Lab Objective:
The objective of this lab exercise is for you to learn and understand how the errdisable recovery feature works on a Layer 2 network. This lab will not work on Packet Tracer.
Lab Purpose:
Understanding how errdisable functionality works on a Layer 2 switch is a fundamental skill that will allow a network engineer to recover a port from the error-disable state. As a Cisco engineer, as well as in the Cisco CCNA exam, you will be expected to know how to recover any port in an error-disable state.
Certification Level:
This lab is suitable for CCENT certification exam preparation.
Lab Difficulty:
This lab has a difficulty rating of 5/10.
Readiness Assessment:
When you are ready for your certification exam, you should complete this lab in no more than 20 minutes.
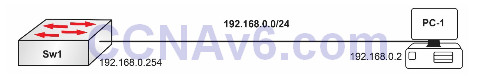
Lab Topology:
Please use the following topology to complete this lab exercise:
Task 1:
Configure the hostname on Sw1 as illustrated in the topology.
Task 2:
Create an SVI for VLAN1 on the switch and apply the respective IP address as illustrated in the topology (do the same thing with PC1).
Task 3:
Configure Sw1 port 0/1 with the following settings:
- Access-port mode
- Access-port VLAN1
- Switchport port-security enabled
- Switchport port-security maximum MACs of 1
- Switchport port-security violation mode shutdown
Task 4:
Remove PC1 and attach PC2 to the same port with a different IP address (192.168.10.2) and see how the port is shut down.
Task 5:
Configure the switch in such a way that any port being shut down by a security violation will recover automatically after 5 minutes. Check the status of the port where PC2 is connected after 5 minutes and make sure that the port is up and running. Issue a relevant show command.
Configuration and Verification
Task 1:
For reference information on configuring hostnames, please refer to earlier labs.
Task 2:
SW1#conf t Enter configuration commands, one per line. End with CTRL/Z. SW1(config)#interface vlan1 SW1(config-if)#ip address 192.168.0.254 255.255.255.0 SW1(config-if)#end SW1#
Task 3:
SW1#conf t Enter configuration commands, one per line. End with CTRL/Z. SW1(config)#interface gigabit0/1 SW1(config-if)#switchport mode access SW1(config-if)#switchport access vlan1 SW1(config-if)#switchport port-security SW1(config-if)#switchport port-security maximum 1 SW1(config-if)#switchport port-security violation-mode shutdown SW1(config-if)#end
Task 4:
My-PC:~ admin$ ping 192.168.0.254 PING 192.168.0.1 (192.168.0.254): 56 data bytes 64 bytes from 192.168.0.254: icmp_seq=0 ttl=64 time=1.969 ms 64 bytes from 192.168.0.254: icmp_seq=1 ttl=64 time=1.986 ms 64 bytes from 192.168.0.254: icmp_seq=2 ttl=64 time=2.047 ms 64 bytes from 192.168.0.254: icmp_seq=3 ttl=64 time=3.192 ms ^C --- 192.168.0.254 ping statistics --- 4 packets transmitted, 4 packets received, 0.0% packet loss round-trip min/avg/max/stddev = 1.969/2.299/3.192/0.517 ms
After removing PC1 and adding a new PC (PC2), the port will be shut down because of a port-security violation (more than one MAC address is being learned over that Gigabit interface).
The following message will be seen at the switch CLI:
%PORT_SECURITY-2-PSECURE_VIOLATION: Security violation occurred, caused by MAC address 001d.60b3.0aff on port FastEthernet0/1
If you go ahead and check the interface status, you will get the following:
Switch#show interface gigabit0/1 gigabitethernet0/1 is down, line protocol is down (err-disabled)
Task 5:
SW1#conf t Enter configuration commands, one per line. End with CTRL/Z. SW1(config)#errdisable recovery cause psecure-violation SW1(config)#errdisable recovery interval 300 SW1(config-if)#end SW1#
After 5 minutes (300 seconds), you will see the following messages at the switch CLI:
%PM-4-ERR_RECOVER: Attempting to recover from psecure-violation err-disable state on interface gigabit0/1 %LINK-3-UPDOWN: interface gigabit0/1, changed state to up %LINEPROTO-5-UPDOWN: Line protocol on Interface FastEthernet0/13, changed state to up
The new host is ready to be used, as the interface transitioned from shutdown (errdisabled) to up/up.
SW1#show errdisable recovery ErrDisable Reason Timer Status ----------------- -------------- Disabled udld Disabled bpduguard Enabled security-violation Disabled channel-misconfig Disabled pagp-flap Disabled dtp-flap Disabled link-flap Disabled l2ptguard Disabled psecure-violation Disabled gbic-invalid Disabled dhcp-rate-limit Disabled mac-limit Disabled unicast-flood Disabled arp-inspection Timer interval: 300 seconds Interfaces that will be enabled at the next timeout: Interface Errdisable reason Time left(sec) --------- ------------------ -------------- Gig0/1 security-violation 300
