOS version that offers all of the Cisco IOS Software feature sets.
- It is an IOS version that can only be used in the United States of America.
107. Refer to the exhibit. Routers R1 and R2 are connected via a serial link. One router is configured as the NTP master, and the other is an NTP client. Which two pieces of information can be obtained from the partial output of the show ntp associations detail command on R2? (Choose two. )
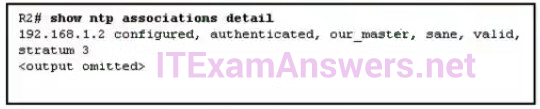
- Both routers are configured to use NTPv2.
- Router R1 is the master, and R2 is the client.
- Router R2 is the master, and R1 is the client.
- The IP address of R1 is 192. 168. 1. 2.
- The IP address of R2 is 192. 168. 1. 2.
108. A network administrator configures a router with the command sequence:
R1(config)# boot system tftp://c1900-universalk9-mz.SPA.152-4.M3.bin
R1(config)# boot system rom
What is the effect of the command sequence?
- The router will copy the IOS image from the TFTP server and then reboot the system.
- The router will load IOS from the TFTP server. If the image fails to load, it will load the IOS image from ROM
- The router will search and load a valid IOS image in the sequence of flash, TFTP, and ROM.
- On next reboot, the router will load the IOS image from ROM.
109. What is used as the default event logging destination for Cisco routers and switches?
- syslog server
- console line
- terminal line
- workstation
110. Refer to the exhibit. Which two ACLs would permit only the two LAN networks attached to R2 to access the network that connects to R1 G0/0 interface? (Choose two.)
- access-list 4 permit 192.168.10.0 0.0.0.255
- access-list 1 permit 192.168.10.128 0.0.0.127
- access-list 2 permit host 192.168.10.131
access-list 2 permit host 192.168.10.201 - access-list 5 permit 192.168.10.128 0.0.0.63
access-list 5 permit 192.168.10.192 0.0.0.63 - access-list 3 permit 192.168.10.128 0.0.0.63
111. A network administrator configures a router to provide stateful DHCPv6 operation. However, users report that workstations do not receive IPv6 addresses within the scope. Which configuration command should be checked to ensure that statefull DHCPv6 is implemented?
- The dns-server line is included in the ipv6 dhcp pool section.
- The ipv6 nd managed-config-flag is entered for the interface facing the LAN segment.
- The ipv6 nd other-config-flag is entered for the interface facing the LAN segment.
- The domain-name line is included in the ipv6 dhcp pool section.
112. Which kind of message is sent by a DHCP client when its IP address lease has expired?
- a DHCPDISCOVER broadcast message
- a DHCPREQUEST broadcast message
- a DHCPREQUEST unicast message
- a DHCPDISCOVER unicast message
113. What is a disadvantage of NAT?
- There is no end-to-end addressing.
- The router does not need to alter the checksum of the IPv4 packets.
- The internal hosts have to use a single public IPv4 address for external communication.
- The costs of readdressing hosts can be significant for a publicly addressed network.
114. Refer to the exhibit. The Gigabit interfaces on both routers have been configured with subinterface numbers that match the VLAN numbers connected to them. PCs on VLAN 10 should be able to print to the P1 printer on VLAN 12. PCs on VLAN 20 should print to the printers on VLAN 22. What interface and in what direction should you place a standard ACL that allows printing to P1 from data VLAN 10, but stops the PCs on VLAN 20 from using the P1 printer? (Choose two.)
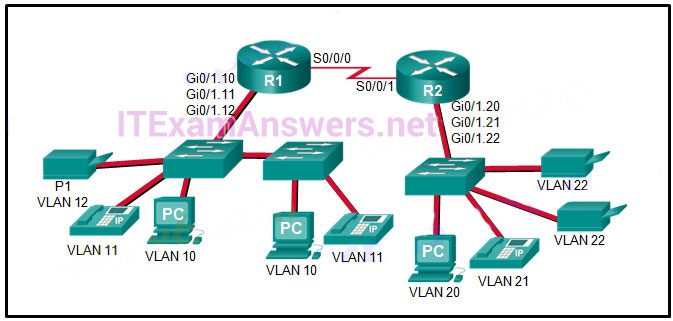
- R1 Gi0/1.12
- R1 S0/0/0
- R2 S0/0/1
- R2 Gi0/1.20
- inbound
- outbound
115. Which two packet filters could a network administrator use on an IPv4 extended ACL? (Choose two.)
- destination MAC address
- ICMP message type
- computer type
- source TCP hello address
- destination UDP port number
116. A network administrator is explaining to a junior colleague the use of the lt and gt keywords when filtering packets using an extended ACL. Where would the lt or gt keywords be used?
- in an IPv6 extended ACL that stops packets going to one specific destination VLAN
- in an IPv4 named standard ACL that has specific UDP protocols that are allowed to be used on a specific server
- in an IPv6 named ACL that permits FTP traffic from one particular LAN getting to another LAN
- in an IPv4 extended ACL that allows packets from a range of TCP ports destined for a specific network device
117. Which three values or sets of values are included when creating an extended access control list entry? (Choose three.)
- access list number between 1 and 99
- access list number between 100 and 199
- default gateway address and wildcard mask
- destination address and wildcard mask
- source address and wildcard mask
- source subnet mask and wildcard mask
- destination subnet mask and wildcard mask
118. A network administrator is adding ACLs to a new IPv6 multirouter environment. Which IPv6 ACE is automatically added implicitly at the end of an ACL so that two adjacent routers can discover each other?
