Quiz-summary
0 of 555 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- 143
- 144
- 145
- 146
- 147
- 148
- 149
- 150
- 151
- 152
- 153
- 154
- 155
- 156
- 157
- 158
- 159
- 160
- 161
- 162
- 163
- 164
- 165
- 166
- 167
- 168
- 169
- 170
- 171
- 172
- 173
- 174
- 175
- 176
- 177
- 178
- 179
- 180
- 181
- 182
- 183
- 184
- 185
- 186
- 187
- 188
- 189
- 190
- 191
- 192
- 193
- 194
- 195
- 196
- 197
- 198
- 199
- 200
- 201
- 202
- 203
- 204
- 205
- 206
- 207
- 208
- 209
- 210
- 211
- 212
- 213
- 214
- 215
- 216
- 217
- 218
- 219
- 220
- 221
- 222
- 223
- 224
- 225
- 226
- 227
- 228
- 229
- 230
- 231
- 232
- 233
- 234
- 235
- 236
- 237
- 238
- 239
- 240
- 241
- 242
- 243
- 244
- 245
- 246
- 247
- 248
- 249
- 250
- 251
- 252
- 253
- 254
- 255
- 256
- 257
- 258
- 259
- 260
- 261
- 262
- 263
- 264
- 265
- 266
- 267
- 268
- 269
- 270
- 271
- 272
- 273
- 274
- 275
- 276
- 277
- 278
- 279
- 280
- 281
- 282
- 283
- 284
- 285
- 286
- 287
- 288
- 289
- 290
- 291
- 292
- 293
- 294
- 295
- 296
- 297
- 298
- 299
- 300
- 301
- 302
- 303
- 304
- 305
- 306
- 307
- 308
- 309
- 310
- 311
- 312
- 313
- 314
- 315
- 316
- 317
- 318
- 319
- 320
- 321
- 322
- 323
- 324
- 325
- 326
- 327
- 328
- 329
- 330
- 331
- 332
- 333
- 334
- 335
- 336
- 337
- 338
- 339
- 340
- 341
- 342
- 343
- 344
- 345
- 346
- 347
- 348
- 349
- 350
- 351
- 352
- 353
- 354
- 355
- 356
- 357
- 358
- 359
- 360
- 361
- 362
- 363
- 364
- 365
- 366
- 367
- 368
- 369
- 370
- 371
- 372
- 373
- 374
- 375
- 376
- 377
- 378
- 379
- 380
- 381
- 382
- 383
- 384
- 385
- 386
- 387
- 388
- 389
- 390
- 391
- 392
- 393
- 394
- 395
- 396
- 397
- 398
- 399
- 400
- 401
- 402
- 403
- 404
- 405
- 406
- 407
- 408
- 409
- 410
- 411
- 412
- 413
- 414
- 415
- 416
- 417
- 418
- 419
- 420
- 421
- 422
- 423
- 424
- 425
- 426
- 427
- 428
- 429
- 430
- 431
- 432
- 433
- 434
- 435
- 436
- 437
- 438
- 439
- 440
- 441
- 442
- 443
- 444
- 445
- 446
- 447
- 448
- 449
- 450
- 451
- 452
- 453
- 454
- 455
- 456
- 457
- 458
- 459
- 460
- 461
- 462
- 463
- 464
- 465
- 466
- 467
- 468
- 469
- 470
- 471
- 472
- 473
- 474
- 475
- 476
- 477
- 478
- 479
- 480
- 481
- 482
- 483
- 484
- 485
- 486
- 487
- 488
- 489
- 490
- 491
- 492
- 493
- 494
- 495
- 496
- 497
- 498
- 499
- 500
- 501
- 502
- 503
- 504
- 505
- 506
- 507
- 508
- 509
- 510
- 511
- 512
- 513
- 514
- 515
- 516
- 517
- 518
- 519
- 520
- 521
- 522
- 523
- 524
- 525
- 526
- 527
- 528
- 529
- 530
- 531
- 532
- 533
- 534
- 535
- 536
- 537
- 538
