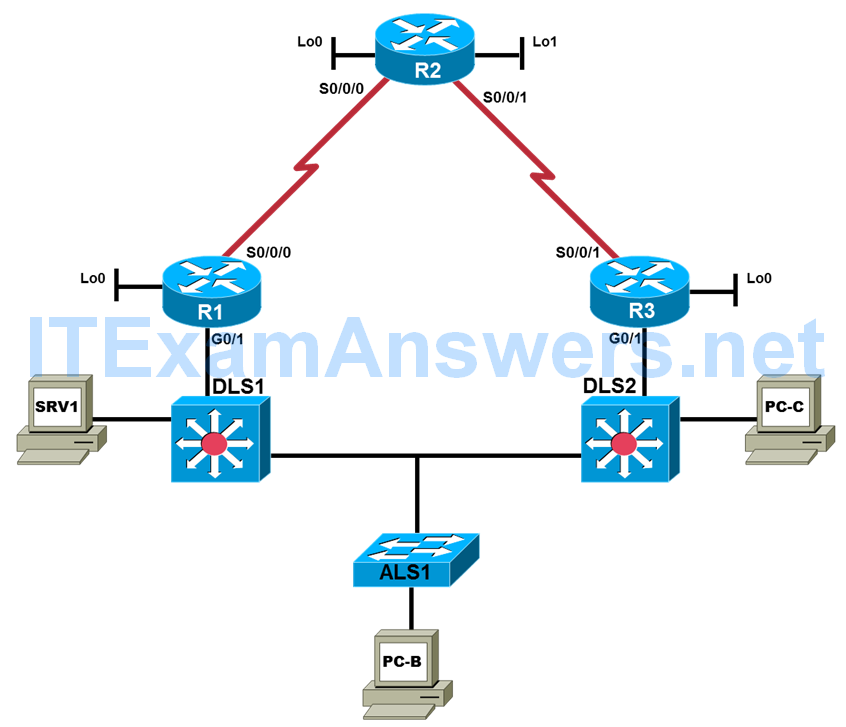
Topology

Objectives
- Assign responsibility for a device or set of devices to team members (optional).
- Load the baseline configuration for each device in the topology.
- Use available tools to document key device configuration parameters, such as the interfaces in use, IP addressing, routing protocols, VLANs, logging mechanisms, and security measures.
- Document the physical topology to support future troubleshooting tasks.
- Document the logical topology to support future troubleshooting tasks.
Background
You have been employed as a network engineering consultant by a company that has made a recent acquisition. The documentation for the acquired company’s network is incomplete and outdated, so you need to inventory their network architecture both logically and physically, per company documentation standards. This will help you learn about the design and implementation of their network and ensure that you have access to up-to-date and accurate network documentation to reference during future troubleshooting procedures. One directive to your predecessor was to transition access layer switches to multilayer switches, so static routing is implemented on the access layer switches until new multilayer switches are procured.
In this lab, you survey the baseline TSHOOT network. No problems are introduced in this lab. The TSHOOT network will evolve over time as changes and enhancements are made. You will analyze and document the current topology and device configuration parameters to develop familiarity with the baseline configurations and network connections. You will review and fill out the provided documentation as you analyze the network. You will assess and assemble tools that can be used for future maintenance and troubleshooting tasks.
Note: This lab uses Cisco ISR G2 routers running Cisco IOS 15.4(3) images with IP Base and Security packages enabled, and Cisco Catalyst 3560 and 2960 switches running Cisco IOS 15.0(2) IP Services and LAN Base images, respectively. The switches have Fast Ethernet interfaces, so the routing metrics for all Ethernet links in the labs are calculated based on 100 Mb/s, although the routers have Gigabit Ethernet interfaces. The 3560 and 2960 switches are configured with the SDM templates dual-ipv4-and-ipv6 routing and lanbase-routing, respectively. Depending on the router or switch model and Cisco IOS Software version, the commands available and output produced might vary from what is shown in this lab. Catalyst 3650 switches (running any Cisco IOS XE release) and Catalyst 2960-Plus switches (running any supported Cisco IOS image) can be used in place of the Catalyst 3560 switches and the Catalyst 2960 switches.
Required Resources
- 3 routers (Cisco IOS Release 15.4 or comparable)
- 2 multilayer switches and 1 access layer switch (Cisco IOS Release 15.0(2) or comparable with Fast Ethernet interfaces)
- SRV1 (PC with static IP address): Windows 7 with RADIUS, TFTP, and syslog servers, plus an SSH client, SNMP monitor, and WireShark.
- PC-B (DHCP client): Windows 7 with SSH client and WireShark software
- PC-C (DHCP client): Windows 7 with SSH client and WireShark software
- Serial and Ethernet cables, as shown in the topology
- Rollover cables to configure the routers and switches via the console
Task 1: Assign Responsibility for Each Device (optional)
Step 1: Review the lab topology together with your team members.
Step 2: Assign responsibility for each device to a team member.
a. The team member who has primary responsibility for a device is in control of the console of that device and changes to that device. No other team member should access the console, make changes to the device, or execute disruptive actions, such as reloading or debugging, without permission from the responsible team member.
b. All team members can access all devices via Telnet or SSH for non-disruptive diagnostic action without permission of the responsible team member. Responsibilities can be reassigned during later labs if necessary.
c. If working in teams, document responsibilities in the Device Responsibilities table.
Device Responsibilities Table
| Device | Description | Responsible Team Member |
| R1 | Core Router 1 | |
| R2 | ISP Router | |
| R3 | Core Router 2 | |
| ALS1 | Access Layer Switch 1 | |
| DLS1 | Distribution Layer Switch 1 | |
| DLS2 | Distribution Layer Switch 2 | |
| SRV1 | TFTP, syslog, SNMP | |
| PC-B | User PC | |
| PC-C | User PC |
Task 2: Load the Baseline Device Configuration Files
Use the following procedure on each device in the network to load the baseline configuration. The procedure shown here is for a switch, but it is very similar to that of a router.
Note: The configuration files for this lab include ip host name ip-addr entries for all devices. This can be helpful in accessing devices using Telnet with this lab. The ip host entries are only provided in this BASE lab, as the device IP addresses will change in subsequent labs.
Step 1: Verify the existence and location of the lab configuration files.
The course lab configuration files for a particular device should be in flash under the tshoot directory. Use the show flash command to verify the presence of this directory. You can also verify the contents of the directory using the cd and dir commands. If the directory and files are not present, contact your instructor.
Note: When the show flash command is used on a switch, it lists the directories and files at the root directory but not the files within the directories. The following example uses the cd and dir commands on switch ALS1.
ALS1# show flash
Directory of flash:/
9 -rwx 916 Feb 28 1993 16:04:03 -08:00 vlan.dat
3 drwx 512 Sep 22 2014 10:40:59 -07:00 tshoot
5 -rwx 11792247 Feb 28 1993 16:24:48 -08:00 c2960-lanbasek9-mz.150-2.SE6.bin
6 -rwx 7192 Sep 26 2014 10:53:31 -07:00 multiple-fs
7 -rwx 106 Feb 28 1993 18:13:09 -08:00 info
8 -rwx 1906 Sep 26 2014 10:53:31 -07:00 private-config.text
10 -rwx 7199 Sep 26 2014 10:53:31 -07:00 config.text
27998208 bytes total (16070656 bytes free)
ALS1# cd tshoot
ALS1# dir
Directory of flash:/tshoot/
9 -rwx 7979 Sep 22 2014 11:26:14 -07:00 BASE-ALS1-Cfg.txt
Alternatively, you can see the contents of the directory by specifying its name using the dir command. For example:
ALS1# cd
ALS1# pwd
flash:
ALS1# dir flash:/tshoot
Directory of flash:/tshoot/
9 -rwx 7979 Sep 22 2014 11:26:14 -07:00 BASE-ALS1-Cfg.txt
<output omitted>
Note: When the show flash command is used on a router, it lists the directories and the files within them. The following example uses only the show flash command on router R1. The tshoot directory and its contents are listed.
