1. A network technician receives a call from a use who is experiencing network connectivity issues. The network technician questions the user and learns the user brought in a personal wired router to use multiple computers and connect to the network. Which of the following has the user MOST likely introduced to the network?
A. Rogue DHCP server
B. Evil twin
C. VLAN mismatch
D. Honeypot
2. A technician is setting up a direct connection between two older PCs so they can communicate but not be on the corporate network. The technician does not have access to a spare switch but does have spare Cat 6 cables, RJ-45 plugs, and a crimping tool. The technician cuts off one end of the cable. Which of the following should the technician do to make a crossover cable before crimping the new plug?
A. Reverse the wires leading to pins 1 and 2
B. Reverse the wires leading to pins 1 and 3
C. Reverse the wires leading to pins 2 and 3
D. Reverse the wires leading to pins 2 and 4
3. An office network consists of one two-port router connected to a 12-port switch. A four-port hub is also connected to the switch. On this particular network, which of the following is the number of collision domain that exist?
A. 3
B. 12
C. 13
D. 14
E. 15
4. A network technician wants to remotely and securely access the desktop of a Linux workstation. The desktop is running remote control software without encryption. Which of the following should the technician use to secure the connection?
A. SSH in tunnel mode
B. RDP set to console connection
C. EAP-PEAP
D. SFTP
5. Which of the following should current network performance be compared against to determine network anomalies?
A. Baseline
B. Traffic analysis
C. Packet capture
D. Logs
6. A network administrator configures an email server to use secure protocols. When the upgrade is completed, which of the following ports on the firewall should be configured to allow for connectivity? (Choose three.)
A. TCP 25
B. TCP 110
C. TCP 143
D. TCP 389
E. TCP 587
F. TCP 993
G. TCP 995
7. After a server outage, a technician discovers that a physically damaged fiber cable appears to be the problem. After replacing the cable, the server will still not connect to the network. Upon inspecting the cable at the server end, the technician discovers light can be seen through one of the two fiber strands. Which of the following should the technician do FIRST to reconnect the server to the network?
A. Reverse the fiber strands of the cable and reconnect them to the server
B. Use a TDR to test both strands of a new replacement cable prior to connecting it to the server
C. Replace the server’s single-mode fiber cable with multimode fiber
D. Move the fiber cable to different port on the switch where both strands function
8. The backups server connects to a NAS device using block-level storage over Ethernet. The performance is very slow, however, and the network technician suspects the performance issues are network related. Which of the following should the technician do to improve performance?
A. Utilize UDP to eliminate packet overhead
B. Turn off MDIX settings on the NAS and server switchports
C. Enable jumbo frames on the NAS and server
D. Encapsulate the storage traffic in a GRE tunnel
9. A technician is trying to determine the IP address of a customer’s router. The customer has an IP address of 192.168.1.55/24. Which of the following is the address of the customer’s router?
A. 192.168.0.55
B. 192.168.1.0
C. 192.168.1.1
D. 192.168.5.5
E. 255.255.255.0
10. A network technician is able to connect the switches between to offices, but the offices cannot communicate with each other, as each office uses a different IP addressing scheme. Which of the following devices needs to be installed between the switches to allow communication?
A. Bridge
B. Access point
C. Router
D. Range extender
11. A network technician is working on a proposal for email migration from an on-premises email system to a vendor-hosted email in the cloud. The technician needs to explain to management what type of cloud model will be utilized with the cloud-hosted email. Which of the following cloud models should the technician identify in the proposal?
A. IaaS
B. PaaS
C. SaaS
D. MaaS
12. Which of the following is the correct port number for NTP?
A. 25
B. 69
C. 123
D. 161
13. A technician is upgrading the firmware on an older KVM switch. The specifications call for a serial port to connect to the computer on one side, and an Ethernet jack to connect to the switch on the other side. Which of the following connectors does the technician need for this cable? (Choose two.)
A. RG-9
B. DB-9
C. RJ-11
D. DB-25
E. RJ-45
F. BNC
14. An end-user device requires a specific IP address every time it connects to the corporate network; however, corporate policy does not allow the use of static IP addresses. Which of the following will allow the request to be fulfilled without breaking the corporate policy?
A. DHCP relay
B. DHCP exclusion
C. DHCP option
D. DHCP reservation
15. A technician is planning a remote-access strategy to manage routers and switches on a dedicated management network. The management network is segregated from the production network and uses site-to-site VPN connections. Some of the equipment does not support encryption. Which of the following should the technician choose that all the equipment would support?
A. Telnet
B. SSL
C. SSH
D. IPSec
16. Which of the following protocols do MOST MITM attacks utilize?
A. ARP
B. SIP
C. FTP
D. SCP
17. An ISP technician gets a call from a business that just changed equipment but can no longer connect to the Internet. The technician checks the ARP table on the ISP switch, and there is no corresponding MAC address present. Instead, the entry is “Incomplete”. Which of the following could cause this condition?
A. VLAN mismatch
B. Duplex/Speed mismatch
C. Duplicate IP address
D. TX/RX reverse
18. A systems administrator has recently purchased and installed a large electronic signage screen for the company’s parking garage. The screen’s management software was installed on a server with public IP address to allow remote management. The systems administrator is now troubleshooting an issue with the screen displaying unknown, random, and inappropriate messages. Which of the following is MOST effective in resolving this issue?
A. Changing the management software’s default credentials
B. Disabling unnecessary services from the server and management software
C. Changing the management software’s default port
D. Replacing the management software’s self-signed certificate with a valid certificate
19. A technician is investigating a server performance issue. The technician has gathered the server utilization statistics. Which of the following should the technician use to determine which statistics are not in the normal range?
A. Baseline review
B. Vulnerability scan
C. System life-cycle report
D. Archiving logs
20. Which of the following devices, if implemented, would result in decreased administration time of an 802.11 network running centralized authentication services? (Choose two.)
A. VPN concentrator
B. Proxy server
C. Wireless controller
D. RADIUS server
E. Multilayer switch
21. A technician must determine if a web page user’s visits are connecting to a suspicious website’s IP address in the background. Which of the following tools would provide the information on TCP connections?
A. netstat
B. tracert
C. arp
D. ipconfig
E. route
22. An administrator is moving to a new office. There will be several network runs through the ceiling area of the office. Which of the following is the BEST to utilize in these areas?
A. Single-mode fiber-optic cabling
B. Cat 5e-rated cabling
C. Cat 6-rated cabling
D. Plenum-rated cabling
23. A network technician receives a spool of Cat 6a cable and is asked to build several cables for a new set of Ethernet runs between devices. Which of the following tools are MOST likely needed to complete the task? (Choose three.)
A. Wire stripper
B. Cable crimper
C. RJ-11 connectors
D. RJ-45 connectors
E. Multimeter
F. Punchdown tool
G. Tone generator
24. As part of a transition from a static to a dynamic routing protocol on an organization’s internal network, the routing protocol must support IPv4 and VLSM. Based on those requirements, which of the following should the network administrator use? (Choose two.)
A. OSPF
B. IS-IS
C. RIPv1
D. BGP
E. VRRP
25. A telecommunications provider has just deployed a new OC-12 circuit at a customer site. While the circuit showed no errors from the provider end to the customer’s demarcation point, a network administrator is trying to determine the cause of dropped packets and errors on the circuit. Which of the following should the network administrator do to rule out any problems at Layer 1? (Choose two.)
A. Use a loopback at the demark and router, and check for a link light
B. Use an OTDR to validate the cable integrity
C. Use a pinout tester to validate the cable integrity
D. Use a multimeter to validate the cable integrity
E. Check for any devices that may be causing EMI on the cable
F. Clean the cables to be sure they are free of dust and debris
26. A single PRI can deliver multiple voice calls simultaneously using which of the following Layer 1 technologies?
A. Time division multiplexing
B. Analog circuit switching
C. CSMA/CD
D. Time division spread spectrum
27. A network technician is diagnosing a time-out issue generated from an end user’s web browser. The web browser issues standard HTTP get and post commands to interact with the website. Given this information, the technician would like to analyze the entire TCP handshake of the HTTP requests offline. Which of the following tools would allow the technician to view the handshake?
A. Packet analyzer
B. Port analyzer
C. SNMP traps
D. Spectrum analyzer
28. A customer cannot access a company’s secure website. The company’s network security is reviewing the firewall for the server and finds the following output:
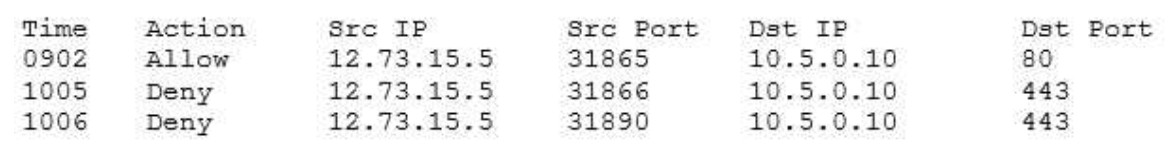
Which of the following changes should be made to allow all customers to access the company’s secure website?
A. Allow any any 10.5.0.10 443
B. Allow any any 12.73.15.5 443
C. Allow 10.5.0.10 443 any any
D. Allow 10.5.0.10 any 10.5.0.10 80
29. Which of the following MUST be implemented to share metrics between routing protocols within the same router?
A. Routing loop
B. Routing table
C. Route redistribution
D. Dynamic routes
30. An engineer is reviewing the implementation requirements for an upcoming project. The basic requirements identified by the customer include the following:
WLAN architecture supporting speeds in excess of 150 Mbps Clientless remote network access Port-based network access control
Which of the following solution sets properly addresses all of the identified requirements?
A. 802.11a, IPSec VPN, 802.1x
B. 802.11ac, MPLS, 802.3
C. 802.11b, PPTP, 802.1x
D. 802.11g, MS-CHAP, 802.16
E. 802.11n, SSL-VPN, 802.1x
31. Which of the following would be the MOST efficient subnet mask for a point-to-point link?
A. /28
B. /29
C. /31
D. /32
32. An office user cannot access local network drives but has full access to the Internet. A technician troubleshoots the issue and observes the following output of the ipconfig command:
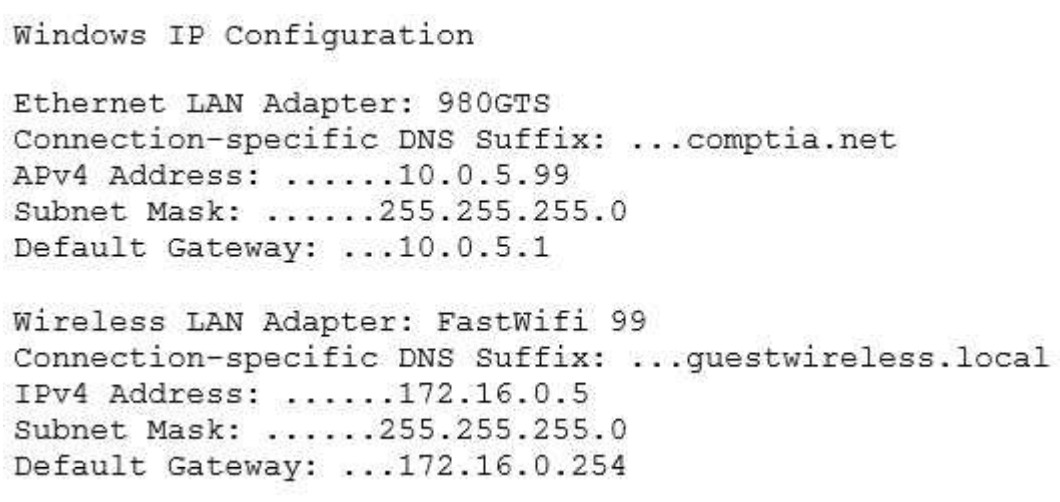
Which of the following would MOST likely allow the network drives to be accessed?
A. Update the WLAN adapter driver
B. Disable the WLAN adapter
C. Check the wireless DHCP configuration
D. Disable the LAN adapter
33. Ann, a network technician, has just installed a fiber switch in a datacenter. To run the fiber cabling, Ann plans the cable route over the top of the rack using the cable trays, down to the switch, coiling up any excess cable. As Ann configures the switch, she notices several messages in the logging buffer stating the receive signal of the SFP is too weak. Which of the following is MOST likely the cause of the errors in the logging buffer?
A. Bend radius exceeded
B. Fiber cable mismatch
C. Fiber type mismatch
D. Bad fiber switch
34. Which of the following wireless connection types utilize MIMO on non-overlapping channels? (Choose two.)
A. 802.11a
B. 802.11ac
C. 802.11b
D. 802.11g
E. 802.11n
35. A network technician is creating a new subnet for 488 host machines. The technician is told to use a class B address scheme when making the subnet and is instructed to leave as much room as possible for additional subnets of the same size. Which of the following subnets would fulfill these requirements?
A. 10.5.4.0/22
B. 10.233.2.0/23
C. 172.16.0.0/22
D. 172.18.0.0/23
E. 192.168.25.0/24
36. A network engineer is designing a new IDF in an old building. The engineer determines the equipment will fit in a two-post rack, and there is power available for this equipment. Which of the following would be the FIRST issue to remediate?
A. Air flow and cooling
B. UPS capability
C. Circuit labeling
D. Power redundancy
37. Which of the following DNS records needs to be configured for SMTP traffic?
A. MX
B. CNAME
C. AAAA
D. PTR
38. In which of the following ways does a DDoS attack differ from a spoofing attack?
A. DDoS attacks target multiple networks
B. Spoofing attacks originate from a single host
C. DDoS attacks are launched from multiple hosts
D. Spoofing attacks require physical presence
39. A user checks an IP address using an external website. The address is different than the one the user sees when opening a command prompt and typing in ipconfig/all. The user does not understand why the two tools show different IP addresses. This is BEST explained by the interworking of:
A. network devices
B. packet flow
C. public/private networks
D. traffic-routing protocols
40. Which of the following communication media can carry many voice, data, and video channels simultaneously over multiple frequencies?
A. Broadband
B. Baseband
C. Analog modem
D. CSMA
41. To replace a defective UPS, the network administrator must take the switch offline. The administrator wants to be able to perform maintenance UPS in the future without affecting the availability of the attached switch. Which of the following would BEST allow this to happen?
A. Add a redundant power supply to the switch
B. Implement stacking on the switches in the rack
C. Add a second UPS into the rack
D. Install a power converter for the switch
42. A forensic first responder arrives at the scene where an employee is suspected to have committed a computer-based crime. Which of the following should the first responder do FIRST?
A. Document the scene
B. Take pictures upon arrival
C. Secure the area
D. Implement chain of custody
43. A small town is attempting to attract tourists who visit larger nearby cities. A network engineer is asked to implement a network encompassing the five-block town center and nearby businesses. The inclusion of smartphones and portable devices is crucial to the plan. Which of the following is the network engineer being asked to implement?
A. LAN
B. PAN
C. MAN
D. WAN
44. An employee wishes to use a personal cell phone for work-related purposes, including storage of sensitive company data, during long business trips. Which of the following is needed to protect BOTH the employee and the company?
A. An NDA ensuring work data stored on the personal phone remains confidential
B. An AUP covering how a personal phone may be used for work matters
C. A consent to monitoring policy covering company audits of the personal phone
D. Real-time remote monitoring of the phone’s activity and usage
45. Which of the following protocols can be both connection-oriented and connectionless?
A. 20 FTP
B. 53 DNS
C. 67 DHCP
D. 80 HTTP
46. Which of the following BEST describes the differences between VLAN hopping and session hijacking?
A. VLAN hopping involves the unauthorized transition from one VLAN to another to gain additional access.
Session hijacking involves overriding a user’s web connection to execute commands
B. VLAN hopping is a brute force attack executed to gain additional access.
Session hijacking involves physically disrupting a network connection
C. VLAN hopping involves overriding a user network connection to execute malicious commands.
Session hijacking involves compromising a host to elevate privileges
D. VLAN hopping is the act of exploiting poor VLAN tagging.
Session hijacking is a web-based attack aimed at privilege escalation
47. An analyst is developing a proof of concept of a wireless-based attack as part of a penetration test against an organization’s network. As part of the attack, the analyst launches a fake access point matching the SSID of the organization’s guest access network. When a user connects to the fake access point, the analyst allows the traffic to flow through the access point to the legitimate site while the data traversing the network is logged for latest analysis and exploitation. Which of the following attacks has the analyst successfully performed in this scenario?
A. Bluesnarfing
B. Session hijacking
C. MAC spoofing
D. VLAN hopping
E. Man-in-the-middle
48. A network administrator receives a call from the sales department requesting ports 20 and 21 be opened on the company’s firewall to allow customers to retrieve a large file. Which of the following should the administrator perform BEFORE making the needed changes? (Choose two.)
A. Document the reason for the request
B. Scan the file for malware to protect the sales department’s computers
C. Follow the company’s approval process for the implementation
D. Install a TFTP server for the customers to use for the transfer
E. Create a honeypot to store the file on for the customers to use
F. Write the SLA for the sales department authorizing the change
49. A user reports that a laptop cannot connect to the Internet despite the fact the wireless Internet was functioning on it yesterday. The user did not modify the laptop in any way, and the wireless Internet is functional on other users’ laptops. Which of the following issues should be reviewed to help the user to connect to the wireless network?
A. Wireless switch toggled off
B. WAP settings
C. WLAN IP address out of scope
D. Wireless controller misconfiguration
50. A network administrator wants to increase the confidentiality of the system by hardening the authentication process. Currently, the users log in using usernames and passwords to access the system. Which of the following will increase the authentication factor to three?
A. Adding a fingerprint reader to each workstation and providing a RSA authentication token
B. Adding a fingerprint reader and retina scanner
C. Using a smart card and RSA token
D. Enforcing a stronger password policy and using a hand geometry scan
51. A network technician is building a network for a small office. The office currently has cable TV and now requires access to the Internet without adding any cabling other than what is already in place. Which of the following solutions should the technician install to meet these requirements?
A. DOCSIS modem
B. Wireless router
C. DSL modem
D. Access point
52. A network engineer arrives at work and discovers that many users are having problems when attempting to connect to the company network shared drives. The network operations center (NOC) technician just completed server upgrades the night before. To which of the following documents should the NOC technician refer to determine what potentially caused the connectivity problem?
A. Network maps
B. Cable management
C. Release notes
D. Change management
53. Which of the following VPN protocols establishes a secure session that can be initiated using a browser?
A. IPSec
B. SSL VPN
C. PTP
D. PPTP
54. A technician is setting up a public guest network for visitors to access the Internet that must be separate from the corporate network. Which of the following are the BEST steps for the technician to take with minimum overhead configuration? (Choose two.)
A. Enable SSID broadcasting to identify the guest network
B. Configure visitor devices to use static IP addresses
C. Enable two-factor authentication on visitor devices
D. Configure the access point to use WPA2-AES encryption
E. Ensure the access point is not running in mixed mode
55. When choosing a type of storage that integrates with the existing network infrastructure, the storage must be easily configurable to share files and can communicate with all existing clients over TCP/IP. Which of the following is the BEST technology for the network administrator to implement?
A. iSCSI
B. Fibre Channel
C. NAS
D. DAS
56. A network technician is installing a new network switch is looking for an appropriate fiber optic patch cable. The fiber optic patch panel uses a twist-style connector. The switch uses a SFP module. Which of the following connector types should the fiber patch cable have?
A. LC
B. ST
C. SC
D. MTRJ
E. MTP
57. Which of the following WAN technologies utilizes the concept of virtual circuits and pointmultipoint connections?
A. ISDN
B. MPLS
C. PRI
D. Broadband cable
E. Frame relay
58. A network administrator wishes to ensure there are no unnecessary open communication paths into a server. Using a port scanner, the administrator finds that ports are reported as closed. Which of the following BEST explains this response?
A. The ports belong to an active system and are denying requests
B. The ports are associated with deprecated services
C. The ports do not belong to a live system
D. The ports replied with a SYN/ACK response
59. Users are reporting issues with slow connection speeds and a loss of connectivity on the newly installed wireless network. The issues are intermittent but seem to occur most often around midday. Which of the following is the MOST likely cause?
A. There is interference from small appliances
B. The signal coverage area is too small
C. Not enough DHCP addresses have been allotted
D. The DNS cache on the users’ computers has become corrupt
60. A user reports difficulties connecting a PC to a wired network. The PC connects to an IP phone, which is working correctly. A network technician can verify that other devices successfully connect to the phone. At which of the following layers of the OSI model is the problem MOST likely located?
A. Network
B. Physical
C. Transport
D. Application
61. Which of the following physical security controls is MOST likely to be susceptible to a false positive?
A. Identification card
B. Biometric device
C. Proximity reader
D. Video camera
62. An assistant systems analyst reports the following findings of an investigation of slow Internet connections in a remote office to the senior systems analyst:
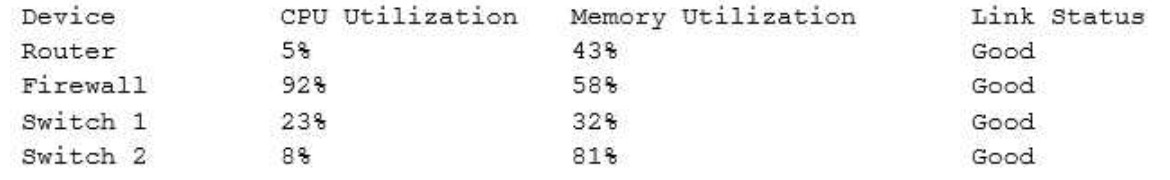
Which of the following devices is causing the issue?
A. Router
B. Firewall
C. Switch 1
D. Switch 2
63. A small business developed an in-house application that is very sensitive to network latency when a communicating between servers. Due to a lack of funds, the business had to build its own network for workstations and servers. Now a network administrator must redesign the network due to performance issues with the application. Which of the following would be the MOST cost effective for the administrator to recommend?
A. Create Ethernet VLANs
B. Disable autonegotiation on the servers
C. Install 10Gb Ethernet NICs in the servers
D. Install Fibre Channel for the server network
64. A network technician is configuring a firewall access list to secure incoming connections to an email server. The internal address of this email server is 192.168.1.143. The firewall should allow external email servers to send email to the email server. The email server also supports client access via a web browser. Only secure protocols should be used, and only the necessary ports should be open. Which of the following ACL rules should be configured in the firewall’s WAN port? (Choose two.)
A. Permit 192.168.1.143.25
B. Permit 192.168.1.143.80
C. Permit 192.168.1.143.110
D. Permit 192.168.1.143.143
E. Permit 192.168.1.143.443
F. Permit 192.168.1.143.587
65. A network administrator needs to transmit traffic to geographically diverse sites to improve performance. Which of the following devices would BEST direct traffic to the remote sites?
A. Hub
B. Bridge
C. Switch
D. Router
66. Which of the following should a technician investigate when using a network baseline to troubleshoot?
A. Tracing a network wire connectivity issue from the datacenter to a host.
B. Determining if the server performance is degraded.
C. Changes that have been made to the network configuration.
D. Location of networking equipment in a rack.
67. A technician needs to upgrade a SOHO wireless router’s firmware. The technician resets the router to factory settings and installs the new firmware. The technician enters the DHCP information and sets the SSID. Which of the following configurations would provide the MOST protection from advance hackers?
A. Disable the broadcasting of the SSID.
B. Enable WPA2 authentication for all hosts.
C. Use private addressing for the DHCP scope.
D. Install unidirectional antennas.
68. A technician notices clients are receiving a 169.254.x.x IP address following the upgrade of a server. Which of the following ports should the technician check on the local server firewall?
A. ports 20 and 21
B. ports 67 and 68
C. ports 80 and 443
D. port 123 and 8080
69. Which of the following datacenter security methodologies is MOST likely to remain usable during a network outage?
A. biometric scanners
B. door locks
C. video surveillance
D. motion detectors
70. A network technician is implementing a solution on the network to hide the workstation internal IP addresses across a WAN. Which of the following is the technician configuring?
A. QoS
B. DMZ
C. RIP
D. NAT
71. Employees want the ability to use personal devices on the guest network while working out at the company gym. In order to meet the request, which of the following policies requires employee adherence?
A. AUP
B. SLA
C. NDA
D. MOU
72. Which of the following BEST describes the BGP routing protocol?
A. distance vector
B. hybrid
C. static
D. link state
73. A customer is reporting difficulty connecting some devices after replacing a wireless router with a new wireless 802.11ac router. The SSID, encryption and password are the same as the previous router. A technician goes on-site and notices the devices that are no longer connecting appear to be several years ago. Which of the following is MOST likely the problem?
A. the password needs to be re-entered.
B. there is a security type mismatch.
C. there is insufficient antenna power.
D. there is a frequency mismatch.
E. the channel has changed.
74. Which of the following functions would be used to securely monitor and actively manage external connections?
A. VPN concentrator
B. HIDS
C. Load balancer
D. Packet shaper
75. A technician has replaced the Internet gateway router, and now no users can reach the Internet. The technician can ping the router Ethernet port but not the ISP’s router IP address. Which of the following is the MOST likely problem?
A. Faulty crossover cable
B. DNS server is down
C. Switching loop
D. Outside interface shutdown
76. Which of the following commands will display the associated IP address of a network adapter in Windows and Linux environments? (Select TWO).
A. dig
B. nslookup
C. nbstat
D. ifconfig
E. ipconfig
77. When querying a DNS server for an AAAA record, which of the following is an appropriate response?
A. 192.168.2.1
B. 00:f3:82:99:a2:b8
C. 61.23.168.192.in-addr.arpa
D. 3ffe:1900:4545:3:200:f8ff:fe21:67cf
78. A computer on VLAN 10 with the IP address of 192.168.1.45/27 cannot ping a computer on VLAN 20 with the IP address of 192.168.1.65/27. Which configuration change will allow the PING to be successful?
A. Replace the router with a Layer 2 switch that supports VLANs
B. Change VLAN 20 computers Default Gateway to 192.168.1.127/27
C. Change VLAN 10 computers Default Gateway to 192.168.1.32/27
D. AllowICMP to pass through the Router
79. Which of the following network devices restricts traffic based on words, signatures, and URLs?
A. Layer 2 switch
B. Content filter
C. Load balancer
D. Traffic analyzer
80. A new firewall was recently installed blocking SMTP traffic. As a result, no one has Internet access.
Which of the following has MOST likely occurred?
A. Port security is blocking all traffic.
B. An IDS is blocking all traffic.
C. Implicit deny is blocking all traffic.
D. SMTP is blocking all traffic.
81. Please refer to the attached exhibit.
Which of the following types of configuration management documentation is represented?
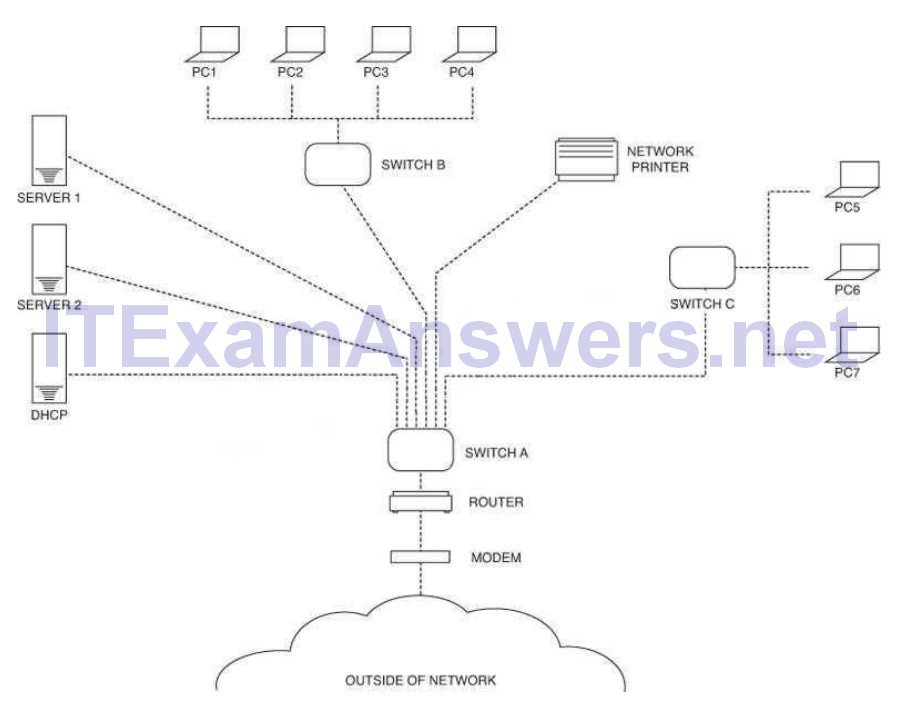
A. Network security policy
B. Network baseline
C. Logical network diagram
D. Wiring schematic
82. A user is unable to open up websites on the Internet from a browser. The administrator determines that the workstation can ping its local gateway, but not the remote web server. At which of the following layers of the OSI model does the problem MOST likely exist?
A. Data link
B. Network
C. Session
D. Physical
83. Which of the following uses types and codes rather than ports?
A. EIGRP
B. ICMP
C. UDP
D. IPv6
84. A technician, Joe, visits a site that has reported a network down emergency. He immediately reboots the switches and the router since the network is down. Which of the following network troubleshooting methodology steps should Joe have performed FIRST?
A. Determine if anything has changed
B. Once a theory is confirmed determine the next step is to resolve the problem
C. Implement the solution or escalate as necessary
D. the obvious
85. Which of the following defines an IP address that is NOT routed on the Internet?
A. Multicast
B. Public
C. Private
D. Classful
86. Matt, an administrator, notices a flood fragmented packet and retransmits from an email server. After disabling the TCP offload setting on the NIC, Matt sees normal traffic with packets flowing in sequence again. Which of the following utilities was he MOST likely using to view this issue?
A. Spam filter
B. Protocol analyzer
C. Web application firewall
D. Load balancer
87. Which of the following specifications would Sara, an administrator, implement as a network access control?
A. 802.1q
B. 802.3
C. 802.11n
D. 802.1x
88. Which of the following is characterized by an attacker attempting to map out an organization’s staff hierarchy in order to send targeted emails?
A. Whaling
B. Impersonation
C. Privilege escalation
D. Spear phishing
89. Which of the following defines when Pete, an attacker, attempts to monitor wireless traffic in order to perform malicious activities?
A. XSS
B. SQL injection
C. Directory traversal
D. Packet sniffing
90. Which of the following provides the MOST protection against zero day attacks via email attachments?
A. Anti-spam
B. Anti-virus
C. Host-based firewalls
D. Patch management
91. Which of the following access controls enforces permissions based on data labeling at specific levels?
A. Mandatory access control
B. Separation of duties access control
C. Discretionary access control
D. Role based access control
92. A username provides which of the following?
A. Biometrics
B. Identification
C. Authorization
D. Authentication
93. Use of group accounts should be minimized to ensure which of the following?
A. Password security
B. Regular auditing
C. Baseline management
D. Individual accountability
94. Privilege creep among long-term employees can be mitigated by which of the following procedures?
A. User permission reviews
B. Mandatory vacations
C. Separation of duties
D. Job function rotation
95. Which of the following wireless standards is capable of ONLY operating on 5.8GHz?
A. 802.11a
B. 802.11b
C. 802.11g
D. 802.11n
96. Which of the following protocols are used to connect devices in a secure manner? (Select TWO).
A. TELNET
B. SSH
C. RDP
D. HTTP
E. DNS
F. FTP
97. Which of the following provides the use of a secure tunnel for telecommuting without manually installing and configuring encryption software?
A. RDP
B. SSL VPN
C. ISAKMP
D. TLS 2.0
98. Which of the following is based ENTIRELY on using ICMP packets?
A. Social engineering
B. NMAP
C. Buffer overflow attack
D. Smurf attack
99. Which of the following could be used to stop unknown threats?
A. DMZ
B. Signature based IPS
C. Behavior based IPS
D. Honeypots
100. Which of the following describes a DNS server?
A. Translates an IP address to a name
B. Caches commonly viewed web pages
C. Assigns IP addresses to network devices
D. Provides port security for a network
101. A workstation on the network is configured as follows. A user reports that they are unable to print to a device located on a different subnet. Which of the following is the MOST likely problem?
IP address: 172.16.204.12 Subnet Mask: 255.255.0.0 Default Gateway: 172.15.204.254 DNS address: 172.16.204.1 Broadcast address: 172.16.255.255
A. DNS address
B. Subnet mask
C. Default gateway
D. Broadcast address
E. IP address
102. A technician recently fixed a computer with several viruses and spyware programs on it and notices the Internet settings were set to redirect all traffic through an unknown proxy. This type of attack is known as which of the following?
A. Phishing
B. Social engineering
C. Man-in-the-middle
D. Shoulder surfing
103. Which of the following is the BEST way to mitigate security threats on a network?
A. Social engineering
B. User training
C. Incident response
D. Man-in-the- middle
104. Which of the following devices should be installed on a network to monitor the presence of and actively defend against attacks?
A. An IPS
B. A protocol analyzer
C. A traffic shaper
D. An IDS
105. Which of the following is an IPv6 address?
A. 00:14:38:05:7B:E5
B. 10.10.1.1
C. 192.168.1.1
D. 2001:cdba::3257:9652
106. A company has a large number of employees that need VPN access from home. Which of the following is the BEST solution for deploying and managing the remote access?
A. Site-to-site VPN
B. Network-based firewall
C. SSL VPN
D. Host-based firewall
107. Which of the following is a routed protocol that functions at layer 3 of the OSI model?
A. IP
B. Frame relay
C. PPP
D. ADSL
108. Something you have, something you are, and something you know are the three tenets of:
A. Social engineering
B. Change management
C. Remote access
D. Access control
109. A firewall that operates at Layer 7 of the OSI model is known as a(n):
A. Circuit gateway
B. Packet filter
C. Application level
D. Redundant firewall
110. Which of the following allows a central point to simultaneously address other points without addressing all of them?
A. Multicast
B. Subnetting
C. Unicast
D. Broadcast
111. Which of the following connector types would Sandy, a network technician, use to connect a serial cable?
A. RJ-11
B. BNC
C. LC
D. DB-9
112. Which of the following are network topologies? (Select TWO).
A. Ethernet
B. Duplex
C. Star
D. Circular
E. Bus
113. Which of the following MUST be kept synchronized in order for Kerberos to work?
A. Certificate
B. Ticket
C. Time
D. Token
114. Which of the following MUST be used when securing a VoIP network consisting of private IP addresses?
A. IPS
B. Application layer firewall
C. IDS
D. An unmanaged switch
115. Which of the following uses certificates as a form of security?
A. Kerberos
B. LDAP
C. PKI
D. CHAP
116. Which of the following cables will MOST likely be used to connect to a satellite dish?
A. RG-6
B. CAT5e
C. Fiber
D. CAT6
Answer: A
117. A VoIP line will MOST likely have which of the following connectors?
A. RJ-11
B. DB-25
C. BNC
D. RJ-45
118. Which of the following is a proprietary routing protocol?
A. RIP
B. EIGRP
C. OSPF
D. BGP
119. Which of the following is an invalid MAC address?
A. AA:CE:58:FD:90:08
B. 44:98:3E:F8:33:23
C. 56:AD:BX:89:55:54
D. 94:9E:FE:EE:8C:DF
120. Which of the following network topologies allows only communication to take place from one node at a time by passing a token around the network?
