Objectives
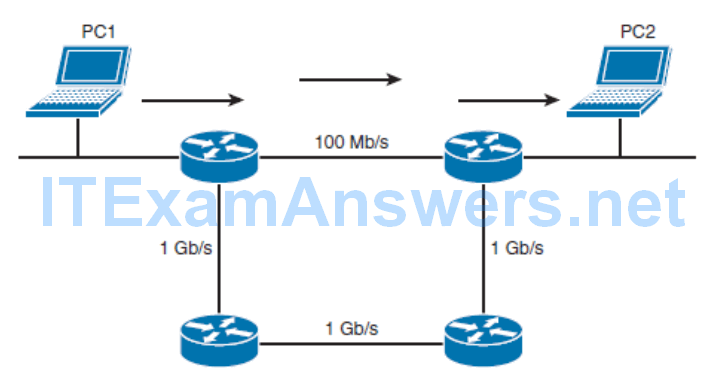
- Differentiating Between Dynamic Routing Protocols
- How Different Traffic Types, Network Types, and Overlaying Network Technologies Influence Routing
- Differentiating Between the Various Branch Connectivity Options and Describing Their Impact on Routing Protocols
- How to Configure Routing Information Protocol Next Generation (RIPng)
Differentiating Between Dynamic Routing Protocols
- Enterprise Network Infrastructure
- Dynamic Routing Protocols in the Enterprise Network Infrastructure
- Choosing a of Dynamic Routing Protocols
- IGP and EGP Routing Protocols
- Types of Routing Protocols
- Importance of convergence
- Route summarization
- Describe what influences routing protocol scalability
Enterprise network infrastructure
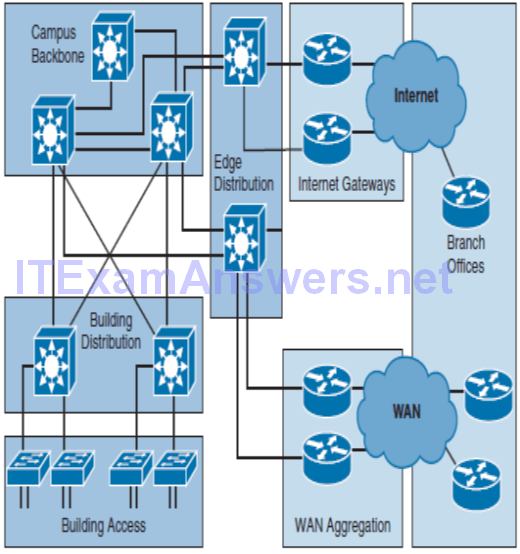
Enterprise Campus
- An enterprise campus provides access to the network communications services and resources to end users and devices.
- It is spread over a single geographic location, spanning a single floor, building, or several buildings in the same locality.
- The campus is commonly designed using a hierarchical model — comprising the core, distribution, and access layers—creating a scalable infrastructure.
Enterprise Edge
- An enterprise edge provides users at geographically disperse remote sites with access to the same network services as users at the main site.
- The network edge aggregates private WAN links that are rented from service providers, and it enables individual users to establish VPN connections.
- In addition, the network edge also provides Internet connectivity for campus and branch users.
Dynamic Routing Protocols in the Enterprise Network Infrastructure
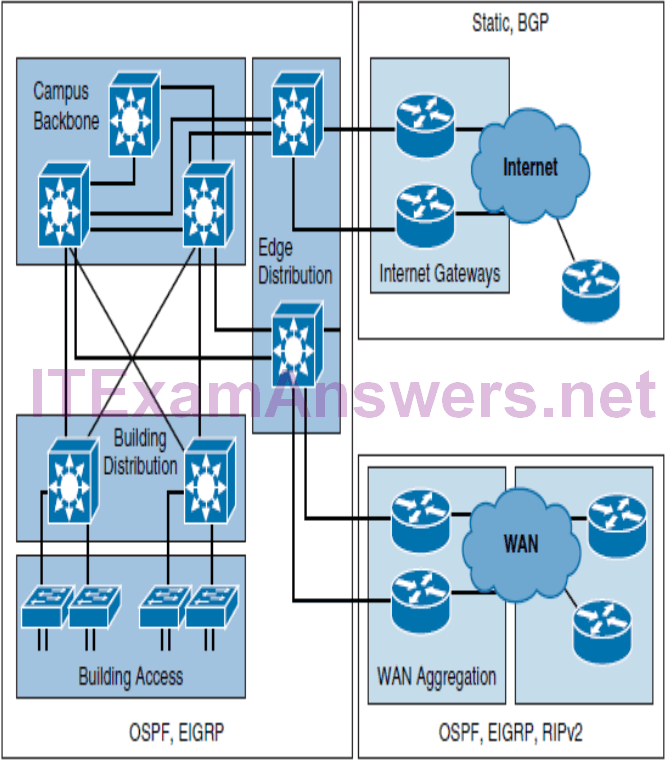
- It is a best practice that you use one IP routing protocol throughout the enterprise, if possible.
- One common example of when multiple routing protocols are used is when the organization is multihomed.
- In this scenario, the most commonly used protocol to exchange routes with the service provider is Border Gateway Protocol (BGP), whereas within the organization, Open Shortest Path First (OSPF) or Enhanced Interior Gateway Routing Protocol (EIGRP) is typically used.
- In a single-homed infrastructures static routes are commonly used between the customer and the ISP.
Choosing a of Dynamic Routing Protocols
Input requirements :
- Size of network
- Multivendor support
- Knowledge level of specific protocol
Protocol characteristics :
- Type of routing algorithm
- Speed of convergence
- Scalability
IGP and EGP Routing Protocols
An autonomous system (AS) represents a collection of network devices under a common administrator.
Routing protocols can be divided based on whether they exchange routes within an AS or between different autonomous systems:
Interior Gateway Protocols (IGP)
Support small, medium-sized, and large organizations, but their scalability has its limits. Fast convergence, and basic functionality is not complex to configure. The most commonly used IGPs in enterprises are EIGRP, OSPF and RIP is rarely used. IS-IS is also commonly found as ISP IGP
Exterior Gateway Protocols (EGP)
Used to exchange routes between different autonomous systems. BGP is the only EGP that is used today. The main function of BGP is to exchange a huge number of routes between different autonomous systems.
Types of Routing Protocols
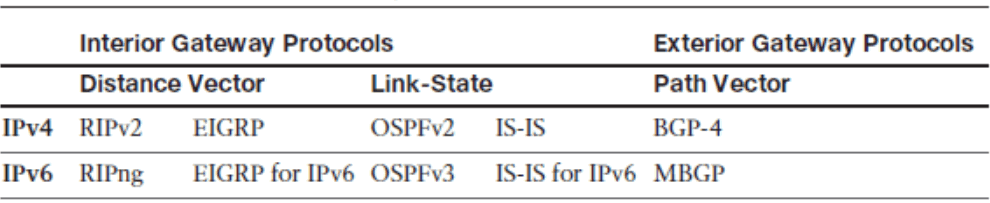
Distance vector protocols
The distance vector routing approach determines the direction (vector) and distance (such as link cost or number of hops) to any link in the network. The only information that a router knows about a remote network is the distance or metric to reach this network and which path or interface to use to get there. Distance vector routing protocols do not have an actual map of the network topology.
Link-state protocols
The link-state approach uses the Shortest Path First (SPF) algorithm to create an abstract of the exact topology of the entire network or at least within its area. A link-state routing protocol is like having a complete map of the network topology. The map is used to determine best path to a destination.
Path vector protocols
Path information is used to determine the best paths and to prevent routing loops. Similar to distance vector protocols, path vector protocols do not have an abstract of the network topology. Path vector protocols indicate direction and distance, but also include additional information about the specific path of the destination.
Early distance vector protocols, such as RIPv1 and IGRP, used only the periodic exchange of routing information for a topology change. Later versions of these distance vector protocols (EIGRP and RIPv2) implemented triggered updates to respond to topology changes.
Importance of Convergence
The process of when routers notice change in the network, exchange the information about the change, and perform necessary calculations to reevaluate the best routes.
To minimize downtime and quickly respond to network changes, a fast convergence time is desired.
Route Summarization
Route summarization reduces routing overhead and improve stability and scalability of routing by reducing the amount of routing information that is maintained and exchanged between routers.
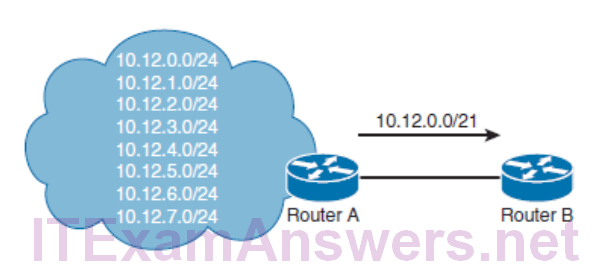
Less frequent and smaller updates, as a result of route summarization, also lower convergence time.
In addition, route summarization also reduces the number of updates that needs to be exchanged between these two routers. For example, examine the event of network change, when network 10.12.6.0/24 becomes unreachable. Router A does not need to inform the neighbor about an unreachable prefix because the summary route is not affected by the network change.
Routing Protocol Scalability
Scalability factors include:
- Number of routes
- Number of adjacent neighbors
- Number of routers in the network
- Network design
- Frequency of changes
- Available resources (CPU and memory)
The scalability of the routing protocol and its configuration options to support a larger network can play an important role when evaluating routing protocols against each other.
Each routing protocol also implements additional protocol-specific features to improve the overall scalability. OSPF, for example, supports the use of hierarchical areas that divide one large network into several subdomains. EIGRP, on the other hand, supports the configuration of stub routers to optimize information exchange process and improve scalability.
Understanding Network Technologies
- Differentiate traffic types
- Differentiate IPv6 address types
- Describe ICMPv6 neighbor discovery
- Network Types
- NBMA Networks
Differentiate traffic types
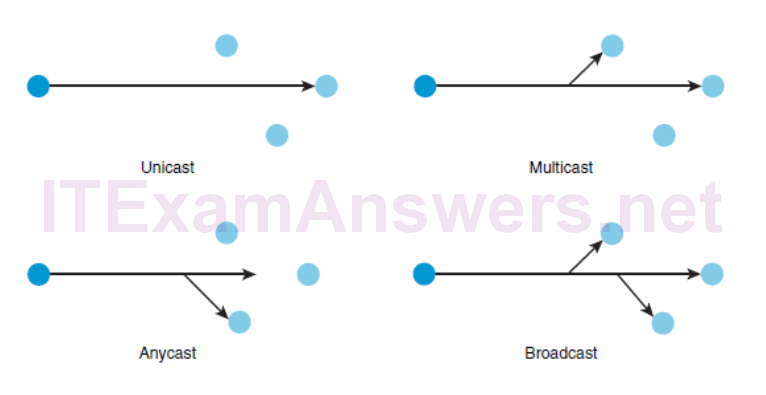
Unicast
- Unicast addresses are used in a one-to-one context. Unicast traffic is exchanged only between one sender and one receiver.
