1. What route would have the lowest administrative distance?
- a directly connected network
- a route received through the EIGRP routing protocol
- a static route
- a route received through the OSPF routing protocol
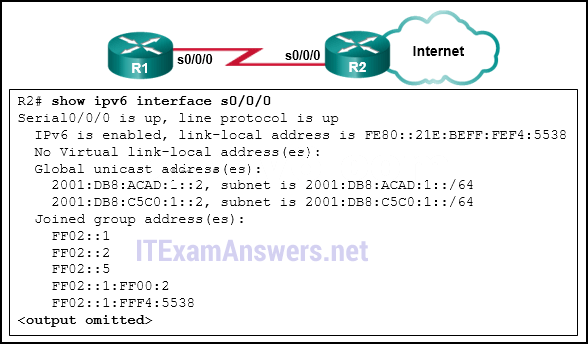
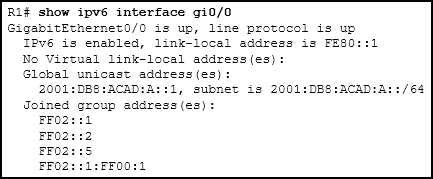
2. Refer to the exhibit. What command would be used to configure a static route on R1 so that traffic from both LANs can reach the 2001:db8:1:4::/64 remote network?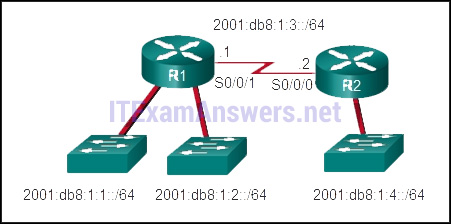
- ipv6 route 2001:db8:1:4::/64 2001:db8:1:3::2
- ipv6 route 2001:db8:1::/65 2001:db8:1:3::1
- ipv6 route 2001:db8:1:4::/64 2001:db8:1:3::1
- ipv6 route ::/0 serial0/0/0
3. What is a characteristic of the distribution layer in the three layer hierarchical model?
- distributes access to end users
- acts as the backbone for the network, aggregating and distributing network traffic throughout the campus
- represents the network edge
- provides access to the rest of the network through switching, routing, and network access policies
4. Which three statements are generally considered to be best practices in the placement of ACLs? (Choose three.)
- Place extended ACLs close to the destination IP address of the traffic.
- Place extended ACLs close to the source IP address of the traffic.
- Place standard ACLs close to the destination IP address of the traffic.
- For every inbound ACL placed on an interface, there should be a matching outbound ACL.
- Filter unwanted traffic before it travels onto a low-bandwidth link.
- Place standard ACLs close to the source IP address of the traffic.
5. Refer to the exhibit. How is a frame sent from PCA forwarded to PCC if the MAC address table on switch SW1 is empty?
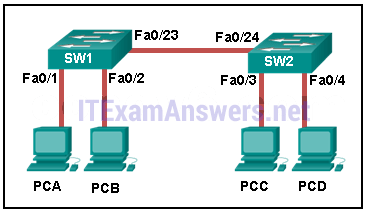
- SW1 floods the frame on all ports on the switch, excluding the interconnected port to switch SW2 and the port through which the frame entered the switch.
- SW1 forwards the frame directly to SW2.
- SW2 floods the frame to all ports connected to SW2, excluding the port through which the frame entered the switch.
- SW1 drops the frame because it does not know the destination MAC address.
- SW1 floods the frame on all ports on SW1, excluding the port through which the frame entered the switch.
6. Which address prefix range is reserved for IPv4 multicast?
- 169.254.0.0 – 169.254.255.255
- 127.0.0.0 – 127.255.255.255
- 240.0.0.0 – 254.255.255.255
- 224.0.0.0 – 239.255.255.255
7. Which statement describes a difference between the operation of inbound and outbound ACLs?
- Inbound ACLs are processed before the packets are routed while outbound ACLs are processed after the routing is completed.
- On a network interface, more than one inbound ACL can be configured but only one outbound ACL can be configured.
- Inbound ACLs can be used in both routers and switches but outbound ACLs can be used only on routers.
- In contrast to outbound ALCs, inbound ACLs can be used to filter packets with multiple criteria.
8. What are three primary benefits of using VLANs? (Choose three.)
- no required configuration
- security
- a reduction in the number of trunk links
- cost reduction
- improved IT staff efficiency
- end user satisfaction
9. What routing table entry has a next hop address associated with a destination network?
- directly-connected routes
- local routes
- C and L source routes
- remote routes
10. Which type of inter-VLAN communication design requires the configuration of multiple subinterfaces?
- legacy inter-VLAN routing
- routing via a multilayer switch
- routing for the management VLAN
- router on a stick
11. Which two devices allow hosts on different VLANs to communicate with each other? (Choose two.)
- repeaterhub
- Layer 3 switch
- Layer 2 switch
- router
12. Which two statements correctly describe a router memory type and its contents? (Choose two.)
- ROM is nonvolatile and stores the running IOS.
- FLASH is nonvolatile and contains a limited portion of the IOS.
- RAM is volatile and stores the IP routing table.
- NVRAM is nonvolatile and stores a full version of the IOS.
- ROM is nonvolatile and contains basic diagnostic software.
