Check answers here:
Chapters 18 – 20: VPNs Exam Answers
Quiz-summary
0 of 31 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
Information
CCNP ENARSI v8 Chapters 18 – 20: VPNs Test Online
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 31 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- Answered
- Review
-
Question 1 of 31
1. Question
1 pointsAn network administrator has created VRF instances on a router and assigned interfaces to the VRF instances. What command can the administrator issue to verify what IP address is assigned to the interface, what VRF instance the interface is in, and whether the interface is up or down?Correct
Incorrect
Hint
Theshow ip vrf interfacescommand will show each interface that is assigned to a VRF as well as the IP address assigned to the interface, and whether the interface is up. -
Question 2 of 31
2. Question
1 pointsWhen connectivity over a VRF instance is being verified, what information must be specified as part of the ping command?Correct
Incorrect
Hint
When the ping command is issued, the VRF instance must be specified, otherwise the global routing table is used and the ping will fail. -
Question 3 of 31
3. Question
1 pointsWhich two components used in MPLS operation are associated with the router data plane? (Choose two.)Correct
Incorrect
Hint
The data plane of a LSR consists of an IP forwarding table (FIB) and a label forwarding table (LFIB). The FIB makes forwarding decisions for unlabeled packets. The LFIB makes forwarding decision for labeled packets. -
Question 4 of 31
4. Question
1 pointsIn an MPLS Layer 3 VPN network, which router is responsible for adding both the VPN and the LDP labels to packets?Correct
Incorrect
Hint
When an IP packet arrives at the ingress PE router, it attaches both the VPN and the LDP label. -
Question 5 of 31
5. Question
1 pointsWhich database on an LSR is used to make forwarding decisions on labeled packets?Correct
Incorrect
Hint
The data plane of a LSR consists of a IP forwarding table (FIB) and a label forwarding table (LFIB). The FIB makes forwarding decisions for unlabeled packets. The LFIB makes forwarding decision for labeled packets. -
Question 6 of 31
6. Question
1 pointsRefer to the exhibit. Which router will perform penultimate hop popping on packets destined for the 10.0.2.0/24 network?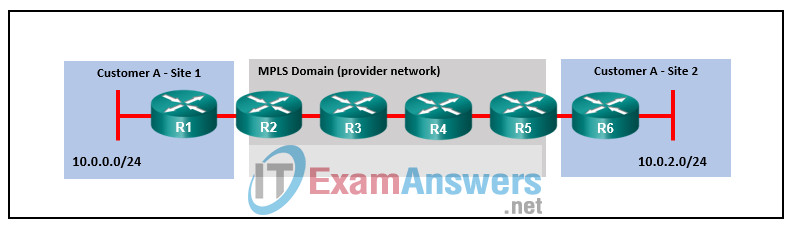 Correct
Correct
Incorrect
Hint
With penultimate hop popping, the last provider (P) router, which is router R4 in this example, removes (pops) the label off packets before they reach the provider edge (PE) router, R5. -
Question 7 of 31
7. Question
1 pointsWhat is a characteristic of CE routers in an MPLS Layer 3 VPN environment?Correct
Incorrect
Hint
CE, or customer edge, routers do not run MPLS. They also are unaware of labels and VRF instances. CE routers are connected to the provider edge (PE) routers of the MPLS service provider. -
Question 8 of 31
8. Question
1 pointsRefer to the exhibit. Which two routers would be participating in MP-BGP? (Choose two.)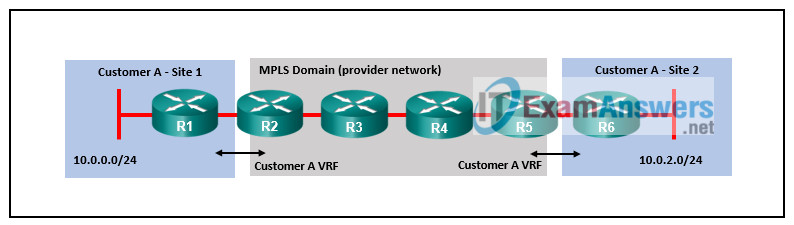 Correct
Correct
Incorrect
Hint