- permit ip any any
- permit ip any host ip_address
- permit icmp any any nd-na
- deny ip any any
119. Refer to the exhibit. How did the router obtain the last route that is shown?

- The ip route command was used.
- The ipv6 route command was used.
- Another router in the same organization provided the default route by using a dynamic routing protocol.
- The ip address interface configuration mode command was used in addition to the network routing protocol configuration mode command.
120. Which statement is correct about IPv6 routing?
- IPv6 routing is enabled by default on Cisco routers.
- IPv6 only supports the OSPF and EIGRP routing protocols.
- IPv6 routes appear in the same routing table as IPv4 routes.
- IPv6 uses the link-local address of neighbors as the next-hop address for dynamic routes.
121. Refer to the exhibit. Which type of route is 172.16.0.0/16?
- child route
- ultimate route
- default route
- level 1 parent route
122. Refer to the exhibit. Which type of IPv6 static route is configured in the exhibit?
![]()
- directly attached static route
- recursive static route
- fully specified static route
- floating static route
123. Which summary IPv6 static route statement can be configured to summarize only the routes to networks 2001:db8:cafe::/58 through 2001:db8:cafe:c0::/58?
- ipv6 route 2001:db8:cafe::/62 S0/0/0
- ipv6 route 2001:db8:cafe::/54 S0/0/0
- ipv6 route 2001:db8:cafe::/56 S0/0/0
- ipv6 route 2001:db8:cafe::/60 S0/0/0
124. Refer to the exhibit. If RIPng is enabled, how many hops away does R1 consider the 2001:0DB8:ACAD:1::/64 network to be?

- 1
- 2
- 3
- 4
125. Which statement is true about the difference between OSPFv2 and OSPFv3?
- OSPFv3 routers use a different metric than OSPFv2 routers use.
- OSPFv3 routers use a 128 bit router ID instead of a 32 bit ID.
- OSPFv3 routers do not need to elect a DR on multiaccess segments.
- OSPFv3 routers do not need to have matching subnets to form neighbor adjacencies.
126. What happens immediately after two OSPF routers have exchanged hello packets and have formed a neighbor adjacency?
- They exchange DBD packets in order to advertise parameters such as hello and dead intervals.
- They negotiate the election process if they are on a multiaccess network.
- They request more information about their databases.
- They exchange abbreviated lists of their LSDBs.
127. What does the cost of an OSPF link indicate?
- A higher cost for an OSPF link indicates a faster path to the destination.
- Link cost indicates a proportion of the accumulated value of the route to the destination.
- Cost equals bandwidth.
- A lower cost indicates a better path to the destination than a higher cost does.
128. Which three pieces of information does a link-state routing protocol use initially as link-state information for locally connected links? (Choose three.)
- the link router interface IP address and subnet mask
- the type of network link
- the link next-hop IP address
- the link bandwidth
- the cost of that link
129. Which three requirements are necessary for two OSPFv2 routers to form an adjacency? (Choose three.)
- The OSPF hello or dead timers on each router must match.
- The link interface subnet masks must match.
- The OSPFv2 process ID must be the same on each router.
- The two routers must include the inter-router link network in an OSPFv2 network command.
- The OSPFv2 process is enabled on the interface by entering the ospf process area-id command.
- The link interface on each router must be configured with a link-local address.
130. A router needs to be configured to route within OSPF area 0. Which two commands are required to accomplish this? (Choose two.)
- RouterA(config)# router ospf 0
- RouterA(config)# router ospf 1
- RouterA(config-router)# network 192.168.2.0 0.0.0.255 0
- RouterA(config-router)# network 192.168.2.0 0.0.0.255 area 0
- RouterA(config-router)# network 192.168.2.0 255.255.255.0 0
131. What are two features of a link-state routing protocol? (Choose two.)
- Routers send periodic updates only to neighboring routers.
- Routers send triggered updates in response to a change.
- Routers create a topology of the network by using information from other routers.
- The database information for each router is obtained from the same source.
- Paths are chosen based on the lowest number of hops to the designated router.
132. Why would an administrator use a network security auditing tool to flood the switch MAC address table with fictitious MAC addresses?
- to determine which ports are not correctly configured to prevent MAC address flooding
- to determine when the CAM table size needs to be increased in order to prevent overflows
- to determine if the switch is forwarding the broadcast traffic correctly
- to determine which ports are functioning
133. Which problem is evident if the show ip interface command shows that the interface is down and the line protocol is down?
- An encapsulation mismatch has occurred.
- A cable has not been attached to the port.
- The no shutdown command has not been issued on the interface.
- There is an IP address conflict with the configured address on the interface.
134. While analyzing log files, a network administrator notices reoccurring native VLAN mismatches. What is the effect of these reoccurring errors?
- All traffic on the error-occurring trunk port is being misdirected or dropped.
- The control and management traffic on the error-occurring trunk port is being misdirected or dropped.
- All traffic on the error-occurring trunk port is being switched correctly regardless of the error.
- Unexpected traffic on the error-occurring trunk port is being received.
135. Which three pairs of trunking modes will establish a functional trunk link between two Cisco switches? (Choose three.)
