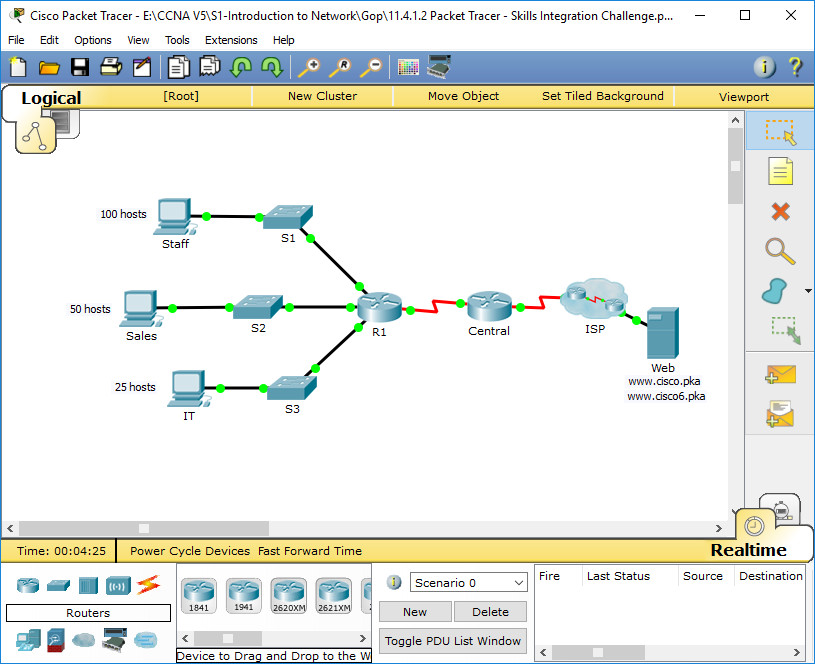
Packet Tracer – Skills Integration Challenge
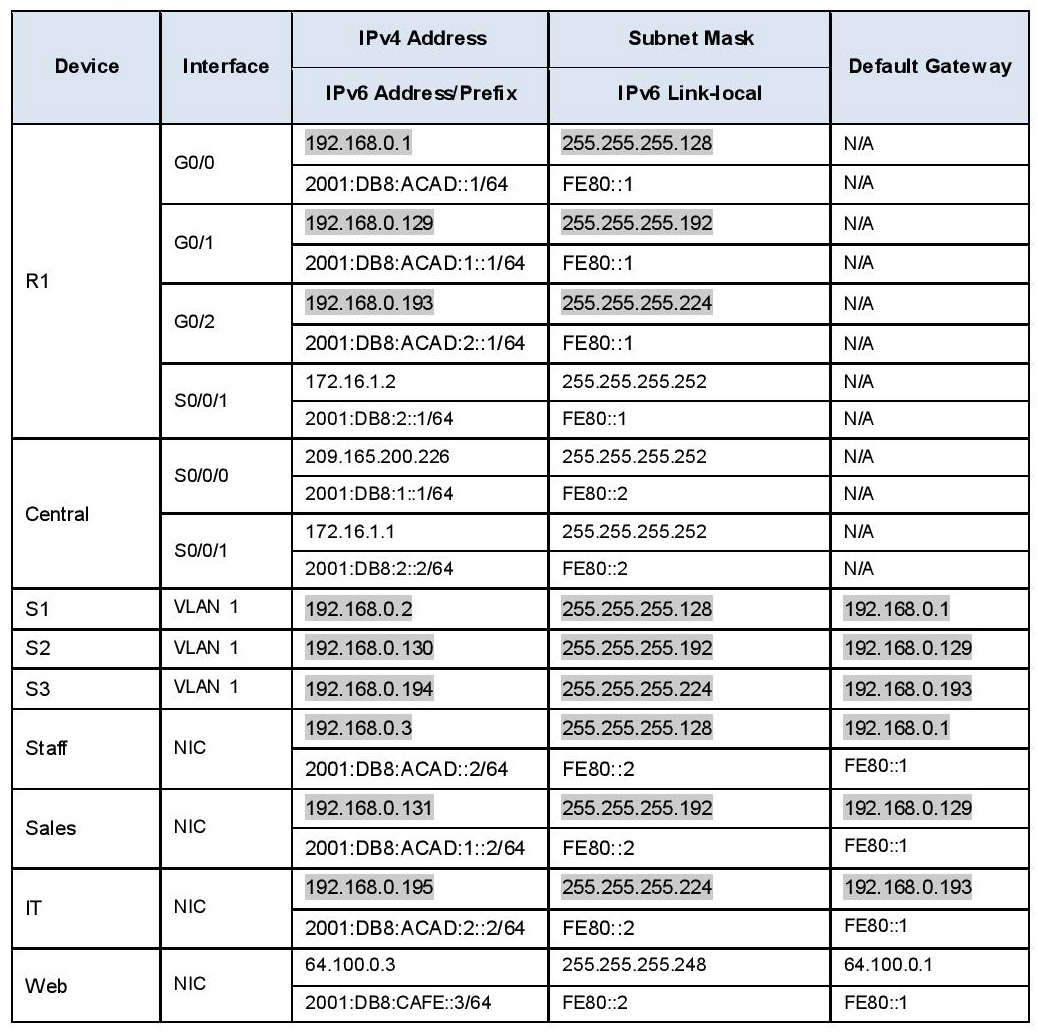
Addressing Table
Scenario / Background
The router Central, ISP cluster and the Web server are completely configured. You have been tasked with creating a new IPv4 addressing scheme that will accommodate 4 subnets using 192.168.0.0/24 network. The IT department requires 25 hosts. The Sales department needs 50 hosts. The subnet for the rest of the staff requires 100 hosts. A Guest subnet will be added in the future to accommodate 25 hosts. You are also tasked with finishing the basic security settings and interface configurations on R1. Furthermore, you will configure the SVI interface and basic security setting on switches S1, S2 and S3.
