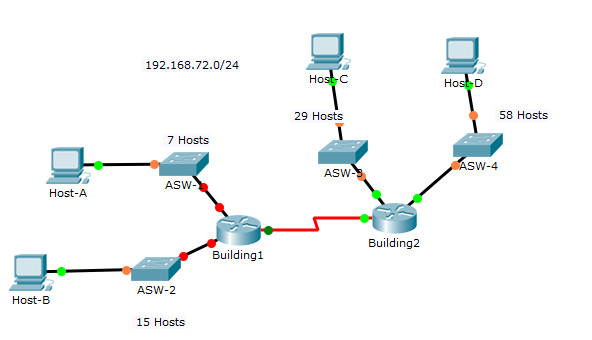
8.2.1.4 Packet Tracer – Designing and Implementing a VLSM Addressing Scheme Answers
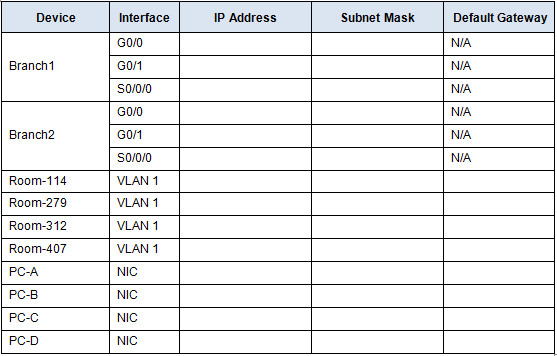
Addressing Table
Objectives
Part 1: Examine the Network Requirements
Part 2: Design the VLSM Addressing Scheme
Part 3: Assign IP Addresses to Devices and Verify Connectivity
Background
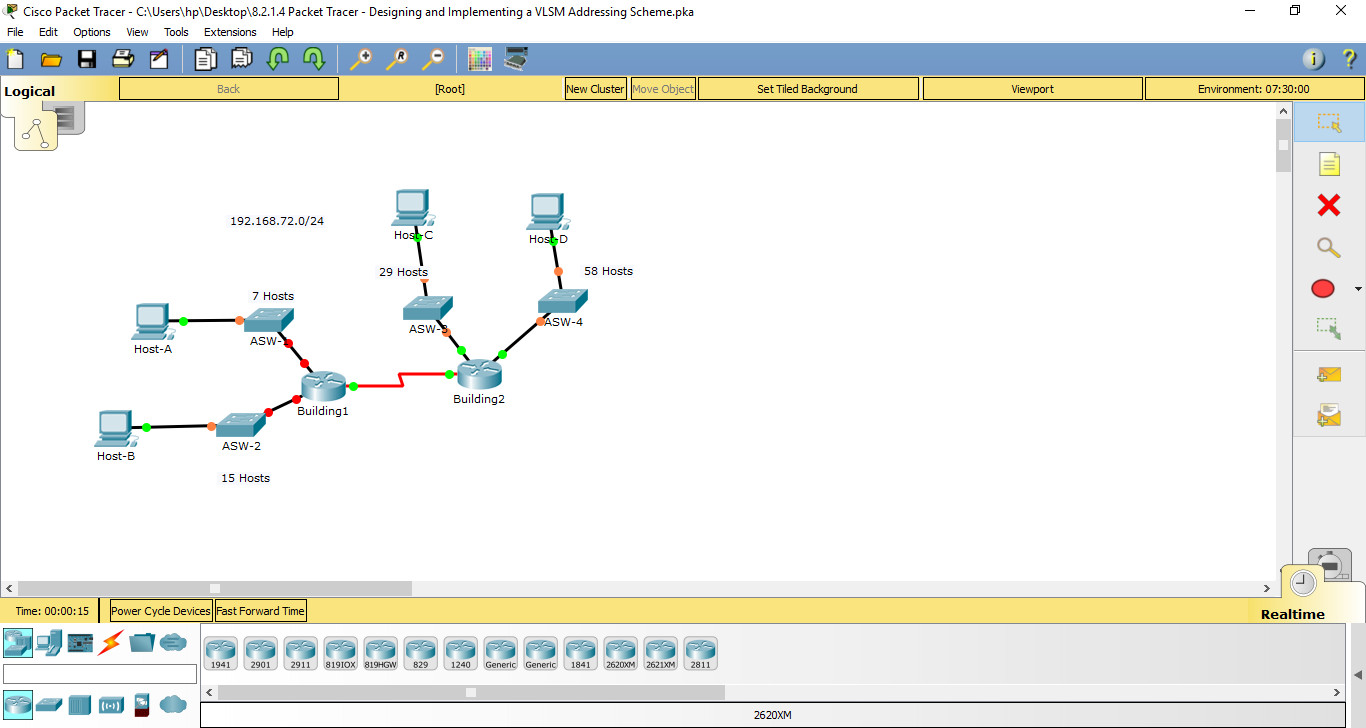
In this activity, you are given a /24 network address to use to design a VLSM addressing scheme. Based on a set of requirements, you will assign subnets and addressing, configure devices and verify connectivity.
