New Version:
1. The network administrator wants to configure a switch to pass VLAN update information to other switches in the domain but not update its own local VLAN database. Which two steps should the administrator perform to achieve this? (Choose two.)
- Reset the VTP counters.
- Configure the switch with the same VTP domain name as other switches in the network.
- Configure the VTP mode of the switch to transparent.
- Configure VTP version 1 on the switch.
- Verify that the switch has a higher configuration revision number.
2. Which statement describes the Autonomous System number that is used in EIGRP?
- It identifies the priority of the networks to be included in update packets.
- It defines the reliability of the EIGRP routing protocol.
- It is associated with the global Autonomous System number that is assigned by IANA.
- It specifies the EIGRP routing process on a router.
3. Refer to the exhibit. Which switch will be the root bridge after the election process is complete?
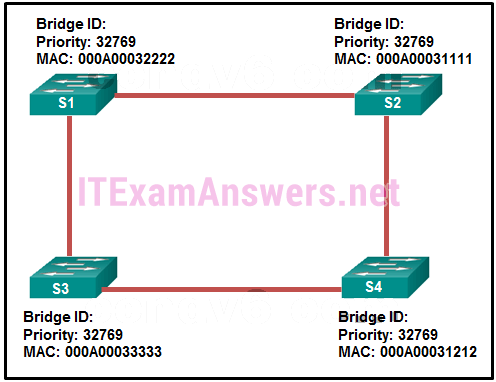
- S1
- S2
- S3
- S4
4. Refer to the exhibit. A network administrator is configuring PVST+ for the three switches. What will be a result of entering these commands?
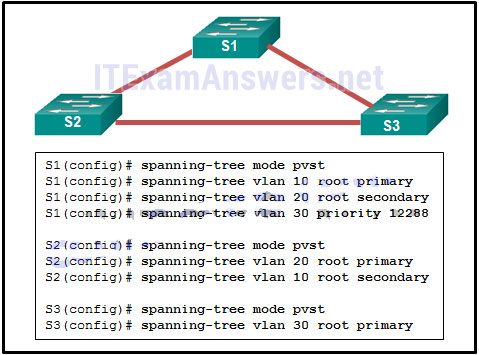
- S1 will set the priority value for VLAN 20 to 24596.
- S2 will set the priority value for VLAN 10 to 24576.
- S1 will set the priority value for VLAN 10 to 0.
- S3 will set the priority value for VLAN 30 to 8192.
5. By default, how often does a Cisco switch that is using RSTP send out BPDU frames?
- every 2 seconds
- every 4 seconds
- every 5 seconds
- every 10 seconds
6. Refer to the exhibit. Why did R1 and R2 not establish an adjacency?
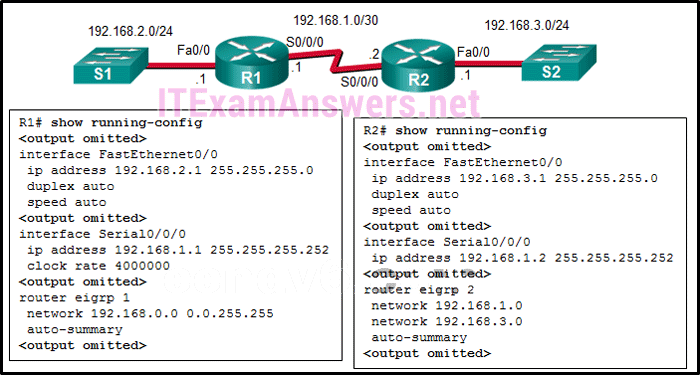
- The IPv4 address of Fa0/0 interface of R1 has a wrong IP address.
- The AS number does not match on R1 and R2.
- The automatic summarization is enabled on R1 and R2.
- There is no network command for the network 192.168.1.0/24 on R1.
7. What address type will OSPFv3 use to form adjacencies to neighboring routers?
- the all OSPF router multicast
- the link-local address of the interface
- the all-link router multicast
- the global unicast of the interface
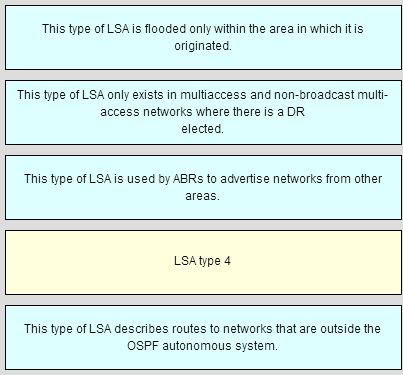
8. Which OSPF LSA type is only used in multiaccess and NBMA networks?
- type 1
- type 2
- type 3
- type 4
9. Which dynamic routing protocol uses hop count to calculate metric value?
- EIGRP
- IS-IS
- OSPF
- RIP
10. What is the default percentage of interface bandwidth that EIGRP is allowed to use for exchanging EIGRP messages?
- 50%
- 10%
- 25%
- 100%
11. How does implementing STP allow for a scalable network design?
- It prevents local traffic from propagating to other parts of the network.
- It eliminates Layer 2 loops from redundant links.
- It filters broadcasts and other undesirable traffic from the network.
- It provides failover services when duplicate network equipment is used.
12. Refer to the exhibit. Which address will R1 use as the source address for all OSPFv3 messages that will be sent to neighbors?
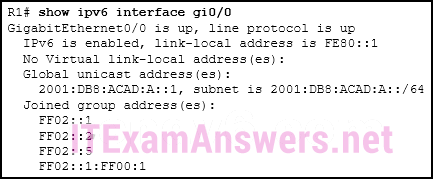
- FF02::5
- FE80::1
- 2001:DB8:ACAD:A::1
- FF02::1
13. Which wildcard mask would be used to advertise the 192.168.5.96/27 network as part of an OSPF configuration?
- 0.0.0.32
- 0.0.0.31
- 255.255.255.224
- 255.255.255.223
14. Refer to the exhibit. A network administrator has configured OSPFv2 on the two Cisco routers as shown. The routers are unable to form a neighbor adjacency. What should be done to fix the problem?
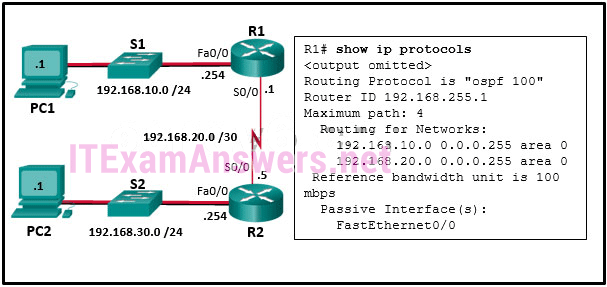
- Add the command network 192.168.30.0 0.0.0.255 area 0 on router R1.
- Change the IP address on S0/0 of router R2 to 192.168.20.2.
- Remove the FastEthernet0/0 passive interface configuration on router R1.
- Add the command network 192.168.20.1 0.0.0.0 area 0 on router R1.
15. What is one reason to use the ip ospf priority command when the OSPF routing protocol is in use?
- to activate the OSPF neighboring processto
- streamline and speed up the convergence process
- to influence the DR/BDR election process
- to provide a backdoor for connectivity during the convergence process
16. Refer to the exhibit. A Layer 3 switch routes for three VLANs and connects to a router for Internet connectivity. Which two configurations would be applied to the switch? (Choose two.)
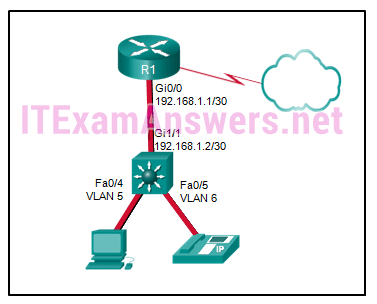
- (config)# ip routing
- (config)# interface fastethernet0/4
(config-if)# switchport mode trunk - (config)# interface vlan 1
(config-if)# ip address 192.168.1.2 255.255.255.0
(config-if)# no shutdown - (config)# interface gigabitethernet 1/1
(config-if)# no switchport
(config-if)# ip address 192.168.1.2 255.255.255.252 - (config)# interface gigabitethernet1/1
(config-if)# switchport mode trunk
17. Refer to the exhibit. A network administrator has issued the show ip eigrp neighbors command. What can be concluded from the output?