- dynamic desirable – dynamic desirable
- dynamic auto – dynamic auto
- dynamic desirable – dynamic auto
- dynamic desirable – trunk
- access – trunk
- access – dynamic auto
136. What are two ways of turning off DTP on a trunk link between switches? (Choose two.)
- Change the native VLAN on both ports.
- Configure attached switch ports with the dynamic desirable command option.
- Configure attached switch ports with the nonegotiate command option.
- Configure one port with the dynamic auto command option and the opposite attached switch port with the dynamic desirable command option.
- Place the two attached switch ports in access mode.
137. On a switch that is configured with multiple VLANs, which command will remove only VLAN 100 from the switch?
- Switch# delete flash:vlan.dat
- Switch(config-if)# no switchport access vlan 100
- Switch(config-if)# no switchport trunk allowed vlan 100
- Switch(config)# no vlan 100
138. What is the purpose of setting the native VLAN separate from data VLANs?
- The native VLAN is for carrying VLAN management traffic only.
- The security of management frames that are carried in the native VLAN can be enhanced.
- A separate VLAN should be used to carry uncommon untagged frames to avoid bandwidth contention on data VLANs.
- The native VLAN is for routers and switches to exchange their management information, so it should be different from data VLANs.
139. A network contains multiple VLANs spanning multiple switches. What happens when a device in VLAN 20 sends a broadcast Ethernet frame?
- All devices in all VLANs see the frame.
- Devices in VLAN 20 and the management VLAN see the frame.
- Only devices in VLAN 20 see the frame.
- Only devices that are connected to the local switch see the frame.
140. Refer to the exhibit. The partial configuration that is shown was used to configure router on a stick for VLANS 10, 30, and 50. However, testing shows that there are some connectivity problems between the VLANs. Which configuration error is causing this problem?
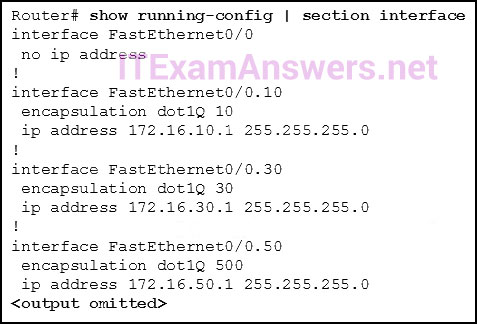
- A configuration for the native VLAN is missing.
- There is no IP address configured for the FastEthernet 0/0 interface.
- The wrong VLAN has been configured on subinterface Fa0/0.50.
- The VLAN IP addresses should belong to the same subnet.
141. What is the purpose of an access list that is created as part of configuring IP address translation?
- The access list defines the valid public addresses for the NAT or PAT pool.
- The access list defines the private IP addresses that are to be translated.
- The access list prevents external devices from being a part of the address translation.
- The access list permits or denies specific addresses from entering the device doing the translation.
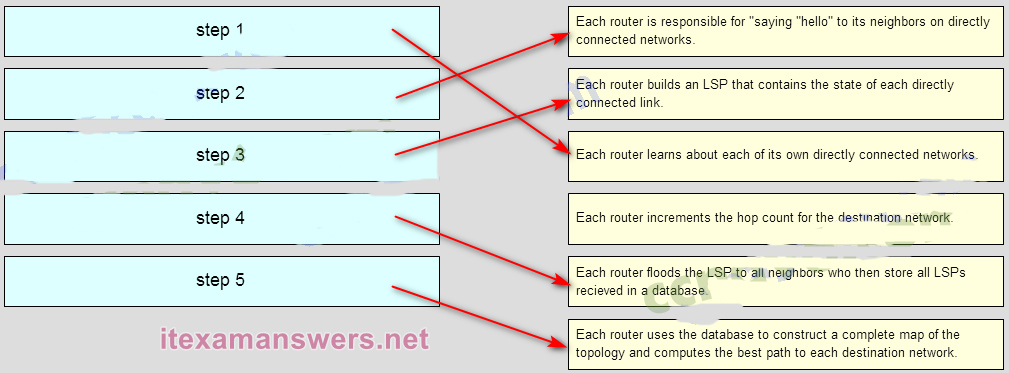
142. Match the order in which the link-state routing process occurs on a router. (Not all options are used.)
Question
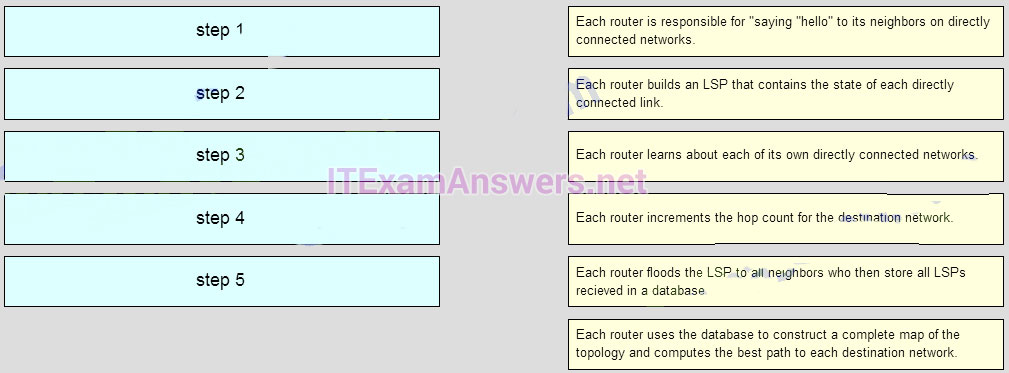
Answer
143. Beginning with the Cisco IOS Software Release 15.0, which license is a prerequisite for installing additional technology pack licenses?