13. Refer to the exhibit. In what switch mode should port G0/1 be assigned if Cisco best practices are being used?
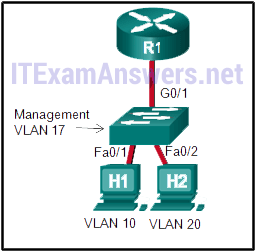
- auto
- trunk
- native
- access
14. Why does a Layer 3 device perform the ANDing process on a destination IP address and subnet mask?
- to identify the network address of the destination network
- to identify the broadcast address of the destination network
- to identify the host address of the destination host
- to identify faulty frames
15. Which range of link-local addresses can be assigned to an IPv6-enabled interface?
- FE80::/10
- FEC0::/10
- FF00::/8
- FDEE::/7
16. What are three parts of an IPv6 global unicast address? (Choose three.)
- a subnet ID that is used to identify networks inside of the local enterprise site
- an interface ID that is used to identify the local host on the network
- a global routing prefix that is used to identify the network portion of the address that has been provided by an ISP
- an interface ID that is used to identify the local network for a particular host
- a global routing prefix that is used to identify the portion of the network address provided by a local administrator
17. An IPv6 enabled device sends a data packet with the destination address of FF02::2. What is the target of this packet?
- all IPv6 enabled devices on the local link
- all IPv6 DHCP servers
- all IPv6 configured routers on the local link
- all IPv6 enabled devices across the network
18. A router is configured to participate in multiple routing protocol: RIP, EIGRP, and OSPF. The router must send a packet to network 192.168.14.0. Which route will be used to forward the traffic?
- a 192.168.14.0/26 route that is learned via RIP
- a 192.168.14.0/25 route that is learned via RIP
- a 192.168.14.0/25 route that is learned via OSPF
- a 192.168.14.0/24 route that is learned via EIGRP
19. Which subnet would include the address 192.168.1.96 as a usable host address?
- 192.168.1.64/29
- 192.168.1.32/28
- 192.168.1.32/27
- 192.168.1.64/26
20. What does the IP address 192.168.1.15/29 represent?
- multicast address
- broadcast address
- unicast address
- subnetwork address
21. Refer to the exhibit. A network administrator is implementing the stateless DHCPv6 operation for the company. Clients are configuring IPv6 addresses as expected. However, the clients are not getting the DNS server address and the domain name information configured in the DHCP pool. What could be the cause of the problem?
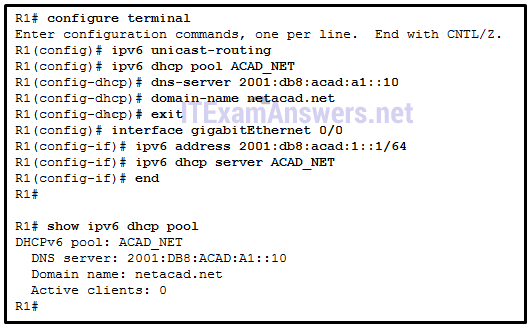
- The GigabitEthernet interface is not activated.
- The DNS server address is not on the same network as the clients are on.
- The router is configured for SLAAC operation.
- The clients cannot communicate with the DHCPv6 server, evidenced by the number of active clients being 0.
22. An organization is assigned an IPv6 address block of 2001:db8:0:ca00::/56. How many subnets can be created without using bits in the interface ID space?
- 4096
- 256
- 512
- 1024
23. What is the term that is used for the area of a network that is affected when a device or network service experiences problems?
- failure domain
- user domain
- broadcast domain
- collision domain
24. As the network administrator you have been asked to implement EtherChannel on the corporate network. What does this configuration consist of?
- grouping two devices to share a virtual IP address
- providing redundant links that dynamically block or forward traffic
- providing redundant devices to allow traffic to flow in the event of device failure
- grouping multiple physical ports to increase bandwidth between two switches
25. Which characteristic would most influence a network design engineer to select a multilayer switch over a Layer 2 switch?
- ability to aggregate multiple ports for maximum data throughput
- ability to have multiple forwarding paths through the switched network based on VLAN number(s)
- ability to build a routing table
- ability to provide power to directly-attached devices and the switch itself
26. A network administrator is planning to add a new switch to the network. What should the network administrator do to ensure the new switch exchanges VTP information with the other switches in the VTP domain?
- Configure all ports on the new switch to access mode.
- Configure the VLANs on the new switch.
- Associate all ports of the new switch to a VLAN that is not VLAN 1.
- Configure the correct VTP domain name and password on the new switch.
27. Refer to the exhibit. Switch SW-A is to be used as a temporary replacement for another switch in the VTP Student domain. What two pieces of information are indicated from the exhibited output? (Choose two.)
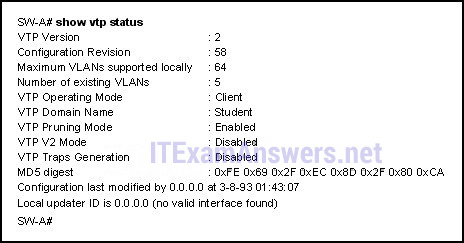
- There is a risk that the switch may cause incorrect VLAN information to be sent through the domain.
- VLAN configuration changes made on this switch will be sent to other devices in the VTP domain.
- The other switches in the domain can be running either VTP version 1 or 2.
- This switch will update its VLAN configuration when VLAN changes are made on a VTP server in the same domain.
- VTP will block frame forwarding on at least one redundant trunk port that is configured on this switch.
