CCNA 2 Practice Final v5.0 Exam Answers 2015 (100%) PDF Download
-
A client is using SLAAC to obtain an IPv6 address for its interface. After an address has been generated and applied to the interface, what must the client do before it can begin to use this IPv6 address?
- It must send a DHCPv6 INFORMATION-REQUEST message to request the address of the DNS server.
- It must send an ICMPv6 Router Solicitation message to determine what default gateway it should use.
- It must send a DHCPv6 REQUEST message to the DHCPv6 server to request permission to use this address.
- It must send an ICMPv6 Neighbor Solicitation message to ensure that the address is not already in use on the network.
-
Which DHCP IPv4 message contains the following information?Destination address: 255.255.255.255
Client IPv4 address: 0.0.0.0
Default gateway address: 0.0.0.0
Subnet mask: 0.0.0.0
- DHCPACK
- DHCPDISCOVER
- DHCPOFFER
- DHCPREQUEST
-
Refer to the exhibit. If the IP addresses of the default gateway router and the DNS server are correct, what is the configuration problem?
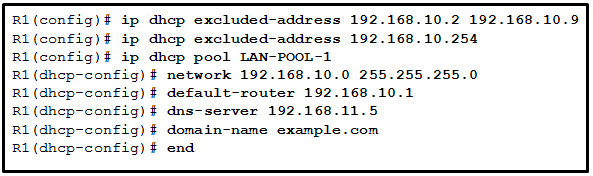
- The DNS server and the default gateway router should be in the same subnet.
- The IP address of the default gateway router is not contained in the excluded address list.
- The default-router and dns-server commands need to be configured with subnet masks.
- The IP address of the DNS server is not contained in the excluded address list.
-
Refer to the exhibit. An administrator is trying to configure PAT on R1, but PC-A is unable to access the Internet. The administrator tries to ping a server on the Internet from PC-A and collects the debugs that are shown in the exhibit. Based on this output, what is most likely the cause of the problem?
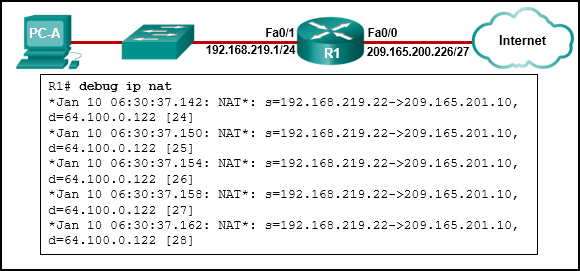
- The address on Fa0/0 should be 64.100.0.1.
- The NAT source access list matches the wrong address range.
- The inside global address is not on the same subnet as the ISP.
- The inside and outside NAT interfaces have been configured backwards.
-
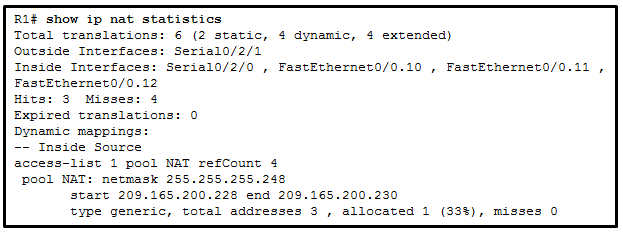
Refer to the exhibit. A PC at address 10.1.1.45 is unable to access the Internet. What is the most likely cause of the problem?
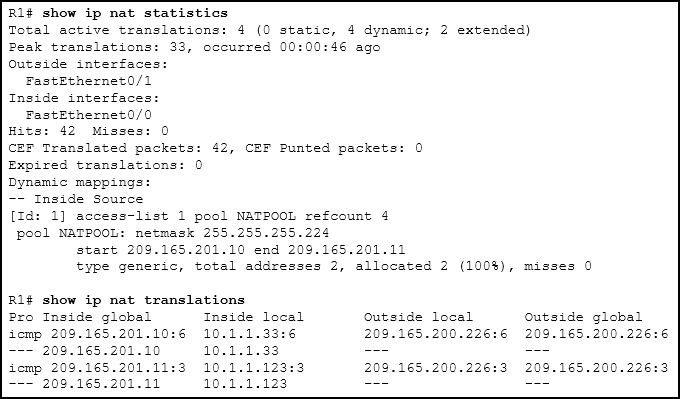
- The NAT pool has been exhausted.
