Time limit: 0
Quiz-summary
0 of 25 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
Information
Good Luck!
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 25 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- Answered
- Review
-
Question 1 of 25
1. Question
1 pointsIn which configuration would an outbound ACL placement be preferred over an inbound ACL placement?Correct
Incorrect
Hint
An outbound ACL should be utilized when the same ACL filtering rules will be applied to packets coming from more than one inbound interface before exiting a single outbound interface. The outbound ACL will be applied on the single outbound interface. -
Question 2 of 25
2. Question
1 pointsWhich address is required in the command syntax of a standard ACL?Correct
Incorrect
Hint
The only filter that can be applied with a standard ACL is the source IP address. An extended ACL can use multiple criteria to filter traffic, such as source IP address, destination IP address, type of traffic, and type of message. -
Question 3 of 25
3. Question
1 pointsWhich statement describes a difference between the operation of inbound and outbound ACLs?Correct
Incorrect
-
Question 4 of 25
4. Question
1 pointsWhich three statements describe ACL processing of packets? (Choose three.)Correct
Incorrect
Hint
When a packet comes into a router that has an ACL configured on the interface, the router compares the condition of each ACE to determine if the defined criteria has been met. If met, the router takes the action defined in the ACE (allows the packet through or discards it). If the defined criteria has not been met, the router proceeds to the next ACE. An implicit deny any statement is at the end of every standard ACL. -
Question 5 of 25
5. Question
1 pointsWhat single access list statement matches all of the following networks? 192.168.16.0 192.168.17.0 192.168.18.0 192.168.19.0Correct
Incorrect
Hint
The ACL statement access-list 10 permit 192.168.16.0 0.0.3.255 will match all four network prefixes. All four prefixes have the same 22 high order bits. These 22 high order bits are matched by the network prefix and wildcard mask of 192.168.16.0 0.0.3.255. -
Question 6 of 25
6. Question
1 pointsA network administrator needs to configure a standard ACL so that only the workstation of the administrator with the IP address 192.168.15.23 can access the virtual terminal of the main router. Which two configuration commands can achieve the task? (Choose two.)Correct
Incorrect
Hint
To permit or deny one specific IP address, either the wildcard mask 0.0.0.0 (used after the IP address) or the wildcard mask keyword host (used before the IP address) can be used. -
Question 7 of 25
7. Question
1 pointsIf a router has two interfaces and is routing both IPv4 and IPv6 traffic, how many ACLs could be created and applied to it?Correct
Incorrect
Hint
In calculating how many ACLs can be configured, use the rule of “three Ps”: one ACL per protocol, per direction, per interface. In this case, 2 interfaces x 2 protocols x 2 directions yields 8 possible ACLs. -
Question 8 of 25
8. Question
1 pointsWhich three statements are generally considered to be best practices in the placement of ACLs? (Choose three.)Correct
Incorrect
Hint
Extended ACLs should be placed as close as possible to the source IP address, so that traffic that needs to be filtered does not cross the network and use network resources. Because standard ACLs do not specify a destination address, they should be placed as close to the destination as possible. Placing a standard ACL close to the source may have the effect of filtering all traffic, and limiting services to other hosts. Filtering unwanted traffic before it enters low-bandwidth links preserves bandwidth and supports network functionality. Decisions on placing ACLs inbound or outbound are dependent on the requirements to be met. -
Question 9 of 25
9. Question
1 pointsRefer to the exhibit. Which command would be used in a standard ACL to allow only devices on the network attached to R2 G0/0 interface to access the networks attached to R1?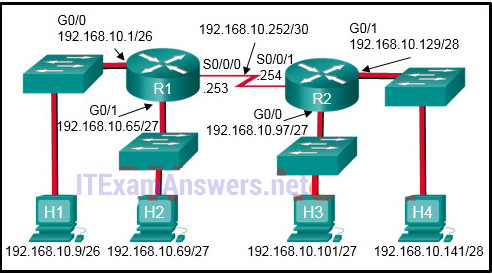 Correct
Correct
Incorrect
Hint
