Objectives Research and analyze cyber security incidents Background / Scenario In 2016, it was estimated that businesses lost $400 million dollars annually to cyber criminals. Governments, businesses, and individual users are increasingly the targets of cyberattacks and cybersecurity incidents are becoming more common. In this lab, you will …
Objectives Research and analyze IoT application vulnerabilities Background / Scenario The Internet of Things (IoT) consists of digitally connected devices that are connecting every aspect of our lives, including our homes, offices, cars, and even our bodies to the Internet. With the accelerating adoption of IPv6 and the …
Objectives Research and analyze cyber security incidents Background / Scenario Governments, businesses, and individual users are increasingly the targets of cyberattacks and experts predict that these attacks are likely to increase in the future. Cybersecurity education is a top international priority as high-profile cyber-security related incidents raise the …
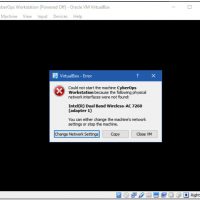
Objectives Part 1: Prepare a Personal Computer for Virtualization Part 2: Import a Virtual Machine into VirtualBox Inventory Background / Scenario Computing power and resources have increased tremendously over the last 10 years. A benefit of having multicore processors and large amounts of RAM is the ability to …
Objectives Upon completion of this chapter, you will be able to answer the following questions: What are the steps in the Cyber Kill Chain? How do you classify an intrusion event using the Diamond Model? How do you apply the VERIS schema to an incident? What are the …
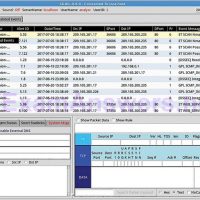
Objectives Upon completion of this chapter, you will be able to answer the following questions: What is the structure of alerts? How are alerts classified? How is data prepared for use in a network security monitoring (NSM) system? How do you use Security Onion tools to investigate network …
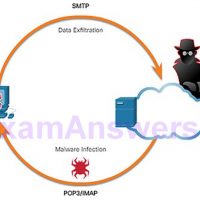
Objectives Upon completion of this chapter, you will be able to answer the following questions: What is the behavior of common network protocols in the context of security monitoring? How do security technologies affect the ability to monitor common network protocols? What are the types of data used …
Objectives Upon completion of this chapter, you will be able to answer the following questions: What are some methods of mitigating malware? What are the contents of host-based IPS/IDS log entries? How do you use a public service to generate a malware analysis report? How do you classify …
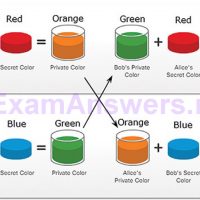
Objectives Upon completion of this chapter, you will be able to answer the following questions: How is cryptography used to secure communications? What is the role of cryptography in ensuring the integrity and authenticity of data? How do cryptographic approaches enhance data confidentiality? What is public key cryptography? …
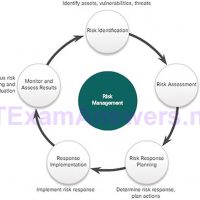
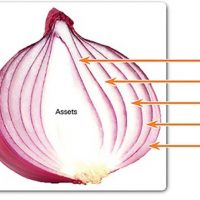
Objectives Upon completion of this chapter, you will be able to answer the following questions: How is the defense-in-depth strategy used to protect networks? What are common security policies, regulations, and standards? What are access control policies? How is AAA used to control network access? What information sources …