Author: IT Administrator
1. Using default settings, what is the next step in the switch boot sequence after the IOS loads from flash? Search for a backup IOS in ROM. Load the bootstrap program from ROM. Load the running-config file from RAM. Perform the POST routine. Locate and load the startup-config …
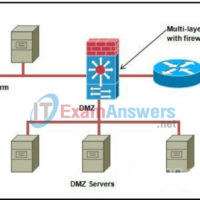
1. What are two mechanisms that provide redundancy for server farm implementations? (Choose two.) host intrusion prevention systems virtual private networks network intrusion prevention systems Rapid Spanning Tree Protocol Hot Standby Routing Protocol 2. The ability to connect securely to a private network over a public network is …
Introduction to Cybersecurity: My Knowledge Check Answers 1. What action will an IDS take upon detection of malicious traffic? Block or deny all traffic Drop only packets identified as malicious Create a network alert and log the detection Reroute malicious traffic to a honeypot 2. Which of the …
1. Which of the following items are considered WAN devices? (Choose three.) Bridge Modem Router Ethernet switch Access server Repeater 2. Which layer of the hierarchical network design model is often called the backbone? Access Distribution Network Core Workgroup WAN 3. Match each term with its definition: 4. …
Endpoint Security Exam Answers 1.6.2 Cybersecurity Threats, Vulnerabilities, and Attacks Quiz 2.3.2 Securing Networks Quiz 3.4.2 Attacking the Foundation Quiz 4.4.2 Attacking What We Do Quiz 5.4.2 Wireless Network Communication Quiz 6.3.2 Network Security Infrastructure Quiz Checkpoint Exam: Network Security 7.5.2 The Windows Operating System Quiz 8.8.2 Linux …
1.6.2 Cybersecurity Threats, Vulnerabilities, and Attacks Quiz Answers 1. What type of attack occurs when data goes beyond the memory areas allocated to an application? SQL injection RAM injection RAM spoofing Buffer overflow 2. Which of the following statements describes a distributed denial of service (DDoS) attack? An …
Ethical Hacker Exam Answers Online Test 1.4.3 Quiz – Introduction to Ethical Hacking and Penetration Testing 2.4.3 Quiz – Planning and Scoping a Penetration Testing Assessment 3.5.3 Quiz – Information Gathering and Vulnerability Scanning 4.6.3 Quiz – Social Engineering Attacks 5.3.3 Quiz – Exploiting Wired and Wireless Networks …
1.4.3 Quiz – Introduction to Ethical Hacking and Penetration Testing Answers 1. Which statement best describes the term ethical hacker? a person who uses different tools than nonethical hackers to find vulnerabilities and exploit targets a person that is financially motivated to find vulnerabilities and exploit targets a …
2.4.3 Quiz – Planning and Scoping a Penetration Testing Assessment Answers 1. A contractor is hired to review and perform cybersecurity vulnerability assessments for a local health clinic facility. Which U.S. government regulation must the contractor understand before the contractor can start? GDPR GLBA HIPAA FedRAMP 2. An …
3.5.3 Quiz – Information Gathering and Vulnerability Scanning Answers 1. Which two tools could be used to gather DNS information passively? (Choose two.) Recon-ng Dig Wireshark Nmap ExifTool 2. When performing passive reconnaissance, which Linux command can be used to identify the technical and administrative contacts of a …