Check answers here:
Chapters 22 – 24: Network Design and Monitoring Exam Answers
Quiz-summary
0 of 43 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
Information
CCNP ENCOR v8 Chapters 22 – 24: Network Design and Monitoring Test Online
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 43 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- Answered
- Review
-
Question 1 of 43
1. Question
1 pointsWhich network design solution will best extend access layer connectivity to host devices?Correct
Incorrect
Hint
EtherChannel allows more data to be moved at the access layer, but does not provide network expansion. Redundancy is used to provide failover solutions but does not focus on network expansion. Routing protocols are not used to provide network expansion at the access layer. Wireless connectivity provides network access to a large number of users at the access layer. -
Question 2 of 43
2. Question
1 pointsA network designer must provide a rationale to a customer for a design which will move an enterprise from a flat network topology to a hierarchical network topology. Which two features of the hierarchical design make it the better choice? (Choose two.)Correct
Incorrect
Hint
A hierarchical design for switches helps network administrators when planning and deploying a network expansion, performing fault isolation when a problem occurs, and providing resiliency when traffic levels are high. A good hierarchical design has redundancy when it can be afforded so that one switch does not cause all networks to be down. -
Question 3 of 43
3. Question
1 pointsWhat are three benefits of employing a hierarchical network design? (Choose three.)Correct
Incorrect
Hint
Hierarchical design provides fault containment by constraining the network changes to a subset of the network, which affects fewer systems and makes it easy to manage as well as improve resiliency. In a modular layer design, network components can be placed or taken out of service with little or no impact to the rest of the network and this facilitates troubleshooting, problem isolation, and network management. -
Question 4 of 43
4. Question
1 pointsAt the distribution layer of a hierarchical network, what are two advantages of using Layer 3 devices instead of Layer 2 switches? (Choose two.)Correct
Incorrect
Hint
Communication between endpoints on different access layer switches occurs through the distribution layer. The distribution layer provides a boundary between the Layer 2 domain of the access layer and the Layer 3 domain of the core. This boundary provides two key functions for the LAN. On the Layer 2 side, the distribution layer creates a boundary for Spanning Tree Protocol (STP), limiting propagation of Layer 2 faults. On the Layer 3 side, the distribution layer provides a logical point to summarize IP routing information when it enters the core layer. The summarization reduces IP route tables for easier troubleshooting and reduces protocol overhead for faster recovery from failures. -
Question 5 of 43
5. Question
1 pointsWhich three characteristics are typically associated with the core layer in the Cisco hierarchical network design model? (Choose three.)Correct
Incorrect
Hint
The core layer is the backbone and aggregation point for multiple networks and provides scalability, high availability, and fast convergence to the network. It can provide high-speed connectivity for large enterprises with multiple campus networks distributed worldwide and it can also provide interconnectivity between the end-user/endpoint campus access layer and other network blocks such as the data center, the private cloud, the public cloud, the WAN, Internet edge, and network services. Packet filtering is a function of the distribution layer. -
Question 6 of 43
6. Question
1 pointsRefer to the exhibit. Which switching technology would allow each access layer switch link to be aggregated to provide more bandwidth between each Layer 2 switch and the Layer 3 switch?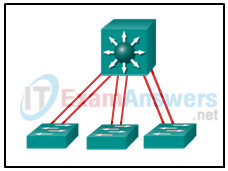 Correct
Correct
Incorrect
Hint
PortFast is used to reduce the amount of time that a port spends going through the spanning-tree algorithm, so that devices can start sending data sooner. Trunking can be implemented in conjunction with EtherChannel, but trunking alone does not aggregate switch links. HSRP is used to load-balance traffic across two different connections to Layer 3 devices for default gateway redundancy. HSRP does not aggregate links at either Layer 2 or Layer 3 as EtherChannel does. -