- UC
- IPBase
- SEC
- DATA
144. Refer to the exhibit. How many broadcast and collision domains exist in the topology?
- 10 broadcast domains and 5 collision domains
- 5 broadcast domains and 10 collision domains
- 5 broadcast domains and 11 collision domains
- 16 broadcast domains and 11 collision domains
145. What is a function of the distribution layer?
- fault isolation
- network access to the user
- high-speed backbone connectivity
- interconnection of large-scale networks in wiring closets
146. Fill in the blank. In IPv6, all routes are level __1__ ultimate routes.
147. Fill in the blank.Static routes are configured by the use of the __ip route__ global configuration command.
148. Fill in the blank. The OSPF Type 1 packet is the __Hello__ packet.
149. Fill in the blank.The default administrative distance for a static route is __1__.
150. When a Cisco switch receives untagged frames on a 802.1Q trunk port, which VLAN ID is the traffic switched to by default?
- data VLAN ID
- native VLAN ID
- unused VLAN ID
- management VLAN ID
151. Refer to the exhibit. A Layer 3 switch routes for three VLANs and connects to a router for Internet connectivity. Which two configurations would be applied to the switch? (Choose two.)
- (config)# interface gigabitethernet 1/1
(config-if)# no switchport - (config-if)# ip address 192.168.1.2 255.255.255.252
(config)# interface vlan 1
(config-if)# ip address 192.168.1.2 255.255.255.0
(config-if)# no shutdown - (config)# interface gigabitethernet1/1
(config-if)# switchport mode trunk - (config)# interface fastethernet0/4
(config-if)# switchport mode trunk - (config)# ip routing
152. How is the router ID for an OSPFv3 router determined?
- the highest IPv6 address on an active interface
- the highest EUI-64 ID on an active interface
- the highest IPv4 address on an active interface
- the lowest MAC address on an active interface
153. Which two statements are characteristics of routed ports on a multilayer switch? (Choose two.)
- In a switched network, they are mostly configured between switches at the core and distribution layers.
- They support subinterfaces, like interfaces on the Cisco IOS routers.
- The interface vlan command has to be entered to create a VLAN on routed ports.
- They are used for point-to-multipoint links.
- They are not associated with a particular VLAN.
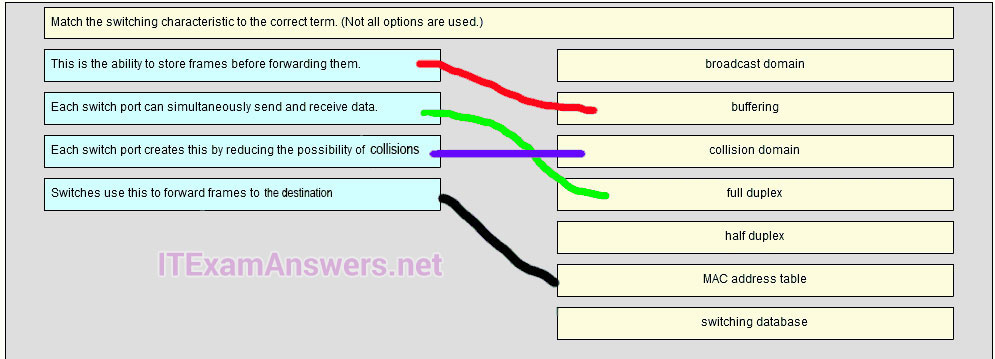
154. Match the switching characteristic to the correct term. (Not all options are used.)
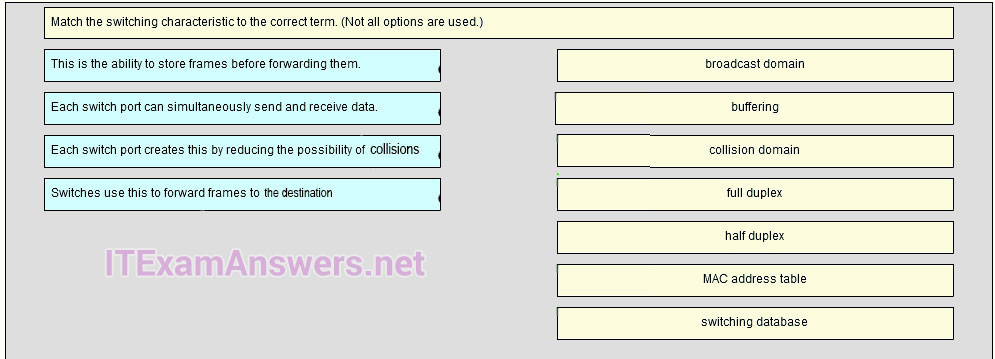
Answer
155. A small-sized company has 20 workstations and 2 servers. The company has been assigned a group of IPv4 addresses 209.165.200.224/29 from its ISP. What technology should the company implement in order to allow the workstations to access the services over the Internet?
- static NAT
- dynamic NAT
- port address translation
- DHCP
156. What best describes the operation of distance vector routing protocols?
- They use hop count as their only metric.
- They send their routing tables to directly connected neighbors.
