Author: IT Administrator
1. What is a good source for safely downloading Android apps? iTunes google play freeware sites the Apple App Store 2. In the context of mobile devices, what does the term tethering involve? connecting a mobile device to another mobile device or computer to share a network connection …
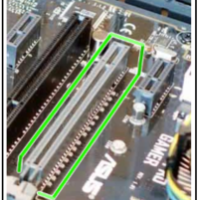
1. Refer to the exhibit. In which section of the motherboard would a memory module be installed? section A section B section C section D 2. Refer to the exhibit. Which type of expansion slot is shown? AGP PCI PCIe x16 memory 3. Which two computer components require …
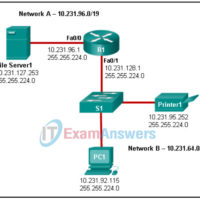
Network Support and Security Final Exam Answers 1. Refer to the exhibit. A technician is attempting to map the local network using CDP. According to the output shown, which two statements are true about router Branch01? (Choose two.) Router Branch01 is directly connected to port Gi0/1/0 on device …
1. What is the level of need for data integrity in an e-commerce organization? low mid high critical 2. Which three solutions are examples of logical access control? (Choose three.) firewall access control list biometrics fence laptop lock swipe card 3. Which host-based solution is installed on a …
1. What does a rootkit modify? operating system programs screen savers Notepad Microsoft Word 2. An attacker is sitting in front of a store and wirelessly copies emails and contact lists from nearby unsuspecting user devices. What type of attack is this? bluesnarfing smishing RF jamming bluejacking 3. …
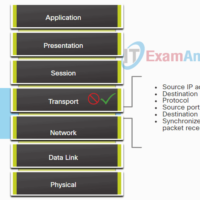
1. After a problem is defined, what is the next step in the seven-step troubleshooting process? gather information analyze information propose hypothesis eliminate possible causes 2. Which two types of problems are best investigated with a bottom-up troubleshooting method? (Choose two.) problems involving an issue not seen before …
Network Technician Career Path Exam Answers 1. What two radio frequency bands are used in home Wireless LANs? (Choose two.) 5 MHz 9 MHz 2.4 GHz 5 GHz 900 GHz 2. Which is a characteristic of the network SSID? It is encrypted by default. It is case sensitive. …
1. Match the task and purpose to the appropriate Big Data analytics method. 2. Match the type of data analysis with the question it can answer. 3. Which statement is true concerning data analytics? Descriptive analytics uses a feedback system to track the outcome of actions taken. Prescriptive …
Module 1.4.2 Quiz – Data Analytic Projects Answers 1. A college has deployed next-generation analytics. Which question would most likely be answered by next generation analytics that could not be answered by traditional analysis tools? Which class has the most sections available? What are the 10 most expensive …
Cybersecurity Pathway Final Exam Answers – Junior Cybersecurity Analyst Career Path Exam 1. What is a characteristic of the security onion analogy to visualizing defense-in-depth? The core or heart of the onion represents the firewall surround by protective layers. The outer skin of the onion represents hardened internet-facing …