Part 1: Examine the Network Requirements
Step 1: Determine the number of subnets needed.
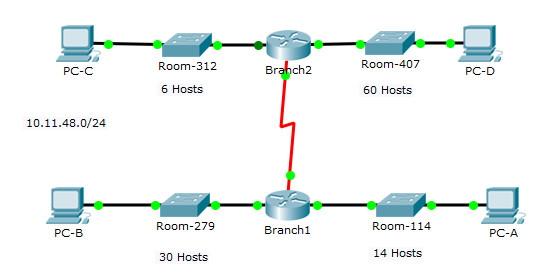
You will subnet the network address 10.11.48.0/24. The network has the following requirements:
• Room-114 LAN will require 14 host IP addresses
• Room-279 LAN will require 30 host IP addresses
• Room-312 LAN will require 6 host IP addresses
• Room-407 LAN will require 60 host IP addresses
How many subnets are needed in the network topology? 5 subnets
Step 2: Determine the subnet mask information for each subnet.
a. Which subnet mask will accommodate the number of IP addresses required for Room-114?
How many usable host addresses will this subnet support?
b. Which subnet mask will accommodate the number of IP addresses required for Room-279?
How many usable host addresses will this subnet support?
c. Which subnet mask will accommodate the number of IP addresses required for Room-312?
How many usable host addresses will this subnet support?
d. Which subnet mask will accommodate the number of IP addresses required for Room-407?
How many usable host addresses will this subnet support?
e. Which subnet mask will accommodate the number of IP addresses required for the connection between Branch1 and Branch2?
Part 2: Design the VLSM Addressing Scheme
Step 1: Divide the 10.11.48.0/24 network based on the number of hosts per subnet.
a. Use the first subnet to accommodate the largest LAN.
b. Use the second subnet to accommodate the second largest LAN.
c. Use the third subnet to accommodate the third largest LAN.
d. Use the fourth subnet to accommodate the fourth largest LAN.
e. Use the fifth subnet to accommodate the connection between Branch1 and Branch2.
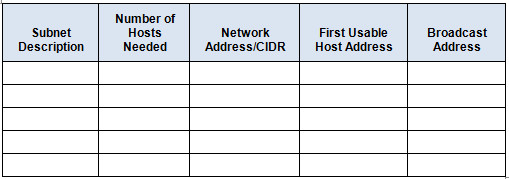
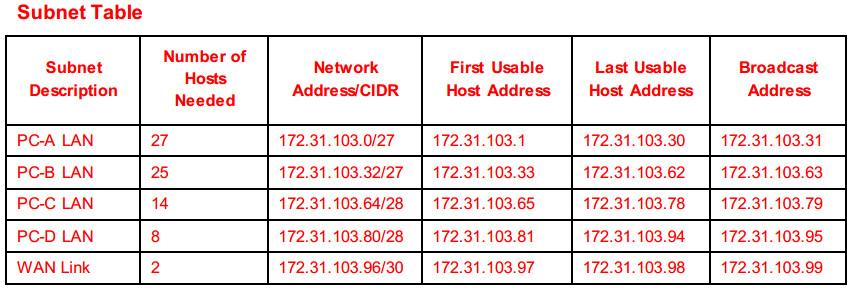
Step 2: Document the VLSM subnets.
Complete the Subnet Table, listing the subnet descriptions (e.g. Room-114 LAN), number of hosts needed, then network address for the subnet, the first usable host address, and the broadcast address. Repeat until all addresses are listed.