Question 7 of 43
7. Question
1 pointsRefer to the exhibit. Which type of Cisco hierarchical LAN design model is used at school site 1?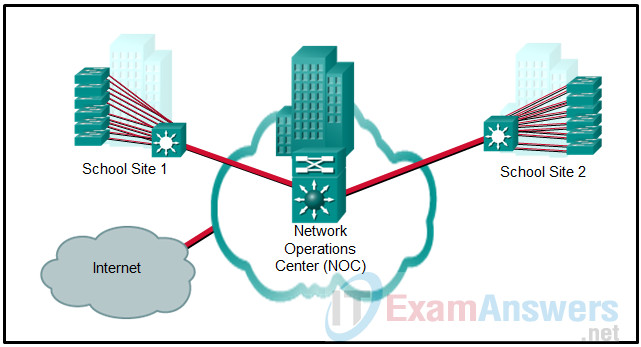 Correct
Correct
Incorrect
Hint
In the two-tier collapsed core model, the distribution layer and the core layer are combined into one. The switch that connects the site to the NOC is serving as both a distribution layer switch and a core layer switch. The NOC is designed with other network devices that are not shown, such as the firewall, as part of an Internet edge design. -
Question 8 of 43
8. Question
1 pointsA network engineer is attempting to explain StackWise technology to a client who wants to deploy a simplified campus design. Which explanation accurately describes this technology?Correct
Incorrect
Hint
The simplified campus design relies on switch clustering such as the Virtual Switching System (VSS) and stacking technologies such as Stackwise in which multiple physical switches act as a single logical switch. -
Question 9 of 43
9. Question
1 pointsOn a campus network, personnel who are located in a five site college have access to servers found in one location. In which network block of the campus network architecture would these servers be found?Correct
Incorrect
Hint
In this hierarchical model, the distribution/core layer provides connectivity to the WAN edge block, the Internet edge block, the network services block, and data center. The WAN edge block is used to connect to remote data centers, remote branches or other campus networks. The Internet edge block is used for regular Internet access, ecommerce, to connect to remote branches, and remote VPN access. The data center/server room block is where business critical servers are placed to serve up websites, corporate e-mail, business applications, storage, big data processing, and backup services. The network services edge is where devices providing network services reside such as the Wireless LAN Controllers (WLCs), Identity Services Engine (ISE), Telepresence Manager, and Cisco Unified Communications Manager (CUCM). -
Question 10 of 43
10. Question
1 pointsIn a new network design, an organization has decided to manage all of its wireless access points using a wireless network controller. In which network design block of the campus network architecture would the centralized wireless network controllers be found?Correct
Incorrect
Hint
In this hierarchical model, the distribution/core layer provides connectivity to the WAN edge block, the Internet edge block, the network services block, and data center. The WAN edge block is used to connect to remote data centers, remote branches or other campus networks. The internet edge block is used for regular Internet access, ecommerce, to connect to remote branches, and remote VPN access. The data center/server room block is where business critical servers are placed to serve up websites, corporate e-mail, business applications, storage, big data processing, and backup services. The network services edge is where devices providing network services reside such as the Wireless LAN Controllers (WLCs), Identity Services Engine (ISE), Telepresence Manager, and Cisco Unified Communications Manager (CUCM). -
Question 11 of 43
11. Question
1 pointsA network engineer has to decide between a Layer 2 Access Layer (STP-based) and a Layer 3 Access Layer (Routed access) campus design option. Which statement must be considered for a decision to be made?Correct
Incorrect
Hint
The Routed access design has a number of advantages over the STP-based design: No FHRP required – no need for FHRP protocols such as HSRP and VRRP. No STP required – since there are no L2 links to block, this design removes the need for STP. Easier troubleshooting – It offers common end-to-end troubleshooting tools (such as ping and traceroute). The Routed access is an excellent design for many environments, but it has the same limitation as the STP-based design, in which it does not support spanning VLANs across multiple access switches. Additionally, it might not be the most cost-effective solution because access layer switches with Layer 3 routing capability might cost more than Layer 2 switches do. -
Question 12 of 43
12. Question
1 pointsWhat is the description for a Syslog Level 3 event?Correct
Incorrect
Hint
