Lab 11.5.2 – Managing Device Configuration (Answers)
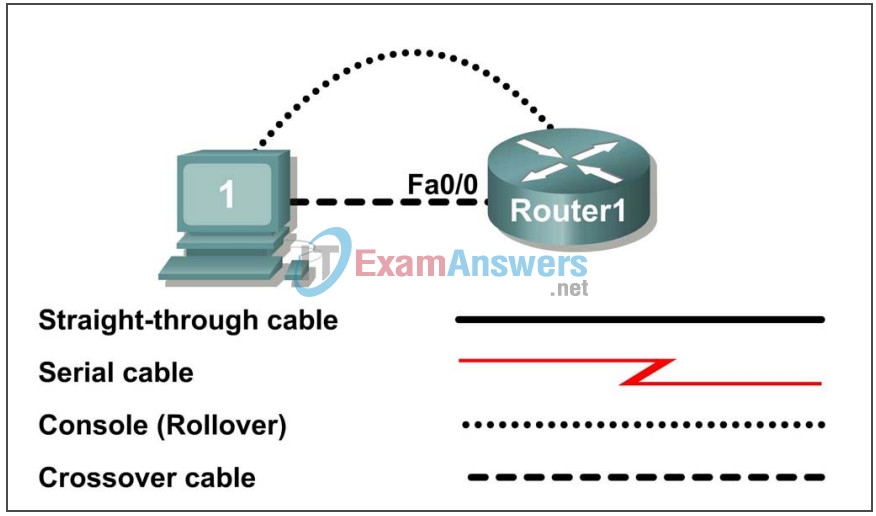
Topology Diagram
Learning Objectives
- Configure network connectivity.
- Use TFTP to save and restore a Cisco IOS configuration.
Background
Table 1. Equipment and hardware required for this lab.
| Hardware | Qty | Description |
|---|---|---|
| Cisco Router | 1 | Part of CCNA Lab bundle. |
| Computer (host) | 1 | Lab computer. |
| Console (rollover) cable | 1 | Connects computer host 1 to Router console port. |
| Crossover cable | 1 | Connects host1 NIC to Router1 Fa0/1 |
Gather the necessary equipment and cables. To configure the lab, make sure the equipment listed in Table 1 is available.
The host computer will be used as a TFTP server. This lab requires the use of SolarWinds TFTP server software. SolarWinds is a free TFTP application for Windows.
You may download a free copy of SolarWinds TFTP server software from www.solarwinds.net/downloads/Solarwinds-TFTP-Server.exe or any freeware or shareware website.
Scenario
In this lab, students will configure common settings on a Cisco Router, save the configuration to a TFTP server, then restore the configuration from a TFTP server.
Given an IP address of 10.250.250.0/24, and 6 bits used for subnets. Use the LAST subnet. Host1 should use the FIRST valid host address, and Router1 should use the LAST valid host address:
| IP Address: 10.250.250.0 | Subnet mask: 255.255.255.252 | ||
|---|---|---|---|
| Subnet | First host address | Last host address | Broadcast |
| 10.250.250.252 | 10.250.250.253 | 10.250.250.254 | 10.250.250.255 |
Note to instructor: To reinforce student cable identification, have several different types of cables available for the students. Mix crossover, straight-through, and rollover cables. Students should be able to identify the proper cable type based on a visual inspection.
Task 1: Configure Network Connectivity.
Step 1: Physically connect devices.
Refer to the Topology Diagram. Connect the console, or rollover, cable to the console port on the router and the other cable end to the host computer with a DB-9 or DB-25 adapter to the COM 1 port. Ensure power has been applied to both the host computer and router.
Step 2: Logically connect devices.
Using the IP address information from the scenario, configure the host1 computer.
Step 3: Connect host computer to router through HyperTerminal.
From the Widows taskbar, start the HyperTerminal program by clicking on Start | Programs | Accessories | Communications | Hyper Terminal.
When the HyperTerminal session window opens, press the Enter key until there is a response from the router.
Step 4: Configure Router1.