- The wrong netmask was used on the NAT pool.
- Access-list 1 has not been configured properly.
- The inside and outside interfaces have been configured backwards.
-
What is a disadvantage when both sides of a communication use PAT?
- Host IPv4 addressing is complicated.
- End-to-end IPv4 traceability is lost.
- The flexibility of connections to the Internet is reduced.
- The security of the communication is negatively impacted.
-
A small company has a web server in the office that is accessible from the Internet. The IP address 192.168.10.15 is assigned to the web server. The network administrator is configuring the router so that external clients can access the web server over the Internet. Which item is required in the NAT configuration?
- an IPv4 address pool
- an ACL to identify the local IPv4 address of the web server
- the keyword overload for the ip nat inside source command
- the ip nat inside source command to link the inside local and inside global addresses
-
Refer to the exhibit. A network administrator has just configured address translation and is verifying the configuration. What three things can the administrator verify? (Choose three.)
- Address translation is working.
- Three addresses from the NAT pool are being used by hosts.
- The name of the NAT pool is refCount.
- A standard access list numbered 1 was used as part of the configuration process.
- Two types of NAT are enabled.
- One port on the router is not participating in the address translation.
-
Which two pieces of information are required when creating a standard access control list? (Choose two.)
- destination address and wildcard mask
- source address and wildcard mask
- subnet mask and wildcard mask
- access list number between 100 and 199
- access list number between 1 and 99
-
Which two keywords can be used in an access control list to replace a wildcard mask or address and wildcard mask pair? (Choose two.)
- most
- host
- all
- any
- some
- gt
-
What is the effect of the access control list wildcard mask 0.0.0.15? (Choose two.)
- The first 28 bits of a supplied IP address will be ignored.
- The last four bits of a supplied IP address will be ignored.
- The first 32 bits of a supplied IP address will be matched.
- The first 28 bits of a supplied IP address will be matched.
- The last five bits of a supplied IP address will be ignored.
- The last four bits of a supplied IP address will be matched.
-
An administrator created and applied an outbound Telnet extended ACL on a router to prevent router-initiated Telnet sessions. What is a consequence of this configuration?
- The ACL will not work as desired because an outbound ACL cannot block router-initiated traffic.
- The ACL will work as desired as long as it is applied to the correct interface.
- The ACL will not work because only standard ACLs can be applied to vty lines.
- The ACL will work as long as it will be applied to all vty lines.
-
A network administrator is testing IPv6 connectivity to a web server. The network administrator does not want any other host to connect to the web server except for the one test computer. Which type of IPv6 ACL could be used for this situation?
- only a standard ACL
- a standard or extended ACL
- only an extended ACL
- an extended, named, or numbered ACL
- only a named ACL
-
A college student is studying for the Cisco CCENT certification and is visualizing extended access lists. Which three keywords could immediately follow the keywords permit or deny as part of an extended access list? (Choose three.)
- www
- tcp
- udp
- icmp
- telnet
- ftp
-
Refer to the exhibit. The student on the H1 computer continues to launch an extended ping with expanded packets at the student on the H2 computer. The school network administrator wants to stop this behavior, but still allow both students access to web-based computer assignments. What would be the best plan for the network administrator?

- Apply an outbound extended ACL on R1 S0/0/1.
- Apply an outbound standard ACL on R2 S0/0/1.
- Apply an inbound standard ACL on R1 Gi0/0.
- Apply an inbound extended ACL on R2 Gi0/1.
- Apply an inbound extended ACL on R1 Gi0/0.
-
What best describes the operation of distance vector routing protocols?
- They use hop count as their only metric.
- They only send out updates when a new network is added.
- They send their routing tables to directly connected neighbors.