Syslog messages include a severity level with a value between 0 and 7, with a lower number being more severe. Each level also has an associated keyword and description. -
Question 13 of 43
13. Question
1 pointsMatch the SD-Access fabric device role to the description. (Not all options are used.)Correct
Incorrect
-
Question 14 of 43
14. Question
1 pointsWhich protocol or service can be configured to send unsolicited messages to alert the network administrator about a network event such as an extremely high CPU utilization on a router?Correct
Incorrect
Hint
SNMP can be used to collect and store information such as device CPU utilization. Syslog is used to access and store system messages. Cisco developed NetFlow for the purpose of gathering statistics on packets that are flowing through Cisco routers and multilayer switches. NTP is used to allow network devices to synchronize time settings. -
Question 15 of 43
15. Question
1 pointsAn administrator issued the following commands on router R1:R1(config)# logging 192.168.10.2 R1(config)# logging trap 5
What conclusion can be drawn from this configuration?Correct
Incorrect
Hint
When these commands are issued, the only messages that appear on the syslog server are those with severity level of 5 or lower. The messages with severity level of 6 or higher appear on the router console output, but do not appear on the syslog server output because the logging trap command limits by severity level the syslog messages that are sent to the syslog server. -
Question 16 of 43
16. Question
1 pointsWhat is the description for a Syslog Level 1 event?Correct
Incorrect
Hint
Syslog messages include a severity level with a value between 0 and 7, with a lower number being more severe. Each level also has an associated keyword and description. -
Question 17 of 43
17. Question
1 pointsWhat is the purpose of ERSPAN?Correct
Incorrect
Hint
Encapsulated Remote Switched Port Analyzer (ERSPAN) is used to route monitored traffic from one network to another through Layer 3 routing instead of Layer 2 port mirroring as other SPAN technologies do. -
Question 18 of 43
18. Question
1 pointsWhat is a primary function of the Cisco IOS IP Service Level Agreements feature?Correct
Incorrect
Hint
The Cisco IOS IP Service Level Agreements (SLAs) feature is a useful tool to discover a network failure as early as possible. It uses generated traffic to measure network performance in real time. The results can help network administrators detect signs of network issues at an early stage. -
Question 19 of 43
19. Question
1 pointsWhat is a tool in the Cisco DNA Center that can apply machine learning in order to diagnose network issues and offer guided remediation steps to fix issues?Correct
Incorrect
Hint
DNA Assurance is part of the Cisco DNA Center. The Cisco DNA Center has the ability to apply machine learning to diagnose network issues and offer guided remediation steps used to fix an issue. The ASSURANCE page shows the overall health of the network including wired and wireless client data as well as access to dashboards, issues, and a way to drill down on single users and their problems. -
Question 20 of 43
20. Question
1 pointsWhat is the description for a Syslog Level 5 event?Correct
Incorrect
-
Question 21 of 43
21. Question
1 pointsWhat is the description for a Syslog Level 6 event?Correct
Incorrect
-
Question 22 of 43
22. Question
1 pointsWhich layer of the Cisco SD-Access Architecture contains the underlay and the overlay networks?Correct
Incorrect
Hint
The network layer of the Cisco SD-Access Architecture contains the underlay and the overlay network which together deliver data packets to and from the network devices participating in SD-Access. -
Question 23 of 43
23. Question
1 pointsWhich two statements describe the SD-Access overlay network? (Choose two.)Correct
Incorrect
Hint
The SD-Access overlay network, also known as the SD-Access fabric, is a virtual network that interconnects all of the network devices to form a fabric of interconnected nodes. The overlay network includes three planes of operation: the control plane, the data plane, and the policy plane. -
Question 24 of 43
24. Question
1 pointsWhat is the role of the fabric edge node in the SD-Access fabric overlay?Correct
Incorrect
Hint
There are five basic device roles in the SDA fabric overlay. The role of the fabric edge node is to connect wired endpoints to the SDA fabric. -
Question 25 of 43
25. Question
