Category: Network Security 1.0
Checkpoint Exam: VPNs Group Exam Answers Modules 18-19 of the Network Security 1.0 1. Which two statements describe the IPsec protocol framework? (Choose two.) AH uses IP protocol 51. AH provides integrity and authentication. AH provides encryption and integrity. ESP uses UDP protocol 51. AH provides both authentication …
Checkpoint Exam: Cryptography Group Exam Answers Modules 15-17 of the Network Security 1.0 1. Which algorithm can ensure data integrity? RSA AES MD5 PKI 2. What is the keyspace of an encryption algorithm? the set of all possible values used to generate a key the set of procedures …
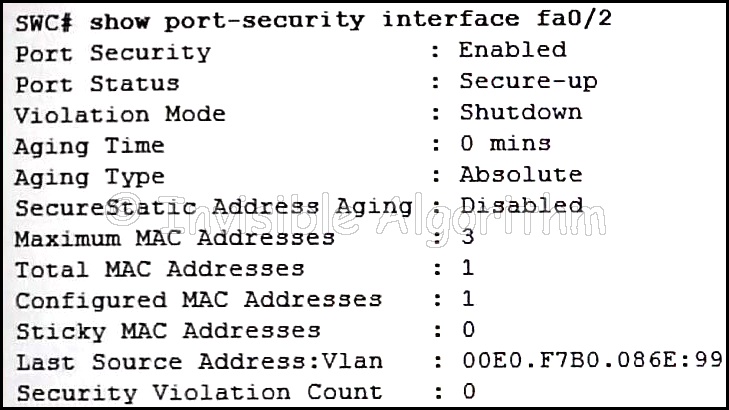
Checkpoint Exam: Layer 2 and Endpoint Security Group Exam Answers Modules 13-14 of the Network Security 1.0 1. Why are traditional network security perimeters not suitable for the latest consumer-based network endpoint devices? These devices are not managed by the corporate IT department. These devices pose no risk …
Checkpoint Exam: Intrusion Prevention Group Exam Answers Modules 11-12 of the Network Security 1.0 1. What are two characteristics of both IPS and IDS sensors? (Choose two.) neither introduce latency or jitter both use signatures to detect patterns both are deployed inline in the data stream both can …
Checkpoint Exam: ACLs and Firewalls Group Exam Answers Modules 8-10 of the Network Security 1.0 1. When creating an ACL, which keyword should be used to document and interpret the purpose of the ACL statement on a Cisco device? remark description established eq 2. Which two pieces of …
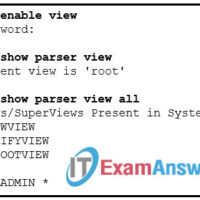
Checkpoint Exam: Monitoring and Managing Devices Group Exam Answers Modules 5-7 of the Network Security 1.0 1. Which privilege level is predefined for the privileged EXEC mode? level 0 level 1 level 15 level 16 2. What is a requirement to use the Secure Copy Protocol feature? At …
Checkpoint Exam: Securing Networks Group Exam Answers Modules 1-4 of the Network Security 1.0 1. An administrator defined a local user account with a secret password on router R1 for use with SSH. Which three additional steps are required to configure R1 to accept only encrypted SSH connections? …
1. Each day, a security analyst spends time examining logs and events from different systems and applications to quickly detect security threats. What function of the Security Information Event Management (SIEM) technology does this action represent? aggregation correlation retention forensic analysis 2. Which network security tool can detect …
1. Which two statements are true about ASA standard ACLs? (Choose two.) They identify only the destination IP address. They are the most common type of ACL. They are applied to interfaces to control traffic. They specify both the source and destination MAC address. They are typically only …
1. What is a characteristic of ASA security levels? An ACL needs to be configured to explicitly permit traffic from an interface with a lower security level to an interface with a higher security level. Each operational interface must have a name and be assigned a security level …