Lab Objective:
The objective of this lab exercise is for you to learn and understand how to create and apply standard numbered access control lists (ACLs).
Lab Purpose:
Configuring and applying standard ACLs is a fundamental skill. Standard ACLs filter based on source address, and they should be applied as close to the destination as possible. As a Cisco engineer, as well as in the Cisco CCNA exam, you will be expected to know how to create and apply standard numbered ACLs.
Certification Level:
This lab is suitable for CCENT and CCNA certification exam preparation.
Lab Difficulty:
This lab has a difficulty rating of 7/10.
Readiness Assessment:
When you are ready for your certification exam, you should complete this lab in no more than 20 minutes.
Lab Topology:
Please use the following topology to complete this lab exercise:

Task 1:
Configure the hostnames on routers R1 and R3 as illustrated in the topology.
Task 2:
Configure R1 S0/0, which is a DCE, to provide a clock rate of 768 Kbps to R3. Configure the IP addresses on the Serial interfaces of R1 and R3 as illustrated in the topology. Configure a static default route on R1 pointing to R3 over the Serial connection between the two routers. Also, configure a static default route on R3 pointing to R1 via the Serial connection between the two routers. Configure the Loopback interfaces specified in the diagram on R1 and R3.
Task 3:
To test connectivity, ping R1 from R3 Serial0/0, Loopback10, Loopback20, and Loopback30 interfaces. To ping from the Loopback interfaces, use the ping <ip_address> source <interface> command.
Task 4:
On R1, create a standard numbered ACL to prevent inbound traffic from the Loopback20 subnet on R3, but explicitly allow all inbound traffic from Loopback10 and Loopback30 subnets on R3. Apply this ACL inbound on Serial0/0. Now try to ping R1 from R3 Serial0/0, Loopback10, Loopback20, and Loopback30 using the ping <ip_address> source <interface>. If you have configured this correctly, only Loopback10 and Loopback30 should still be able to ping.
Configuration and Verification
Task 1:
For reference information on configuring hostnames, please refer to previous labs.
Task 2:
For reference information on configuring IP addresses, please refer to previous labs.
R1#config t Enter configuration commands, one per line. End with CTRL/Z. R1(config)#ip route 0.0.0.0 0.0.0.0 serial0/0 172.16.1.2 R1(config-if)#end R1# R3#conf t Enter configuration commands, one per line. End with CTRL/Z. R3(config)#ip route 0.0.0.0 0.0.0.0 serial0/0 172.16.1.1 R3(config)#int loop10 R3(config-if)#ip address 10.10.10.3 255.255.255.128 R3(config-if)#exit R3(config)#int loop20 R3(config-if)#ip address 10.20.20.3 255.255.255.240 R3(config-if)#exit R3(config)#int loop30 R3(config-if)#ip address 10.30.30.3 255.255.255.248 R3(config-if)#end R3#
Task 3:
R3#ping 172.16.1.1 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 172.16.1.1, timeout is 2 seconds: !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 4/5/8 ms R3#ping 172.16.1.1 source loopback10 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 172.16.1.1, timeout is 2 seconds: Packet sent with a source address of 10.10.10.3 !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 4/6/8 ms R3#ping 172.16.1.1 source loopback20 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 172.16.1.1, timeout is 2 seconds: Packet sent with a source address of 10.20.20.3 !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 4/4/8 ms R3#ping 172.16.1.1 source loopback30 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 172.16.1.1, timeout is 2 seconds: Packet sent with a source address of 10.30.30.3 !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 4/4/4 ms
Task 4:
R1#conf t Enter configuration commands, one per line. End with CTRL/Z. R1(config)#access-list 10 remark “Permit From R3 Loopback10” R1(config)#access-list 10 permit 10.10.10.0 0.0.0.127 R1(config)#access-list 10 remark “Deny From R3 Loopback20” R1(config)#access-list 10 deny 10.20.20.0 0.0.0.15 R1(config)#access-list 10 remark “Permit From R3 Loopback30” R1(config)#access-list 10 permit 10.30.30.0 0.0.0.7 R1(config)#int s0/0 R1(config-if)#ip access-group 10 in R1(config)#end R1#show ip access-lists Standard IP access list 10 10 permit 10.10.10.0, wildcard bits 0.0.0.127 20 deny 10.20.20.0, wildcard bits 0.0.0.15 30 permit 10.30.30.0, wildcard bits 0.0.0.7
NOTE: The wildcard masks used in ACLs are configured in the same way as those for Enhanced Interior Gateway Routing Protocol (EIGRP) and OSPF. To determine the wildcard mask, you can simply subtract the network mask for the network on which you want to match with the ACL from the broadcast mask. This concept is illustrated in the subtraction table shown below:
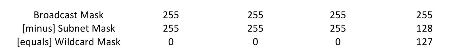
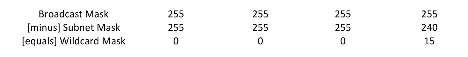
In our example, the subnet mask of the 10.10.10.0/25 subnet is 255.255.255.128. If this is subtracted from the broadcast mask of 255.255.255.255, the result is 0.0.0.127, which is the wildcard mask we will use in the ACL match for this subnet. Using the same concept, the subnet mask of the 10.20.20.0/28 subnet is 255.255.255.240. If we used the table above to determine the wildcard mask, we would get the following:
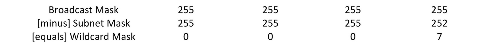
And, finally, the subnet mask of the 10.30.30.0/29 subnet is 255.255.255.248. If we used the same table to get the wildcard mask, we would end up with the following:
It is extremely important to practice creating wildcards for ACLs. Take time out to practice these until you are extremely comfortable with them. ACLs are a very important part of the CCNA certification exam and in the real world.
While it is not mandatory, I prefer to use the access-list [number] remark [description] statement so that I know which ACL line is matching what. This will make it easier for you. You may or may not want to do so, but I feel that it is good practice to do so. Do whatever you feel comfortable doing.
R3#ping 172.16.1.1 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 172.16.1.1, timeout is 2 seconds: U.U.U Success rate is 0 percent (0/5) R3#ping 172.16.1.1 source loopback10 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 172.16.1.1, timeout is 2 seconds: Packet sent with a source address of 10.10.10.3 !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 4/4/4 ms R3#ping 172.16.1.1 source loopback20 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 172.16.1.1, timeout is 2 seconds: Packet sent with a source address of 10.20.20.3 U.U.U Success rate is 0 percent (0/5) R3#ping 172.16.1.1 source loopback30 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 172.16.1.1, timeout is 2 seconds: Packet sent with a source address of 10.30.30.3 !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 4/4/4 ms
NOTE: Whenever you see a ping fail and the router shows U.U.U, it is typically because your ping request was administratively prohibited by an ACL on the other end.
The second lesson to be learned in this exercise is that even though the ACL configuration focused on R3 Loopback10, Loopback20, and Loopback30, because we did not explicitly allow the Serial0/0 subnet between R1 and R3, this is implicitly denied at the end of the ACL. Keep this in mind: if traffic is not explicitly permitted, it is implicitly denied. It is very important to understand this aspect in regard to access control lists. The explicitly configured statements show as matches against ACL entries, but implicit deny matches do not.
R1#show access-lists Standard IP access list 10 10 permit 10.10.10.0, wildcard bits 0.0.0.127 (15 matches) 20 deny 10.20.20.0, wildcard bits 0.0.0.15 (11 matches) 30 permit 10.30.30.0, wildcard bits 0.0.0.7 (15 matches)
Your output may differ from mine due to differences in IOS releases and platforms.