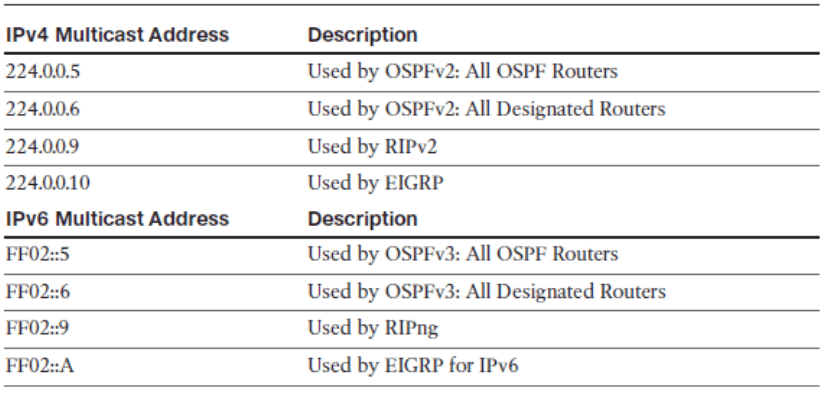
Multicast
- Multicast addresses identify a group of interfaces across different devices. Traffic that is sent to a multicast address is sent to multiple destinations at the same time.
- IPv6 reserved multicast addresses 224.0.0.0–239.255.255.255.
- IPv6 reserved multicast addresses have the prefix FF00::/8.
Anycast
- An anycast address is assigned to an interface on more than one node. When a packet is sent to an anycast address, it is routed to the nearest interface that has this address. The nearest interface is found according to the measure of distance of the particular routing protocol.
Broadcast
- IPv4 broadcast addresses are used when sending traffic to all devices in the subnet. Local broadcast address 255.255.255.255.
- IPv6 does not use a broadcast address, but uses multicast addresses instead
(ANYCAST)All nodes that share the same address should behave the same way so that the service is offered similarly regardless of the node that services the request. A common use case for anycast is the Internet DNS server. There are several instances of the same server across the world, and anycast enables you to reach the nearest one by simply using the anycast destination address. The arrows in the figure for anycast indicate that one destination is closer than the other.
Well-known IPv4 and Assigned IPv6 Multicast Addresses
Differentiate IPv6 address types
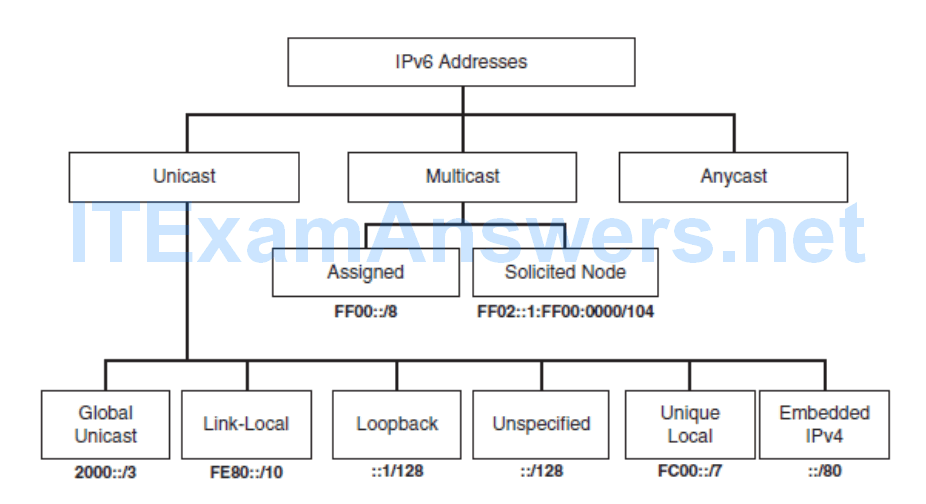
Solicited node multicast addresses are used by ICMPv6 Neighbor Discovery (ND) address resolution. Similar toARP for IPv4, ND address resolution is used to map a Layer 2 MAC address to a Layer 3 IPv6 address.
Describe ICMPv6 neighbor discovery
Router Solicitation (RS)
- Sent by a device to the all IPv6 routers multicast to request a Router Advertisement message from the router.
Router Advertisement (RA)
- Sent by an IPv6 router to the all IPv6 devices multicast. Includes link information such as prefix, prefix-length, and the default gateway address.
- The RA also indicates to the host whether it needs to use a stateless or stateful DHCPv6 server.
Neighbor Solicitation (NS)
- Sent by a device to the solicited node multicast address when it knows the IPv6 address of a device but not its Ethernet MAC address. This is similar to ARP for IPv4.
Neighbor Advertisement (NA)
- Sent by a device usually in response to a Neighbor Solicitation message.
Redirect
- This has similar functionality as in IPv4. Sent by a router to inform the source of a packet of a better next-hop router on the link that is closer to the destination.
Network Types
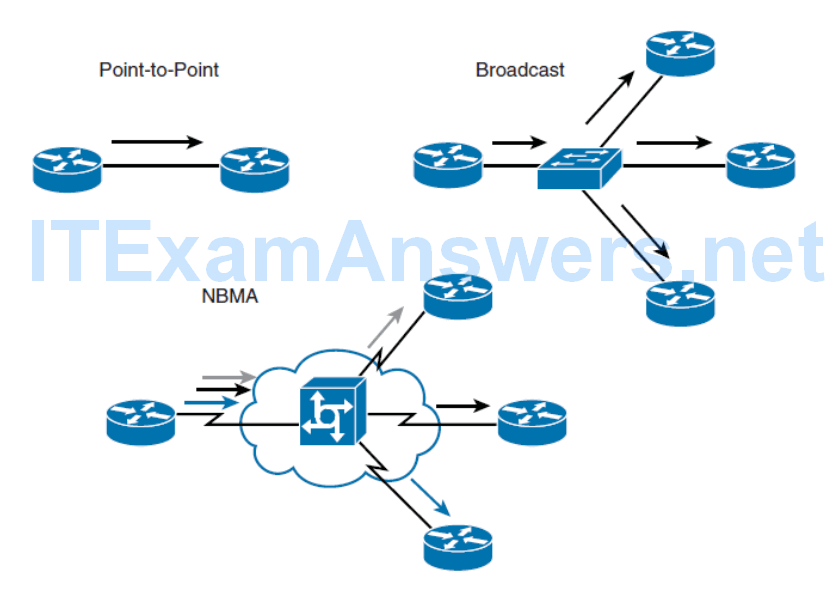
Point-to-point network
- A network that connects a single pair of routers.
- A serial link is an example of a point-to-point connection.
Broadcast network
- A network that can connect many routers along with the capability to address a single message to all of the attached routers.
- Ethernet is an example of a broadcast network.
Nonbroadcast Multiaccess (NBMA) network
- A network that can support many routers but does not have broadcast capability.
- The sender needs to create an individual copy of the same packet for each recipient if it wishes to inform all connected packet can be transmitted.
- Frame Relay and Asynchronous Transfer Mode (ATM) are examples of an NBMA network type.
NBMA Networks Issues
Split horizon
- Prevents a routing update that is received on an interface from being forwarded out of the same interface.
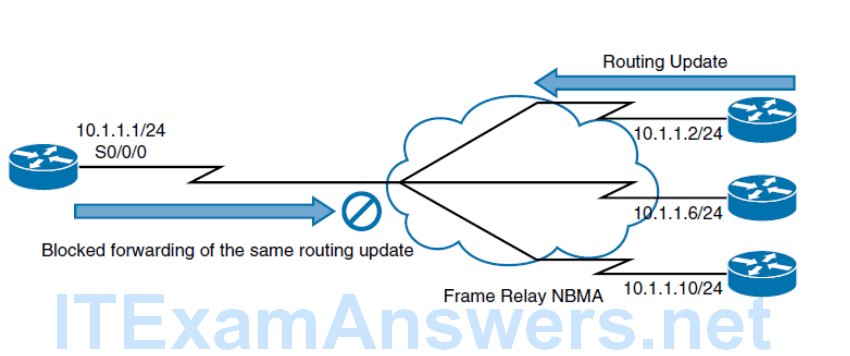
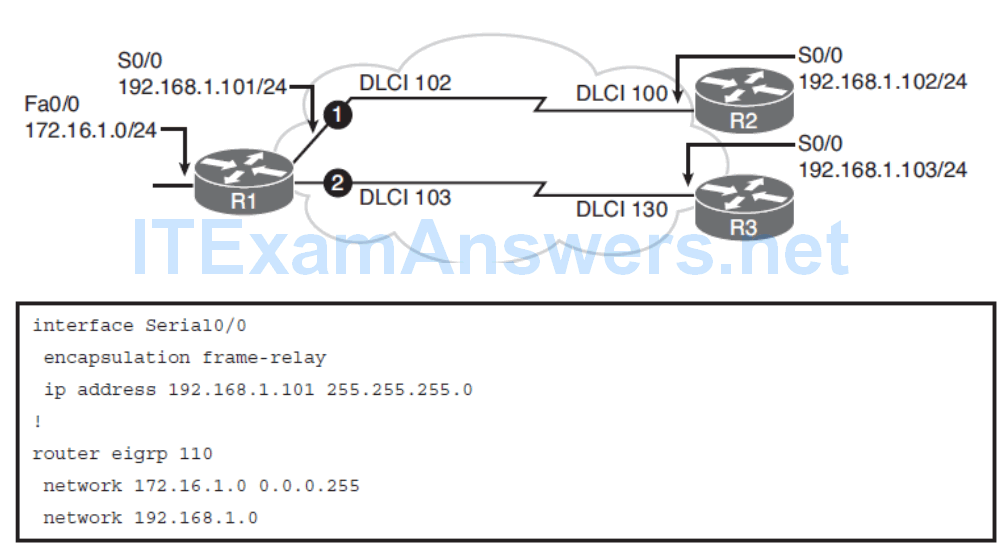
While point-to-point and broadcast networks do not present any difficulties for routing protocols, NBMA networks introduce several challenges. Routing protocols need to be adapted through configuration in how they perform neighbor discovery. Distance vector protocols need additional configuration, which also changes the default behavior of how routing information is exchanged between neighbors. This is due to the loop prevention mechanism split horizon that prevents the transmitting of information that is received on a specific interface from going out of that same interface.
