Time limit: 0
Quiz-summary
0 of 52 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
Information
Good luck for you!
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 52 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- Answered
- Review
-
Question 1 of 52
1. Question
1 pointsA host is accessing a Web server on a remote network. Which three functions are performed by intermediary network devices during this conversation? (Choose three.)Correct
Incorrect
-
Question 2 of 52
2. Question
1 pointsFor which three reasons was a packet-switched connectionless data communications technology used when developing the Internet? (Choose three.)Correct
Incorrect
-
Question 3 of 52
3. Question
1 pointsA medium-sized business is researching available options for connecting to the Internet. The company is looking for a high speed option with dedicated, symmetric access. Which connection type should the company choose?Correct
Incorrect
-
Question 4 of 52
4. Question
1 pointsWhat is an ISP?Correct
Incorrect
-
Question 5 of 52
5. Question
1 pointsAn administrator needs to upgrade the IOS in a router to a version that supports new features. Which factor should the administrator consider before performing the upgrade?Correct
Incorrect
-
Question 6 of 52
6. Question
1 pointsRefer to the exhibit. A network engineer is attempting to connect to a new router to perform the initial configuration. The engineer connects a rollover cable from the serial port of a PC to the Aux port on the router, then configures HyperTerminal as shown. The engineer cannot get a login prompt in HyperTerminal. What would fix the problem? Correct
Correct
Incorrect
-
Question 7 of 52
7. Question
1 pointsWhich connection provides a secure CLI session with encryption to a Cisco router?Correct
Incorrect
-
Question 8 of 52
8. Question
1 pointsRefer to the exhibit. An administrator is trying to view the current configuration on this switch but receives the error message that is displayed. What does this error indicate? Correct
Correct
Incorrect
-
Question 9 of 52
9. Question
1 pointsRefer to the exhibit. From global configuration mode, an administrator is attempting to create a message-of-the-day banner by using the command banner motd V Authorized access only! Violators will be prosecuted! V When users log in using Telnet, the banner does not appear correctly. What is the problem?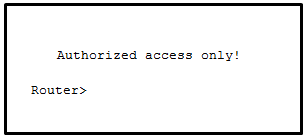 Correct
Correct
Incorrect
-
Question 10 of 52
10. Question
1 pointsA network administrator enters the service password-encryption command into the configuration mode of a router. What does this command accomplish?Correct
Incorrect
-
Question 11 of 52
11. Question
1 pointsRefer to the exhibit. A network administrator is configuring access control to switch SW1. If the administrator uses a console connection to connect to the switch, which password is needed to access user EXEC mode? Correct
Correct
Incorrect
-
Question 12 of 52
12. Question
1 pointsWhat will happen if the default gateway address is incorrectly configured on a host?Correct
Incorrect
-
Question 13 of 52
13. Question
1 pointsA network administrator is designing a new network infrastructure that includes both wired and wireless connectivity. Under which situation would a wireless connection be recommended?Correct
Incorrect
-
Question 14 of 52
14. Question
1 pointsA network administrator is troubleshooting connectivity issues on a server. Using a tester, the administrator notices that the signals generated by the server NIC are distorted and not usable. In which layer of the OSI model is the error categorized?Correct
Incorrect
-
Question 15 of 52
15. Question
1 pointsWhy are the paired wires twisted in a CAT5 cable?Correct
Incorrect
-
Question 16 of 52
16. Question
1 pointsWhat makes fiber preferable to copper cabling for interconnecting buildings? (Choose three.)Correct
Incorrect
-
Question 17 of 52
17. Question
1 pointsRefer to the exhibit. Which layer of the OSI model would format data in this way?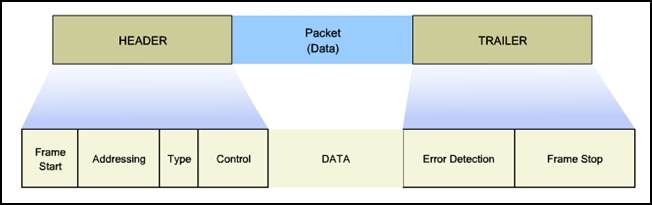 Correct
Correct
Incorrect
-
Question 18 of 52
18. Question
1 pointsOn a point-to-point network, which communication type is used when two devices can both transmit and receive but not at the same time?Correct
Incorrect
-
Question 19 of 52
19. Question
1 pointsWhat three statements describe features or functions of media access control? (Choose three.)Correct
Incorrect
-
Question 20 of 52
20. Question
1 pointsA frame is transmitted from one networking device to another. Why does the receiving device check the FCS field in the frame?Correct
Incorrect
-
Question 21 of 52
21. Question
1 pointsThe ARP table in a switch maps which two types of address together?Correct
Incorrect
-
Question 22 of 52
22. Question
1 pointsWhat are two actions performed by a Cisco switch? (Choose two.)Correct
Incorrect
-
Question 23 of 52
23. Question
1 pointsWhich two functions are primary functions of a router? (Choose two.)Correct
Incorrect
-
Question 24 of 52
24. Question
1 pointsA router boots and enters setup mode. What is the reason for this?Correct
Incorrect
-
Question 25 of 52
25. Question
1 pointsUsing default settings, what is the next step in the router boot sequence after the IOS loads from flash?Correct
Incorrect
-
Question 26 of 52
26. Question
1 pointsWhat are two ways that TCP uses the sequence numbers in a segment? (Choose two.)Correct
Incorrect
-
Question 27 of 52
27. Question