28. Refer to the exhibit. The network administrator configures both switches as displayed. However, host C is unable to ping host D and host E is unable to ping host F. What action should the administrator take to enable this communication?
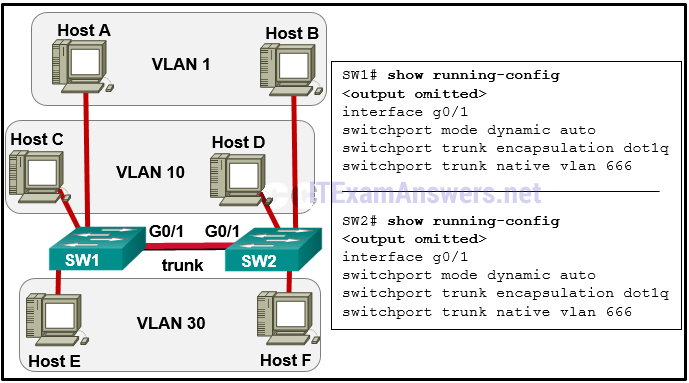
- Associate hosts A and B with VLAN 10 instead of VLAN 1.
- Configure either trunk port in the dynamic desirable mode.
- Include a router in the topology.
- Add the switchport nonegotiate command to the configuration of SW2.
- Remove the native VLAN from the trunk.
29. What eliminates switching loops?
- Time to Live
- VTP
- hold-down timers
- poison reverse
- Spanning Tree Protocol
30. Refer to the exhibit. Which switch will be elected the root bridge and which switch will place a port in blocking mode? (Choose two.)
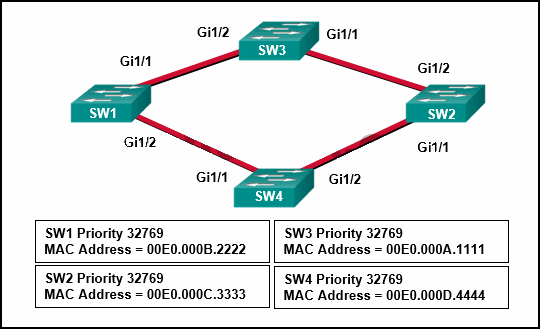
- SW2 will get a port blocked.
- SW4 will get a port blocked.
- SW1 will become the root bridge.
- SW4 will become the root bridge.
- SW2 will become the root bridge.
- SW3 will become the root bridge.
31. Refer to the exhibit. A network administrator has configured OSPF in the topology as shown. What is the preferred path to get from the LAN network that is connected to R1 to the LAN network that is connected to R7?
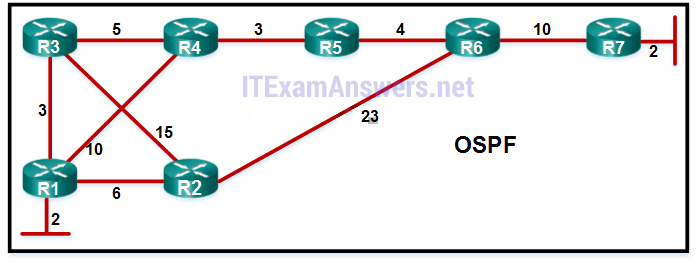
- R1-R2-R6-R7
- R1-R3-R4-R5-R6-R7
- R1-R4-R5-R6-R7
- R1-R3-R2-R6-R7
32. Which statement describes the autonomous system number used in EIGRP configuration on a Cisco router?
- It carries the geographical information of the organization.
- It is a globally unique autonomous system number that is assigned by IANA.
- It functions as a process ID in the operation of the router.
- It identifies the ISP that provides the connection to network of the organization.
33. An EIGRP router loses the route to a network. Its topology table contains two feasible successors to the same network. What action will the router take?
- The DUAL algorithm is recomputed to find an alternate route.
- The best alternative backup route is immediately inserted into the routing table.
- The router will query neighbors for an alternate route.
- The router uses the default route.
34. What is a function of OSPF hello packets?
- to send specifically requested link-state records
- to ensure database synchronization between routers
- to discover neighbors and build adjacencies between them
- to request specific link-state records from neighbor routers
35. Refer to the exhibit. R1 and R2 are OSPFv3 neighbors. Which address would R1 use as the next hop for packets that are destined for the Internet?
- 2001:DB8:C5C0:1::2
- FE80::21E:BEFF:FEF4:5538
- FF02::5
- 2001:DB8:ACAD:1::2
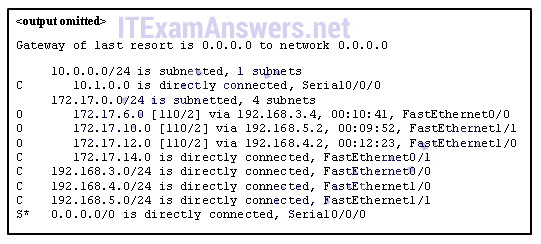
36. Refer to the exhibit. Match the packets with their destination IP address to the exiting interfaces on the router. (Not all targets are used.)