In a scenario using a hub-and-spoke Frame Relay topology, a spoke router sends an update to the hub router that is connecting multiple permanent virtual circuits (PVCs) over a single physical interface. The hub router receives the update on its physical interface but cannot forward it through the same interface to other spoke routers. Split horizon is not a problem if there is a single PVC on a physical interface because this type of connection would be point-to-point
Neighbor discovery
- OSPF over NBMA neighbors are not automatically discovered.
- You can statically configure neighbors, but an additional configuration is required to manually configure the hub as a Designated Router (DR).
- OSPF treats an NBMA network like Ethernet by default
Broadcast replication
- With routers that support multipoint connections over a single interface that terminates at multiple PVCs, the router must replicate broadcast packets.
- These replicated broadcast packets consume bandwidth and cause significant latency variations in user traffic.
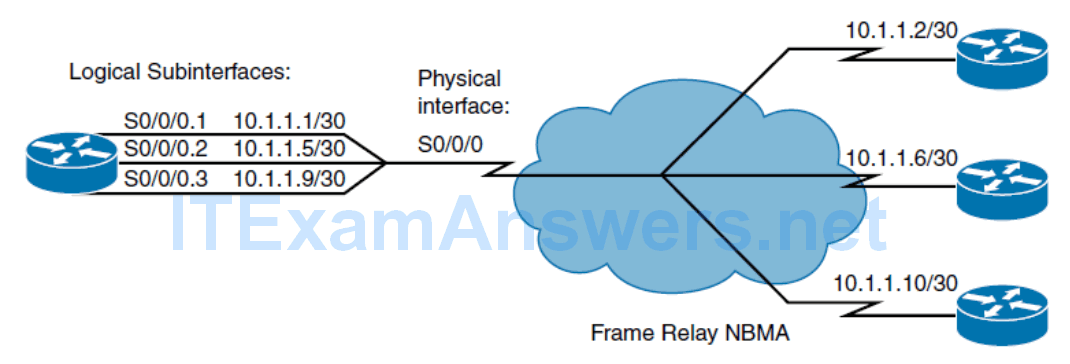
Point-to-point subinterfaces
- Each subinterface, which provides connectivity between two routers, uses its own subnet for addressing.
Point-to-multipoint subinterfaces
- One subnet is shared between all virtual circuits.
- Both EIGRP and OSPF need additional configuration to support this underlying technology.
Connecting Remote Locations with Headquarters
- Identify options for connecting branch offices and remote locations
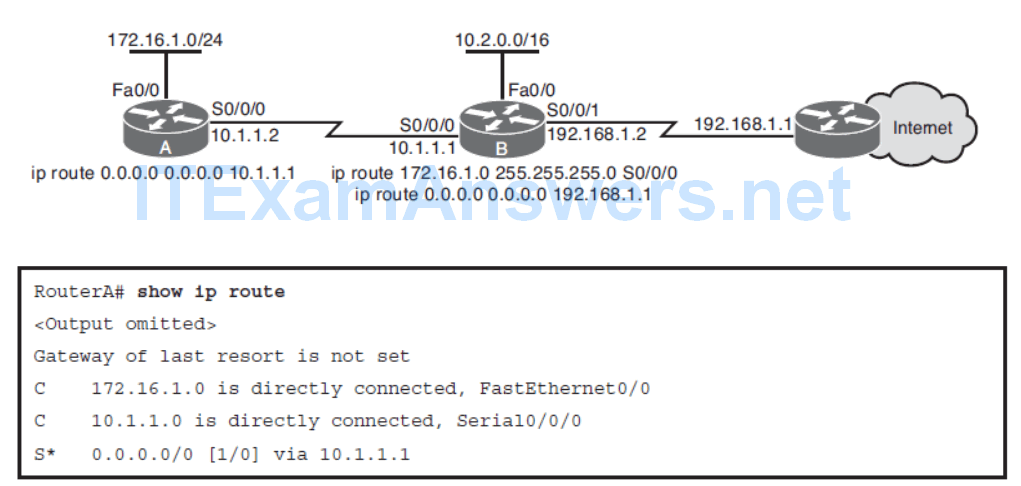
- Describe the use of static and default static routes
- Describe basic PPP configuration on point-to-point serial links
- Describe basic Frame Relay on point-to-point serial links
- Explain VRF Lite
- Describe the interaction of routing protocols over MPLS VPNs
- Explain the use of GRE for branch connectivity
- Describe Dynamic Multipoint virtual private networks
- Describe multipoint GRE tunnels
- Describe the Next Hop Resolution Protocol
- Identify the role of IPsec in DMVPN solutions
Principles of Static Routing
A static route can be used in the following circumstances
- When it is undesirable to have dynamic routing updates forwarded across slow bandwidth links, such as a dialup link.
- When the administrator needs total control over the routes used by the router.
- When a backup to a dynamically recognized route is necessary.
- When it is necessary to reach a network accessible by only one path (a stub network).
- When a router connects to its ISP and needs to have only a default route.
- When a router is underpowered and does not have the CPU or memory resources necessary to handle a dynamic routing protocol.
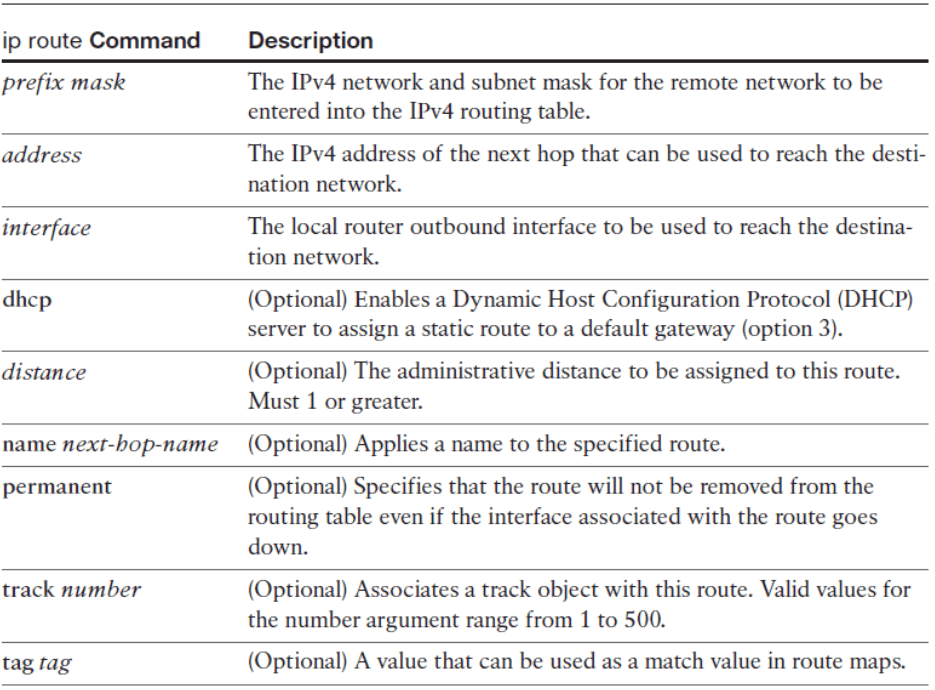
Configuring an IPv4 Static Route
ip route prefix mask { address | interface [ address ]} [ dhcp ] [ distance ] [ name next-hop-name ] [ permanent | track number ] [ tag tag ]
Configuring a Static Default Route
Basic PPP Overview
- Point-to-Point Protocol (PPP) has several advantages over its predecessor High-Level Data Link Control (HDLC).