- They flood the entire network with routing updates.
- They only send out updates when a new network is added.
157. Which three advantages are provided by static routing? (Choose three.)
- The path a static route uses to send data is known.
- No intervention is required to maintain changing route information.
- Static routing does not advertise over the network, thus providing better security.
- Static routing typically uses less network bandwidth and fewer CPU operations than dynamic routing does.
- Configuration of static routes is error-free. Static routes scale well as the network grows.
158. When configuring a switch to use SSH for virtual terminal connections, what is the purpose of the crypto key generate rsa command?
- show active SSH ports on the switch
- disconnect SSH connected hosts
- create a public and private key pair
- show SSH connected hosts
- access the SSH database configuration
159. Open the PT Activity. Perform the tasks in the activity instructions and then answer the question. What is the problem preventing PC0 and PC1 from communicating with PC2 and PC3?
- The routers are using different OSPF process IDs.
- The serial interfaces of the routers are in different subnets.
- No router ID has been configured on the routers.
- The gigabit interfaces are passive.
160. Which two commands can be used to verify the content and placement of access control lists? (Choose two.)
- show processes show cdp neighbor
- show access-lists
- show ip route
- show running-config
161. Refer to the exhibit.
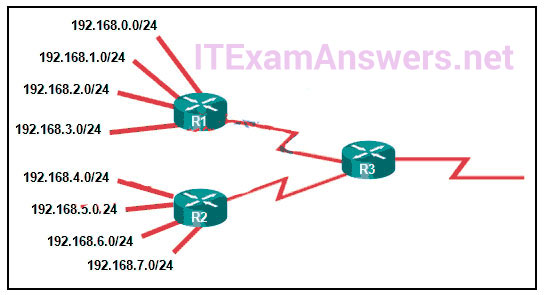
What summary static address would be configured on R1 to advertise to R3?
- 192.168.0.0/24
- 192.168.0.0/23
- 192.168.0.0/22
- 192.168.0.0/21
162. Which value represents the “trustworthiness” of a route and is used to determine which route to install into the routing table when there are multiple routes toward the same destination?
- routing protocol
- outgoing interface
- metric
- administrative distance
163. Which type of router memory temporarily stores the running configuration file and ARP table?
- flash
- NVRAM
- RAM
- ROM
164. Refer to the exhibit. If the switch reboots and all routers have to re-establish OSPF adjacencies, which routers will become the new DR and BDR?
- Router R3 will become the DR and router R1 will become the BDR.
- Router R1 will become the DR and router R2 will become the BDR.
- Router R4 will become the DR and router R3 will become the BDR.
- Router R1 will become the DR and router R2 will become the BDR.
165. Refer to the exhibit. The Branch Router has an OSPF neighbor relationship with the HQ router over the 198.51.0.4/30 network. The 198.51.0.8/30 network link should serve as a backup when the OSPF link goes down. The floating static route command ip route 0.0.0.0 0.0.0.0 S0/1/1 100 was issued on Branch and now traffic is using the backup link even when the OSPF link is up and functioning. Which change should be made to the static route command so that traffic will only use the OSPF link when it is up?
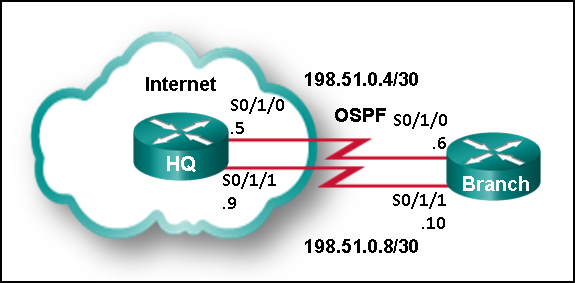
- Add the next hop neighbor address of 198.51.0.8.
- Change the administrative distance to 1.
- Change the destination network to 198.51.0.5.
- Change the administrative distance to 120.
166. Refer to the exhibit. An attacker on PC X sends a frame with two 802.1Q tags on it, one for VLAN 40 and another for VLAN 12. What will happen to this frame?
- SW-A will drop the frame because it is invalid.
- SW-A will leave both tags on the frame and send it to SW-B, which will forward it to hosts on VLAN 40.
- SW-A will remove both tags and forward the rest of the frame across the trunk link, where SW-B will forward the frame to hosts on VLAN 40.
- SW-A will remove the outer tag and send the rest of the frame across the trunk link, where SW-B will forward the frame to hosts on VLAN 12.
167. A new network policy requires an ACL to deny HTTP access from all guests to a web server at the main office. All guests use addressing from the IPv6 subnet 2001:DB8:19:C::/64. The web server is configured with the address 2001:DB8:19:A::105/64. Implementing the NoWeb ACL on the interface for the guest LAN requires which three commands? (Choose three.)
- permit tcp any host 2001:DB8:19:A::105 eq 80
- deny tcp host 2001:DB8:19:A::105 any eq 80
- deny tcp any host 2001:DB8:19:A::105 eq 80
- permit ipv6 any any
- deny ipv6 any any
- ipv6 traffic-filter NoWeb in
- ip access-group NoWeb in
168. An OSPF router has three directly connected networks; 172.16.0.0/16, 172.16.1.0/16, and 172.16.2.0/16. Which OSPF network command would advertise only the 172.16.1.0 network to neighbors?