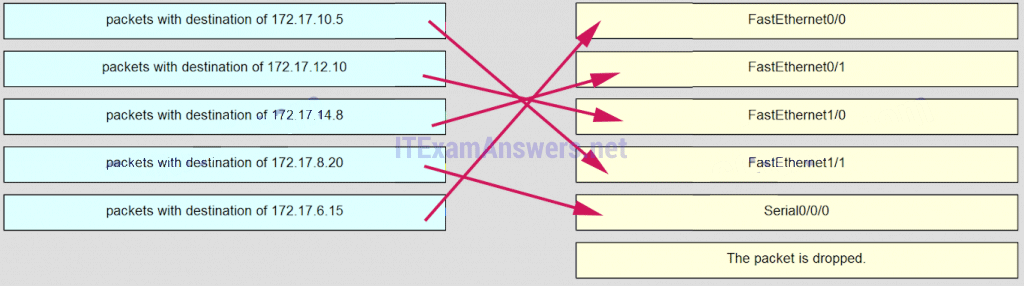
37. Match the DHCP message types to the order of the DHCPv4 process. (Not all options are used.)
Match the DHCP message types to the order of the DHCPv4 process.
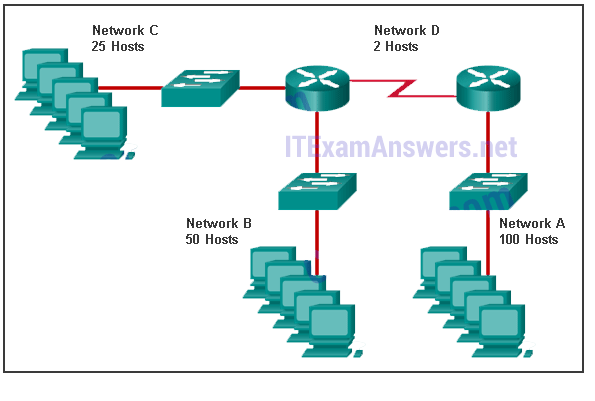
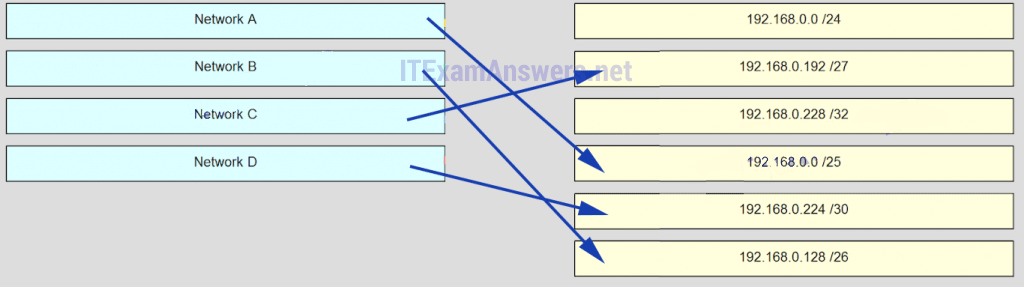
38. Refer to the exhibit. Match the network with the correct IP address and prefix that will satisfy the usable host addressing requirements for each network. (Not all options are used.)
39. Match the description to the term. (Not all options are used.)
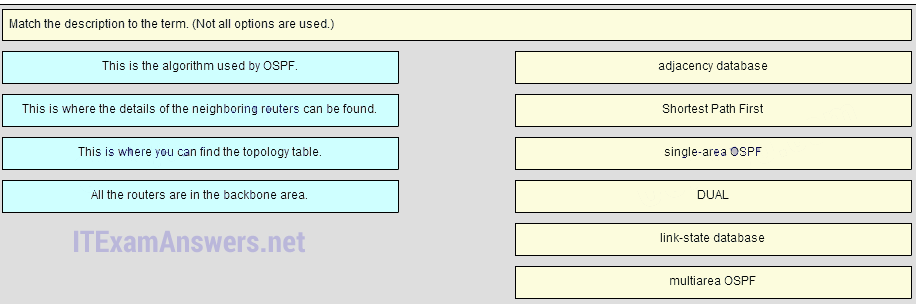
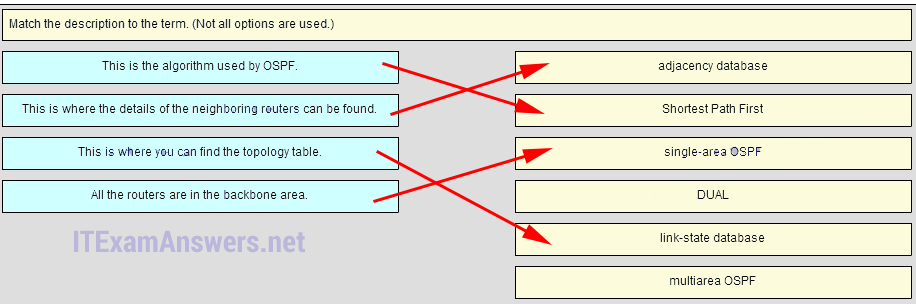
Place the options in the following order:
This is where the details of the neighboring routers can be found. -> adjacency database
This is the algorithm used by OSPF. -> Shortest Path First
All the routers are in the backbone area. -> Single-area OSPF
– not scored –
This is where you can find the topology table. -> link-state database
– not scored –
40. Match the order of precedence to the process logic that an OSPFv3 network router goes through in choosing a router ID. (Not all options are used.)