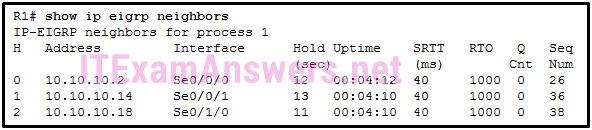
- An EIGRP neighbor with IP address 10.10.10.14 is connected to R1 via serial interface 0/1/0.
- There is no incoming EIGRP message at this moment.
- The first EIGRP neighbor R1 learned about has the IP address 10.10.10.2.
- If R1 does not receive a Hello packet in 4 seconds from the neighbor with IP 10.10.10.18, it will declare the neighbor is down.
18. Refer to the exhibit. Which command will configure unequal-cost load balancing with EIGRP on the HQ router?
- maximum-paths 1
- maximum-paths 2
- variance 2
- variance 1
19. Refer to the exhibit. Based on the command output shown, what is the status of the EtherChannel?
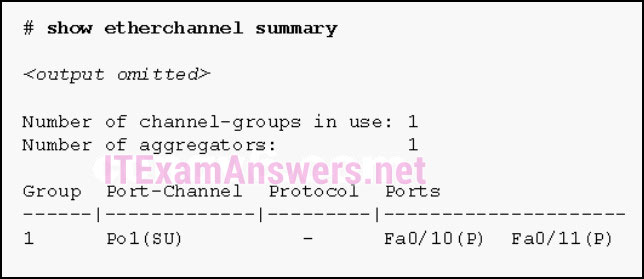
- The EtherChannel is down as evidenced by the protocol field being empty.
- The EtherChannel is in use and functional as indicated by the SU and P flags in the command output.
- The EtherChannel is partially functional as indicated by the P flags for the FastEthernet ports.
- The EtherChannel is dynamic and is using ports Fa0/10 and Fa0/11 as passive ports.
20. Which function is provided by EtherChannel?
- enabling traffic from multiple VLANs to travel over a single Layer 2 link
- creating one logical link by using multiple physical links between two LAN switches
- dividing the bandwidth of a single link into separate time slots
- spreading traffic across multiple physical WAN links
21. Which OSPFv3 function works differently from OSPFv2?
- election process
- metric calculation
- authentication
- hello mechanism
- OSPF packet types
22. What are two requirements to be able to configure an EtherChannel between two switches? (Choose two.)
- All interfaces need to be assigned to different VLANs.
- Different allowed ranges of VLANs must exist on each end.
- The interfaces that are involved need to be contiguous on the switch.
- All the interfaces need to be working in the same duplex mode.
- All the interfaces need to work at the same speed.
23. On what type of OSPF router is interarea route summarization configured?
- intra-area routers
- ASBRs
- ABRs
- backbone routers
24. Which three steps should be taken before moving a Cisco switch to a new VTP management domain? (Choose three.)
- Configure the switch with the name of the new management domain.
- Reset the VTP counters to allow the switch to synchronize with the other switches in the domain.
- Select the correct VTP mode and version.
- Download the VTP database from the VTP server in the new domain.
- Reboot the switch.
- Configure the VTP server in the domain to recognize the BID of the new switch.
25. Which two commands are used in the implementation of a dynamic IPv4 routing protocol? (Choose two.)
- lineip route
- network
- router
- interface
26. What is the reason for a network engineer to alter the default reference bandwidth parameter when configuring OSPF?
- to force that specific link to be used in the destination route
- to more accurately reflect the cost of links greater than 100 Mb/s
- to enable the link for OSPF routing
- to increase the speed of the link
27. Which technology is an open protocol standard that allows switches to automatically bundle physical ports into a single logical link?
- LACP
- PAgP
- DTP
- Multilink PPP
28. Refer to the exhibit. The partial configuration that is shown was used to configure router on a stick for VLANS 10, 30, and 50. However, testing shows that there are some connectivity problems between the VLANs. Which configuration error is causing this problem?
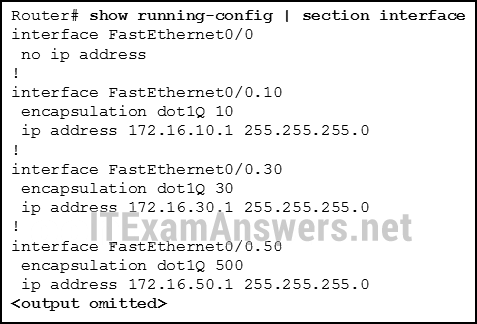
- There is no IP address configured for the FastEthernet 0/0 interface.
- The wrong VLAN has been configured on subinterface Fa0/0.50.
- A configuration for the native VLAN is missing.
- The VLAN IP addresses should belong to the same subnet.
29. Refer to the exhibit. A network administrator issues the show ip protocols command. Based on the exhibited output, what can be concluded?
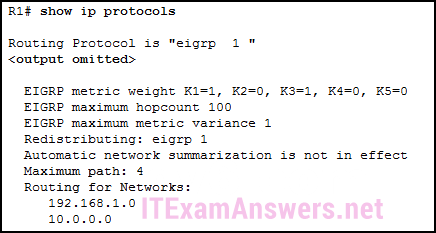
- The EIGRP K values are default values.
- R1 receives routes to the network 192.168.1.0/24 and 10.0.0.0/24.
- Up to 4 routes of different metric values to the same destination network will be included in the routing table.
- The no auto-summary command is not applied for the EIGRP operation.
30. Which two statements are characteristics of routed ports on a multilayer switch? (Choose two.)
- In a switched network, they are mostly configured between switches at the core and distribution layers.
- They are not associated with a particular VLAN.
- The interface vlan command has to be entered to create a VLAN on routed ports.
- They are used for point-to-multipoint links.
- They support subinterfaces, like interfaces on the Cisco IOS routers.
31. Which action should be taken when planning for redundancy on a hierarchical network design?
- Implement STP PortFast between the switches on the network.
- Immediately replace a nonfunctioning module, service, or device on a network.
- Purchase backup equipment for every network device at the distribution layer.
- Add alternate physical paths for data to traverse the network.
32. Refer to the exhibit. Suppose that routers B, C, and D have a default priority, and router A has a priority 0. Which conclusion can be drawn from the DR/BDR election process?
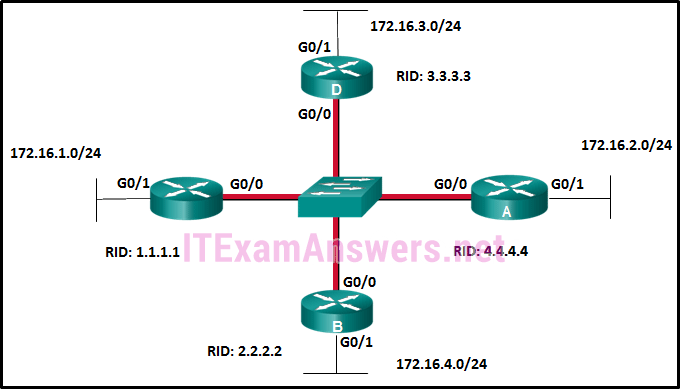
- Router A will become the DR and router D will become the BDR.
- If the priority of router C is changed to 255, then it will become the DR.
- If the DR fails, the new DR will be router B.
- If a new router with a higher priority is added to this network, it will become the DR.
33. A network administrator is troubleshooting the EIGRP routing between two routers, R1 and R2. The problem is found to be that only some, but not all networks attached to R1 are listed in the routing table of router R2. What should the administrator investigate on router R1 to determine the cause of the problem?
- Do the network commands include all the networks to be advertised?
- Does the hello interval setting match the hello interval on R2?
- Does the AS number match the AS number on R2?
- Is the interface connected to R2 configured as a passive interface?
34. Where does EIGRP maintain the list of feasible successors?
- the routing table
- the neighbor table
- the topology table
- the link-state database
35. Refer to the exhibit. On which router or routers would a default route be statically configured in a corporate environment that uses single area OSPF as the routing protocol?
