Lab Objective:
The objective of this lab exercise is for you to learn and understand how to create and apply extended numbered access control lists.
Lab Purpose:
Configuring and applying extended ACLs is a fundamental skill. Extended ACLs filter based on source and destination address, as well as Layer 4 protocols TCP (Transmission Control Protocol) and UDP (User Datagram Protocol). Extended ACLs should be applied as close to the source as possible. As a Cisco engineer, as well as in the Cisco CCNA exam, you will be expected to know how to create and apply extended numbered ACLs.
Certification Level:
This lab is suitable for CCENT and CCNA certification exam preparation.
Lab Difficulty:
This lab has a difficulty rating of 8/10.
Readiness Assessment:
When you are ready for your certification exam, you should complete this lab in no more than 20 minutes.
Lab Topology:
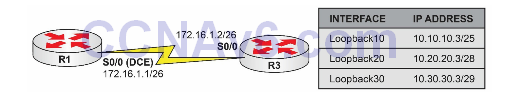
Please use the following topology to complete this lab exercise:
Task 1:
Configure the hostnames on routers R1 and R3 as illustrated in the topology.
Task 2:
Configure R1 S0/0, which is a DCE, to provide a clock rate of 768 Kbps to R3. Configure the IP addresses on the Serial interfaces of R1 and R3 as illustrated in the topology.
Task 3:
Configure a static default route on R1 pointing to R3 over the Serial connection between the two routers. Also, configure a static default route on R3 pointing to R1 via the Serial connection between the two routers. Configure the Loopback interfaces specified in the diagram on R1 and R3.
Task 4:
To test connectivity, ping R1 from R3 Serial0/0, Loopback10, Loopback20, and Loopback30 interfaces. To ping from the Loopback interfaces, use the ping <ip_address> /source <interface> command.
Task 5:
Configure both R1 and R3 to allow Telnet connections. The password CISCO should be used for Telnet access. Also, configure an enable secret of CISCO on both routers.
Task 6:
Configure a numbered extended ACL on R1 to allow Telnet from R3 Loopback10 and Loopback30 networks. Explicitly configure the extended ACL to deny Telnet from R3 Loopback20 but allow ping traffic from R3 Loopback20. When done, apply this ACL inbound on R1 Serial0/0 interface.
Telnet to R1 from R3 Loopback10, Loopback20, and Loopback30 interfaces using the telnet <ip_address> /source-interface <name> command. If your ACL has been configured correctly, Telnet should be allowed from Loopback10 and Loopback30 only.
Ping R1 from Loopback10, Loopback 20, and Loopback30 interfaces using the ping <ip_address> /source <interface> command. If your ACL has been configured correctly, ping should only work when you ping from R3 Loopback20.
Configuration and Verification
Task 1:
For reference information on configuring hostnames, please refer to earlier labs.
Task 2:
For reference information on configuring clock rates and IP addresses, please refer to earlier labs.
Task 3:
For reference information on configuring static routes, please refer to earlier labs.
Task 4:
For reference information on pinging, please refer to earlier labs.
Task 5:
R1#conf t Enter configuration commands, one per line. End with CTRL/Z. R1(config)#enable secret CISCO R1(config)#line vty 0 4 R1(config-line)#password CISCO R1(config-line)#login R1(config-line)#end R1# R3#conf t Enter configuration commands, one per line. End with CTRL/Z. R3(config)#enable secret CISCO R3(config)#line vty 0 4 R3(config-line)#password CISCO R3(config-line)#login R3(config-line)#end R3#
Note: GNS3 has more vty lines so use the ? to establish how many you need to configure.
R1(config)#line vty 0 ? <1-903> Last Line number <cr>
Task 6:
R1#conf t Enter configuration commands, one per line. End with CTRL/Z. R1(config)#access-list 150 remark “Allow Telnet For R3 Loopback10” R1(config)#access-list 150 permit tcp 10.10.10.0 0.0.0.127 any eq telnet R1(config)#access-list 150 remark “Deny Telnet For R3 Loopback20” R1(config)#access-list 150 deny tcp 10.20.20.0 0.0.0.15 any eq telnet R1(config)#access-list 150 remark “Allow Telnet For R3 Loopback30” R1(config)#access-list 150 permit tcp 10.30.30.0 0.0.0.7 any eq telnet R1(config)#access-list 150 remark “Allow PING For R3 Loopback20” R1(config)#access-list 150 permit icmp 10.20.20.0 0.0.0.15 any echo R1(config)#int s0/0 R1(config-if)#ip access-group 150 in R1(config-if)#end R1#
NOTE: Extended ACLs have the capability to match Layer 4 protocol information. This means that you must know your well-known TCP and UDP port numbers. Fortunately, instead of having TCP and UDP port numbers, Cisco IOS ACLs allow you to use keywords for common protocols. For example, you can use the keyword telnet instead of having to use port number 23 to configure an ACL to match Telnet traffic. However, if you do decide to use a port number, Cisco IOS automatically converts it to the common name as illustrated below:
R1#conf t Enter configuration commands, one per line. End with CRTL/Z. R1(config)#access-list 100 permit tcp any any eq 23 R1(config)#access-list 100 permit tcp any any eq 80 R1(config)#access-list 100 permit tcp any any eq 179 R1(config)#access-list 100 permit udp any any eq 520 R1(config)#access-list 100 permit 88 any any R1(config)#access-list 100 permit 89 any any R1(config)#end R1# R1#show ip access-lists 100 Extended IP access list 100 10 permit tcp any any eq telnet 20 permit tcp any any eq www 30 permit tcp any any eq bgp 40 permit udp any any eq rip 50 permit eigrp any any 60 permit ospf any any
As can be seen, while we configured the ACL using port numbers, IOS converted it to common names.
Now test the ACL from the lab. To quit your Telnet access, hit the Control-Shift-6 key at the same time and then let go and press the X key. Don’t hit the enter key right after or it will resume your Telnet session.
R3#telnet 172.16.1.1 /source-interface loopback10 Trying 172.16.1.1 ... Open User Access Verification Password: R1# R3#telnet 172.16.1.1 /source-interface loopback20 Trying 172.16.1.1 ... % Destination unreachable; gateway or host down R3#telnet 172.16.1.1 /source-interface loopback30 Trying 172.16.1.1 ... Open User Access Verification Password: R1# R3#ping 172.16.1.1 source loopback 20 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 172.16.1.1, timeout is 2 seconds: Packet sent with a source address of 10.20.20.3 !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 4/5/8 ms
NOTE: When you see the message % Destination unreachable; gateway or host down when trying to telnet to a host, it is typically because there is an ACL preventing Telnet to this device. Based on our configuration, everything works, and if we looked at the ACL configured on R1, we would see matches against it as follows:
R1#show ip access-lists 150 Extended IP access list 150 10 permit tcp 10.10.10.0 0.0.0.127 any eq telnet (66 matches) 20 deny tcp 10.20.20.0 0.0.0.15 any eq telnet (3 matches) 30 permit tcp 10.30.30.0 0.0.0.7 any eq telnet (465 matches) 40 permit icmp 10.20.20.0 0.0.0.15 any echo (15 matches)