R1# show flash: -#- --length-- -----date/time------ path 1 103727964 Sep 18 2014 05:20:10 -07:00 c2900-universalk9-mz.SPA.154-3.M.bin 2 2857 Feb 22 2014 01:01:52 -08:00 pre_autosec.cfg 3 0 Sep 22 2014 11:39:18 -07:00 tshoot 4 3887 Sep 22 2014 11:42:20 -07:00 tshoot/BASE-R1-Cfg.txt
Step 2: Erase startup-config from NVRAM, and then reset the SDM template.
ALS1# erase startup-config
Erasing the nvram filesystem will remove all configuration files! Continue? [confirm]
[OK]
Erase of nvram: complete
ALS1#
Sep 26 22:00:26.222: %SYS-7-NV_BLOCK_INIT: Initialized the geometry of nvram
ALS1# configure terminal
Enter configuration commands, one per line. End with CNTL/Z.
ALS1(config)# sdm prefer lanbase-routing
ALS1(config)#
Sep 26 22:00:45.155: %PARSER-5-CFGLOG_LOGGEDCMD: User:console logged command:sdm prefer lanbase-routing
ALS1(config)# exit
ALS1#
Sep 26 22:00:48.393: %SYS-5-CONFIG_I: Configured from console by console
ALS1# show sdm prefer
The current template is "lanbase-routing" template.
The selected template optimizes the resources in
the switch to support this level of features for
0 routed interfaces and 255 VLANs.
number of unicast mac addresses: 4K
number of IPv4 IGMP groups + multicast routes: 0.25K
number of IPv4 unicast routes: 4.25K
number of directly-connected IPv4 hosts: 4K
number of indirect IPv4 routes: 256
number of IPv6 multicast groups: 0.375k
number of IPv6 unicast routes: 1.25K
number of directly-connected IPv6 addresses: 0.75K
number of indirect IPv6 unicast routes: 448
number of IPv4 policy based routing aces: 0
number of IPv4/MAC qos aces: 0.125k
number of IPv4/MAC security aces: 0.375k
number of IPv6 policy based routing aces: 0
number of IPv6 qos aces: 0.375k
number of IPv6 security aces: 127
Note: For a 3560 switch, use the “dual-ipv4-and-ipv6 routing” template. If using another type of Cisco switch, choose an SDM template that supports IPv4/IPv6 routing and IPv4/IPv6 ACEs. The SDM setting reverts to the “default” template on a 2960 and the “desktop default” template on the 3560 after deleting startup-config, so it is important to change the SDM template setting after deleting startup-config. Most time-stamped logging messages, as seen in the output above, will be removed from the lab outputs going forward.
Step 3: Delete the VLAN database from flash (switches only).
ALS1# delete vlan.dat Delete flash:/vlan.dat? [confirm]
Step 4: Reload the device, but do not save the system configuration if prompted.
ALS1# reload System configuration has been modified. Save? [yes/no]: no Proceed with reload? [confirm]
Step 5: When the device restarts, do not enter the initial configuration dialog.
Press RETURN to get started!
--- System Configuration Dialog ---
Enable secret warning
----------------------------------
In order to access the device manager, an enable secret is required
If you enter the initial configuration dialog, you will be prompted for the enable secret
If you choose not to enter the intial configuration dialog, or if you exit setup without setting the enable secret,
please set an enable secret using the following CLI in configuration mode-
enable secret 0 <cleartext password>
----------------------------------
Would you like to enter the initial configuration dialog? [yes/no]: no
Note: On some platform/IOS combinations, a message appears after choosing not to enter the initial configuration dialog, asking whether or not to “terminate autoinstall”. If this message appears, enter yes to terminate autoinstall.
Step 6: Copy the specified lab device configuration file from flash to running-config.
Switch> enable Switch# copy flash:/tshoot/BASE-ALS1-Cfg.txt running-config Destination filename [running-config]?
Note: Although it is possible to copy the file to startup-config and reload the device, the RSA keys for SSH cannot be generated from the startup-config file. The device configuration files loaded from flash contain commands that remove any existing keys and create new keys.
It is also possible to cut-and-paste the
Step 7: Copy the running config to the startup config.
Depending on the platform/IOS combination, AUTOSAVE may automatically save a copy of running-config to NVRAM for startup. AUTOSAVE does not copy the console line and vty line configurations from running-config to startup-config. To ensure that the startup configuration is complete, manually copy:
ALS1# copy running-config startup-config Building configuration... [OK]
Note: If the device is rebooted at this point, you can log in with the username cisco and the password cisco. To access privileged EXEC mode, use the enable secret: cisco.
Step 8: Repeat Steps 1 through 7 for the other devices in the network.
Step 9: Configure the PCs.
a. Configure SRV1 with the static IPv4 address 10.1.100.1/24 and default gateway 10.1.100.254 (on DLS1). Configure SRV1 with the static IPv6 address 2001:DB8:CAFE:100::1 and default gateway 2001:DB8:CAFE:100::D1 (on DLS1).
b. Configure PC-B and PC-C as DHCP clients for both IPv4 and IPv6.
Note: Make sure the PC’s learn addresses of the form 2001:DB8:CAFE:x:ABCD:u:v:w where x is the VLAN for the respective PC. Use ipconfig/release6 followed by ipconfig/renew6 to release and renew the stateful IPv6 data. If necessary, reset the NIC. The SVI commands for VLANs 110, 120, and 200,
ipv6 nd prefix 2001:DB8:CAFE:x::/64 no-autoconfig ipv6 nd managed-config-flag
set the IPv6 RA M, O, and A flags so that the Windows 7 stateful DHCPv6 clients populate a singular GUA and appropriate link-local default routes, as seen in the ipconfig and route print outputs.
Step 10: Test basic network connectivity between devices.
a. Ping from PC-B to SRV1 at 10.1.100.1 and 2001:DB8:CAFE:100::1. Were the pings successful?
_________________________________________________________________
b. Ping from ALS1 to R2 Lo1 at 2.2.2.2 and 2001:DB8:EFAC::2. Were the pings successful?
_________________________________________________________________
Note: If the pings are not successful, contact your instructor.
Task 3: Analyze and Document the Physical Lab Topology
Note: At this time, only examine and document the physical connections. Documenting the logical topology, such as subnets, IP addresses, and routing protocols, is addressed in Task 4 of this lab.
Step 1: Review the physical topology diagram on page 1 of the lab.
Step 2: Use Cisco Discovery Protocol and show commands to verify the Layer 1 and Layer 2 connections of the lab topology.
a. Use the show cdp command to discover the interfaces associated with the physical connections. Fill in the correct device and interface designators in the following Device Links table and label them on the physical topology diagram on the first page of the lab.
b. Review the configurations of the devices for using Layer 1 and Layer 2 features, such as trunks and EtherChannels. Fill in the information in the Device Links table and add it to the diagram. If a link is accounted for from one device to another, it is not necessary to repeat the entry from the other device. The first entry for ALS1, interface F0/1 is filled in as an example.