A. Star
B. Mesh
C. Bus
D. Ring
121. A technician discovers that a malware infection has damaged part of the Windows TCP/IP stack.
Which of the following commands can help repair the damage?
A. netsh lan
B. netsh interface
C. netsh wlan
D. netsh winsock
122. Which of the following devices exist as either hardware or software to assist in routing traffic? (Select TWO).
A. Cable modern
B. Layer 2 switch
C. Router
D. NIDS
E. Layer 3 switch
123. Which of the following operates at OSI layer 2 to forward traffic based on the MAC address?
A. Switch
B. Proxy Server
C. Router
D. VPN Concetnrator
124. The Transport Layer of the TCP/IP model corresponds to which of the following layers of the OSI model?
A. 1
B. 3
C. 4
D. 5
125. Which of the following is used to provide hot standby capabilities using paired routers?
A. CARP
B. L2TP
C. PPTP
D. ISAKMP
126. Which of the following is used to assign an IP address to a device?
A. DHCP
B. NTP
C. DNS
D. RADIUS
127. Which of the following protocols is used to transmit outgoing email?
A. RDP
B. NTP
C. POP3
D. SMTP
128. A network technician is configuring a wireless network. To avoid interference from other wireless networks in the area, the technician should change which setting?
A. Channel
B. SSID
C. Firewall rule
D. Encryption
129. A user is unable to print to a network printer. Which of following is the FIRST step that a technician should take to troubleshoot the issue?
A. Identify the problem.
B. Establish a plan of action to resolve the problem.
C. Establish a theory of probable cause.
D. Implement preventative measures.
130. Which of the following is a purpose of a VLAN?
A. Decreases bandwidth on a network
B. Segments broadcast traffic
C. Increases port speed
D. Allows another connection to the router
131. Which of the following would Sandy, a technician, find in a network map?
A. QoS standards
B. MDF/IDFs
C. System logs
D. Firewall rules
132. Which of the following protocols would be used to send email to an email server?
A. NTP
B. FTP
C. SNMP
D. SMTP
133. Which of the following default ports would need to be open on a firewall to allow remote desktop access?
A. 143
B. 443
C. 3389
D. 8080
134. After plugging a cable into a computer, a user reports there is no network access. Which of the following tools would the technician MOST likely check to verify that the cable was crimped correctly?
A. Punch down tool
B. Cable certifier
C. Loopback plug
D. Toner probe
135. Which of the following DNS records would allow for a website to have more than one FQDN?
A. TXT
B. PTR
C. MX
D. CNAME
136. A small office home office (SOHO) customer is going to be replacing their switch. The customer also wants to add a WAP in a dropped ceiling; however, there are no power outlets above the drop ceiling, but there is a CAT5e network jack. Which of the following technologies should the new switch have to allow this WAP to be placed where the customer requests, without any other major changes to the environment?
A. PoE
B. Layer 3 switching
C. STP
D. VLAN
137. Tenants access multiple wireless networks in a building. Users report intermittent connectivity.
Which of the following is the MOST likely cause of the problem?
A. The channels are overlapping with other wireless networks and should be changed.
B. The SSIDs are incompatible and should be renamed.
C. The users have incompatible wireless network cards and should upgrade.
D. The default idle period for logoff is too short and should be changed to a longer limit.
138. Which of the following BEST describes how a layer 2 switch functions?
A. Switches packets within the same subnet based on MAC addresses
B. Switches packets between different subnets based on IP addresses
C. Switches packets between different subnets based on MAC addresses
D. Switches packets between different subnets based on MAC addresses
139. Jeff, a technician, has been asked to add a subnet to the company’s LAN. Which of the following interfaces on the router will be modified?
A. FastEthernet 0/0
B. AUX 0
C. Console 0
D. Serial 0/0/0
140. Jeff, a network engineer, is troubleshooting an issue where clients are not receiving IP addresses from a new, properly configured DHCP server on another subnet. Statically addressed clients can get onto the same network with no issues. Which of the following is causing the issue?
A. Incorrect VLAN tagging
B. Missing helper addresses
C. Wrong default gateway
D. Improper routing protocols
141. Which of the following subnet masks would allow for 192.168.0.3 and 192.168.0.240 to be in the same subnet?
A. 255.255.255.0
B. 255 255.255.128
C. 255.255.255.192
D. 255.255.255.248
142. Jeff, an administrator, has just finished installing a new switch and connected two servers with IPs of 192.168.105.20 and .30. The servers are able to communicate with each other, but are unable to reach the Internet. Jeff sees the following information in the switch configuration:
interface VLAN 105 IP address 192.168.105.5 255.255.255.0
Jeff is able to ping the router at 192.168.105.1 from the switch.
Which of the following is the MOST likely cause of the problem?
A. The subnet mask is incorrect.
B. A routing loop has occurred.
C. Jeff used a crossover cable to connect the switch to the gateway.
D. The server is missing default-gateway information.
143. Kim, a user, took a laptop on vacation and made changes to the configuration in order to use the device at the hotel. She can reach the Internet, but cannot access any internal network resources.
Which of the following is the MOST likely reason?
A. Incorrect DNS
B. Incorrect subnet mask
C. Duplicate IP address
D. Incorrect SSID
144. Which of the following is the default subnet mask for a Class B address?
A. 255.0.0.0
B. 255.255.0.0
C. 255.255.255.0
D. 255.255.255.255
145. Which of the following default ports would need to be disabled to block TFTP traffic?
A. 20
B. 21
C. 69
D. 123
146. Which of the following ports would Zach, a technician, need to open on a firewall to allow SSH on the default port?
A. 20
B. 21
C. 22
D. 23
147. Which of the following ports is the default telnet port?
A. 20
B. 21
C. 22
D. 23
148. Which of the following ports would have to be allowed through a firewall to allow SNMP traffic to pass on its default port? (Select TWO).
A. 22
B. 23
C. 143
D. 161
E. 162
F. 8080
149. Which of the following has a maximum transfer rate of 54Mbps and operates at the 5GHz frequency?
A. 802.11a
B. 802.11b
C. 802.11g
D. 802.11n
150. Kim, a network technician, is installing an 802.11n network. Which of the following should Kim enable to ensure that the network only allows 802.11n clients?
A. Name the SSID on the 802.11n network only
B. Limit the DHCP address pool
C. Disable 802.11b and 802.11g
D. Only use WPA encryption
151. Zach, a technician, is installing an 802.11n network. Which of the following should he disable to stop broadcasting the network name?
A. Channel
B. WEP
C. SSID
D. WPA
152. Which of the following default services uses TCP/UDP port 88?
A. LDAP
B. IGMP
C. HTTP
D. Kerberos
153. Which of the following ports should be allowed through a firewall to allow DNS resolution to occur to an outside DNS server?
A. 20
B. 53
C. 80
D. 3389
154. Which of the following uses port 53 by default?
A. RDP
B. QoS
C. DHCP
D. DNS
155. Which of the following ports does DHCP use? (Select TWO).
A. 22
B. 23
C. 67
D. 68
E. 69
156. Lisa, a network administrator, needs to allow all websites to be accessible by the sales team for business purposes. Which of the following ports need to be enabled on the firewall? (Select TWO).
A. 23
B. 25
C. 53
D. 80
E. 443
157. Lisa, a technician, is asked to not allow FTP traffic on a network. Which of the following ports should be blocked on the firewall to achieve this?
A. 21
B. 22
C. 23
D. 25
158. Which of the following ports are MOST commonly used to interactively configure a networking device? (Select TWO).
A. 21
B. 22
C. 23
D. 53
E. 67
158. A technician is diagnosing an issue with a new T1 connection. The router is configured, the cable is connected, but the T1 is down. To verify the configuration of the router, which of the following tools should the technician use?
A. Loopback adapter
B. Cable tester
C. Tone generator
D. Multimeter
159. In order to reduce spam email, Kim, a network administrator, changes the standard SMTP port from which of the following port numbers to port number 587?
A. 20
B. 21
C. 23
D. 25
160. A company would like all HTTP traffic to filter through a proxy server on port 8080. Which of the following port numbers needs to be redirected through the proxy server to accomplish this?
A. 20
B. 80
C. 143
D. 443
161. A company wants to only allow incoming HTTP and HTTPS traffic on their public wireless network. Which of the following port numbers should be the only allowed open ports on the firewall to accomplish this? (Select TWO).
A. 20
B. 80
C. 143
D. 443
E. 8080
162. An organization has installed a new firewall. Users need to have access to remote websites and must be able to use SSH to retrieve files from remote locations. Which of the following actions should be taken on the new firewall? (Select TWO).
A. Allow UDP port 21 outbound
B. Allow UDP port 22 outbound
C. Allow UDP port 80 outbound
D. Allow TCP port 21 outbound
E. Allow TCP port 22 outbound
F. Allow TCP port 80 outbound
163. An organization recently installed a firewall on the network. Employees must have access to their work computer from their home computer. In which of the following ways should the firewall be configured?
A. Allow TCP port 3389 outbound
B. Allow UDP port 3389 inbound
C. Allow UDP port 3389 outbound
D. Allow TCP port 3389 inbound
164. An organization recently installed a firewall on the network. Employees must be able to send and receive email from a POP3 server. In which of the following ways should the firewall be configured? (Select TWO).
A. Allow TCP port 23
B. Allow TCP port 25
C. Allow TCP port 110
D. Allow UDP port 25
E. Allow UDP port 110
165. Which of the following protocols uses port 3389?
A. IMAP
B. DHCP
C. SSH
D. RDP
166. Kurt, a network technician, has configured a new firewall on the network. Users are reporting errors when attempting to access several websites. Kurt attempts to access several popular websites with no errors, however, he does receive an error when attempting to access a bank website. Which of the following rules would BEST allow access to the bank website?
A. Allow UDP port 53
B. Allow TCP port 80
C. Allow UDP port 340
D. Allow TCP port 443
167. attempting to access a popular website. Which of the following will MOST likely correct the error?
A. HTTP uses UDP
B. DNS port 23 needs to be allowed
C. HTTP needs port 443 allowed
D. UDP port 53 needs to be allowed
168. A network technician needs to address bandwidth issues on the wireless network. There are currently four 802.11n access points. The technician would like to increase the bandwidth. Which of the following would be the BEST solution?
A. Disable SSID
B. Channel bonding
C. MIMO
D. Increase the signal
169. An administrator is receiving reports from an executive that the executive’s wireless access point loses the signal frequently, even though the WAP is on the executive’s desk. The office contains four other 802.11n access points. Which of the following would MOST likely correct interference problems in the executive’s office?
A. Turn off SSID broadcasting for the executive’s access point
B. Replace the 802.11n access point in the office with an 802.11a access point.
C. Change the channel on the access point to channel 11.
D. Turn off as many lights in the executive’s office as possible to reduce interference.
170. A network technician needs to install an additional access point to the company’s wireless network. The network has two 802.11b access points. Which of the following channels should be used to allow the access point’s coverage areas to overlap?
A. 1, 6, 11
B. 2, 5, 10
C. 3, 13, 23
D. 4, 8, 16
171. Kim, a network administrator, is seeing workstations in building C authenticate to the building A wireless access point. Which of the following would resolve this issue?
A. Change the security method
B. Reduce the transmission power
C. Change the SSID
D. Change the frequency
172. An 801.11g wireless access point was configured as follows:
- AP encryption forced to WPA2-AES mode only - MAC address filtering enabled with the following MAC address in the allow list: 00-ab-29-da-c3-40
Which is true about the above configuration?
A. Any 802.11b/g compatible client can connect to the wireless network if they support TKIP, the MAC address is 00-ab-29-da-c3-40, and the encryption key is known by the client.
B. An 802.11a compatible client can connect to the wireless network only if its MAC address is 00- ab-29-da-c3-40 and the encryption key is known by the client.
C. An 802.11n compatible client can connect to the wireless network only if its MAC address is 00- ab-29-da-c3-40 and the encryption key is known by the client.
D. Any 802.11g compatible client can connect to the wireless network if the encryption key is known by the client.
173. Jeff, a business owner, has discovered that several of the nearby businesses have wireless networks. Jeff wants to implement a unique wireless network inside the business. Which of the following should be configured on the wireless access point to reduce interference from the other wireless networks?
A. PPPoE authentication
B. MAC filtering
C. WPA encryption
D. Wireless channel
174. A company only wants preapproved laptops to be able to connect to a wireless access point.
Which of the following should be configured?
A. SSID disable
B. ACL rules
C. WPA encryption
D. MAC filtering
175. company wants the public to be able to connect to the wireless network with minimal security, but not be able to connect to the private internal network. Which of the following firewall rules would BEST accomplish this?
A. Content filtering on the wireless access point
B. Allow traffic from the wireless access point
C. Block traffic from the wireless access point
D. Packet filtering on the wireless access point
176. Which of the following occurs when antenna gain is increased on an access point?
A. Connection speeds decrease
B. Throughput decreases
C. Cell size increases
D. Attenuation increases
177. Which of the following technologies allows more than two transceivers with an access point?
A. MIMO
B. FIFO
C. 802.1x
D. WPA
178. Jeff, a customer, has a wireless network and has reported that the network traffic from the wireless access points seems high compared to the limited number of wireless devices used. Jeff believes that other non-employees are using the wireless network to access the Internet. Which of the following could be used to limit the access to the wireless network? (Select TWO).
A. WPA encryption
B. Changing wireless channels
C. MAC filtering
D. Changing wireless speed standards
E. SSID disable
179. Kim, a technician, is configuring an 802.11n access point. Other WAPs on the network use 802.11b. Which of the following will Kim have to setup to make sure these WAPs will be able to communicate?
A. Enable mixed mode
B. Disable SSID
C. Disable encryption
D. Enable `n’ only mode
180. Lisa, an administrator, has set up an 802.11n wireless network. Users with 802.11n laptops have reported that speeds are slow. After testing, Lisa determines that users max out at 802.11g speeds. Which of the following would MOST likely fix this issue?
A. Enable wireless multimedia (WMM) for QoS
B. Use the 40MHz channels in the 2.4GHz band
C. Enable access point antenna isolation
D. Limit the clients to 802.11g compatible laptops
181. Zach, a network administrator, needs to purchase a new switch to support VoIP phones and wireless access points in a new building. Which of the following features are the MOST important for the new switch to support?
A. PoE and QoS
B. LACP and OSPF
C. 802.1x and 802.11n
D. NAT and VTP
182. Which of the following would Kim, a technician, do to monitor remote traffic through an access point?
A. Enable an SNMP agent
B. Enable network mapping
C. Set monitoring SSID
D. Select WPA2
183. Which of the following solutions will detect and disable a rogue access point?
A. Port scan
B. Packet sniffer
C. IPS
D. IDS
184. When configuring a wireless access point, Zach, a network administrator, needs to determine the MAC address of a local printer. Which of the following commands would be MOST helpful in determining the MAC address?
A. ping
B. arp
C. route
D. dig
185. Kim, the client, has requested a cost-effective network solution to accommodate the ability to reconfigure the office space as needed. Which networking solution would provide the BEST solution?
A. Private IP Addressing
B. Wireless Access Points
C. Wide Area Networking
D. Virtual Local Area Networks
186. A SOHO office recently installed a wireless network for employees to use during lunch breaks. As such, the access point was placed in the kitchen area by the microwave. Employees have been reporting intermittent connectivity when using the wireless network. Which of the following would BEST improve connectivity?
A. Disable SSID broadcast
B. Increase the signal strength
C. Move the access point
D. Change the broadcast channel
187. A SOHO with ten Wi-Fi equipped laptops needs a new network installed. Which of the following items would be used to setup the office using a new DSL line? (Select TWO).
A. Router
B. Wi-Fi Access point
C. Cable modem
D. Ten WiMAX adapters
E. Ten CAT6 patch cables
188. Which of the following security threats relies primarily on user deception and misinformation?
A. Rogue access points
B. DoS attacks
C. Man-in-the-middle attacks
D. Phishing
189. Which of the following is the prefix for a link-local IPv6 address?
A. FE80::/10
B. FF00::/8
C. 2FFE::/16
D. FEEF:/12
190. Which of the following could be used to estimate RTT across a router?
A. Dig
B. Traceroute
C. Arp
D. Uptime
191. Which of the following does the IP address 169.254.222.10 indicate?
A. No DHCP server connectivity
B. The DNS server is unavailable
C. Firewall issue
D. Duplicate IP addresses are found
192. A network administrator notices that all of the company switches are running at capacity on a given day, which is abnormal according to network baselines taken recently. Which tool would BEST allow the administrator to inspect what type of traffic is on the network?
A. Wire tap
B. Network sniffer
C. Load balancing appliance
D. NIPS
193. A supervisor requests that a technician downloads a MIB for a particular server.
Which of the following protocols requires MIBs?
A. IPSec
B. SSL
C. ISAKMP
D. SNMP
194. When configuring a WAP for a SOHO, which parameter will BEST limit access to the office area?
A. Signal strength
B. SSID enable
C. Encryption
D. Password hardening
195. Which of the following should be implemented in a networked environment carrying teleconferencing packets?
A. L2TP
B. SSH
C. QoS
D. SNMP
196. Lisa, a network technician, needs to introduce a few more cables to the existing patch panel. Which of the following tools would she use?
A. OTDR
B. Multimeter
C. Punch down tool
D. Temperature monitor
197. A network technician is installing a simple SOHO router with wireless functionality. Which of the following wireless encryption standards would be BEST suited for the HIGHEST level of security?
A. WPA2
B. WPA
C. WEP64
D. WEP128
198. A technician notices that network access is becoming increasingly slow. All of the activity lights, on the only network layer 2 switch, are blinking at steadily increasing rates. Which of the following is the MOST likely cause of the increased traffic?
A. STP blocking
B. IP addresses
C. MTU mismatch
D. Switching loop
199. A user wants a SOHO network to be protected from unauthorized users hacking their network. Which of the following should be implemented to aide in this matter?
A. VPN
B. Throughput tester
C. Firewall
D. OC3
200. Zach, a technician, suspects a duplicate IP address assignment on the network. Which of the following resources can be used to verify this problem?
A. Network map
B. Environmental monitor
C. Placement map
D. Syslog
201. Which of the following protocols are used for accessing a command line terminal session for management purposes? (Select TWO).
A. Telnet
B. FTP
C. SNMP
D. SSH
E. RDP
202. A user is getting very weak signals while trying to connect to the wireless. Which of the following should the user do to help with signal strength?
A. Call the wireless provider and ask for a T3 circuit.
B. Move the wireless router to a better location where line of sight is obtained.
C. Reinstall the operating system to the PC to ensure the newest patches are installed.
D. Install a hub to ensure there is a clear path for the cables to run.
203. Lisa, a consultant, is inspecting an office that reports frequent wireless issues. Upon scanning the network broadcasting in the vicinity of the office, seven SSIDs are found. The company’s Wi-Fi network and three others all share channel six. Which of the following is MOST likely causing the issue?
A. Frequency interference
B. Low signal strength
C. Standard mismatch
D. Incorrect channel
204. Kim, a user, cannot access the network using wireless.
Which of the following is MOST likely the cause?
A. TXRX is reversed
B. Faulty crossover cable
C. Incorrect WEP key
D. A short in the cable pairs
205. A network administrator wants to monitor traffic by deploying MIBs. Which of the follow network monitoring resources would be used?
A. SCTP
B. Packet sniffer
C. DCCP
D. SNMP
206. Kim, a technician, is installing a switch that does not feature auto-negotiation. Which of the following characteristics would need to be manually configured? (Select TWO).
A. MAC addressing
B. IP addressing
C. Port speed
D. IPv6 addressing
E. Duplex
207. Zach, a technician, discovers a switch is not communicating with the other switches in a stack. Which of the following is the MOST likely cause?
A. Both T568A and T568B standards are being used.
B. STP is disabled.
C. The cable is not a crossover.
D. The port is not trunked.
208. Which of the following technologies allows for redundant links within a Layer 2 segment?
A. OSPF
B. RIP
C. Port Mirroring
D. Spanning Tree
209. A company has attempted to introduce a new major network segment to allow growth in capacity. On the core switch, a GBIC was used to interconnect with a newly placed downstream distribution switch for the first time. Soon after this implementation, a network flood and an outage occurred between the core and new distribution network modules. Which of the following should the network administrator troubleshoot FIRST in order to rectify the issue?
A. Check for switching loops between core and distribution switches.
B. Check whether an incorrect VLAN has been assigned to the new distribution switch.
C. Check for inconsistent or missing routes between the core and distribution switches.
D. Check whether the GBIC was set to multi-mode instead of single-mode SFP.
210. Which of the following is used to create a secure connection between a client and a host?
A. VLAN
B. Proxy server
C. IIS server
D. VPN
211. A user reports a network failure on a computer. The technician determines that the computer and NIC are operating properly. Which of the following tools can the technician use to trace the network cabling back to the punch down block?
A. Protocol analyzer
B. Multimeter
C. Punch down tool
D. Toner probe
212. Several users from the same building are reporting connectivity issues. The SFP at that building’s IDF switch is showing a link light, but there is no link light to the corresponding switch’s SFP at the MDF.
Which of the following is the MOST likely cause?
A. A crossover cable is being used.
B. DB loss is too high on all strands.
C. Only TX or RX strand is working.
D. TX and RX are reversed.
213. Which of the following is the correct representation of an IPv6 address?
A. ::
B. 0:0:0:0:0:0:0:0:1
C. 1:2:3:4:AB:CD:EF
D. 2001::4860:800f::
214. Which of the following 802.11n features allows for the use of multiple simultaneous frequencies in order to increase usable bandwidth?
A. Channel bonding
B. MIMO
C. Spartial reuse
D. 20MHz channel spacing
215. Kim, a network administrator, should consult which documentation sources FIRST to determine the cause of recent network issues?
A. Network map
B. Cable management
C. Change management
D. Asset management
216. The network optimization process used to allow reasonable use of data, voice, and video on the same network infrastructure is called:
A. CARP
B. QoS
C. Traffic shaping.
D. Fault tolerance.
217. A network administrator is troubleshooting an intermittent network issue between devices that have a particularly long cable run. The issue was escalated to a network designer who alluded to potential attenuation issues. Which of the following BEST describes what the network designer was referring to?
A. Bad connectors
B. Cross-talk
C. EMI / Interference
D. dB loss
218. An analog POTS voice line is no longer working and Kim, the technician, is tasked to verify if a dial tone is present at the IDF. Which of the following tools would be used?
A. Protocol analyzer
B. Butt set
C. OTDR
D. Toner probe
219. A network technician is troubleshooting intermittent issues with VoIP call quality. A throughput tester can help assess the functionality of which of the following?
A. LLDP
B. VLAN tagging
C. QoS
D. SIP trunking
220. Lisa, a user, reports increased delays and timeouts when trying to reach several Internet sites. Which of the following would MOST likely be used when investigating the problem at Lisa’s workstation?
A. nslookup
B. route
C. nbtstat
D. arp
221. Which of the following utilities would a technician use to determine the location of lost packets on a routed network?
A. ping
B. nslookup
C. route
D. tracert
222. A DSL modem connects to the provider’s network using which of the following authentication techniques?
A. PoE
B. MS-CHAP
C. PPPoE
D. EAP
223. Jeff, a user, is having a problem with a POTS line. Which of the following tools would Jeff use to make sure the phone lines have a dial tone?
A. Loopback plugs
B. Butt set
C. Cable certifier
D. Toner probe
224. 169.254.0.100 is an IP address which would MOST likely come from which of the following?
A. CIDR
B. DHCP
C. APIPA
D. DNS
225. Zach, a technician, is checking newly installed CAT5e cabling, and suspects that some of the ends were not properly terminated. Which of the following tools will verify this?
A. Cable tester
B. Toner probe
C. OTDR
D. Loopback plug
226. Which of the following DNS records allows for reverse lookup of a domain?
A. PTR
B. AAAA
C. A
D. MX
227. Which of the following is an example of two factor authentication?
A. Password, device certificate and PIN
B. SSL web server certificate and password
C. User password and administrator password
D. Password and hardware token OTP
228. Which of the following IP addresses would be classified as private?
A. 10.100.200.0
B. 169.253.10.20
C. 172.168.5.0
D. 200.100.25.0
229. A network technician wants to baseline traffic flows on a specific network. Which of the following will provide the GREATEST level of detail?
A. Network flow information
B. SNMP traps
C. Debug level syslog
D. Protocol analyzer
230. Which of the following will prevent switching loops by selectively shutting down switch ports?
A. RIP
B. IGP
C. STP
D. VLAN
231. When using high bandwidth applications over multiple WAN connections, which of the following should be used?
A. Static IP addressing
B. Half-duplex
C. PoE devices
D. Load balancing
232. A network technician is trying to terminate CAT5 modular jacks. Which of the following tools would be MOST appropriate for this scenario?
A. Crimper
B. OTDR
C. Throughput tester
D. Punch down tool
233. Which of the following media types can carry a standard Ethernet signal for network connectivity?
A. USB
B. PArallel
C. Serial
D. CAT6
234. There is suspected virus activity on the network. Which of the following would Lisa, a technician, use to study network traffic?
A. Protocol analyzer
B. Cable tester
C. Cable certifier
D. Environmental monitor
235. Zach, a network technician, is configuring several switches to be managed remotely. Which of the following must be configured to connect via SSH to each of those devices, as well as to retrieve various parameters?
A. PoE settings and VTP configuration
B. SNMP configuration only
C. IP address and SNMP configuration
D. QoS and PoE settings
236. A Windows server has a problem after booting up. Kim, a technician, should immediately check the:
A. history logs.
B. cron logs.
C. application logs.
D. system logs.
237. A user has no network connectivity. Jeff, the network technician, is unable to locate the CAT5e cable from the user at the IDF. Which of the following tools would be used to assist Jeff in locating the CAT5e cable?
A. Butt set
B. Punch down tool
C. Toner probe
D. D. Protocol analyzer
238. An administrator is setting up a secure wireless network. The administrator decides to support 802.11n and 802.11g with a WPA2 pre-shared key. Users are given the SSID with the pre-shared key, but the administrator has disabled the SSID broadcast and MAC filtering. Some users have reported connection issues. Which of the following would MOST likely resolve the users’ connection issues?
A. Limit the devices to 802.11n only.
B. Enable the SSID broadcast.
C. Enable MAC filtering.
D. Use a WEP 128-bit key.
239. Which of the following protocols is used to securely connect to a multi-layer switch?
A. HTTP
B. SMTP
C. SSH
D. Telnet
240. The software in a virtualized environment that controls resource allocation and allows multiple operating system guests to run on the same physical platform is known as the:
A. hypervisor.
B. LPAR.
C. broker.
D. VDI.
241. A new monitoring device is installed in the network that uses ping to determine whether critical network Internet routers are up. After three missing pings, the alarm reports the device is down. The device is now constantly reporting alarms, yet there are no reported Internet problems from users.
Which of the following is the MOST likely cause?
A. A missing route on the alarm device.
B. Incorrect VLAN assignment on the router.
C. A missing route on the network routers.
D. Incorrect speed/duplex setting on the alarm device.
242. A customer wishes to network several computers throughout a large warehouse containing numerous metal shelves and concrete walls. The computers are at least 175 meters (574 feet) apart. Which of the following media types should be recommended for the customer using only a single switch?
A. Fiber optic
B. Wireless
C. CAT5e
D. CAT3
243. A network administrator suspects an employee of using the company’s Internet connection to download illegal content. Which of the following can be used to inspect ongoing network traffic?
A. Syslog server
B. Toner probe
C. OTDR
D. Packet sniffer
244. A technician is setting up a firewall on the network that would show a public IP address out to the Internet and assign private IP addresses to users inside the network. Which of the following processes should be set up?
A. Port security
B. MAC filtering
C. ACL
D. NAT
245. Two WAPs are positioned with overlapping coverage, but seamless roaming across them is not working. Which of the following should be checked?
A. WPA should be enabled
B. PKI should be turned off
C. WAP SSIDs are matching
D. WAPs are transmitting on same channel
246. No link lights on a switch’s SFP are functioning, so the network technician re-terminates the end. After testing the cable, the tester is showing a db loss of-9. Which of the following types of cable is MOST likely being tested?
A. Fiber
B. CAT3
C. CAT5e
D. CAT6a
247. An administrator has received a recommendation against deploying WEP as a wireless encryption protection scheme. Which of the following is MOST likely the reason?
A. WEP’s IV is too small.
B. WEP uses RC4 which is easily accessible and not secure.
C. WEP uses plain text.
D. WEP is not well supported.
248. Jeff, a network technician, is installing a wireless router. Which of the following should Jeff consider to get the BEST signal strength?
A. WAP placement
B. PoE devices
C. MAC filtering
D. Encryption type
249. Which of the following devices can be used to offload outbound web server SSL encryption overhead?
A. NIPS
B. Proxy server
C. Content filter
D. VPN connectator
250. A user snapped the retention tab off of a network cable. Which of the following tools would Jeff, a technician, use to replace the RJ-45 connector?
A. Wire tester
B. Punch down
C. Crimper
D. Multimeter
251. Which of the following methods for network performance optimization is used to distribute traffic among similar devices?
A. Fault tolerance
B. QoS
C. Proxy server
D. Load balancing
252. A user is unable to connect to a server in another building. A technician is troubleshooting the issue and determines the following:
1) Client PC 1 has an IP address if 192.168.10.25/25 2) PC 1 can successfully ping its gateway of 192.168.10.1/25 which is an interface of router A 3) Server A is named 'BLDGBFILESRVR01' and has an IP address of 192.168.10.145/25 4) PC 2 with an IP address of 192.168.10.200/25 can successfully ping server A
However, when PC 1 pings server A, it receives a destination host unreachable responds. Which of the following is the MOST likely cause?
A. Link from touter A to PC 1 are on different subnets
B. Link from router A to server A is down
C. Link from PC 1 to router A has duplex issues
D. Link from server A top PC 2 is down
253. A technician needs to limit the amount of broadcast traffic on a network and allow different segments to communicate with each other. Which of the following options would satisfy these requirements?
A. Add a router and enable OSPF.
B. Add a layer 3 switch and create a VLAN.
C. Add a bridge between two switches.
D. Add a firewall and implement proper ACL.
Explanation:
We can limit the amount of broadcast traffic on a switched network by dividing the computers into logical network segments called VLANs.
A virtual local area network (VLAN) is a logical group of computers that appear to be on the same LAN even if they are on separate IP subnets. These logical subnets are configured in the network switches. Each VLAN is a broadcast domain meaning that only computers within the same VLAN will receive broadcast traffic.
To allow different segments (VLAN) to communicate with each other, a router is required to establish a connection between the systems. We can use a network router to route between the VLANs or we can use a `Layer 3′ switch. Unlike layer 2 switches that can only read the contents of the data-link layer protocol header in the packets they process, layer 3 switches can read the (IP) addresses in the network layer protocol header as well.
254. A technician is connecting a router directly to a PC using the G1/0/1 interface. Without the use of auto-sensing ports, which of the following cables should be used?
A. Straight-through
B. Console
C. Rollover
D. Crossover
255. A company finds that many desktops are being reported as missing or lost. Which of the following would BEST assist in recovering these devices?
A. Asset tracking tags
B. Motion detectors
C. Security guards
D. Computer locks
256. A company is experiencing accessibility issues reaching services on a cloud-based system.
Which of the following monitoring tools should be used to locate possible outages?
A. Network analyzer
B. Packet analyzer
C. Protocol analyzer
D. Network sniffer
Explanation:
A network analyzer is a useful tool, helping you do things like track traffic and malicious usage on the network.
257. A network administrator has created a virtual machine in the cloud. The technician would like to connect to the server remotely using RDP.
Which of the following default ports needs to be opened?
A. 445
B. 3389
C. 5004
D. 5060
258. Which of the following cloud infrastructure designs includes on premise servers utilizing a centralized syslog server that is hosted at a third party organization for review?
A. Hybrid
B. Public
C. Community
D. Private
259. An administrator hosts all of the company’s virtual servers internally. In the event of total server failure, the server images can be restored on a cloud provider and accessed through the VPN. Which of the following cloud services is the administrator using?
A. Community PaaS
B. Public Iaas
C. Hybrid Saas
D. Private Iaas
260. Which of the following should be performed to verify that unnecessary services are disabled on all switches in an environment?
A. packet capturing
B. port scanning
C. Log scanning
D. Baseline review
261. A technician is assigned to secure a basic wireless network. Which of the following authentication protocol should the technician use to performed this task (select TWO).
A. RDP
B. SNMP
C. WPA2
D. EAP SSL
262. A technician is sent to a remote office to set up a device to connect to the internet. The company Standard document requires stateful inspection. Which of the following should the technician install?
A. ROUTER
B. Multilayer switch
C. Firewall
D. Bridge
263. A system administrator receives report from users of odd behavior in regard to recently installed server. While reviewing the server network configuration, the systems administrator does both a forward and a reverse DNS lookup on the host, along with the network adapter configuration.
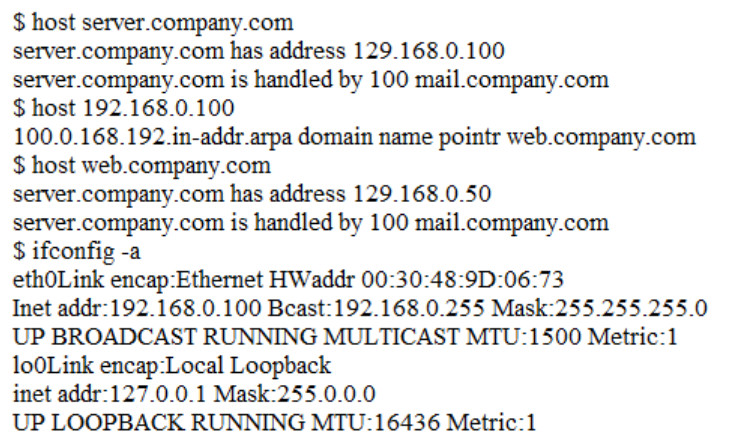
Which of the following is the problem identified in the output above?
A. There is no reverse DNS entry for this host.
B. The server IP address is incorrectly configured.
C. The DNS lookup entry is incorrectly configured.
264. A technician is investigating the cause of a network outage. Which of the following documents should be checked to rule out configuration issues?
A. charge management records
B. inventory management
C. Network log files
D. Logical diagrams
265. A junior network technician receives a help desk ticket from an end user who is having trouble accessing a web application that was working the previous day. After talking with the end user and gathering information about issue, which of the following would be the most likely course of action for the technician to perform next?