- 539
- 540
- 541
- 542
- 543
- 544
- 545
- 546
- 547
- 548
- 549
- 550
- 551
- 552
- 553
- 554
- 555
Information
 Demonstrates your expertise in the simulator of exam ccna 200 125, this Simulator you will allow prepare you for the exam real that is the 99.99% equal
Topics:
1: Networks Fundamentals
2: LAN Switching Technologies
3: Routing Technologies
4: WAN Technologies
5: Address Space Management
6: Infrastructure Services
7: Infrastructure Management
8: Infrastructure Security
9: SNMP / Syslog /CEF
10: Temas Miscelaneos (exclusivos de Nettraining)
11: Subnetting (exclusivo de Nettraining)
550 questions
Demonstrates your expertise in the simulator of exam ccna 200 125, this Simulator you will allow prepare you for the exam real that is the 99.99% equal
Topics:
1: Networks Fundamentals
2: LAN Switching Technologies
3: Routing Technologies
4: WAN Technologies
5: Address Space Management
6: Infrastructure Services
7: Infrastructure Management
8: Infrastructure Security
9: SNMP / Syslog /CEF
10: Temas Miscelaneos (exclusivos de Nettraining)
11: Subnetting (exclusivo de Nettraining)
550 questions
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 555 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- 143
- 144
- 145
- 146
- 147
- 148
- 149
- 150
- 151
- 152
- 153
- 154
- 155
- 156
- 157
- 158
- 159
- 160
- 161
- 162
- 163
- 164
- 165
- 166
- 167
- 168
- 169
- 170
- 171
- 172
- 173
- 174
- 175
- 176
- 177
- 178
- 179
- 180
- 181
- 182
- 183
- 184
- 185
- 186
- 187
- 188
- 189
- 190
- 191
- 192
- 193
- 194
- 195
- 196
- 197
- 198
- 199
- 200
- 201
- 202
- 203
- 204
- 205
- 206
- 207
- 208
- 209
- 210
- 211
- 212
- 213
- 214
- 215
- 216
- 217
- 218
- 219
- 220
- 221
- 222
- 223
- 224
- 225
- 226
- 227
- 228
- 229
- 230
- 231
- 232
- 233
- 234
- 235
- 236
- 237
- 238
- 239
- 240
- 241
- 242
- 243
- 244
- 245
- 246
- 247
- 248
- 249
- 250
- 251
- 252
- 253
- 254
- 255
- 256
- 257
- 258
- 259
- 260
- 261
- 262
- 263
- 264
- 265
- 266
- 267
- 268
- 269
- 270
- 271
- 272
- 273
- 274
- 275
- 276
- 277
- 278
- 279
- 280
- 281
- 282
- 283
- 284
- 285
- 286
- 287
- 288
- 289
- 290
- 291
- 292
- 293
- 294
- 295
- 296
- 297
- 298
- 299
- 300
- 301
- 302
- 303
- 304
- 305
- 306
- 307
- 308
- 309
- 310
- 311
- 312
- 313
- 314
- 315
- 316
- 317
- 318
- 319
- 320
- 321
- 322
- 323
- 324
- 325
- 326
- 327
- 328
- 329
- 330
- 331
- 332
- 333
- 334
- 335
- 336
- 337
- 338
- 339
- 340
- 341
- 342
- 343
- 344
- 345
- 346
- 347
- 348
