Lab Objective:
The objective of this lab exercise is for you to learn and understand how to create and apply extended access control lists to restrict Telnet access from a router or switch.
Lab Purpose:
Configuring and applying extended ACLs to restrict Telnet access is a fundamental skill. Extended ACLs filter based on source and destination address, as well as Layer 4 protocols TCP and UDP. Telnet traffic sourced from the router or switch cannot be filtered using outbound interface ACLs. Instead, because VTY lines are used, this is where the ACL restrictions should be applied. As a Cisco engineer, as well as in the Cisco CCNA exam, you will be expected to know how to create and apply extended numbered ACLs.
Certification Level:
This lab is suitable for CCNA certification exam preparation.
Lab Difficulty:
This lab has a difficulty rating of 8/10.
Readiness Assessment:
When you are ready for your certification exam, you should complete this lab in no more than 20 minutes.
Lab Topology:
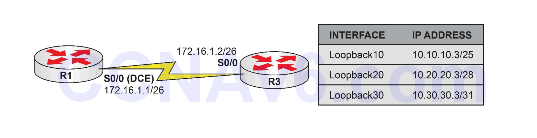
Please use the following topology to complete this lab exercise:
Task 1:
Configure hostnames on R1 and R3 as illustrated in the topology.
Task 2:
Configure R1 S0/0, which is a DCE, to provide a clock rate of 768 Kbps to R3. Configure IP addresses on the Serial interfaces of R1 and R3 as illustrated in the topology.
Task 3:
Configure a static default route on R1 pointing to R3 over the Serial connection between the two routers. Configure the Loopback interfaces specified in the diagram on R3. Configure R3 to allow Telnet sessions. Use the password CISCO for Telnet login.
Task 4:
To test connectivity, telnet from R1 to R3 Loopback10, Loopback20, and Loopback30 interfaces.
Task 5:
Create an extended named ACL called TELNET-OUT on R1. This ACL should deny all Telnet traffic to 10.10.10.0/25; permit Telnet traffic to 10.20.20.0/28; and deny Telnet traffic to 10.30.30.0/29. Apply this ACL to the Telnet lines on R1 for outbound Telnet traffic originated from the router.
Task 6:
To test your ACL configurations, telnet from R1 from R3 Loopback10, Loopback20, and Loopback30 interfaces. If your ACL configurations are correct, only telnetting from R3 Loopback20 should work.
Configuration and Verification
Task 1:
For reference information on configuring hostnames, please refer to earlier labs.
Task 2:
For reference information on configuring IP addressing, please refer to earlier labs.
Task 3:
R1#config t Enter configuration commands, one per line. End with CTRL/Z. R1(config)#ip route 0.0.0.0 0.0.0.0 serial0/0 172.16.1.2 R1(config)#line vty 0 4 R1(config-line)#password CISCO R1(config-line)#login R1(config-line)#end R1# R3#conf t Enter configuration commands, one per line. End with CTRL/Z. R3(config)#int loop10 R3(config-if)#ip address 10.10.10.3 255.255.255.128 R3(config-if)#exit R3(config)#int loop20 R3(config-if)#ip address 10.20.20.3 255.255.255.240 R3(config-if)#exit R3(config)#int loop30 R3(config-if)#ip address 10.30.30.3 255.255.255.248 R3(config-if)#exit R3(config)#line vty 0 4 R3(config-line)#password CISCO R3(config-line)#login R3(config-line)#end R3#
Task 4:
R1>telnet 10.10.10.3 Trying 10.10.10.3 ... Open User Access Verification Password: R3# R1>telnet 10.20.20.3 Trying 10.20.20.3 ... Open User Access Verification Password: R3# R1>telnet 10.30.30.3 Trying 10.30.30.3 ... Open User Access Verification Password: R3#
Task 5:
R1#conf t Enter configuration commands, one per line. End with CTRL/Z. R1(config)#ip access-list extended TELNET-OUT R1(config-ext-nacl)#remark “Deny Traffic To 10.10.10.0/25” R1(config-ext-nacl)#deny ip any 10.10.10.0 0.0.0.127 R1(config-ext-nacl)#remark “Permit Traffic To 10.20.20.0/28” R1(config-ext-nacl)#permit ip any 10.20.20.0 0.0.0.15 R1(config-ext-nacl)#remark “Deny Traffic To 10.30.30.0/29” R1(config-ext-nacl)#deny ip any 10.30.30.0 0.0.0.7 R1(config-ext-nacl)#exit R1(config)#line vty 0 4 R1(config-line)#access-class TELNET-OUT out R1(config-line)#end R1#
Task 6:
For reference information on completing Task 6, please use the telnet command from R1.