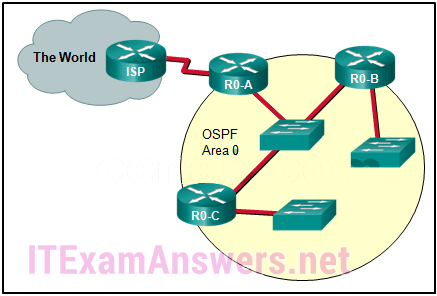
- ISP
- R0-A
- ISP and R0-A
- R0-A, R0-B, and R0-C
- R0-B and R0-C
- ISP, R0-A, R0-B, and R0-C
36. Refer to the exhibit. What will Router1 do if it receives packets that are destined to network 172.16.4.0/24?
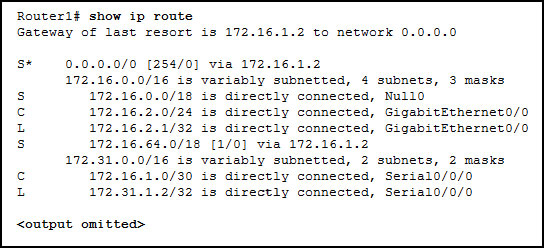
- forward the packets to the gateway of last resort
- drop the packets
- send the packets to network 0.0.0.0
- send the packets out interface GigabitEthernet 0/0
37. In a large enterprise network, which two functions are performed by routers at the distribution layer? (Choose two.)
- connect users to the network
- provide a high-speed network backbone
- connect remote networks
- provide Power over Ethernet to devices
- provide data traffic security
38. Which two metric weights are set to one by default when costs in EIGRP are being calculated? (Choose two.)
- k6
- k4
- k2
- k1
- k5
- k3
39. Open the PT Activity. Perform the tasks in the activity instructions and then answer the question.
Which message was displayed on the web server?
- Work done!
- Congratulations!
- You’ve made it!
- Wonderful work!
40. An administrator is troubleshooting an adjacency issue between two OSPFv3 routers. Which two neighbor states indicate a stable adjacency between the routers? (Choose two.)
- 2way
- full
- loading
- exstart
- exchange
41. What is the function of ASICs in a multilayer switch??
- They prevent Layer 2 loops by disabling redundant links between switches.
- They provide power to devices such as IP phones and wireless access points through Ethernet ports.
- They streamline forwarding of IP packets in a multilayer switch by bypassing the CPU.
- They aggregate multiple physical switch ports into a single logical port.
42. Which two VTP modes allow for the creation, modification, and deletion of VLANs on the local switch? (Choose two.)
- client
- server
- slave
- master
- distribution
- transparent
43. Which is a link-state routing protocol?
- OSPF
- EIGRP
- BGP
- RIP
44. Refer to the exhibit. The routing table on R2 does not include all networks that are attached to R1. The network administrator verifies that the network statement is configured to include these two networks. What is a possible cause of the issue?
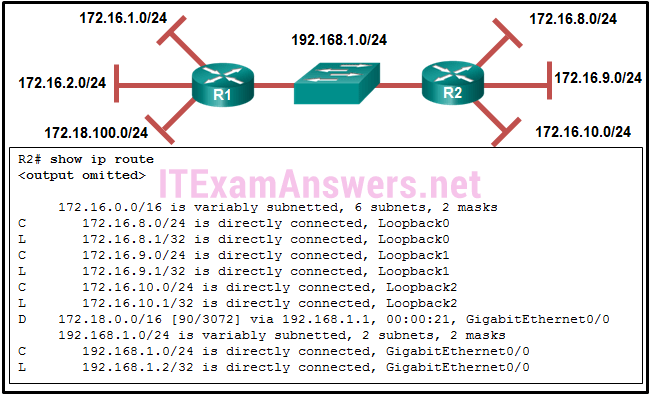
- The AS number does not match between R1 and R2.
- The network statements should include the wild card mask.
- The interfaces that are connected to these two networks are configured as passive interfaces.
- The no auto-summary command is missing in the R1 configuration.
45. Which type of OSPF LSA represents an external route and is propagated across the entire OSPF domain?
- type 1
- type 2
- type 3
- type 4
- type 5
46. Refer to the exhibit. What are three results for the DR and BDR elections for the given topologies? (Choose three.)
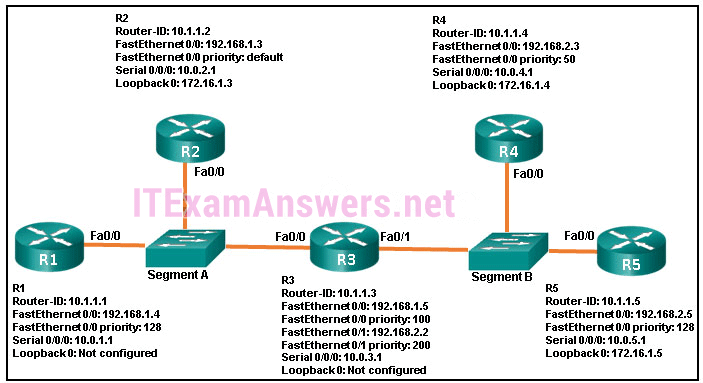
- R3 is DR for segment A.
- R3 is BDR for segment A.
- R2 is BDR for segment A.
- R1 is DR for segment A.
- R5 is BDR for segment B.
- R4 is DR for segment B.
47. Refer to the exhibit. What can be concluded about network 192.168.1.0 in the R2 routing table?
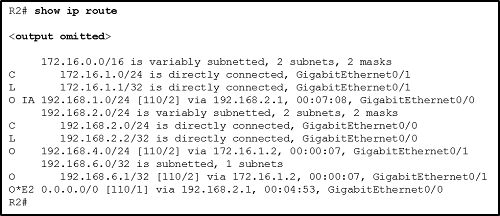
- This network was learned through summary LSAs from an ABR.
- This network is directly connected to the interface GigabitEthernet0/0.
- This network should be used to forward traffic toward external networks.
- This network has been learned from an internal router within the same area.
48. Refer to the exhibit. A network administrator has connected two switches together using EtherChannel technology. If STP is running, what will be the end result?
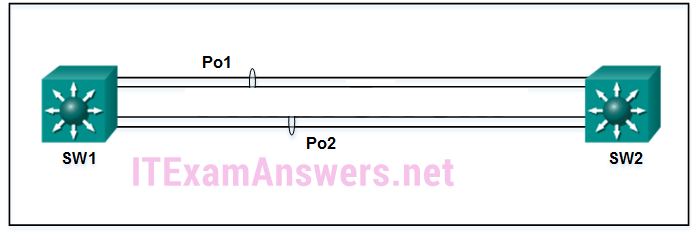
- The resulting loop will create a broadcast storm.
- STP will block one of the redundant links.
- The switches will load balance and utilize both EtherChannels to forward packets.
- Both port channels will shutdown.
49. What are two reasons to implement passive interfaces in the EIGRP configuration of a Cisco router? (Choose two.)
- to provide increased network security
- to exclude interfaces from load balancingto shut down unused interfaces
- to mitigate attacks coming from the interfaces
- to avoid unnecessary update traffic
50. Which model and which two characteristics would be more likely to be considered in purchasing an access layer switch, as compared to buying switches that operate at the other layers of the Cisco hierarchical design model? (Choose three.)
- Catalyst 4500X
- EtherChannel
- PoE
- Catalyst 2960
- number of ports
- RSTP
51. What is the order of packet types used by an OSPF router to establish convergence?
- LSU, LSAck, Hello, DBD, LSR
- Hello, DBD, LSR, LSU, LSAck
- Hello, LSAck, LSU, LSR, DBD
- LSAck, Hello, DBD, LSU, LSR
52. What two STP features are incorporated into Rapid PVST+? (Choose two.)
- BackboneFast
- loop guard
- BPDU filter
- UplinkFast
- BPDU guard
- PortFast
53. Which feature of the EIGRP routing protocol can provide fast re-convergence without DUAL recomputation in the event of a route failure?
- having a route in the passive state
- having a feasible successor route
- having a route in the active state
- having a successor route
54. What is the function of STP in a scalable network?
- It combines multiple switch trunk links to act as one logical link for increased bandwidth.