Configure Router1. Configuration tasks for Router1 include the following:
| Task- refer to Appendix 1 for help with commands |
|---|
| Specify Router name- Router1 |
| Specify an encrypted privileged exec password- cisco |
| Specify a console access password- class |
| Specify a telnet access password- class |
| Configure the MOTD banner. |
| Configure Router1 interface Fa0/0- set the description set the Layer 3 address issue no shutdown |
NOTE **DO NOT SAVE THE CONFIGURATION IN NVRAM.
Step 5: Verify connectivity.
Verify connectivity between host1 and Router1:
Router1# ping 10.250.250.253 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 10.250.250.253, timeout is 2 seconds: .!!!! Success rate is 80 percent (4/5), round-trip min/avg/max = 1/1/1 ms Router1#
Task 2: Use TFTP to Save and Restore a Cisco IOS Configuration.
Step 1: Install SolarWinds TFTP application.
Double click on the SolarWinds TFTP application to begin installation. Select Next. Agree to the license agreement, and accept default settings. After SolarWinds has finished installation, click on Finish.
Step 2: Start TFTP server.
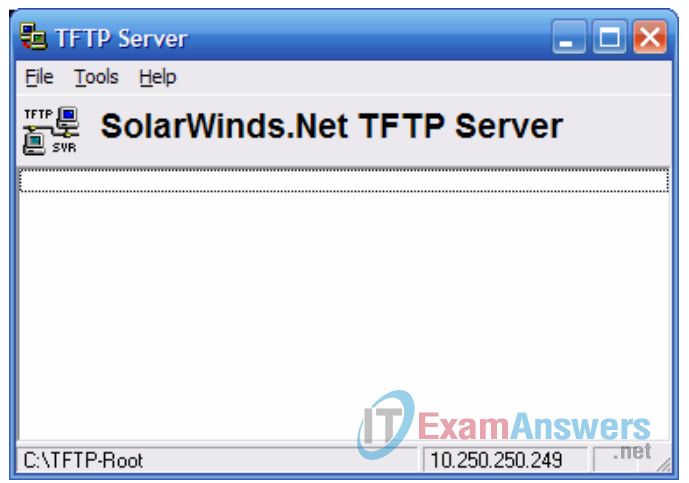
Figure 2. TFTP Server window.
Start the TFTP server by selecting Start | Programs | SolarWinds Free Tools | TFTP Server. Figure 2 shows an active TFTP Server window.
Step 3: Configure the TFTP server.
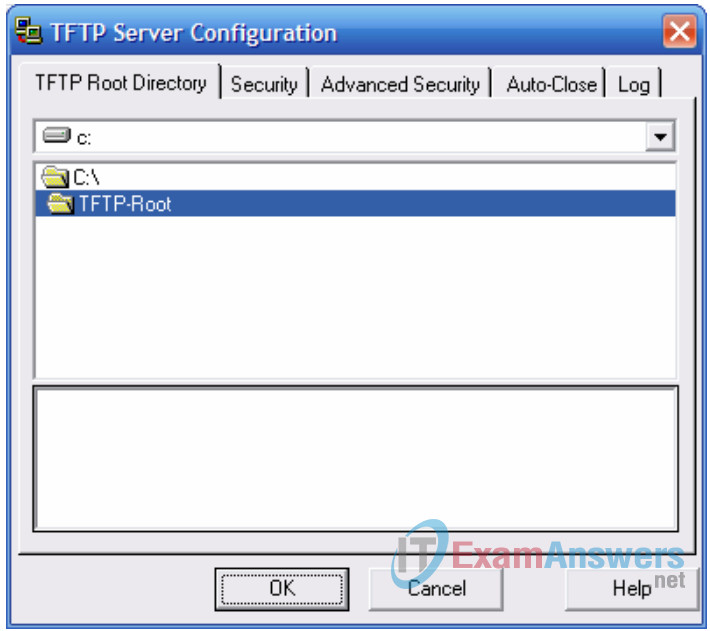
Figure 3. TFTP Server window.