- They flood the entire network with routing updates.
-
Refer to the exhibit. Host A has sent a packet to host B. What will be the source MAC and IP addresses on the packet when it arrives at host B?
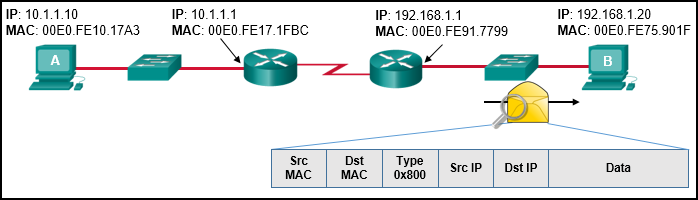
- Source MAC: 00E0.FE91.7799Source IP: 192.168.1.1
- Source MAC: 00E0.FE10.17A3
Source IP: 10.1.1.10 - Source MAC: 00E0.FE91.7799
Source IP: 10.1.1.10 - Source MAC: 00E0.FE10.17A3
Source IP: 192.168.1.1 - Source MAC: 00E0.FE91.7799
Source IP: 10.1.1.1
-
What is an advantage of using dynamic routing protocols instead of static routing?
- easier to implement
- more secure in controlling routing updates
- fewer router resource overhead requirements
- ability to actively search for new routes if the current path becomes unavailable
-
In a routing table which route can never be an ultimate route?
- parent route
- child route
- level one route
- level two route
-
What is meant by the term “best match” when applied to the routing table lookup process?
- network match
- supernet match
- exact match
- longest match
-
Refer to the exhibit. In the routing table entry, what is the administrative distance?
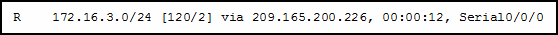
- 24
- 120
- 2
- 12
-
Which three advantages are provided by static routing? (Choose three.)
- Static routing does not advertise over the network, thus providing better security.
- Configuration of static routes is error-free.
- Static routes scale well as the network grows.
- Static routing typically uses less network bandwidth and fewer CPU operations than dynamic routing does.
- The path a static route uses to send data is known.
- No intervention is required to maintain changing route information.
-
Which type of static route typically uses the distance parameter in the ip route global configuration command?
- summary static route
- default static route
- floating static route
- standard static route
-
How will a router handle static routing differently if Cisco Express Forwarding is disabled?
- It will not perform recursive lookups.
- Serial point-to-point interfaces will require fully specified static routes to avoid routing inconsistencies.
- Ethernet multiaccess interfaces will require fully specified static routes to avoid routing inconsistencies.
- Static routes that use an exit interface will be unnecessary.
-
Refer to the exhibit. R1 was configured with the static route command ip route 209.165.200.224 255.255.255.224 S0/0/0 and consequently users on network 172.16.0.0/16 are unable to reach resources on the Internet. How should this static route be changed to allow user traffic from the LAN to reach the Internet?
- Add the next-hop neighbor address of 209.165.200.226.
- Change the exit interface to S0/0/1.
- Change the destination network and mask to 0.0.0.0 0.0.0.0.
- Add an administrative distance of 254.
-
How many classful networks are summarized by the static summary route ip route 192.168.32.0 255.255.248.0 S0/0/0?
- 2
- 4
- 8
- 16
-
A network administrator is implementing a distance vector routing protocol between neighbors on the network. In the context of distance vector protocols, what is a neighbor?
- routers that are reachable over a TCP session
- routers that share a link and use the same routing protocol
- routers that reside in the same area
- routers that exchange LSAs
-
What is associated with link-state routing protocols?
- low processor overhead
- poison reverse
- routing loops
- split horizon
- shortest-path first calculations
-
How is the router ID for an OSPFv3 router determined?
- the highest IPv6 address on an active interface
- the lowest MAC address on an active interface
- the highest IPv4 address on an active interface
- the highest EUI-64 ID on an active interface
-
An administrator attempts to change the router ID on a router that is running OSPFv3 by changing the IPv4 address on the router loopback interface. Once the IPv4 address is changed, the administrator notes that the router ID did not change. What two actions can the administrator take so that the router will use the new IPv4 address as the router ID? (Choose two.)