- Authentication
- Multi-link
- Compression
- Quality
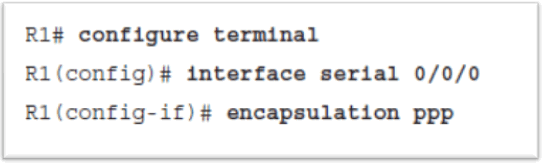
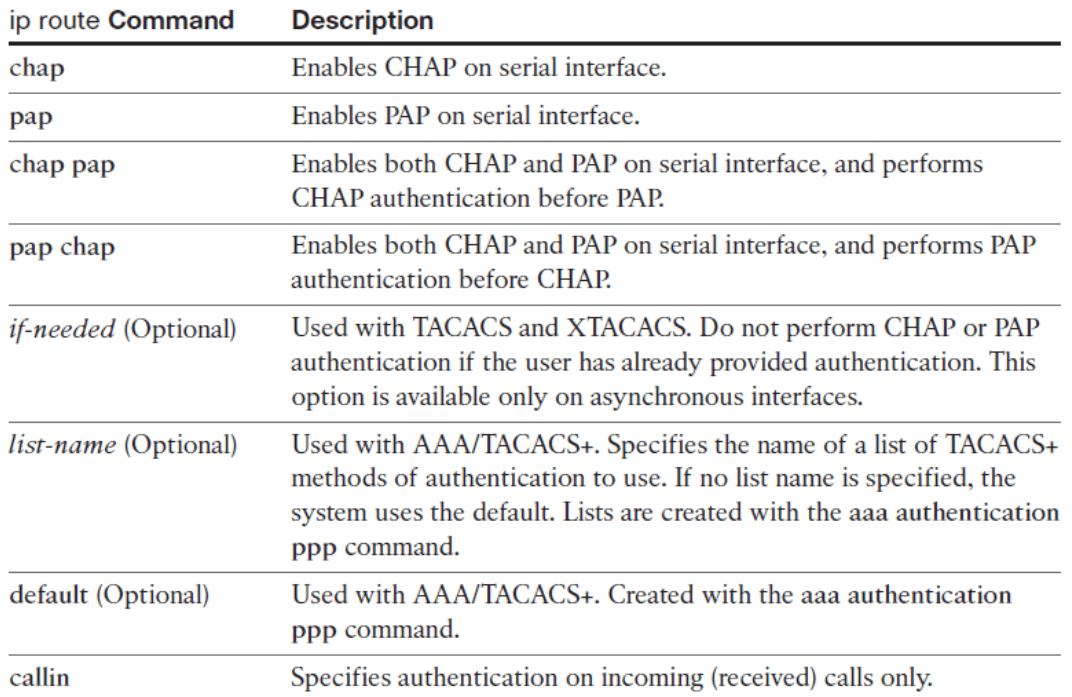
PPP Authentication Overview
Router(config-if)# ppp authentication { chap | chap pap | pap chap | pap } [ if-needed ][ list-name | default ] [ callin ]
PPP Configuration Example
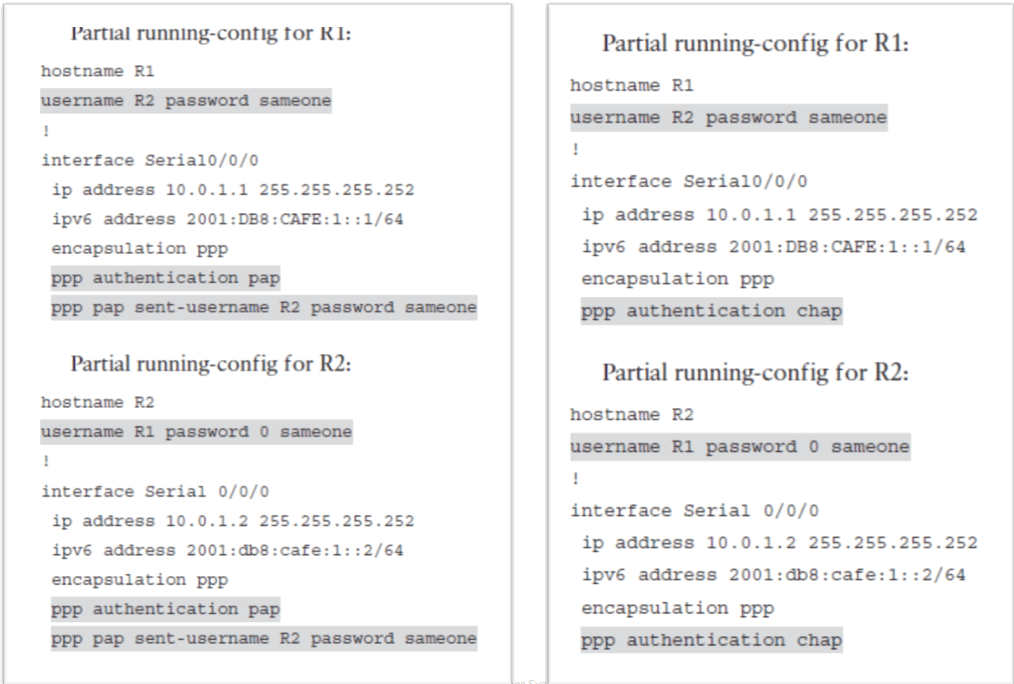
PPPoE
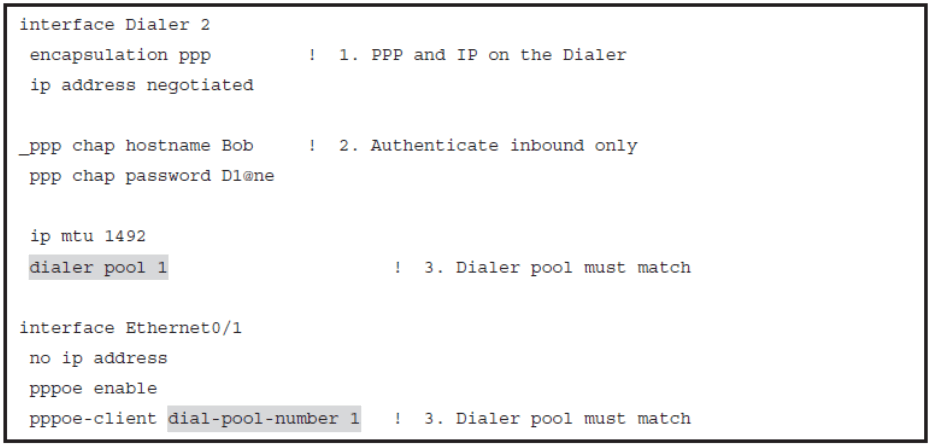
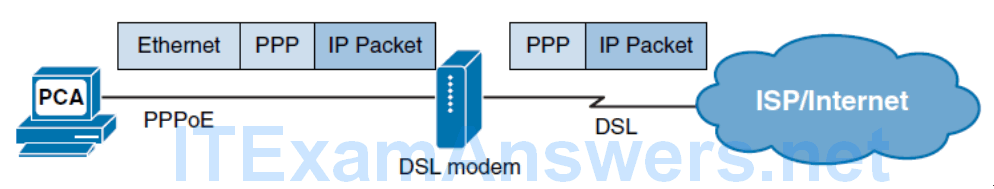
1. To create a PPP tunnel, the configuration uses a dialer interface. A dialer interface is a virtual interface. The PPP configuration is placed on the dialer interface, not on the physical interface. The dialer interface is created using the interface dialer number command. The client can configure a static IP address, but will more likely be automatically assigned a public IP address by the ISP.
2. The PPP CHAP configuration usually defines one-way authentication; therefore, the ISP authenticates the customer. The hostname and password configured on the customer router must match the hostname and password configured on the ISP router.
3. The physical Ethernet interface that connects to the DSL modem is then enabled with the command pppoe enable that enables PPPoE and links the physical interface to the dialer interface. The dialer interface is linked to the Ethernet interface with the dialer pool and pppoe-client commands, using the same number. The dialer interface number does not have to match the dialer pool number.
4. The maximum transmission unit (MTU) should be reduced to 1492, versus the default of 1500, to accommodate the PPPoE headers. The default maximum data field of an Ethernet frame is 1500 bytes. However, in PPPoE the Ethernet frame payload includes a PPP frame which also has a header. This reduces the available data MTU to 1492 bytes.
Basic Frame Relay Overview
Frame Relay provides several benefits over traditional point-to-point leased lines
- No need for separate physical interface per connection on the router
- Bandwidth cost is much more flexible
Frame Relay is a switched WAN technology where virtual circuits (VCs) are created by a service provider (SP) through the network.
- The VCs are typically PVCs that are identified by a data-link connection identifier (DLCI)
By default, a Frame Relay network is an NBMA network.
- To emulate the LAN broadcast capability that is required by IP routing protocols Cisco IOS implements pseudo-broadcasting
- Dynamic maps always allow pseudo-broadcasting.
Dynamic maps created via Frame Relay Inverse Address Resolution Protocol (INARP) for IPv4 or Frame Relay Inverse Neighbor Discovery (IND) for IPv6
Split horizon is disabled by default on Frame Relay physical interfaces.
pseudo-broadcasting, in which the router creates a copy of the broadcast or multicast packet for each neighbor reachable through the WAN media, and sends it over the appropriate PVC for that neighbor.
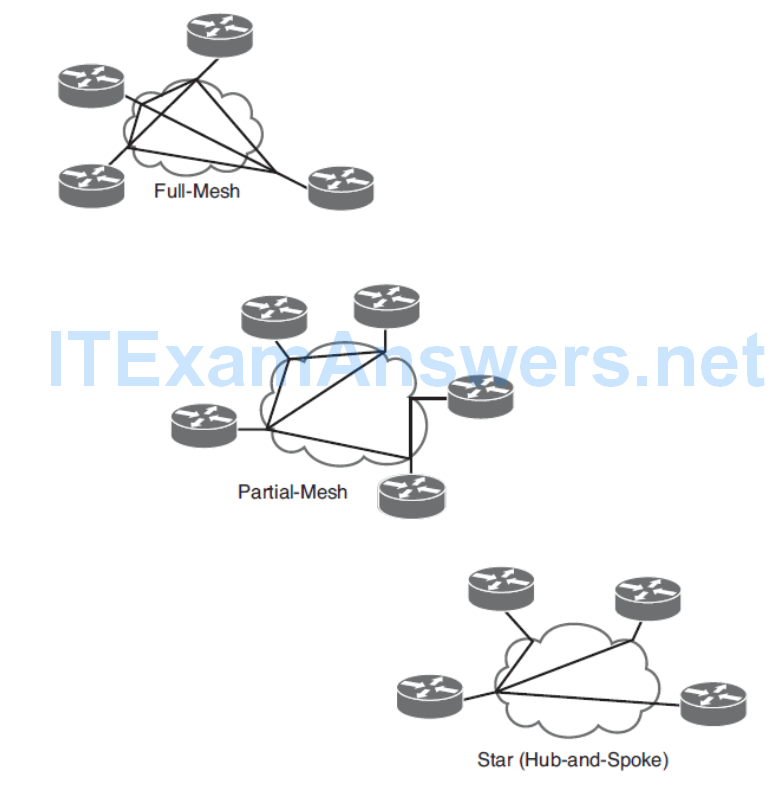
Frame Relay Topologies
Basic Frame Relay Configuration
VPN Connectivity Overview
MPLS-based VPNs
Tunneling VPNs
- GRE
- Ipsec
- DMVPN
L3 MPLS VPNs
Traffic forwarding through the MPLS backbone is based on labels that are previously distributed among the core routers.
With a Layer 3 MPLS VPN, the service provider participates in customer routing.
The service provider establishes routing peering between the PE and CE routers.
Then customer routes that are received on the PE router are redistributed into MP-BGP and conveyed over the MPLS backbone to the remote PE router.
On the remote PE, these customer routes are redistributed back from MP-BGP into a remote PE-CE routing protocol.
Routing protocols between PE-CE routers on the local and remote sites may be totally different.
L2 MPLS VPNs
A Layer 2 MPLS VPN CE router interconnects with the PE router at Layer 2 using any Layer 2 protocol with Ethernet being the most common.
Layer 2 traffic is sent between PE routers, over a pre-established pseudowire.
Pseudowire emulates a wire between PE routers that carries Layer 2 frames across the IP-MPLS backbone.
There are two basic Layer 2 MPLS VPN service architectures.
- Virtual Private Wire Service (VPWS) is a point-to-point technology that allows the transport of any Layer 2 protocol at the PE.
- The second type of Layer 2 MPLS VPN is Virtual Private LAN Service (VPLS), which emulates an Ethernet multiaccess LAN segment over the MPLS core and provides multipoint- to-multipoint service.
