Check answers here:
Chapters 21 – 23: Infrastructure Security and Management Exam Answers
Quiz-summary
0 of 33 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
Information
CCNP ENARSI v8 Chapters 21 – 23: Infrastructure Security and Management Test Online
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 33 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- Answered
- Review
-
Question 1 of 33
1. Question
1 pointsWhich two characteristics are shared by both standard and extended ACLs? (Choose two.)Correct
Incorrect
Hint
Standard ACLs filter traffic based solely on a specified source IP address. Extended ACLs can filter by source or destination, protocol, or port. Both standard and extended ACLs contain an implicit deny as a final statement. Standard and extended ACLs can be identified by either names or numbers. -
Question 2 of 33
2. Question
1 pointsWhat method is used to apply an IPv6 ACL to a router interface?Correct
Incorrect
Hint
A network administrator will use the ipv6 traffic-filter command within interface configuration mode to apply an IPv6 ACL. -
Question 3 of 33
3. Question
1 pointsRefer to the exhibit. A network administrator created an IPv6 ACL to block the Telnet traffic from the 2001:DB8:CAFE:10::/64 network to the 2001:DB8:CAFE:30::/64 network. What is a command the administrator could use to allow only a single host 2001:DB8:CAFE:10::A/64 to telnet to the 2001:DB8:CAFE:30::/64 network?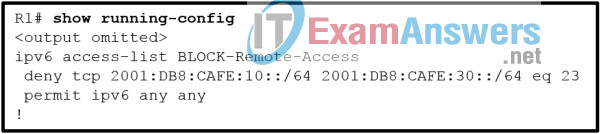 Correct
Correct
Incorrect
Hint
When an IPv6 ACE is created and is to be processed before an existing ACE is processed, the next command entered must use the sequence argument with a number lower than the existing ACE. This allows an entry to be placed before an existing entry, as the default sequence numbers are commonly numbered by increments of 10. Thus, using a sequence number of 5 on an ACE will place it in front of a prior existing entry with a sequence number of 10. -
Question 4 of 33
4. Question
1 pointsWhich two statements describe the effect of the access control list wildcard mask 0.0.0.15? (Choose two.)Correct
Incorrect
Hint
A wildcard mask uses 0s to indicate that bits must match. 0s in the first three octets represent 24 bits and four more zeros in the last octet, represent a total of 28 bits that must match. The four 1s represented by the decimal value of 15 represents the four bits to ignore. -
Question 5 of 33
5. Question
1 pointsA network administrator is configuring an IPv6 ACL to deny Telnet access from all staff in the branch office to a file server in home office. All branch office staff use addressing from the IPv6 subnet 2001:DB8:100:20::/64. The file server in home office uses the address 2001:DB8:100:50::15/64. Implementing the No-Telnet ACL on the LAN interface of the branch office router requires which three commands? (Choose three.)Correct
Incorrect
Hint
The ACL requires an ACE denying Telnet access from all users in the LAN to the file server at 2001:DB8:100:50::15/64. The IPv6 ACL also has an implicit deny, so a permit statement is required to allow all other traffic. With IPv6, the ipv6 traffic filter command is used to bind the ACL to the interface. -
Question 6 of 33
6. Question
1 pointsRefer to the exhibit. An administrator is configuring a prefix list to stop advertising 172.18.100.0/24, a secure Branch network, to the internet. After adding the prefix list, the administrator notices that the branch network is still being advertised. How can the administrator fix the error?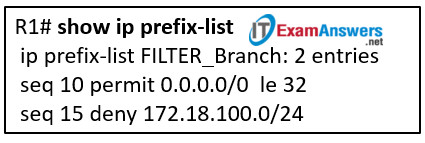 Correct
Correct
Incorrect
Hint
The order of the statements within the prefix list is wrong. Currently, all networks are permitted before the Branch network is denied. The administrator must modify the prefix list to add a sequence 5 with the deny statement to deny network 172.18.100.0/24 and remove the seq 15 statement. -