A. Establish a theory of probable cause.
B. Escalate the ticket to a senior technician.
C. Implement the solution.
D. Document the findings and outcomes.
266. Which of the following storage network technologies inherently leverages block-level storage?
A. NAS
B. SAN
C. FCoE
D. iSCSI
E. FTP
267. A network administrator wants to employ a username and password authentication system for guest WiFi. Which of the following is the BEST option to provide this type of authentication?
A. port security
B. MAC filtering
C. Network access control
D. Captive portal
268. Multiple users are reporting that they are unable to access the network. The ENTIRE network is shown in the diagram. PCs are not statically assigned IP addresses. The following devices will display settings:
WorkstationA
WorkstationB
WorkstationC
WorkstationD
WorkstationE
WorkstationF
WorkstationG
Laptop1
Laptop2
DHCP server1
DHCP server2
Review the settings and select the box in the diagram that identifies the device causing the issue. Only one device can be selected at a time.
After checking the device that is causing the issue, select the second tab in the lower left hand corner. Identify the reason as to why some users are unable to access the network.
Instructions:
When the simulation is complete, select the Done button to submit.
Part 1
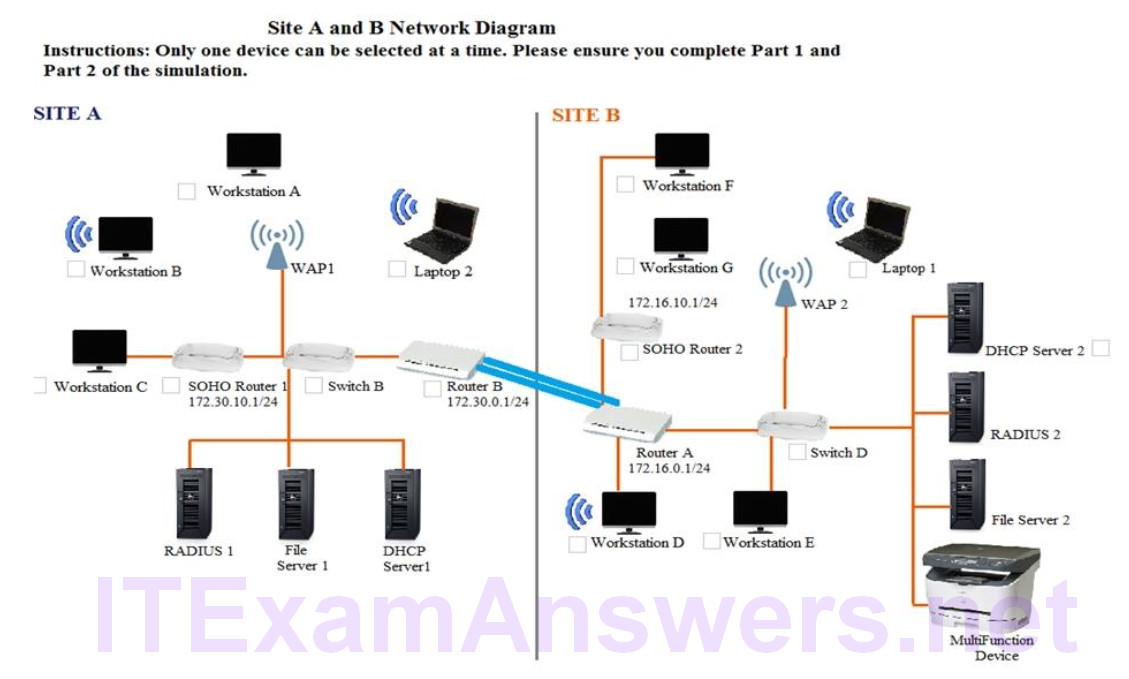
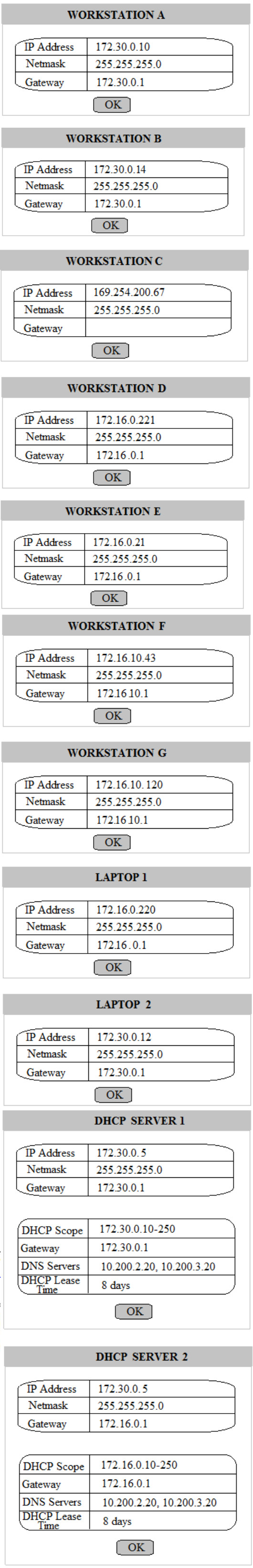
Part 2
Identify the reason as to why some users are unable to access the network.
A. Workstation(s) are plugged into switch ports configured with half duplex
B. The site-to-site router was configured with the incorrect ACL
C. DHCP server scope is full and is not providing IP addresses
D. WAN and LAN ports are reversed on the router
E. STP has disabled some of the ports on the switch
F. The NIC driver is not installed
G. A wireless client is unable to associate to the AP
269. A UTM is deployed on the external edge of the main corporate office. The office connects to the WAN port of the edge router. The edge router at the main office connects to the remote offices using GRE IPSec tunnels. A network administrator notices that a worm that was not detected by the UTM has spread from the remote sites into the corporate network. The UTM currently has traffic rules applied that should block the port used by the worm. Which of the following steps would MOST likely correct this issue?
A. Move the UTM onto the LAN side of the network
B. Enable TLS inspection on the UTM
C. Enable stateful inspection on the UTM
D. Configure the UTM to deny encrypted files from being transferred
270. A technician has racked a new access switch and has run multimode fiber to a new location. After installing an extended-range 10Gb SFP in the core switch, the technician installed a 10Gb SFP in the access switch and connected the port to the new extension with a fiber jumper. However, the link does not display, and the technician cannot see light emitting from the core switch. Which of the following solutions is MOST likely to resolve the problem?
A. Swap the fiber pairs in one of the SFPs
B. Replace the jumpers with single-mode fiber
C. Set the correct MTU on the new interface
D. Install an optic that matches the fiber type
271. A network technician has implemented ACLs to limit access to cloud-based file storage. Which of the following security mechanisms has the technician enforced?
A. DLP
B. IDS
C. WAF
D. WPA
E. TPM
272. A network technician receives a call from a user in the accounting department stating that Internet connectivity has been lost after receiving a new workstation. No other users in accounting are reporting similar issues. The network technician is able to ping the machine from the accounting department’s router, but is not able to ping the machine from the IT network. Which of the following is MOST likely the cause?
A. Incorrect default gateway
B. Duplicate IP address
C. Misconfigured OSPF
D. Improper VLAN assignment
273. A firewall administrator is implementing a rule that directs HTTP traffic to an internal server listening on a non-standard socket. Which of the following types of rules is the administrator implementing?
A. NAT
B. PAT
C. STP
D. SNAT
E. ARP
274. A technician is installing a new wireless badging system on a hospital network. The requirements of the badging system are for it to have its own SSID and low power levels. The badging system has to cover 99.9% of the hospital. Which of the following is the BEST action to take to meet the system requirements?
A. Install additional WAPs
B. Install external antennas
C. Move the WAPs closer to the more populated area
D. Change the antenna types
275. A technician attempts to replace a switch with a new one of similar model from the same vendor. When the technician moves the fiber and SFP plug, the switch does not completely boot up. Considering that the config files are the same, which of the following is the MOST likely cause of the failure?
A. Damaged fiber
B. Corrupted operating system
C. VLAN mismatch
D. Bad port
276. A company has hundreds of nodes on a single subnet and has decided to implement VLANs. Which of the following BEST describes the benefit of this approach?
A. It segments broadcast domains in the network infrastructure
B. It provides a faster port to all servers
C. It provides multiple collision domains on one switchport
D. It provides multiple broadcast domains within a single collision domain
277. Which of the following uses eight groups of characters for addressing?
A. MAC
B. IPv4
C. IPv6
D. DHCP
278. A pest control contractor attempts to gain access to the datacenter; however, the manager on duty notes that a pest control inspection was not on the schedule. Which of the following attacks is in progress?
A. Phishing
B. Social engineering
C. Man-in-the-middle
D. Smurfing
279. Which of the following is the MOST economical way for Sandy, a technician, to implement 10- Gigabit Ethernet at a datacenter?
A. 10GBaseLR
B. 10GBaseSR
C. 10GBaseX
D. 10GBaseT
280. Which of the following is the network topology in which computers connect in a closed circle?
A. Bus
B. Mesh
C. Ring
D. Star
281. Which of the following protocols would Kurt, a technician, use to synchronize local date and time of a client workstation to that of a server?
A. RTP
B. NTP
C. TFTP
D. ARP
282. An administrator is replacing an existing WAP because the customer is reporting that the connection speeds are too slow. Which of the following should be installed?
A. 802.11a
B. 802.11b
C. 802.11g
D. 802.11n
283. Which of the following cables has the MOST twists per inch?
A. CAT3
B. CAT5
C. CAY5e
D. CAT6
284. Which of the following is true about an IP address if the first bit is a one and the second bit is a zero?
A. The address is a Class A address.
B. The address is a Class B address.
C. The address is a Class C address.
D. The address is a Class D address.
285. Which of the following cables is MOST likely to be terminated into a patch panel?
A. Serial
B. RG-6
C. RG-59
D. CAT6
286. Which of the following security mechanisms dynamically assigns a Layer 2 address and restricts traffic only to that Layer 2 address?
A. Sticky MAC
B. 802.1x
C. ACL
D. NAC
287. Which of the following is a vulnerable system designed to detect and log unauthorized access?
A. SIEM
B. Honeypot
C. DMZ
D. Proxy server
288. According to the OSI model, at which of the following layers is data encapsulated into a packet?
A. Layer 2
B. Layer 3
C. Layer 4
D. Layer 5
E. Layer 6
289. Which of the following WAN technologies is MOST preferred when developing a VoIP system with 23 concurrent channels?
A. DSL
B. POTS
C. T1
D. DOCSIS
290. A junior network technician is setting up a new email server on the company network. Which of the following default ports should the technician ensure is open on the firewall so the new email server can relay email?
A. 23
B. 25
C. 110
D. 143
291. Which of the following policies would Joe, a user, have to agree to when he brings in his personal tablet to connect to the company’s guest wireless Internet?
A. NDA
B. IRP
C. BYOD
D. SLA
292. In a service provider network, a company has an existing IP address scheme. Company A’s network currently uses the following scheme:
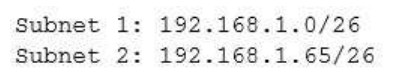
Company b uses the following scheme:
Subnet 1: 192.168.1.50/28
The network administrator cannot force the customer to update its IP scheme.
Considering this, which of the following is the BEST way for the company to connect these networks?
A. DMZ
B. PAT
C. NAT
D. VLAN
293. A technician is troubleshooting a problem with a network printer. The technician thinks the network printer is out of paper and ink. Which of the following should the technician do NEXT?
A. Implement the solution
B. users
C. Test the theory
D. Escalate the problem
294. A company has just installed wireless in their office. In one corner of the office building users are not able to establish a connection. Which of the following can be changed on the AP to help resolve this issue?
A. SSID
B. Channels
C. Signal strength
D. Encryption
295. Which of the following cable types have a rated MAXIMUM bandwidth of 100Mbps?
A. CAT3
B. CAT5
C. CAT5e
D. CAT6
296. A company has installed an access point and configured it to broadcast at 802.11n only. Some users are stating that they cannot connect to this access point. Which of the following is the MOST likely reason some users cannot connect?
A. Incorrect channel
B. Weak encryption
C. Incompatible NICs
D. Incorrect SSID
297. Which of the following will allow multiple frequencies to be combined?
A. WiMAX
B. MPLS
C. MIMO
D. Channel bonding
298. Which of the following technologies is required to allow all ports of a single private IP to be publically accessible via a single public IP?
A. NAT
B. RIP
C. PAT
D. ACL
299. Which of the following allows a technician to gather information about the operating system?
A. Domain services
B. Fingerprinting
C. Countermeasures
D. Reconnaissance
300. Which of the following is indicative of an FTP bounce?
A. Arbitrary IP address
B. Reverse DNS lookups
C. Same Port Number
D. File Transfer Success
301. The software that allows a machine to run multiple operating systems at once is called the:
A. Server manager
B. Hypervisor
C. Boot loader
D. Partition manager
302. Which of the following routing protocols relies on hop count as its ONLY metric?
A. BGP
B. EIGRP
C. OSPF
D. RIP
303. A company has completed construction of a new datacenter, and the IT staff is now planning to relocate all server and network equipment from the old site to the new site. Which of the following should the IT staff reference to determine the location of the equipment being moved?
A. Rack diagrams
B. Network topology
C. Standard operating procedures
D. Wiring documentation
304. Which of the following would allow a device to maintain the same IP address lease based on the physical address of the network card?
A. MAC address reservation
B. Static IP address
C. IP address exclusion
D. Custom DNS server entry
305. A technician wants to prevent an unauthorized host from connecting to the network via Ethernet. Which of the following is a Layer 2 access control the technician should implement?
A. Access control lists
B. Captive portal
C. WPA2
D. Port security
306. A network engineer is configuring wireless access for guests at an organization. Access to other areas in the organization should not be accessible to guests. Which of the following represents the MOST secure method to configure guest access to the wireless network?
A. Guests should log into a separate wireless network using a captive portal
B. Guests should log into the current wireless network using credentials obtained upon entering the
facility
C. The existing wireless network should be configured to allow guest access
D. An additional wireless network should be configured to allow guest access
307. The server team has just installed an application across three different servers. They are asking that all requests to the application are spread evenly across the three servers. Which of the following should the network team implement to fulfil the request?
A. Proxy server
B. UTM appliance
C. Content filter
D. Load balancer
308. A network technician is deploying mobile phones for a company’s sales staff. Salespeople frequently travel nationally and internationally to meet with clients, and often have to roam or switch cellular providers. Which of the following standards is the BEST option to fit the requirements?
A. GSM
B. TDM
C. CDMA
D. PSTN
E. MIMO
309. A network administrator has been given a network of 172.16.85.0/21 and wants to know the usable range of IP addresses on that subnet. Which of the following indicates the correct IP address range?
A. 172.16.80.0-172.16.85.254
B. 172.16.80.0-172.16.88.255
C. 172.16.80.1-172.16.87.254
D. 172.16.80.1-172.16.85.255
310. A network technician is troubleshooting wireless network issues in a crowded office complex and suspects there is interference from nearby wireless networks. Which of the following should the technician perform to discover possible interference?
A. Site survey
B. Vulnerability scanning
C. Wardriving
D. Checking logical diagram
E. Bandwidth test
311. A network technician is troubleshooting an issue and has established a theory of probable cause. Which of the following steps should the network technician take NEXT?
A. Test the possible solution
B. the users
C. Determine what has changed
D. Document the theory
312. Which of the following is the number of broadcast domain that are created when using an unmanaged 12-port switch?
A. 0
B. 1
C. 2
D. 6
E. 12
313. A network engineer wants to a segment the network into multiple broadcast domains. Which of the following devices would allow for communication between the segments?
A. Layer 2 switch
B. Layer 3 switch
C. Bridge
D. Load balancer
314. The Chief Information Officer (CIO) has noticed the corporate wireless signal is available in the parking lot. Management requests that the wireless network be changed so it is no longer accessible in public areas, without affecting the availability inside the building. Which of the following should be changed on the network?
A. Power levels
B. Overcapacity
C. Distance limitations
D. Channel overlap
315. A network technician is assisting the security team with some traffic captures. The security team wants to capture all traffic on a single subnet between the router and the core switch. To do so, the team must ensure there is only a single collision and broadcast domain between the router and the switch from which they will collect traffic. Which of the following should the technician install to BEST meet the goal?
A. Bridge
B. Crossover cable
C. Hub
D. Media converter
316. Based on networks 10.8.16.0/22 and 10.8.31.0/21, which of the following is the BEST summarized CIDR notation?
A. 10.8.0.0/16
B. 10.8.0.0/19
C. 10.8.0.0/20
D. 10.0.0.0/24
317. A technician discovers that multiple switches require a major update. Which of the following policies should be followed?
A. Change management policy
B. Remote access policy
C. Acceptable use policy
D. Memorandum of understanding
318. A technician is troubleshooting a point-to-point fiber-optic connection. The technician is at a remote site and has no connectivity to the main site. The technician confirms the switch and the send-and- receive light levels are within acceptable range. Both fiber SFPs are confirmed as working. Which of the following should the technician use to reveal the location of the fault?
A. OTDR
B. Light meter
C. Tone generator
D. CSU/DSU
319. A Chief Information Officer (CIO) wants to move some IT services to a cloud service offering. However, the network administrator still wants to be able to control some parts of the cloud service’s networking components. Which of the following should be leveraged to complete this task?
A. IaaS
B. PaaS
C. SaaS
D. DaaS
320. Client PCs are unable to receive addressing information from a newly configured interface on a router. Which of the following should be added to allow the clients to connect?
A. DHCP lease me
B. IP helper
C. TTL
D. DNS record type
321. When enabling jumbo frames on a network device, which of the following parameters is being adjusted?
A. Speed
B. Duplex
C. MTU
D. TTL
322. A technician logs onto a system using Telnet because SSH is unavailable. SSH is enabled on the target device, and access is allowed from all subnets. The technician discovers a critical step was missed. Which of the following would allow SSH to function properly?
A. Perform file hashing
B. Generate new keys
C. Update firmware
D. Change default credentials
323. A network administrator wants to ensure sensitive data is not exfiltrated from the system electronically. Which of the following should be implemented?
A. DLP
B. AUP
C. NDA
D. SLA
324. A network technician configures a firewall to block only certain IP addresses from accessing the Internet. All users are reporting that they are unable to access the Internet. Which of the following is the MOST likely reason?
A. Incorrectly configured ACL
B. Implicit allow statement
C. SMTP requests are being denied
D. All protocols are being allowed in
325. A technician wants to connect a new wireless router to a main network switch. Which of the following cable types would MOST likely be used to establish this connection?
A. Telephone
B. Parallel
C. Serial
D. CAT6
326. Zach, a technician, wants to test a laptop’s NIC for functionality but has no other networking equipment to attach it to. Which of the following would allow him to test basic functionality of the NIC?
A. Loopback plug
B. Protocol analyzer
C. Smart jack
D. Coupler
327. A new user is reporting connectivity issues. Zach, the network technician, notices that there is no link light on the user’s NIC. Which of the following would be used to verify the wiring back to the patch panel?
A. Butt set
B. Cable certifier
C. Toner probe
D. Snips
328. Zach, a network technician, is unable to remotely manage or ping certain layer 2 switches. To manage those devices remotely, which of the following will MOST likely need to be configured?
A. IP address on the native VLAN interface
B. Port security
C. Port forwarding
D. IP addres on the fiber interface
329. Which of the following devices is used to distribute network traffic equally over multiple links?
A. Content filter
B. DNS server
C. Load balancer
D. Proxy server
330. Lisa, a technician, has configured a new switch that is remotely accessed using SSH. The switch is working properly but cannot be accessed remotely. Which of the following items is MOST likely missing in the configuration?
A. Port speed
B. Cryptokey
C. Data VLAN
D. NAT/PAT
331. Zach, a technician, needs to terminate a CAT5e Ethernet cable to a 110 block. Which of the following tools should he use?
A. Toner probe
B. Punch down
C. Wire tester
D. Crimper
332. Which of the following protocols is used for remote management of devices?
A. SNMP
B. TFTP
C. Syslog
D. SMTP
333. A mobile user is no longer able to access network resources. Jeff, the network technician, is unable to ping the user’s workstation. Which of the following commands would MOST likely be used on that workstation to verify its current network settings?
A. net share
B. hostname
C. ipconfig
D. tracert
334. Which of the following methods limits access to a network based on characteristics of the network card?
A. IP filtering
B. MAC filtering
C. Port filtering
D. Encryption
335. A company has contracted with an outside vendor to perform a service that will provide hardware, software, and procedures in case of a catastrophic failure of the primary datacenter. The Chief Information Officer (CIO) is concerned because this contract does not include a long-term strategy for extended outages. Which of the following should the CIO complete?
A. Disaster recovery plan
B. Business continuity plan
C. Service level agreement
D. First responder training
336. A typical cell tower will have microwave and cellular antennas. Which of the following network topologies do these represent? (Choose two.)
A. Point-to-multipoint
B. Bus
C. Point-to-point
D. Mesh
E. Peer-peer
F. Ring
337. A network administrator has a monitoring system in place that is currently polling hundreds of network devices at regular intervals. The continuous polling is causing high CPU utilization on the server. Which of the following tasks should the administrator perform to resolve the CPU issue while maintaining full monitoring capabilities?
A. Remove SNMP polling and configure SNMP traps on each network device
B. Remove SNMP polling and implement snmpwalk on each network device
C. Upgrade SNMP to the latest version to mitigate vulnerabilities
D. Modify SNMP polling to poll only during business hours
338. A contractor is setting up and configuring conference rooms for a convention. The contractor sets up each room in the conference center to allow wired Internet access going to individual tables. The contractor measured the distance between the hotel’s patch panel to the jack, and the distance is within Cat 5e specifications. The contractor is concerned that the room will be out of specification if cables are run in each room from the wall jacks. Which of the following actions should the contractor take to ensure the cable runs meet specifications and the network functions properly?
A. Place a switch at the hotel’s patch panel for connecting each room’s cables
B. Place a switch on each table to ensure strong connectivity
C. Place repeaters between the patch panel and the rooms
D. place a switch at the wall jack and run the cables in the room from there
339. Users are reporting their network is extremely slow. The technician discovers pings to external host have excessive response times. However, internal pings to printers and other PCs have acceptable response times. Which of the following steps should the technician take NEXT?
A. Determine if any network equipment was replaced recently
B. Verify malware has not disabled the users’ PC firewalls
C. Replace users’ network cables with known-good network cables
D. Power cycle the web server
340. Which of the following is a system of notation that uses base 16 rather than base 10?
A. Hex
B. Octal
C. Binary
D. CIDR
341. A network administrator would like to collect information from several networking devices using SNMP. Which of the following SNMP options should a network administrator use to ensure the data transferred is confidential?
A. authpriv
B. SHA
C. MD5
D. Authentication passphrase
342. The IT manager at a small firm is in the process of renegotiating an SLA with the organization’s ISP. As part of the agreement, the organization will agree to a dynamic bandwidth plan to provide 150Mbps of bandwidth. However, if the ISP determines that a host on the organization’s internal network produces malicious traffic, the ISP reserves the right to reduce available bandwidth to 1.5 Mbps. Which of the following policies is being agreed to in the SLA?
A. Session hijacking
B. Blocking
C. Throttling
D. Data usage limits
E. Bandwidth quotas
343. A network technician has just configured NAC for connections using Cat 6 cables. However, none of the Windows clients can connect to the network. Which of the following components should the technician check on the Windows workstations? (Choose two.)
A. Start the Wired AutoConfig service in the Services console
B. Enable IEEE 802.1q Authentication in Network Interface Card Properties
C. Enable IEEE 802.1x Authentication in Network Interface Card Properties
D. Start the Wireless AutoConfig service in the Services console
E. Enable IEEE 802.3 Ethernet IPv6 in Network Interface Card Properties
344. A network technician has discovered a rogue access point under an empty cubicle desk. Which of the following should the technician perform to ensure another cannot be placed on the network?
A. Disable unused ports on switches
B. Enable DHCP guard to detect rogue servers
C. Configure WPA2 on all access points
D. Use TACACS+ authentication
345. Which of the following provides the ability to deploy consistent access point configurations from a central location?
A. Wireless controller
B. AAA server
C. WiFi-protected setup
D. Proxy server
E. VPN concentrator
346. A network technician is configuring a wireless network at a branch office. Users at this office work with large files and must be able to access their files on the server quickly. Which of the following 802.11 standards provides the MOST bandwidth?
A. a
B. ac
C. g
D. n
347. A network administrator configures a router with the following IP address information:
Gigabit Ethernet 1 Interface: 10.10.0.1/24 Serial 0 Interface: 10.10.0.253/30
Clients are connected to a switch on the gigabit Ethernet interface; the ISP is connected to the Serial 0 interface.
When the router configuration is complete and client devices are reconfigured, all clients report that they are unable to connect to the Internet.
Which of the following is the MOST likely reason?
A. The router was configured with an incorrect IP address
B. The router was configured with an incorrect default gateway
C. The router was configured with an incorrect subnet mask
D. The router was configured with an incorrect loopback address
348. A penetration tester has been tasked with reconnaissance to determine which ports are open on the network. Which of the following tasks should be done FIRST? (Choose two.)
A. Network scan
B. Banner grab
C. Tracert
D. DHCP server check
E. Brute-force attack
349. Users are reporting Internet connectivity issues. The network administrator wants to determine if the issues are internal to the company network or if there is an issue with the ISP. Which of the following tools should be used to BEST determine where the outage is occurring?
A. traceroute
B. ping
C. nslookup
D. netstat
350. A network engineer is designing a new network for a remote site. The remote site consists of ten desktop computers, ten VoIP phones, and two network printers. In addition, two of the desktop computers at the remote site will be used by managers who should be on a separate network from the other eight computers. Which of the following represents the BEST configuration for the remote site?
A. One router connected to one 24-port switch configured with three VLANS: one for the manager’s
computers and printer, one for the other computers and printer, and one for the VoIP phones
B. Two routers with each router connected to a 12-port switch, with a firewall connected to the switch connected to the manager’s desktop computers, VoIP phones, and printer
C. One router connected to one 12-port switch configured for the manager’s computers, phones, and printer, and one 12-port switch configured for the other computers, VoIP phones, and printer
D. One router connected to one 24-port switch configured with two VLANS: one for the manager’s computers, VoIP phones, and printer, and one for the other computers, VoIP phones, and printer
351. Which of the following BEST describes the difference between layer 2 switching and layer 2 routing?
A. Switching moves packets between hosts on different subnets, and routing moves packets between hosts on the same subnet.
B. Routing moves packets between hosts on different subnets, and switching moves packets between hosts on the same subnet.
C. Both routing and switching move packets between hosts on the same subnet, but routing does so at a faster pace.
D. Both routing and switching move packets between hosts on different subnets, but switching does so at a faster pace.
352. Which of the following problems is MOST likely to arise when configuring an IPv6 over IPv4 tunnel?
A. Routing loop
B. MTU black hole
C. Framing errors
D. SYN flood
353. Kim, a technician, needs to locate a cable in an unorganized wiring closet. Which of the following tools will help her locate the cable?
A. Protocol analyzer
B. Cable tester
C. Toner probe
D. Punch down tool
354. Which of the following separates broadcast domains?
A. Port mirroring
B. Router
C. Convergence
D. Switch
355. A national cable company providing TV, telephone, and Internet service to home users over its IP network, has been tracking a large increase of network bandwidth due to P2P file sharing. Which of the following should the company deploy to ensure excellent TV and telephone service?
A. QoS
B. Load balancing
C. High availability
D. Fiber optics
356. Jeff, a technician, is charged with setting up network monitoring for critical devices in the network. It is important the information be sent securely to the monitoring station. Which of the following protocols will support secure transmission of the data?
A. SNMP v2
B. VPN
C. SYSLOG
D. SMTP
357. Keeping an authoritative and timely record of network devices and their settings is a key activity of which of the following?
A. Project management
B. Quality of service
C. Configuration management
D. Bandwidth shaping
358. Which of the following technologies could be implemented to improve call clarity when using VoIP technology?
A. Static IP addressing
B. Caching engines
C. QoS
D. Port forwarding
359. A customer has not been using security on a wireless network and has recently received many attacks through this vector.
Which of the following would be the MOST secure way to harden this wireless network?
A. Disable the SSID
B. WPA encryption
C. VLAN implementation
D. WEP encryption
360. Which of the following needs to be configured on a switch to use a packet sniffer?
A. Port trunking
B. Port mirroring
C. Tagged VLAN
D. Untagged VLAN
361. A network technician is connecting two switches together. Which of the following protocols should the technician use to increase speed and fault tolerance?
A. SIP
B. BGP
C. LACP
D. LLDP
362. A company has a web-based application that is used by many different departments. The company has experienced some overload of resources on the database server. The network administrator implements a network device in between the servers and the database. Which of the following BEST describes the purpose of this device?
A. Content filtering and network analysis
B. Load balancing and providing high availability
C. Port sniffing and protocol analysis
D. Clustering and NIC teaming
363. A technician is replacing a switch at a branch office and discovers the existing backbone cable does not fit in the new switch. The fiber patch panel has circular connections. The new switch has a transceiver that accepts a smaller square adapter of two strands. Which of the following patch cables would the technician need to complete the installation?
A. LC to SC
B. SC to ST
C. LC to ST
D. ST to ST
E. SC to SC
364. A computer lab on a campus network was recently reconfigured using recycled network cables. One of the 24 computers in the lab is unable to connect to the network after the upgrade. A network technician successfully uses the cable in to connect directly to another computer. Which of the following is MOST likely issue with the cable?
A. The cable is a crossover cable
B. The cable is rollover cable
C. The cable has bent pins
D. The cable is a Cat 5 cable
365. Which of the following is a reason why a business may be hesitant to move sensitive data to a SaaS cloud service?
A. Decreased performance of internal network
B. Loss of full control over data resources
C. Increased malware exposure
D. Incompatibility with the current network
366. Users have been experiencing slow network response times, and management has asked the network technician to provide evidence of network improvement. After optimizing the network, which of the following would be required?
A. IDF/MDF documentation
B. Change management
C. Performance baseline
D. Physical diagram
367. A network technician has created a network that consists of a router, a firewall, a switch, and several PCs. Which of the following physical network topologies was created?
A. Star
B. Mesh
C. Ring
D. Bus
368. A technician is setting up a branch office on a point-to-point connection. Which of the following IP network blocks is the MOST efficient use of IP address space for the router connections between the two sites?
A. /24
B. /25
C. /30
D. /32
369. At which of the following layers of the OSI model do packets exist?
A. Network
B. Session
C. Data link
D. Transport
370. A company is having a new T1 line installed. Which of the following will the connection MOST likely terminate to?
A. Core switch
B. MDF
C. Ethernet router
D. IDF
371. A network technician performs several switch commands to enable various advanced features on the switch in the accounting department. During the configuration changes, several users from this department report connectivity issues. Which of the following logs would the network technician need to analyze to troubleshoot the connectivity issues?
A. Router logs
B. History logs
C. Startup/bootup config logs
D. Event Viewer logs
372. A technician needs to test the length of a newly installed cable run because it is believed that it exceeds the maximum specification length. Which of the following tools should be used?
A. Cable certifier
B. Toner probe
C. Cable tester
D. Protocol analyzer
373. Which of the following layers of the OSI model is between the Data Link and Transport layers?
A. Application
B. Session
C. Network
D. Physical
374. An administrator is troubleshooting analog telephony issues on the punch down block. Which of the following tools would be MOST useful in this scenario?
A. T1 loopback
B. Butt set
C. Multimeter
D. Protocol analyzer
375. Which of the following protocols is used to allow multiple hosts to share a common IP address?
A. HTTPS
B. ARP
C. CARP
D. NAT
376. Which of the following tools can the technician use to analyze TCP/IP packets when trying to determine a connection problem within a subnet?
A. Wire mapper
B. Protocol analyzer
C. Cable tester
D. SYSLOG server
377. Which of the following is used to classify network data for the purpose of providing QoS?
A. STP
B. VLANs
C. SIP
D. DSCP
378. A network technician needs to separate a web server listening on port 80 from the internal LAN and secure the server from the public Internet. The web server should be accessible to the public Internet over port 80 but not the private LAN. Currently, the network is segmented with a networkbased firewall using the following IP addressing scheme on each interface:
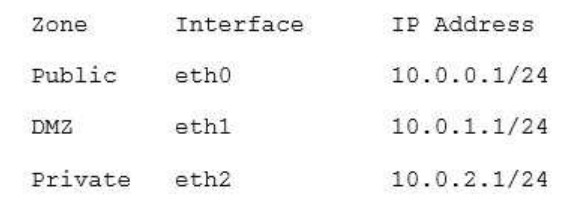
Which of the following ones should the technician use to place the web server and which of the following firewall rules should the technician configure?
A. Place the web server in the public zone with an inbound rule from eth0 interface to accept traffic over port 80 designated to the web server
B. Place the web server in the DMZ with an inbound rule from eth0 interface to eth1 to accept traffic over port 80 designated to the web server
C. Place the web server in the private zone with an inbound rule from eth2 interface to eth1 to accept traffic over port 80 designated to the web server
D. Place the web server in the DMZ with an inbound rule from eth1 interface to eth0 to accept traffic over port 80 designated to the web server
379. A company recently upgraded all of its printers to networked multifunction devices. Users can print to the new devices, but they would also like the ability to scan and fax files from their computers. Which of the following should the technician update to allow this functionality?
A. Device software
B. Printer drivers
C. Printer firmware
D. NIC drivers
380. A disgruntled employee executes a man-in-the-middle attack on the company network. Layer 2 traffic destined for the gateway is redirected to the employee’s computer. This type of attack is an example of:
A. ARP cache poisoning
B. IP spoofing
C. amplified DNS attack
D. evil twin
381. The process of attempting to exploit a weakness in a network after being given permission by the company is known as:
A. penetration testing
B. vulnerability scanning
C. reconnaissance
D. social engineering
382. The security manager reports that individual systems involved in policy or security violations or incidents cannot be located quickly. The security manager notices the hostnames all appear to be randomly generated characters. Which of the following would BEST assist the security manager identifying systems involved in security incidents?
A. Enforce port security to require system authentication
B. Implement a standardized UNC
C. Label existing systems with current hostnames
D. Forward the DHCP logs to the security manager every day
383. A building is equipped with light sensors that turn off the fluorescent lights when natural light is above a certain brightness. Users report experiencing network connection issues only during certain hours. The west side of the building experiences connectivity issues in the morning hours and the east side near the end of the day. At night the connectivity issues affect the entire building. Which of the following could be the cause of the connectivity issues?
A. Light sensors are interfering with the network
B. EMI from the lights is interfering with the network cables
C. Network wiring is run perpendicular to electrical conduit
D. Temperature changes are causing attenuation in copper cabling
384. A network technician configures a firewall’s ACL to allow outgoing traffic for several popular services such as email and web browsing. However, after the firewall’s deployment, users are still unable to retrieve their emails. Which of the following would BEST resolve this issue?