Tunneling VPNs
GRE
- Tunneling protocol developed by Cisco that enables encapsulation of arbitrary Layer 3 protocols inside a point-to-point, tunnel-over-IP network.
- Traffic that is transported over the GRE tunnel is not encrypted
- GRE traffic is usually encapsulated within IPsec.
IPsec
- Is a framework that uses a set of cryptographic protocols to secure traffic at Layer 3.
DMVPN
- This solution offers the capability to dynamically establish hub-to-spoke and spoke-to-spoke IPsec tunnels, thus reducing latency and optimizing network performance.
- DMVPN supports dynamic routing protocols between hub and spokes as well as IP multicast. It is also suitable for environments with dynamic IP addresses on physical interfaces such as DSL or cable connections.
Routing Across MPLS VPNs
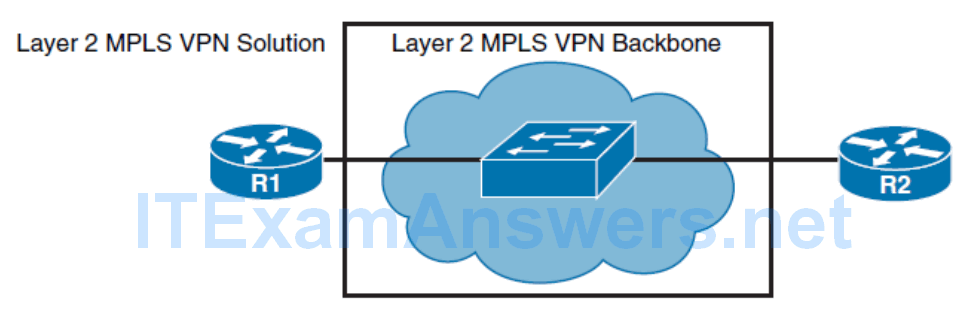
The Layer 2 MPLS VPN backbone solution is providing the Layer 2 service across the backbone, where R1 and R2 are connected together directly using the same IP subnet.
If you deploy a routing protocol over the Layer 2 MPLS VPN, neighbor adjacency is established between your R1 and R2 routers. The figure presents the connectivity through the backbone, which can be illustrated as one big switch.
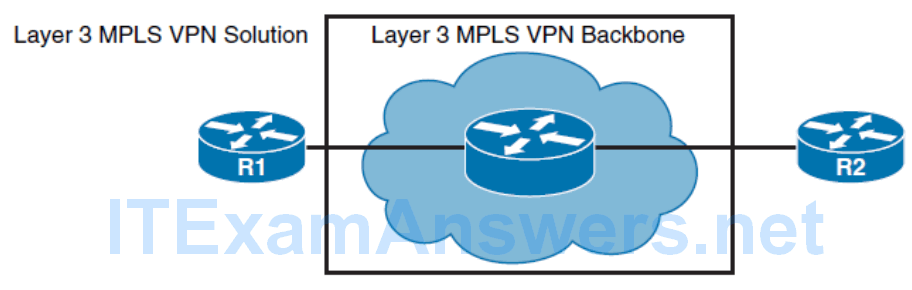
The Layer 3 MPLS VPN backbone solution is providing the Layer 3 service across the backbone, where R1 and R2 are connected to ISP edge routers.
A separate IP subnet is used on each side. If you deploy a routing protocol over this VPN, service providers need to participate in it.
Neighbor adjacency is established between your R1 and the closest PE router and between your R2 and it’s closest PE router.
Routing Over GRE Tunnel
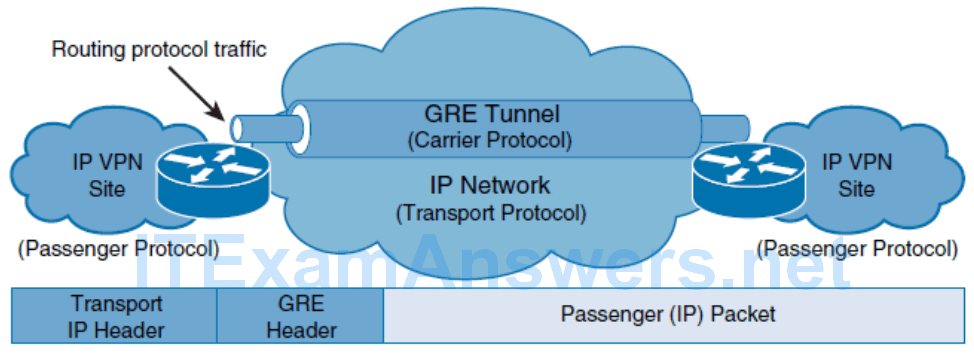
- A passenger protocol or encapsulated protocol, such as IPv4 or IPv6 that is being encapsulated.
- A carrier protocol, GRE in this example, that is defined by Cisco as a multiprotocol carrier protocol.
- A transport protocol, such as IP, that carries the encapsulated protocol.
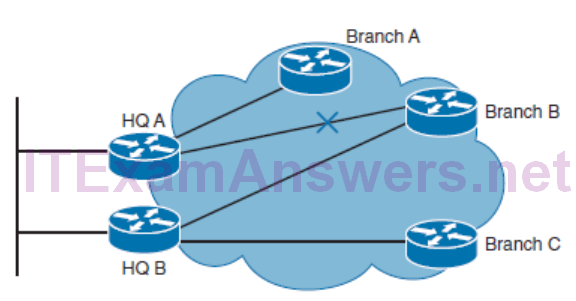
Dynamic Multipoint Virtual Private Network
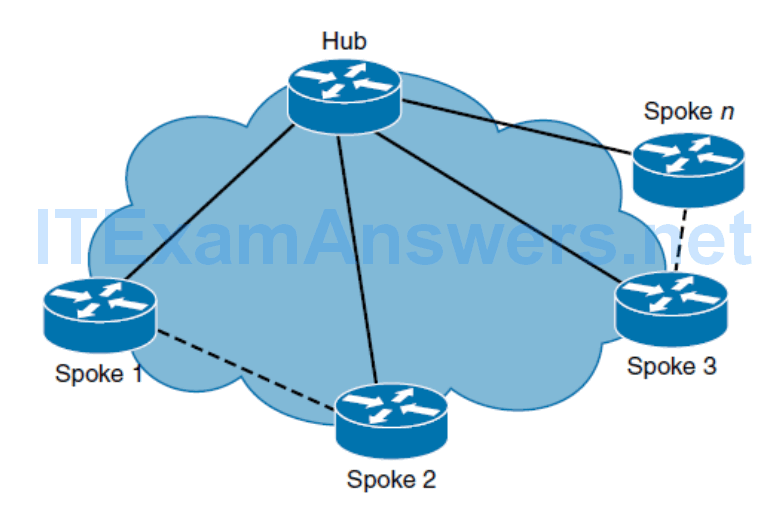
With a generic hub-and-spoke topology, you can typically implement static tunnels (typically GRE with IPsec) between central hub and remote spokes. When a new spoke needs to be added to the network, it requires configuration on the hub router. In addition, traffic between spokes has to traverse the hub, where it must exit one tunnel and enter another. Static tunnels may be an appropriate solution for small networks, but this solution becomes unacceptable as the number of spokes grows larger and larger.
DMVPN
The primary benefits of DMVPNs follow:
Hub router configuration reduction
- Traditionally, the individual configuration of a GRE tunnel and IPsec would need to be defined for each individual spoke router. The DMPVN feature enables the configuration of a single mGRE tunnel interface and a single IPsec profile on the hub router to manage all spoke routers
Automatic IPsec initiation
- GRE uses NHRP to configure and resolve the peer destination address. This feature allows IPsec to be immediately triggered to create point-to-point GRE tunnels without any IPsec peering configuration.
Support for dynamically addressed spoke routers
- When using point-to-point GRE and IPsec hub-and-spoke VPN networks, it is important to know the physical interface IP address of the spoke routers when configuring the hub router.
- DMVPN enables spoke routers to have dynamic physical interface IP addresses and uses NHRP to register the dynamic physical interface IP addresses of the spoke routers with the hub router.
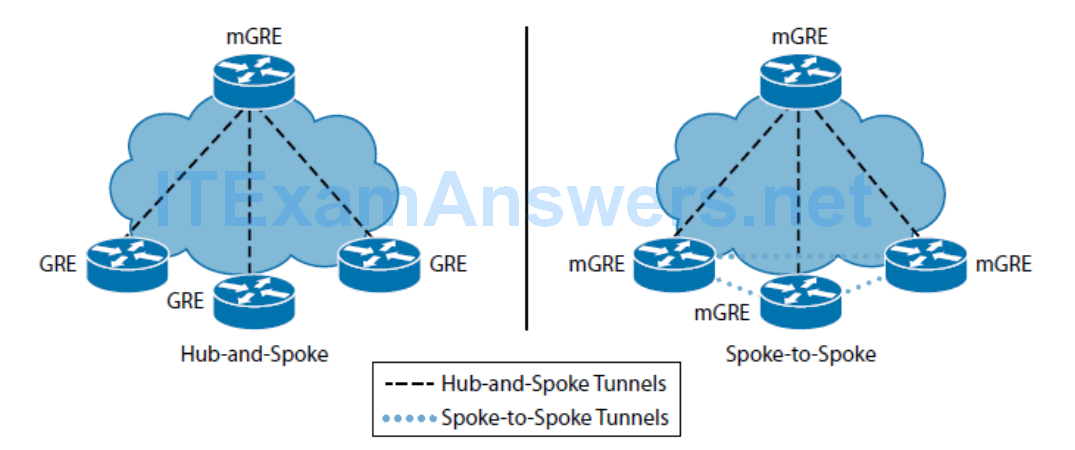
Multipoint GRE
The main characteristics of the mGRE configuration are as follows:
- Only one tunnel interface needs to be configured on a router to support multiple remote GRE peers
- To learn the IP addresses of other peer, devices using mGRE require NHRP to build dynamic GRE tunnels.
- mGRE interfaces also support unicast, multicast, and broadcast traffic.