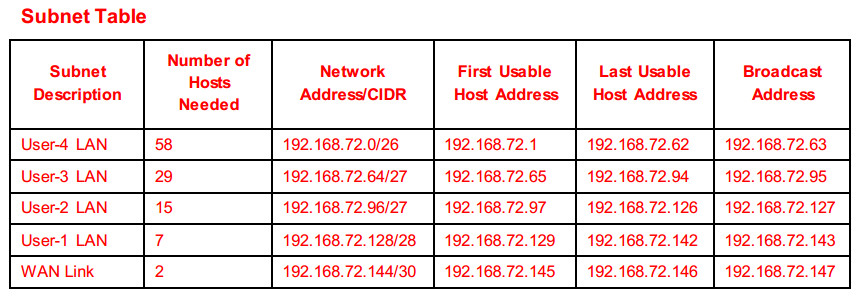
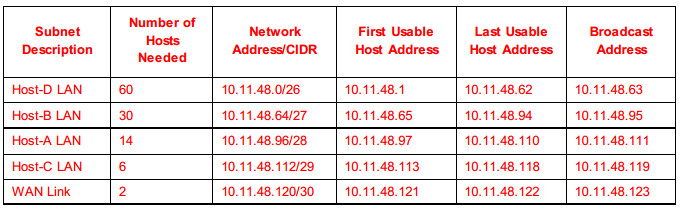
Subnet Table
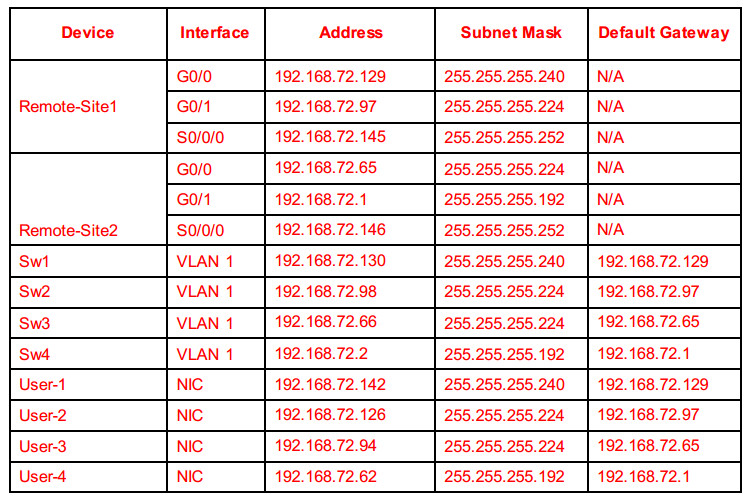
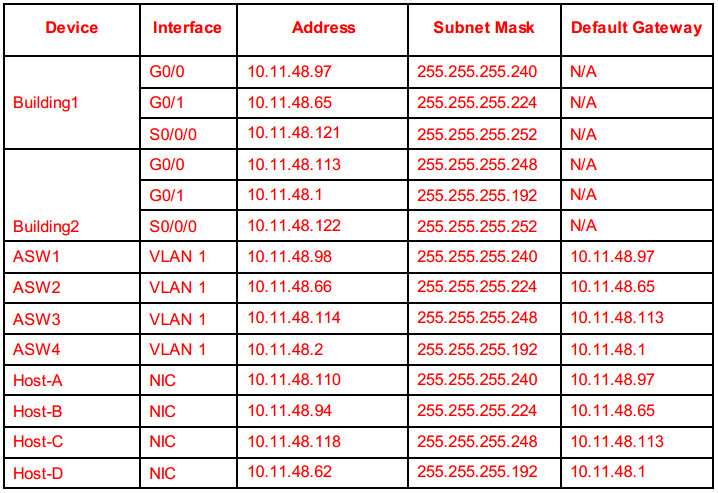
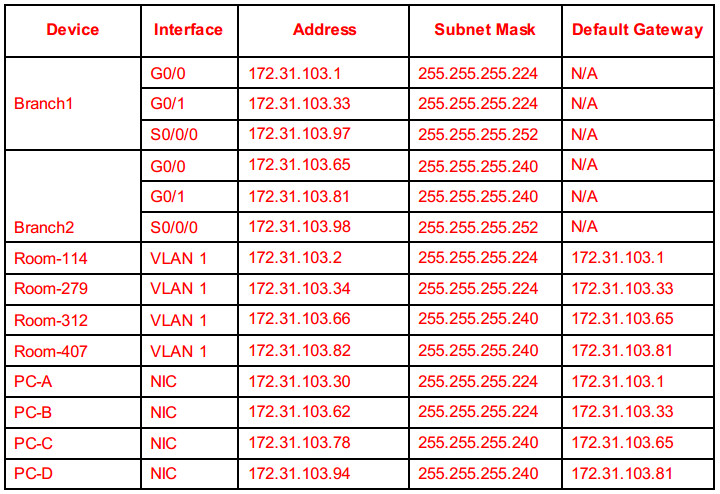
Step 3: Document the addressing scheme.
