3.5.1 Packet Tracer – Create a Simple Network Answers Answers Note: Red font color or gray highlights indicate text that appears in the Answers copy only. Addressing Table Device Interface IP Address Subnet Mask Default Gateway PC Ethernet0 DHCP 192.168.0.1 Wireless Router LAN 192.168.0.1 255.255.255.0 N/A Internet DHCP …
3.4.3 Packet Tracer – Configure End Devices Answers Answers Note: Red font color or gray highlights indicate text that appears in the Answers copy only. Objectives Configure various end devices in Packet Tracer. Background / Scenario In this activity, you will construct a simple Packet Tracer network and …
3.3.4 Packet Tracer – Deploy and Cable Devices Answers Answers Note: Red font color or gray highlights indicate text that appears in the Answers copy only. Objectives Deploy and Cable Network Devices. Background / Scenario You will locate, deploy, and cable multiple types of devices. Instructions Part 1: …
3.3.3 Packet Tracer – Deploy Devices Answers Answers Note: Red font color or gray highlights indicate text that appears in the Answers copy only. Objectives In this activity, you will deploy multiple devices. Required Resources Latest version of Packet Tracer Instructions A list of device labels is visible …
20.3.12 Lab – Troubleshoot Using Network Utilities Answers Answers Note: Red font color or gray highlights indicate text that appears in the Answers copy only. Objectives Interpret the output of commonly used network command line utilities. Determine which network utility can provide the necessary information to perform troubleshooting …
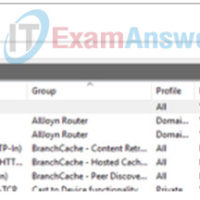
16.3.8 Lab – Configure Windows Firewall Settings Answers Topology Addressing Table Device Interface IP Address Subnet Mask PC-A NIC 192.168.1.10 255.255.255.0 PC-B NIC 192.168.1.11 255.255.255.0 Objectives Access Windows Firewall settings to add a new firewall rule. Create a firewall rule to permit ping requests. Remove the new firewall …
15.2.3 Lab – Social Engineering Answers Objective In this lab, you will research examples of social engineering and identify ways to recognize and prevent it. Resources Computer with internet Access Instructions Part 1: Research Social Engineering Examples Social engineering, as it relates to information security, is used to …
14.3.8 Lab – Configure a Mobile Device for Wi-Fi Connectivity Answers Objectives Familiarize yourself with the Wi-Fi settings on mobile devices. Turn the Wi-Fi radio on and off Set the device to forget a found Wi-Fi network Connect to a new Wi-Fi network. Background / Scenario In this …
14.2.13 Lab – Install Linux in a Virtual Machine and Explore the GUI Answers Objectives Part 1: Prepare a Computer for Virtualization Part 2: Install a Linux OS on the Virtual Machine Part 3: Explore the GUI Background / Scenario Computing power and resources have increased tremendously over …
13.5.5 Lab – Configure a Wireless Router and Client Answers Topology Sample Wireless Router Settings Network Name (SSID) Network Passphrase Router Password Home-Net cisco123 cisco12345 Note: The above wireless router settings are used as example only. Objectives Part 1: Configure Basic Settings on a Wireless Router Part 2: …