NHRP
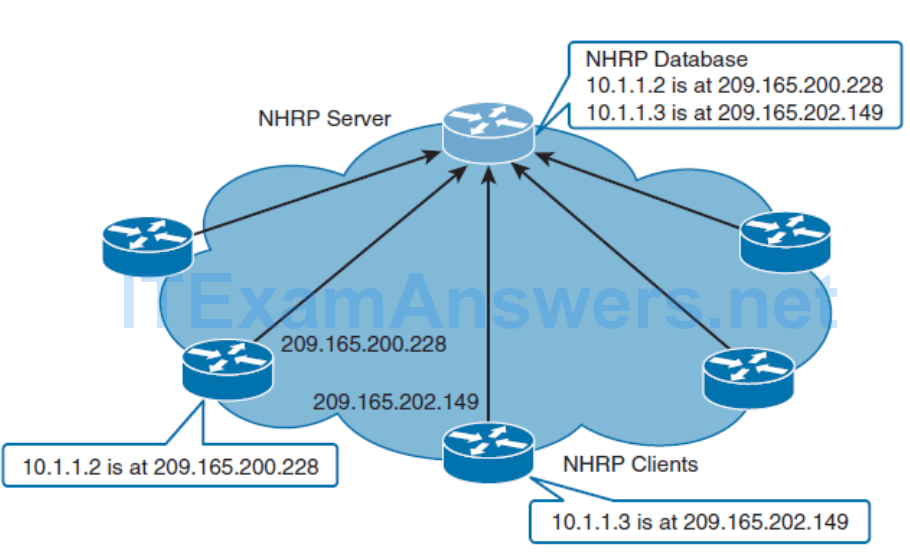
NHRP is a client-server protocol, as illustrated in Figure 1-21 . The hub acts as the server, and the spokes are clients. NHRP is used by routers to determine the IP address of the next hop in IP tunneling networks. When a spoke router initially connects to a DMVPN network, it registers its inner (tunnel) and outer (physical interface) address with the hub router (NHRP server). This registration enables the mGRE interface on the hub router to build a dynamic GRE tunnel back to the registering spoke router without having to know the branch tunnel destination in advance. Therefore, NHRP creates a mapping for a tunnel IP address to the physical interface IP address for each spoke at the hub.
- From the routing protocol perspective, the NHRP domain operates similarly to an NBMA network, such as a multipoint Frame Relay network.
- Using NHRP in mGRE networks maps inner tunnel IP addresses to the outer transport IP addresses. In a hub-and-spoke DMVPN deployment, no GRE or IPsec information about a spoke is configured on the hub router. The spoke router for the GRE tunnel is configured (via NHRP commands) with information about the hub router as the next-hop server.
- When the spoke router starts up, it automatically initiates the IPsec tunnel with the hub route. It then uses NHRP to notify the hub router of its current physical interface IP address.
- Configuration of the hub router is shortened and simplified because it does not need to have GRE or IPsec information about the peer routers. All of this information is learned dynamically via NHRP.
- When you add a new spoke router to the DMVPN network, you do not need to change the configuration on the hub or on any of the current spoke routers. The new spoke router is configured with the hub information, and when it starts up, it dynamically registers with the hub router. The dynamic routing protocol propagates the routing information from the spoke to the hub. The hub propagates new routing information to the other spokes, and it also propagates the routing information from the other spokes to the new spoke.
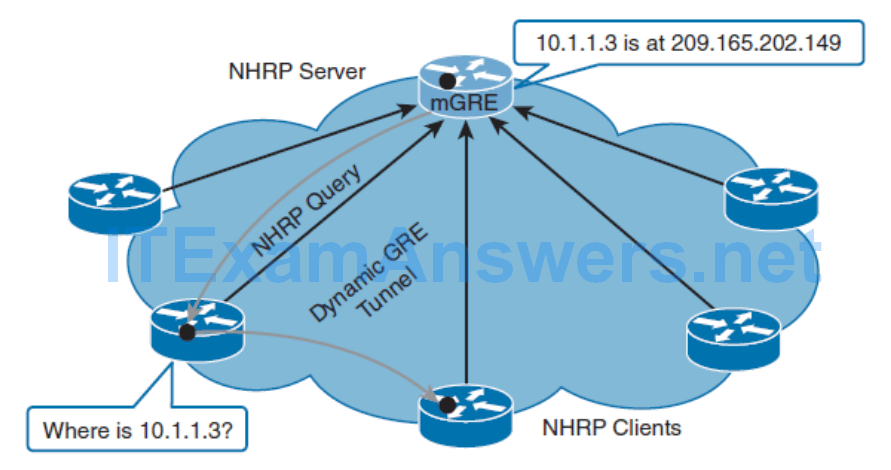
- In Figure 1-22 , one spoke wants to send IP traffic to another spoke, which has a tunnel interface that is configured with the IP address of 10.1.1.3. The originating router sends an NHRP query for the 10.1.1.3 IP address to the hub, which is configured as an NHRP server. The hub responds with information that IP address 10.1.1.3 is mapped to the physical interface (209.165.202.149) of the receiving spoke router.
IPsec
IPsec provides four important security services:
Confidentiality (encryption)
- No one can eavesdrop on the communication. If the communication is intercepted, it cannot be read.
Data integrity
- The receiver can verify that the data was transmitted through the path without being changed or altered in any way.
Authentication
- Authentication ensures that the connection is made with the desired communication partner. IPsec uses Internet Key Exchange (IKE) to authenticate users and devices that can carry out communication independently.
Antireplay protection
- Antireplay protection verifies that each packet is unique and not duplicated.
Routing and TCP/IP Operations
- MSS, Fragmentation, and PMTUD
- IPv4 Fragmentation and PMTUD
- Bandwidth Delay Product
- TCP Starvation
- Latency
- ICMP Redirect
MSS, Fragmentation, and PMTUD
- An IPv4 packet has a maximum size of 65,535 bytes
- An IPv6 packet with a hop-by-hop extension header and the jumbo payload option can support up to 4,294,967,295 bytes
- However, most transmission links enforce a smaller maximum packet length called the maximum transmission unit (MTU).
- When a router receives an IPv4 packet larger than the MTU of the egress or outgoing interface, it must fragment the packet unless the DF (Don’t Fragment) bit is set in the IPv4 header.
Fragmentation causes several issues including the following:
- CPU and memory overhead in fragmentation of the packet
- CPU and memory overhead in destination devices during reassembly of packets
- Retransmission of the entire packet when one fragment is dropped
- Firewalls that do Layer 4 through Layer 7 filtering may have trouble processing IPv4 fragments correctly
IPv4 Fragmentation and PMTUD
- TCP Maximum Segment Size (MSS) defines the largest amount of data that the receiving device is able to accept in a single TCP segment.
- To avoid fragmentation of an IPv4 packet, the selection of the TCP MSS is the minimum buffer size and MTU of the outgoing interface minus 40 bytes. The 40 bytes take into account the 20-byte IPv4 header and the 20-byte TCP header.
- The TCP MSS helps avoid fragmentation at the two ends of the TCP connection but it does not prevent fragmentation due to a smaller MTU on a link along the path.
- Path MTU Discovery (PMTUD) was developed for the purpose of determining the lowest MTU along a path from the packet’s source to destination.
- PMTUD is only supported by TCP.
Bandwidth Delay Product
- TCP can experience bottlenecks on paths with high bandwidth and long round-trip delays.
- These networks are known as a long fat pipe or long fat network , LFN (pronounced “elephan [t]).”
- The key parameter is the Bandwidth Delay Product (BDP), which is the product of the bandwidth (bps) times the round-trip delay (RTT in seconds).
- The BDP is the number of bits it takes to “fill the pipe” (in other words, the amount of unacknowledged data that TCP must handle to keep the pipeline full).
- BDP is used to optimize the TCP window size to fully utilize the link.
- The result is the maximum of data that can be transmitted on the link at any given time. The TCP window size should then use the BDP.
- The TCP window size indicates the amount of data that can be sent before expecting an acknowledgment, usually several times the MSS.
TCP Starvation
- TCP incorporates mechanisms for reliability, flow control, and congestion avoidance.
- However, UDP is a lightweight protocol for faster and simpler data transmissions and does not include these features.
- When there is a combination of TCP and UDP flows during a period of congestion, TCP tries to do its part by backing off on bandwidth, called slow start .
- However, UDP without any flow control mechanisms continues, potentially using up the available bandwidth given up by TCP.
- This is known as TCP starvation/UDP dominance .
- It is not always possible to separate TCP- and UDP-based flows, but it is important to be aware of this behavior when mixing applications that use both transport layer protocols.
Latency
- Latency is the amount of time for a message to go from point to another.
- Network latency is the amount of time for the packet to travel the network from the original source to the final destination.
- Several factors can cause latency, including propagation delay, serialization, data protocols, routing, switching, queuing, and buffering.
- The flow control and reliability features of TCP have an effect on end-to-end latency.
- TCP requires an established virtual connection, and bidirectional communications for acknowledgments, window sizes, congestion control, and other TCP mechanisms, all of which has an effect on latency.
- UDP is a protocol that does not include reliability or flow control. A device simply sends packets with UDP segments with the assumption that they will reach their destination.
- UDP is typically used for applications such as streaming media that require minimal delay and can tolerate occasional packet loss. UDP has very low latency, better than most TCP connections.
ICMP Redirect
- ICMPV4 Redirect messages are used by routers to notify the sender of a packet that there is a better route available for a particular destination.
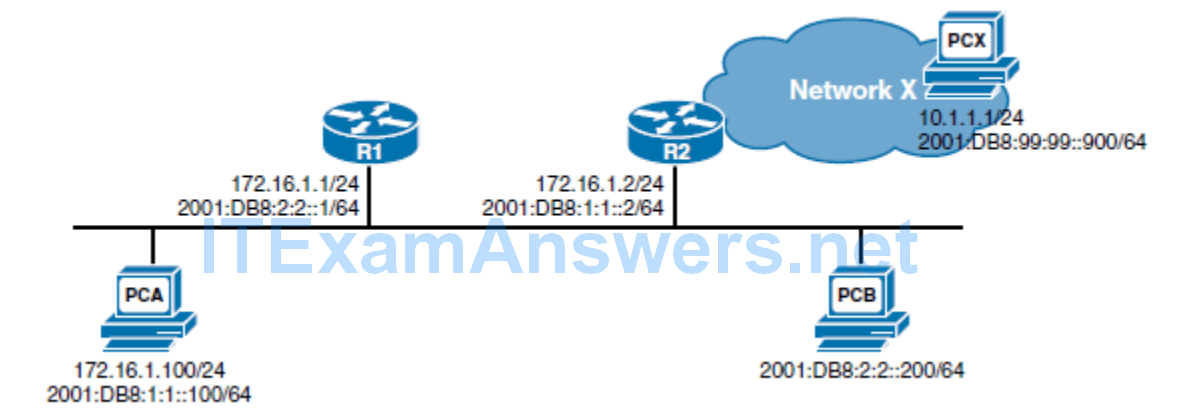
- Similar to IPv4, R1 will forward the IPv6 packet to PCB, but unlike ICMP for IPv4, it will send an ICMPv6 redirect message to PCA informing the source of the better route. PCA can now send subsequent IPv6 packets directly to PCB even though it is on a different IPv6 network.
