1. IPsec can protect traffic in which OSI layers? (Choose four.) Layer 1 Layer 2 Layer 3 Layer 4 Layer 5 Layer 6 Layer 7 2. Which IPsec function uses pre-shared passwords, digital certificates, or RSA certificates? IPsec protocol Confidentiality Integrity Authentication Diffie-Hellman 3. True or False: The …
1. What type of VPN can be established with a web browser using HTTPS? IPsec Client-based VPN Site-to-Site VPN Clientless VPN 2. Which feature describes SSL VPNs? All IP-based applications are supported Only requires a web browser on a host Specific devices with specific configurations can connect Uses …
1. Which VPN benefit allows an enterprise to easily add more users to the network? Cost Savings Security Scalability Compatibility 2. Which VPN benefit allows an enterprise to increase the bandwidth for remote sites without necessarily adding more equipment or WAN links? Cost Savings Security Scalability Compatibility 3. …
1. Which WAN connectivity option is based on Ethernet LAN technology? ATM Cable DSL Metro Ethernet MPLS 2. Which is a service provider WAN solution that uses labels to direct the flow of packets through the provider network? ATM Cable DSL Metro Ethernet MPLS
1. Which traditional WAN connectivity option uses T-Carrier or E-Carrier lines? ATM Frame Relay ISDN Leased lines PSTN 2. Which two traditional WAN connectivity options are circuit-switched? (Choose two.) ATM Frame Relay ISDN Leased lines PSTN 3. Which two traditional WAN connectivity options are packet-switched? (Choose two.) ATM …
1. Which two statements about the WAN OSI Layer 1 are true? (Choose two.) It describes how data will be encapsulated into a frame. It describes the electrical, mechanical, and operational components needed to transmit bits. It includes protocols such as PPP, HDLC, and Ethernet. It includes protocols …
1. Which two options describe a WAN? (Choose two.) A WAN is owned and managed by an organization or home user. A WAN provides networking services over large geographical areas. WAN services are provided for a fee. WANs providers offer low bandwidth speeds over short-distances. WANs guarantee security …
1. True or False? A side effect of NAT is that it hides the inside local IP address of a host from the outside network. True False 2. True or False? With NAT overload, each inside local IP address is translated to a unique inside global IP address …
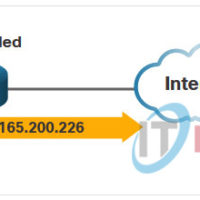
1. Refer to the exhibit. What type of NAT address is the IP address of PC1 (i.e., 192.168.10.10)? Outside Local Inside Local Outside Global Inside Global 2. Refer to the exhibit. Into what type of address has the IPv4 address for PC1 been translated (i.e., 209.165.200.226)? Outside Local …
1. Which ACL is capable of filtering based on TCP port number? extended ACL standard ACL 2. Which statement about ACLs is true? Extended ACLs are numbered 1300 – 2699. Named ACLs can be standard or extended. Numbered ACLs is the preferred method to use when configuring ACLs. …