Question 7 of 33
7. Question
1 pointsRefer to the exhibit. A network administrator is configuring an ACL to limit the connection to R1 vty lines to only the IT group workstations in the network 192.168.22.0/28. The administrator verifies the successful Telnet connections from a workstation with IP 192.168.22.5 to R1 before the ACL is applied. However, after the ACL is applied to the interface Fa0/0, Telnet connections are denied. What is the cause of the connection failure?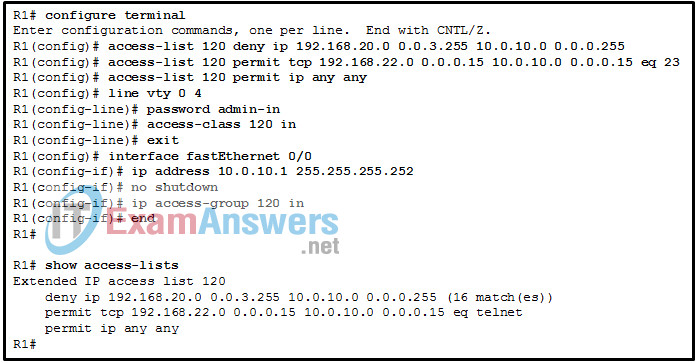 Correct
Correct
Incorrect
Hint
The source IP range in the deny ACE is 192.168.20.0 0.0.3.255, which covers IP addresses from 192.168.20.0 to 192.168.23.255. The IT group network 192.168.22.0/28 is included in the 192.168.20/22 network. Therefore, the connection is denied. To fix it, the order of the deny and permit ACE should be switched. -
Question 8 of 33
8. Question
1 pointsWhich two commands can be used to verify the content and placement of access control lists? (Choose two.)Correct
Incorrect
Hint
If troubleshooting or verifying an ACL, an administrator needs to view the access list statements and verify what interface and direction is being used. Two commands that accomplish this task are show access-lists and show running-config . -
Question 9 of 33
9. Question
1 pointsWhich prefix-list entry will be used when multiple entries in a prefix list match a given prefix?Correct
Incorrect
Hint
A prefix list is made up of various sequences; these sequences are processed sequentially from the top of the prefix list to the bottom of the prefix list, in order of sequence number. A prefix list begins looking for a match using the lowest sequence number first and the very first sequence that matches is the sequence that is used. -
Question 10 of 33
10. Question
1 pointsWhich feature is unique to IPv6 ACLs when compared to those of IPv4 ACLs?Correct
Incorrect
Hint
One of the major differences between IPv6 and IPv4 ACLs are two implicit permit statements at the end of any IPv6 ACL. These two permit statements allow neighbor discovery operations to function on the router interface. -
Question 11 of 33
11. Question
1 pointsRefer to the exhibit. The settings to connect to a RADIUS server were issued on router Rtr1. Which conclusion can be drawn if a problem occurs with AAA authentication between Rtr1 and Server1?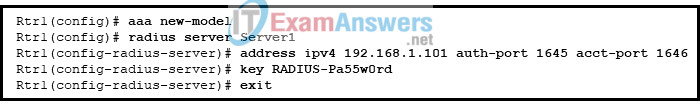 Correct
Correct
Incorrect
Hint
RADIUS uses ports 1812 or 1645 (Cisco default) for authentication and 1813 or 1646 (Cisco default) for accounting. Therefore, if the RADIUS server is using ports 1812 and 1813, these same port numbers have to be configured on the Cisco router. -
Question 12 of 33
12. Question
1 pointsWhich mitigation technique would prevent rogue servers from providing false IPv6 configuration parameters to clients?Correct
Incorrect
Hint
DHCPv6 Guard is a feature designed to ensure that rogue DHCPv6 servers are not able to hand out addresses to clients, redirect client traffic, or starve out the DHCPv6 server and cause a DoS attack. DHCPv6 Guard requires a policy to be configured in DHCP Guard configuration mode, and DHCPv6 Guard is enabled on an interface-by-interface basis. -
Question 13 of 33
13. Question
1 pointsWhich IPv6 First-Hop Security feature can block IPv6 traffic if this traffic is from an unknown origin?Correct
Incorrect
Hint
IPv6 Source Guard is a Layer 2 snooping interface feature for validating the source of IPv6 traffic. If the traffic arriving on an interface is from an unknown source, IPv6 Source Guard can block it. -
Question 14 of 33
14. Question
1 pointsRefer to the exhibit. Router R1 is configured as shown. An administrative user attempts to use Telnet from router R2 to R1 using the interface IP address 10.10.10.1. However, Telnet access is denied. Which conclusion can be drawn from this scenario?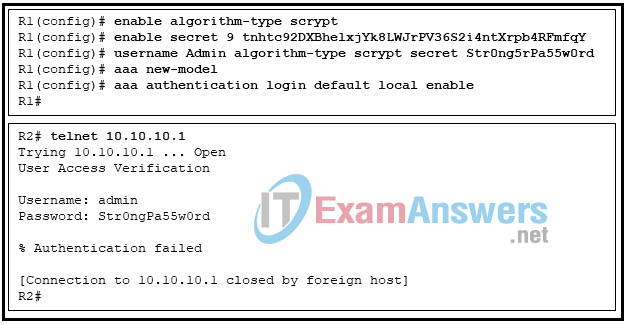 Correct