To configure TFTP server, select menu option File | configure. Refer to Figure 3. Verify the following settings:
| Setting | Value |
|---|---|
| TFTP Root Directory: | TFTP-Root |
| Security | Transmit and Receive Files |
| Advanced Security | 10.250.250.254 To 10.250.250.254 |
| Auto-Close | Never |
| Log | Enable Log Requests to the Following File. Leave the default file. |
When finished, select OK.
Step 4: Save Router1 configuration to TFTP server.
From HyperTerminal, begin a TFTP upload to the TFTP server:
Router1#copy running-config tftp: Address or name of remote host []? 10.250.250.253 Destination filename [router1-confg]? <ENTER> !! 1081 bytes copied in 2.008 secs (538 bytes/sec) Router1#
Verify a successful upload transfer. Open Log file c:\Program Files\SolarWinds\Free Tools\TFTP-Server.txt. Contents should be similar to the following:
3/25/2007 12:29 :Receiving router1-confg from (10.250.250.254) 3/25/2007 12:29 :Received router1-confg from (10.250.250.254), 1081 bytes
Verify the transferred file. Use Microsoft Word or Wordpad to examine the contents of file c:\TFTP-Root\router1-confg. Contents should be similar to the following configuration:
! version 12.4 service timestamps debug datetime msec service timestamps log datetime msec no service password-encryption ! hostname Router1 ! boot-start-marker boot-end-marker ! enable secret 5 $1$D02B$AuX05n0HPT239yYRoQ0oE. ! no aaa new-model ip cef ! interface FastEthernet0/0 description connection to host1 ip address 10.250.250.254 255.255.255.252 duplex auto speed auto ! interface FastEthernet0/1 no ip address shutdown duplex auto speed auto ! interface Serial0/1/0 no ip address shutdown no fair-queue ! interface Serial0/1/1 no ip address shutdown clock rate 2000000 ! ip http server no ip http secure-server ! control-plane ! banner motd *** ABC COMPANY NETWORK DEVICE **** *** Authorized access only ***** *** Logging is enabled **** ! line con 0 password class login line aux 0 line vty 0 4 password class login ! scheduler allocate 20000 1000 End
Step 5: Restore Router1 configuration from TFTP server.
Verify that NVRAM is clear, then reboot Router1:
Router1# show startup-config startup-config is not present Router1# reload Proceed with reload? [confirm] <ENTER>
Connectivity must be established with the TFTP server. Router1 fa0/0 must be configured with an IP address, and the interface enabled:
Router> enable Router# conf t Enter configuration commands, one per line. End with CNTL/Z. Router(config)# interface fa0/0 Router(config-if)# ip address 10.250.250.254 255.255.255.252 Router(config-if)# no shutdown Router(config-if)# exit *Mar 25 16:43:03.095: %SYS-5-CONFIG_I: Configured from console by console *Mar 25 16:43:04.967: %LINEPROTO-5-UPDOWN: Line protocol on Interface FastEthernet0/0, changed state to up
Configure the hostname of the router to TEST
Router(config-if)#exit Router(config)#hostname TEST Router(config-if)#end TEST#
Verify connectivity with the ping command:
Router# ping 10.250.250.253 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 10.250.250.253, timeout is 2 seconds: .!!!! Success rate is 80 percent(4/5), round-trip min/avg/max = 1/1/1ms Router#
Download Router1 configuration file from the TFTP server:
Router# copy tftp startup-config Address or name of remote host []? 10.250.250.253 Source filename []? router1-confg Destination filename [startup-config]? <ENTER> Accessing tftp://10.250.250.253/router1-confg... Loading router1-confg from 10.250.250.253 (via FastEthernet0/0): ! [OK - 1081 bytes] 1081 bytes copied in 9.364 secs (115 bytes/sec) Router1# *Mar 25 16:55:26.375: %SYS-5-CONFIG_I: Configured from tftp://10.250.250.253/router1-confg by console Router1#
View the configuration in NVRAM to verify an accurate transfer. The configuration should be the same as what was configured in Task 1, Step 4.
Reload the router select no at the prompt that says “Configuration has been modified”.
The previous the configuration should be restored and the router’s hostname should now be Router1.