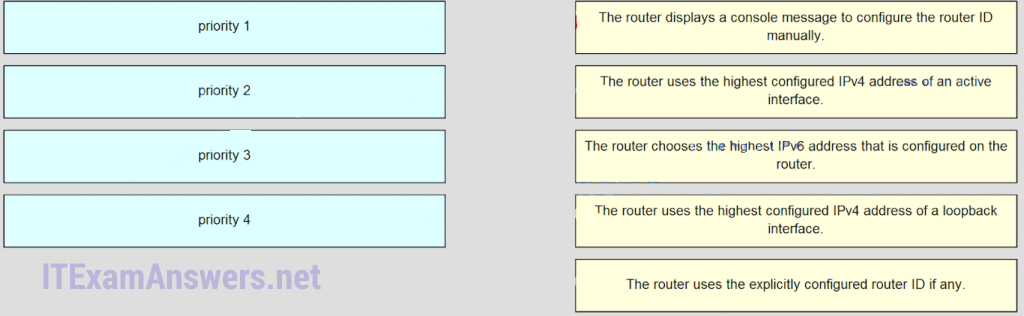
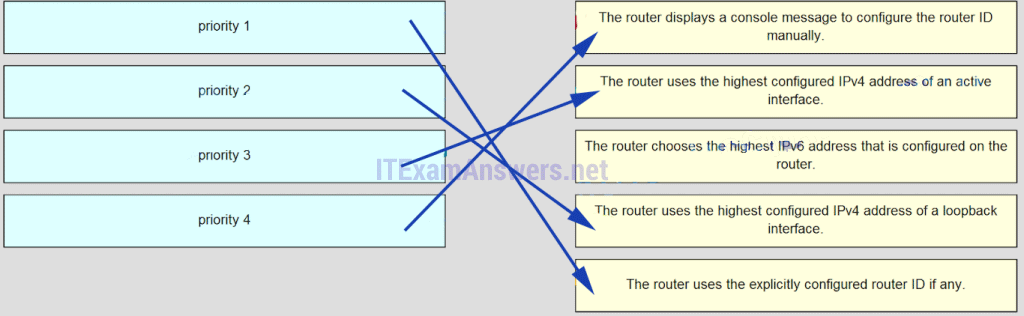
Older Version
41. A router needs to be configured to route within OSPF area 0. Which two commands are required to accomplish this? (Choose two.)
- RouterA(config)# router ospf 0
- RouterA(config)# router ospf 1
- RouterA(config-router)# network 192.168.2.0 0.0.0.255 0
- RouterA(config-router)# network 192.168.2.0 0.0.0.255 area 0
- RouterA(config-router)# network 192.168.2.0 255.255.255.0 0
42. The computers used by the network administrators for a school are on the 10.7.0.0/27 network. Which two commands are needed at a minimum to apply an ACL that will ensure that only devices that are used by the network administrators will be allowed Telnet access to the routers? (Choose two.)
- access-class 5 in
- access-list 5 deny any
- access-list standard VTY
permit 10.7.0.0 0.0.0.127 - access-list 5 permit 10.7.0.0 0.0.0.31
- ip access-group 5 out
- ip access-group 5 in
43. Refer to the exhibit. Router R1 has an OSPF neighbor relationship with the ISP router over the 192.168.0.32 network. The 192.168.0.36 network link should serve as a backup when the OSPF link goes down. The floating static route command ip route 0.0.0.0 0.0.0.0 S0/0/1 100 was issued on R1 and now traffic is using the backup link even when the OSPF link is up and functioning. Which change should be made to the static route command so that traffic will only use the OSPF link when it is up?
- Add the next hop neighbor address of 192.168.0.36.
- Change the administrative distance to 1.
- Change the destination network to 192.168.0.34.
- Change the administrative distance to 120.
44. Refer to the exhibit. A network administrator is configuring a router as a DHCPv6 server. The administrator issues a show ipv6 dhcp pool command to verify the configuration. Which statement explains the reason that the number of active clients is 0?
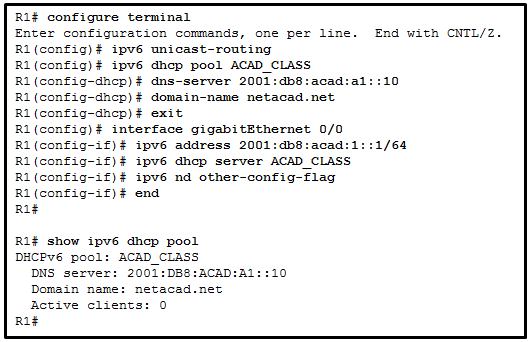
- The default gateway address is not provided in the pool.
- No clients have communicated with the DHCPv6 server yet.
- The IPv6 DHCP pool configuration has no IPv6 address range specified.
- The state is not maintained by the DHCPv6 server under stateless DHCPv6 operation.
45. Refer to the exhibit. What summary static address should be configured on R3 to advertise to an upstream neighbor?
- 192.168.0.0/24
- 192.168.0.0/23
- 192.168.0.0/22
- 192.168.0.0/21
46. Which two commands should be implemented to return a Cisco 3560 trunk port to its default configuration? (Choose two.)
- S1(config-if)# no switchport trunk allowed vlan
- S1(config-if)# no switchport trunk native vlan
- S1(config-if)# switchport mode dynamic desirable
- S1(config-if)# switchport mode access
- S1(config-if)# switchport access vlan 1
47. Which two methods can be used to provide secure management access to a Cisco switch? (Choose two.)
- Configure all switch ports to a new VLAN that is not VLAN 1.
- Configure specific ports for management traffic on a specific VLAN.
- Configure SSH for remote management.