- Shut down and re-enable the loopback interface.
- Reboot the router.
- Copy the running configuration to NVRAM.
- Clear the IPv6 OSPF process.
- Disable and re-enable IPv4 routing.
-
Refer to the exhibit. Which would be chosen as the router ID of R2?
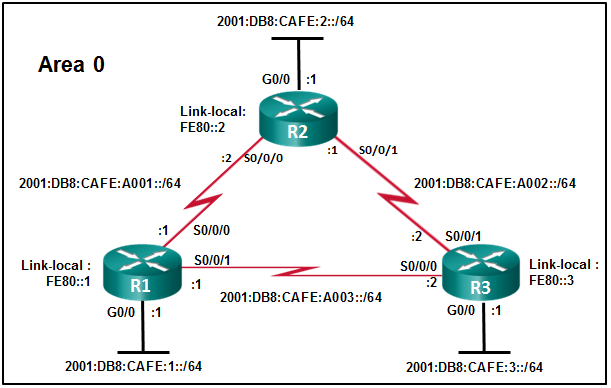
- 2001:DB8:CAFE:2::/64
- LLA: FE80::2
- 2001:DB8:CAFE:A001::/64
- The router ID has to be manually configured.
-
What does an OSPF area contain?
- routers that share the same router ID
- routers whose SPF trees are identical
- routers that have the same link-state information in their LSDBs
- routers that share the same process ID
-
What is the effect of entering the network 192.168.10.1 0.0.0.0 area 0 command in router configuration mode?
- The interface with the IPv4 address 192.168.10.1 will be a passive interface.
- OSPF advertisements will include the network on the interface with the IPv4 address 192.168.10.1.
- This command will have no effect because it uses a quad zero wildcard mask.
- OSPF advertisements will include the specific IPv4 address 192.168.10.1.
-
What is the order of packet types used by an OSPF router to establish convergence?
- Hello, LSAck, LSU, LSR, DBD
- LSAck, Hello, DBD, LSU, LSR
- Hello, DBD, LSR, LSU, LSAck
- LSU, LSAck, Hello, DBD, LSR
-
Refer to the exhibit. R1 and R2 are OSPFv3 neighbors. Which address would R1 use as the next hop for packets that are destined for the Internet?
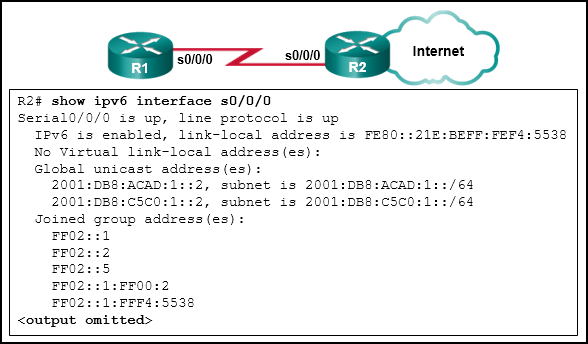
- FF02::5
- 2001:DB8:ACAD:1::2
- 2001:DB8:C5C0:1::2
- FE80::21E:BEFF:FEF4:5538
-
Refer to the exhibit. What address will be used as the router ID for the OSPFv3 process?
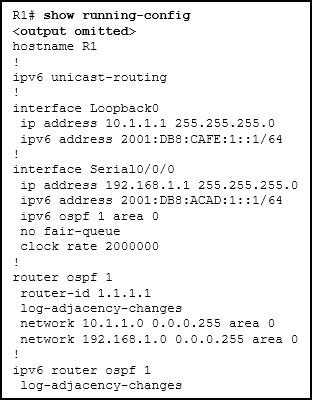
- 1.1.1.1
- 10.1.1.1
- 192.168.1.1
- 2001:DB8:CAFE:1::1
- 2001:DB8:ACAD:1::1
-
Which switching method provides error-free data transmission?