1 pointsMatch the layer of the Cisco SD-Access Architecture with the description.Correct
Incorrect
Hint
- abstracts all the complexities and dependencies of the other layers
- includes all devices that actively participate in the SD-Access fabric
- contains the NCP, NDP and ISE subsystems
- consists of the SD-Access fabric and underlay network
-
Question 26 of 43
26. Question
1 pointsWhich IGP is used in the automated underlay model of the Cisco SD-Access architecture?Correct
Incorrect
Hint
In an automated underlay model, the Cisco DNA Center LAN automation feature creates a Layer 3 routed access campus design through the use of IS-IS. -
Question 27 of 43
27. Question
1 pointsWhich tunneling technology is used by the SD-Access fabric data plane to create the overlay network for the SD-Access fabric?Correct
Incorrect
Hint
The overlay network is built by the SD-Access fabric data plane over an underlay network by using VXLAN tunneling technology. Using VXLAN allows the SD-Access fabric to support Layer 2 and Layer 3 virtual topologies (overlays) and the ability to operate over any IP-based network. -
Question 28 of 43
28. Question
1 pointsWhat is the responsibility of the ISE subsystem within the Cisco SD-Access Architecture controller layer?Correct
Incorrect
Hint
There are three control layer subsystems in the Cisco SD-Access Architecture. Cisco Network Control Platform (NCP) – provides underlay and fabric automation and orchestration Cisco Network Data Platform (NDP) – analyzes and correlates network events Cisco Identity Services Engine (ISE) – provides identity and policy services -
Question 29 of 43
29. Question
1 pointsWhat function is provided by the vManage Network Management System in the Cisco SD-WAN solution?Correct
Incorrect
Hint
The vManage NMS enables centralized provisioning and simplifies network changes. -
Question 30 of 43
30. Question
1 pointsWhat are three functions of the Cisco SD-WAN vBond orchestrator? (Choose three.)Correct
Incorrect
Hint
There are three components of the vBond orchestrator: The control plane connection over DTLS tunnels for communication with SD-WAN routers NAT traversal to connect SD-WAN routers and vSmart controllers Load balancing of SD-WAN routers across the vSmart controllers -
Question 31 of 43
31. Question
1 pointsIn a domain with multiple vSmart controllers, which Cisco SD-WAN solution performs automatic load balancing of SD-WAN routers across multiple controllers?Correct
Incorrect
Hint
The three major components of the vBond orchestrator are as follows: The control plane connection over DTLS tunnels for communication with SD-WAN routers NAT traversal to connect SD-WAN routers and vSmart controllers Load balancing of SD-WAN routers across the vSmart controllers -
Question 32 of 43
32. Question
1 pointsRefer to the exhibit. A junior network engineer is handed a print-out of the network information shown. Which protocol or service originated the information shown in the graphic?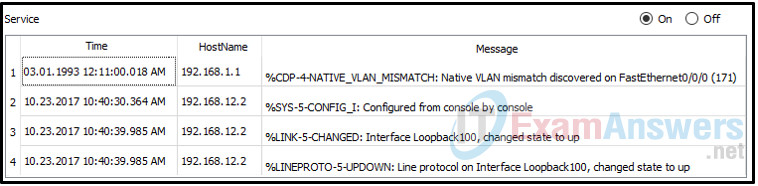 Correct
Correct
Incorrect
Hint
Syslog clients send log entries to a syslog server. The syslog server concentrates and stores log entries. Log entries are categorized by seven severity levels: emergencies (0), alerts (1), critical (2), errors (3), warnings (4), notifications (5), informational (6), and debugging (7). -
Question 33 of 43
33. Question
1 pointsRefer to the exhibit. Host H3 is having trouble communicating with host H1. The network administrator suspects a problem exists with the H3 workstation and wants to prove that there is no problem with the R2 configuration. What tool could the network administrator use on router R2 to prove that communication exists to host H1 from the interface on R2, which is the interface that H3 uses when communicating with remote networks?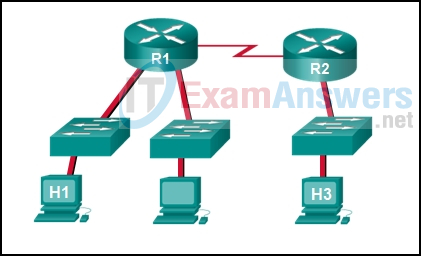 Correct
Correct
Incorrect
Hint
An extended ping allows an administrator to select specific ping features. For example in this situation, the network administrator could do an extended ping and specify a source address of the gigabit Ethernet port on the router. The destination address would be the IP address of host H1. If the ping succeeds connectivity exists from the Ethernet router interface on R2 to device H1. -
Question 34 of 43
34. Question
1 pointsIn the data gathering process, which type of device will listen for traffic, but only gather traffic statistics?Correct
Incorrect
Hint