- 349
- 350
- 351
- 352
- 353
- 354
- 355
- 356
- 357
- 358
- 359
- 360
- 361
- 362
- 363
- 364
- 365
- 366
- 367
- 368
- 369
- 370
- 371
- 372
- 373
- 374
- 375
- 376
- 377
- 378
- 379
- 380
- 381
- 382
- 383
- 384
- 385
- 386
- 387
- 388
- 389
- 390
- 391
- 392
- 393
- 394
- 395
- 396
- 397
- 398
- 399
- 400
- 401
- 402
- 403
- 404
- 405
- 406
- 407
- 408
- 409
- 410
- 411
- 412
- 413
- 414
- 415
- 416
- 417
- 418
- 419
- 420
- 421
- 422
- 423
- 424
- 425
- 426
- 427
- 428
- 429
- 430
- 431
- 432
- 433
- 434
- 435
- 436
- 437
- 438
- 439
- 440
- 441
- 442
- 443
- 444
- 445
- 446
- 447
- 448
- 449
- 450
- 451
- 452
- 453
- 454
- 455
- 456
- 457
- 458
- 459
- 460
- 461
- 462
- 463
- 464
- 465
- 466
- 467
- 468
- 469
- 470
- 471
- 472
- 473
- 474
- 475
- 476
- 477
- 478
- 479
- 480
- 481
- 482
- 483
- 484
- 485
- 486
- 487
- 488
- 489
- 490
- 491
- 492
- 493
- 494
- 495
- 496
- 497
- 498
- 499
- 500
- 501
- 502
- 503
- 504
- 505
- 506
- 507
- 508
- 509
- 510
- 511
- 512
- 513
- 514
- 515
- 516
- 517
- 518
- 519
- 520
- 521
- 522
- 523
- 524
- 525
- 526
- 527
- 528
- 529
- 530
- 531
- 532
- 533
- 534
- 535
- 536
- 537
- 538
- 539
- 540
- 541
- 542
- 543
- 544
- 545
- 546
- 547
- 548
- 549
- 550
- 551
- 552
- 553
- 554
- 555
- Answered
- Review
-
Question 1 of 555
1. Question
Refer to the exhibit. What will Router1 do when it receives the data frame shown? (Choose three.)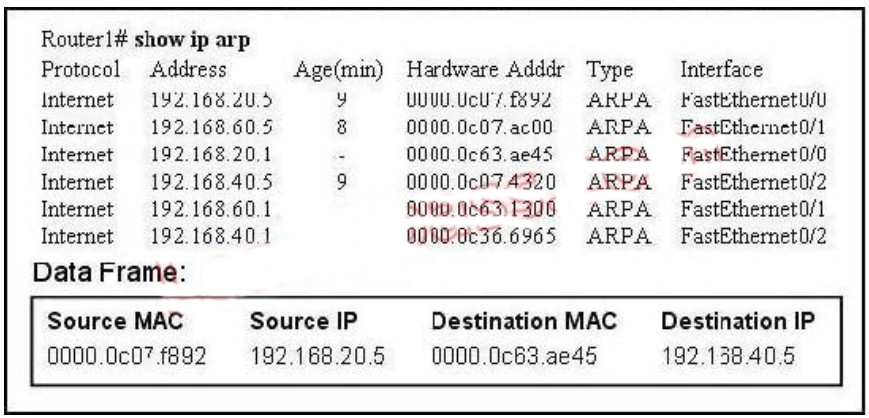 Correct
Correct
Incorrect
Hint
Remember, the source and destination MAC changes as each router hop along with the TTL being decremented but the source and destination IP address remain the same from source to destination. -
Question 2 of 555
2. Question
Refer to the exhibit. Which three statements correctly describe Network Device A? (Choose three.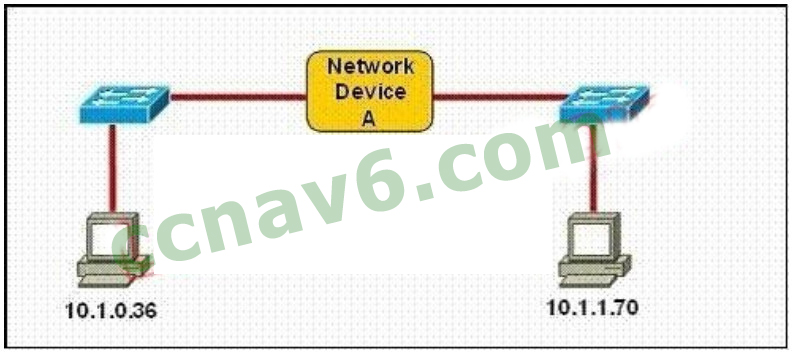 Correct
Correct
Incorrect
Hint
Explanation: If Subnet Mask is 255.255.255.128 the hosts vary from x.x.x.0 – x.x.x.127 & x.x.x.128-x.x.x.255,so the IP Addresses of 2 hosts fall in different subnets so each interface needs an IP an address so that they can communicate each other. If Subnet Mask is 255.255.255.0 the 2 specified hosts fall in different subnets so they need a Layer 3 device to communicate. If Subnet Mask is 255.255.254.0 the 2 specified hosts are in same subnet so are in network address and can be accommodated in same Layer 2 domain and can communicate with each other directly using the Layer 2 address. -
