Category: Network Security 1.0
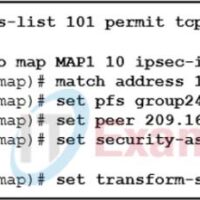
1. What is defined by an ISAKMP policy? the security associations that IPsec peers are willing to use the IP addresses of IPsec peers access lists that identify interesting traffic the preshared keys that will be exchanged between IPsec peers 2. Which are the five security associations to …
1. A network administrator is planning a VPN tunnel. Why would the engineer select main mode for IKE Phase 1? It requires less configuration. It is the industry standard. It is quicker. It is more secure. 2. What are the two types of VPN connections? (Choose two.) site-to-site …
1. What are the two important components of a public key infrastructure (PKI) used in network security? (Choose two.) digital certificates pre-shared key generation intrusion prevention system certificate authority symmetric encryption algorithms 2. What is the purpose of code signing? integrity of source .EXE files data encryption source …
1. Which security function is provided by encryption algorithms? confidentiality key management authorization integrity 2. Which type of cryptographic key would be used when connecting to a secure website? symmetric keys digital signatures DES key hash keys 3. What do most cryptographic system attacks seek to target? user …
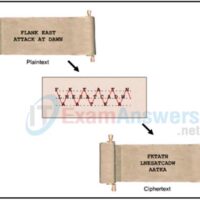
1. Refer to the exhibit. Which type of cipher method is depicted? stream cipher substitution cipher transposition cipher Caesar cipher 2. What are two objectives of ensuring data integrity? (Choose two.) Access to the data is authenticated. Data is unaltered during transit. Data is available all the time. …
1. What is the only type of traffic that is forwarded by a PVLAN protected port to other protected ports? broadcast control user management 2. A network administrator is configuring DAI on a switch with the command ip arp inspection validate src-mac. What is the purpose of this …
1. A switch has the following command issued as part of an 802.1X deployment. address ipv4 10.1.1.50 auth-port 1812 acct-port 1813 What is the purpose of this command? It identifies the address of the default gateway and the ports used for traffic destined for remote networks. It identifies …
1. Which IPS signature trigger category uses the simplest triggering mechanism and searches for a specific and pre-defined atomic or composite pattern? Pattern-Based Detection Honey Pot-Based Detection Policy-Based Detection Anomaly-Based Detection 2. What term describes a set of rules used by an IDS or IPS to detect typical …
1. What is an IPS signature? It is the timestamp that is applied to logged security events and alarms. It is the authorization that is required to implement a security policy. It is a set of rules used to detect typical intrusive activity. It is a security script …
1. Which statement accurately describes Cisco IOS zone-based policy firewall operation? The pass action works in only one direction. A router interface can belong to multiple zones. Router management interfaces must be manually assigned to the self zone. Service policies are applied in interface configuration mode. 2. How …