- It decreases the size of the failure domain to contain the impact of failures.
- It protects the edge of the enterprise network from malicious activity.
- It disables redundant paths to eliminate Layer 2 loops.
55. As the network administrator you have been asked to implement EtherChannel on the corporate network. What does this configuration consist of?
- providing redundant devices to allow traffic to flow in the event of device failure
- grouping two devices to share a virtual IP address
- providing redundant links that dynamically block or forward traffic
- grouping multiple physical ports to increase bandwidth between two switches
56. Refer to the exhibit. If the switch has been configured for PVST+ mode, what command output would replace the question marks?
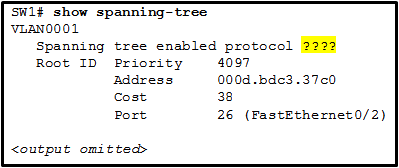
- ieee
- pvst+
- pvst
- rstp
57. Refer to the exhibit. An administrator attempts to configure EIGRP for IPv6 on a router and receives the error message that is shown. Which command must be issued by the administrator before EIGRP for IPv6 can be configured?
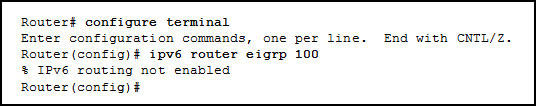
- ipv6 unicast-routing
- eigrp router-id 100.100.100.100
- ipv6 eigrp 100
- no shutdown
- ipv6 cef
58. For troubleshooting missing EIGRP routes on a router, what three types of information can be collected using the show ip protocols command? (Choose three.)
- any ACLs that are affecting the EIGRP routing process
- any interfaces that are enabled for EIGRP authentication
- the local interface that is used to establish an adjacency with EIGRP neighbors
- the IP addresses that are configured on adjacent routers
- networks that are unadvertised by the EIGRP routing protocol
- any interfaces on the router that are configured as passive
59. In which IOS CLI mode must a network administrator issue the maximum-paths command to configure load balancing in EIGRP?
- router configuration mode
- privileged mode
- interface configuration mode
- global configuration mode
60. A network engineer is configuring a LAN with a redundant first hop to make better use of the available network resources. Which protocol should the engineer implement?
- GLBP
- HSRP
- VRRP
- FHRP
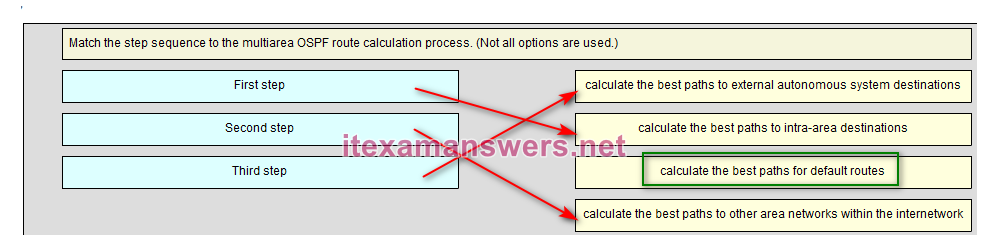
61. Match the step sequence to the multiarea OSPF route calculation process. (Not all options are used.)
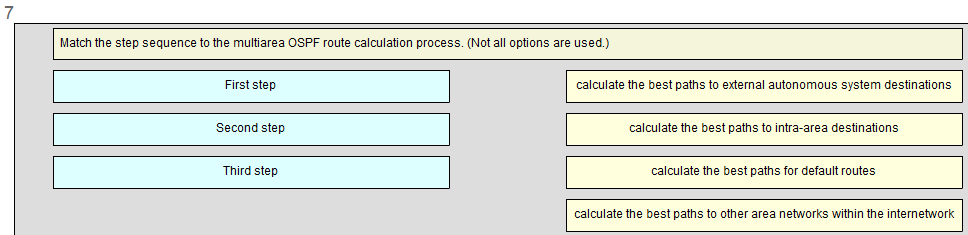
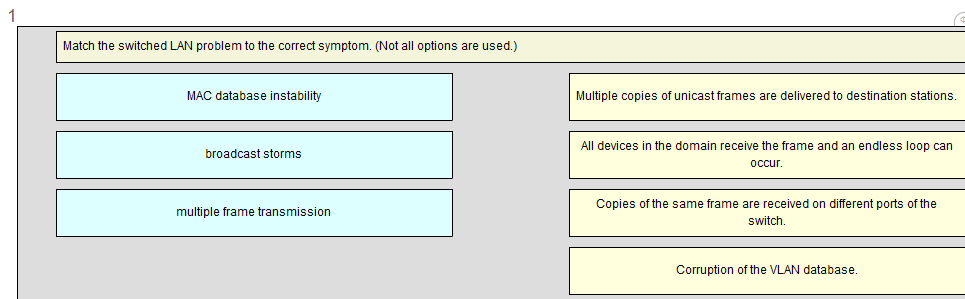
62. Match the switched LAN problem to the correct symptom. (Not all options are used.)
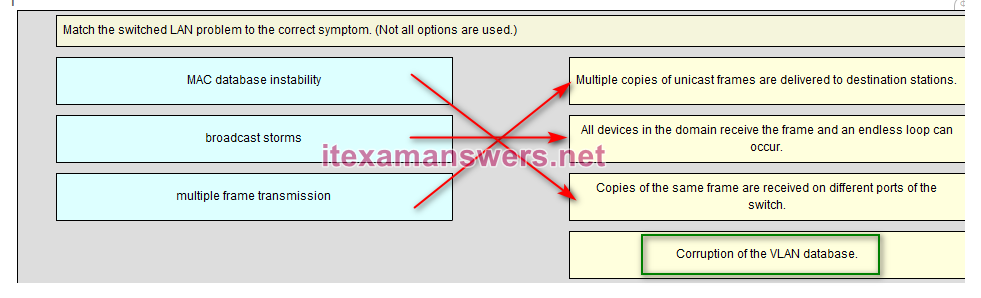
63. Match the port state with its condition. (Not all options are used.)
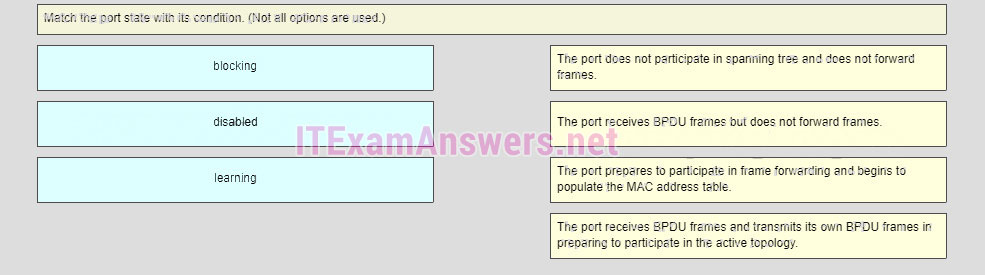
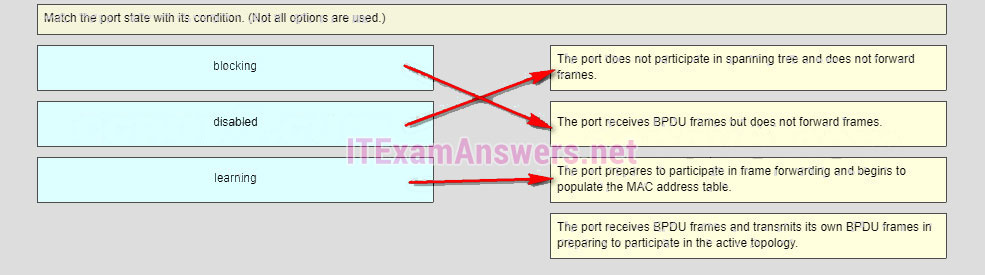
- The port does not participate in spanning tree and does not forward frames. –> disabled
- The port receives BPDU frames but does not forward frames. –> blocking
- The port prepares to participate in frame forwarding and begins to populate the MAC address table. –> learning
- The port receives BPDU frames and transmits its own BPDU frames in preparing to participate in the active topology. –> (none)
Older Version:
64. Which technological factor determines the impact of a failure domain?
- the number of layers of the hierarchical network
- the number of users on the access layer
- the role of the malfunctioning device
- the forwarding rate of the switches used on the access layer
65. Which routing protocol is able to scale for large networks and utilizes non-backbone areas for expansion?
- EIGRP
- BGP
- OSPF
- RIPv2
66. What are two reasons to install a single 48-port fixed configuration switch, rather than two 24-port fixed configuration switches, in a wiring closet that supports two classrooms? (Choose two.)