- Configure all unused ports to a “black hole.”
- Configure the native VLAN to match the default VLAN.
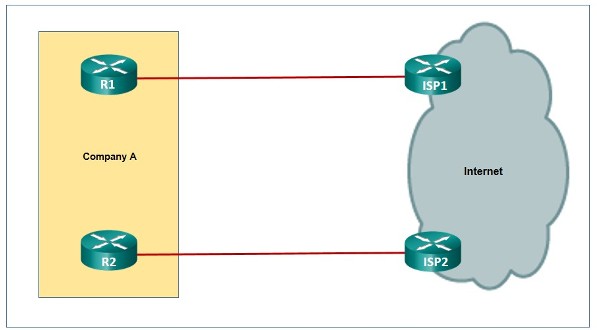
48. Which two factors are important when deciding which interior gateway routing protocol to use? (Choose two.)
- scalability
- ISP selection
- speed of convergence
- the autonomous system that is used
- campus backbone architecture
49. Which three pieces of information does a link-state routing protocol use initially as link-state information for locally connected links? (Choose three.)
- the link router interface IP address and subnet mask
- the type of network link
- the link next-hop IP address
- the link bandwidth
- the cost of that link
50. What is a disadvantage of NAT?
- There is no end-to-end addressing.
- The router does not need to alter the checksum of the IPv4 packets.
- The internal hosts have to use a single public IPv4 address for external communication.
- The costs of readdressing hosts can be significant for a publicly addressed network.
51. A network administrator is using the router-on-a-stick method to configure inter-VLAN routing. Switch port Gi1/1 is used to connect to the router. Which command should be entered to prepare this port for the task?
- Switch(config)# interface gigabitethernet 1/1
Switch(config-if)# spanning-tree vlan 1 - Switch(config)# interface gigabitethernet 1/1
Switch(config-if)# spanning-tree portfast - Switch(config)# interface gigabitethernet 1/1
Switch(config-if)# switchport mode trunk - Switch(config)# interface gigabitethernet 1/1
Switch(config-if)# switchport access vlan 1
52. What is a function of the distribution layer?
- fault isolation
- network access to the user
- high-speed backbone connectivity
- interconnection of large-scale networks in wiring closets
53. Which two statements are true about half-duplex and full-duplex communications? (Choose two.)
- Full duplex offers 100 percent potential use of the bandwidth.
- Half duplex has only one channel.
- All modern NICs support both half-duplex and full-duplex communication.
- Full duplex allows both ends to transmit and receive simultaneously.
- Full duplex increases the effective bandwidth.
54. Which three parameters could be in an extended access control list? (Choose three.)
- access list number between 1 and 99
- access list number between 100 and 199
- default gateway address and wildcard mask
- destination address and wildcard mask
- source address and wildcard mask
- subnet mask and wild card mask
55. An organization needs to provide temporary voice and data services to a new small lab building. They plan to install an access switch in the new lab and connect it using a 100Mb/s FastEthernet trunk link. The network administrator is concerned about the capability of the link to meet quality requirements of the proposed voice and data services. The administrator plans to manage the datalink layer traffic to and from the lab so that trunk usage is optimized. What could the administrator apply to the trunk to help achieve this?
- Disable Spanning Tree Protocol to provide maximum bandwidth for the voice and data traffic.
- Configure the switches to run Per VLAN Spanning Tree for the voice and data VLANs only.
- Configure the lab switch to use the same voice and data VLAN as the rest of the campus LAN.
- Configure the trunk ports on the trunk link to the lab to allow only the voice and data VLANs.
56. Which statement is true about the difference between OSPFv2 and OSPFv3?
- OSPFv3 routers use a different metric than OSPFv2 routers use.
- OSPFv3 routers use a 128 bit router ID instead of a 32 bit ID.
- OSPFv3 routers do not need to elect a DR on multiaccess segments.
- OSPFv3 routers do not need to have matching subnets to form neighbor adjacencies.
57. Refer to the exhibit. Which address will R1 use as the source address for all OSPFv3 messages that will be sent to neighbors?
- FE80::1
- 2001:DB8:ACAD:A::1
- FF02::1
- FF02::5
58. What are two features of a link-state routing protocol? (Choose two.)
- Routers send periodic updates only to neighboring routers.
- Routers send triggered updates in response to a change.
- Routers create a topology of the network by using information from other routers.
- The database information for each router is obtained from the same source.
- Paths are chosen based on the lowest number of hops to the designated router.
59. Which OSPF component is identical in all routers in an OSPF area after convergence?
- adjacency database
- link-state database
- routing table
- SPF tree
60. Which statement describes a characteristic of standard IPv4 ACLs?
- They are configured in the interface configuration mode.
- They filter traffic based on source IP addresses only.
- They can be created with a number but not with a name.
- They can be configured to filter traffic based on both source IP addresses and source ports.
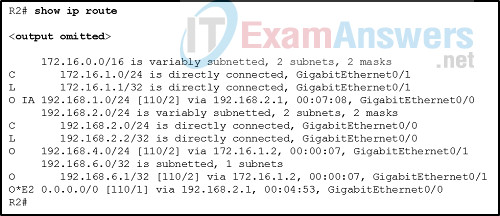
61. Refer to the exhibit. A network administrator issues the show ip route command on R2. What two types of routes are installed in the routing table? (Choose two.)