Requirements
IPv4 Addressing
Create subnets that meet the host requirements using 192.168.0.0/24.
- Staff: 100 hosts
- Sales: 50 hosts
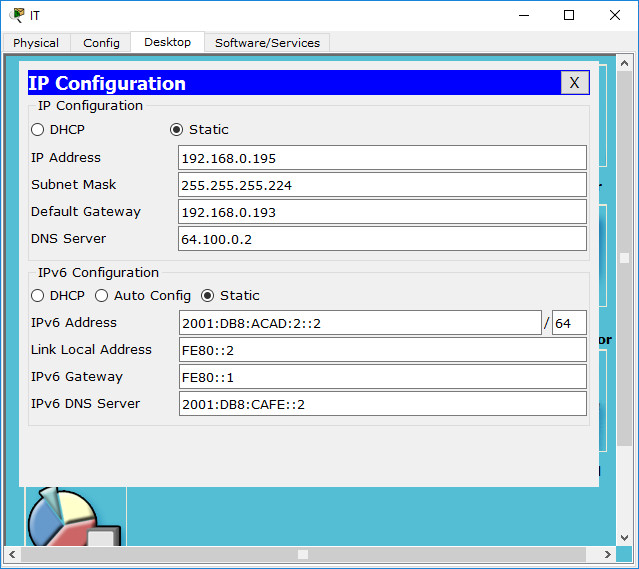
- IT: 25 hosts
- Guest network to be added later: 25 hosts
Document the assigned IPv4 addresses in the Addressing Table.
Record the subnet for Guest network: 192.168.0.224/27
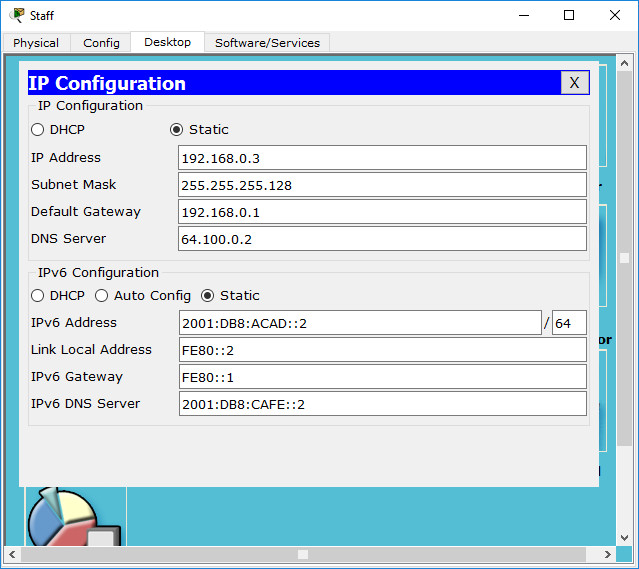
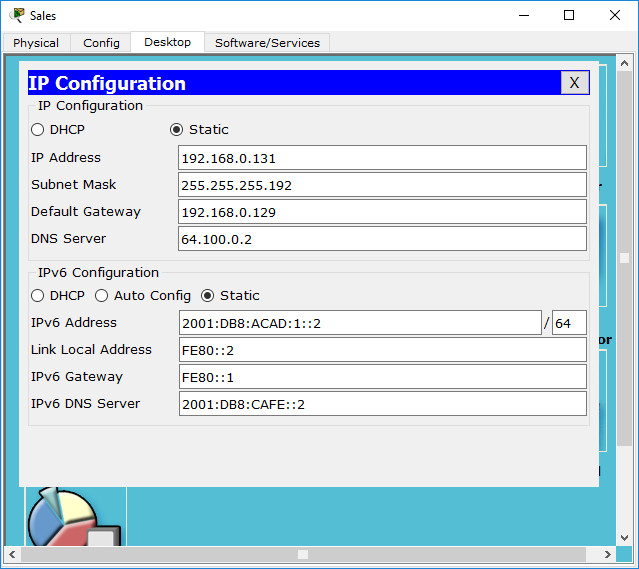
PC Configurations
· Configure the assigned IPv4 address, subnet mask, and default gateway settings on the Staff, Sales and IT PCs using your addressing scheme.