A. Allow the firewall to accept inbound traffic to ports 25, 67, 179, and 3389
B. Allow the firewall to accept inbound traffic to ports 80, 110, 143, and 443
C. Set the firewall to operate in transparent mode
D. Allow the firewall to accept inbound traffic to ports 21, 53, 69, and 123
385. A network security technician observes multiple attempts to scan network hosts and devices. All the attempts originate from a single host on the network. Which of the following threats is MOST likely involved?
A. Smurf attack
B. Rogue AP
C. Compromised system
D. Unintentional DoS
386. A network technician is troubleshooting an end-user connectivity problem. The network technician goes to the appropriate IDF but is unable to identify the appropriate cable due to poor labeling. Which of the following should the network technician use to help identify the appropriate cable?
A. Tone generator
B. Multimeter
C. OTDR
D. Loopback adapter
387. A network technician notices the site-to-site VPN and Internet connection have not come back up at a branch office after a recent power outage. Which of the following is an out-of-band method the technician would MOST likely utilize to check the branch office’s router status?
A. Use a modem to console into the router
B. Walk a user through troubleshooting the connection
C. Travel to the branch office
D. Hire a contractor to go on-site
388. A network technician is considering opening ports on the firewall for an upcoming VoIP PBX implementation. Which of the following protocols is the technician MOST likely to consider? (Choose three.)
A. SIP
B. NTP
C. H.323
D. SMB
E. ICMP
F. RTP
G. IPSec
H. RDP
389. A device operating at Layer 3 of the OSI model uses which of the following protocols to determine the path to a different network?
A. STP
B. RTP
C. RIP
D. NTP
E. SIP
390. Lisa, a technician, is tasked to monitor various analog POTS lines for voice activity. Which of the following hardware tools would be used?
A. Butt set
B. Toner probe
C. Wire mapper
D. Cable certifier
391. An organization wants to perform maintenance on any of its web servers without affecting the service availability during a scheduled change window. Which of the following network devices would be required to provide this functionality?
A. Router
B. Forward proxy
C. Load balancer
D. Firewall
392. Which of the following communication modes has the LOWEST overhead necessary to support streaming protocols such as RTP?
A. Connectionless
B. Stateful
C. Full Duplex
D. Quality of Service
393. Which of the following diagnostic commands relies on proper forwarding of ICMP ECHO packets?
A. ipconfig
B. ping
C. route
D. nbstat
394. A technician replaces a customer’s router, and is now unable to ping the ISP’s gateway. Which of the following should the technician check?
A. The arp table of the new customer’s router.
B. The route table of the next-hop router.
C. The route table of the new customer’s router.
D. The arp table of a network user.
395. When Jeff, a technician, is troubleshooting a problem, which of the following is the NEXT step after verifying full system functionality?
A. Establish a plan of action to resolve the problem and identify potential effects.
B. Implement the solution.
C. Establish a theory of probable cause.
D. Document findings, actions, and outcomes.
396. A technician needs to verify an Ethernet run is functioning properly. Which of the following tools should be used?
A. Protocol analyzer
B. Crimper
C. Cable tester
D. Punch down tool
397. A network administrator is testing connectivity at a new corporate site. The site has a wireless guest as well as a wired employee network. After verifying connectivity, the administrator checks link speeds by using a speed testing website. The speed testing website shows lower download and upload speeds for the wired network than the wireless network. Which of the following is the MOST likely explanation?
A. There is less local congestion on the wireless network
B. The testing server for the wired network was farther away
C. The firewall is configured to throttle traffic to specific websites
D. The wireless access points were misconfigured
398. A technician replaces a failed router with a spare that has been in inventory for some time. After attempting to enable HTTPS on the spare router, the technician discovers the feature is unavailable. The support office was able to connect to the previous router. Which of the following actions should the technician perform to enable HTTPS access for the support team?
A. Reboot the router
B. Enable HTTP on the router
C. Update the firmware of the spare router
D. Perform a factory reset on the router
399. A technician is trying to configure a previously owned WAP. The technician successfully logs into the administrative console and attempts to input the IP address on the WAP. However, the WAP is not accepting the command. Which of the following is causing the problem?
A. The WAP antenna is damaged
B. The WAP transmitter light is dim
C. The terminal emulation software is misconfigured
D. The LWAPP image is installed on the WAP
400. Drag and Drop Question
Your company recently purchased a new building down the street from the existing office.
For each of the tasks below, select the appropriate antenna type and encryption object for all wireless access point (AP).
1. Create an encrypted wireless connection between the two buildings that BEST controls signal propagation, while maximizing security.
2. Restrict the wireless signal generated by the access points (AP’s) inside Building 1, so that it minimizes broadcast beyond the building.
3. Maximize wireless coverage inside Building 1.
4. Building 1’s internal wireless network is for visitors only and must not require any special configuration on the visitor’s device to connect.
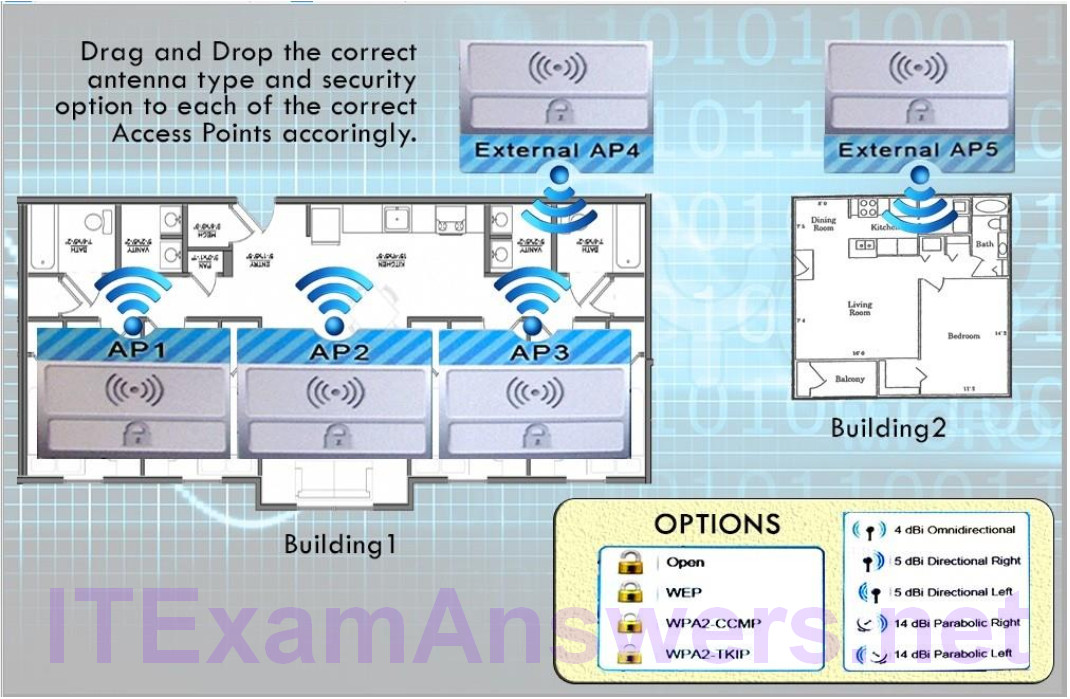
Answer:
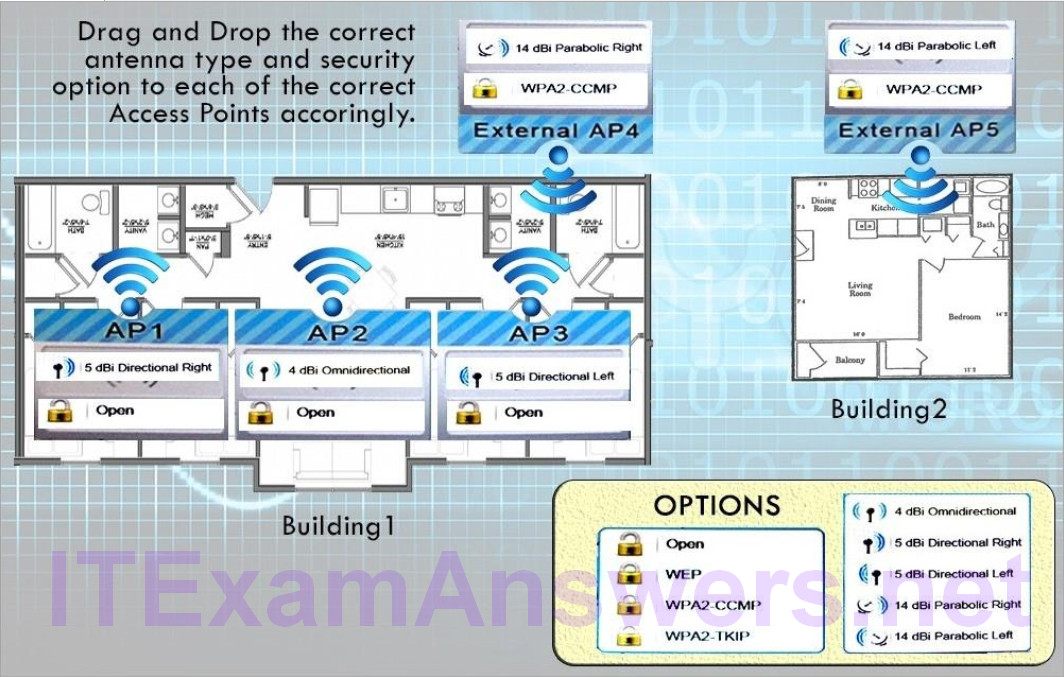
401. A technician has installed a Linux server in the tax office. The server can access most of the resources on the network, but it cannot connect to another server that has a share for backup. The technician learns that the target server is on a different subnet. Which of the following tools should the technician use to ensure the Linux server can reach the backup location?
A. netstat
B. traceroute
C. route
D. dig
E. ifconfig
402. Which of the following WAN technologies provides a guaranteed throughput rate?
A. DSL
B. T-1
C. Cable broadband
D. Dial-up
403. Which of the following is the SHORTEST way to write
2001:0000:0d58:0000:0000:0095:7565:0001 in proper IPv6 shorthand?
A. 2001::d58::95:7565:1
B. 2001:0:d58:0:0:95:7565:1
C. 2001:0:d58::95:7565:1
D. 2001:0:0d58::95:7565:1
404. Which of the following WAP security features offers the STRONGEST encryption?
A. WPA
B. WPA2
C. WEP
D. Hidden SSID
405. Which of the following standards can operate at both the 2.4GHz and 5GHz frequencies?
A. 802.11a
B. 802.11b
C. 802.11g
D. 802.11n
406. Which of the following mediums is circuit switched?
A. PSTN
B. ATM
C. Frame relay
D. MPLS
407. Which of the following is true about tunneling and encryption?
A. SIP encrypts all data going through the tunnel.
B. PPTP creates a secure tunnel.
C. SSL VPN provides a secure tunnel.
D. RAS is a secure way to create a tunnel.
408. Which of the following is a secure way to connect to a device?
A. RSH
B. TFTP
C. SNMPv2
D. SFTP
409. A network administrator is setting up a web-based application that needs to be continually accessible to the end users. Which of the following concepts would BEST ensure this requirement?
A. High availability
B. Snapshots
C. NIC teaming
D. Cold site
410. Which of the following devices should a network administrator configure on the outermost part of the network?
A. Media converter
B. Switch
C. Modem
D. Firewall
411. Lab Simulation
Workstations are unable to access the internet after a recent power outage. Configure the
appropriate devices to ensure All workstations have internet connectivity.
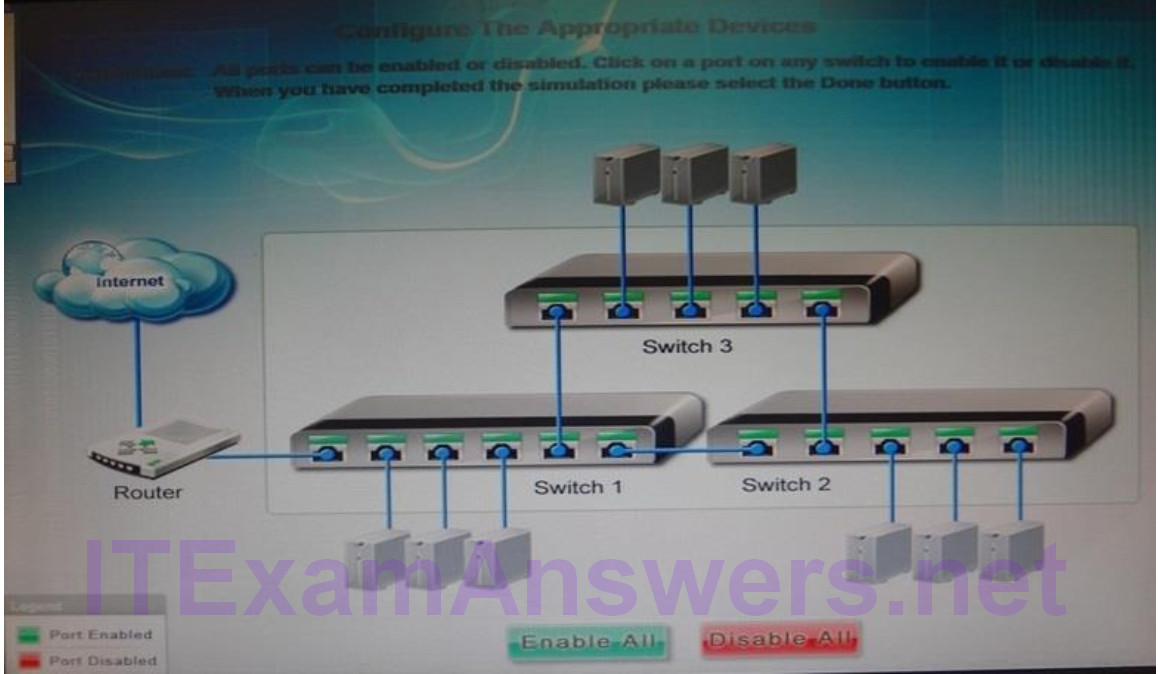
Answer:
The switches are not connected properly.
Connect Switch 1 to switch three on the last port and then connect the last port of the switch 3 to the first port of switch 2. In this way the switches will be connected properly. Click Enable All to enable the switches.
412. Lab Simulation
You have been tasked with testing a CAT5e cable.
A summary of the test results can be found on the screen.
Step 1: Select the tool that was used to create the cable test results.
Step 2: Interpret the test results and select the option that explains the results.
After you are done with your analysis, click the ‘Submit Cable Test Analysis’ button.
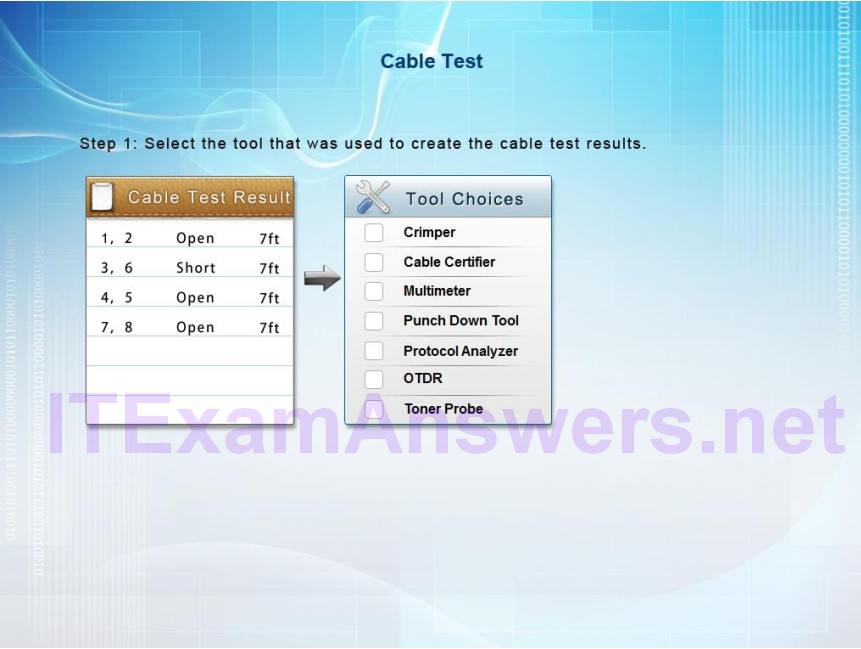
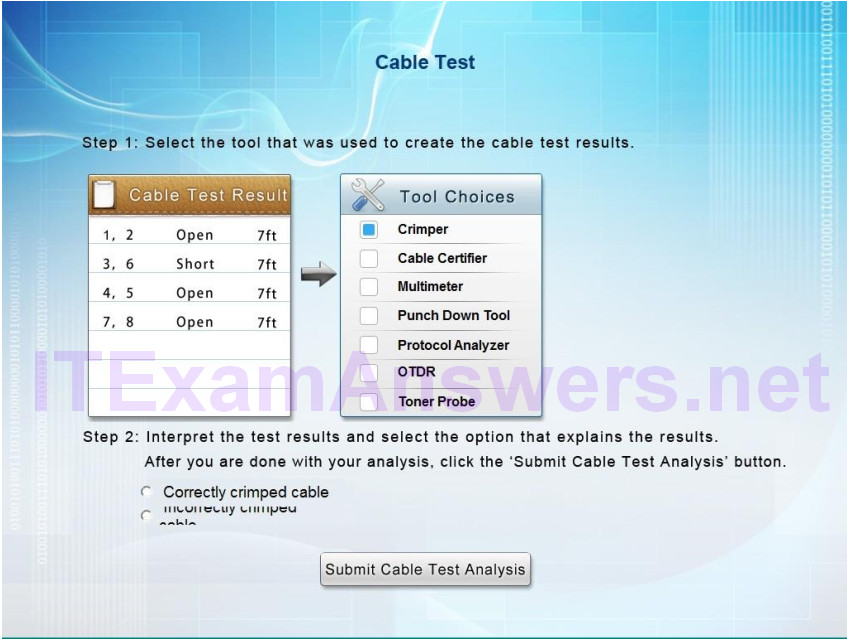
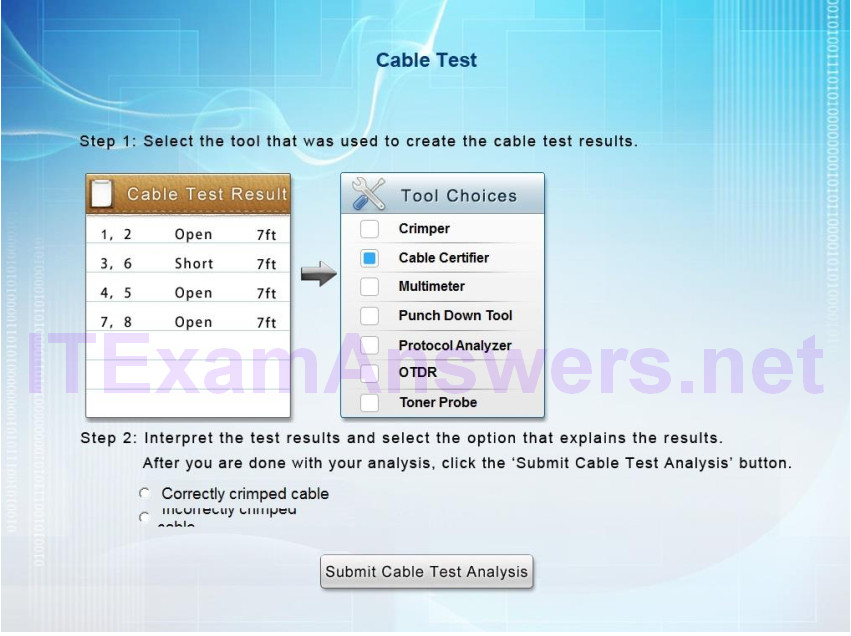
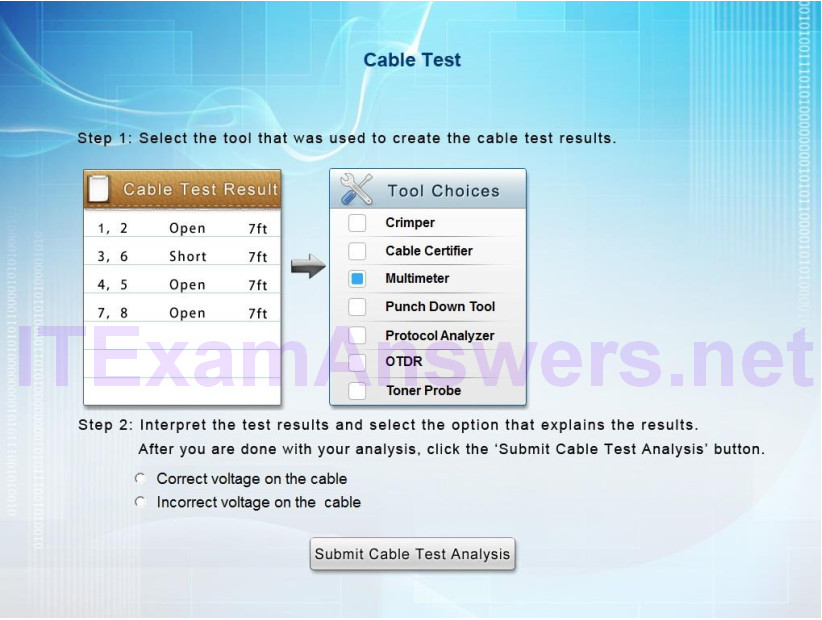
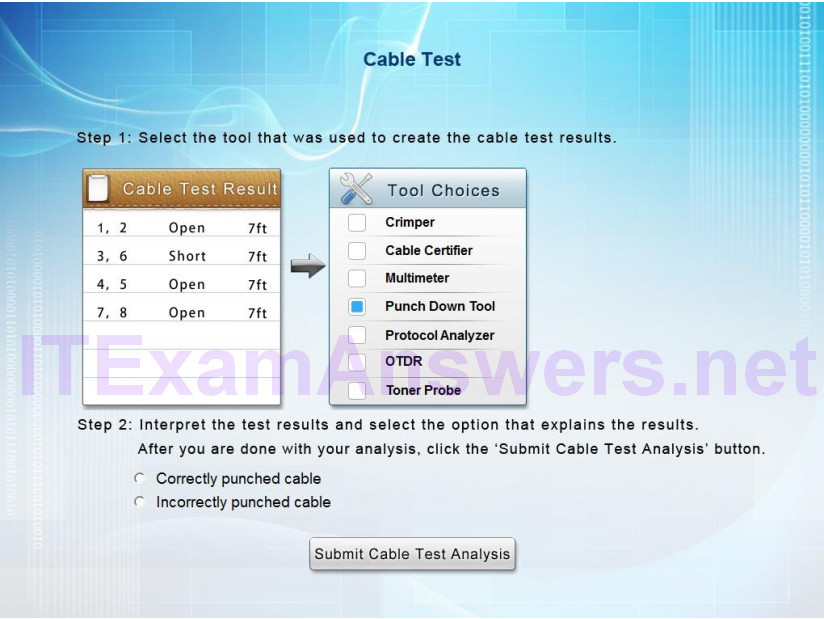
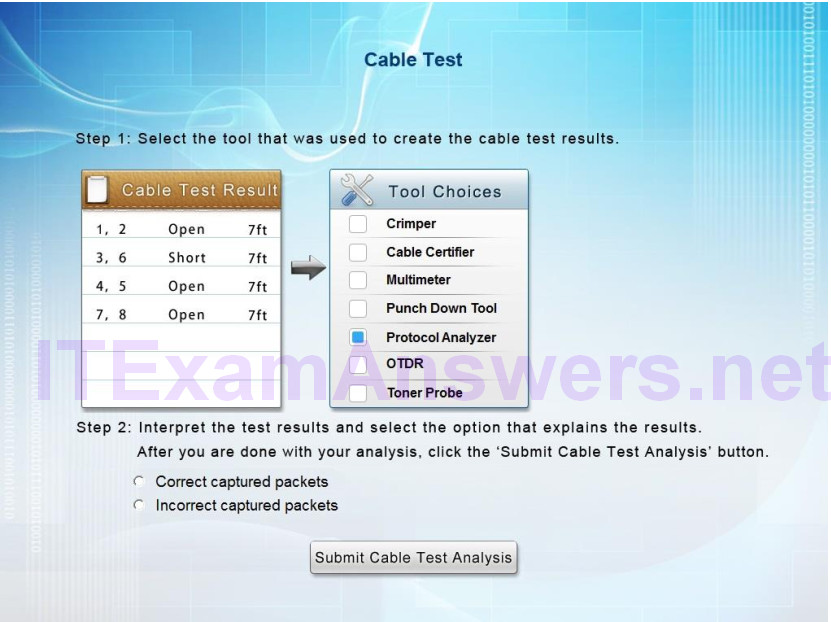
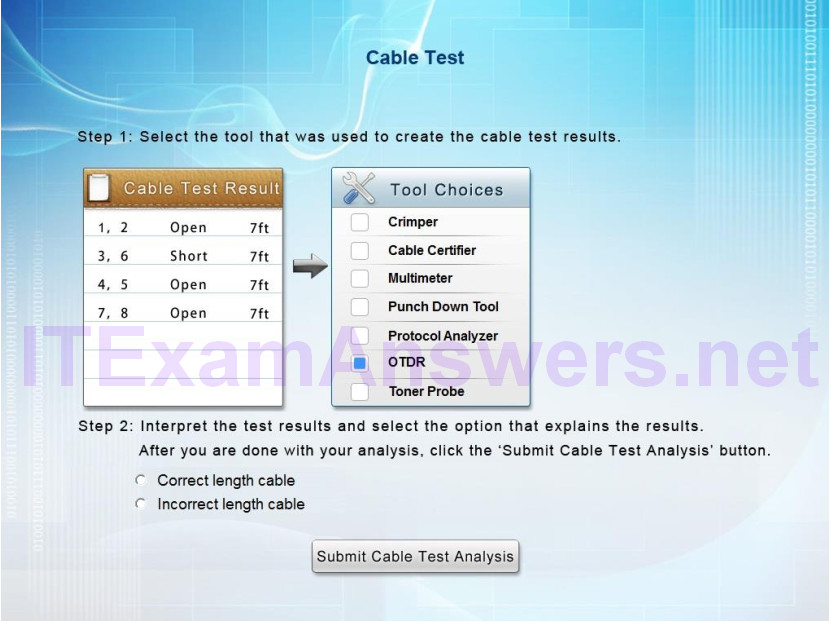
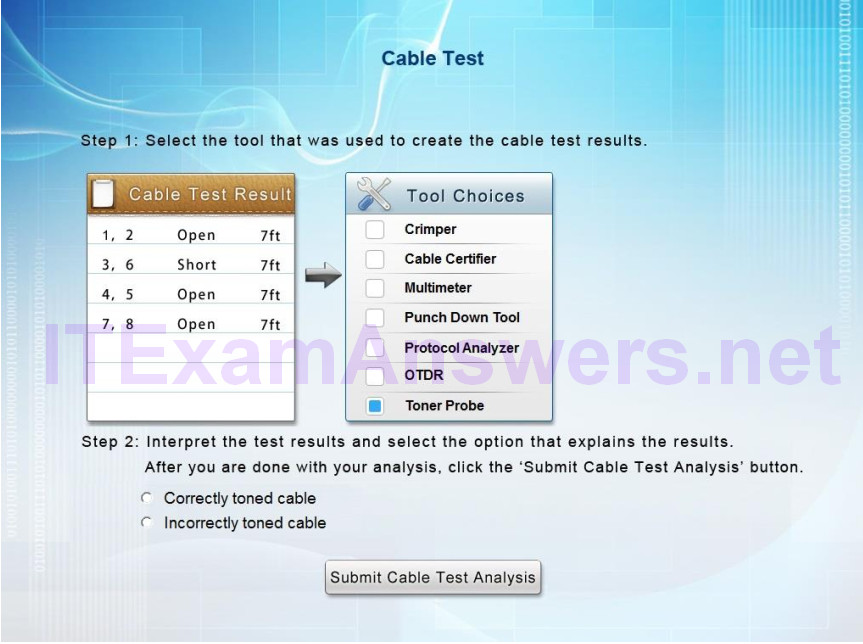
Answer: Cable certifier – incorrectly crimped cable
Explanation:
A Cable Certifier provides “Pass” or “Fail” information in accordance with industry standards but can also show detailed information when a “Fail” occurs. This includes shorts, the wire pairs involved and the distance to the short. When a short is identified, at the full length of the cable it means the cable has not been crimped correctly.
413. Drag and Drop Question
Wireless network users recently began experiencing speed and performance issues after access point 2 (AP2) was replaced due to faulty hardware. The original network was installed according to a consultant’s specifications and has always worked without a problem.
You a network technician, have been tasked with evaluating the situation and resolving the issues to improve both performance and connectivity.
Refer to the following exhibits and perform any necessary changes to the wireless and wired infrastructure by adjusting devices.
Note: Adjust the LEAST number of devices needed to fix the issue.
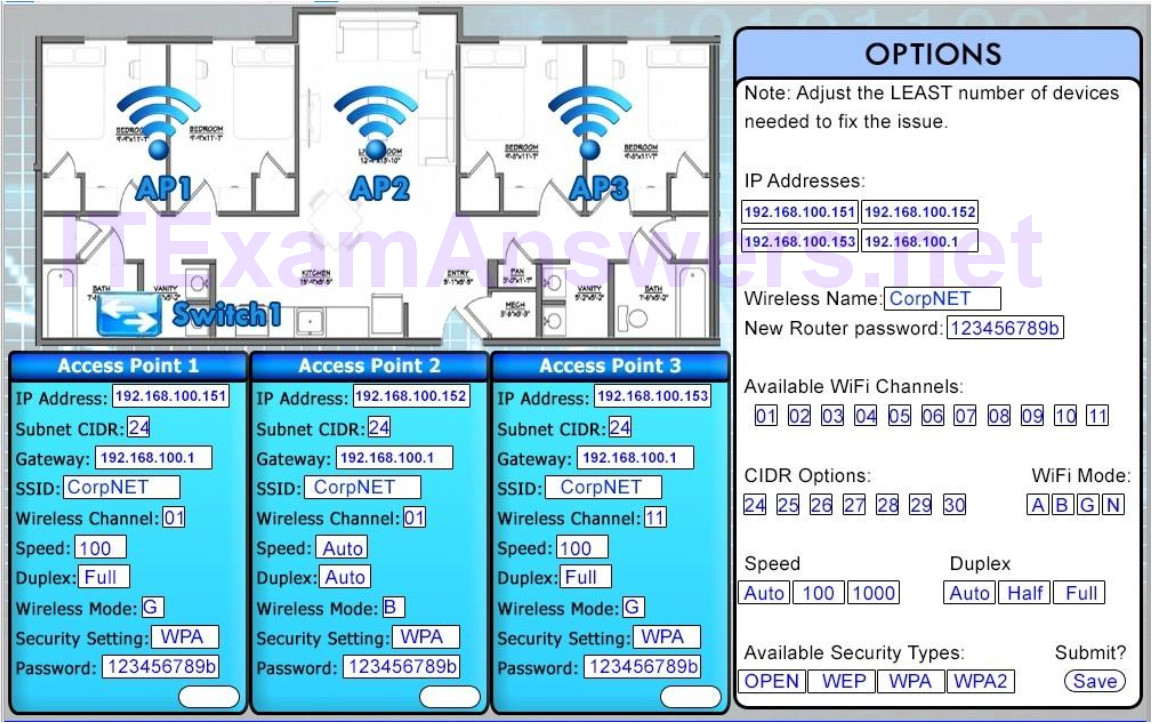
Answer:
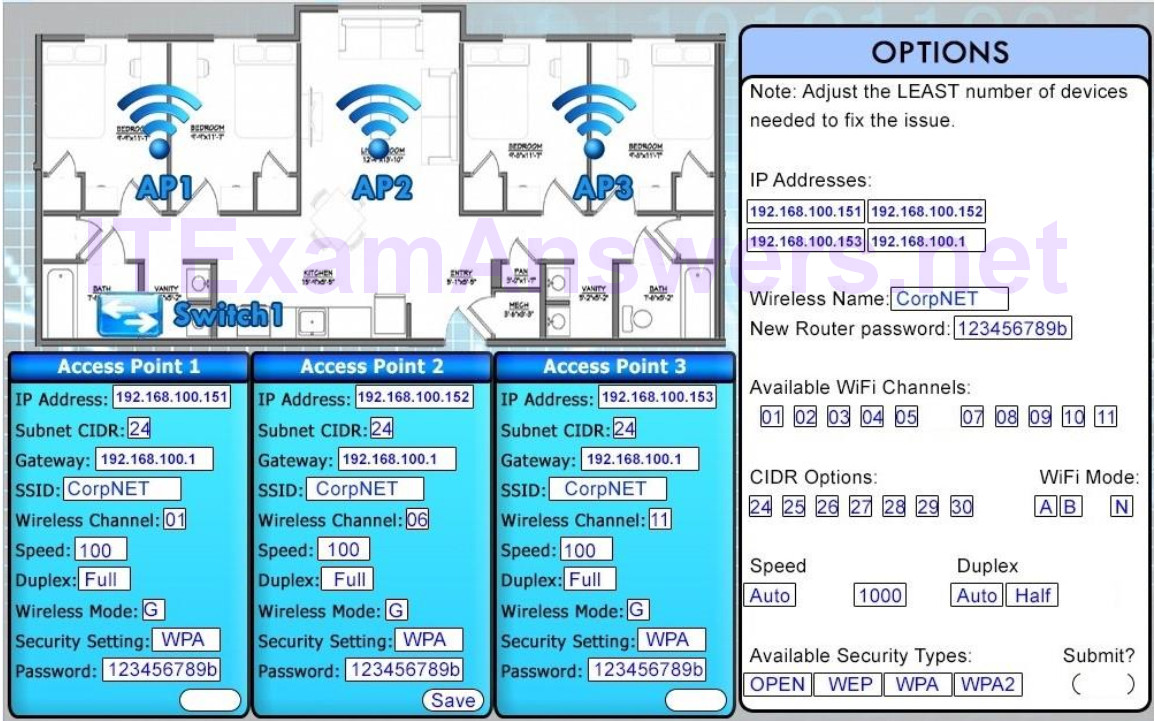
Explanation:
After you fix AP2, you must click on the switch, which will bring up the switch interface. Type in the two commands that they show there, to prove the fix. Do not worry that interface 4 is down, there is no interface 4 for you to do.
414. Lab Simulation
Wireless network users recently began experiencing speed and performance issues after access point 2 (AP2) was replaced due to faulty hardware.
The original network was installed according to a consultant’s specifications and has always worked without a problem.
You, a network technician, have been tasked with evaluating the situation and resolving the issues to improve both performance and connectivity.
Refer to the following diagram and perform any NECESSARY changes to the wireless and wired infrastructure by adjusting devices.
Note: Adjust the LEAST number of devices needed to fix the issue, all blue icons in the image are clickable.
When you feel the simulation is complete please select the Done button.