Standard access lists only filter on the source IP address. In the design, the packets would be coming from the 192.168.10.96/27 network (the R2 G0/0 network). The correct ACL is access-list 1 permit 192.168.10.96 0.0.0.31. -
Question 10 of 25
10. Question
1 pointsRefer to the exhibit. If the network administrator created a standard ACL that allows only devices that connect to the R2 G0/0 network access to the devices on the R1 G0/1 interface, how should the ACL be applied?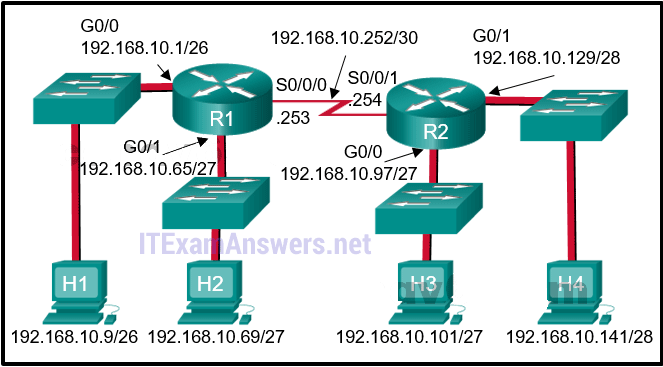 Correct
Correct
Incorrect
Hint
Because standard access lists only filter on the source IP address, they are commonly placed closest to the destination network. In this example, the source packets will be coming from the R2 G0/0 network. The destination is the R1 G0/1 network. The proper ACL placement is outbound on the R1 G0/1 interface. -
Question 11 of 25
11. Question
1 pointsRefer to the following output. What is the significance of the 4 match(es) statement? R1#Correct
Incorrect
Hint
The show access-lists command shows how many packets have met the criteria for each ACE in terms of a specific number of “matches.” -
Question 12 of 25
12. Question
1 pointsOn which router should the show access-lists command be executed?Correct
Incorrect
Hint
The show access-lists command is only relevant to traffic passing through the router on which the ACL is configured. -
Question 13 of 25
13. Question
1 pointsWhat is the quickest way to remove a single ACE from a named ACL?Correct
Incorrect
Hint
Named ACL ACEs can be removed using the no command followed by the sequence number. -
Question 14 of 25
14. Question
1 pointsWhich feature will require the use of a named standard ACL rather than a numbered standard ACL?Correct
Incorrect
Hint
Standard ACLs (whether numbered or named) only filter on the source IP address. Having a named ACL makes it easier at times to identify the purpose as well as modify the ACL. -
Question 15 of 25
15. Question
1 pointsAn administrator has configured an access list on R1 to allow SSH administrative access from host 172.16.1.100. Which command correctly applies the ACL?Correct
Incorrect
Hint
Administrative access over SSH to the router is through the vty lines. Therefore, the ACL must be applied to those lines in the inbound direction. This is accomplished by entering line configuration mode and issuing the access-class command. -
Question 16 of 25
16. Question
1 pointsWhich type of router connection can be secured by the access-class command?Correct
Incorrect
Hint
Access to vty lines can be filtered with an ACL and applied using the access-class in command. -
Question 17 of 25
17. Question
1 pointsConsider the following output for an ACL that has been applied to a router via the access-class in command. What can a network administrator determine from the output that is shown? R1#Correct
Incorrect
Hint
The access-class command is used only on VTY ports. VTY ports support Telnet and/or SSH traffic. The match permit ACE is how many attempts were allowed using the VTY ports. The match deny ACE shows that a device from a network other than 192.168.10.0 was not allowed to access the router through the VTY ports. -
Question 18 of 25
18. Question
1 pointsRefer to the exhibit. A router has an existing ACL that permits all traffic from the 172.16.0.0 network. The administrator attempts to add a new ACE to the ACL that denies packets from host 172.16.0.1 and receives the error message that is shown in the exhibit. What action can the administrator take to block packets from host 172.16.0.1 while still permitting all other traffic from the 172.16.0.0 network?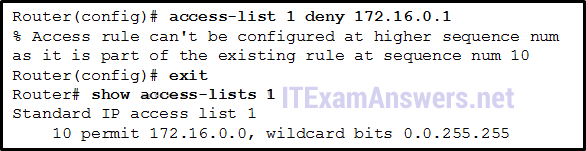 Correct
Correct
Incorrect
Hint
Because the new deny ACE is a host address that falls within the existing 172.16.0.0 network that is permitted, the router rejects the command and displays an error message. For the new deny ACE to take effect, it must be manually configured by the administrator with a sequence number that is less than 10. -
Question 19 of 25
19. Question