Which other commands could you use to identify Layer 1 and Layer 2 characteristics?
_________________________________________________________________
Device Links Table
| From Device | Interface | To Device | Interface | Layer 1 and 2 Features and Protocols Used |
|---|---|---|---|---|
| ALS1 | F0/1 | DLS1 | F0/1 | EtherChannel Po1, 802.1Q |
c. Verify that all physical links shown in the diagram are operational. Which commands did you use?
____________________________________________________________________
Step 3: Map the VLANs used in the lab to the devices in the diagram.
Fill in the VLAN Definition table and label the physical topology diagram with the VLANs used for this topology. Identify all host devices that are members of each VLAN. The first entry for VLAN 99 is filled in as an example.
VLAN Definition Table
| VLAN # | Name | Description | VLAN Members |
|---|---|---|---|
| 99 | MANAGEMENT | Management VLAN | ALS1, DLS1, DLS2 |
Step 4: Analyze spanning tree for the Layer 2 switched domain.
a. Analyze the spanning tree characteristics of the Layer 2 switched portion of the network. Which type of spanning-tree mode is implemented?
_________________________________________________________________
b. Which switch is the root switch for each VLAN, and what are the configured spanning-tree priorities?
_________________________________________________________________
c. What is the resulting spanning-tree topology for VLANs that have client devices connected?
_________________________________________________________________
d. Which commands did you use to analyze the spanning-tree characteristics?
_________________________________________________________________
Step 5: Diagram the spanning tree for VLAN 120.
a. Label the STP role and port status for each port channel used in the physical topology diagram below.
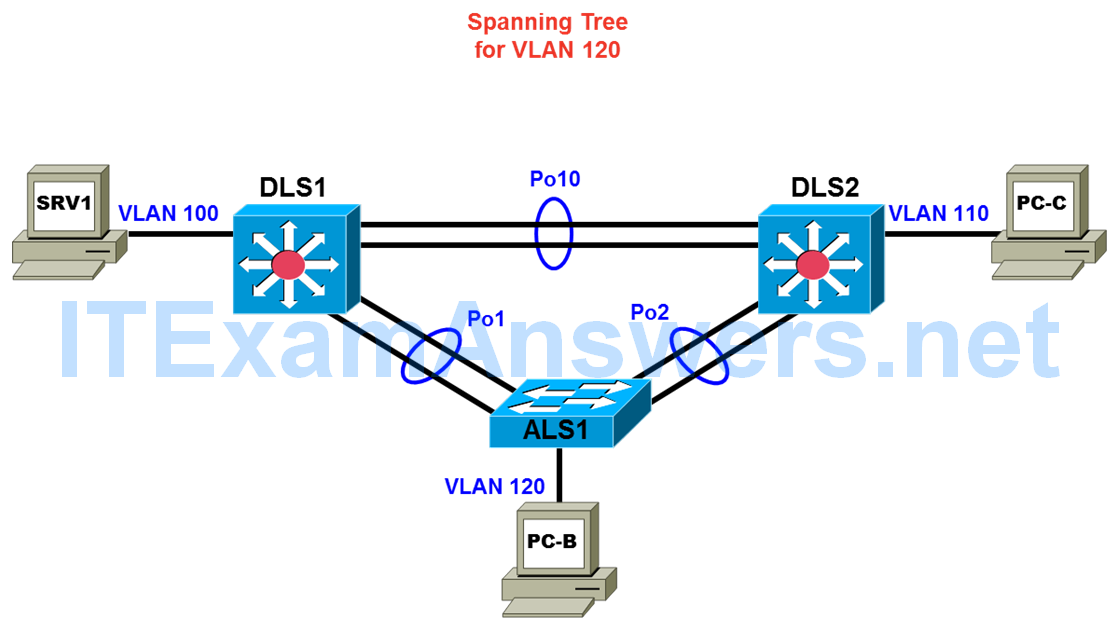
b. If working as a team, discuss your findings with your teammates to ensure that all team members understand the physical and data link aspects of the network design.
Student Notes
Use this space to make any additional notes regarding the physical configuration and the commands used.
__________________________________________________________________
Task 4: Analyze and Document the Logical Lab Topology
Step 1: Review the logical lab diagram and the subnets.
Review the IP subnets in the Subnet table for the VLANs and WAN links that are used in the lab network. Router interface designations from the physical topology diagram are provided in two copies of the logical topology, one to be used for IPv4 data and one for IPv6 data.
Subnet Table
| Description | IPv4 Subnet | IPv6 Prefix | Devices |
| VLANs | |||
| Management VLAN 99 | 10.1.99.0/24 | 2001:DB8:CAFE:99::/64 | ALS1,DLS1,DLS2 |
| Servers VLAN 100 | 10.1.100.0/24 | 2001:DB8:CAFE:100::/64 | SRV1 |
| Guest VLAN 110 | 10.1.110.0/24 | 2001:DB8:CAFE:110::/64 | PC-C |
| Office VLAN 120 | 10.1.120.0/24 | 2001:DB8:CAFE:120::/64 | PC-B |
| Management VLAN | 10.1.99.0/24 | 2001:DB8:CAFE:200::/64 | ALS1, DLS1, DLS2 |
| WAN Links | |||
| DLS1 – R1 | 10.1.2.0/30 | 2001:DB8:CAFE:20::/64 | DLS1 and R1 GE link |
| DLS2 – R3 | 10.1.2.12/30 | 2001:DB8:CAFE:212::/64 | DLS2 and R3 GE link |
| R1 – R2 | 10.1.1.0/30 | 2001:DB8:CAFE:10::/64 | R1 and R2 serial link |
| R2 – R3 | 10.1.1.4/30 | 2001:DB8:CAFE:14::/64 | R2 and R3 serial link |
Step 2: Map the subnet scheme to the logical diagram.
In the previous step, the subnets were documented in the Subnet table. Now document the host portion of the addresses. To document the host part, research the routing tables and interface IP addresses of all the devices. Document the interface IPv4 and IPv6 addresses in the IP Address table and on the associated logical topology diagram. Use only the number of the last octet for IPv4 addresses and the last hextet for IPv6 addresses in the respective diagrams. The device names and interfaces are listed to help identify the IP addresses. The entry for ALS1 VLAN 99 is shown as an example. If an interface is not in use, indicate this in the Additional Information column. Account for all physical and virtual interfaces.