- fragment-free
- fast-forward
- integrity-checking
- store-and-forward
-
Which network design may be recommended for a small campus site that consists of a single building with a few users?
- a network design where the access and core layers are collapsed into a single layer
- a collapsed core network design
- a three-tier campus network design where the access, distribution, and core are all separate layers, each one with very specific functions
- a network design where the access and distribution layers are collapsed into a single layer
-
When does a switch use frame filtering?
- The destination MAC address is for a host on a different network segment from the source of the traffic.
- The destination MAC address is for a host on the same network segment as the source of the traffic.
- The destination MAC address is for a host with no entry in the MAC address table.
- The destination MAC address is for a host on a network supported by a different router.
-
Which command will verify the status of both the physical and the virtual interfaces on a switch?
- show running-config
- show ip interface brief
- show startup-config
- show vlan
-
Refer to the exhibit. A network administrator is investigating a lag in network performance and issues the show interfaces fastethernet 0/0 command. Based on the output that is displayed, what two items should the administrator check next? (Choose two.)
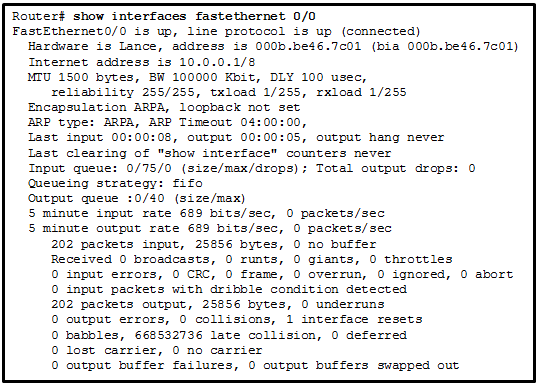
- cable lengths
- damaged cable termination
- duplex settings
- electrical interference
- incorrect cable types
-
Which command would be best to use on an unused switch port if a company adheres to the best practices as recommended by Cisco?
- shutdown
- ip dhcp snooping
- switchport port-security mac-address sticky
- switchport port-security violation shutdown
- switchport port-security mac-address sticky mac-address
-
Open the PT activity. Perform the tasks in the activity instructions and then answer the question.
Which ping command completed successfully?
- ping 192.168.25.7
- ping 192.168.25.8
- ping 192.168.25.9
- ping 192.168.25.10
-
Which two commands should be implemented to return a Cisco 3560 trunk port to its default configuration? (Choose two.)
- S1(config-if)# no switchport trunk allowed vlan
- S1(config-if)# no switchport trunk native vlan
- S1(config-if)# switchport mode dynamic desirable
- S1(config-if)# switchport mode access
- S1(config-if)# switchport access vlan 1
-
Which two methods can be used to provide secure management access to a Cisco switch? (Choose two.)
- Configure all switch ports to a new VLAN that is not VLAN 1.
- Configure specific ports for management traffic on a specific VLAN.
- Configure SSH for remote management.
- Configure all unused ports to a “black hole.”
- Configure the native VLAN to match the default VLAN.
-
Refer to the exhibit. A network administrator is configuring inter-VLAN routing on a network. For now, only one VLAN is being used, but more will be added soon. What is the missing parameter that is shown as the highlighted question mark in the graphic?
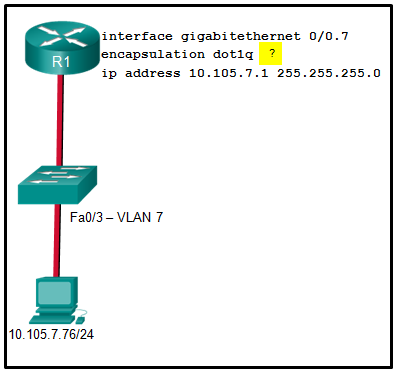
- It identifies the subinterface.
- It identifies the VLAN number.
- It identifies the native VLAN number.
- It identifies the type of encapsulation that is used.
- It identifies the number of hosts that are allowed on the interface.
-
Refer to the exhibit. A Layer 3 switch routes for three VLANs and connects to a router for Internet connectivity. Which two configurations would be applied to the switch? (Choose two.)