- ICMP Redirect messages are used by routers to notify the sender of a packet that there is a better route available for a particular destination.
- For example, in Figure 1-23 , two routers, R1 and R2, are connected to the same Ethernet segment as host PCA. The IPv4 default gateway of PCA is the IPv4 address of router R1. PCA sends a packet for PCX to its default gateway R1. R1 examines its routing table and determines the next hop as router R2, on the same Ethernet segment as PCA. R1 forwards the packet out the same interface used to receive the packet from PCA. R1 also sends an ICMP Redirect message informing PCA of a better route to PCX by way of R2. PCA can now forward subsequent packets more directly using R2 as the next-hop router.
- The ICMPv6 (ICMP for IP version 6) Redirect message functions the same way as the Redirect message for ICMPv4, with one additional feature. In Figure 1-23 , PCA and PCB are on separate IPv6 networks. R1 is the IPv6 default gateway for PCA. When sending an IPv6 packet to PCB, a device on the same Ethernet segment but different IPv6 networks, PCA will forward that packet to R1, its default gateway. Similar to IPv4, R1 will forward the IPv6 packet to PCB, but unlike ICMP for IPv4, it will send an ICMPv6 redirect message to PCA informing the source of the better route. PCA can now send subsequent IPv6 packets directly to PCB even though it is on a different IPv6 network.
Implementing RIPng
- Describe general RIP characteristics
- Describe how to configure and verify basic RIPng
- Describe how to configure RIPng to share default routes
- Analyze the RIPng database
RIP Overview
- RIP is an IGP that is used in smaller networks.
- It is a distance vector routing protocol that uses hop count as a routing metric.
- There are three versions of RIP: RIPv1, RIPv2, and RIPng. RIPv1 and RIPv2 route in IPv4 networks.
- RIPng routes in IPv6 networks.
- RIP is a standardized IGP routing protocol that works in a mixed-vendor router environment.
- RIP uses hop count, the number of routers, as the metric.
- If a device has two paths to the destination network, the path with fewer hops will be chosen as the path to forward traffic.
- If a network is 16 or more hops away, the router considers it unreachable.
- As a routing loop-prevention technique, RIP implements split horizon. Split horizon prevents routing information from being sent out the same interface from which it was received.
- Split horizon with poison reverse is a similar technique but sends the update with a metric of 16, which is considered unreachable by RIP.
- RIP is also capable of load balancing traffic over equal-cost paths.
- The default is four equal-cost paths.
- If the maximum number of paths is set to one, load balancing is disabled.
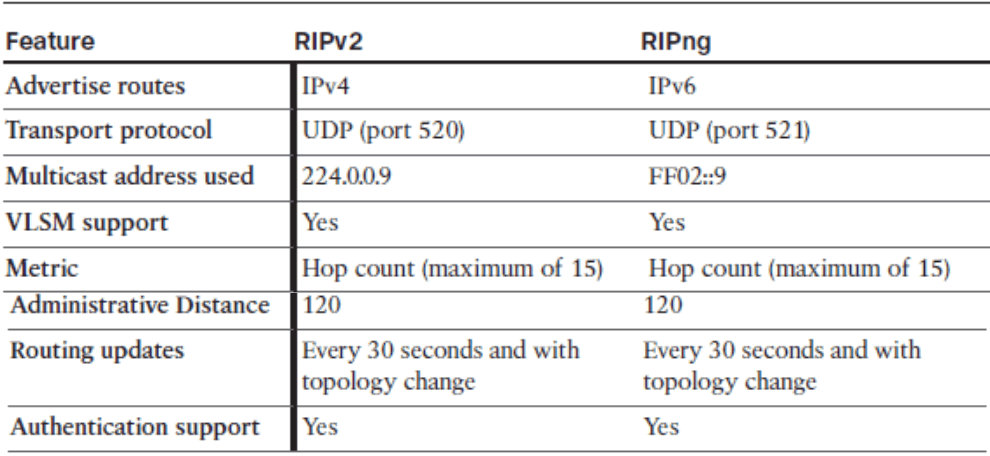
Comparing Features in RIPv2 and RIPng
RIPv2 Configuration
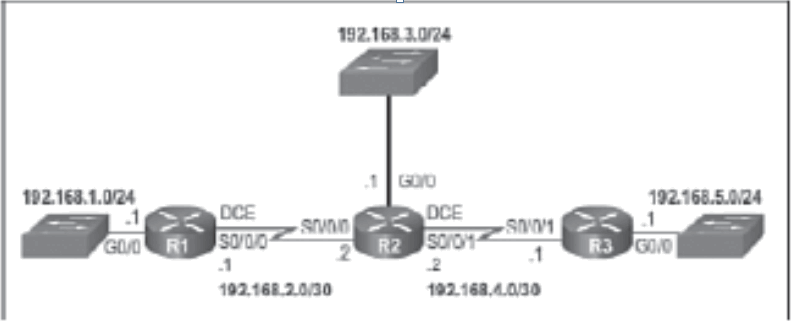
- By default, RIPv2 automatically summarizes networks at major network boundaries, summarizing routes to the classful network address
- When route summarization is disabled, the software sends subnet routing information across classful network boundaries.
Router(config-router)# no auto-summary
- The ip summary-address rip ip-address network-mask interface command is used to summarize an address or subnet under a specific interface.
Router(config-if)# ip summary-address rip 10.2.0.0 255.255.0.0
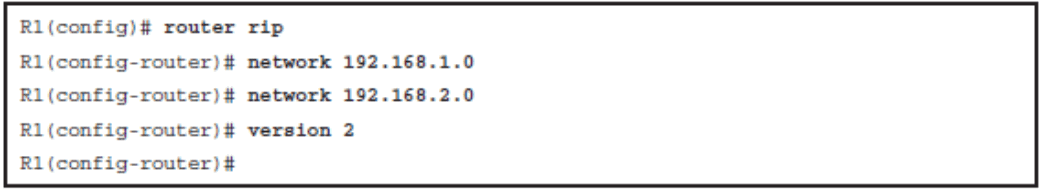
Configuring RIPng
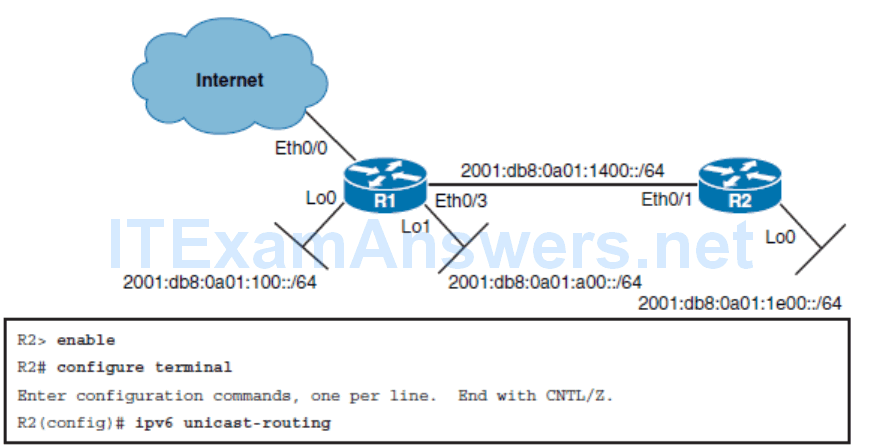
R2(config)# ipv6 router rip CCNP_RIP
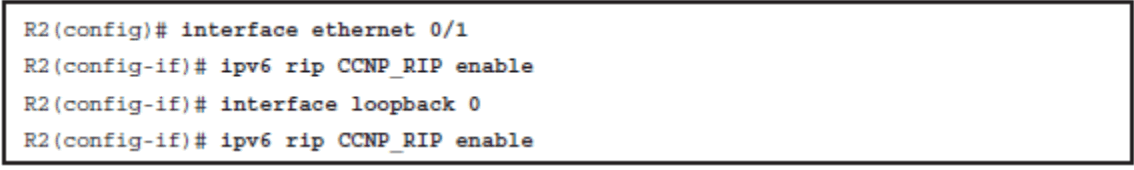
- While IPv4 routing is enabled by default on Cisco routers, IPv6 routing is not.
- If you forgot to create a routing process using the ipv6 router rip name command and you enable RIPng on an interface, the command will be accepted. In this case, the RIPng process will be automatically created by Cisco IOS Software.
- Suppose that you created a RIPng routing process called “CCNP_RIP” in the second step of configuring RIPng. But then in the fourth step, you made a mistake and enabled RIPng on an interface using the process name “CCNP_PIR.” The command will not be rejected.
- Cisco IOS Software will create a new RIPng process called “CCNP_PIR.” You will end up with two routing processes, one that was created by you directly and the second that Cisco IOS Software created on your behalf. AS RIPng process name has local significance, and as both interfaces will be included in the same routing process, RIPng configuration will be operational, even though two processes with different names has been defined.