- router(config-router)# network 172.16.1.0 0.0.255.255 area 0
- router(config-router)# network 172.16.0.0 0.0.15.255 area 0
- router(config-router)# network 172.16.1.0 255.255.255.0 area 0
- router(config-router)# network 172.16.1.0 0.0.0.0 area 0
169. Which subnet mask would be used as the classful mask for the IP address 192.135.250.27?
- 255.0.0.0
- 255.255.0.0
- 255.255.255.0
- 255.255.255.224
170. Refer to the exhibit. A small business uses VLANs 8, 20, 25, and 30 on two switches that have a trunk link between them. What native VLAN should be used on the trunk if Cisco best practices are being implemented?
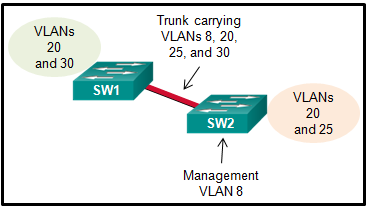
- 5
- 8
- 20
- 25
- 30
171. The buffers for packet processing and the running configuration file are temporarily stored in which type of router memory?
- Flash
- NVRAM
- RAM
- ROM
172. A standard ACL has been configured on a router to allow only clients from the 10.11.110.0/24 network to telnet or to ssh to the VTY lines of the router. Which command will correctly apply this ACL?
- access-group 11 in
- access-class 11 in
- access-list 11 in
- access-list 110 in
173. Refer to the exhibit.What address will summarize the LANs attached to routers 2-A and 3-A and can be configured in a summary static route to advertise them to an upstream neighbor?
- 10.0.0.0/24
- 10.0.0.0/23
- 10.0.0.0/22
- 10.0.0.0/21
174. A security specialist designs an ACL to deny access to a web server from all sales staff. The sales staff are assigned addressing from the IPv6 subnet 2001:db8:48:2c::/64. The web server is assigned the address 2001:db8:48:1c::50/64. Configuring the WebFilter ACL on the LAN interface for the sales staff will require which three commands? (Choose three.)
- permit tcp any host 2001:db8:48:1c::50 eq 80
- deny tcp host 2001:db8:48:1c::50 any eq 80
- deny tcp any host 2001:db8:48:1c::50 eq 80
- permit ipv6 any any
- deny ipv6 any any
- ip access-group WebFilter in
- ipv6 traffic-filter WebFilter in
175. To enable RIP routing for a specific subnet, the configuration command network 192.168.5.64 was entered by the network administrator. What address, if any, appears in the running configuration file to identify this network?
- 192.168.5.64
- 192.168.5.0
- 192.168.0.0
- No address is displayed.
176. Refer to the exhibit. An ACL preventing FTP and HTTP access to the interval web server from all teaching assistants has been implemented in the Board Office. The address of the web server is 172.20.1.100 and all teaching assistants are assigned addresses in the 172.21.1.0/24 network. After implement the ACL, access to all servers is denied. What is the problem?
- inbound ACLs must be routed before they are processed
- the ACL is implicitly denying access to all the servers
- named ACLs requite the use of port numbers
- the ACL is applied to the interface using the wrong direction
177. A router learns of multiple toward the same destination. Which value in a routing table represents the trustworthiness of learned routes and is used by the router to determine which route to install into the routing table for specific situation?
- Metric
- Colour
- Meter
- Bread
178. What is the minimum configuration for a router interface that is participating in IPv6 routing?
- Ipv6
- OSPF
- Link-access
- To have only a link-local IPv6 address
- Protocol
179. Which two statements are true about half-duplex and full-duplex communications? (Choose two.)
- Full duplex offers 100 percent potential use of the bandwidth.
- Half duplex has only one channel.
- All modern NICs support both half-duplex and full-duplex communication.
- Full duplex allows both ends to transmit and receive simultaneously.
- Full duplex increases the effective bandwidth.
180. Fill in the blank.
The acronym describes the type of traffic that has strict QoS requirements and utilizes a one-way overall delay less than 150 ms across the network. __VoIP__
181. Which two commands should be implemented to return a Cisco 3560 trunk port to its default configuration? (Choose two.)
- S1(config-if)# no switchport trunk allowed vlan
- S1(config-if)# no switchport trunk native vlan
- S1(config-if)# switchport mode dynamic desirable
- S1(config-if)# switchport mode access
- S1(config-if)# switchport access vlan 1
182. Which command will enable auto-MDIX on a device?
- S1(config-if)# mdix auto
- S1# auto-mdix S1(config-if)# auto-mdix
- S1# mdix auto S1(config)# mdix auto
- S1(config)# auto-mdix
183. What is the effect of issuing the passive-interface default command on a router that is configured for OSPF?
- Routers that share a link and use the same routing protocol
- It prevents OSPF messages from being sent out any OSPF-enabled interface.
- All of above
- Routers that share a link and use the same routing protocol
New Questions (v6.0):
184. A network administrator is implementing a distance vector routing protocol between neighbors on the network. In the context of distance vector protocols, what is a neighbor?
- routers that are reachable over a TCP session
- routers that share a link and use the same routing protocol
- routers that reside in the same area
- routers that exchange LSAs
185. Refer to the exhibit. A network administrator has just configured address translation and is verifying the configuration. What three things can the administrator verify? (Choose three.)