· Assign IPv6 unicast and link local addresses and default gateway to the Staff, Sales, and IT networks according to the Addressing Table.
Instructions:
R1 Configurations
– Configure the device name according to the Addressing Table.
– Disable DNS lookup.
– Assign Ciscoenpa55 as the encrypted privileged EXEC mode password.
– Assign Ciscoconpa55 as the console password and enable login.
– Require that a minimum of 10 characters be used for all passwords.
– Encrypt all plaintext passwords.
– Create a banner that warns anyone accessing the device that unauthorized access is prohibited. Make sure to include the word Warning in the banner.
– Configure all the Gigabit Ethernet interfaces.
- Configure the IPv4 addresses according to your addressing scheme.
- Configure the IPv6 addresses according to the Addressing Table.
– Configure SSH on R1:
- Set the domain name to CCNA-lab.com
- Generate a 1024-bit RSA key.
- Configure the VTY lines for SSH access.
- Use the local user profiles for authentication.
- Create a user Admin1 with a privilege level of 15 using the encrypted password for Admin1pa55.
– Configure the console and VTY lines to log out after five minutes of inactivity.
– Block anyone for three minutes who fails to log in after four attempts within a two-minute period.
Instructions:
Router>enable Router#conf terminal Router(config)#hostname R1 R1(config)#no ip domain-lookup R1(config)#enable secret Ciscoenpa55 R1(config)#line con 0 R1(config-line)#exec-timeout 5 0 R1(config-line)#password Ciscoconpa55 R1(config-line)#login R1(config-line)#security passwords min-length 10 R1(config)#service password-encryption R1(config)#banner motd #Warning: Unauthorized Access Prohibited!# R1(config)#interface GigabitEthernet0/0 R1(config-if)#ip address 192.168.0.1 255.255.255.128 R1(config-if)#ipv6 address FE80::1 link-local R1(config-if)#ipv6 address 2001:DB8:ACAD::1/64 R1(config-if)#no shutdown R1(config-if)#interface GigabitEthernet0/1 R1(config-if)#ip address 192.168.0.129 255.255.255.192 R1(config-if)#ipv6 address FE80::1 link-local R1(config-if)#ipv6 address 2001:DB8:ACAD:1::1/64 R1(config-if)#no shutdown R1(config-if)#interface GigabitEthernet0/2 R1(config-if)#ip address 192.168.0.193 255.255.255.224 R1(config-if)#ipv6 address FE80::1 link-local R1(config-if)#ipv6 address 2001:DB8:ACAD:2::1/64 R1(config-if)#no shutdown R1(config-if)#ip domain-name CCNA-lab.com R1(config)#crypto key generate rsa How many bits in the modulus [512]: 1024 R1(config)#line vty 0 4 R1(config-line)#transport input ssh R1(config-line)#exec-timeout 5 0 R1(config-line)#login local R1(config-line)#username Admin1 secret Admin1pa55 R1(config-line)#login block-for 180 attempts 4 within 120
Switch Configurations
· Configure the device name according to the Addressing Table.
· Configure the SVI interface with the IPv4 address and subnet mask according your addressing scheme.
· Configure the default gateway.
· Disable DNS lookup.
· Assign Ciscoenpa55 as the encrypted privileged EXEC mode password.
· Assign Ciscoconpa55 as the console password and enable login.
· Configure the console and VTY lines to log out after five minutes of inactivity.
· Encrypt all plaintext passwords.
Instructions:
Verify Connectivity
· Using the web browser from Staff, Sales, and IT PCs, navigate to www.cisco.pka.
· Using the web browser from Staff, Sales, and IT PCs, navigate to www.cisco6.pka.
· All PCs should be able to ping all the devices.

What is the password in CLI of s1,s2,s3
Ciscoconpa55
Ciscoenpa55
when accessing again after being given a password….what should be filled in part S1
tanku