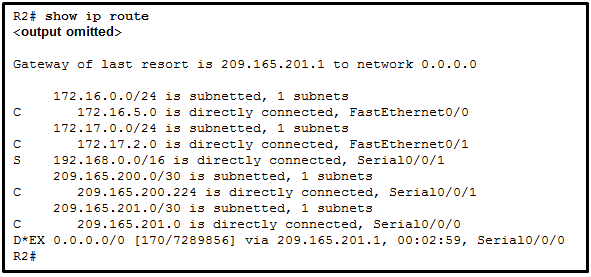
- a configured default route
- directly connected networks
- routes that are learned through the OSPF routing protocol
- routes that are learned through the EIGRP routing protocol
- a configured static route to the network 209.165.200.224
62. Refer to the exhibit. Based on the output that is shown, what type of NAT has been implemented?
- dynamic NAT with a pool of two public IP addresses
- PAT using an external interface
- static NAT with one entry
- static NAT with a NAT pool
63. What condition is required to enable Layer 3 switching?
- The Layer 3 switch must have IP routing enabled.
- All participating switches must have unique VLAN numbers.
- All routed subnets must be on the same VLAN.
- Inter-VLAN portions of Layer 3 switching must use router-on-a-stick.
64. Fill in the blank.
The ip default-gateway command is used to configure the default gateway on a switch.
65. Open the PT Activity. Perform the tasks in the activity instructions and then answer the question. Which PCs will receive the broadcast sent by PC-C?
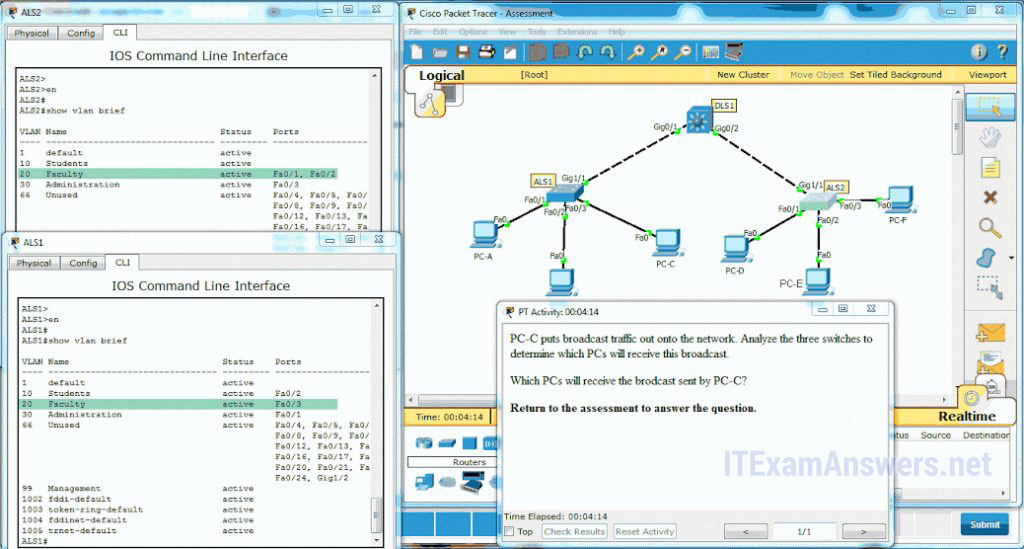
- PC-A, PC-B
- PC-D, PC-E
- PC-A, PC-B, PC-E
- PC-A, PC-B, PC-D, PC-E
- PC-A, PC-B, PC-D, PC-E, PC-F
66. When are EIGRP update packets sent?
- only when necessary
- when learned routes age out
- every 5 seconds via multicast
- every 30 seconds via broadcast
67. Which statement describes a characteristic of the delivery of EIGRP update packets?
- EIGRP uses UDP to send all update packets.
- EIGRP sends all update packets via unicast.
- EIGRP sends all update packets via multicast.
- EIGRP uses a reliable delivery protocol to send all update packets.
68. What is the purpose of the Spanning Tree Protocol (STP)?
- prevents Layer 2 loops
- prevents routing loops on a router
- creates smaller collision domains
- creates smaller broadcast domains
- allows Cisco devices to exchange routing table updates
69. Which statement is true regarding states of the IEEE 802.1D Spanning Tree Protocol?
- Ports are manually configured to be in the forwarding state.
- Ports listen and learn before going into the forwarding state.
- Ports must be blocked before they can be placed in the disabled state.
- It takes 15 seconds for a port to go from blocking to forwarding
70. Which wireless encryption method is the most secure?
- WPA
- WEP
- WPA2 with TKIP
- WPA2 with AES
71. Which wireless network topology is being configured by a technician who is installing a keyboard, a mouse, and headphones, each of which uses Bluetooth?
- ad hoc mode
- hotspot
- infrastructure mode
- mixed mode
72. A network engineer is troubleshooting a newly deployed wireless network that is using the latest 802.11 standards. When users access high bandwidth services such as streaming video, the wireless network performance is poor. To improve performance the network engineer decides to configure a 5 Ghz frequency band SSID and train users to use that SSID for streaming media services. Why might this solution improve the wireless network performance for that type of service?
- The 5 GHz band has a greater range and is therefore likely to be interference-free.
- Requiring the users to switch to the 5 GHz band for streaming media is inconvenient and will result in fewer users accessing these services.
- The 5 GHz band has more channels and is less crowded than the 2.4 GHz band, which makes it more suited to streaming multimedia.