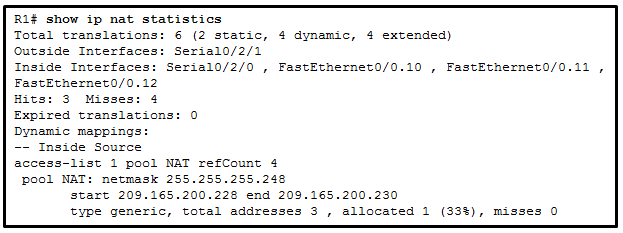
- Address translation is working.
- Three addresses from the NAT pool are being used by hosts.
- The name of the NAT pool is refCount.
- A standard access list numbered 1 was used as part of the configuration process.
- Two types of NAT are enabled.
- One port on the router is not participating in the address translation.
186. Which two methods can be used to provide secure management access to a Cisco switch? (Choose two.)
- Configure all switch ports to a new VLAN that is not VLAN 1.
- Configure specific ports for management traffic on a specific VLAN.
- Configure SSH for remote management.
- Configure all unused ports to a “black hole.”
- Configure the native VLAN to match the default VLAN.
187. A router learns of multiple routes toward the same destination. Which value in a routing table represents the trustworthiness of learned routes and is used by the router to determine which route to install into the routing table for this specific situation?
- routing protocol
- outgoing interface
- metric
- administrative distance
188. Which value in a routing table represents trustworthiness and is used by the router to determine which route to install into the routing table when there are multiple routes toward the same destination?
- administrative distance
- metric
- outgoing interface
- routing protocol
189. The network address 172.18.9.128 with netmask 255.255.255.128 is matched by which wildcard mask?
- 0.0.0.31
- 0.0.0.255
- 0.0.0.127
- 0.0.0.63
190. Which three addresses could be used as the destination address for OSPFv3 messages? (Choose three.)
- FF02::5
- FF02::6
- FF02::A
- 2001:db8:cafe::1
- FF02::1:2
- FE80::1
191. Refer to the exhibit. What is the OSPF cost to reach the West LAN 172.16.2.0/24 from East?
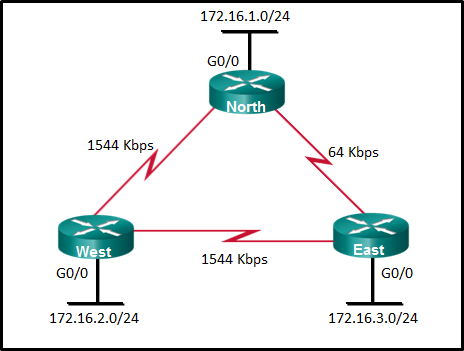
- 782
- 74
- 128
- 65
192. Refer to the exhibit. What is the OSPF cost to reach the R2 LAN 172.16.2.0/24 from R1?
- 782
- 74
- 128
- 65
193. What are two reasons that will prevent two routers from forming an OSPFv2 adjacency? (Choose two.)
- mismatched subnet masks on the link interfaces
- a mismatched Cisco IOS version that is
- used use of private IP addresses on the link interfaces
- one router connecting to a FastEthernet port on the switch and the other connecting to a GigabitEthernet port
- mismatched OSPF Hello or Dead timers
194. Refer to the exhibit. The network administrator needs as many switch ports as possible for end devices and the business is using the most common type of inter-VLAN method. What type of inter-VLAN interconnectivity is best to use between the switch and the router if R1 routes for all VLANs?
- one link between the switch and the router with the router using three router subinterfaces
- one link between the switch and the router with the one switch port being configured in access mode
- three links between the switch and the router with the three switch ports being configured in access mode
- two links between the switch and the router with the two switch ports being configured in access mode
195. Refer to the exhibit. An ACL preventing FTP and HTTP access to the internal web server from all teaching assistants has been implemented in the Board office. The address of the web server is 172.20.1.100 and all teaching assistants are assigned addresses in the 172.21.1.0/24 network. After implementing the ACL, access to all servers is denied. What is the problem?
- Inbound ACLs must be routed before they are processed.
- The ACL is implicitly denying access to all the servers.
- Named ACLs require the use of port numbers.
- The ACL is applied to the interface using the wrong direction.
196. Refer to the exhibit. A new network policy requires an ACL denying FTP and Telnet access to a Corp file server from all interns. The address of the file server is 172.16.1.15 and all interns are assigned addresses in the 172.18.200.0/24 network. After implementing the ACL, no one in the Corp network can access any of the servers. What is the problem?
- Inbound ACLs must be routed before they are processed.
- The ACL is implicitly denying access to all the servers.
- Named ACLs require the use of port numbers.
- The ACL is applied to the interface using the wrong direction.
197. Router R1 routes traffic to the 10.10.0.0/16 network using an EIGRP learned route from Branch2. The administrator would like to install a floating static route to create a backup route to the 10.10.0.0/16 network in the event that the link between R1 and Branch2 goes down. Which static route meets this goal?