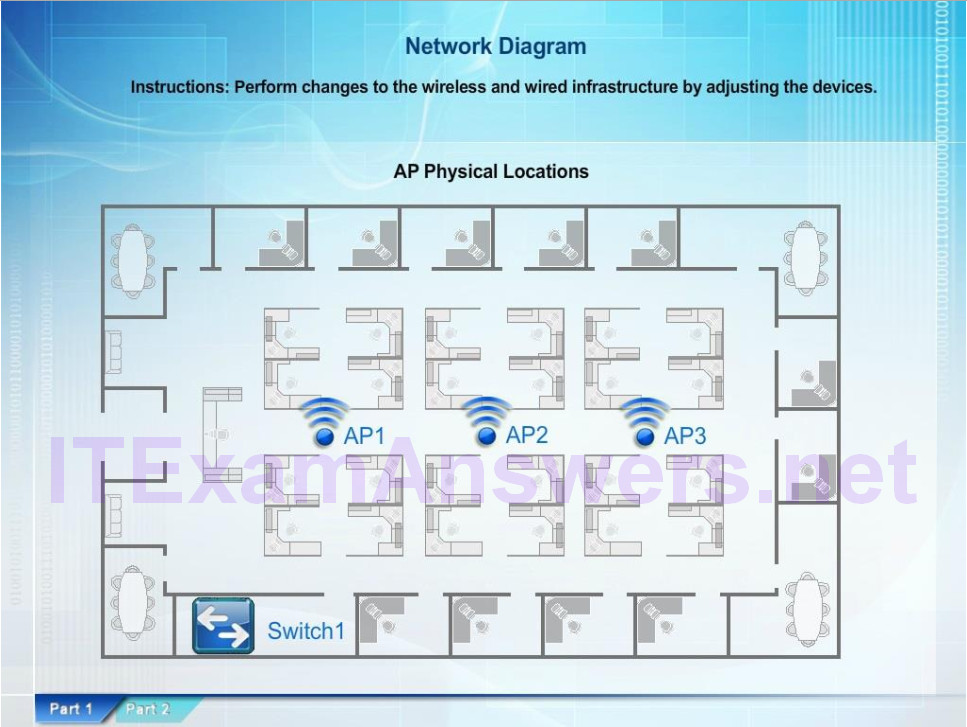
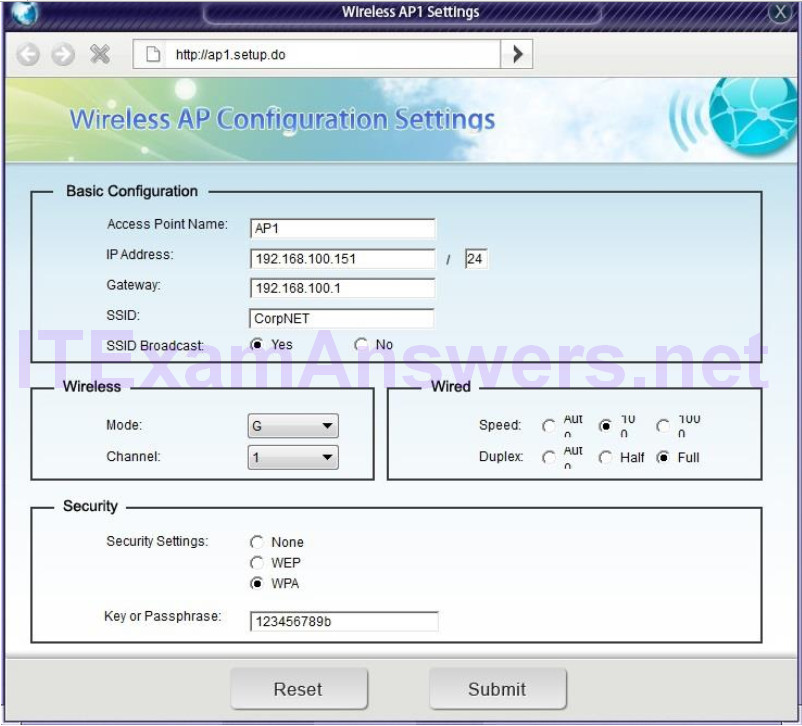
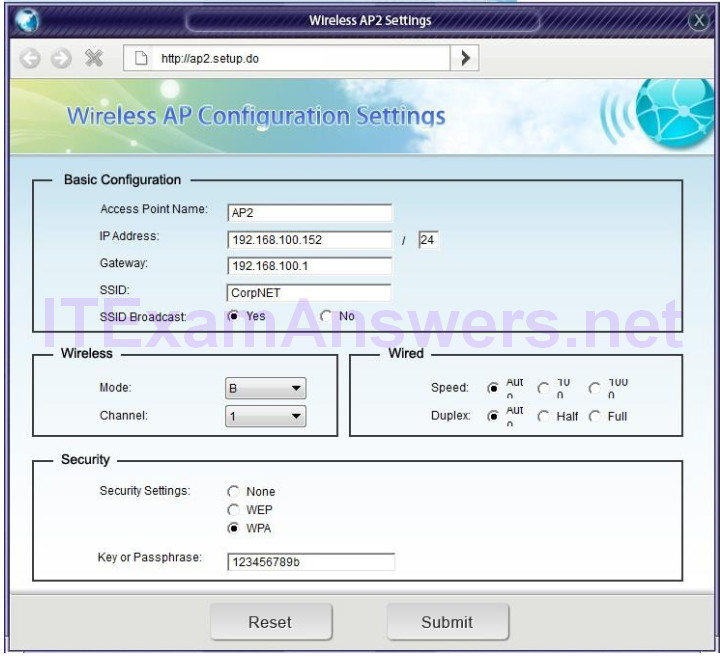
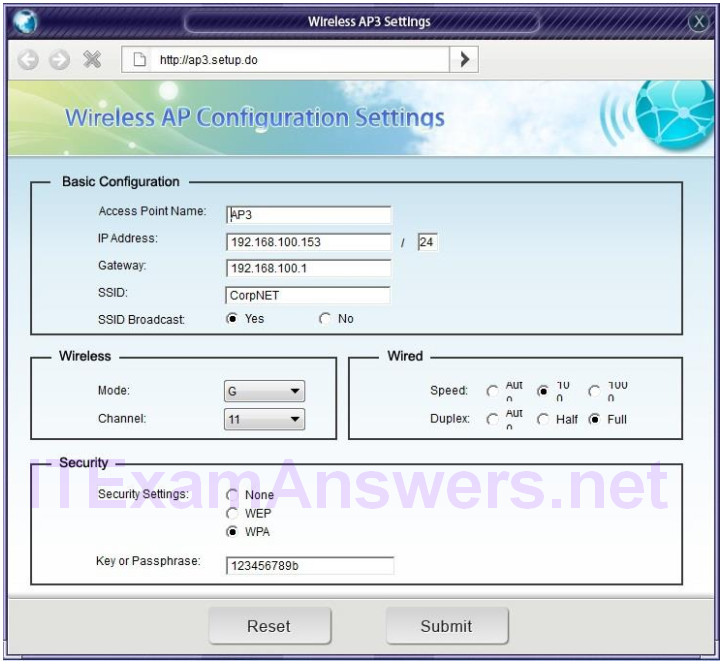
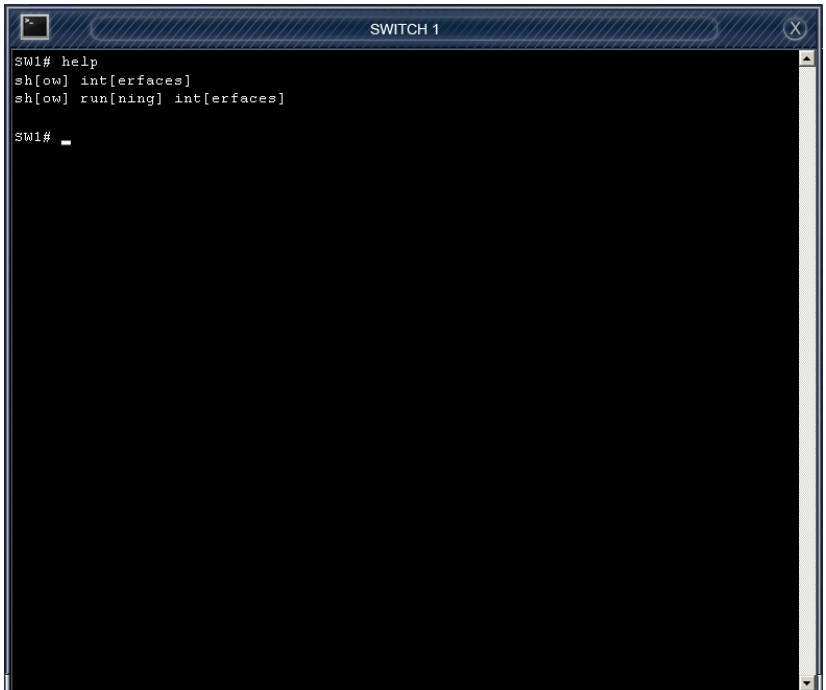
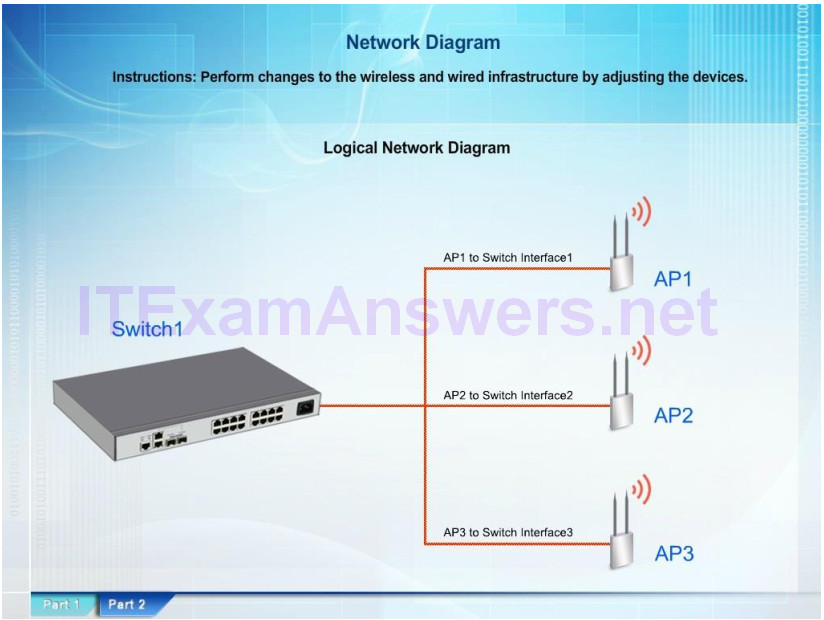
Answer:
– Change the speed and duplex settings on AP2 only to 100 and full.
– Change the mode to G on AP2
– Change the channel to 6 on AP2
Explanation:
Since we know that the network was running perfectly before replacing AP2 we should start by looking at this new device that was used to replace the old one. Here we see that the other AP’s
have hard coded the speed and duplex settings to 100/full, while AP2 is set to auto/auto.
Also, the other AP’s have been configured to use 802.11G, while AP2 is using 802.11B.
Finally the channel that AP2 is using overlaps with AP1 which can cause problems.
Channels 1, 6, and 11 are spaced far enough apart that they don’t overlap.
On a non-MIMO setup (i.e. 802.11 a, b, or g) you should always try to use channel 1, 6, or 11.
Since AP1 is using 1, and AP3 is using 11, AP2 should be using 6.
415. Drag and Drop Question
Drag and drop the fiber cable connection types to the appropriate image.

Answer:
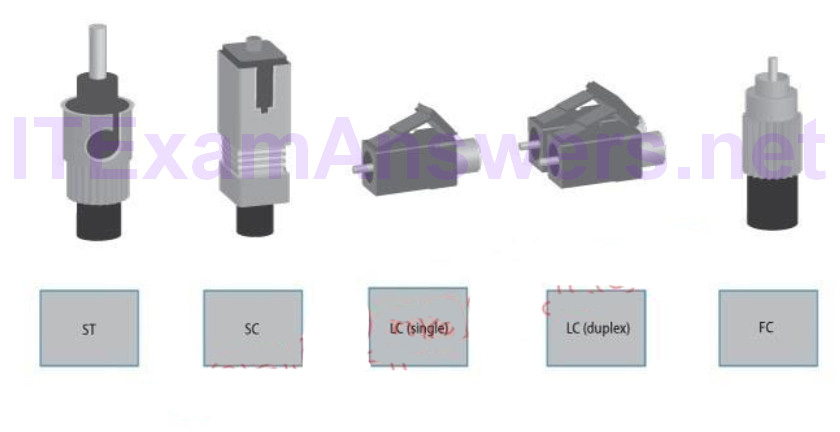
416. Drag and Drop Question
A customer’s email server is not sending emails. Arrange the troubleshooting steps in the order the technician should perform them:
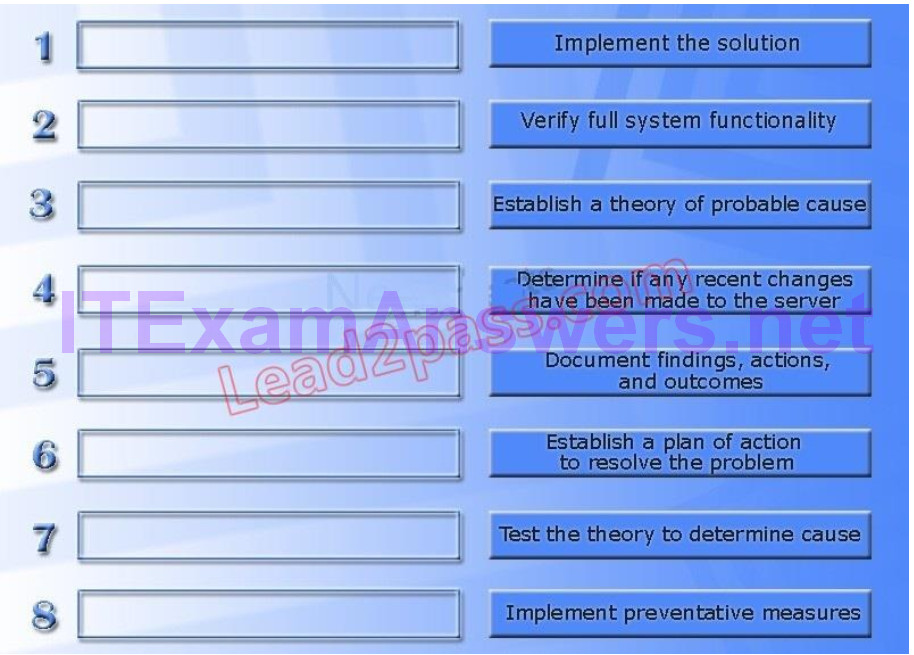
Answer:
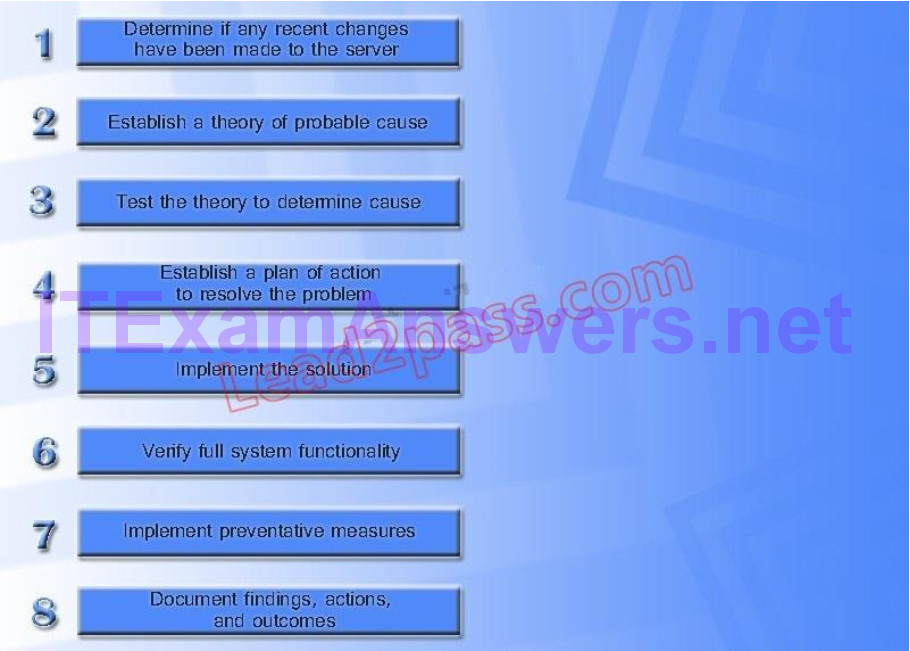
417. Drag and Drop Question
GigSwitch1 is currently configured with a speed of 100 and Duplex is set to Auto on all interfaces. Interface 2 will be connected to GigSwitch2 which is used for all departments. Interface 1 will be used for HR traffic only.
GigSwitch1 needs to be configured with the following parameters:
* Configure the necessary protocol to prevent switching loops * Configure GigSwitch1 with a /24 IP address for management * Traffic across Interface 1 needs to be forced to accept and receive up to 100Mbps data at the same time * Traffic across Interface 2 needs to be forced to use Gigabit speeds and maximum performance
Drag and drop the appropriate configurations to their corresponding requirements.
All placeholders must be filled. Not all configurations will be used.
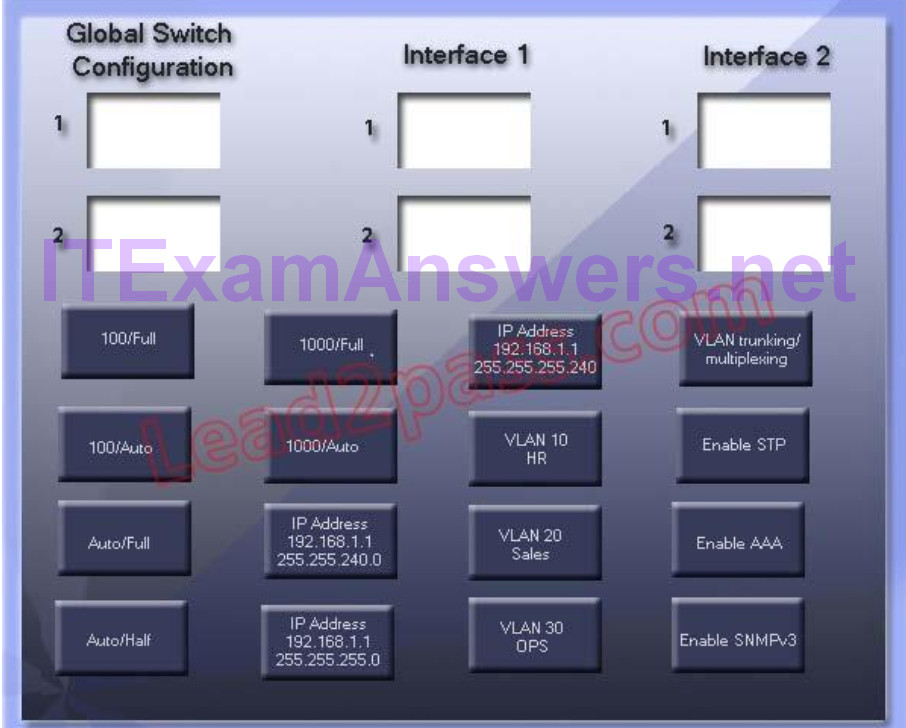
Answer:
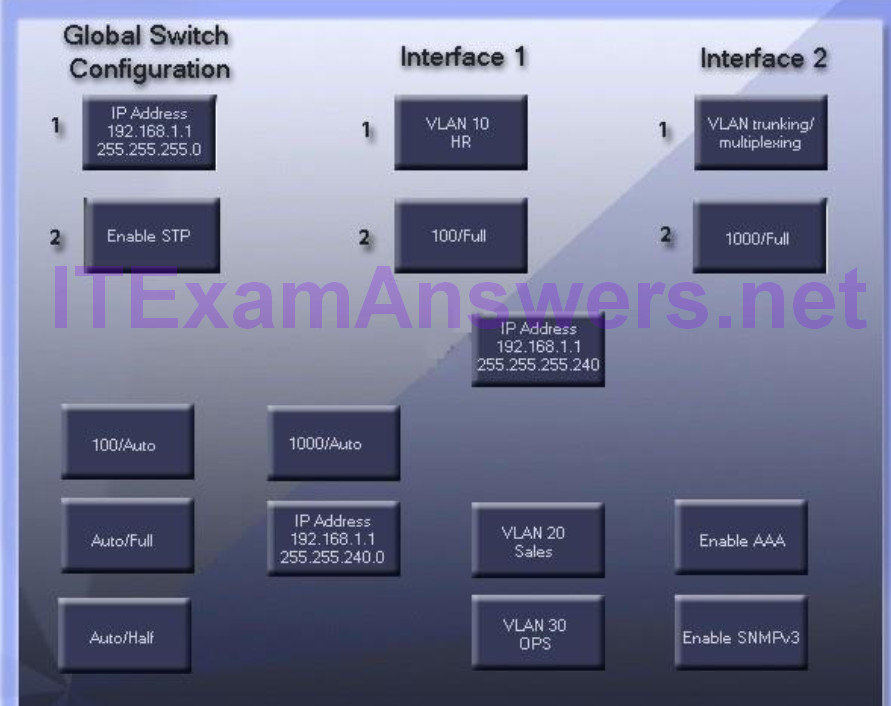
418. Drag and Drop Question
Drag and drop each networking tool to the MOST appropriate descriptor. Each tool may only be used once.
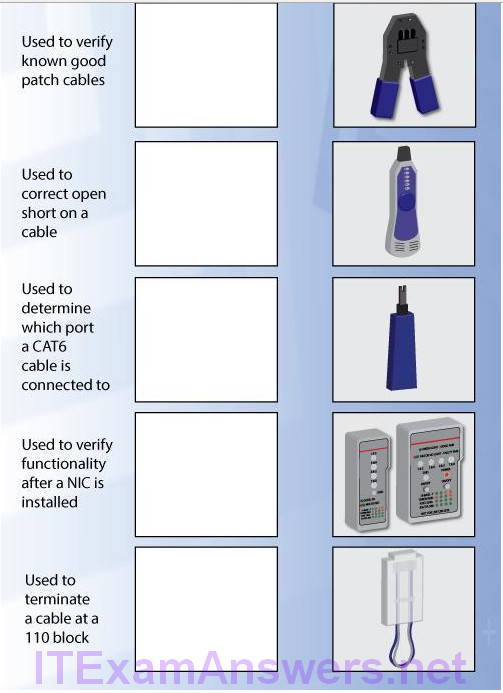
Answer:
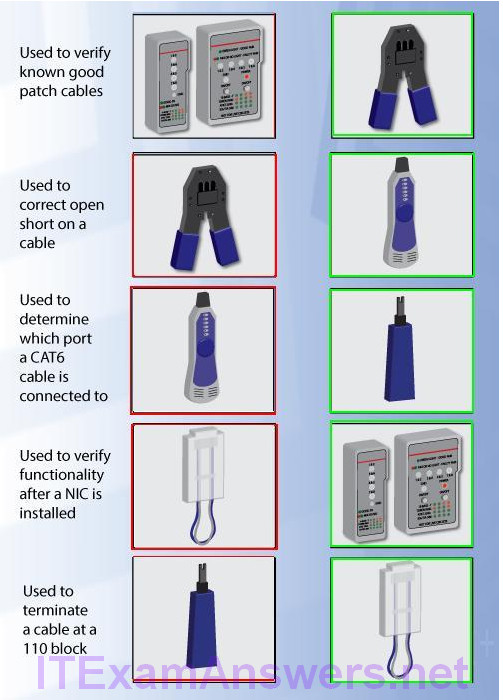
419. Drag and Drop Question
Drag and drop the following maximum speeds to their corresponding wireless standards.
Tokens can be used more than once.
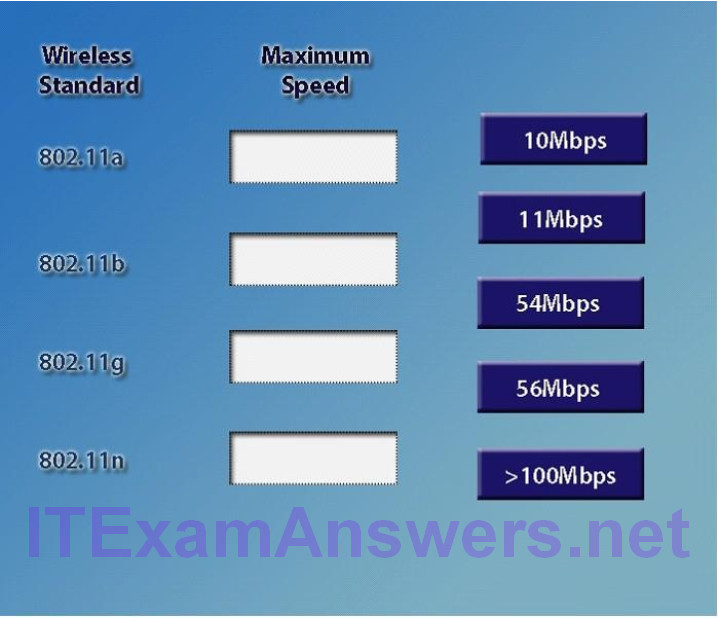
Answer:
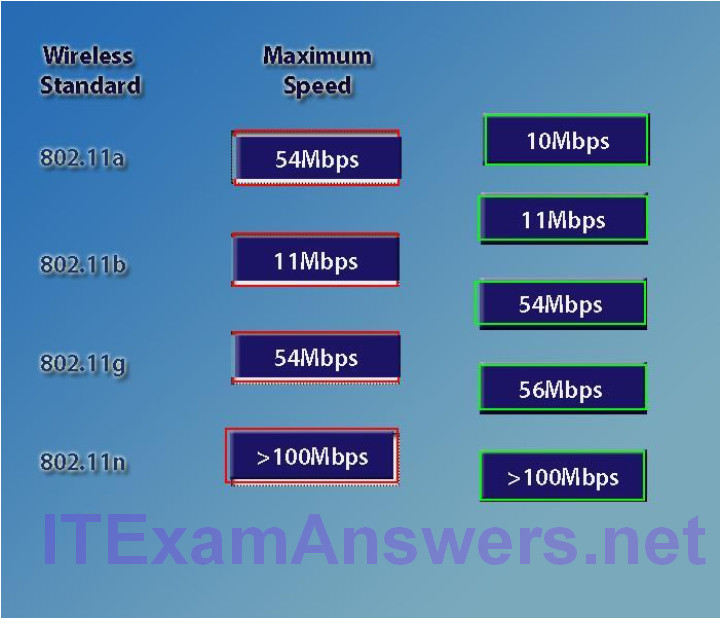
420. Crimp out a T568B.
Answer:
White/Orange, Orange, White/Green, Blue, White/Blue, Green, White/Brown, Brown.
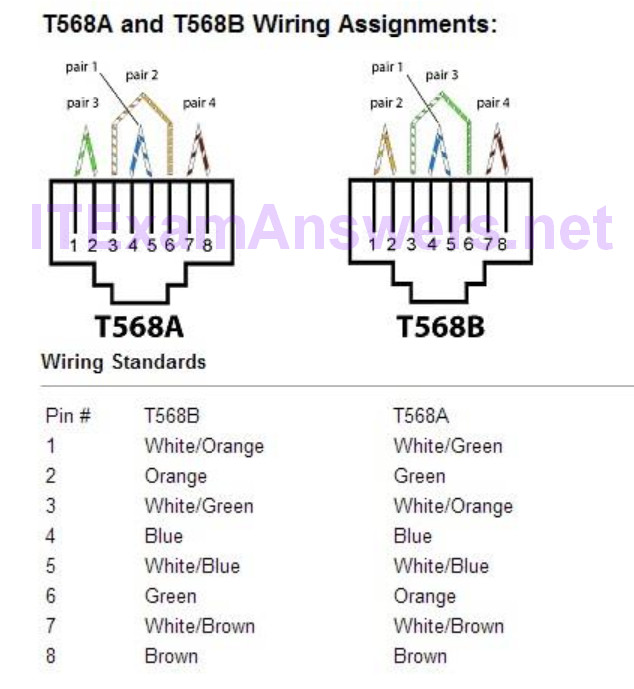
421. Lab Simulation
Alter recent changes to the pictured network, several users are unable to access the servers. Only PC1, PC2, PC3, and PC4 are clickable and will give you access to the command prompt and the adapter configuration tabs.
Instructions: Verify the settings by using the command prompt, after making any system changes. Next, restore connectivity by making the appropriate changes to the infrastructure. When you have completed these steps, select the Done button to submit.
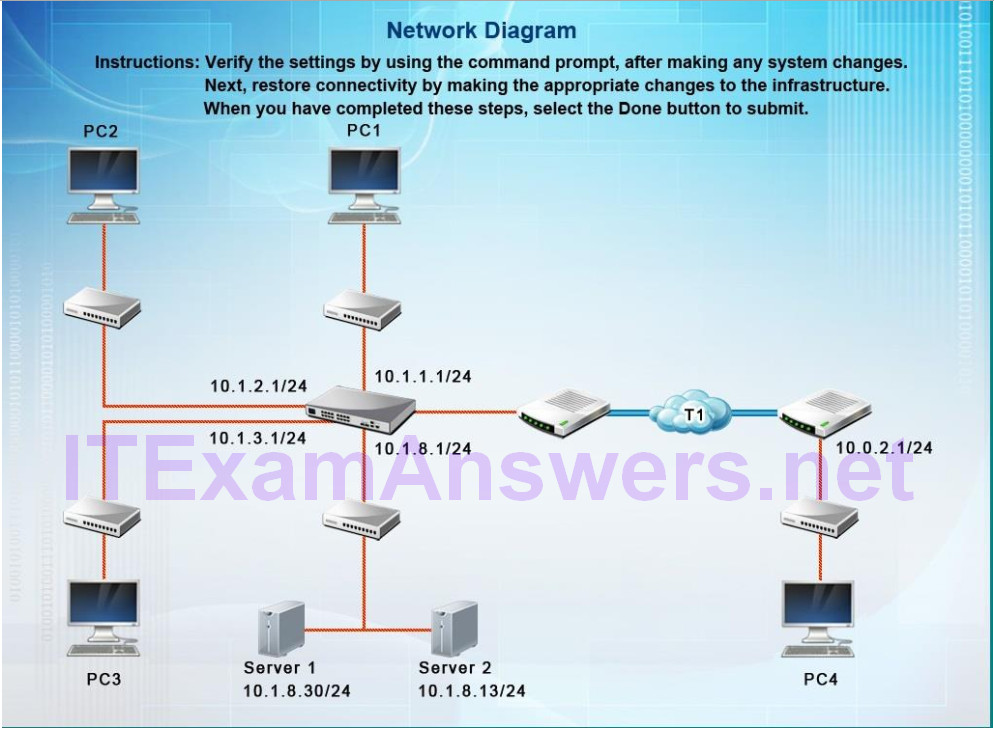
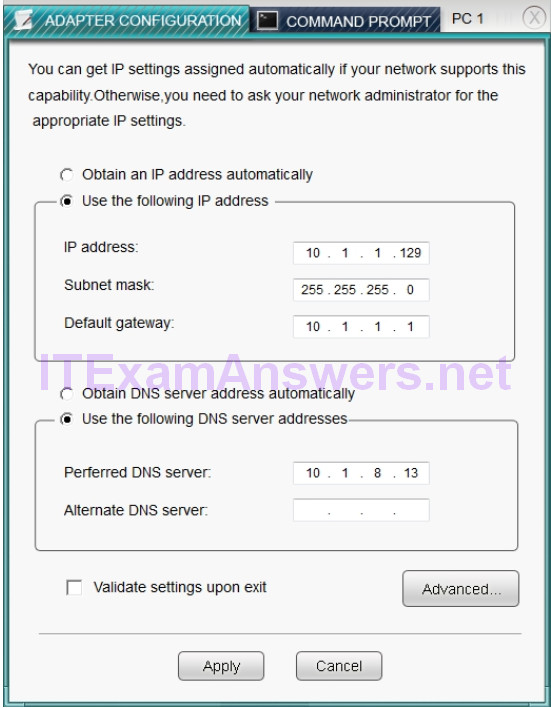
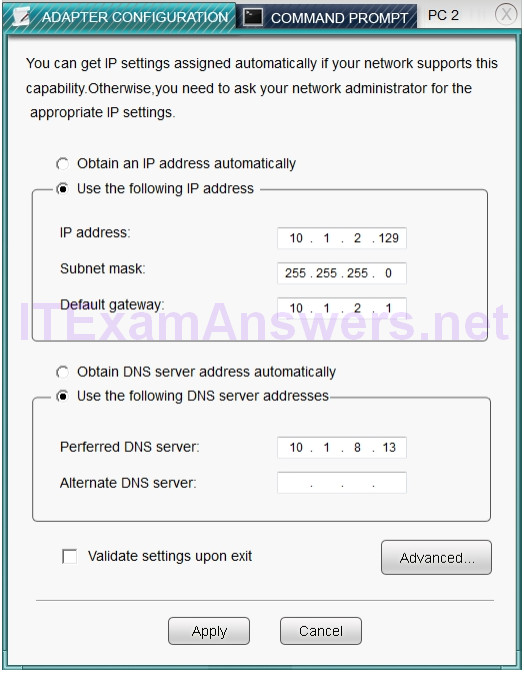
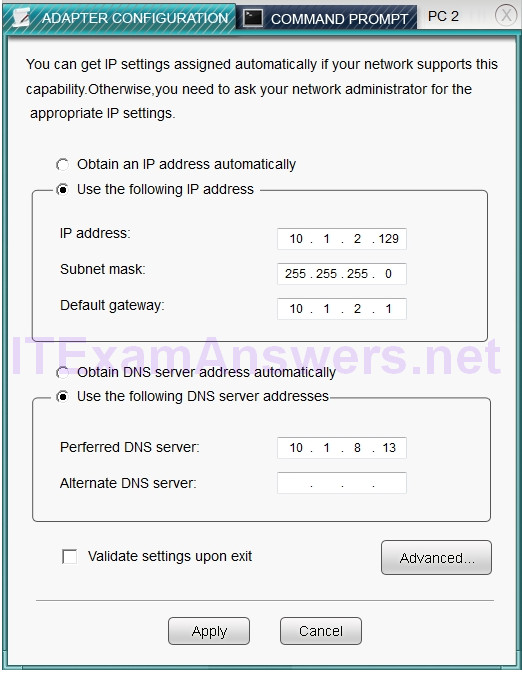
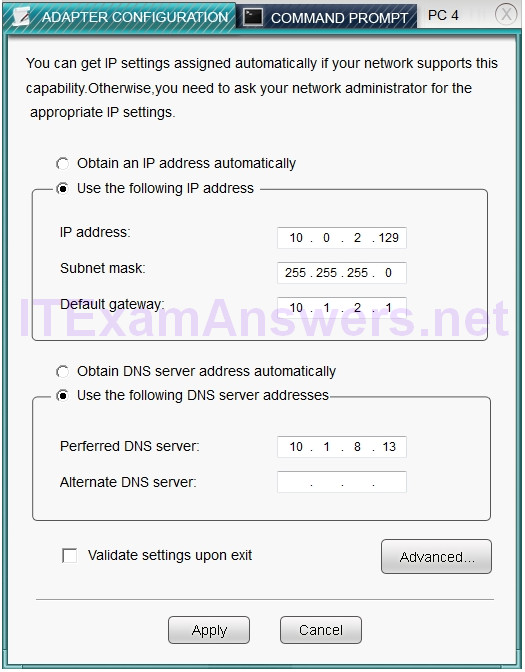
Answer:
On PC3, change the subnet mask to 255.255.255.0.