1 pointsA high school in New York (school A) is using videoconferencing technology to establish student interactions with another high school (school B) in Russia. The videoconferencing is conducted between two end devices through the Internet. The network administrator of school A configures the end device with the IP address 192.168.25.10. The administrator sends a request for the IP address for the end device in school B and the response is 192.168.25.10. The administrator knows immediately that this IP will not work. Why?Correct
Incorrect
-
Question 28 of 52
28. Question
1 pointsWhich service will translate private internal IP addresses into Internet routable public IP addresses?Correct
Incorrect
-
Question 29 of 52
29. Question
1 pointsWhich IPv6 address notation is valid?Correct
Incorrect
-
Question 30 of 52
30. Question
1 pointsWhich range of link-local addresses can be assigned to an IPv6-enabled interface??Correct
Incorrect
-
Question 31 of 52
31. Question
1 pointsWhat are the three parts of an IPv6 global unicast address? (Choose three.)Correct
Incorrect
-
Question 32 of 52
32. Question
1 pointsWhat is the purpose of ICMP messages?Correct
Incorrect
-
Question 33 of 52
33. Question
1 pointsWhich statement describes a characteristic of the traceroute utility?Correct
Incorrect
-
Question 34 of 52
34. Question
1 pointsRefer to the exhibit. Using VLSM, what is the largest and smallest subnet mask required on this network in order to minimize address waste? Correct
Correct
Incorrect
-
Question 35 of 52
35. Question
1 pointsA network administrator has been issued a network address of 192.31.7.64/26. How many subnets of equal size could be created from the assigned /26 network by using a /28 prefix?Correct
Incorrect
-
Question 36 of 52
36. Question
1 pointsA small satellite office has been given the overall network number of 192.168.99.0/24 and the network technician can subdivide the network addresses as needed. The office needs network access for both wired and wireless devices. However, because of the security consideration, these two networks should be separate. The wired network will have 20 devices. The wireless network has a potential connection of 45 devices. Which addressing scheme would be most efficient for these two networks?Correct
Incorrect
-
Question 37 of 52
37. Question
1 pointsThe administrator of a branch office receives an IPv6 prefix of 2001:db8:3000::/52 from the corporate network manager. How many subnets can the administrator create?Correct
Incorrect
-
Question 38 of 52
38. Question
1 pointsA user is attempting to do an http://www.cisco.com/ without success. Which two configuration values must be set on the host to allow this access? (Choose two.)Correct
Incorrect
-
Question 39 of 52
39. Question
1 pointsWhich devices should be secured to mitigate against MAC address spoofing attacks?Correct
Incorrect
-
Question 40 of 52
40. Question
1 pointsWhich router configuration mode would an administrator use to configure the router for SSH or Telnet login access?Correct
Incorrect
-
Question 41 of 52
41. Question
1 pointsRefer to the exhibit. An administrator is testing connectivity to a remote device with the IP address 10.1.1.1. What does the output of this command indicate?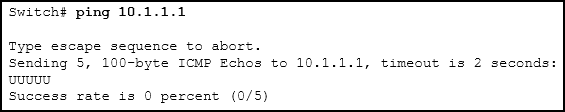 Correct
Correct
Incorrect
-
Question 42 of 52
42. Question
1 pointsWhich is a function of the show ip route command when used as a tool for troubleshooting network connectivity?Correct
Incorrect
-
Question 43 of 52
43. Question
1 pointsA user calls the help desk to report that a Windows XP workstation is unable to connect to the network after startup and that a popup window says “This connection has limited or no connectivity.” The technician asks the user to issue the ipconfig /all command. The user reports the IP address is 169.254.69.196 with subnet mask of 255.255.0.0 and nothing is displayed for the DNS server IP address. What is the cause of the problem?Correct
Incorrect
-
Question 44 of 52
44. Question
1 pointsA particular email site does not appear to be responding on a Windows 7 computer. What command could the technician use to show any cached DNS entries for this web page?Correct
Incorrect
-
Question 45 of 52
45. Question
1 pointsTo revert to a previous configuration, an administrator issues the command copy tftp startup-config on a router and enters the host address and file name when prompted. After the command is completed, why does the current configuration remain unchanged?Correct
Incorrect
-
Question 46 of 52
46. Question
1 pointsRefer to the graphic. What is the effect of setting the security mode to WEP on the Linksys integrated router? Correct
Correct
Incorrect
-
Question 47 of 52
47. Question
1 pointsWhich type of wireless security is easily compromised?Correct
Incorrect
-
Question 48 of 52
48. Question
1 pointsRefer to the exhibit. Which two settings could be changed to improve security on the wireless network? (Choose two.)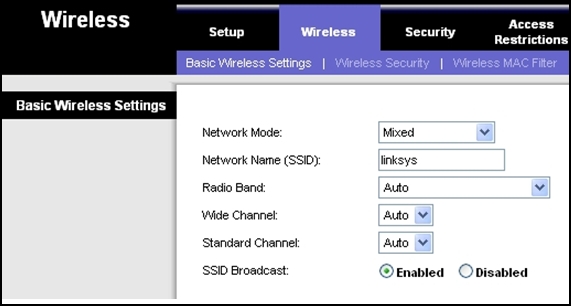 Correct
Correct
Incorrect
-
Question 49 of 52
49. Question
1 pointsOpen the PT Activity. Perform the tasks in the activity instructions and then answer the question. What is the secret keyword that is displayed on the web page?Correct
Incorrect
-
Question 50 of 52
50. Question
1 pointsFill in the blank. Do not abbreviate. Use lower case.- Which interface configuration mode command puts a Layer 3 switch interface into Layer 3 mode? (no switchport)
Correct
Incorrect
-
Question 51 of 52
51. Question
1 pointsFill in the blank.- A nibble consists of (4) bits.
Correct
Incorrect
-
Question 52 of 52
52. Question
1 pointsOpen the PT activity. Perform the tasks in the activity instructions and then fill in the blank.- The Server0 message is (winner) .?
Correct
Incorrect