Correct
Incorrect
Hint
The AAA authentication is defined with the list default with two methods. The first method is to use the local database and the second method is to use the enable password. The local keyword indicates that the username and password are not case-sensitive, so the username can be typed as “admin”. The problem is that the password is “Str0ng5rPa55w0rd” and the user typed “Str0ngPa55w0rd”. -
Question 15 of 33
15. Question
1 pointsWhat happens when a packet does not match any of the defined class maps specified in a policy map?Correct
Incorrect
Hint
If a packet does not match any of the defined classes, it is subject to the conditions laid out in the default class. -
Question 16 of 33
16. Question
1 pointsRefer to the exhibit. Which piece of information can be obtained from the AAA configuration commands?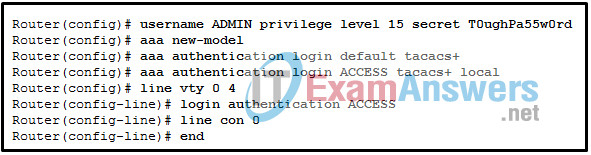 Correct
Correct
Incorrect
Hint
The login authentication ACCESS command under the line vty 0 4 command configures the AAA authentication for VTY lines access to use the method list named ACCESS. The aaa authentication login ACCESS tacacs+ local command configures the authentication method for ACCESS to use the AAA server with TACACS+ protocol. If the AAA server cannot be connected, then the local user database is used next. -
Question 17 of 33
17. Question
1 pointsA junior engineer is learning how to apply a service policy to a Cisco router control plane. Which piece of information should be considered to perform this configuration?Correct
Incorrect
Hint
Policy map names are case-sensitive. The service policy needs to be attached to the correct interface, the control plane interface. CoPP can be applied to packets entering or leaving the control plane interface. Not all Cisco IOS versions support output CoPP. -
Question 18 of 33
18. Question
1 pointsWhat is the recommended action when troubleshooting scenarios for CoPP, where specific source and destination IP addresses are used in the ACL?Correct
Incorrect
Hint
When troubleshooting ACLs for CoPP, one recommended action if specific source and destination IP addresses are used is changing the IP addresses in the ACL to any / any . If the match is successful, then there is an issue with the original IP addresses. If not, the IP addresses were likely not the problem. -
Question 19 of 33
19. Question
1 pointsWhich action is necessary to provide encrypted transfer of data between a RADIUS server and a AAA-enabled router?Correct
Incorrect
Hint
The key command configures the preshared key on a RADIUS server that is used for encryption. The keys must be identical on the router and on the RADIUS server. The creation of a VPN tunnel is unnecessary. The configuration of ports does not have any effect on encryption. -
Question 20 of 33
20. Question
1 pointsA teacher is explaining uRPF to network students in a classroom. Which two statements are accurate about uRPF operation on a Cisco router? (Choose two.)Correct
Incorrect
Hint
Unicast Reverse Path Forwarding (uRPF) helps limit or even eliminate spoofed IP packets on a network. This is accomplished by examining the source IP address of an ingress packet and determining whether the packet is valid. Cisco Express Forwarding must be enabled on the IOS device for uRPF to work. The feature uRPF can operate in three different modes: strict, loose, and VRF. With uRPF, any packets generated by the router and destined to the router are discarded by default. -
Question 21 of 33
21. Question
1 pointsA network administrator is configuring SSH on a router. When verifying the configuration, the administrator notices that the SSH connection requests fail, but the Telnet connection requests from the same workstation are successful. Which two parts of the router configuration should be checked to try to locate the problem? (Choose two.)Correct