A NetFlow collector is the device that receives traffic statistics from networking devices. NetFlow only gathers traffic statistics, unlike syslog and SNMP which can collect various network events. -
Question 35 of 43
35. Question
1 pointsWhich type of information can an administrator obtain with the show ip cache flow command?Correct
Incorrect
Hint
The show ip cache flow command provides information about the flow of data through the network, not specific information about configuration. -
Question 36 of 43
36. Question
1 pointsWhich network monitoring tool can provide a complete audit trail of basic information of all IP flows on a Cisco router and forward the data to a device?Correct
Incorrect
Hint
NetFlow is a Cisco technology that provides statistics on packets flowing through a Cisco router or multilayer switch. -
Question 37 of 43
37. Question
1 pointsWhich monitoring technology mirrors traffic flowing through a switch to an analysis device connected to another switch port?Correct
Incorrect
Hint
When enabled on a switch, SPAN or port mirroring, copies frames sent and received by the switch and forwards them to another port, known as a Switch Port Analyzer port, which has a analysis device attached. -
Question 38 of 43
38. Question
1 pointsRefer to the exhibit. Which command or set of commands will configure SW_A to copy all traffic for the server to the packet analyzer?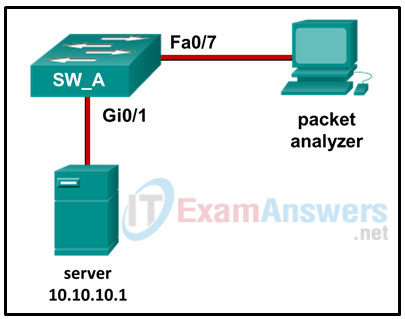 Correct
Correct
Incorrect
Hint
The local SPAN configuration requires two statements to identify the source and destination ports for the mirrored traffic. The statements must use the same session number. In this example, the source port is the port connected to the server (Gi0/1) and the destination port is the port attached to the packet analyzer (Fa0/7). -
Question 39 of 43
39. Question
1 pointsRefer to the exhibit. The RSPAN configuration for each switch is shown. The network administrator has configured RSPAN to allow the monitoring of traffic to a corporate server. Unfortunately, the administrator is unable to sniff any traffic from the link. Why is the administrator unable to sniff traffic?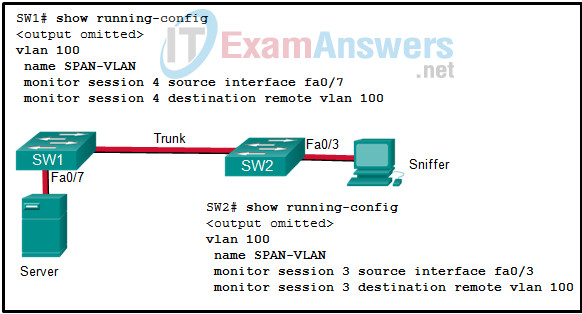 Correct
Correct
Incorrect
Hint
Both switches need the VLAN configuration mode command of remote-span to be added. -
Question 40 of 43
40. Question
1 pointsRefer to the exhibit. Host A is monitoring data and RSPAN is configured on Sw_A with the following commands: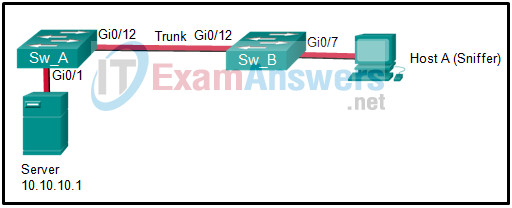
Sw_A# show running-config ...output omitted... monitor session 5 source interface gi0/1 monitor session 5 destination remote vlan 75 ...output omitted... vlan 75 name RSPAN remote span
Which set of commands would complete the RSPAN configuration?Correct
Incorrect
Hint
The Sw_B configuration is almost identical to the Sw_A configuration except the destination interface for the monitor session is Gi0/12 (the port to which host A connects). -
Question 41 of 43
41. Question
1 pointsA network administrator is using the Cisco DNA Center to monitor network health and to troubleshoot network issues. Which area should the administrator use to perform these tasks?Correct
Incorrect
Hint
The Cisco DNA Center has five main areas: Design – Model the entire network, from sites and buildings to devices and links, both physical and virtual, across campus, branch, WAN and cloud. Policy – Use policies to automate and simplify network management, reducing cost and risk while speeding rollout of new and enhanced services. Provision – Provide new services to users with ease, speed, and security across your enterprise network, regardless of network size and complexity. Assurance – Use proactive monitoring and insights from the network, devices, and applications to predict problems faster and ensure that policy and configuration changes achieve the business intent and the user experience you want. Platform – Use APIs to integrate with the preferred IT systems to create end-to-end solutions and add support for multi-vendor devices. -
Question 42 of 43
42. Question
1 pointsRefer to the exhibit. Based on the output generated by the show monitor session 1 command, how will SPAN operate on the switch?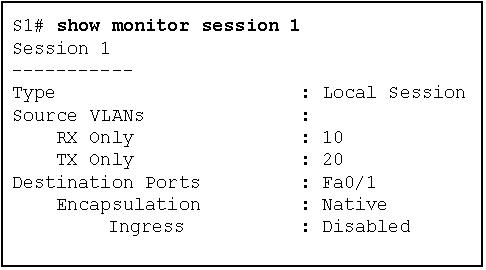 Correct
Correct
Incorrect
Hint
The show monitor session command is used to verify how SPAN is configured (what ports are involved in the traffic mirroring). -
Question 43 of 43
43. Question
1 pointsWhat is the description for a Syslog Level 0 event?Correct
Incorrect