1 pointsRefer to the exhibit. An ACL was configured on R1 with the intention of denying traffic from subnet 172.16.4.0/24 into subnet 172.16.3.0/24. All other traffic into subnet 172.16.3.0/24 should be permitted. This standard ACL was then applied outbound on interface Fa0/0. Which conclusion can be drawn from this configuration?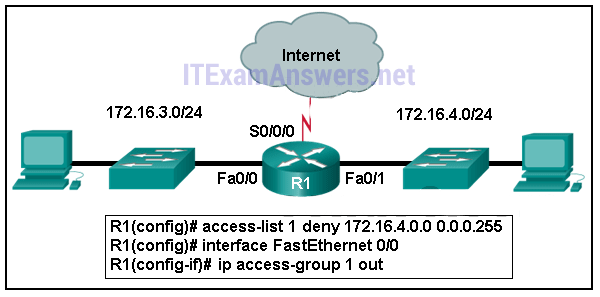 Correct
Correct
Incorrect
Hint
Because of the implicit deny at the end of all ACLs, the access-list 1 permit any command must be included to ensure that only traffic from the 172.16.4.0/24 subnet is blocked and that all other traffic is allowed. -
Question 20 of 25
20. Question
1 pointsRefer to the exhibit. What will happen to the access list 10 ACEs if the router is rebooted before any other commands are implemented?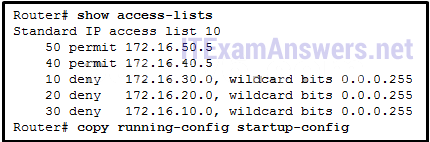 Correct
Correct
Incorrect
Hint
After a reboot, access list entries will be renumbered to allow host statements to be listed first and thus more efficiently processed by the Cisco IOS. -
Question 21 of 25
21. Question
1 pointsWhat is the effect of configuring an ACL with only ACEs that deny traffic?Correct
Incorrect
Hint
Because there is a deny any ACE at the end of every standard ACL, the effect of having all deny statements is that all traffic will be denied regardless of the direction in which the ACL is applied. -
Question 22 of 25
22. Question
1 pointsWhich type of ACL statements are commonly reordered by the Cisco IOS as the first ACEs?Correct
Incorrect
Hint
ACEs are commonly reordered from the way they were entered by the network administrator. The ACEs that have host criteria such as in the statement permit host 192.168.10.5, are reordered as the first statements because they are the most specific (have the most number of bits that must match). -
Question 23 of 25
23. Question
1 pointsA network administrator is configuring an ACL to restrict access to certain servers in the data center. The intent is to apply the ACL to the interface connected to the data center LAN. What happens if the ACL is incorrectly applied to an interface in the inbound direction instead of the outbound direction?Correct
Incorrect
Hint
Always test an ACL to ensure that it performs as it was designed. Applying an ACL that is applied using the ip access-group in command instead of using the ip access-group out command is not going to work as designed. -
Question 24 of 25
24. Question
1 pointsWhen would a network administrator use the clear access-list counters command?Correct
Incorrect
Hint
The clear access-list counters command is used to reset all numbers relating to ACE match conditions that have been made within a particular ACE. The command is useful when troubleshooting an ACL that has recently been deployed. -
Question 25 of 25
25. Question
1 pointsMatch each statement with the example subnet and wildcard that it describes. (Not all options are used.)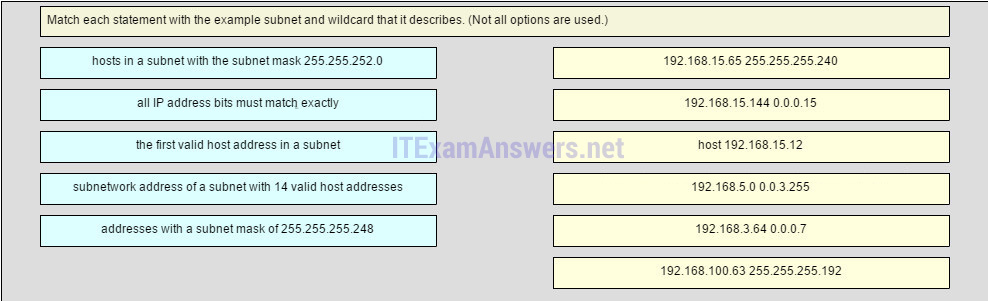
Sort elements
- 192.168.15.65 255.255.255.240
- 192.168.15.144 0.0.0.15
- host 192.168.15.12
- 192.168.5.0 0.0.3.255
- 192.168.3.64 0.0.0.7
- 192.168.100.63.255.255.255.192
-
the first valid host address in a subnet
-
subnetwork address of a subnet with 14 valid host addreses
-
all IP address bits must match exactly
-
hosts in a subnet with the subnet mask 255.255.252.0
-
address with a subnet mask of 255.255.255.248
Correct
Incorrect
Hint
Converting the wildcard mask 0.0.3.255 to binary and subtracting it from 255.255.255.255 yields a subnet mask of 255.255.252.0. Using the host parameter in a wildcard mask requires that all bits match the given address. 192.168.15.65 is the first valid host address in a subnetwork beginning with the subnetwork address 192.168.15.64. The subnet mask contains 4 host bits, yielding subnets with 16 addresses. 192.168.15.144 is a valid subnetwork address in a similar subnetwork. Change the wildcard mask 0.0.0.15 to binary and subtract it from 255.255.255.255, and the resulting subnet mask is 255.255.255.240. 192.168.3.64 is a subnetwork address in a subnet with 8 addresses. Convert 0.0.0.7 to binary and subtract it from 255.255.255.255, and the resulting subnet mask is 255.255.255.248. That mask contains 3 host bits, and yields 8 addresses.

Hi, ccna2 chap7, the last quiz using drag and drop, can’t be done from a cell phone. Can’t pick answers. :-) Windows phone 8.1 thanks’