The PE routers, R2 and R5, learn routes from the CE routers, R1 and R6, and redistribute the routes into MP-BGP so they can be exchanged with other PE routers. The P routers, R3 and R4, and the customer (CE) routers do not participate in MP-BGP. -
Question 9 of 31
9. Question
1 pointsWhat addressing method is used by MPLS-enabled routers to forward packets through the MPLS domain?Correct
Incorrect
Hint
Provider MPLS-enabled routers use labels attached to IP packets to forward traffic through the MPLS domain. -
Question 10 of 31
10. Question
1 pointsRefer to the exhibit. Which two routers are considered P routers? (Choose two.)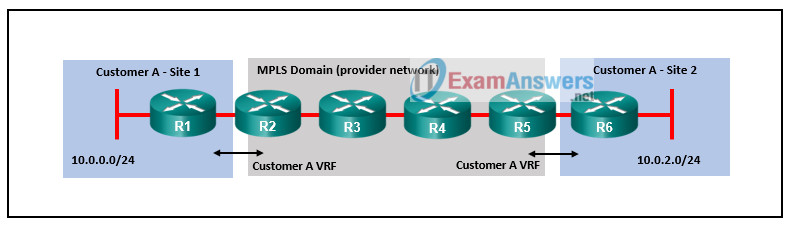 Correct
Correct
Incorrect
Hint
The PE routers, R2 and R5, learn routes from the CE routers. The PE routers label packets from the CE routers and forward the labeled packets to the P routers, R4 and R5. -
Question 11 of 31
11. Question
1 pointsMatch the DMVPN tunnel state with the description. (Not all options are used.)Correct
Incorrect
-
Question 12 of 31
12. Question
1 pointsRefer to the exhibit. Which DMVPN phase or phases will support a DMVPN tunnel between R5 and R6?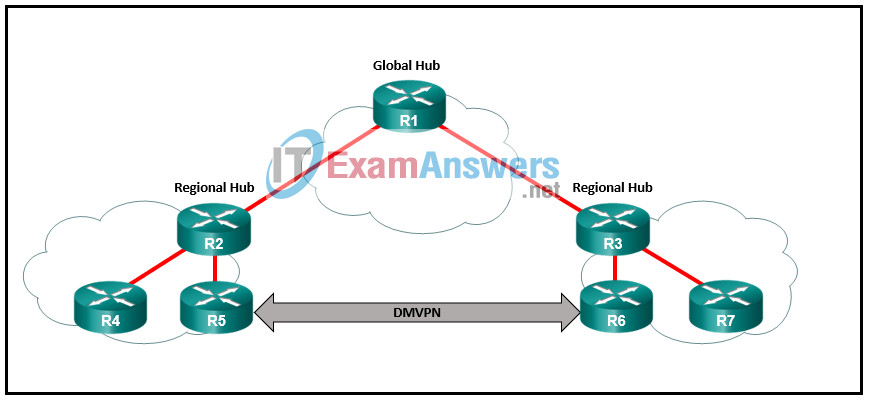 Correct
Correct
Incorrect
Hint
There are three DMVPN phase models: Phase 1, Phase 2, and Phase 3. The first DMVPN implementation is Phase 1. Phase 1 supports only spoke-to-hub tunnels. Traffic between spokes must traverse the hub. Phases 2 and 3 support not only spoke-to-hub tunnels, but also direct spoke-to-spoke tunnels. Only Phase 2 supports spoke-to-spoke communication between DMVPN networks or regions. -
Question 13 of 31
13. Question
1 pointsAfter how many NHRP registration request re-transmissions is a next-hop server (NHS) declared “down” if a spoke has not received an NHRP registration reply?Correct
Incorrect
Hint
NHRP registration requests are sent by the spoke every NHRP timeout period. If an NHRP registration reply is not received, the spoke will make three additional attempts. If after the third additional attempt a reply is not received, the NHS is declared “down”. -
Question 14 of 31
14. Question
1 pointsWhen implementing IPv6 DMVPN with IPv6 as the tunneling protocol, what IPv6 address type must be assigned to the tunnel interface?Correct
Incorrect
Hint
Because IPv6 routing protocols use IPv6 link-local addresses for neighbor discovery, IPv6 DMVPN configuration must assign IPv6 link-local addresses on the tunnel interfaces. -
Question 15 of 31
15. Question
1 pointsWhich additional command, beyond DVMPN Phase 1 configuration, is added to spoke routers for Phase 3 DMVPN (Multipoint)?Correct
Incorrect
Hint
The Phase 3 DMVPN configuration for spoke routers uses the ip nhrp shortcut command on the tunnel interface. -
Question 16 of 31
16. Question
1 pointsWhich capability is supported by all three DMVPN phase models?Correct
Incorrect
Hint
There are three DMVPN phase models: Phase 1, Phase 2, and Phase 3. The first DMVPN implementation is Phase 1. Phase 1 only supports spoke-to-hub tunnels. Traffic between spokes must traverse the hub. Phases 2 and 3 support not only spoke-to-hub tunnels, but also direct spoke-to-spoke tunnels. -