When it is set to 255.255.255.128, then the PC with a .129 address will not be on the same subnet as the default gateway which is .1 On PC4, change the default gateway to 10.0.2.1.
It has been incorrectly set as 10.1.2.1.
422. Hotspot Question
Corporate headquarters provided your office a portion of their class B subnet to use at a new office location.
Allocate the minimum number of addresses (using CIDR notation) needed to accommodate each department.
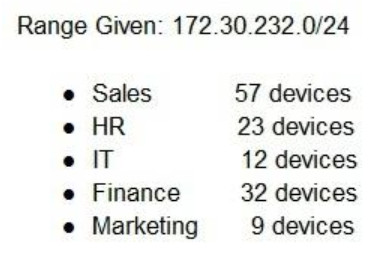
Alter accommodating each department, identify the unused portion of the subnet by responding to the question on the graphic.
All drop downs must be filled.
Instructions: When the simulation is complete, please select the Done button to submit.
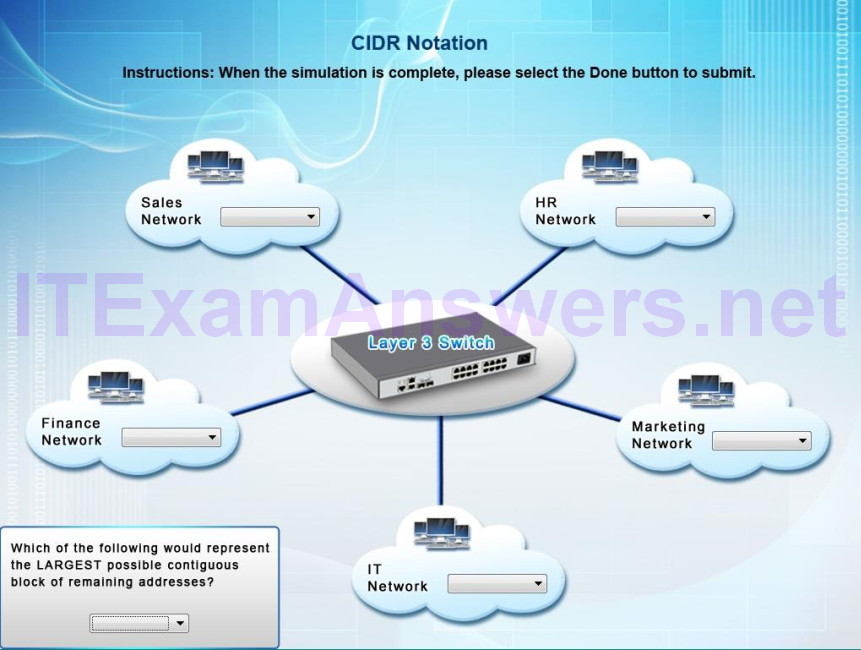
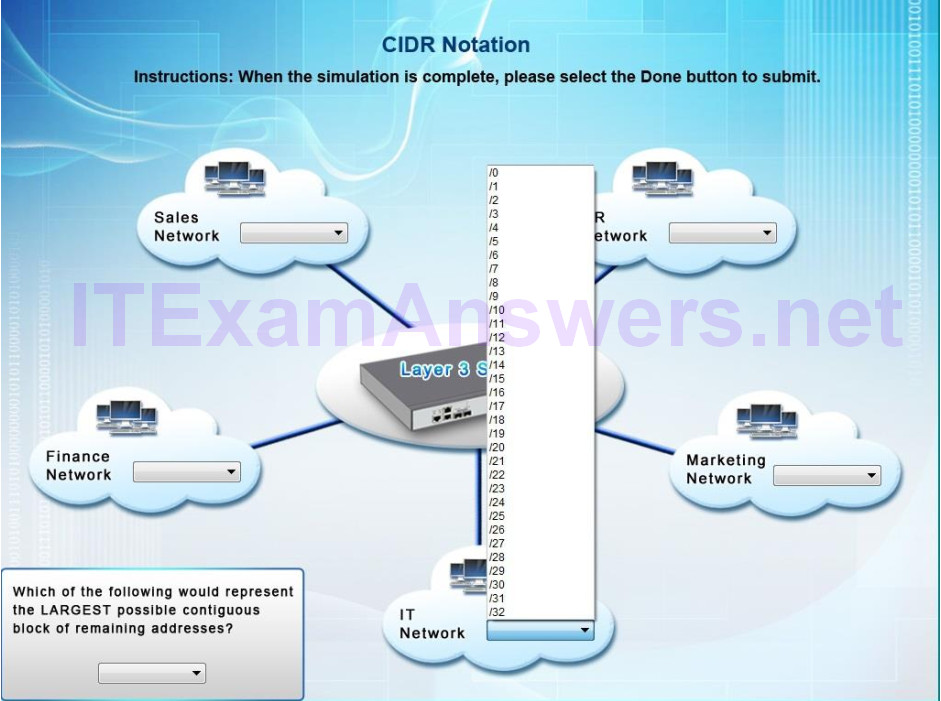

All Networks have the range form /0 to/32
Answer:
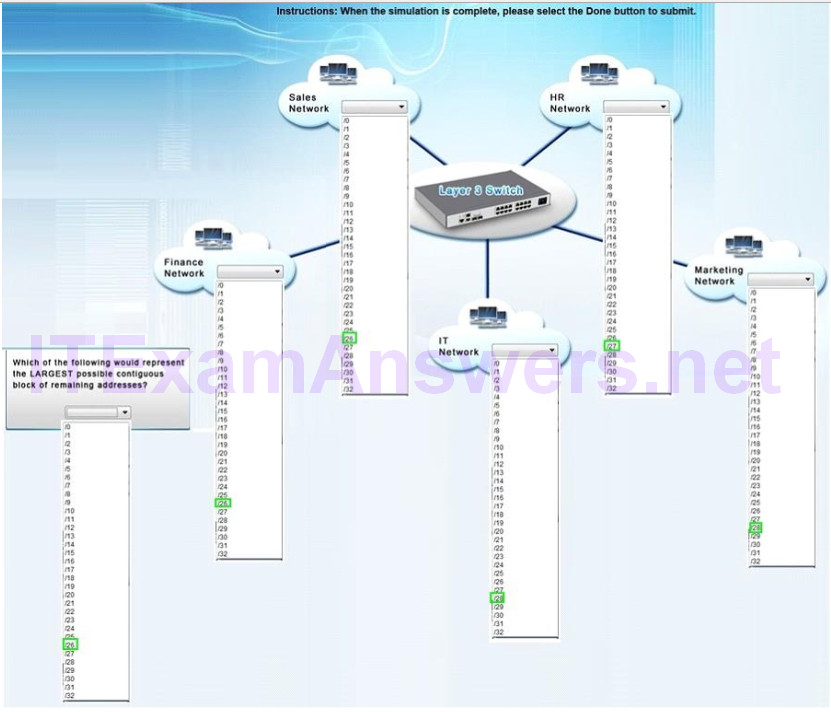
Explanation:
Sales network-/26-This will provide up to 62 usable IP addresses (64-2 for subnet and broadcast IP)
HR network – /27-This will provide for up to 30 usable IP’s (32-2)
IT – /28-This will provide for up to 14 usable IP’s (16-2)
Finance – /26-Note that a /27 is 32 IP addresses but 2 of those are reserved for the network and
broadcast IP’s and can’t be used for hosts.
Marketing – /28
If we add up how many IP blocks are used that is 64+32+16+64+16=192.
A /24 contains 256 IP addresses, so 256-192=64.
So the last unused box should be a /26, which equates to 64 addresses
423. Lab Simulation
After recent changes to the pictured network, several users are unable to access the servers. Only PC1, PC2, PC3, and PC4 are configurable. You can only change the adapter configurations to each PC.
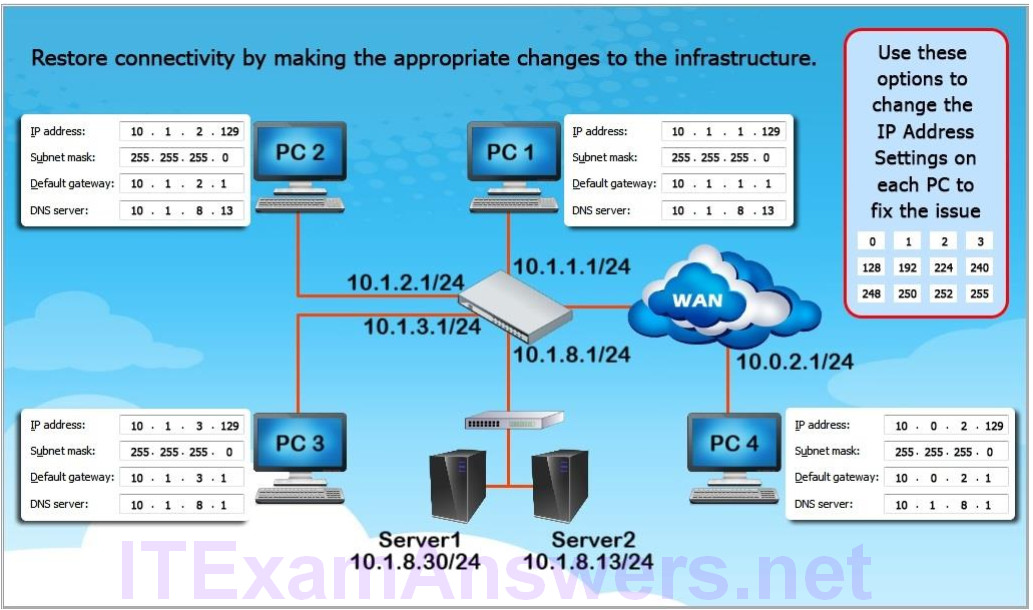
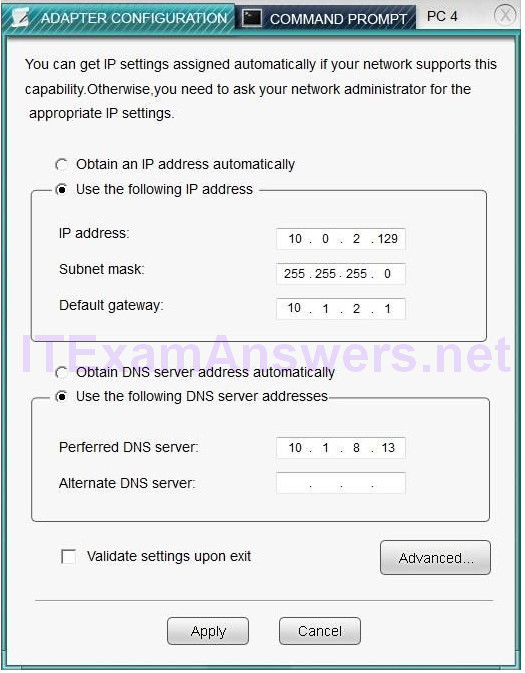
Answer:
On PC3, change the subnet mask to 255.255.255.0. When it is set to 255.255.255.128, then the PC with a .129 address will not be on the same subnet as the default gateway which is .1
On PC4, change the default gateway to 10.0.2.1. It has been incorrectly set as 10.1.2.1.
On this simulation, you will be asked to test connectivity after fixing the issues.
You MUST ping the other three computers on EACH computer (i.e. from PC1, ping PC2, PC3,
PC4, and from PC2, ping PC1, PC3 and PC4, etc)
424. Drag and Drop Question
Build a T-658A Connection
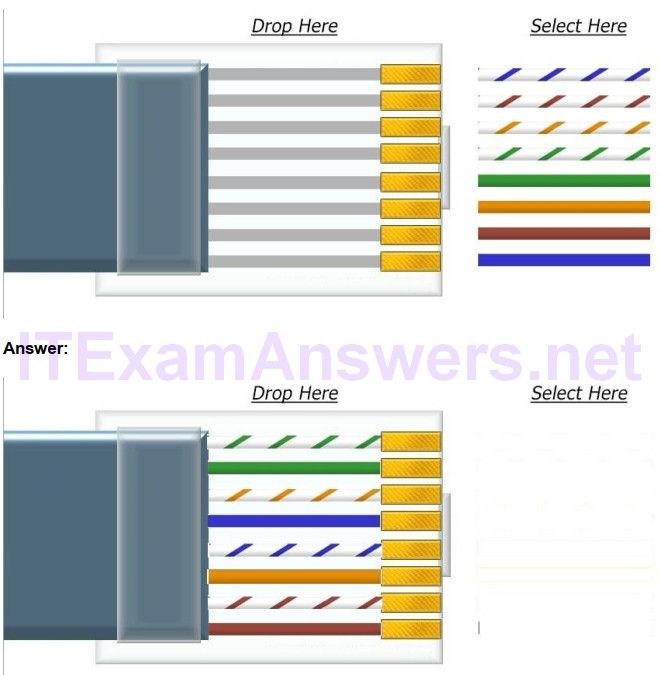
425. Drag and Drop Question
Build a T-658B Connection
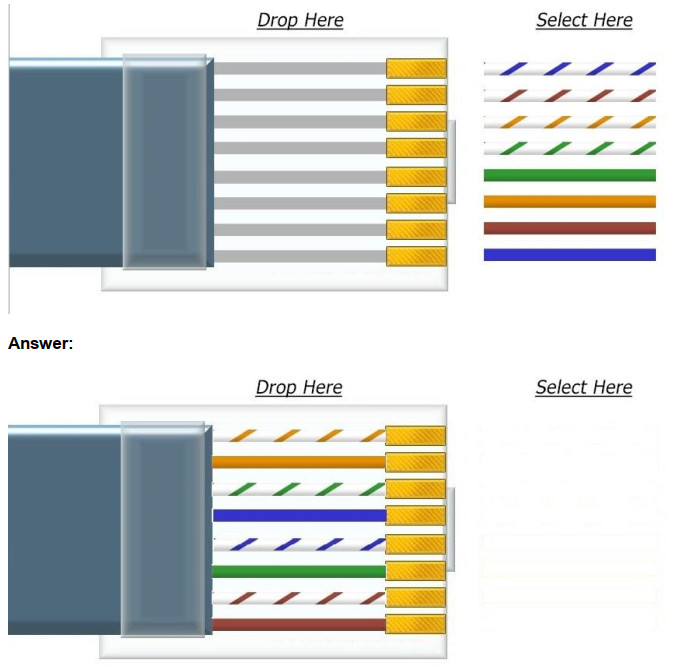
426. Drag and Drop Question
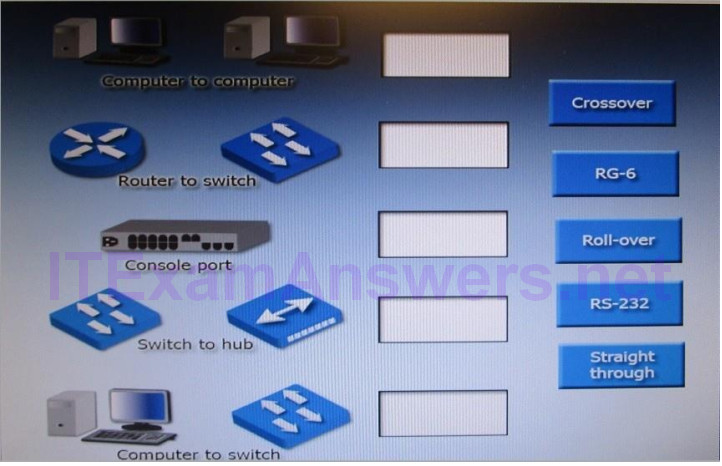
Answer:

427. Drag and Drop Question
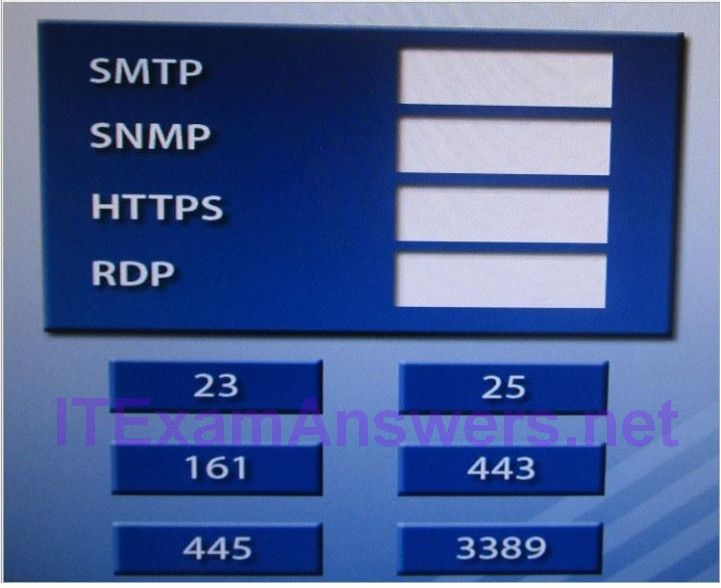
Answer:

428. Drag and Drop Question
You are tasked with creating a network that will accomplish the following requirements
Requirements:
1) The remote sales team must be able to connect to the corporate
network
2) Each department must have ONLY two PCs and a server
3) Each department must be segmented from each other
4) The following VLANs have been designated:
a) VLAN 2- Finance
b) VLAN 12- Sales
c) VLAN 22- Human Resources (HR)
Complete the network by dragging the required objects into the diagram
INSTRUCTIONS: Objects can be used multiple times and not all placeholders need to be filled
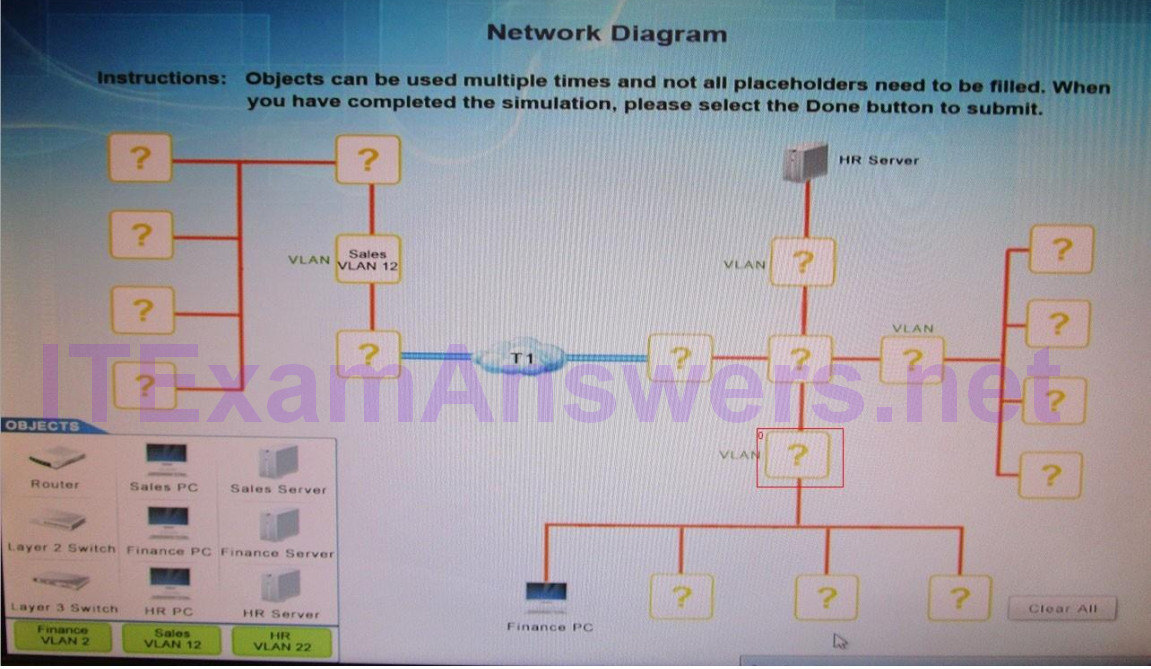
Answer:
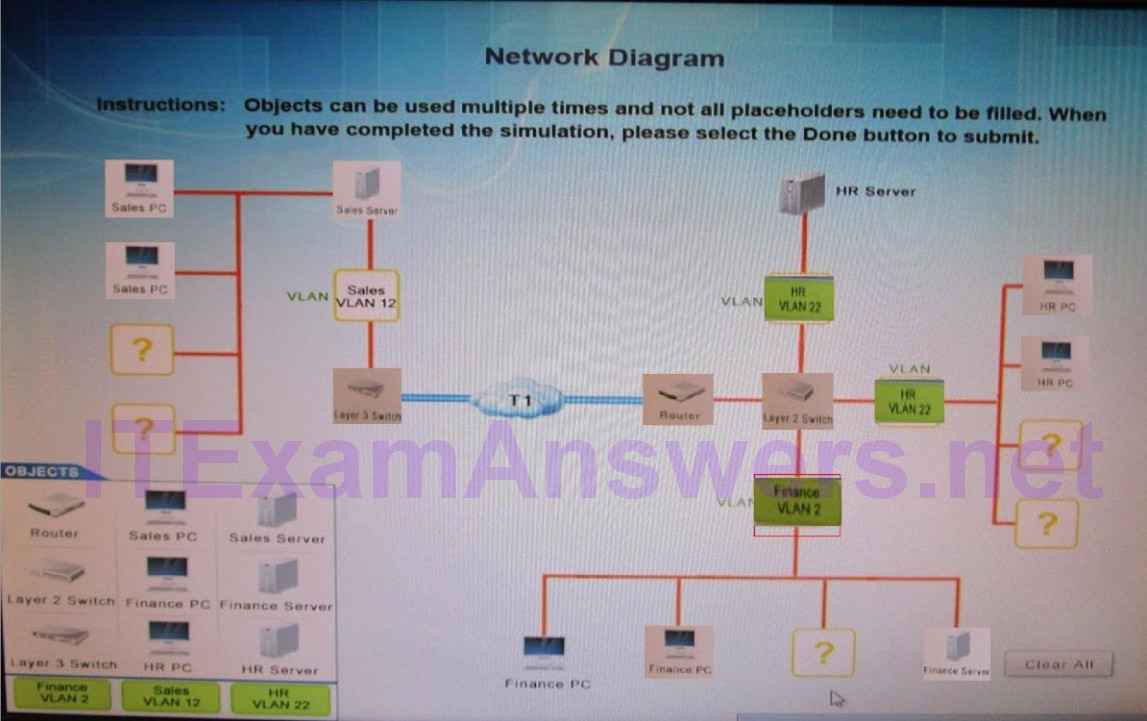
429. Lab Simulation
You have been tasked with setting up a wireless network in an office. The network will consist of 3 access points and a single switch. The network must meet the following parameters.
– The SSIDs need to be configured as corpnet with a key of S3cr3t!
– The wireless signals should not interfere with each other
– The subnet the Access points and Switch are on should only support 30 devices maximum
– The access Points should be configured to only support TKIP clients at a maximum speed
Instructions: Click on the devices to review their information and adjust the setting of the APs to meet the given requirements.
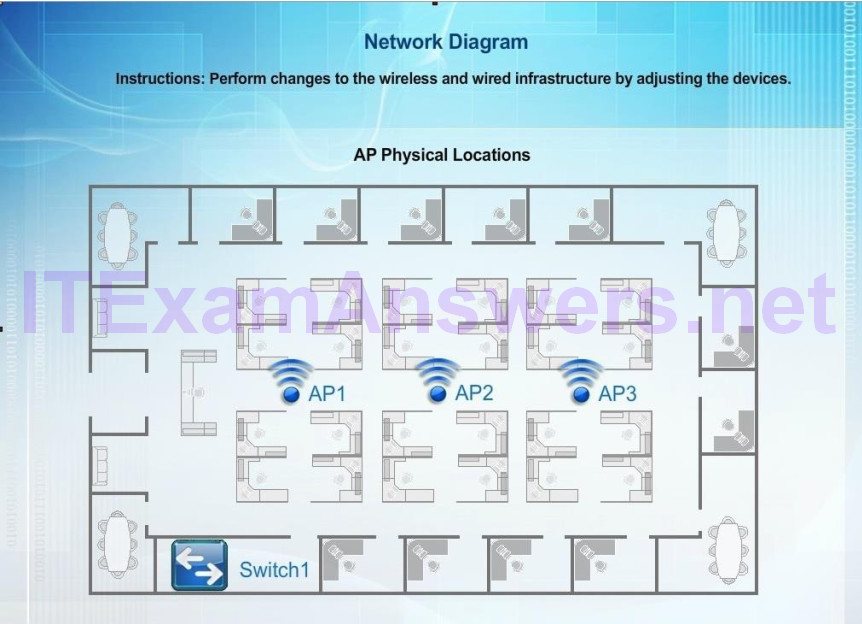
Answer:
This simulation is still under construction. On the first exhibit, the layout should be as follows
Access Point Name AP1
IP Address 192.168.1.3
Gateway 192.168.1.2
SSID corpnet
SSID Broadcast yes
Mode G
Channel 1
Speed Auto
Duplex Auto
WPA
Passphrase S3cr3t!
Exhibit 2 as follows
Access Point Name AP2
IP Address 192.168.1.4
Gateway 192.168.1.2
SSID corpnet
SSID Broadcast yes
Mode G
Channel 6
Speed Auto
Duplex Auto
WPA
Passphrase S3cr3t!
Exhibit 3 as follows
Access Point Name AP3
IP Address 192.168.1.5
Gateway 192.168.1.2
SSID corpnet
SSID Broadcast yes
Mode G
Channel 11
Speed Auto
Duplex Auto
WPA
Passphrase S3cr3t!
430. Drag and Drop Question
Under each network device, drag and drop the associated broadcast and/or collison description.
Objects may be used multiple times, as needed.
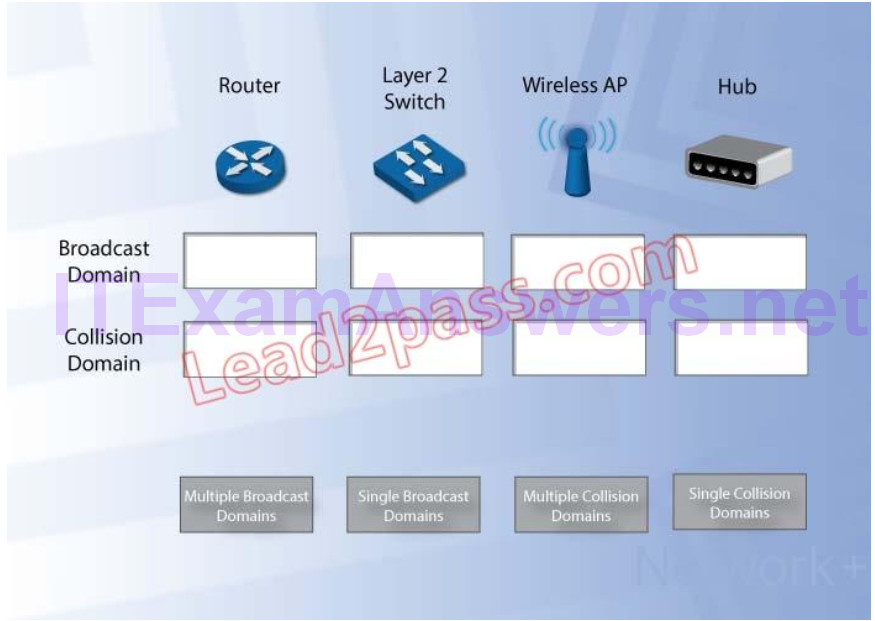
Answer:
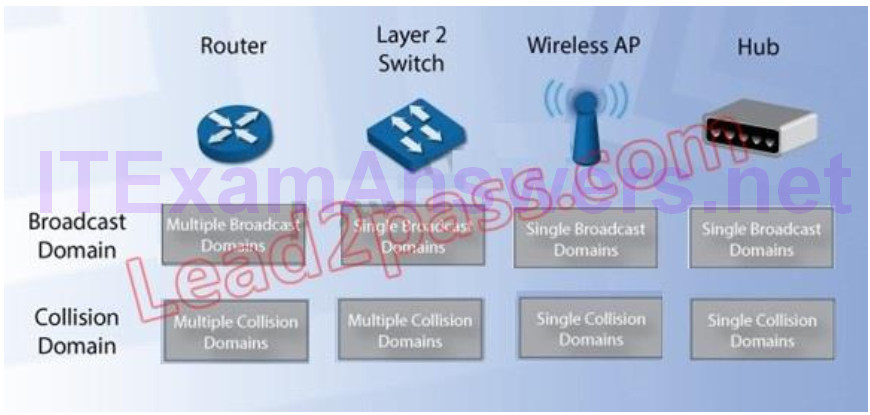
431. Which of the following protocols would the network administrator use to protect login credentials when accessing a router terminal session?
A. SCP
B. SNMPv3
C. SSL
D. SSH
432. A network technician is doing a wireless audit and finds an SSID that does not match the company’s SSID. The company uses the SSID of ABC123, and the SSID the technician found is Default. Which of the following threats did the network technician find?
A. AP isolation
B. DDoS
C. Evil twin
D. Rogue AP
433. A network administrator notices that load balancing is not working properly on the web cluster as previously configured. In speaking with management, a change to the IP addressing scheme was made yesterday which possibly affected one member of the cluster. Due to the timing of the events, the administrator theorizes that this change caused the problem. Which of the following should the administrator do NEXT?
A. Escalate to the management team
B. Change the IP address back to its previous state
C. Test the theory by analyzing logs
D. Create a plan of action to present to management
434. Which of the following are standard fiber cable connector types? (Select TWO).
A. RJ-11
B. F-connector
C. MTRJ
D. DB-9
E. ST
435. A user would like to connect two laptops together and transfer files via the Ethernet ports. Which of the following should MOST likely be provided to the user to accomplish this?
A. Crossover
B. Rollover
C. Loopback
D. Straight cable
436. Hubs are differentiated from switches in that between the two, only hubs have:
A. a single collision domain.
B. a single broadcast domain.
C. multiple collision domains.
D. multiple broadcast domains.
437. The phone company has provided a channelized T1 line. Which of the following should this line be connected to?
A. Switch
B. CSU/DSU
C. IDF
D. MDF
438. Which of the following spreads out each of the individual wires of a UTP cable onto their own metal connector?
A. BNC connection
B. 110 block
C. Plenum
D. LC connector
439. A user at a hotel sees two SSIDs; both are called “HotelWireless”. After the PC connects to one of the APs, the user notices their browser homepage has been changed. Which of the following BEST describes this AP?
A. Man-in-the-middle
B. DDoS
C. Evil twin
D. War driving
440. An administrator would like to search for network vulnerabilities on servers, routers, and embedded appliances. Which of the following tools would MOST likely accomplish this?
A. Baseline analyzer
B. Ping
C. Protocol analyzer
D. Nessus
441. A technician needs to install a new wireless encryption system. They are evaluating the feasibility of implementing WPA. WPA increases protection over WEP by implementing which of the following?
A. Strong RC4 encryption
B. Shared secret keys
C. AES encryption
D. Key rotation
442. A network administrator wants to perform a test to see if any systems are passing clear text through the network. Which of the following would be used?
A. Social engineering
B. Packet sniffing
C. Rogue access point
D. Man-in-the-middle
443. A network administrator is setting up a WAP and wants to disable the ability of gaining access from the parking garage. Which of the following should the network administrator review?
A. Signal strength
B. SSID name
C. WPA2 encryption
D. WEP encryption
444. A network administrator wants to balance the amount of data between two networking cards. Which of the following can be used for two or more networking cards?
A. NIC bonding
B. Proxy server
C. Firewall ACLs
D. VLANs
445. Which of the following assists a network administrator in reverse engineering malware and viruses?
A. Virtual switches
B. Virtual machines
C. VLANs
D. IDS
446. A home user states during a basement remodel, one of the workers cut the network cable that goes from the modem to the WAP and nothing else has changed. According to the network troubleshooting methodology, which of the following is the NEXT step?
A. Identify the problem
B. the user
C. Establish a plan of action
D. Establish a theory of probable cause
447. Which of the following layers of the OSI model make up the Network Interface layer of the TCP/IP model? (Select TWO).
A. Application
B. Physical
C. Presentation
D. Transport
E. Data Link
F. Network
448. At which layer of the OSI model do MAC addresses operate?
A. Data Link
B. Network
C. Application
D. Physical
449. A network technician recently replaced a managed switch in an enterprise network with a new managed switch. Users on the switch can communicate with each other but now cannot access other network segments. Which of the following is the MOST likely reason that the users are unable to access any network segments?
A. The newly installed switch is defective and must be returned.
B. The newly installed switch is using a different MAC address than the previous switch.
C. The technician forgot to change the VTP mode on the new switch to server.
D. The technician did not use the correct cable when trunking the new switch.
450. A network administrator currently collects log files from several different servers. Which of the following would allow the network administrator to collect log files on a centralized host?
A. The network administrator should install and configure a traffic analysis server.
B. The network administrator should install and configure a DMZ server.
C. The network administrator should install and configure a syslog server.
D. The network administrator should install and configure a network sniffer.
451. A company has been given a Class C address to be utilized for all devices. The company has several subnets and the largest subnet has 15 hosts. Which of the following represents the MINIMUM CIDR notation of this subnet mask?
A. /26
B. /27
C. /28
D. /29
452. A company has gone through several upgrades on their network but unfortunately have no way of identifying who approved the upgrades. Which of the following should be implemented to track this type of work?
A. Change management
B. Asset management
C. Access log
D. Baselines
453. An administrator is trying to retrieve management information from the network devices on their LAN. Which of the following monitoring resources provides the ability to collect this information encrypted over the network?
A. SNMPv3
B. VTP
C. CDP
D. IPSec
454. Which of the following WAN technologies utilizes an optical SONET carrier and has a maximum bandwidth of 155.54Mbps?
A. DS3
B. E3
C. OC3
D. T3
455. A network administrator decides to secure their small network by allowing only specific MAC addresses to gain access to the network from specific switches. Which of the following is described by this example?
A. Packet filtering
B. Hardware firewalls
C. Port security
D. Stateful inspection
456. Which of the following is used to limit the amount of bandwidth used on a link for different applications to improve overall performance?