Task 3: Reflection
TFTP is a fast, efficient way to save and load Cisco IOS configuration files.
Task 4: Challenge
Similar to uploading a configuration file, the IOS can also be stored off-line for future use. To discover the IOS filename, issue the Cisco IOS command show version. The filename is highlighted, below:
Router1# show version Cisco IOS Software, 1841 Software (C1841-ADVIPSERVICESK9-M), Version 12.4(10b), RELEASE SOFTWARE (fc3) Technical Support: http://www.cisco.com/techsupport Copyright (c) 1986-2007 by Cisco Systems, Inc. Compiled Fri 19-Jan-07 15:15 by prod_rel_team ROM: System Bootstrap, Version 12.4(13r)T, RELEASE SOFTWARE (fc1) Router1 uptime is 17 minutes System returned to ROM by reload at 16:47:54 UTC Sun Mar 25 2007 System image file is "flash:c1841-advipservicesk9-mz.124-10b.bin" This product contains cryptographic features and is subject to United States and local country laws governing import, export, transfer and use. Delivery of Cisco cryptographic products does not imply third-party authority to import, export, distribute or use encryption. Importers, exporters, distributors and users are responsible for compliance with U.S. and local country laws. By using this product you agree to comply with applicable laws and regulations. If you are unable to comply with U.S. and local laws, return this product immediately. A summary of U.S. laws governing Cisco cryptographic products may be found at: http://www.cisco.com/wwl/export/crypto/tool/stqrg.html If you require further assistance please contact us by sending email to [email protected]. Cisco 1841 (revision 6.0) with 174080K/22528K bytes of memory. Processor board ID FHK110918KJ 2 Serial(sync/async) interfaces DRAM configuration is 64 bits wide with parity disabled. 191K bytes of NVRAM. 62720K bytes of ATA CompactFlash (Read/Write) Configuration register is 0x2102 Router1#
The commands to upload the IOS are similar to uploading the configuration file:
Router1# copy flash tftp Source filename []? c1841-advipservicesk9-mz.124-10b.bin Address or name of remote host []? 10.250.250.253 Destination filename [c1841-advipservicesk9-mz.124-10b.bin]? !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! !!!!!!!!!!! 22063220 bytes copied in 59.564 secs (370412 bytes/sec) Router1#
Task 5: Clean Up.
Before turning off power to the router, remove the NVRAM configuration file if it was loaded. Use the privileged exec command erase startup-config.
Remove SolarWinds TFTP server from the host computer. Select Start | Control Panel. Open Add or Remove Applications. Select SolarWinds, then Remove. Accept defaults.
Delete any configuration files saved on the host computers.
Unless directed otherwise by the instructor, restore host computer network connectivity, then turn off power to the host computers. Remove anything that was brought into the lab, and leave the room ready for the next class.
Appendix 1
| Purpose | Command |
|---|---|
| Enter the global configuration mode. | configure terminal Example: Router> enable Router# configure terminal Router(config)# |
| Specify the name for the router. | hostname name Example: Router(config)# hostname Router1 Router(config)# |
| Specify an encrypted password to prevent unauthorized access to the privileged exec mode. | enable secret password Example: Router(config)# enable secret cisco Router(config)# |
| Specify a password to prevent unauthorized access to the console. | password password login Example: Router(config)# line con 0 Router(config-line)# password class Router(config-line)# login Router(config)# |
| Specify a password to prevent unauthorized telnet access. Router vty lines: 0 4 Switch vty lines: 0 15 |
password password login Example: Router(config)# line vty 0 4 Router(config-line)# password class Router(config-line)# login Router(config-line)# |
| Configure the MOTD banner. | Banner motd % Example: Router(config)# banner motd % Router(config)# |
| Configure an interface. Router- interface is OFF by default Switch- interface is ON by default |
Example: Router(config)# interface fa0/0 Router(config-if)# description description Router(config-if)# ip address address mask Router(config-if)# no shutdown Router(config-if)# |
| Save the configuration to NVRAM. | copy running-config startup-config Example: Router# copy running-config startup-config Router# |