Question 17 of 31
17. Question
1 pointsMatch the NHRP message type with the description.Correct
Incorrect
Hint
- resolution – locates and provides address information of remote spoke
- redirect – informs router of more optimal path to a destination
- registration – informs hubs of spoke NBMA information
- purge – removes cached NHRP entries
-
Question 18 of 31
18. Question
1 pointsWhich solution would prevent the problem of recursive routing over DMVPN tunnels?Correct
Incorrect
Hint
A front door VRF instance occurs when the VRF instance is associated with the DMVPN transport network. It allows the interface associated with the transport network to be associated with a transport VRF that is a different VRF instance from the DMVPN tunnel. -
Question 19 of 31
19. Question
1 pointsRefer to the exhibit. A network administrator has configured a GRE tunnel between routers CE1 and CE2 to connect two corporate sites across the provider network. From the perspective of router CE1, how many hops away is network 10.0.0.0/24?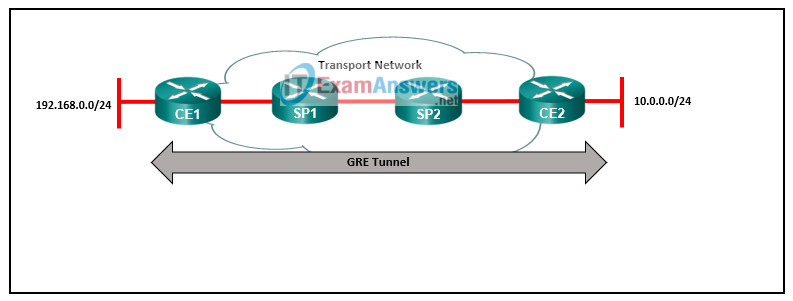 Correct
Correct
Incorrect
Hint
The GRE tunnel creates an overlay network through the provider network. The provider routers, SP1 and SP2, do not participate in the routing protocol connecting the two GRE edge routers CE1 and CE2. From the perspective of router CE1, the 10.0.0.0/24 network is only 1 hop away. -
Question 20 of 31
20. Question
1 pointsWhat is the default NHRP cache holdtime period?Correct
Incorrect
Hint
NHRP entries in the NHRP cache stay valid for 7200 seconds (2 hours) by default. This hold time can be modified using the ip nhrp holdtime command. It is recommended that the hold time for valid entries be modified to 600 seconds. -
Question 21 of 31
21. Question
1 pointsWhich component is an element of secure data transport that is concerned with ensuring data is viewable to only authorized users?Correct
Incorrect
Hint
The three elements of data security are as follows:- Confidentiality, which ensures data is viewable to only authorized users
- Integrity, which ensures data can only be modified by authorized users and has not been changed
- Availability, which ensures that the network is always available allowing the secure transport of the data
-
Question 22 of 31
22. Question
1 pointsWhat element of security is ensured by data confidentiality?Correct
Incorrect
Hint
The three elements of data security are as follows:- Confidentiality, which ensures data is viewable to only authorized users
- Integrity, which ensures data can only be modified by authorized users and has not been changed
- Availability, which ensures that the network is always available allowing the secure transport of the data
-
Question 23 of 31
23. Question
1 pointsWhich security mechanism is used to ensure data integrity?Correct
Incorrect
Hint
Hashing algorithms ensure data integrity by using a checksum to compare the transported data with the original data. -
Question 24 of 31
24. Question
1 pointsWhat protection is provided by IPsec perfect forward secrecy?Correct
Incorrect
Hint