IP Address Table
| Device Name | Interface | IPv4 Address/Prefix | IPv6 Address/Prefix | Additional Information |
|---|---|---|---|---|
| ALS1 | Vlan 99 | 10.1.99.251/24 | 2001:DB8:CAFE:99::A1/64 | SVI |
| ALS1 | Vlan 110 | |||
| ALS1 | Vlan 120 | |||
| ALS1 | Vlan 200 | |||
| DLS1 | Vlan 99 | |||
| DLS1 | Vlan 100 | |||
| DLS1 | Vlan 110 | |||
| DLS1 | Vlan 120 | |||
| DLS1 | Vlan 200 | |||
| DLS1 | F0/5 | |||
| DLS2 | Vlan 99 | |||
| DLS2 | Vlan 100 | |||
| DLS2 | Vlan 110 | |||
| DLS2 | Vlan 120 | |||
| DLS2 | Vlan 200 | |||
| DLS2 | F0/5 | |||
| R1 | G0/0 | |||
| R1 | G0/1 | |||
| R1 | S0/0/0 | |||
| R1 | S0/0/1 | |||
| R1 | Loopback 0 | |||
| R2 | G0/0 | |||
| R2 | G0/1 | |||
| R2 | S0/0/0 | |||
| R2 | S0/0/1 | |||
| R2 | Loopback 0 | |||
| R2 | Loopback 1 | |||
| R3 | G0/0 | |||
| R3 | G0/1 | |||
| R3 | S0/0/0 | |||
| R3 | S0/0/1 | |||
| R3 | Loopback 0 | |||
| SRV1 | NIC | |||
| PC-B | NIC | |||
| PC-C | NIC |
Step 3: Analyze and document control plane logical configuration features.
Analyze the configurations of the devices for control plane features such as routing protocols, First Hop Redundancy Protocols (FHRPs), dynamic host configuration protocol (DHCP), and network address translation (NAT). Review, document, and discuss the following aspects of the logical network configuration.
a. Is dynamic or static routing being used?
_____________________________________________________________
b. If dynamic, which routing protocol?
_____________________________________________________________
c. Are FHRPs in use, such as the Hot Standby Router Protocol (HSRP), Virtual Router Redundancy Protocol (VRRP), or Gateway Load Balancing Protocol (GLBP)? If yes, which one?
_____________________________________________________________
d. What is the active router for all relevant VLANs?
_____________________________________________________________
e. From the PC-B command prompt, issue the tracert command to router R2 Lo0 at 10.1.202.1 for IPv4 and 2001:DB8:CAFE:202:2 for IPv6. What path did the packets take in each case?
_____________________________________________________________
f. Are any access lists used to filter traffic on the network? If yes, describe their function.
_____________________________________________________________
g. Is DHCP in use? If yes, which DHCP server is used and for which VLANs present in the logical topology diagram?
_____________________________________________________________
h. How does ALS1 send ICMP echo requests to SRV1 in VLAN 100, when ALS1 has no VLAN 100?
_____________________________________________________________
i. If working as a team, discuss your findings with your teammates to ensure that all team members understand the high-level design of the network.
Notes
Use this space to make any additional notes regarding the logical configuration and the commands used.
___________________________________________________________________
Task 5: Identify Troubleshooting and Maintenance Tools
Step 1: Analyze device configurations for troubleshooting and maintenance features.
Analyze the configurations of the devices for services that support troubleshooting and maintenance, such as syslog, Simple Network Management Protocol (SNMP), and other network management features.
Step 2: Document the troubleshooting and maintenance features.
a. Document the troubleshooting and maintenance applications or tools in use with the network devices in the Troubleshooting and Maintenance Tools table. An entry for system logging is provided as an example.
Troubleshooting and Maintenance Tools Table
| Configured Feature | Devices | Target Server | Target Tool or Application |
|---|---|---|---|
| System message logging | All | SRV1 | Syslog server |
b. If working as a team, discuss your findings with your teammates to ensure that all team members know which maintenance and troubleshooting tools are available in the network.
Notes
Use this space to make any additional notes regarding troubleshooting and maintenance applications or tools.
______________________________________________________________
Task 6: Identify the Security Measures Implemented
Step 1: Analyze device configurations for security-related features.
Analyze the configurations of your assigned devices for configuration options that help support a more secure network implementation, such as password security, login authentication, secure remote management, switch trunk and access port security, and VLANs. Record your entries in the Security Features table. An entry for password security is provided as an example.
Security Features Table
| Security Feature Configured | Implementation Method or Commands |
|---|---|
| Password security | Enable secret, password encryption |
Notes
Use this space to make any additional notes regarding security measures.
_________________________________________________________________
Note: Configuration command sequences for all devices are provided at the end of the lab. These are not outputs resulting from entering the show running-config command. Only the non-default commands used to configure the devices are included (along with no shutdown on appropriate interfaces).
Lab Debrief Notes
Use this space to make notes regarding the key concepts learned during the lab debrief discussions with your instructor. This may include alternate solutions, methods, and processes; this may include procedure and communication improvements; and this may include key commands and tools.
Note: This is your primary opportunity to document a baseline of the lab network before starting the troubleshooting exercises. During the debrief session, ask your instructor for clarification of any aspects of the network design and configurations that are unclear.
__________________________________________________________________
Device Configurations
Switch ALS1
!BASE ALS1 Config ! service timestamps debug datetime msec service timestamps log datetime msec service password-encryption ! hostname ALS1 ! logging buffered 16384 enable secret cisco ! username cisco secret cisco aaa new-model ! ! aaa authentication login default local aaa authentication login CONSOLE none aaa authorization exec default local ! ! clock timezone PST -8 clock summer-time PDT recurring system mtu routing 1500 vtp domain TSHOOT vtp mode transparent ip routing ! ! no ip domain-lookup ip domain-name tshoot.net ip host R1 10.1.2.2 10.1.1.1 10.1.201.1 ip host R2 10.1.1.2 10.1.1.6 10.1.202.1 ip host R3 10.1.1.5 10.1.2.14 10.1.203.1 ip host ALS1 10.1.99.1 ip host DLS1 10.1.99.252 10.1.2.1 ip host DLS2 10.1.99.253 10.1.2.13 ipv6 unicast-routing ! errdisable recovery cause psecure-violation errdisable recovery interval 120 ! spanning-tree mode rapid-pvst spanning-tree portfast default spanning-tree extend system-id ! vlan 99 name MANAGEMENT ! vlan 110 name GUEST ! vlan 120 name OFFICE ! vlan 200 name VOICE ! vlan 666 name NATIVE ! vlan 999 name PARKING_LOT ! ip telnet source-interface Vlan99 ip ssh source-interface Vlan99 ! ! interface Port-channel1 description Channel to DLS1 switchport trunk native vlan 666 switchport trunk allowed vlan 99,110,120,200 switchport mode trunk switchport nonegotiate no shutdown ! interface Port-channel2 description Channel to DLS2 switchport trunk native vlan 666 switchport trunk allowed vlan 99,110,120,200 switchport mode trunk switchport nonegotiate no shutdown ! interface