Author: ITExamAnswers
1.2.2.9 Lab – Evaluate the IoT Security Risk in an Industry Sector (Instructor Version) Objectives Part 1: Research Risks for an Industry Sector Part 2: Investigate the Potential Impact of a Security Breach Part 3: Describe Security Measures for Your Industry Sector Background / Scenario Any implementation of …
1.2.1.3 Lab – Evaluate Home Automation Products (Instructor Version) Objectives Part 1: Conduct Research for Home Automation Products Part 2: Prepare a Presentation Background / Scenario In this lab, you will investigate the wide variety of home automation products. Some products may require monitoring or maintenance services, so …
1.1.1.7 Lab – Evaluate Recent IoT Attacks (Instructor Version) Objectives Part 1: Research Recent IoT Attacks Part 2: Describe Mitigation Techniques Background / Scenario As the number of IoT devices continue to grow at an exponential rate, so are the number of attacks on these devices. There are …
1.1.1.6 Lab – Shodan Search (Instructor Version) Objectives Part 1: Obtain Access to Shodan’s Free Features Part 2: Investigate Connected IoT Devices Background / Scenario Warning: Do not attempt to login to any device you find on the Shodan search engine. Doing so violates your ethical hacking agreement. …
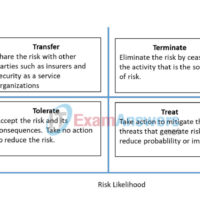
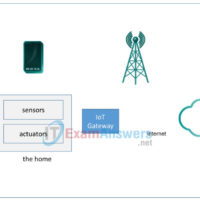
6.2.4.4 Packet Tracer – Threat Modeling to Assess Risk in an IoT System (Instructor Version) Topology This is a home IoT system that has been prototyped in Packet Tracer. It shows a cutaway view of a home with different sensors, actuators, and connections shown. Objectives Part 1: Creating …
5.2.1.6 Packet Tracer – Threat Modeling at the IoT Application Layer (Instructor Version) Topology This is a home IoT system that has been prototyped in Packet Tracer. It shows a cutaway view of a home with different sensors, actuators, and connections shown. Objectives In this Packet Tracer, you …
4.3.1.6 Packet Tracer – Threat Modeling at the IoT Communication Layer (Instructor Version) Topology The topology is a home IoT system that has been prototyped in Packet Tracer. It shows a cutaway view of a home with different sensors, actuators, and connections shown. Objectives In this Packet Tracer, …
3.3.2.5 Packet Tracer – Threat Modeling at the IoT Device Layer (Instructor Version) Topology The topology is a home IoT system that has been prototyped in Packet Tracer. It shows a cutaway view of a home with different sensors, actuators, and connections shown. Objectives In this Packet Tracer, …
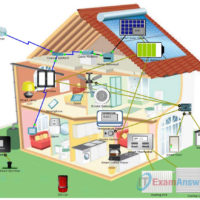
1.2.1.1 Packet Tracer – Explore the Smart Home (Instructor Version) Topology Objectives Explore the Smart Home Analyze the Usage of Fog Computing in the Smart Home Background / Scenario In this activity, you will explore the smart home example. Depending on the application, some data is best processed …
IoT Security 1.1 Chapter 6 Quiz Exam Answers 1. What is a characteristic of a blockchain? It uses risk avoidance. It is a government approved authentication protocol. It is immutable. It uses the XML format. 2. Which problem associated with transactions is solved by blockchain technology? trust encryption …