A. QoS
B. Fault tolerance
C. Load balancing
D. Traffic shaping
457. Users are reporting that all of a sudden some of the files stored on the remote file server share are becoming corrupted and cannot be opened. A technician is dispatched to the server room to troubleshoot. The technician verifies that no changes to the network infrastructure occurred recently. Which of the following tools is MOST likely to reveal why files are becoming corrupted?
A. Environmental monitor
B. OTDR
C. Cable tester
D. Punch down tool
458. A large corporate office is looking to place smaller network closets around campus to handle switching for remote workstations. To which of the following is this referring?
A. MDF
B. VPN
C. RDP
D. IDF
459. MIMO technology in the 802.11n standard provides for which of the following benefits?
A. Channel expansion
B. Gigabit wireless bandwidth
C. Multipath support
D. Channel bonding
460. A small office is looking to deploy wireless to cover one half of the work area only. The technician is restricted to suspending the WAP in the middle of the office due to network jack limitations. Which of the following antenna types would BEST meet these requirements?
A. Dipole
B. Parabolic
C. Directional
D. Omni-directional
461. If a technician does not assign an IP address to a device, the DHCP server will assign the device
A. static IP address.
B. reservation.
C. dynamic IP address.
D. MAC address.
462. A technician has been called about intermittent connectivity near IDF 2. Multiple cables were recently pulled through a common conduit. Which of the following is MOST likely the cause of the problem?
A. Crosstalk
B. Bad connectors
C. Wrong DNS
D. Duplicate IP address
463. Which of the following would be used on a network to ensure access to resources if a critical host becomes unavailable?
A. QoS
B. CARP
C. VLAN
D. DHCP server
464. Which of the following is used to ensure traffic flows efficiently on multiple T-1 circuits?
A. DNS server
B. Content filter
C. Proxy server
D. Load balancer
465. All users on a specific network segment report losing access to the wired network. During troubleshooting, the network administrator observes link lights on the workstations. When physically reviewing each switch, the network administrator changes the switch view settings to Activity and sees that all port lights remain solid green. Which of the following is MOST likely causing this issue?
A. STP convergence
B. Power failure
C. Excessive bandwidth usage
D. Broadcast storm
466. Which of the following STP states indicates an inactivated port due to a loop?
A. Disabled
B. Learning
C. Blocking
D. Forwarding
467. Which of the following cables supports 10Gbps throughput and 100 meters as the maximum distance?
A. T1 crossover
B. Singlemode fiber
C. CAT6a
D. Coaxial
468. A number of remote users have reported being unable to securely log on to the company’s network. Upon speaking with some of the employees experiencing the issue, no changes were made to their configurations, usernames, or passwords. The technician establishes a theory that one of the VPN concentrators may be down. Which of the following should the technician do NEXT?
A. Plan to reboot the concentrator as the potential solution
B. Escalate the problem to management
C. Continue to speak to users, questioning if changes have been made
D. Test access to the concentrator to confirm the status
469. In a small office environment, one computer is set up to provide Internet access to three other computers that are not interconnected. This is an example of which of the following topology types?
A. Peer-to-peer
B. Point-to-multipoint
C. Hybrid
D. Point-to-point
470. A network technician is trying to run a protocol analyzer and is instructed to record the chimney offload state of TCP. Which of the following utilities did the technician use to check this parameter with the output listed below?
Querying active state... TCP Global Parameters ---------------------------------------------- Receive-Side Scaling State : enabled Chimney Offload State : disabled Receive Window Auto-Tuning Level : normal Add-On Congestion Control Provider : ctcp ECN Capability : disabled RFC 1323 Timestamps : disabled
A. net
B. netstat
C. nbtstat
D. netsh
471. Which of the following can use a third party back-end LDAP user database for authentication?
A. ISAKMP
B. TACACS+
C. PKI
D. CHAP
472. A technician has spent most of the day replacing a server running DHCP. Some of the users have begun to call the help desk stating that Internet connection stopped working even after rebooting. Upon investigation, the users’ PCs with issues all have IP addresses that start with 169.254.x.x. The technician completes the replacement and powers on the new DHCP server. Which of the following is the BEST way to provide the PCs with issues a new IP address?
A. Statically assign a legitimate IP address, and then set the PCs’ NICs to DHCP
B. Inform each user to replace 169.254 with 192.168
C. Wait five minutes until the PC resends a DHCP request
D. Run netstat on each PC and then reboot into safe mode
473. A network administrator is implementing an IPS on VLAN 1 and wants the IPS to learn what to prevent on its own. Which of the following would MOST likely be installed?
A. Honeynet
B. Signature based IPS
C. Behavior based IPS
D. Host based IPS
474. Which of the following network topologies is ONLY possible between two users?
A. Star
B. Client-server
C. Hybrid
D. Peer-to-peer
475. Ann, a new user, is unable to communicate on the network from her computer. A technician has verified that the cables are functioning properly. Based on the information below, which action should the technician take to correct Ann’s problem?
Computer_ASwitch_A IP: 10.0.0.60Int VLAN10 SM: 255.255.255.0IP address 10.0.0.1/28 GW: 10.0.0.1Speed 100 Duplex Full
A. Change the duplex on the switch interface to half
B. Change the speed on the switch interface to 10Mbps
C. Change the subnet mask of the computer to 255.255.255.240
D. Change the IP address of the computer to 10.0.0.12
476. A new technician has been tasked with implementing a QoS policy for the Network. The technician decides it would be best to monitor the information traversing the network to gain statistical information on ports and protocols utilized. Which of the following tools should the technician use to complete this objective QUICKEST?
A. Traffic analyzer
B. Network sniffer
C. SNMPv3
D. System logs
477. Users report that they are unable to access the production server with IP address 192.168.30.17. These users need to be provided access without changing any subnet to VLAN information. The VLANs configured on the network are listed below:
DepartmentVLAN #Subnet used Marketing20192.168.20.0/28 Customer Service25192.168.20.64/28 Finance30192.168.30.0/28 WHSE35192.168.30.16/28 Sales40192.168.3.16/28
The users experiencing this issue need to be added to which of the following VLANs?
A. 25
B. 30
C. 35
D. 40
478. A technician is installing an 802.11n network. The technician is using a laptop that can connect at a maximum speed of 11 Mbps. The technician has configured the 802.11n network correctly but thinks it could be the type of WLAN card used on the laptop. Which of the following wireless standards is the WLAN card MOST likely using?
A. 802.11a
B. 802.11b
C. 802.11g
D. 802.11n
479. Which of the following firewall rules will block destination telnet traffic to any host with the source IP address 1.1.1.2/24?
A. Deny any source host on source port 23 to destination any
B. Deny any source network 1.1.1.0/24 to destination any on port 23
C. Deny source host 1.1.12 on source port 23 to destination any
D. Deny any source network 1.1.1.0/24 with source port 23 to destination any
480. Which of the following addresses is a class B private address?
A. 132.216.14.184
B. 152.119.25.213
C. 162.17.43.22
D. 172.23.226.34
481. A technician installs a wireless router on an existing network by connecting it directly to the firewall. By default, the main network is a Class A network, while the wireless network is a Class C network. After the wireless router is installed, users connected to the wireless network report they are unable to connect to the Internet. Which of the following needs to be configured to BEST resolve this issue?
A. Configure the main network to Class C
B. Allow for duplicate IP addresses
C. Allow the main network to handle DHCP
D. Create a spanning tree to prevent switching loops
482. Which of the following configurations of a wireless network would be considered MOST secure?
A. WEP using MAC Filtering
B. WEP and hiding the SSID
C. WPA2
D. WPA TKIP and hiding the SSID
483. Which of the following is the minimum subnet mask to allow 172.16.1.5 and 172.16.4.3 to be on the same subnet?
A. /19
B. /21
C. /22
D. /24
484. DHCP uses which of the following ports by default?
A. 21
B. 23
C. 68
D. 443
485. Which of the following describes a manually entered route?
A. Static
B. Dynamic
C. Multicast
D. Unicast
486. Which of the following is the unit used to transfer information at Layer 2 of the OSI model?
A. Packet
B. Socket
C. Session
D. Frame
487. A network technician visits a site that needs voice connectivity to the corporate office and installs four IP phones. The phone exchange resides at the telephone company. Which of the following technologies is being used?
A. Virtual switch
B. Virtual server
C. Virtual desktop
D. Virtual PBX
488. A client has just leased a new office space in a busy commercial building and would like to install a wireless network. Several other tenants are on the same floor. Multiple wireless networks are present in the building. Which of the following can be changed on the client’s wireless network to help ensure that interference from other wireless networks is at a minimum?
A. WPA encryption key selection
B. Channel selection
C. Antenna types
D. Disable SSID
489. A MAC address is a part of which of the following OSI model layers?
A. Network
B. Data Link
C. Physical
D. Transport
490. Which of the following is the reason why a company’s network may contain a DHCP server?
A. To assign IP addresses to devices on the network
B. To convert IP addresses to fully qualified domain names
C. To provide POP3 and IMAP email functionality
D. To allow secure remote access
491. A company recently added an addition to their office building. A technician runs new plenum network cables from the switch on one side of the company’s gymnasium 80 meters (262 ft.) to the new offices on the other side, draping the wires across the light fixtures. Users working out of the new offices in the addition complain of intermittent network connectivity. Which of the following is MOST likely the cause of the connectivity issue?
A. dB loss
B. Distance
C. Incorrect connector type
D. EMI
E. Crosstalk
492. Which of the following tools would a technician use to determine if a CAT6 cable is properly terminated?
A. Cable tester
B. Punch down tool
C. Crimper
D. Multimeter
493. An administrator is able to list the interfaces on a switch after providing the community string “public”. Which of the protocols is the administrator MOST likely using?
A. Telnet
B. RADIUS
C. SSH
D. SNMP
494. Which of the following characteristics allows an 802.11g WAP to have transfer speeds up to 108Mbps?
A. MIMO technology
B. Channel bonding
C. Encryption type
D. Frequency
495. The systems administrator has assigned an IP address and default gateway to a standard Layer 2 switch. Which of the following would be the primary purpose of doing this?
A. Allow VLAN routing
B. Enable packet filtering on the switch
C. Allow remote administration of the switch
D. Enable MAC filtering on the switch
496. Ann, a technician, installs a wireless router in a network closet in a large office. She then configures all workstations in various offices on that floor to use the wireless connection. Maximum connection speed at each workstation is 54 Mbps. Some users complain that their network connection is very slow. Which of the following is MOST likely the problem?
A. Workstations were configured with the wrong connection speed on the wireless adapter.
B. Users with a slow connection are too far away from the wireless router.
C. Users that cannot connect are configured on the wrong channel.
D. Wireless network SSID is incorrect.
497. Which of the following dynamic routing protocols selects routing paths based upon hop count?
A. BGP
B. RIP
C. OSPF
D. IGRP
498. A technician, Joe, visits a site that has reported a network down emergency. He immediately reboots the switches and the router since the network is down. Which of the following network troubleshooting methodology steps should Joe have performed FIRST?
A. Determine if anything has changed
B. Once a theory is confirmed determine the next step is to resolve the problem
C. Implement the solution or escalate as necessary
D. the obvious
499. A network technician is designing a SOHO environment where cost is a consideration. The requirements include access to the Internet and access to the guest house which is 100 feet away. The location of the Internet modem is located in the main house. Which of the following is the BEST option to accomplish these requirements?
A. Use two combined Internet/router/wireless devices, one in each house.
B. Use a Layer 3 switch in the main house and a combined Internet/router/wireless device in the guest house.
C. Use a combined Internet/router/wireless device in the main house and a wireless access point in the guest house.
D. Use a single combined Internet/router/wireless device at the guest house.
500. Which of the following cable types is MOST commonly used with POTS?
A. CAT3
B. Multimode
C. CAT6
D. Coaxial
501. Which of the following is used to determine whether or not a user’s account is authorized to access a server remotely?
A. VPN
B. RDP
C. LDAP
D. Encryption
502. A firewall that detects and prevents attacks from outside the network based on learned data patterns can BEST be described as which of the following?
A. Signature based IDS
B. Behavior based IPS
C. Host based IPS
D. Network based IDS
503. Which of the following technologies prevents network collisions to maximize safe delivery of network data?
A. CSMA/CA
B. DWDM
C. RADIUS
D. SONET
504. Which of the following are authentication methods that can use AAA authentication? (Select TWO).
A. Kerberos
B. PKI
C. TKIP/AES
D. MS-CHAP
E. RADIUS
F. TACACS+
505. A company is connected to an ISP, but owns the premise router with an internal CSU/DSU. Which of the following is considered the demarc?
A. Premise router
B. ISP router
C. Smart jack
D. CSU/DSU
506. Which of the following are considered AAA authentication methods? (Select TWO).
A. Kerberos
B. Radius
C. MS-CHAP
D. TACACS+
E. 802.1X
507. An IP camera has a failed PoE NIC. This is the third time in months that a PoE NIC has failed on this device. The technician suspects a possible power issue. Which of the following should be used to test the theory?
A. Toner probe
B. Loopback plug
C. Protocol analyzer
D. Multimeter
508. A technician is troubleshooting a network issue and needs to view network traffic on a switch in real-time. Which of the following would allow the technician to view network traffic on a switch?
A. ISAKMP
B. Port forwarding
C. Port security
D. Port mirroring
509. A technician finds that the network card is no longer functioning. At which of the following OSI layers is the problem occurring?
A. Layer 1
B. Layer 3
C. Layer 5
D. Layer 7
510. The address 6FFE:FFFF:0000:2F3B:04AC:00FF:FEBE:5C4A is an example of which of the following?
A. APIPA
B. MAC
C. IPv4
D. IPv6
511. An administrator has added four switches to a campus network. The switch in wiring closet A is only connected to the switch in wiring closet C. The switch in wiring closet B is connected to the switch in wiring closet C as well as wiring closet D. The switch in wiring closet D is only connected to the switch in wiring closet B. Which of the following topologies is represented in this design?
A. Ring
B. Star
C. Bus
D. Mesh
512. A company wants an administrator to perform a vulnerability test. The administrator finds the company has a POTS phone system. Which of the following can the administrator use to point out the phone system vulnerability?
A. Honeypot
B. Butt set
C. Spyware
D. Blue jacking
513. Which of the following is used to explain guidelines for users while using network resources?
A. Network cut sheet
B. Baselines
C. Acceptable use policy
D. Regulations
514. Standards such as JPEG and ASCII operate at which of the following OSI model layers?
A. Presentation
B. Data link
C. Session
D. Application
515. Which of the following cable types is employed to protect against interference in the physical environment or when security is a concern?
A. STP
B. RG-6
C. Fiber
D. RG-59
516. A technician is responsible for configuring a new firewall. The hardware team has already installed, powered, and connected the system. Which of the following types of documentation should the technician utilize to complete the task?
A. Rack diagram
B. IDF/MDF documentation
C. Network performance baseline
D. Logical and physical diagrams
517. Which of the following networking devices operates at Layer1?
A. Router
B. Firewall
C. Hub
D. Bridge
518. A disgruntled employee decides to leak critical information about a company’s new product. The employee places keyloggers on the department’s computers, allowing the information to be sent out to the Internet.
Which of the following attacks is occurring?
A. Man-in-the-middle
B. Logic bomb
C. Insider threat
D. Social engineering
519. A network technician needs to set up an access method for Ann, a manager, to work from home. Ann needs to locally mapped corporate resources to perform her job. Which of the following would provide secure access to the corporate resources?
A. Utilize an SSH connection to the corporate server.
B. Use TFTP to transfer files to corporate resources.
C. Allow RDP through an external firewall.
D. Connect utilizing client-to-site VPN.
520. Which of the following DNS record types is an alias?
A. CNAME
B. PTR
C. NS
D. SRV
521. A recently constructed building makes use of glass and natural light. Users in the building are reporting poor cellular connectivity and speeds. Which of the following is MOST likely the cause?
A. Absorption
B. Channel overlap
C. Reflection
D. Frequency mismatch
522. A network technician is working on a new switch implementation to expand the network. Which of the following is the BEST option to ensure the implementation goes according to business requirements?
A. AUP
B. NDA
C. SOP
D. SLA
523. A technician is utilizing SNMPv3 to monitor network statistics. Which of the following actions would occur immediately of a server’s utilization spikes above the prescribed value?
A. A trap message is sent via UDP to the monitoring workstation.
B. The SET function pushes an alert to the MIB database.
C. The object identifier is modified and reported during the next monitoring cycle.
D. A response message is sent from the agent to the manager.
524. In which of the following scenarios should a technician use a cross-over cable to provide connectivity?
A. PC to switch
B. Switch to AP
C. Router to switch
D. Router to modem
E. PC to PC
525. 802.11n clients currently have no way to connect to the network. Which of the following devices should be implemented to let the clients connect?
A. Router
B. Range extender
C. VoIP endpoint
D. Access point
526. A network technician is setting up a new router. Since it is exposed to the public, which of the following are the BEST steps the technician should take when setting up this device? (Choose two.)
A. Disable unnecessary services.
B. Use private IP addresses.
C. Allow remote management access.
D. Disable the console port.
E. Enable encryption.
F. Upgrade to the latest firmware.
527. A network technician is configuring user access to a VPN concentrator and has been advised to use a protocol that supports encryption over UDP. Which of the following protocols has the technician MOST likely configured for client use?
A. TFTP
B. DTLS
C. DNS
D. SNMP
528. A switch has detected duplicate broadcast messages sourced from a second port. The broadcasts continue to be transmitted and duplicated until the amount of traffic causes severe performance issues. Which of the following should be configured to prevent this behavior?
A. BPDU guard
B. DHCP snooping
C. ARP protection
D. Spanning tree
529. A Chief Information Officer (CIO) is concentrated about an attacker gaining administrative access to the company’s network devices. Which of the following is the MOST secure way to prevent this?
A. ACL allowing only HTTP
B. ACL allowing only Telnet
C. Out-of-band modem
D. Out-of-band console router
530. The Chief Executive Officer’s (CEO’s) tablet cannot connect to the wireless network from the corner office. A network technician verified the tablet can connect to the wireless network in other areas of the building. The distance between the office and the 802.11ac WAP is 150ft (46m), and there are a few cubicles in between. Which of the following is the MOST likely cause of the tablet not connecting?
A. Absorption
B. Reflection
C. Distance
D. Refraction
E. Attenuation
531. A company has two geographically separate locations that need to connect using a VPN. Which of the following devices must be specifically configured to allow VPN traffic into the network?
A. Firewall
B. Switch
C. Router
D. Modem
532. A technician is working on a new machine that has been procured for testing and development. The machine will run a hypervisor and host several operating systems of various types so the development team can test the company’s applications in a variety of environments. The technician wants the virtual machines to be available to communicate with each other without leaving the hypervisor. Which of the following is the BEST solution to the problem?
A. The technician should connect the machine to its own separate switch.
B. The technician should add a route in each virtual machine to the default gateway.
C. The technician should configure a virtual switch.
D. The technician should set up individual routes between the machines.
533. A network technician is repurposing a switch that has been in storage for some time. The device has been wiped to factory defaults. Which of the following should be done FIRST to ensure the device has been hardened before configuration?
A. Generate new keys.
B. Disable unused ports.
C. Check for updated firmware.
D. Configure the default VLAN.
534. A technician is setting up a wireless access point in a coffee shop. The shop is not concerned with security but only wants to allow customers to have access. Which of the following configurations should the technician deploy?
A. Use a pre-shared key.
B. Set up EAP.
C. Configure RADIUS.
D. Configure MAC filtering.
535. A network technician at a small office upgrades the LAN switch. After the upgrade, a user reports being unable to access network resources. When the technician checks the switchport, the LED light is not lit. Which of the following should the technician check FIRST?
A. The device is using the correct cable type.
B. The switchport is functioning properly.
C. The device is connected to the switch.
D. The switch is connected to the router.
536. A technician looks at an ARP table in an attempt to resolve a connectivity issue. After table of the switch is a cleared, a different MAC in the output, Which of the following does this indicate?
A. ARP flooding
B. VLAN mismatch
C. Duplicate IP address
D. Faulty NIC
537. Which of the following is networking stand-alone hardware that will permit any WiFi-compliant device to connect to a network?
A. Wireless hub
B. Wireless firewall
C. Wireless access point
D. Wireless bridge
538. An administrator wants to implement an additional authentication factor to the remote SSH servers. Which of the following accomplishes this goal with the principle of “something you have”?
A. Certificate
B. Pattern
C. Password
D. Fingerprint
539. Which of the following devices are MOST often responsible for 1q tagging? (Select TWO).
A. Switch
B. Router
C. IDS
D. Hub
E. IPS
F. Network tap
540. A VoIP system will require 23 concurrent voice channels and signaling channel. Which of the following types of service would provides the BEST connectivity to the PSTN?
A. PRI
B. BRI
C. E1/E3
D. DSL
541. A company decides to deploy customer-facing, touch-scan kiosks. The kiosks appear to have several open service ports that could potentially become compromised. Which of the following is the MOST effective way to protocol the kiosks?
A. Install an IDS to monitor all traffic to and from the kiosks.
B. Install honeypots on the network to detect and analyze potential kiosk attacks before they occur.
C. Enable switchport security on the ports to which the kiosks are connected to prevent network ?level attacks.
D. Create a new network segment with ACLs, limiting kiosks’ traffic with the internal network.
542. A network technician is configuring user’s access to a VPN concentrator and has advised to use a protocol that supports encryption over UDP.
Which of the following protocols has the technician MOST likely configured for client use?
A. TFTP
B. DTLS
C. DNS
D. SNMP
543. A network technician at a small office upgrades the VLAN switch. After the upgrade, a user reports being unable to access network resources. When the technician checks the switchport, the LED light is not lit. Which of the following should technician check FIRST?
A. The device is using the correct cable type.
B. The switchport is functioning properly.
C. The device is connected to the switch.
D. The switch is connected to the router.
544. Which of the follow creates a secure remote connection at the OSI network layer?
A. L2TP
B. SSL
C. DTLS
D. IPSec
545. A junior technician is settings up a voice control device so the Chief Executive Officer (CEO) will able to control various things in the office. Of which of the following types of the loT technologies is this an example?
A. LAN
B. WAN
C. SAN
D. PAN
546. A technician is downloading an ISO from a vendor’s website. To ensure the integrity of the download, which of the following should be verified?
A. File size
B. Vendor URL
C. File hashing
D. Encryption
547. A network administrator is assigned to run and connect a Cat 6e Ethernet cable between two nodes in a datacenter. Which of the following connector types should the network administrator use to terminate this cable?
A. DB-9
B. RS-232
C. DB-25
D. RJ-45
548. Management has requested that services be available within 72 hours of a disaster. Budget is a major concern. A contract is signed with a company that has plenty of space, and the technician will have the option of putting infrastructure equipment in place. Which of the following BEST describes this business continuity strategy?
A. Cold site
B. Differential backup
C. Hot site
D. Incremental backup
E. Warm site
F. Full backup
549. A network technician is planning to update the firmware on a router on the network. The technician has downloaded the file from the vendor’s website. Before installing the firmware update, which of the following steps should the technician perform to ensure file integrity?
A. Perform antivirus and anti-malware scans of the file.
B. Perform a hash on the file for comparison with the vendor’s hash.
C. Download the file a second time and compare the version numbers.
D. Compare the hash of the file to the previous firmware update.
550. A network technician performs a wireless site survey at a company building and identifies that the cafeteria is not covered by a wireless signal. The cafeteria is located in a medium-size, squareshaped room. Which of the following types of WAP antenna should the technician install in the center of the cafeteria to provide the BEST coverage?
A. Unidirectional
B. Parabolic
C. Omnidirectional
D. Yagi
551. An entire enterprise cannot access a specific website. The network technician knows the website was accessible last week. The technician can also ping the website. Which of the following is the technician MOST likely to find upon investigation?
A. The firewall is misconfigured.
B. The network is being hit by a zero-day attack.
C. The SSL certificate is untrusted.
D. The SSL certificate has expired.
552. At which of the following OSI model layers would a router operate?
A. Physical
B. Network
C. Transport
D. Data link
553. Which of the following are DNS record types? (Choose three.)
A. CNAME
B. NTP
C. PTR
D. LDAP
E. DHCP
F. TTL
G. SRV
H. SSH
554. Which of the following backup techniques is used to capture all the data that has changed since the last full backup?
A. Incremental
B. Replica
C. Differential
D. Snapshot
555. A network administrator frequently needs to assist users with troubleshooting network hardware remotely, but the users are non-technical and unfamiliar with network devices. Which of the following would BEST help the administrator and users during hands-on troubleshooting?
A. Logical diagrams
B. MDF documentation
C. Equipment labeling
D. Standard operating procedures
556. A technician is observing brownout issues at a smaller office. At least once a week, the edge switch power cycles. Which of the following should the technician do to resolve the issue?
A. Install a new switch
B. Install a UPS
C. Replace the switch uplink cable.
D. Install a new electrical circuit.
557. A technician is troubleshooting a workstation’s network connectivity and wants to confirm which switchport corresponds to the wall jack the PC is using. Which of the following concepts would BEST help the technician?
A. Consistent labeling
B. Change management
C. Standard work instructions
D. Inventory management
E. Network baseline
558. Under which of the following layers of the OSI model do ATM cells operate?
A. Data link
B. Network
C. Session
D. Transport
E. Presentation
559. A new building needs to be joined to an existing network, but management has decided that running fiber is too expensive. Since the buildings are about 1000ft (305m) apart, the IT department has been asked to propose alternatives. Which of the following is the BEST device to add to each building to facilitate the extension of the network while meeting budgetary demands?
A. Switch
B. Router
C. Media converter
D. PRP wireless
560. A junior network technician is working in the field and needs to connect to the company’s remote server, however, doing so will require the junior technician to use the public Internet. Because security is a concern, which of the following is the BEST method to use?
A. Telnet
B. SSH
C. SFTP
D. VNC
561. A home user has purchased a new smart TV to stream online video services. The smart TV is unable to connect to the wireless network after several attempts. After returning from vacation, the home user tries again and can connect the TV to the wireless network. However, the user notices a laptop is no longer able to connect to the network. Which of the following is the MOST likely cause?
A. The DHCP scope has been exhausted.
B. The security passcode has been changed.
C. The SSID is hidden.
D. The AP configuration was reset.
562. A security guard notices an authorized individual, who is dressed like a lab technician, has entered a secure area of the hospital with a large group. Which of the following security attacks is taking place?
A. Evil twin
B. Social engineering
C. Insider threat
D. Phishing
563. Which of the following DNS record types allows IPv6 records to be resolved to DNS names?
A. PTR
B. A
C. AAAA
D. SRV
564. A network technician has recently installed new VoIP phones at all employee’s desks to support a new SIP cloud VoIP solution. However, the technician is unable to make a call from the device after testing. Which of the following should the technician verify? (Choose two.)
A. TCP 443 is allowed.
B. UDP 1720 is allowed.
C. UDP 5060 is allowed.
D. UDP 5061 is allowed.
E. TCP 8080 is allowed.
F. TCP 8181 is allowed.
565. Which of the following would allow a network technician to access files on a remote system? (Choose two.)
A. FTP
B. TFTP
C. VLSM
D. SIP
E. SMTP
F. IMAP
566. Which of the following provides two-factor authentication?
A. Username + password
B. Smart card + PIN
C. Fingerprint + retina scan
D. Key fob + ID card
567. A technician set up a new SOHO network recently. The installed router has four Ethernet ports, however, the customer has seven devices that need wired connections. Which of the following should the technician do to BEST meet the customer’s requirements?
A. Install a six-port switch.
B. Configure port forwarding on the router.
C. Install WAPs near the devices.
D. Configure the switchports as EtherChannel ports.
568. A technician is performing a maintenance task on a weekly basis and wants to ensure the task is properly documented and able to be performed by other technicians. Which of the following types of documentation should the technician complete?
A. Standard operating procedure
B. Work order
C. Performance baseline
D. Logical diagram
E. Change management
569. A company is allowing its employees to use their personal computers, tablets, and IoT devices while at work. However, there are rules and guidelines to which employees must adhere. Which of the following documents applies to these employees?
A. NDA
B. SOP
C. BYOD
D. SLA
570. Which of the following are characteristics of jumbo frames? (Choose two.)
A. Commonly used on SAN
B. MTU size greater than 1500
C. MTU size greater than 10000
D. Commonly used on IaaS
E. MTU size greater than 12000
571. A network administrator gets a call regarding intermittent network outages across the country. Which of the following should be used to connect to the network so the administrator can troubleshoot this issue from home? (Choose two.)
A. FTP
B. SMTP
C. VPN
D. SSH
E. SNMP
572. A network technician downloaded new firmware for the company firewall. Which of the following should the network technician verify to ensure the downloaded file is correct and complete?
A. File hash
B. File date
C. File type
D. File size
573. A technician is troubleshooting network connectivity issues with a remote host. Which of the following tools would BEST inform the technician of nodes between the client and the remote host? (Choose two.)
A. tracert
B. ping
C. tcpdump
D. pathping
E. netstat
F. nslookup
G. route
574. Which of the following will listen on the line to ensure there is no traffic transmitting and implement a back- off timer if a collision occurs?
A. CSMA/CD
B. CSMA/CA
C. MPLS
D. OSPF
575. A network technician receives a call from a branch office about a problem with its wireless connectivity. The user states the office is hosting a large meeting that includes some online training with local businesses. The guest users have all brought devices to connect to the guest network at the branch office. All users are connected to a single WAP and are reporting that connections keep dropping and network spends are unusable. Which of the following is the MOST likely cause of this issue?
A. DHCP exhaustion
B. Channel overlapping
C. Interference
D. Overcapacity
576. Which of the following BEST describes an exploit?
A. A router with default credentials
B. An open mail relay server
C. An SNMPv1 private community
D. A privilege escalation script
577. A server in a LAN was configured to act as a gateway between all company computers and an external network. Which of the following networking devices offers the ability to increase both performance and security?
A. Load balancer
B. IDS
C. Proxy server
D. Wireless controller
578. A technician is setting up VoIP phones on a wireless network. Users report that calls are choppy and sometimes dropped. The technician has measured two characteristics using simple command-line tools that verify the problem. Which of the following characteristics did the technician measure? (Choose two.)
A. Reflection
B. Latency
C. Interference
D. Packet loss
E. Signal-to-noise ratio
F. Attenuation
579. Which of the following ports should a network technician open on a firewall to back up the configuration and operating system files of a router to a remote server using the FASTEST method possible?
A. UDP port 22
B. TCP port 22
C. TCP port 25
D. UDP port 53
E. UDP port 69
580. A technician is replacing a failed SOHO router for a customer who has an existing switch, cable modem, and static IP address. The user has a web server that faces the Internet so users can visit and leave comments. Which of the following BEST describes the correct configuration for this customer’s requirements?
A. The modem is placed in bridge mode, the router is placed behind the modem, and the web server is placed behind the router.
B. The router is placed in bridge mode, the modem is placed behind the router, and the web server is placed behind the modem.
C. The web server is placed in bridge mode, the router is placed behind the web server, and the modem is placed behind the router.
D. The switch is placed in bridge mode, the modem is placed behind the router, and the router is placed behind the modem.
581. A network technician is attempting to troubleshoot a connectivity issue. The issue is only reported during the evening hours, and only a single workstation loses connectivity. Which of the following is the MOST likely cause of the issue?
A. The router has a time-based ACL, applied for the network segment.
B. A light source is creating EMI interference, affecting the UTP cabling.
C. Nightly backups are consuming excessive bandwidth.
D. The user has violated the AUP, and Internet access has been restricted.
582. A network administrator is redesigning network security after an attack. During the attack, an attacker used open cubicle locations to attach devices to the network. The administrator wants to be able to monitor future attacks in a safe environment and determine the method of attack. Which of the following should the administrator do to BEST meet this requirement?
A. Create a VLAN for the unused ports and create a honeyspot on the VLAN.
B. Install a BPDU guard on switchports and enable STP.
C. Create a DMZ for public servers and secure a segment for the internal network.
D. Install antivirus software and set an ACL on the servers.
583. A company has just refreshed the hardware in its datacenter with new 10G Ethernet switches. A technician wishes to set up a new storage area network but must use existing infrastructure. Which of the following storage standards should the technician use?
A. iSCSI
B. Fibre Channel
C. NAS
D. InfiniBand
584. A network technician needs to install a new access switch. After installing the new switch, the technician begins to move connections from the old switch to the new switch. The old switch used a GBIC with SC connectors, and the new switch uses an SFP with LC connectors. After connecting the SC connector to the SC-to-LC adapter and plugging it into the switch, the link does not come up as expected. Which of the following should a network technician perform NEXT?
A. Replace SFP with a new one.
B. Fall back to the old switch.
C. Transpose the fiber pairs.
D. Replace multimode with single-mode cable.
585. A network technician is installing a new SOHO branch office that requires the use of a DOCSIScompatible modem. The modem needs to be connected to the ISP’s network at the demarc. Which of the following cable types should be used?
A. UTP
B. Multimode
C. Coaxial
D. Serial
586. A technician needs to order cable that meets 10GBaseT and fire safety requirements for an installation between a drop ceiling and a standard ceiling. Which of the following should the technician order to ensure compliance with the requirements?
A. PVC Cat 5
B. Plenum Cat 5e
C. Plenum Cat 6a
D. PVC Cat 7
587. Which of the following physical security devices is used to detect unauthorized server room access?
A. Access badge
B. Biometrics
C. Smart card
D. Video surveillance
588. A network technician recently installed a new server on a network. The technician must ensure the server does not have any unnecessary services running. The IP address of the server is 204.211.38.50. Which of the following commands would allow the technician to make this determination?
A. nmap
B. pathping
C. route
D. nslookup
589. Joe, an employee at a large regional bank, wants to receive company email on his personal smartphone and tablet. To authenticate on the mail server, he must first install a custom security application on those mobile devices. Which of the following policies would BEST enforce this requirement?
A. Incident response policy
B. BYOD policy
C. DLP policy
D. Remote access policy
590. A technician is allocating the IP address space needed for a new remote office. This office will contain the engineering staff with six employees and the digital marketing staff with 55 employees. The technician has decided to allocate the 192.168.1.0/24 block to the remote office. The engineering staff has been allocated the 192.168.1.64/29 subnet. Using the LEAST amount of space possible, which of the following would be the last usable IP address in the engineering subnet?
A. 192.168.1.62
B. 192.168.1.63
C. 192.168.1.70
D. 192.168.1.71
591. An administrator is troubleshooting a user’s intermittent wireless connectivity issue. Other users across the hallway can connect and use the wireless network properly. Upon inspection of the connection details, the administrator finds the following:
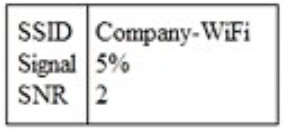
Which of the following is MOST likely the cause of the poor wireless connection?
A. Channel overlap
B. Overcapacity
C. Incorrect antenna type
D. Latency
592. A VoIP system will require 23 concurrent voice channels and one signaling channel. Which of the following types of WAN service would provide the BEST connectivity to the PSTN?
A. PRI
B. BRI
C. E1/E3
D. DSL
593. A network administrator is going to be performing a major upgrade to the network. Which of the following should the administrator use in case of a failure?