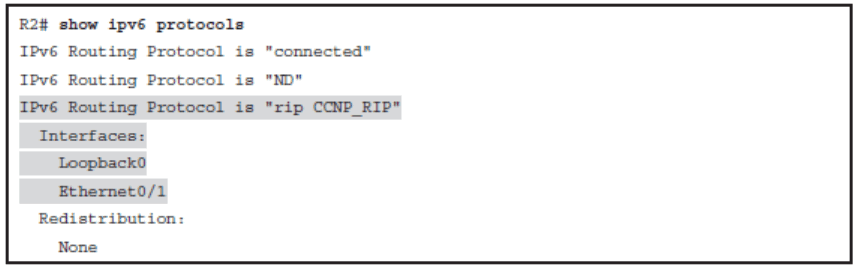
Verify RIPng Configuration
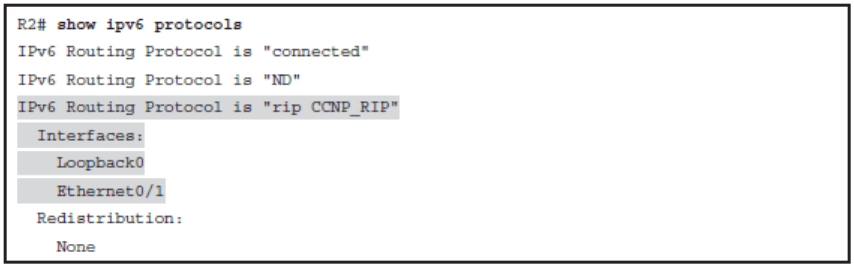
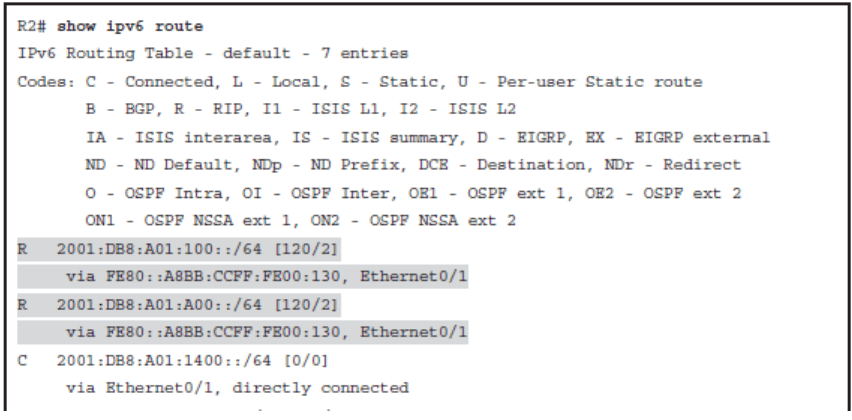
- The metric for RIPng routes in the routing table is shown as 2. In RIPng, the sending router already considers itself to be one hop away; therefore
- There is a significant difference in how RIPv2 and RIPng calculate the number of hops for a remote network. In RIPng, the routers adds one hop to the metric when it receives the RIPng update and then includes that metric in its IPv6 routing table for that network. In RIPv1 and RIPv2, the router receives the RIP update, uses that metric for its IPv4 routing table and then increments the metric by one before sending the update to other routers. The effect of all of this is that RIPng will show a metric, a hop count of one more than RIPv1 or RIPv2.
RIPng Summarization
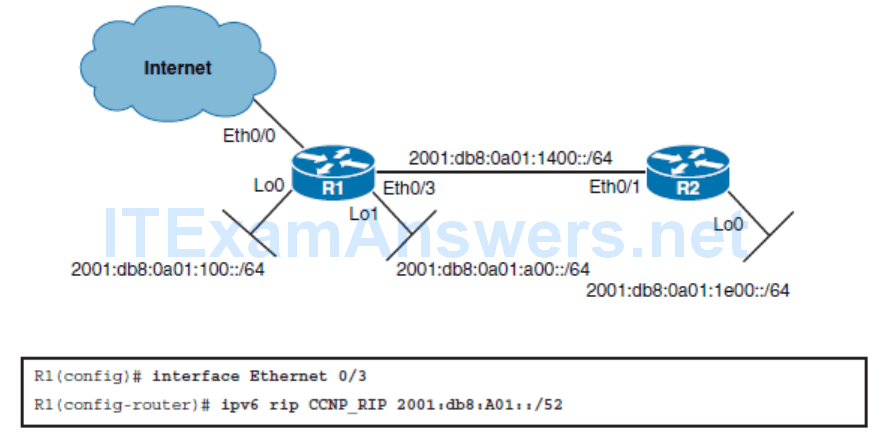
- The same process for summarizing IPv4 networks is used for summarizing IPv6 prefixes.
- The 2001:DB8:A01:100::/64 and 2001:DB8:A01:A00::/64 prefixes have the first 52 bits in common, represented as 2001:DB8:A01::/52.
Propagating a Default Route
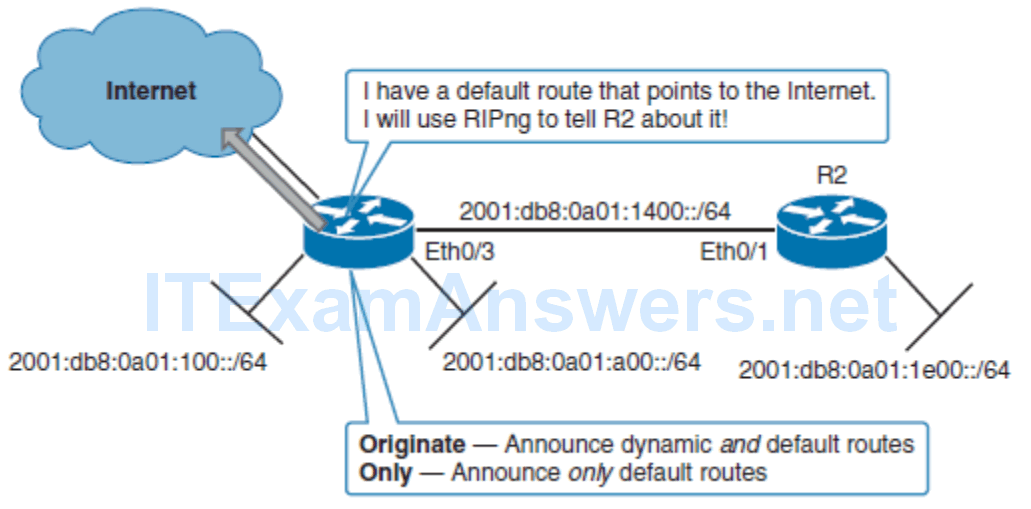
R1(config-if)# ipv6 rip name default-information originate | only
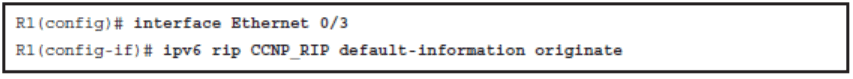
RIPng Verification Commands
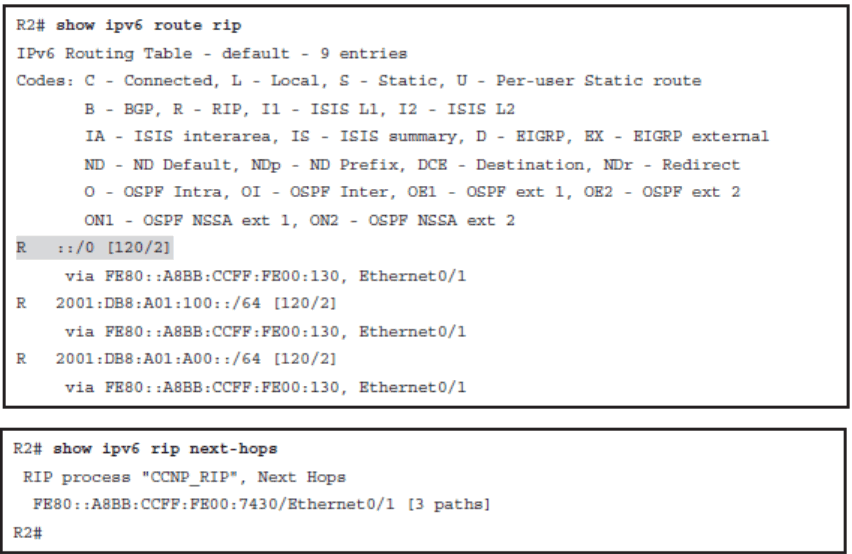
Investigating the RIPng Database
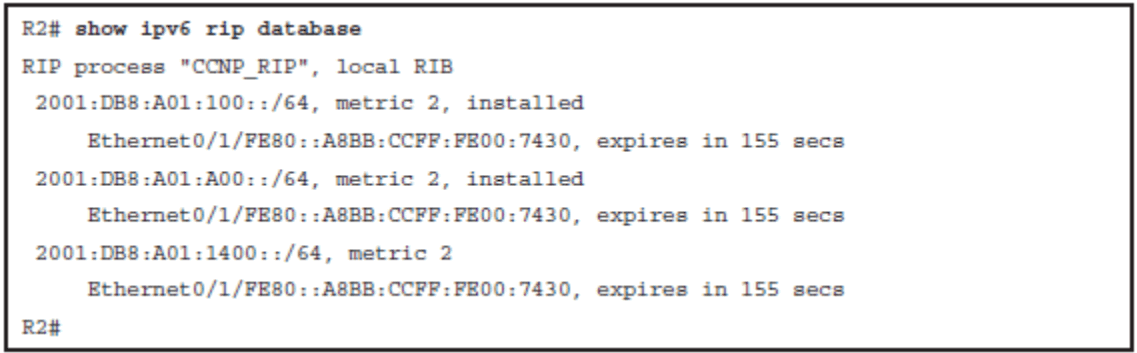
- The RIP process (there can be multiple RIPng processes on a single router).
- The route prefix.
- The route metric, in which RIPng uses hop count as a metric. In the example, all three routes have a metric of 2. This means the destination network is 2 hops away, counting itself as a hop.
- Installed and expired, in which the keyword “installed” means the route is in the routing table. If a network becomes unavailable, the route will become “expired” after the dead timer expires. An expired route value (in seconds), during which the route will be advertised as expired, is listed.
- Expires in, in which if the countdown timer reaches 0, the route is removed from the routing table and marked expired. This timer, the dead timer, is by default three times the hello timer—180 seconds.
Chapter 1 Summary
- The role of static routes and dynamic routing protocols in enterprise networks.
- The differences between IGP and EGP routing protocols.
- The three types of routing protocols: distance vector, link-state and path vector.
- The importance of convergence time and how route summarization reduced convergence time and improves scalability.
- The four traffic types: unicast, multicast, anycast, and broadcast.
- The differences between point-to-point, broadcast, and NBMA networks.
- How point-to-point subinterfaces are used to overcome the limitations of NBMA networks.
- How VPNs are used to provide security of a public Internet.
- Common types of VPNs: MPLS-based VPNs, GRE+IPsec, and DMVPN.
- How a customer establishes connectivity with a service provider using a routing protocol and a layer 3 MPLS VPN.
- How static GRE tunnels can establish virtual point-to-point links and support dynamic routing protocols.
- Using DMVPN to provide fully meshed VPN connectivity with a simple hub-andspoke configuration.
- How DMVPN relies on NHRP, mGRE, and IPsec.
- The differences and similarities between RIPv2 and RIPng.
- How to configure RIPng.
- How to propagate a default route in RIPng.