- The only users that can switch to the 5 GHz band will be those with the latest wireless NICs, which will reduce usage.
73. What are two advantages of EtherChannel? (Choose two.)
- Configuring the EtherChannel interface provides consistency in the configuration of the physical links.
- Load balancing occurs between links configured as different EtherChannels.
- EtherChannel uses upgraded physical links to provide increased bandwidth.
- Spanning Tree Protocol views the physical links in an EtherChannel as one logical connection.
- Spanning Tree Protocol ensures redundancy by transitioning failed interfaces in an EtherChannel to a forwarding state.
74. Refer to the exhibit. Which destination MAC address is used when frames are sent from the workstation to the default gateway?
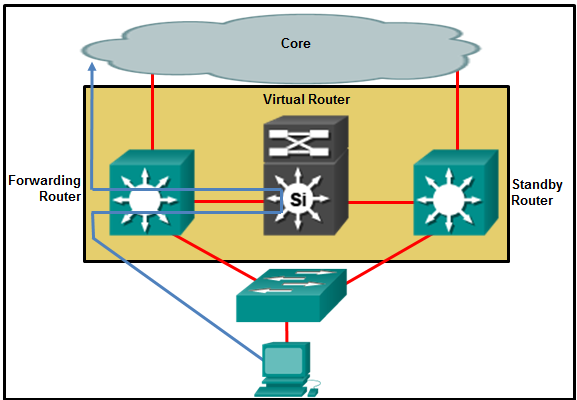
- MAC address of the forwarding router
- MAC addresses of both the forwarding and standby routers
- MAC address of the standby router
- MAC address of the virtual router
75. Refer to the exhibit. Which two conclusions can be derived from the output? (Choose two.)
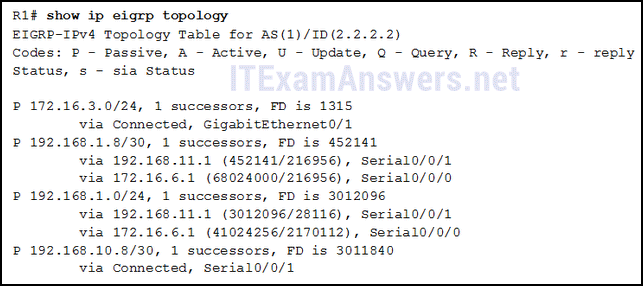
- There is one feasible successor to network 192.168.1.8/30.
- The network 192.168.10.8/30 can be reached through 192.168.11.1.
- The reported distance to network 192.168.1.0/24 is 41024256.
- The neighbor 172.16.6.1 meets the feasibility condition to reach the 192.168.1.0/24 network.
- Router R1 has two successors to the 172.16.3.0/24 network.
76. Refer to the exhibit. What can be concluded about network 192.168.1.0 in the R2 routing table?
- This network has been learned from an internal router within the same area.
- This network was learned through summary LSAs from an ABR.
- This network is directly connected to the interface GigabitEthernet0/0.
- This network should be used to forward traffic toward external networks.
77. Refer to the exhibit. A network technician is troubleshooting missing OSPFv3 routes on a router. What is the cause of the problem based on the command output?
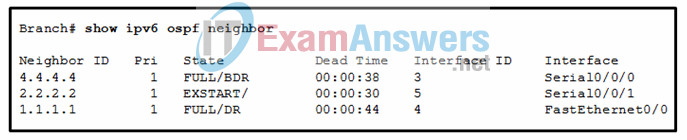
- There is a problem with the OSPFv3 adjacency between the local router and the router that is using the neighbor ID 2.2.2.2.
- The local router has formed complete neighbor adjacencies, but must be in a 2WAY state for the router databases to be fully synchronized.
- The dead time must be higher than 30 for all routers to form neighbor adjacencies.
- The neighbor IDs are incorrect. The interfaces must use only IPv6 addresses to ensure fully synchronized routing databases.
78. Refer to the exhibit. What are two results of issuing the displayed commands on S1, S2, and S3? (Choose two.)
- S1 will automatically adjust the priority to be the lowest.
- S1 will automatically adjust the priority to be the highest.
- S3 can be elected as a secondary bridge.
- S2 can become root bridge if S3 fails.
- S2 can become root bridge if S1 fails.
79. A network administrator is troubleshooting slow performance in a Layer 2 switched network. Upon examining the IP header, the administrator notices that the TTL value is not decreasing. Why is the TTL value not decreasing?
- This is the normal behavior for a Layer 2 network.
- The MAC address table is corrupt.
- The VLAN database is full.
- The outbound interface is set for half duplex.
80. What are the two methods that a wireless NIC can use to discover an AP? (Choose two.)
- sending an ARP request broadcast
- sending a multicast frame
- transmitting a probe request
- initiating a three-way handshake
- receiving a broadcast beacon frame

Question 74 might have incorrect image
Fixed! thanks for report! :)
Question 16.
Not all three options are chosen.
What are three parts of an IPv6 global unicast address? (Choose three.)
.a subnet ID that is used to identify networks inside of the local enterprise site*
.an interface ID that is used to identify the local host on the network*
.a global routing prefix that is used to identify the network portion of the address that has been provided by an ISP*
.an interface ID that is used to identify the local network for a particular host
.a global routing prefix that is used to identify the portion of the network address provided by a local administrator
Updated! Thanks so much!