A. Baseline report
B. Vulnerability report
C. Rollback plan
D. Business continuity plan
594. A web application is unable to authenticate customers so they can access their bills. The server administrator has tested the LDAP query but is not receiving results. Which of the following is the NEXT step the server administrator should take to correct the problem?
A. Check port 636 to see if it is being blocked.
B. Change service port 636 to port 389.
C. Restart the web server.
D. Verify the browser is using port 443.
595. Which of the following is networking stand-alone hardware that will permit any WiFi-compliant device to connect to a wired network?
A. Wireless hub
B. Wireless firewall
C. Wireless access point
D. Wireless bridge
596. Which of the following devices are MOST often responsible for 802.1q tagging? (Choose two.)
A. Switch
B. Router
C. IDS
D. Hub
E. IPS
F. Network tap
597. A network technician is installing a new wireless network in a small office. Due to environmental concerns, the customer wants the network to run exclusively on the 5GHz frequency. Which of the following wireless technologies should the technician install to BEST meet this requirement? (Choose two.)
A. 802.11ac
B. 802.11b
C. 802.11g
D. 802.11n
E. Bluetooth
F. Z-Wave
598. Which of the following concepts would BEST describe when a company chooses to use a thirdparty vendor to host and administer a critical application?
A. SaaS
B. IaaS
C. PaaS
D. CASB
599. A content filter is set to analyze XML and JSON that users access from the Internet. At which of the following layers is this analysis taking place?
A. 1
B. 3
C. 5
D. 7
E. 6
600. Ann, a new employee within a department, cannot print to any of the printers in the department or access any of the resources that others can. However, she can access the Internet. The network engineer has confirmed that Ann’s account has been set up the same as the others. There are no access lists restricting Ann’s access. Which of the following could be the issue for this lack of access?
A. Duplex/speed mismatch
B. VLAN mismatch
C. DNS server issue
D. DHCP server issue
E. Spanning tree blocked ports
601. A technician is configuring a printer for a client. The technician connects the printer to the network, but is unsure how to determine its switchport. Which of the following should the technician do FIRST to locate the switchport?
A. Perform a DNS lookup on the server.
B. Set up an SSH session to the desktop.
C. Reference the ARP table in the router.
D. Configure port security on the switch.
602. A router is set up to utilize RIPv2 to route traffic throughout the network. Which of the following routing metrics is used to determine the path?
A. Distance
B. Bandwidth
C. Speed
D. Hop count
603. A second router was installed on a network to be used as a backup for the primary router that works as a gateway. The infrastructure team does not want to change the IP address of the gateway on the devices. Which of the following network components should be used in this scenario?
A. Loopback IP
B. Virtual IP
C. Reserved IP
D. Public IP
604. Which of the following can be done to implement network device hardening? (Choose two.)
A. Implement spanning tree
B. Perform VLAN hopping
C. Patch and update
D. Perform backups
E. Enable port mirroring
F. Change default admin password
605. A critical vulnerability is discovered on a network device. The vendor states it has already patched this vulnerability in its current release. Which of the following actions should an administrator take?
A. Change the default password
B. Use a firewall in front of the device.
C. Update the firmware.
D. Upgrade the configuration.
606. A technician has been alerted of incoming HTTP traffic on the LAN segment that should not contain any web servers. The technician has the IP address of the destination host and wants to determine if the socket for HTTP is open. Which of the following should the technician perform?
A. Baseline assessment
B. Packet analysis
C. Port scan
D. Patch-level assessment
607. Which of the following creates a secure remote connection at the OSI network layer?
A. L2TP
B. SSL
C. DTLS
D. IPSec
608. A network technician has salvaged several Ethernet cables from a datacenter. The technician attempts to use the cables to connect desktops to the network without success. Which of the following is MOST likely the issue?
A. The cables have an incorrect pin-out.
B. The cables are UTP instead of STP.
C. The cables are Cat 6 instead of Cat 5.
D. The cables are not plenum rated.
609. A company decides to deploy customer-facing, touch-screen kiosks. The kiosks appear to have several open source service ports that could potentially become compromised. Which of the following is the MOST effective way to protect the kiosks?
A. Install an IDS to monitor all traffic to and from the kiosks.
B. Install honeypots on the network to detect and analyze potential kiosk attacks before they occur.
C. Enable switchport security on the ports to which the kiosks are connected to prevent networklevel attacks.
D. Create a new network segment with ACLs, limiting kiosks’ traffic with the internal network.
610. While working on a Linux-based OS, a technician experiences an issue accessing some servers and some sites by name. Which of the following command-line tools should the technician use to assist in troubleshooting?
A. dig
B. iptables
C. ifconfig
D. traceroute
611. A network administrator has had difficulty keeping track of IP address assignments on networking devices and clients recently. Which of the following is the BEST technology to aid in this scenario?
A. DNS
B. DHCP
C. IPAM
D. NTP
612. A technician is surveying a college’s network equipment rooms and connectivity. Which of the following types of documentation does the technician need to perform a detailed site survey? (Choose three.)
A. IDF/MDF documentation.
B. Cable run label documentation.
C. Network configuration documentation.
D. Performance baseline documentation.
E. Standard operating procedure documentation.
F. Change management documentation.
G. Rack diagram documentation.
613. A technician is connecting a PC to a switchport. At the wiring closet, the technician is unable to identify which cable goes from patch panel A connected to the switch to patch panel B connected to the PC. Which of the following tools should the technician use to resolve the issue?
A. Cable tester
B. Multimeter
C. Tone generator
D. OTDR
614. A technician wants to deploy a network that will require wireless client devices to prompt for a username and password before granting access to the wireless network. Which of the following must be configured to implement this solution?
A. EAP-PEAP
B. CCMP-AES
C. WPA2-PSK
D. TKIP-RC4
615. Which of the following protocols are classified as connectionless? (Choose two.)
A. TFTP
B. FTP
C. HTTP
D. SNMP
E. SSH
F. IMAP
616. Users in a school lab are reporting slow connections to the servers and the Internet. Other users in the school have no issues. The lab has 25 computers and is connected with a single 1Gb Ethernet connection on Cat 5e wiring to an unmanaged switch. There are also three spare Cat 5e cable runs, which are not in use. The school wants to double the connection speed between the lab and the servers without running new cables. Which of the following would be the BEST solution?
A. Plug in a second spare cable at each end to double the speed.
B. Replace the switches with ones that utilize port bonding and use the spare cables.
C. Replace the switches with 10Gb switches and utilize the existing cabling.
D. Plug in a second cable and set one port to TX and one port to RX.
617. A junior technician is setting up a voice control device so the Chief Executive Officer (CEO) will be able to control various things in the office. Of which of the following types of IoT technologies is this an example?
A. LAN
B. WAN
C. SAN
D. PAN
618. Users on a LAN segment are reporting a loss of connectivity to network services. The client PCs have been assigned with 169.254.X.X IP addresses. Which of the following IP address schemas is being utilized?
A. Private IP
B. Static IP
C. APIPA
D. Loopback
619. A network administrator has created a new VLAN for the server and clients within the accounting department and wants to outline how it integrates with the existing network. Which of the following should the administrator create?
A. Logical diagram
B. Physical diagram
C. Rack diagram
D. Configuration diagram
620. Which of the following would indicate that a circuit speed should be increased?
A. Low latency
B. Low bandwidth consumption
C. High number of SIEM alerts
D. High packet drops
621. A technician has installed an older IP camera as a temporary replacement for a recently failed newer one. The technician notices that when the camera’s video stream is off, the ping roundtrip time between the camera and the network DVR is consistently less than 1ms without dropped packets. When the camera video stream is turned on, the ping roundtrip time increases dramatically, and network communication is slow and inconsistent. Which of the following is MOST likely the issue in this scenario?
A. VLAN mismatch
B. Duplex mismatch
C. Cat 6 RX/TX reversed
D. Damaged cable
622. Wireless users have been experiencing connectivity problems. Investigation shows neighboring wireless appliances, which are not connected to the network, have been on the same 5GHz frequency to communicate. Which of the following wireless performance problem concepts defines this issue?
A. Interference
B. Distance limitation
C. Signal-to-noise ratio
D. Absorption
623. Which of the following BEST explains the purpose of signature management as a mitigation technique?
A. Hardening devices
B. Segmenting the network
C. Detecting malicious activity
D. Restricting user credentials
624. A network technician installs a web server on the firewall. Which of the following methods should the technician implement to allow access to outside users without giving access to the inside network?
A. VLAN
B. DMZ
C. SNMP
D. NTP
625. A Chief Information Officer (CIO) tasks the network engineer with protecting the network from outside attacks. Placing which of the following devices on the network perimeter would provide the MOST security for the system?
A. Firewall
B. NGFW
C. Content filter
D. IDS/IPS
626. Management has requested that a wireless solution be installed at a new office. Which of the following is the FIRST thing the network technician should do?
A. Order equipment
B. Create network diagrams
C. Perform a site survey
D. Create an SSID.
627. A technician has deployed an additional DHCP server for redundancy. Clients in certain subnets are not receiving DHCP leases from the new DHCP server. Which of the following is the MOST likely cause?
A. The new DHCP server’s IP address was not added to the router’s IP helper list.
B. The new DHCP server is not receiving the requests from the clients.
C. The ARP cache of the new DHCP server needs to be updated.
D. The ARP table on the router needs to be cleared.
628. Greater bandwidth and availability are required between two switches. Each switch has multiple 100Mb Ethernet ports available. Which of the following should a technician implement to help achieve these requirements?
A. Spanning tree
B. Clustering
C. Power management
D. Port aggregation
629. A technician is configuring a new server with an IP address of 10.35.113.47 on the 10.35.112.0 subnet to allow for the maximum number of hosts. When configuring network settings, which of the following is the correct subnet mask?
A. 10.35.112.0/30
B. 10.35.112.0/24
C. 255.255.240.0
D. 255.255.248.0
E. 255.255.255.0
630. Ann, a customer, recently upgraded her SOHO Internet to gigabit fiber from cable. She was previously getting speeds around 75Mbps down and 25Mbps up. After the upgrade, Ann runs a speed test on her desktop and gets results of 1000Mbps down and 100Mbps up. A technician connects directly to the router and sees the correct 1000Mbps speeds. Which of the following is MOST likely the cause? (Select two).
A. All ports should be configured for full duplex.
B. There is a 10/100 switch on the network.
C. The connections are using Cat 5 cable.
D. The connections are using Cat 6 cable.
E. There is a transceiver mismatch at the fiber termination point.
F. Signal attenuation on the new fiber has reached the upper limits.
631. A user reports intermittent performance issues on a segment of the network. According to the troubleshooting methodology, which of the following steps should the technician do NEXT after collecting initial information from the customer?
A. Document findings, actions, and outcomes.
B. Establish a theory of probable cause.
C. Establish a plan of action to resolve the problem.
D. Duplicate the problem, if possible.
632. Which of the following protocols is associated with a three-way handshake?
A. UDP
B. ICMP
C. GRE
D. TCP
633. Which of the following would a company place at the edge of its network if it wants to view and control which Internet applications are being used?
A. VPN concentrator
B. NGFW
C. IDS/IPS
D. Proxy server
634. A technician wants to physically connect two office buildings’ networks. The office buildings are located 600ft (183m) apart. Which of the following cable types is the BEST choice?
A. Cat 5e
B. Cat 6a
C. Multimode
D. Coaxial
636. A network engineer at a multinational company is asked to purchase mobile phones for senior executives who often travel internationally. The executives want their phones to work with wireless carriers in multiple countries when they travel. Which of the following cellular standards should these new phones support?
A. GSM
B. TDM
C. CDMA
D. PSTN
637. Which of the following should a network administrator use to configure Layer 3 routes? (Select TWO).
A. Multilayer switch
B. Firewall
C. Hub
D. Bridge
E. Modem
F. Media converter
638. While logged into a financial application, a user gets errors when trying to write to the database. The network administrator is not familiar with the application and how it communicates with the database. Which of the following documentation types should the network administrator use to troubleshoot the data flow?
A. Logical diagram
B. Physical diagram
C. Network baseline
D. Change management log
639. Joe, a network engineer, is attempting to install wireless in a large work area. He installs the access point in the middle of the work space. When testing, he notices a -60dB reading on one side of the room and a – 92dB reading on the other side. Which of the following is MOST likely the issue?
A. External interference
B. Distance limitations
C. Channel overlap
D. Incorrect antenna type
640. A network technician wants to address PCs on a subnet with IPv6 in addition to IPv4. The subnet currently uses a DHCP server that only supports IPv4. Which of the following should the technician use to assign IPv6 addresses automatically without DHCP?
A. APIPA
B. MAC reservations
C. EUI-64
D. IPv4 to IPv6 tunnel
641. A technician is establishing connectivity through a VPN for remote server access. Which of the following protocols should be utilized to configure this VPN connection securely?
A. IPSec
B. IGRP
C. L2TP
D. PPTP
642. A network technician receives a request for a disaster recovery solution. Management has requested no downtime in the event of a disaster. Which of the following recovery solutions is the appropriate choice?
A. Hot site
B. Business continuity
C. File backups
D. Virtual snapshot
643. A network technician receives a new firmware update for a network device. The technician wants to ensure the file has not been tampered with. Which of the following techniques should the technician use to ensure the integrity of the file?
A. Cyclic redundancy check
B. System integrity check
C. Hash comparison
D. Root guard
644. An AP is configured to authenticate clients by using their Active Directory username and password. The AP uses UDP to connect to the authentication service, which then queries Active Directory. Which of the following authentication services is being used by the AP in this scenario?
A. RADIUS
B. TACACS+
C. LDAP
D. Kerberos
645. Which of the following should be configured on the network to achieve performance for the FCoE storage traffic?
A. PoE
B. DHCP snooping
C. Jumbo frames
D. Virtual IP
646. A network administrator wants to narrow the scope of a subnet to two usable IP addresses within a class C network. Which of the following is the correct CIDR notation?
A. 10.10.50.0/30
B. 172.16.20.0/30
C. 192.1.0.124/30
D. 192.168.0.192/24
E. 192.170.10.0/24
647. A network technician notices that most of the nodes in the 10.10.74.0/23 address space return either 1 or 2 node hop after running a tracert, however, some of the new servers are showing a hop count larger than 10. Which of the following is the MOST likely reason for this?
A. New servers are being provisioned in the cloud.
B. Those servers have host-based firewalls.
C. Some of the servers are configured to use different gateways.
D. Part of the subnet is configured to use different VLANs.
648. A technician has a remote site that often has congestion issues. When this happens, the remote router cannot be managed using SSH because the session drops. Which of the following is a possible solution to the issue?
A. Out-of-band management
B. HTTPS management URL
C. Client-to-site VPN
D. Router ACL
649. A technician has installed multiple new PC clients and is connecting them to the network. Only one client is receiving IP addressing information. Which of the following should the technician verify as the NEXT troubleshooting step?
A. DHCP scrope
B. DHCP lease
C. Default gateway
D. DNS zone
650. Which of the following WAN technologies swaps the header on a packet when internally switching from one provider router to another?
A. ATM
B. Frame relay
C. MPLS
D. PPP
651. A network administrator is purchasing a mobile phone for a manager who is traveling internationally. The phone needs to be able to make and receive calls in multiple countries outside of North America. Which of the following cellular technologies should the administrator look for in the phone?
A. CDMA
B. GSM
C. TDMA
D. CSMA
652. A network administrator is downloading a large patch that will be uploaded to several enterprise switches simultaneously during the day’s upgrade cycle. Which of the following should the administrator do to help ensure the upgrade process will be less likely to cause problems with the switches?
A. Confirm the patch’s MD5 hash prior to the upgrade.
B. Schedule the switches to reboot after an appropriate amount of time.
C. Download each switch’s current configuration before the upgrade.
D. Utilize FTP rather than TFTP to upload the patch.
653. A network technician is segmenting network traffic into various broadcast domains. Which of the following should the network technician utilize?
A. VLAN
B. STP
C. ACL
D. BPDU
654. After rebooting a PC, a user is no longer able to connect to the corporate network. As a test, the technician plugs a different laptop into the same network jack and receives an IP address of 169.254.112.137. Which of the following is MOST likely causing the issue?
A. DHCP scope exhaustion
B. Improper DNS setting
C. Incorrect ACL setting
D. Port-security violation
655. A network administrator is concerned about clients being able to access the local Internet while connected to the corporate VPN. Which of the following should be disabled on the client to prevent this?
A. TLS
B. Remote file access
C. Split tunneling
D. HTTPS
656. A network technician travels to a remote office to set up a new SOHO for the company. Wireless networking should be used at the remote office. The network technician sets up all the related wireless network equipment, and the last step is to connect the users’ devices to the company network. To complete this step, which of the following should be used to secure the remote network location?
A. Host-based firewalls
B. WPA2/WPA
C. Open access
D. Port filtering
657. The length of an IPv6 address is:
A. 32 bits
B. 64 bits
C. 128 bits
D. 256 bits
658. A network technician is troubleshooting a problem with a user’s client-to-site VPN connection. The user is unable to establish a connection to the server, but the error message that appears on screen does not contain useful information. Which of the following should the technician do NEXT to troubleshoot the issue?
A. Reconfigure the user’s VPN connection in the router to fix profile corruption.
B. Inform the user that provisioning sometimes fails and the connection needs to be attempted again.
C. Review the logs in the VPN client to check for any informational messages.
D. Verify the system has the latest OS patches installed.
659. Management requires remote access to network devices when the ISP is down. Which of the following devices would provide the BEST solution?
A. Router
B. Firewall
C. Bridge
D. Modem
660. A network technician installed a new host on the network. The host is not connecting to the company’s cloud servers. The technician attemtps to ping a server using the AP address with no success. Checking the IP address using ipconfing displays:
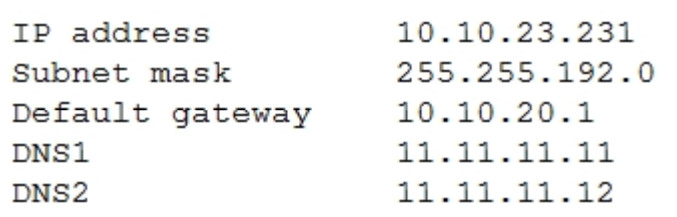
Which of the following should the technician perform NEXT to determine where the issue is located?
A. Modify the default gateway address and ping the server to test connectivity.
B. Change the DNS servers to be on the same subnet as the host.
C. Modify the router’s ACL to allow port 80 to exit the network.
D. Perform a tracert command to locate where the packet is dropped.
661. A network technician is performing a firmware upgrade on a switch. The firmware needs to be downloaded to the device. Which of the following methods should the technician use to retrieve the updated firmware?
A. RDP
B. SSH
C. TFTP
D. Telnet
662. A network technician is assisting a user who is experiencing connectivity problems with the VPN. The technician has confirmed the VPN is functioning and other users at the site cannot access the Internet. Which of the following commands would MOST likely be used to further troubleshoot?
A. tracert
B. netstat
C. arp
D. dig
663. Which of the following MUST be installed on an employee’s computer if the remote access VPN implements an SSL VPN with PKI authentication?
A. Shared secret
B. HTTPS server
C. Soft spoken
D. Private certificate
664. Which of the following default ports should be opened on a firewall to allow for SSH and Telnet (Select TWO)
A. 21
B. 22
C. 23
D. 25
E. 123
F. 443
665. Two computers are connected to a multilayer switch, and both can access the corporate file server. The computers cannot talk to one another. Which of the following is MOST likley the cause?
A. Duplex/speed mismatch
B. ACL misconfiguration
C. Bad port
D. Crosstalk
666. A user calls the help desk for assistance with setting up a new SOHO router. The user has three employees who all have laptops that need to connect to the wireless network. The users need to have firewall rules allowing access to an internal server, but cannot be configured with static IP addresses. Which of the following BEST describes what the technician should implement?
A. CNAME record in the users’ dynamic DNS accounts
B. Additional lease time for the laptop computers
C. IP helper relay system for configuration hops
D. DHCP reservation for the laptops’ MACs
667. A home user is unable to get to the Internet from a workstation that is connected to a wireless network. When reviewing the results of the ipconfig command, the user wants to verity the default gateway is correct. Which of the following devices should be the gateway?
A. Cable modem
B. SOHO router
C. DNS server
D. Layer 2 switch
668. A technician is troubleshooting intermittent connectivity on a line-of-sight wireless bridge. Which of the following tools should the technician use to determine the cause of the packet loss?
A. Spectrum analyzer
B. OTDR
C. Packet sniffer
D. Multimeter
669. Which of the following should be configured to allow for IP-to-name resolutions?
A. CNAME
B. A
C. PTR
D. NS
670. When configuring a new switch in a packet-switched network, which of the following helps protect against network loops?
A. Spanning tree
B. Flood guard
C. BPDU guard
D. DHCP snooping
671. A company has just installed a new cloud VoIP solution, however, users occasionally report poor call quality or dead air being present. Which of the following describes the NEXT troubleshooting step the technician should take?
A. The technician should check the internal diagnostics on all the phones to look for a common thread.
B. The technician should reset all the phones and deprovision information from the provider
C. The technician should use a packet tracer to see if the traffic is getting out of the network
D. The technician should run ping tests on the Internet line to monitor for packet loss and latency
672. A network technician needs to configure a device with an embedded OS so it can be connected to a wireless handheld scanner. Which of the following technologies should be configured on the OS to create the wireless connection?
A. Partial mesh
B. Ad hoc
C. Ring
D. Bus
673. An NGFW alerts that a web server in the DMZ is sending suspicious traffic. A network administrator finds that port 25 is open, and the traffic is originating from this port. The only purpose of this server is to deliver website traffic. Which of the following should the network administrator recommend to the systems administrator?
A. Disable Telnet service on the server.
B. Disable DHCP service on the server.
C. Disable the SMTP service on the server
D. Disable FTP service on the server.
674. Joe, a network technician, wants to locally back up several router and switch configurations. He wants to store them on a server that can be accessed easily for recovery without authentication. Which of the following servers should Joe use?
A. Telnet
B. LDAP
C. TFTP
D. Samba
675. According to the troubleshooting methodology, which of the following steps will help a technician gather information about a network problem? (Select TWO).
A. Test solutions.
B. Duplicate the problem
C. Establish a theory of probable cause
D. users
E. Implement preventive measures.
F. Document findings
676. A user reports network resources can no longer be accessed. The PC reports a link but will only accept static IP addresses. The technician pings other devices on the subnet, but the PC displays the message . Which of the following are MOST likley the causes of this issue? (Select Destination unreachable TWO).
A. Damaged cables
B. Crosstalk
C. Bent pins
D. TX/RX reverse
E. VLAN mismatch
F. Duplex mismatch
677. While testing an ACL on the default gateway router to allow only web browsing, ports TCP 80 and TCP 443 were the only ports open. When tested, no websites were accessible via their URLs inside the network. Which of the following configurations should be added to the ACL?
A. permit tcp any any eq 20
B. permit udp any any eq 25
C. permit udp any any eq 53
D. permit udp any any eq 68
E. permit tcp any any eq 110
F. permit tcp any any eq 8080
678. Users have been experiencing connection timeout issues when using a web-based program. The network technician determines the problem happened due to a TTL setting that was set too low on the firewall. Which of the following BEST enabled the network technician to reach this conclusion?
A. Reviewing application logs
B. Reviewing a baseline report
C. Reviewing a vulnerability scan
D. Reviewing SLA requirements
679. A network technician is installing a new wireless network for a client. The client has experienced issues with other building tenants connecting to the wireless network and utilizing the bandwidth. The client wants to prevent this from happening by using certificate-based authentication. Which of the following technologies should the network administrator implement?
A. WPA-PSK
B. EAP-TLS
C. AES-CCMP
D. WEP-TKIP
680. A network administrator is installing a campus network of two routers, 24 switches, 76 APs, and 492 VoIP phone sets. Which of the following additional devices should the administrator install to help manage this network?
A. VoIP PBX
B. Content filter
C. RADIUS server
D. Wireless controller
681. A technician arrives at a new building to find cabling has been run and terminated, but only the wall ports have been labeled. Which of the following tools should be utilized to BEST facilitate labeling the patch panel?
A. Tone generator
B. Cable tester
C. Multimeter
D. Loopback adapter
682. Which of the following policies prohibits a network administrator from using spare servers in the datacenter to mine bitcoins?
A. NDA
B. BYOD
C. AUP
D. MOU
683. Which of the following technologies is used when multiple Ethernet adapters work to increase speed and fault tolerance?
A. Clustering
B. Load balancing
C. Redundant circuits
D. NIC teaming
684. A network technician has finished configuring a new DHCP for a network. To ensure proper functionality, which of the following ports should be allowed on the server’s local firewall? (Select TWO).
A. 20
B. 21
C. 53
D. 67
E. 68
F. 389
685. A network technician is reviewing switch ACLs to determine if they are causing communication issues with one PC. The PC’s IP address is 192.168.12.66. Which of the following is the network range found in the ACL that could have affected this PC?
A. 192.168.12.97 255.255.255.192
B. 192.168.12.97 255.255.255.224
C. 192.168.12.97 255.255.255.240
D. 192.168.12.97 255.255.255.248
686. A new technician is connecting an access switch to a distribution switch uplink in a datacenter using fiber cables. Which of the following are transceivers the technician should use to perform this job? (Select TWO).
A. RJ45
B. DB-9
C. LC
D. SFTP
E. GBIC
F. SC
687. Which of the following physical security devices is used to prevent unauthorized access into a datacenter?
A. Motion detector
B. Video camera
C. Asset tracking
D. Smart card reader
688. A technician is installing two new servers that collect logs. After installing the servers, the technician reviews the logical output from various commands. Which of the following should be included in a logical network diagram?
A. Rack location
B. Room number
C. Media type
D. Hostname
689. A few weeks after starting a new position, Joe, a junior network administrator, receives a call from an internal number asking for his username and password to update some records. Joe realizes this may be a type of attack on the network, since he has full access to network resources. Which of the following attacks is described?
A. Logic bomb
B. Social engineering
C. Trojan horse
D. Insider threat
690. A technician is sent to troubleshoot a faulty network connection. The technician tests the cable, and data passes through successfully. No changes were made in the environment, however, when a network device is connected to the switch using the cable, the switchport will not light up. Which of the following should the technician attempt NEXT?
A. Modify the speed and duplex
B. Plug in to another port
C. Replace the NIC
D. Change the switch
691. A technician has been assigned to capture packets on a specific switchport. Which of the following switch feature MUST be used to accomplish this?
A. Spanning tree
B. Trunking
C. Port aggregation
D. Port mirroring
692. Which of the following operate only within the UDP protocol?
A. Frames
B. Datagrams
C. Segments
D. Packets
693. An employee reports an error when visiting a website using SSL, and a message is displayed warning of an invalid certificate. Which of the following could be occurring?
A. Phishing
B. DDoS
C. Evil twin
D. MITM
E. OCSP stapling
694. A network technician is troubleshooting a connectivity issue and determines the cause is related to the VLAN assignment on one of the access switches in the network. After resolving the issue, the network technician decides to update the documentation to refer to the correct VLAN. Which of the following should the technician update?
A. Physical diagram
B. Logical diagram
C. IDF documentation
D. Change management documentation
E. Incident ronse plan
695. A university has a lecture hall containing 100 students. Currently, the lecture hall has two 802.11ac wireless access points, which can accommodate up to 50 devices each. Several students report they are unable to connect devices to the wireless network. Which of the following is MOST likely the issue?
A. One of the wireless access points is on the wrong frequency
B. The students are attempting to connect 802.11g devices
C. The students are using more than one wireless device port seat.
D. Distance limitations are preventing the students from connecting.
696. A WAP has been dropping off the network sporadically and reconnecting shortly thereafter. The Cat5 wire connecting the access point is a long run of 265ft (81m) and goes through the business area and the mechanical room. Which of the following should the technician do to fix the AP connectivity issue?
A. Install a repeater to boost the signal to its destination
B. Replace the UTP cable with plenum cable.
C. Upgrade the cable from Cat 5 to Cat 5e.
D. Set the AP to half duplex to compensate for signal loss.
697. A technician wants to configure a SOHO network to use a specific public DNS server. Which of the following network components should the technician configure to point all clients on a network to a new DNS server?
A. Router
B. Switch
C. Load balancer
D. Proxy server
698. A company wishes to allow employees with company-owned mobile devices to connect automatically to the corporate wireless network upon entering the facility. Which of the following would BEST accomplish this objective?
A. Open wireless
B. Geofencing
C. Pre-shared key
D. MAC filtering
699. A network engineer for a manufacturing company is implementing a wireless network that provides reliable coverage throughout the facility. There are several large, electric, motorized machines installed on the shop floor for automating the manufacturing process. These machines are known to be significant sources of RF interference. Which of the following frequencies should the wireless network use to MINIMIZE this interference?
A. 2.4 GHz
B. 56MHz
C. 5GHz
D. 900MHz
700. A company has procured a new office building and started the process of assigning employees to work at that location. The company has also purchased equipment for the new location. There are 5033 laptops, 6000 monitors, and 857 printers. Which of the following steps is the technician most likely to complete FIRST?
A. Create a rack diagram
B. Create a network baseline
C. Create an inventory database
D. Create a port location diagram
701. Which of the following is created on a 48-port switch with five active VLANs?
A. 48 networks, five segments
B. 48 collision domains, five broadcast domains
C. 240 private networks
D. 240 usable IP addresses
702. A corporate manager says wireless phones do not work properly inside the main building. After a troubleshooting process, the network administrator detects that the voice packets are arriving on the wireless phones with different delay times. Which of the following performance issues is the company facing?
A. Jitter
B. Latency
C. Attenuation
D. Frequency mismatch
703. Which of the following technologies is used to attach multiple guest operating systems to a single physical network port?
A. Virtual switch
B. FCoE
C. VPC
D. vSAN
E. Fibre Channel
704. When speaking with a client, an employee realizes a proposed solution may contain a specific cryptographic technology that is prohibited for non-domestic use. Which of the following documents or regulations should be consulted for confirmation?
A. Incident response policy
B. International export controls
C. Data loss prevention
D. Remote access policies
E. Licensing restrictions
705. A network technician is installing a new network switch in the MDF. The technician is using fiber to connect the switch back to the core. Which of the following transceiver types should the technician use?
A. MT-RJ
B. BNC
C. GBIC
D. F-type
706. A network technician notices a router that repeatedly reboots. When contacting technical support, the technician discovers this is a known problem in which an attacker can craft packets and send them to the router through an obsolete protocol port, causing the router to reboot. Which of the following did the network technician fail to do? (Select TWO).
A. Generate new crypto keys.
B. Keep patches updated.
C. Disable unnecessary services.
D. Shut down unused interfaces.
E. Avoid using common passwords.
F. Implement file hashing.
707. A technician has replaced a customer’s desktop with a known-good model from storage. However, the replacement desktop will not connect to network resources. The technician suspects the desktop has not been kept up to date with security patches. Which of the following is MOST likely in place?
A. ACL
B. NAC
C. Traffic shaping
D. SDN
E. NTP
708. A network technician wants to gain a better understanding of network trends to determine if they are over capacity. Which of the following processes should the technician use?
A. Log review
B. Port scanning
C. Vulnerability scanning
D. Traffic analysis
709. A network technician is configuring network addresses and port numbers for a router ACL to block a peer- to-peer application. Which of the following is the HIGHEST layer of the OSI model at which this router ACL operates?
A. Transport
B. Network
C. Session
D. Application
710. An attacker has flooded the hardware tables of a switch to forward traffic to the attacker’s IP address rather than the default router. The traffic received is copied in real time, and then forwarded to the default router transparently from the end-user perspective. Which of the following attacks are occurring in this scenario? (Select TWO).
A. DNS poisoning
B. ARP poisoning
C. Man-in-the-middle
D. Ransomware
E. Evil twin
F. Reflective
711. A remote user is required to upload weekly reports to a server at the main office. Both the remote user and the server are using a Windows-based OS. Which of the following represents the BEST method for the remote user to connect to the server?
A. RDP
B. Telnet
C. SSH
D. VNC
712. At which of the following layers of the OSI model would TCP/UDP operate?
A. Layer 3
B. Layer 4
C. Layer 5
D. Layer 6
713. Drag and Drop Question
You are tasked with creating a network that will accomplish the following requirements.
Requirements:
The remote Sales Team must be able to connect to the corporate network.
Each department must have ONLY two PCs and a server.
Eqach department must be segmented from each other.
The following VLANs have been designed:
– VLAN 2 – Finance
– VLAN 12 – Sales
– VLAN 22 – Human Resources (HR)
Routing for VLAN 12 is implemented on the router. Routing for VLAN 2 and VLAN 22 is on the switch.
Instructions
Complete the network by dragging the required objects onto the diagram.
Objects can be used multiple times and not all placeholders need to be filled.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Answer:
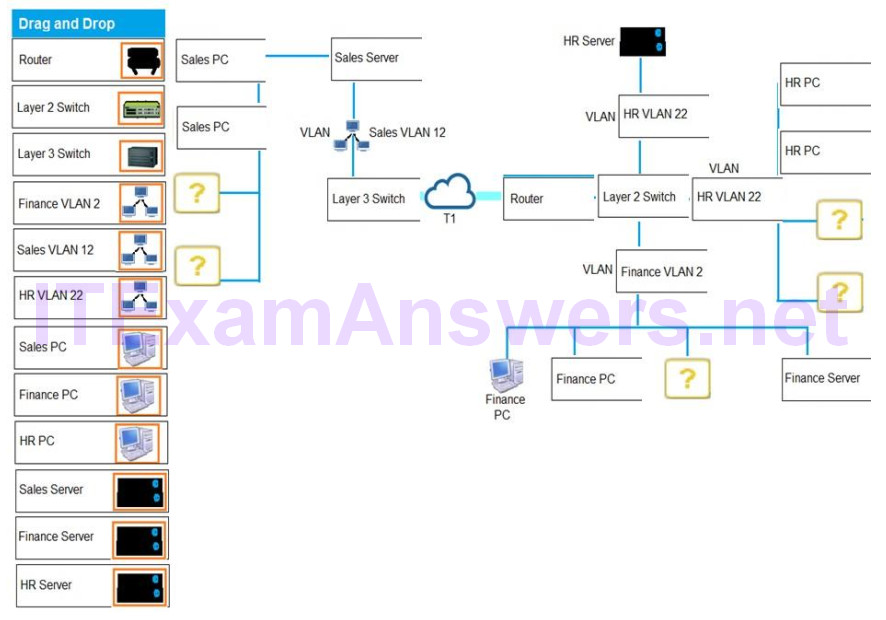

Hi Admin,
Please can you help by updating the exam questions also the vce CompTia Network+?
Please!
Hi Admin,
Can you please help with vce CompTIA Network+ update exam question that i can use with my vce player?
Any new updates on this exam?
Is it still valid?
i got these pbq 268,412 and 411 TODAY……and still have NO idea……..23/2/21