- more power provided to each port
- more ports available for end devices
- higher uplink speeds
- reduced power and space requirements
- reduced number of VLANs/broadcast domains
67. In the Cisco hierarchical design model, which layer is more likely to have a fixed configuration switch than the other layers?
- distribution
- transport
- internet
- access
- core
68. What are two requirements when using out-of-band configuration of a Cisco IOS network device? (Choose two.)
- HTTP access to the device
- a terminal emulation client
- Telnet or SSH access to the device
- a direct connection to the console or AUX port
- a connection to an operational network interface on the device
69. Which port role is assigned to the switch port that has the lowest cost to reach the root bridge?
- root port
- non-designated port
- designated port
- disabled port
70. Refer to the exhibit. A network administrator is verifying the bridge ID and the status of this switch in the STP election. Which statement is correct based on the command output?
- The bridge priority of Switch_2 has been lowered to a predefined value to become the root bridge.
- The bridge priority of Switch_2 has been lowered to a predefined value to become the backup root bridge.
- The STP instance on Switch_2 is failing due to no ports being blocked and all switches believing they are the root.
- The STP instance on Switch_2 is using the default STP priority and the election is based on Switch_2 MAC address.
71. When the show spanning-tree vlan 33 command is issued on a switch, three ports are shown in the forwarding state. In which two port roles could these interfaces function while in the forwarding state? (Choose two.)
- disabled
- designated
- root
- alternate
- blocked
72. A network administrator is analyzing first-hop router redundancy protocols. What is a characteristic of VRRPv3?
- VRRPv3 is Cisco proprietary.
- It supports IPv6 and IPv4 addressing.
- It works together with HSRP.
- It allows load balancing between routers.
73. Refer to the exhibit. Which switching technology would allow data to be transmitted over each access layer switch link and prevent the port from being blocked by spanning tree due to the redundant link?
- EtherChannel
- HSRP
- PortFast
- trunking
74. A network administrator has configured an EtherChannel between two switches that are connected via four trunk links. If the physical interface for one of the trunk links changes to a down state, what happens to the EtherChannel?
- The EtherChannel will transition to a down state.
- Spanning Tree Protocol will recalculate the remaining trunk links.
- The EtherChannel will remain functional.
- Spanning Tree Protocol will transition the failed physical interface into forwarding mode.
75. What are two advantages of EtherChannel? (Choose two.)
- Configuring the EtherChannel interface provides consistency in the configuration of the physical links.
- Load balancing occurs between links configured as different EtherChannels.
- EtherChannel uses upgraded physical links to provide increased bandwidth.
- Spanning Tree Protocol views the physical links in an EtherChannel as one logical connection.
- Spanning Tree Protocol ensures redundancy by transitioning failed interfaces in an EtherChannel to a forwarding state.
76. When a range of ports is being configured for EtherChannel, which mode will configure LACP on a port only if the port receives LACP packets from another device?
- active
- auto
- desirable
- passive
77. Which two parameters must match on the ports of two switches to create a PAgP EtherChannel between the switches? (Choose two.)
- MAC address
- speed
- VLAN information
- PAgP mode
- port ID
78. When EtherChannel is configured, which mode will force an interface into a port channel without exchanging aggregation protocol packets?
- active
- auto
- on
- desirable
79. Which IOS 12.4 software package integrates full features, including voice, security, and VPN capabilities, for all routing protocols?
- Advanced Security
- Advanced IP Services
- Advanced Enterprise Services
- Service Provider Services
80. What is the major release number in the IOS image name c1900-universalk9-mz.SPA.152-3.T.bin?
- 2
- 3
- 15
- 52
- 1900
81. Which statement describes a difference between the IOS 15.0 extended maintenance release and a standard maintenance release?
- They consist of two separate parallel trains.
- The extended maintenance release will deliver new IOS features as soon as they are available.
- The standard maintenance release enables faster IOS feature delivery than the extended maintenance release does.
- A new standard maintenance release will synchronize with the latest extended maintenance release before the extended is made available.
82. When a router is powered on, where will the router first search for a valid IOS image to load by default?
- RAM
- ROM
- flash memory
- NVRAM
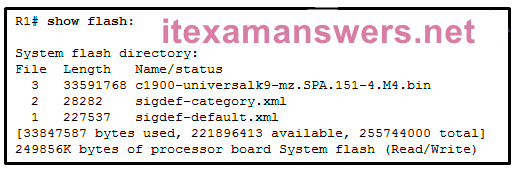
83. A network engineer is upgrading the Cisco IOS image on a 2900 series ISR. What command could the engineer use to verify the total amount of flash memory as well as how much flash memory is currently available?
- show flash0:
- show version
- show interfaces
- show startup-config
84. A network administrator configures a router with the command sequence:R1(config)# boot system tftp://c1900-universalk9-mz.SPA.152-4.M3.bin
R1(config)# boot system rom
What is the effect of the command sequence?
- On next reboot, the router will load the IOS image from ROM.
- The router will copy the IOS image from the TFTP server and then reboot the system.
- The router will load IOS from the TFTP server. If the image fails to load, it will load the IOS image from ROM.
- The router will search and load a valid IOS image in the sequence of flash, TFTP, and ROM.
85. Beginning with the Cisco IOS Software Release 15.0, which license is a prerequisite for installing additional technology pack licenses?
- IPBase
- DATA
- UC
- SEC
86. Which three software packages are available for Cisco IOS Release 15.0?
- DATA
- IPVoice
- Security
- Enterprise Services
- Unified Communications
- Advanced IP Services
87. When a customer purchases a Cisco IOS 15.0 software package, what serves as the receipt for that customer and is used to obtain the license as well?
- Software Claim Certificate
- End User License Agreement
- Unique Device Identifier
- Product Activation Key
88. Which command would a network engineer use to find the unique device identifier of a Cisco router?
- show version
- show license udi
- show running-configuration
- license install stored-location-url
89. A newly hired network engineer wants to use a 2911 router from storage. What command would the technician use to verify which IOS technology licenses have been activated on the router?
- show flash0:
- show interfaces
- show license
- show startup-config
- show version
90. Which command is used to configure a one-time acceptance of the EULA for all Cisco IOS software packages and features?
- license save
- show license
- license boot module module-name
- license accept end user agreement
91. How long is the evaluation license period for Cisco IOS Release 15.0 software packages?
- 15 days
- 30 days
- 60 days
- 180 days
92. What is the purpose of a T train release in Cisco IOS 15?
- It is used for long-term maintenance, enabling customers to qualify, deploy, and remain on the release for an extended period.
- It provides regular bug fix maintenance rebuilds, plus critical fix support for network-affecting bugs.
- It provides premium packages and enables additional IOS software feature combinations that address more complex network requirements.
- It specifies advanced IP services features such as advanced security and service provider packages.
93. What code in the Cisco IOS 15 image filename c1900-universalk9-mz.SPA.153-3.M.bin indicates that the file is digitally signed by Cisco?
- SPA
- universalk9
- M
- mz
94. A network technician is troubleshooting problems with a router that is running IOS 15. Which command will display the features activated for the licenses that are installed on the router?
- show flash0:
- show license
- show startup-config
- show version
95. Which wireless network topology would be used by network engineers to provide a wireless network for an entire college building?
- ad hoc
- hotspot
- infrastructure
- mixed mode
96. In wireless networks what is a disadvantage of using mixed mode on an AP?
- Only 802.11n wireless NICs can attach to the AP.
- Devices must be closer to the AP due to the limited distance range.
- The wireless network operates slower if one device uses an older standard wireless NIC.
- No encryption can be used by the AP or by the wireless NIC that is attached to the AP.