ip route 10.10.0.0 255.255.0.0 209.165.200.225 100
198. Refer to the exhibit. Based on the exhibited configuration and output, why is VLAN 99 missing?
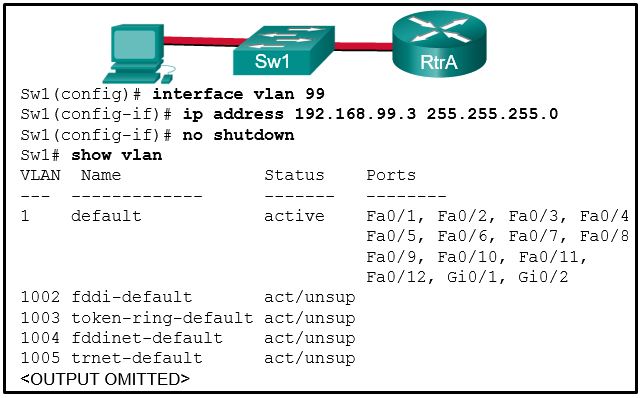
- because there is a cabling problem on VLAN 99
- because VLAN 99 is not a valid management VLAN
- because VLAN 1 is up and there can only be one management VLAN on the switch
- because VLAN 99 has not yet been created

I studied all these and sat for my exam today (5the June 2018) and this are exact questions that came in my exam. Got 100%
All the best everyone.
thank you very much ! i will donate
please add some ccna final exam dumps :)
As part of the new security policy, all switches on the network are configured to automatically learn MAC addresses for each port. All running configurations are saved at the start and close of every business day. A severe thunderstorm causes an extended power outage several hours after the close of business. When the switches are brought back online, the dynamically learned MAC addresses are retained. Which port security configuration enabled this?
26. A network technician has been asked to secure all switches in the campus network. The security requirements are for each switch to automatically learn and add MAC addresses to both the address table and the running configuration. Which port security configuration will meet these requirements?
auto secure MAC addresses
dynamic secure MAC addresses
static secure MAC addresses
sticky secure MAC addresses*
DYNAMIC
in the v6 exam, add some questions to here and as well as the test online. also, remove dupes for test online.
DHCP process steps need to be added to the test online. #90
#89 needs two answers, not just one. also for the test online.
new question: (paraphrased) network engineer is checking a config implemented by an intern for an ip phone switchport. ID the issue, if any:
r()# vlan 2222
R()# name voice
r()# int f0/20
r()# switchport mode access
r()# mls qos trust cos
r()# switchport access vlan 2222
r()# end
options:
config is correct
(answer found somewhere in a comment) spanning tree BDU guard feature is missing
there were some other suggestions for answers. the official exam would not let me get item feedback for the correct answer. just took it tonight
The correct answer is:
The configuration is correct.
Which characteristic describes cut-through switching?
Frames are forwarded without any error checking.*
Error-free fragments are forwarded, so switching accurs with lower latency.
Buffering is used to support different Ethernet
speeds.
Only outgoing frames are checked for errors.
Correct answer here differs from your practice Final exam online. The correct answer there is “Only outgong frames are checked for errors.”. Just thought I’d point that out.
ok, thank you!
does anyone think if i read all these mcq
then i will be able to pass my in-class networking exam?
SW3(config-vlan)# vlan2222
SW3(config-vlan)# name voice
SW3(config-vlan)# int fa0/20
SW3(config-if)# mls qos trust cos
SW3(config-if)# switchport mode access
SW3(config-if)# end
Refer to the exhibit. A network engineer is examining a configuration implemented by a new intern who attached an IP phone to a switch port and configured the switch. Identify the issue, if any, with the configuration.
A) The spanning-tree BPDU guard feature is missing.
B) The switch port is not configured as a trunk.
C) The configuration is correct.
D) The voice VLAN should be 150. >>>
E) There must be a data VLAN added.
C) The configuration is correct.
I am taking the exam in two weeks. Are there really that many questions?? Does anyone know where I can find a video to the practical part on PT?
As part of the new security policy, all switches on the network are configured to automatically learn MAC addresses for each port. All running configurations are saved at the start and close of every business day. A severe thunderstorm causes an extended power outage several hours after the close of business. When the switches are brought back online, the dynamically learned MAC addresses are retained. Which port security configuration enabled this?
As part of the new security policy, all switches on the network are configured to automatically learn MAC addresses for each port. All running configurations are saved at the start and close of every business day. A severe thunderstorm causes an extended power outage several hours after the close of business. When the switches are brought back online, the dynamically learned MAC addresses are retained. Which port security configuration enabled this?
auto secure MAC addresses
dynamic secure MAC addresses
static secure MAC addresses
sticky secure MAC addresses***
A network administrator is configuring port security on a Cisco switch. The company security policy specifies that when a violation occurs, packets with unknown source addresses should be dropped and no notification should be sent. Which violation mode should be configured on the interfaces?
A network administrator is configuring port security on a Cisco switch. When a violation occurs, which violation mode that is configured on an interface will cause packets with an unknown source address to be dropped with no notification sent?
off
restrict
protect* —> correct answer
shutdown
protect
In what situation would a Layer 2 switch have an IP address configured?
In what situation would a Layer 2 switch have an IP address configured ?
when the Layer 2 switch is using a routed port
when the Layer 2 switch needs to be remotely managed* —> correct answer
when the Layer 2 switch is the default gateway of user traffic
when the Layer 2 switch needs to forward user traffic to another device
Yes I did my exam yesterday and the questions were still valid.
I am confident
yayis!
I am taking this exam next month, are these still valid?
Almost Complete CCNA2 v6.0 Final Exam. Spring Q 2017.
Thank You.
Thanks so much!!
unfortunately this semester have no dumps
is there a pdf of this?
Just wondering, are these questions and answers still valid as of right now? Im taking the netacad final exam this month. Anyone can let me know?
Im taking the exam this month, is this still valid?