Incorrect
Hint
There are several possible configuration issues to account for why SSH connections are failing. Among them are (1) the VTY lines should accept SSH connections by the transport input all or transport input ssh command; and (2) if there is an extended ACL to protect access to the vty lines, the port (either by the word ssh or the numeric number) should be included in the permit ACE. Because Telnet works, the connectivity to the vty line can be established, and thus the option that the standard ACL is blocking the workstation from access to the router does not apply. The option that the ip access-class command is missing does not apply because if the command is missing, no ACL will be applied to filter the access to vty lines. (Although the statement might be true in the router configuration, it is not a reason why SSH is not successful.) Finally the option that the password is misconfigured on the console line does not apply because SSH connects to vty lines, not to the console line. -
Question 22 of 33
22. Question
1 pointsA network technician is configuring SNMPv3 and has set a security level of auth . What is the effect of this setting?Correct
Incorrect
Hint
For enabling SNMPv3 one of three security levels can be configured:- noAuth
- auth
- priv
-
Question 23 of 33
23. Question
1 pointsRefer to the exhibit. A SNMP manager has IP address 172.16.1.120. The SNMP manager is unable to change configuration variables on the R1 SNMP agent. What could be the problem?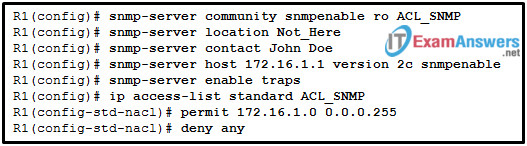 Correct
Correct
Incorrect
Hint
Because the SNMP manager is able to access the SNMP agent, the problem is not related to the ACL configuration. The SNMP agent configuration should have an access level configured of rw to support the SNMP manager set requests. The SNMP manager cannot change configuration variables on the SNMP agent R1 with only ro access. The IP address of the SNMP manager does not have to be 172.16.1.1 to make changes to the SNMP agent. The SNMP agent does not have to have traps disabled. -
Question 24 of 33
24. Question
1 pointsRefer to the exhibit. Which SNMP authentication password must be used by the member of the ADMIN group that is configured on router R1?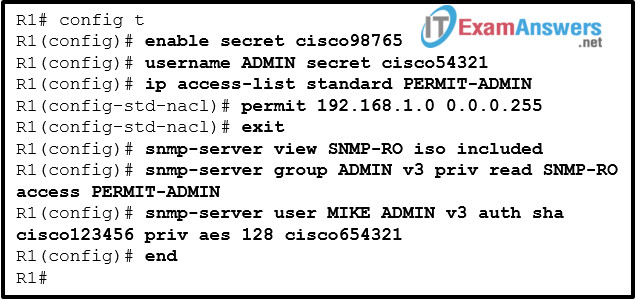 Correct
Correct
Incorrect
Hint
The syntax for the configuration of a SNMPv3 user with a corresponding authentication and encryption password is: Router(config)# snmp-server user username group-name v3 auth {md5 | sha} auth-password priv {des | 3des | aes {128 | 192 | 256}} privpassword -
Question 25 of 33
25. Question
1 pointsA computer technician is monitoring traffic on a network where users are complaining about slow network performance. The technician is curious as to whether the new network management software is causing the slowdown. Which two port numbers would the technician be looking for in the captured packets for SNMP traffic? (Choose two.)Correct
Incorrect
Hint
SNMP uses UDP ports 161 and 162. -
Question 26 of 33
26. Question
1 pointsWhich two types of probes can be configured to monitor traffic by IP SLA within a network environment? (Choose two.)Correct
Incorrect
Hint
IP SLA is a tool that allows for the continuous monitoring of various aspects of the network. Different types of probes can be configured to monitor traffic within a network environment:- Delay
- Jitter (directional)
- Packet loss (directional)
- Packet sequencing (packet ordering)
- Path (per hop)
- Connectivity (directional)
- Server or website download time
- Voice quality scores
-
Question 27 of 33
27. Question
1 pointsA network administrator has issued the snmp-server user admin1 admin v3 encrypted auth md5 abc789 priv des 256 key99 command. What are two features of this command? (Choose two.)Correct