97. When would a network engineer configure an access point with channel bonding?
- when security is an issue
- when more throughput is needed
- when older wireless NICs are being used
- when trunking is enabled between the access point and switch
98. Which method of wireless authentication is currently considered to be the strongest?
- WEP
- WPA
- WPA2
- open
- shared key
99. What is a wireless security mode that requires a RADIUS server to authenticate wireless users?
- enterprise
- personal
- shared key
- WEP
100. A laptop cannot connect to a wireless access point. Which two troubleshooting steps should be taken first? (Choose two.)
- Ensure that the wireless NIC is enabled.
- Ensure that the laptop antenna is attached.
- Ensure that the wireless SSID is chosen.
- Ensure that the correct network media is selected.
- Ensure that the NIC is configured for the proper frequency.
101. A network engineer is troubleshooting a newly deployed wireless network that is using the latest 802.11 standards. When users access high bandwidth services such as streaming video, the wireless network performance is poor. To improve performance the network engineer decides to configure a 5 Ghz frequency band SSID and train users to use that SSID for streaming media services. Why might this solution improve the wireless network performance for that type of service?
- The 5 GHz band has a greater range and is therefore likely to be interference-free.
- Requiring the users to switch to the 5 GHz band for streaming media is inconvenient and will result in fewer users accessing these services.
- The 5 GHz band has more channels and is less crowded than the 2.4 GHz band, which makes it more suited to streaming multimedia.
- The only users that can switch to the 5 GHz band will be those with the latest wireless NICs, which will reduce usage.
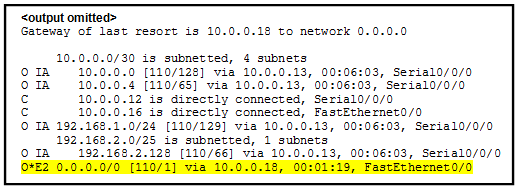
102. Refer to the exhibit. How did this router learn of the highlighted route in the routing table?
- by entering the router configuration mode command default-information originate
- by entering the global configuration mode command ip route 0.0.0.0 0.0.0.0 interface-type interface-number
- by entering the global configuration mode command ip route 0.0.0.0 0.0.0.0 ip-address
- by receiving an update from another OSPF router that is running another routing protocol
- by receiving an update from another OSPF router that has the default-information originate command configured
103. Refer to the exhibit. What are two consequences of issuing the displayed commands? (Choose two.)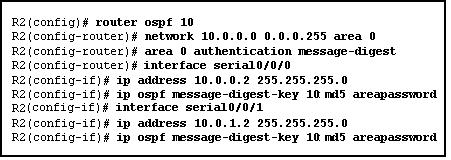
- The routing update information is protected against being falsified.
- The routing table of R2 will be secured.
- The key is encrypted with the MD5 hashing algorithm.
- OSPF routes will get priority over EIGRP routes going into the routing table.
- The overhead of OSPF information exchange will reduce.
104. What does an OSPF area contain?
- routers that share the same router ID
- routers whose SPF trees are identical
- routers that have the same link-state information in their LSDBs
- routers that share the same process ID
105. Refer to the exhibit. Why are some of the entries marked O IA?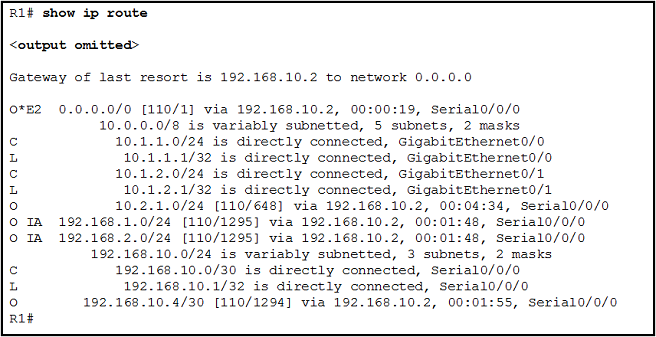
- They correspond to entries that are learned from other areas.
- They correspond to entries that are learned from other routing protocols.
- They represent summary routes that are internal to the area.
- They are default routes that are learned from other routing protocols.
106. In which mode is the area area-id range address mask command issued when multiarea OSPF summarization is being configured?
- global configuration mode
- router configuration mode
- interface configuration mode of area 0 interfaces
- interface configuration mode of all participating interfaces
107. Refer to the exhibit. What two pieces of information could be determined by a network administrator from this output? (Choose two.)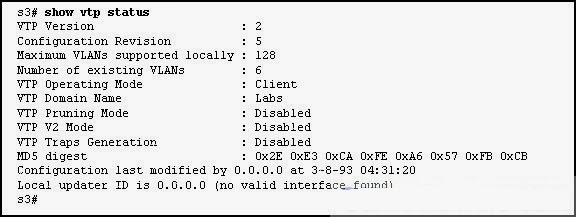
- R1 is participating in multiarea OSPF.
- The OSPF process number that is being used is 0.
- Interface Fa0/1 is not participating in the OSPF process.
- R1 is the distribution point for the routers that are attached to the 10.0.0.4 network.
- The metric that will be installed in the routing table for the 10.0.0.0 route will be 65 (64+1).
108. Refer to the exhibit. Two routers have been configured to use EIGRP. Packets are not being forwarded between the two routers. What could be the problem?
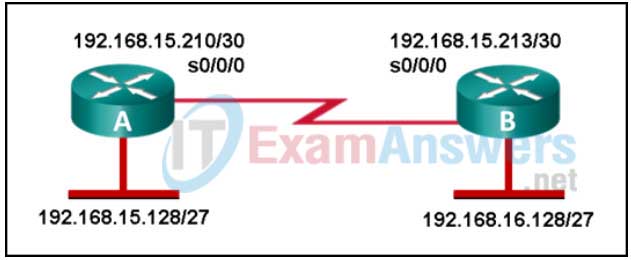
- EIGRP does not support VLSM.
- The routers were not configured to monitor neighbor adjacency changes.
- The default bandwidth was used on the routers.
- An incorrect IP address was configured on a router interface.
109. Which command can be issued on a router to display information about the successors and feasible successors for a destination network when EIGRP is used as the routing protocol?
- show ip protocols
- show ip eigrp topology
- show ip eigrp interfaces
- show ip eigrp neighbors
110. A network administrator is configuring the authentication for EIGRP routing. The administrator enters these commands:R1(config)# key chain THE_KEY
R1(config-keychain)# key 1
R1(config-keychain-key)# key-string key123What is the next step necessary to enable the authentication for EIGRP routing?
- Configure the priority of authentication algorithms to be used.
- Configure the authentication on all interfaces that are participating in EIGRP.
- Configure an ACL to identify the networks that are participating in EIGRP.
- Configure the authentication in the router eigrp as-number configuration mode.
111. What are three characteristics of the Cisco IOS Software Release 12.4T train? (Choose three.)
- It requires the activation of a license.
- It has a number of embedded technology packages.
- It is updated with new features and hardware support.
- It is derived from the Cisco IOS Software Release 12.4 Mainline train.
- It has extended maintenance new feature releases approximately every 16 to 20 months.
- It receives regular software fixes that are synchronized with the 12.4 Mainline train.
112. If a company wants to upgrade a Cisco 2800 router from IOS 12.4T, what IOS should be recommended for a stable router platform?
- 12.5T
- 13.1T
- 14.0
- 15.1M
113. A router has been removed from the network for maintenance. A new Cisco IOS software image has been successfully downloaded to a server and copied into the flash of the router. What should be done before placing the router back into service?
- Back up the new image.
- Copy the running configuration to NVRAM.
- Delete the previous version of the Cisco IOS software from flash.
- Restart the router and verify that the new image starts successfully.
114. Which step supports disaster recovery and should be performed first when upgrading an IOS system image on a Cisco router?
- Delete the current image from flash memory.
- Copy the current image from the router to a TFTP server.
- Use the boot system command to configure the router to load the new image.
- Configure the router to load the new image from the TFTP server.
