1.3.1.3 Lab – Researching Converged Network Services (Instructor Version – Optional Lab) Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy only. Optional activities are designed to enhance understanding and/or to provide additional practice. Objectives Part 1: Survey Your Understanding of …
1.1.1.8 Lab – Researching Network Collaboration Tools (Instructor Version – Optional Lab) Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy only. Optional activities are designed to enhance understanding and/or to provide additional practice. Objectives Part 1: Use Collaboration Tools Part …
1.0.1.2 Class Activity – Draw Your Concept of the Internet (Instructor Version – Optional Class Activity) Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy only. Optional activities are designed to enhance understanding and/or to provide additional practice. Objectives Demonstrate that …
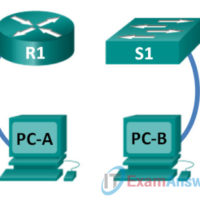
0.0.0.1 Lab – Initializing and Reloading a Router and Switch (Instructor Version) Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy only. Topology Objectives Part 1: Set Up Devices in the Network as Shown in the Topology Part 2: Initialize the …
1. Which tool provides information about vulnerabilities and aids in penetration testing and IDS signature development? SuperScan Metasploit SIEM Tripwire 2. Which tool discovers computers and services on a computer network, therefore creating a map of the network? Nessus GFI LANguard SuperScan Nmap/Zenmap 3. Which tool is a …
1. Which type of object group can contain a mix of services, such as TCP, and UDP, and can contain any protocol, such as ESP or GRE? Network User Service Protocol Security 2. Which type of object group uses unique types to send control messages? Network User Service …
1. ESP provides data authentication and integrity. true false 2. ESP provides confidentiality and authentication. true false 3. AH does not provide data confidentiality (encryption). true false 4. AH provides confidentiality by performing encryption on the IP packet. true false 5. ESP provides authentication for the inner IP …
1. IPsec can protect traffic in which OSI layers? (Choose four.) Layer 1 Layer 2 Layer 3 Layer 4 Layer 5 Layer 6 Layer 7 2. Which IPsec function uses pre-shared passwords, digital certificates, or RSA certificates? IPsec protocol Confidentiality Integrity Authentication Diffie-Hellman 3. True or False: The …
1. Which type of VPN supports dynamically changing connection information and can be enabled when needed? remote site-to-site 2. Which type of VPN is used when the host sends and receives normal TCP/IP traffic through a VPN gateway? remote site-to-site 3. Which type of VPN is used when …
1. True or False? In asymmetric encryption, encryption and decryption use the same key. True False 2. What is an example of a symmetric encryption algorithm? Internet Key Exchange (IKE) Secure Socket Layer (SSL) Secure Shell (SSH) Advanced Encryption Standard (AES) 3. Which algorithm provides asymmetric encryption? Data …