FastEthernet0/1 description Channel to DLS1 switchport trunk native vlan 666 switchport trunk allowed vlan 99,110,120,200 switchport mode trunk switchport nonegotiate channel-group 1 mode on no shutdown ! interface FastEthernet0/2 description Channel to DLS1 switchport trunk native vlan 666 switchport trunk allowed vlan 99,110,120,200 switchport mode trunk switchport nonegotiate channel-group 1 mode on no shutdown ! interface FastEthernet0/3 description Channel to DLS2 switchport trunk native vlan 666 switchport trunk allowed vlan 99,110,120,200 switchport mode trunk switchport nonegotiate channel-group 2 mode on no shutdown ! interface FastEthernet0/4 description Channel to DLS2 switchport trunk native vlan 666 switchport trunk allowed vlan 99,110,120,200 switchport mode trunk switchport nonegotiate channel-group 2 mode on no shutdown ! interface FastEthernet0/5 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/6 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/7 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/8 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/9 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/10 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/11 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/12 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/13 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/14 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/15 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/16 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/17 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/18 description To PC-B switchport access vlan 120 switchport mode access switchport voice vlan 200 switchport port-security maximum 3 switchport port-security switchport port-security mac-address sticky spanning-tree portfast no shutdown ! interface FastEthernet0/19 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/20 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/21 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/22 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/23 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/24 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface GigabitEthernet0/1 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface GigabitEthernet0/2 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface Vlan1 no ip address shutdown ! interface Vlan99 ip address 10.1.99.251 255.255.255.0 ipv6 address FE80::A1 link-local ipv6 address 2001:DB8:CAFE:99::A1/64 no shutdown ! interface Vlan110 ip address 10.1.110.251 255.255.255.0 ipv6 address FE80::A1 link-local ipv6 address 2001:DB8:CAFE:110::A1/64 ipv6 nd prefix 2001:DB8:CAFE:110::/64 no-autoconfig ipv6 nd managed-config-flag no shutdown ! interface Vlan120 ip address 10.1.120.251 255.255.255.0 ipv6 address FE80::A1 link-local ipv6 address 2001:DB8:CAFE:120::A1/64 ipv6 nd prefix 2001:DB8:CAFE:120::/64 no-autoconfig ipv6 nd managed-config-flag no shutdown ! interface Vlan200 ip address 10.1.200.251 255.255.255.0 ipv6 address FE80::A1 link-local ipv6 address 2001:DB8:CAFE:200::A1/64 ipv6 nd prefix 2001:DB8:CAFE:200::/64 no-autoconfig ipv6 nd managed-config-flag no shutdown ! crypto key gen rsa general-keys modulus 1024 ! no ip http server no ip http secure-server ip route 0.0.0.0 0.0.0.0 10.1.99.254 logging source-interface Vlan99 logging host 10.1.100.1 ipv6 route ::/0 2001:DB8:CAFE:99::D1 ! snmp-server community cisco RO snmp-server community san-fran RW snmp-server trap-source Vlan99 snmp-server location TSHOOT Lab Facility snmp-server contact [email protected] snmp-server enable traps vtp snmp-server enable traps vlancreate snmp-server enable traps vlandelete snmp-server enable traps port-security snmp-server enable traps vlan-membership snmp-server host 10.1.100.1 version 2c cisco ! ! banner motd ^*** BASE ALS1 Config ***^ ! ipv6 access-list REMOTEv6 deny ipv6 any any ! line con 0 exec-timeout 0 0 logging synchronous login authentication CONSOLE line vty 0 4 exec-timeout 0 0 ipv6 access-class REMOTEv6 in logging synchronous length 0 transport input telnet ssh ! ntp source Vlan99 ntp server 10.1.202.1 ! archive log config logging enable logging size 50 notify syslog contenttype plaintext hidekeys path tftp://10.1.100.1/$h-archive-config file prompt quiet ! end !
Switch DLS1
!BASE DLS1 Config ! service timestamps debug datetime msec service timestamps log datetime msec service password-encryption ! hostname DLS1 ! ! logging buffered 16384 enable secret cisco ! username cisco secret cisco aaa new-model ! ! aaa authentication login default local aaa authentication login CONSOLE none aaa authorization exec default local ! ! clock timezone PST -8 clock summer-time PDT recurring system mtu routing 1500 vtp domain TSHOOT vtp mode transparent ip routing no ip domain-lookup ip domain-name tshoot.net ip host R1 10.1.2.2 10.1.1.1 10.1.201.1 ip host R2 10.1.1.2 10.1.1.6 10.1.202.1 ip host R3 10.1.1.5 10.1.2.14 10.1.203.1 ip host ALS1 10.1.99.251 ip host DLS1 10.1.99.252 10.1.2.1 ip host DLS2 10.1.99.253 10.1.2.13 ! ip dhcp excluded-address 10.1.120.251 10.1.120.254 ip dhcp excluded-address 10.1.200.251 10.1.200.254 ip dhcp excluded-address 10.1.110.251 10.1.110.254 ! ip dhcp pool VOICE network 10.1.200.0 255.255.255.0 default-router 10.1.200.254 ! ip dhcp pool GUEST network 10.1.110.0 255.255.255.0 default-router 10.1.110.254 ! ip dhcp pool OFFICE network 10.1.120.0 255.255.255.0 default-router 10.1.120.254 ! ! ipv6 unicast-routing ipv6 dhcp pool DHCPv6OFFICE address prefix 2001:DB8:CAFE:120:ABCD::/80 domain-name tshoot.net ! ipv6 dhcp pool DHCPv6VOICE address prefix 2001:DB8:CAFE:200:ABCD::/80 domain-name tshoot.net ! ipv6 dhcp pool DHCPv6GUEST address prefix 2001:DB8:CAFE:110:ABCD::/80 domain-name tshoot.net ! ! errdisable recovery cause bpduguard ! spanning-tree mode rapid-pvst spanning-tree extend system-id spanning-tree vlan 99,110,120 priority 24576 spanning-tree vlan 100,200 priority 28672 ! ! vlan 99 name MANAGEMENT ! vlan 100 name SERVERS ! vlan 110 name GUEST ! vlan 120 name OFFICE ! vlan 200 name VOICE ! vlan 666 name NATIVE ! vlan 999 name PARKING_LOT ! ip telnet source-interface Vlan99 ip ssh source-interface Vlan99 ! ! interface Port-channel1 description Channel to ALS1 switchport trunk encapsulation dot1q switchport trunk native vlan 666 switchport trunk allowed vlan 99,110,120,200 switchport mode trunk switchport nonegotiate no shutdown ! interface Port-channel10 description Channel to DLS2 switchport trunk encapsulation dot1q switchport trunk native vlan 666 switchport trunk allowed vlan 99,100,110,120,200 switchport mode trunk switchport nonegotiate no shutdown ! interface FastEthernet0/1 description Channel to ALS1 switchport trunk encapsulation dot1q switchport trunk native vlan 666 switchport trunk allowed vlan 99,110,120,200 switchport mode trunk switchport nonegotiate channel-group 1 mode on no shutdown ! interface FastEthernet0/2 description Channel to ALS1 switchport trunk encapsulation dot1q switchport trunk native vlan 666 switchport trunk allowed vlan 99,110,120,200 switchport mode trunk switchport nonegotiate channel-group 1 mode on no shutdown ! interface FastEthernet0/3 description Channel to DLS2 switchport trunk encapsulation dot1q switchport trunk native vlan 666 switchport trunk allowed vlan 99,100,110,120,200 switchport mode trunk switchport nonegotiate