115. Refer to the exhibit. A network engineer is preparing to upgrade the IOS system image on a Cisco 2901 router. Based on the output shown, how much space is available for the new image?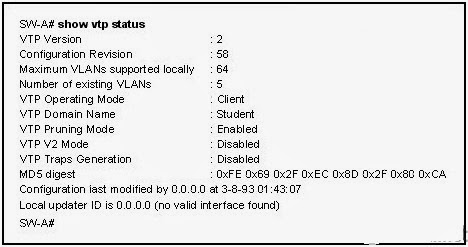
- 25574400 bytes
- 249856000 bytes
- 221896413 bytes
- 33591768 bytes
116. The customer of a networking company requires VPN connectivity for workers who must travel frequently. To support the VPN server, the customer router must be upgraded to a new Cisco IOS software version with the Advanced IP Services feature set. What should the field engineer do before copying the new IOS to the router?
- Set the router to load the new IOS image file directly from the TFTP server on the next reboot.
- Delete the currently installed IOS by using the erase flash: command, and reload the router.
- Issue the show running-configuration command to determine the features of the currently installed IOS image file.
- Issue the show version and the show flash commands to ensure that the router has enough memory and file space to support the new IOS image.
117. Match each OSPF LSA description with its type. (Not all options are used.)
118. Open the PT Activity. Perform the tasks in the activity instructions and then answer the question.Why are users in the OSPF network not able to access the Internet?
- The default route is not redistributed correctly from router R1 by OSPF.
- The interface that is connected to the ISP router is down.
- The OSPF network statements are misconfigured on routers R2 and R3.
- The OSPF timers that are configured on routers R1, R2, and R3 are not compatible.
- The network statement is misconfigured on router R1.
119. Which command will start the process to bundle two physical interfaces to create an EtherChannel group via LACP?
- channel-group 2 mode auto
- interface port-channel 2
- channel-group 1 mode desirable
- interface range GigabitEthernet 0/4 – 5
120. What statement describes a Cisco IOS image with the “universalk9_npe” designation for Cisco ISR G2 routers?
- It is an IOS version that, at the request of some countries, removes any strong cryptographic functionality.
- It is an IOS version that provides only the IPBase feature set.
- It is an IOS version that offers all of the Cisco IOS Software feature sets.
- t is an IOS version that can only be used in the United States of America.
121. Fill in the blank. Do not use abbreviations.
The license ” install” flash0:seck9-C1900-SPE150_K9-FAB12340099.xml command will restore the specified saved Cisco IOS Release 15 license to a router.
122. Refer to the exhibit. Match the components of the IOS image name to their description. (Not all options are used.)
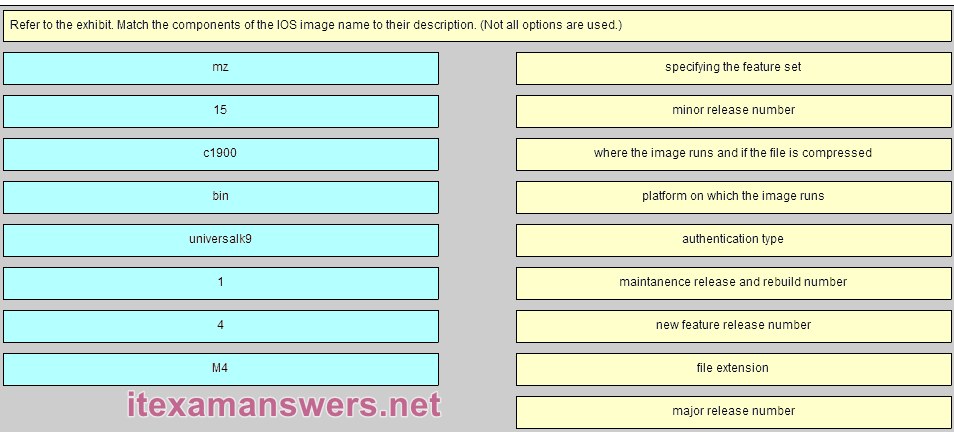
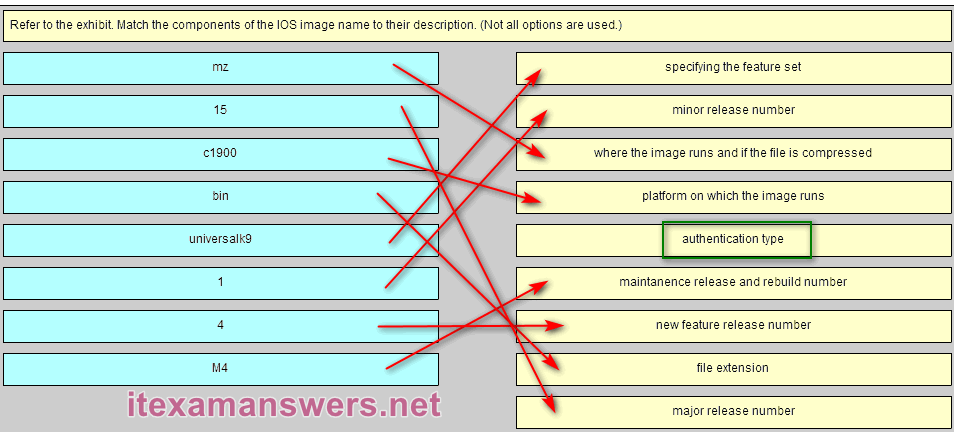
Place the options in the following order:
specifying the feature set -> universalk9
minor release number -> 1
where the image runs and if the file is compressed -> mz
platform on which the image runs -> c1900
– not scored –
maintanence release and rebuild number -> M4
new feature release number -> 4
file extension -> bin
major release number -> 15
123. Match the description to the Cisco IOS category. (Not all options apply.)
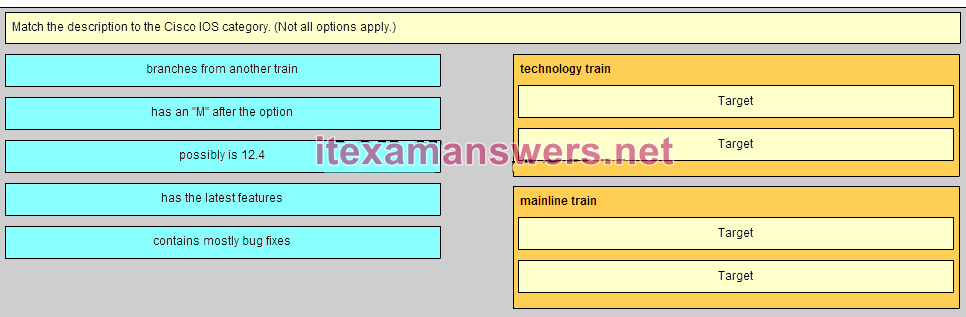
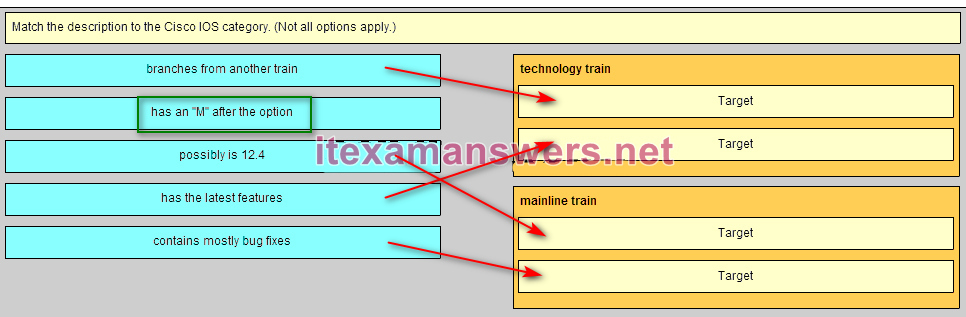
Place the options in the following order:
technology train
[+] branches from another train
[+] has the latest features
mainline train
[#] possibly is 12.4
[#] contains mostly bug fixes
124. Refer to the exhibit. 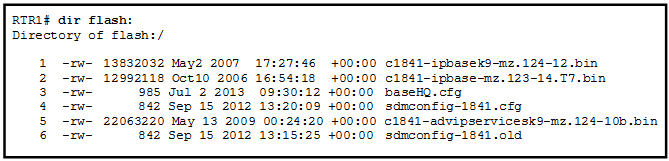 Which of the three Cisco IOS images shown will load into RAM?