-
(config)# interface gigabitethernet 1/1
(config-if)# no switchport
(config-if)# ip address 192.168.1.2 255.255.255.252
- (config)# interface vlan 1
(config-if)# ip address 192.168.1.2 255.255.255.0
(config-if)# no shutdown - (config)# interface gigabitethernet1/1
(config-if)# switchport mode trunk - (config)# interface fastethernet0/4
(config-if)# switchport mode trunk - (config)# ip routing
-
-
Fill in the blank.
Using router-on-a-stick inter-VLAN routing, how many subinterfaces have to be configured to support 10 VLANs?
- 10
-
Refer to the exhibit. Inter-VLAN communication between VLAN 10, VLAN 20, and VLAN 30 is not successful. What is the problem?
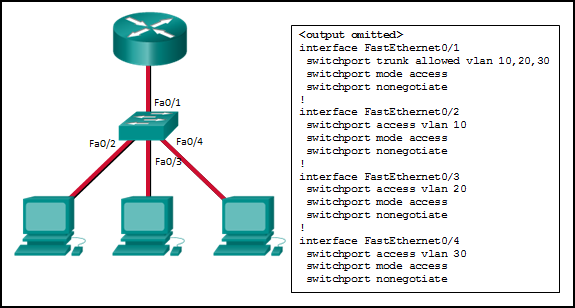
- The access interfaces do not have IP addresses and each should be configured with an IP address.
- The switch interface FastEthernet0/1 is configured as an access interface and should be configured as a trunk interface.
- The switch interface FastEthernet0/1 is configured to not negotiate and should be configured to negotiate.
- The switch interfaces FastEthernet0/2, FastEthernet0/3, and FastEthernet0/4 are configured to not negotiate and should be configured to negotiate.
-
When routing a large number of VLANs, what are two disadvantages of using the router-on-a-stick inter-VLAN routing method rather than the multilayer switch inter-VLAN routing method? (Choose two.)
- Multiple SVIs are needed.
- A dedicated router is required.
- Router-on-a-stick requires subinterfaces to be configured on the same subnets.
- Router-on-a-stick requires multiple physical interfaces on a router.
- Multiple subinterfaces may impact the traffic flow speed.
-
Which two statements are characteristics of routed ports on a multilayer switch? (Choose two.)
- They are not associated with a particular VLAN.
- The interface vlan <vlan number> command has to be entered to create a VLAN on routed ports.
- They support subinterfaces, like interfaces on the Cisco IOS routers.
- They are used for point-to-multipoint links.
- In a switched network, they are mostly configured between switches at the core and distribution layers.
-
Fill in the blank.
Do not use abbreviations.
The duplex full command configures a switch port to operate in the full-duplex mode. -
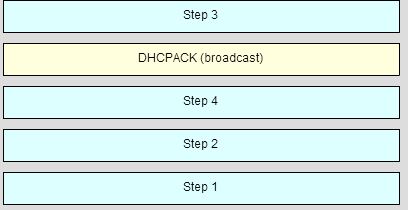
Order the DHCP process steps. (Not all options are used.)
-
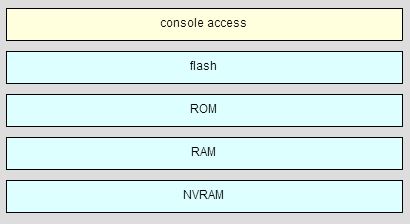
Match the router memory type that provides the primary storage for the router feature. (Not all options are used.)
-
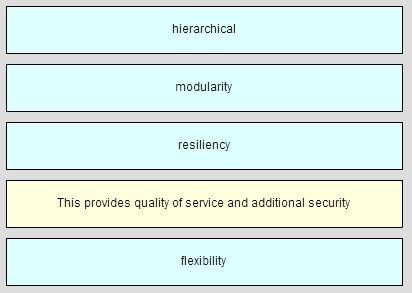
Match each borderless switched network principle to its description. (Not all options are used.)