channel-group 10 mode on no shutdown ! interface FastEthernet0/4 description Channel to DLS2 switchport trunk encapsulation dot1q switchport trunk native vlan 666 switchport trunk allowed vlan 99,100,110,120,200 switchport mode trunk switchport nonegotiate channel-group 10 mode on no shutdown ! interface FastEthernet0/5 description FE to R1 no switchport ip address 10.1.2.1 255.255.255.252 speed 100 duplex full ipv6 address FE80::D1 link-local ipv6 address 2001:DB8:CAFE:20::D1/64 ipv6 eigrp 1 spanning-tree bpduguard enable no shutdown ! interface FastEthernet0/6 description FE to SRV1 switchport access vlan 100 switchport mode access switchport nonegotiate spanning-tree portfast ! interface FastEthernet0/7 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/8 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/9 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/10 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/11 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/12 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/13 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/14 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/15 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/16 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/17 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/18 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/19 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/20 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/21 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/22 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/23 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/24 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface GigabitEthernet0/1 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface GigabitEthernet0/2 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface Vlan1 no ip address shutdown ! interface Vlan99 ip address 10.1.99.252 255.255.255.0 standby 99 ip 10.1.99.254 standby 99 priority 110 standby 99 preempt ipv6 address FE80::D1 link-local ipv6 address 2001:DB8:CAFE:99::D1/64 ipv6 eigrp 1 no shutdown ! interface Vlan100 ip address 10.1.100.252 255.255.255.0 standby 100 ip 10.1.100.254 standby 100 preempt ipv6 address FE80::D1 link-local ipv6 address 2001:DB8:CAFE:100::D1/64 ipv6 eigrp 1 no shutdown ! interface Vlan110 ip address 10.1.110.252 255.255.255.0 standby 110 ip 10.1.110.254 standby 110 priority 110 standby 110 preempt ipv6 address FE80::D1 link-local ipv6 address 2001:DB8:CAFE:110::D1/64 ipv6 nd prefix 2001:DB8:CAFE:110::/64 no-autoconfig ipv6 nd managed-config-flag ipv6 eigrp 1 ipv6 dhcp server DHCPv6GUEST no shutdown ! interface Vlan120 ip address 10.1.120.252 255.255.255.0 standby 120 ip 10.1.120.254 standby 120 priority 110 standby 120 preempt ipv6 address FE80::D1 link-local ipv6 address 2001:DB8:CAFE:120::D1/64 ipv6 nd prefix 2001:DB8:CAFE:120::/64 no-autoconfig ipv6 nd managed-config-flag ipv6 eigrp 1 ipv6 dhcp server DHCPv6OFFICE no shutdown ! interface Vlan200 ip address 10.1.200.252 255.255.255.0 standby 200 ip 10.1.200.254 standby 200 preempt ipv6 address FE80::D1 link-local ipv6 address 2001:DB8:CAFE:200::D1/64 ipv6 nd prefix 2001:DB8:CAFE:200::/64 no-autoconfig ipv6 nd managed-config-flag ipv6 eigrp 1 ipv6 dhcp server DHCPv6VOICE no shutdown ! ! router eigrp 1 network 10.1.0.0 0.0.255.255 passive-interface default no passive-interface FastEthernet0/5 no passive-interface Vlan99 no passive-interface Vlan100 no passive-interface Vlan110 no passive-interface Vlan120 no passive-interface Vlan200 ! crypto key gen rsa general-keys modulus 1024 ! no ip http server no ip http secure-server ! ! logging source-interface Vlan99 logging host 10.1.100.1 ipv6 router eigrp 1 eigrp router-id 1.1.1.1 ! ! snmp-server community cisco RO snmp-server community san-fran RW snmp-server trap-source Vlan99 snmp-server location TSHOOT Lab Facility snmp-server contact [email protected] snmp-server enable traps eigrp snmp-server enable traps vtp snmp-server enable traps vlancreate snmp-server enable traps vlandelete snmp-server enable traps port-security snmp-server enable traps config snmp-server enable traps hsrp snmp-server enable traps vlan-membership snmp-server enable traps errdisable snmp-server host 10.1.100.1 version 2c cisco ! ! banner motd ^*** BASE DLS1 Config ***^ ! line con 0 exec-timeout 0 0 logging synchronous login authentication CONSOLE line vty 0 4 exec-timeout 0 0 logging synchronous transport input telnet ssh ! ntp source Vlan99 ntp server 10.1.202.1 ! archive log config logging enable logging size 50 notify syslog contenttype plaintext hidekeys path tftp://10.1.100.1/$h-archive-config write-memory file prompt quiet ! end !
Switch DLS2
!BASE DLS2 Config ! service timestamps debug datetime msec service timestamps log datetime service password-encryption ! hostname DLS2 ! ! logging buffered 16384 enable secret cisco ! username cisco secret cisco aaa new-model ! ! aaa authentication login default local aaa authentication login CONSOLE none aaa authorization exec default local ! ! clock timezone PST -8 clock summer-time PDT recurring system mtu routing 1500 vtp domain TSHOOT vtp mode transparent ip routing no ip domain-lookup ip domain-name tshoot.net ip host R1 10.1.2.2 10.1.1.1 10.1.201.1 ip host R2 10.1.1.2 10.1.1.6 10.1.202.1 ip host R3 10.1.1.5 10.1.2.14 10.1.203.1 ip host ALS1 10.1.99.1 ip host DLS1 10.1.99.252 10.1.2.1 ip host DLS2 10.1.99.253 10.1.2.13 ! ! ipv6 unicast-routing ! ! errdisable recovery cause bpduguard ! spanning-tree mode rapid-pvst spanning-tree extend system-id spanning-tree vlan 99,110,120 priority 28672 spanning-tree vlan 100,200 priority 24576 ! ! vlan 99 name MANAGEMENT ! vlan 100 name SERVERS ! vlan 110 name GUEST ! vlan 120 name OFFICE ! vlan 200 name VOICE ! vlan 666 name NATIVE ! vlan 999 name PARKING_LOT ! ip telnet source-interface Vlan99 ip ssh source-interface Vlan99 ! ! interface Port-channel2 description Channel to ALS1 switchport trunk encapsulation dot1q switchport trunk native vlan 666 switchport trunk allowed vlan 99,110,120,200 switchport mode trunk switchport nonegotiate no shutdown ! interface Port-channel10 description Channel to DLS1 switchport trunk encapsulation dot1q switchport trunk native vlan 666 switchport trunk allowed vlan 99,100,110,120,200 switchport mode trunk switchport nonegotiate no shutdown ! interface FastEthernet0/1 description Channel to ALS1 switchport trunk encapsulation dot1q switchport trunk native vlan 666 switchport trunk allowed vlan 99,110,120,200 switchport mode trunk switchport nonegotiate channel-group 2 mode on no shutdown ! interface FastEthernet0/2 description Channel to ALS1 switchport trunk encapsulation dot1q switchport trunk native vlan 666 switchport trunk allowed vlan 99,110,120,200 switchport mode trunk switchport nonegotiate channel-group 2 mode on no shutdown ! interface FastEthernet0/3 description Channel to DLS1 switchport trunk encapsulation dot1q switchport trunk native vlan 666 switchport trunk allowed vlan 99,100,110,120,200 switchport mode trunk switchport nonegotiate channel-group 10 mode on no shutdown ! interface FastEthernet0/4 description Channel to DLS1 switchport trunk encapsulation dot1q switchport trunk native vlan 666 switchport trunk allowed vlan 99,100,110,120,200 switchport mode trunk switchport nonegotiate channel-group 10 mode on no