Which of the three Cisco IOS images shown will load into RAM?
- The router selects the second Cisco IOS image because it is the smallest IOS image.
- The router selects an image depending on the boot system command in the configuration.
- The router selects the third Cisco IOS image because it contains the advipservicesk9 image.
- The router selects the third Cisco IOS image because it is the most recent IOS image.
- The router selects an image depending on the value of the configuration register.
125. In addition to IPBase, what are the three technology packs that are shipped within the universal Cisco IOS Software Release 15 image? (Choose three.)
- Advanced IP Services
- SP Services
- Unified Communications
- Security
- DATA
126. Which two conditions should the network administrator verify before attempting to upgrade a Cisco IOS image using a TFTP server? (Choose two.)
- Verify the name of the TFTP server using the show hosts command.
- Verify that the TFTP server is running using the tftpdnld command.
- Verify that the checksum for the image is valid using the show version command.
- Verify connectivity between the router and TFTP server using the ping command.
- Verify that there is enough flash memory for the new Cisco IOS image using the show flash command.
127. Which three images are considered premium software packages for Cisco IOS Release 12.4? (Choose three.)
- IP Voice
- Enterprise Base
- Advanced Security
- Enterprise Services
- Advanced IP Services
- Advanced Enterprise Services
128. What are two reasons to enable OSPF routing protocol authentication on a network? (Choose two.)
- to prevent data traffic from being redirected and then discarded
- to ensure faster network convergence
- to provide data security through encryption
- to prevent redirection of data traffic to an insecure link
- to ensure more efficient routing
129. While attending a conference, participants are using laptops for network connectivity. When a guest speaker attempts to connect to the network, the laptop fails to display any available wireless networks. The access point must be operating in which mode?
- active
- passive
- mixed
- open
130. What is the purpose of issuing the ip ospf message-digest-key key md5 password command and the area area-id authentication message-digest command on a router?
- to facilitate the establishment of neighbor adjacencies
- to encrypt OSPF routing updates
- to enable OSPF MD5 authentication on a per-interface basis
- to configure OSPF MD5 authentication globally on the router
131. Refer to the exhibit. Which destination MAC address is used when frames are sent from the workstation to the default gateway?
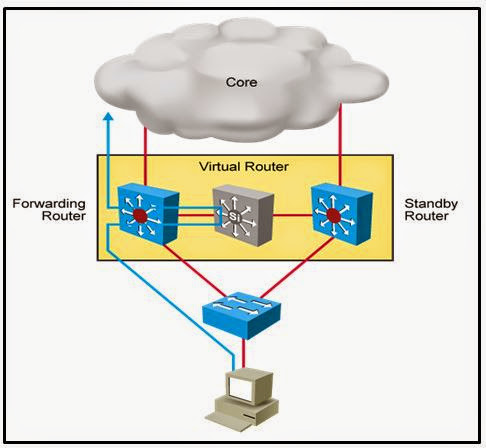
- MAC addresses of both the forwarding and standby routers
- MAC address of the forwarding router
- MAC address of the standby router
- MAC address of the virtual router
132. A network technician is attempting to upgrade an IOS system image on a Cisco 1941 router. Which command should the technician issue to verify the presence of sufficient free space in flash for the new image on the router that is being upgraded?
- show file system
- show flash0:
- show running-config
- show version
133. Which statement describes a characteristic of a Cisco Enterprise Architecture module?
- Server Farm and Data Center Module are submodules of the Enterprise Edge module.
- The Enterprise Campus only consists of the core layer of the campus infrastructure.
- The Enterprise Edge consists of the Internet, VPN, and WAN modules connecting the enterprise with the service provider’s network.
- The Service Provider Edge provides QoS, policy reinforcement, service levels, and security.
134. Match the step number to the sequence of stages that occur during the HSRP failover process. (Not all options are used.)
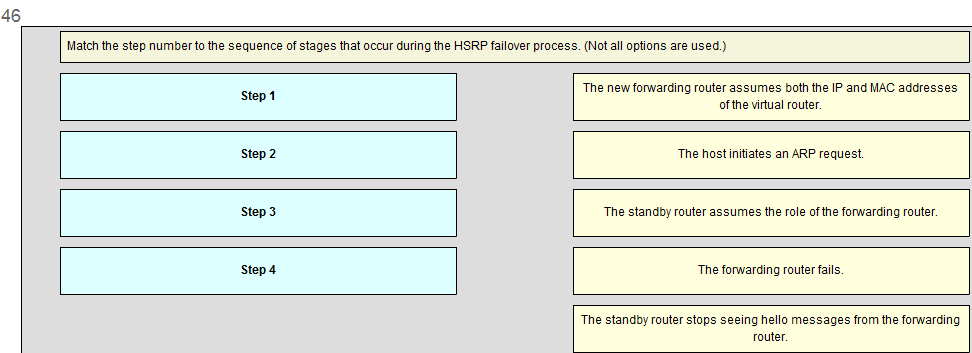
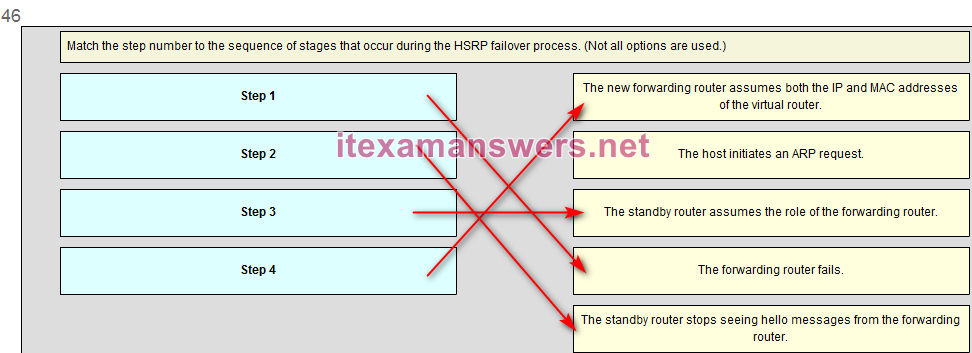

Match the port state with its condition. (Not all options are used.)
answer:
disabled
blocking
learning
–
Thanks you!
Thank you!
100% thanks
When should EIGRP automatic summarization be turned off?
By default, how often does a Cisco switch that is using RSTP send out BPDU frames?
Which is a link-state routing protocol?
EIGRP
BGP
OSPF
RIP
Open the PT Activity. Perform the tasks in the activity instructions and then answer the question.
Which message was displayed on the web server
Wonderful work!
Congratulations!
You’ve made it!
Work done!
The three routers R1, R2 and R3 implement EIGRP as the routing protocol. There are two discontiguous networks with no connectivity between them. Automatic summarization is enabled by default on routers R1 and R2, and this is causing a routing problem between discontiguous networks. The solution is to issue the no auto-summary command on each router:
R1(config)# router eigrp 100
R1(conf-router)# no auto-summary
R2(config)# router eigrp 100
R2(conf-router)# no auto-summary
After these commands are issued, PC1 is able to access the web server and the message displayed is “You’ve made it!”.
What is the default percentage of interface bandwidth that EIGRP is allowed to use for exchanging EIGRP messages?
10%
50%
25%
100%
Where does EIGRP maintain the list of feasible successors?
the neighbor table
the link-state database
the topology table
the routing table
By default, how often does a Cisco switch that is using RSTP send out BPDU frames
1). every 2 seconds
2). every 4 seconds
3), every 5 seconds
4). every 10 seconds
Refer to the exhibit. A network administrator has configured OSPFv2 on the two Cisco routers as shown. The routers are unable to form a neighbor adjacency. What should be done to fix the problem?
Implement the command network 192.168.2.4 0.0.0.3 area 0 on router R2.
Implement the command no passive-interface Serial0/1.
Implement the command network 192.168.3.0 0.0.0.255 area 0 on router R2.
Change the router-id of router R2 to 2.2.2.2.
I just took this practice final yesterday and there were 3 or 4 new questions.
i have new questions
you can comment here. Thank you!
its helping i like