With perfect forward secrecy each session key is derived independently of the previous key so that a compromise of one key does not mean compromise of future keys. -
Question 25 of 31
25. Question
1 pointsWhat is a characteristic of the IPsec Encapsulation Security Payload protocol?Correct
Incorrect
Hint
IPsec uses two protocols to provide data integrity and confidentiality, the IP Authentication Header (AH) and the Encapsulating Security Payload (ESP). AH, which uses IP protocol number 51, provides integrity and authentication but does not provide encryption. ESP provides data confidentiality, integrity, and authentication. ESP ensures confidentiality by encrypting the payload and adding a new set of headers during transport across a public network. -
Question 26 of 31
26. Question
1 pointsWhat are two characteristics of IPsec ESP tunnel mode? (Choose two.)Correct
Incorrect
Hint
There are two modes of ESP operation, tunnel mode and transport mode. In ESP tunnel mode the entire original packet is encrypted and a new IPsec header is added which is used to route the packet. -
Question 27 of 31
27. Question
1 pointsWhat is a characteristic of the DMVPN IPsec tunnel mode?Correct
Incorrect
Hint
There are two modes of DMVPN IPsec operation, tunnel mode and transport mode. In ESP tunnel mode the entire original packet and the GRE IP header are encrypted and a new IPsec IP header is added which is used to route the packet. -
Question 28 of 31
28. Question
1 pointsWhat algorithm is used with IPsec to provide data confidentiality?Correct
Incorrect
Hint
The IPsec framework uses various protocols and algorithms to provide data confidentiality, data integrity, authentication, and secure key exchange. Two popular algorithms that are used to ensure that data is not intercepted and modified (data integrity) are MD5 and SHA. AES is an encryption protocol and provides data confidentiality. DH (Diffie-Hellman) is an algorithm that is used for key exchange. RSA is an algorithm that is used for authentication. -
Question 29 of 31
29. Question
1 pointsWhat can be configured with DMVPN tunnels to provide confidentiality and integrity to data transported over the Internet?Correct
Incorrect
Hint
Data confidentiality and integrity can be accomplished by adding IPsec encryption to DMVPN tunnels that use the Internet as a transport. -
Question 30 of 31
30. Question
1 pointsWhich algorithm is used to support ESP encryption?Correct
Incorrect
Hint
The Advanced Encryption Standard (AES) and the Galois Counter Mode (GCM) encryption algorithms are used to provide encryption for IPsec ESP. -
Question 31 of 31
31. Question
1 pointsWhat two protocols provide data authentication and integrity for IPsec? (Choose two.)Correct
Incorrect
Hint
IPsec uses two protocols to provide data integrity and confidentiality, the IP Authentication Header (AH) and the Encapsulating Security Payload (ESP). AH provides integrity and authentication but does not provide encryption. AH can ensure that the original data packet has not been modified during transport but it does not encrypt data to ensure it is viewable only by authorized users. ESP provides confidentiality, integrity, and authentication.