shutdown ! interface FastEthernet0/5 description FE to R3 no switchport ip address 10.1.2.13 255.255.255.252 speed 100 duplex full ipv6 address FE80::D2 link-local ipv6 address 2001:DB8:CAFE:212::D2/64 ipv6 eigrp 1 spanning-tree bpduguard enable no shutdown ! interface FastEthernet0/6 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/7 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/8 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/9 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/10 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/11 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/12 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/13 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/14 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/15 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/16 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/17 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/18 description FE to PC-C switchport access vlan 110 switchport mode access switchport nonegotiate spanning-tree portfast no shutdown ! interface FastEthernet0/19 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/20 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/21 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/22 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/23 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface FastEthernet0/24 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface GigabitEthernet0/1 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface GigabitEthernet0/2 description PARKING_LOT switchport access vlan 999 switchport mode access switchport nonegotiate shutdown ! interface Vlan1 no ip address shutdown ! interface Vlan99 ip address 10.1.99.253 255.255.255.0 standby 99 ip 10.1.99.254 standby 99 preempt ipv6 address FE80::D2 link-local ipv6 address 2001:DB8:CAFE:99::D2/64 ipv6 eigrp 1 no shutdown ! interface Vlan100 ip address 10.1.100.253 255.255.255.0 standby 100 ip 10.1.100.254 standby 100 priority 110 standby 100 preempt ipv6 address FE80::D2 link-local ipv6 address 2001:DB8:CAFE:100::D2/64 ipv6 eigrp 1 no shutdown ! interface Vlan110 ip address 10.1.110.253 255.255.255.0 standby 110 ip 10.1.110.254 standby 110 preempt ipv6 address FE80::D2 link-local ipv6 address 2001:DB8:CAFE:110::D2/64 ipv6 nd prefix 2001:DB8:CAFE:110::/64 no-autoconfig ipv6 nd managed-config-flag ipv6 eigrp 1 no shutdown ! interface Vlan120 ip address 10.1.120.253 255.255.255.0 standby 120 ip 10.1.120.254 standby 120 preempt ipv6 address FE80::D2 link-local ipv6 address 2001:DB8:CAFE:120::D2/64 ipv6 nd prefix 2001:DB8:CAFE:120::/64 no-autoconfig ipv6 nd managed-config-flag ipv6 eigrp 1 no shutdown ! interface Vlan200 ip address 10.1.200.253 255.255.255.0 standby 200 ip 10.1.200.254 standby 200 priority 110 standby 200 preempt ipv6 address FE80::D2 link-local ipv6 address 2001:DB8:CAFE:200::D2/64 ipv6 nd prefix 2001:DB8:CAFE:200::/64 no-autoconfig ipv6 nd managed-config-flag ipv6 eigrp 1 no shutdown ! ! router eigrp 1 network 10.1.0.0 0.0.255.255 passive-interface default no passive-interface FastEthernet0/5 no passive-interface Vlan99 no passive-interface Vlan100 no passive-interface Vlan110 no passive-interface Vlan120 no passive-interface Vlan200 ! crypto key gen rsa general-keys modulus 1024 ! no ip http server no ip http secure-server ! ! logging source-interface Vlan99 logging host 10.1.100.1 ipv6 router eigrp 1 eigrp router-id 2.2.2.2 ! ! snmp-server community cisco RO snmp-server community san-fran RW snmp-server trap-source Vlan99 snmp-server location TSHOOT Lab Facility snmp-server contact [email protected] snmp-server enable traps eigrp snmp-server enable traps vtp snmp-server enable traps vlancreate snmp-server enable traps vlandelete snmp-server enable traps port-security snmp-server enable traps config snmp-server enable traps hsrp snmp-server enable traps vlan-membership snmp-server enable traps errdisable snmp-server host 10.1.100.1 version 2c cisco ! ! banner motd ^*** BASE DLS2 Config ***^ ! line con 0 exec-timeout 0 0 logging synchronous login authentication CONSOLE line vty 0 4 exec-timeout 0 0 logging synchronous transport input telnet ssh ! ntp source Vlan99 ntp server 10.1.202.1 ! archive log config logging enable logging size 50 notify syslog contenttype plaintext hidekeys path tftp://10.1.100.1/$h-archive-config write-memory file prompt quiet ! end !
Router R1
!BASE R1 Config ! service timestamps debug datetime msec service timestamps log datetime msec service password-encryption ! hostname R1 ! logging buffered 16384 enable secret cisco ! aaa new-model ! ! aaa authentication login default local aaa authentication login CONSOLE none aaa authorization exec default local ! ! clock timezone PST -8 clock summer-time PDT recurring ! ! no ip domain lookup ip domain name tshoot.net ip host R1 10.1.2.2 10.1.1.1 10.1.201.1 ip host R2 10.1.1.2 10.1.1.6 10.1.202.1 ip host R3 10.1.1.5 10.1.2.14 10.1.203.1 ip host ALS1 10.1.99.1 ip host DLS1 10.1.99.252 10.1.2.1 ip host DLS2 10.1.99.253 10.1.2.13 ip cef ipv6 unicast-routing ipv6 cef ! ! username cisco secret cisco ! ! ip telnet source-interface Loopback0 ip ssh source-interface Loopback0 ! ! interface Loopback0 ip address 10.1.201.1 255.255.255.255 ipv6 address FE80::1 link-local ipv6 address 2001:DB8:CAFE:201::1/64 ! interface GigabitEthernet0/0 no ip address shutdown duplex auto speed auto ! interface GigabitEthernet0/1 description FE to DLS1 ip address 10.1.2.2 255.255.255.252 ip flow ingress duplex full speed 100 ipv6 address FE80::1 link-local ipv6 address 2001:DB8:CAFE:20::1/64 no shutdown ! interface Serial0/0/0 description WAN link to R2: 2 Mbps leased line ip address 10.1.1.1 255.255.255.252 ip flow ingress encapsulation ppp ipv6 address FE80::1 link-local ipv6 address 2001:DB8:CAFE:10::1/64 clock rate 2000000 no shutdown ! interface Serial0/0/1 description WAN link to R3 (not used) no ip address shutdown ! ! router eigrp HQ ! address-family ipv4 unicast autonomous-system 1 ! af-interface GigabitEthernet0/0 passive-interface exit-af-interface ! af-interface Loopback0 passive-interface exit-af-interface ! topology base exit-af-topology network 0.0.0.0 exit-address-family ! address-family ipv6 unicast autonomous-system 1 ! topology base exit-af-topology exit-address-family ! crypto key gen rsa general-keys modulus 1024 ! ip http server ip http secure-server ip flow-top-talkers top 3 sort-by bytes cache-timeout 600000 ! ! logging source-interface Loopback0 logging host 10.1.100.1 ! ! snmp-server community cisco RO snmp-server community san-fran RW snmp-server trap-source Loopback0 snmp-server location TSHOOT Lab Facility snmp-server contact [email protected] snmp-server enable traps eigrp snmp-server enable traps flash insertion snmp-server enable traps flash removal snmp-server enable traps config snmp-server enable traps cpu threshold snmp-server host 10.1.100.1 version 2c cisco ! ! banner motd ^*** BASE R1 Config ***^ ! line con 0 exec-timeout 0 0 logging synchronous login authentication CONSOLE ! line vty 0 4 exec-timeout 0 0 logging synchronous transport input telnet ssh ! ntp source Loopback0 ntp update-calendar ntp server 10.1.202.1 ! archive log config logging enable logging size 50 notify syslog contenttype plaintext hidekeys path tftp://10.1.100.1/$h-archive-config write-memory file prompt quiet ! end !