a. Assign the first usable IP addresses to Branch1 for the two LAN links and the WAN link.
b. Assign the first usable IP addresses to Branch2 for the two LANs links. Assign the last usable IP address for the WAN link.
c. Assign the second usable IP addresses to the switches.
d. Assign the last usable IP addresses to the hosts.
Part 3: Assign IP Addresses to Devices and Verify Connectivity
Most of the IP addressing is already configured on this network. Implement the following steps to complete the addressing configuration.
Step 1: Configure IP addressing on Branch1 LAN interfaces.
Step 2: Configure IP addressing on Room-312, including the default gateway.
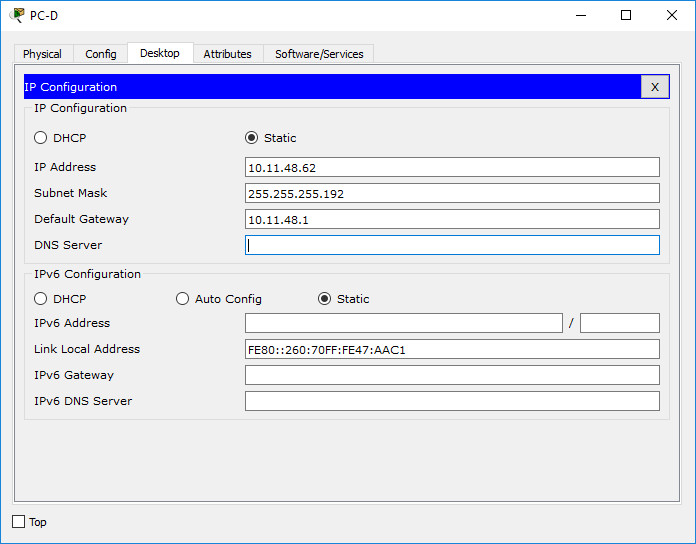
Step 3: Configure IP addressing on PC-D, including the default gateway.
Step 4: Verify connectivity.
You can only verify connectivity from Branch1, Room-312, and PC-D. However, you should be able to ping every IP address listed in the Addressing Table.
Suggested Scoring Rubric
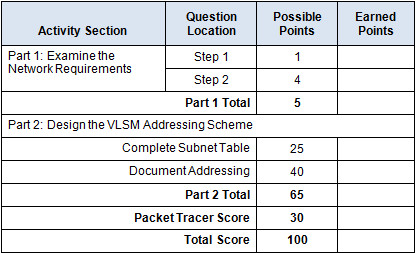
Instructor Notes:
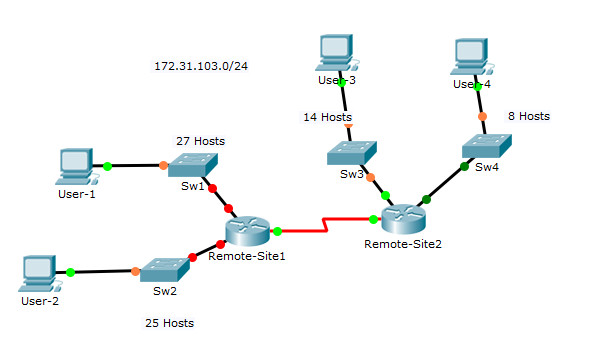
The following addressing tables represent the three possible addressing scenarios the student may get. Note that
the Device column is independent of the addressing scheme. For example, a student could receive the device
names from Scenario 1 and the addressing scheme from Scenario 3. In addition, the three possible topologies
are also independent of the device names and the addressing scheme (click reset in the activity to see the
different topologies). Therefore, this activity uses three independent variables with three possible values each for
a total of 27 possible combinations (3 device names x 3 addressing schemes x 3 topologies = 27 isomorphs)
Scenario 1 – Network Address: 10.11.48.0/24
Subnet Table
Refer:
VLSM Calculator Online
Scenario 2 – Network Address: 172.31.103.0/24
Scenario 3 – Network Address: 192.168.72.0/24