Incorrect
Hint
The command snmp-server user admin1 admin v3 encrypted auth md5 abc789 priv des 256 key99 creates a new user and configures authentication with MD5. The command does not use a secret encrypted password on the server. The command snmp-server community string access-list-number-or-name restricts SNMP access to defined SNMP managers. -
Question 28 of 33
28. Question
1 pointsWhen configuring SSH on a router to implement secure network management, a network engineer has issued the login local and transport input ssh line vty commands. What three additional configuration actions have to be performed to complete the SSH configuration? (Choose three.)Correct
Incorrect
Hint
SSH is automatically enabled after the RSA keys are generated. Setting user privilege levels and configuring role-based CLI access are good security practices but are not a requirement of implementing SSH. -
Question 29 of 33
29. Question
1 pointsA technician configured a switch with console, enable secret, and VTY passwords. The service password-encryption command was then used to encrypt all unencrypted passwords. What happens if the technician issues the no service password-encryption command?Correct
Incorrect
Hint
After the service password-encryption command was issued, there is no way to present the passwords again in clear text. The no service password-encryption command stops any new passwords from being encrypted. -
Question 30 of 33
30. Question
1 pointsWhich statement correctly describes how an ACL can be used with the access-class command to filter vty access to a router?Correct
Incorrect
Hint
By design, the access-class command only matches the source IP address. Therefore, if an extended access list is used, the any parameter must be used as the destination IP address or the configuration will not work. -
Question 31 of 33
31. Question
1 pointsA network administrator is configuring a prefix list with the ip prefix-list command. Which entry is valid?Correct
Incorrect
Hint
Prefix lists are configured with the global configuration command ip prefix-list prefix-listname [ seq sequence-number ] { permit | deny } high-order-bit-pattern / high-order-bit-count [ ge ge-value ] [ le le-value ]. IOS and IOS XE require that the ge-value be greater than the high-order bit count and that the le-value be greater than or equal to the ge-value, that is, high-order-bit-count — ge-value — le-value . -
Question 32 of 33
32. Question
1 pointsA network administrator configures uRPF on a Cisco router interface with the ip verify unicast source reachable-via rx allow-default command to eliminate spoofed IP packets on a network. Which conclusion can be drawn from this configuration?Correct
Incorrect
Hint
The uRPF configuration is applied on an interface-by-interface basis with the ip verify unicast source reachable-via { rx | any } [ allow-default ] [ allow-self-ping ] [list ] command. For strict mode, the rx option should be used, and for loose mode the any option should be used. The allow-default option is used when the return path is associated with an interface that is chosen based on a default route. -
Question 33 of 33
33. Question
1 pointsRefer to the exhibit. The administrator configured the access to the console and the vty lines of a router. Which conclusion can be drawn from this configuration?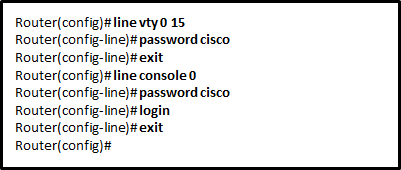 Correct
Correct
Incorrect
Hint
By default, the IOS includes the login command on the vty lines. This prevents Telnet access to the device without authentication. If, by mistake, the no login command is set, which removes the requirement for authentication, unauthorized persons could connect across the network to the line through Telnet. This would be a major security risk.