Router R2
!BASE R2 Config ! service timestamps debug datetime msec service timestamps log datetime msec service password-encryption ! hostname R2 ! logging buffered 16384 enable secret cisco ! aaa new-model ! ! aaa authentication login default local aaa authentication login CONSOLE none aaa authorization exec default local ! ! clock timezone PST -8 clock summer-time PDT recurring ! ! no ip domain lookup ip domain name tshoot.net ip host R1 10.1.2.2 10.1.1.1 10.1.201.1 ip host R2 10.1.1.2 10.1.1.6 10.1.202.1 ip host R3 10.1.1.5 10.1.2.14 10.1.203.1 ip host ALS1 10.1.99.1 ip host DLS1 10.1.99.252 10.1.2.1 ip host DLS2 10.1.99.253 10.1.2.13 ip cef ipv6 unicast-routing ipv6 cef ! username cisco secret cisco ! ! ip telnet source-interface Loopback0 ip ssh source-interface Loopback0 ! ! interface Loopback0 ip address 10.1.202.1 255.255.255.255 ipv6 address FE80::2 link-local ipv6 address 2001:DB8:CAFE:202::2/64 ! interface Loopback1 ip address 2.2.2.2 255.0.0.0 ipv6 address FE80::2 link-local ipv6 address 2001:DB8:EFAC::2/48 ! interface GigabitEthernet0/0 no ip address shutdown duplex auto speed auto ! interface GigabitEthernet0/1 description optional connection for PC-C w/ static address no ip address shutdown duplex auto speed auto ! interface Serial0/0/0 description WAN link to R1: 2 Mbps leased line ip address 10.1.1.2 255.255.255.252 ip flow ingress encapsulation ppp ipv6 address FE80::2 link-local ipv6 address 2001:DB8:CAFE:10::2/64 no shutdown ! interface Serial0/0/1 description WAN link to R3: 2 Mbps leased line ip address 10.1.1.6 255.255.255.252 ip flow ingress encapsulation ppp ipv6 address FE80::2 link-local ipv6 address 2001:DB8:CAFE:14::2/64 clock rate 2000000 no shutdown ! ! router eigrp HQ ! address-family ipv4 unicast autonomous-system 1 ! af-interface GigabitEthernet0/0 passive-interface exit-af-interface ! af-interface GigabitEthernet0/1 passive-interface exit-af-interface ! af-interface Loopback0 passive-interface exit-af-interface ! af-interface Loopback1 passive-interface exit-af-interface ! topology base exit-af-topology network 0.0.0.0 exit-address-family ! address-family ipv6 unicast autonomous-system 1 ! topology base exit-af-topology exit-address-family ! crypto key gen rsa general-keys modulus 1024 ! ip http server ip http secure-server ip flow-top-talkers top 3 sort-by bytes cache-timeout 600000 ! ! logging source-interface Loopback0 ! ! snmp-server community cisco RO snmp-server community san-fran RW snmp-server trap-source Loopback0 snmp-server location TSHOOT Lab Facility snmp-server contact [email protected] snmp-server enable traps eigrp snmp-server enable traps flash insertion snmp-server enable traps flash removal snmp-server enable traps config snmp-server enable traps cpu threshold snmp-server host 10.1.100.1 version 2c cisco ! ! banner motd ^*** BASE R2 Config ***^ ! line con 0 exec-timeout 0 0 logging synchronous login authentication CONSOLE ! line vty 0 4 exec-timeout 0 0 logging synchronous transport input telnet ssh ! ntp master 3 ! ! archive log config logging size 50 notify syslog contenttype plaintext hidekeys path tftp://10.1.100.1/$h-archive-config write-memory file prompt quiet ! end !
Router R3
!BASE R3 Config ! service timestamps debug datetime msec service timestamps log datetime msec service password-encryption ! hostname R3 ! ! logging buffered 16384 enable secret cisco ! aaa new-model ! ! aaa authentication login default local aaa authentication login CONSOLE none aaa authorization exec default local ! ! clock timezone PST -8 clock summer-time PDT recurring ! ! no ip domain lookup ip domain name tshoot.net ip host R1 10.1.2.2 10.1.1.1 10.1.201.1 ip host R2 10.1.1.2 10.1.1.6 10.1.202.1 ip host R3 10.1.1.5 10.1.2.14 10.1.203.1 ip host ALS1 10.1.99.1 ip host DLS1 10.1.99.252 10.1.2.1 ip host DLS2 10.1.99.253 10.1.2.13 ip cef ipv6 unicast-routing ipv6 cef ! username cisco secret cisco ! ! ip telnet source-interface Loopback0 ip ssh source-interface Loopback0 ! ! interface Loopback0 ip address 10.1.203.1 255.255.255.255 ipv6 address FE80::3 link-local ipv6 address 2001:DB8:CAFE:203::3/64 ! ! interface GigabitEthernet0/0 no ip address shutdown duplex auto speed auto ! interface GigabitEthernet0/1 description FE to DLS2 ip address 10.1.2.14 255.255.255.252 ip flow ingress duplex full speed 100 ipv6 address FE80::3 link-local ipv6 address 2001:DB8:CAFE:212::3/64 no shutdown ! interface Serial0/0/0 description WAN link to R1 - (Not used) no ip address encapsulation ppp shutdown clock rate 2000000 ! interface Serial0/0/1 description WAN link to R2: 2 Mbps leased line ip address 10.1.1.5 255.255.255.252 ip flow ingress encapsulation ppp ipv6 address FE80::3 link-local ipv6 address 2001:DB8:CAFE:14::3/64 no shutdown ! ! router eigrp HQ ! address-family ipv4 unicast autonomous-system 1 ! af-interface GigabitEthernet0/0 passive-interface exit-af-interface ! af-interface Loopback0 passive-interface exit-af-interface ! topology base exit-af-topology network 0.0.0.0 exit-address-family ! address-family ipv6 unicast autonomous-system 1 ! topology base exit-af-topology exit-address-family ! crypto key gen rsa general-keys modulus 1024 ! ip http server ip http secure-server ip flow-top-talkers top 3 sort-by bytes cache-timeout 600000 ! ! logging source-interface Loopback0 logging host 10.1.100.1 ! ! snmp-server community cisco RO snmp-server community san-fran RW snmp-server trap-source Loopback0 snmp-server location TSHOOT Lab Facility snmp-server contact [email protected] snmp-server enable traps eigrp snmp-server enable traps flash insertion snmp-server enable traps flash removal snmp-server enable traps config snmp-server enable traps cpu threshold snmp-server host 10.1.100.1 version 2c cisco ! ! banner motd ^*** BASE R3 Config ***^ ! line con 0 exec-timeout 0 0 logging synchronous login authentication CONSOLE ! line vty 0 4 exec-timeout 0 0 logging synchronous transport input telnet ssh ! ntp source Loopback0 ntp update-calendar ntp server 10.1.202.1 ! ! archive log config logging enable logging size 50 notify syslog contenttype plaintext hidekeys path tftp://10.1.100.1/$h-archive-config write-memory file prompt quiet ! end !
TCL Script for testing ping connectivity to all IPv4 addresses in baseline:
tclsh
foreach i {
10.1.100.1
10.1.100.252
10.1.100.253
10.1.100.254
10.1.99.251
10.1.99.252
10.1.99.253
10.1.99.254
10.1.110.1
10.1.110.251
10.1.110.252
10.1.110.253
10.1.110.254
10.1.120.1
10.1.120.251
10.1.120.252
10.1.120.253
10.1.120.254
10.1.200.251
10.1.200.252
10.1.200.253
10.1.200.254
10.1.2.1
10.1.2.2
10.1.1.1
10.1.1.2
10.1.2.13
10.1.2.14
10.1.1.5
10.1.1.6
10.1.201.1
10.1.202.1
10.1.203.1
2.2.2.2
} { puts [exec "ping $i"] }
tclquit
To use this script, paste it into User EXEC mode on any Cisco networking device.

where are the awnsers to the questions in the lab?