Question 3 of 555
3. Question
Which layer in the OSI reference model is responsible for determining the availability of the receiving program and checking to see if enough resources exist for that communication?Correct
Incorrect
Hint
This question is to examine the OSI reference model. The Application layer is responsible for identifying and establishing the availability of the intended communication partner and determining whether sufficient resources for the intended communication exist. -
Question 4 of 555
4. Question
Refer to the exhibit. Host A pings interface S0/0 on router 3. What is the TTL value for that ping?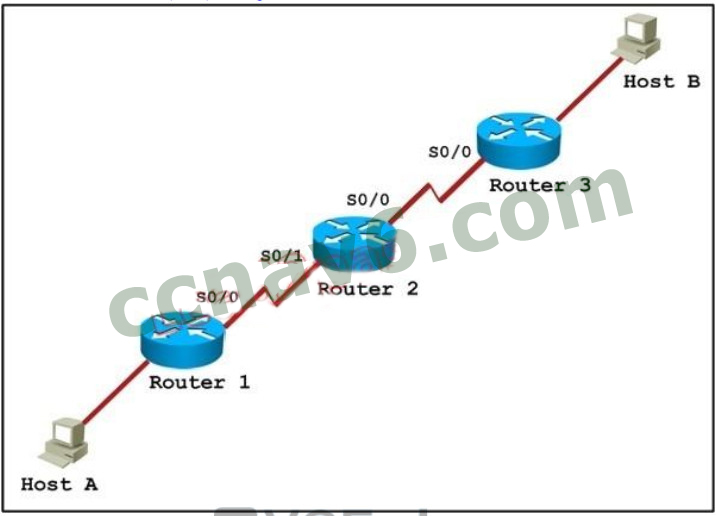 Correct
Correct
Incorrect
Hint
From the CCNA ICND2 Exam book: “Routers decrement the TTL by 1 every time they forward a packet; if a router decrements the TTL to 0, it throws away the packet. This prevents packets from rotating forever.” I want to make it clear that before the router forwards a packet, the TTL is still remain the same. For example in the topology above, pings to S0/1 and S0/0 of Router 2 have the same TTL. -
Question 5 of 555
5. Question
Which of the following describes the roles of devices in a WAN? (Choose three.)Correct
Incorrect
Hint
The idea behind a WAN is to be able to connect two DTE networks together through a DCE network. The network’s DCE device (includes CSU/DSU) provides clocking to the DTE-connected interface (the router’s serial interface). A modem modulates outgoing digital signals from a computer or other digital device to analog signals for a conventional copper twisted pair telephone line and demodulates the incoming analog signal and converts it to a digital signal for the digital device. A CSU/DSU is used between two digital lines – For more explanation of answer D, in telephony the local loop (also referred to as a subscriber line) is the physical link or circuit that connects from the demarcation point of the customer premises to the edge of the carrier or telecommunications service provider’s network. Therefore a modem terminates an analog local loop is correct.
A modem modulates outgoing digital signals from a computer or other digital device to analog signals for a conventional copper twisted pair telephone line and demodulates the incoming analog signal and converts it to a digital signal for the digital device. A CSU/DSU is used between two digital lines – For more explanation of answer D, in telephony the local loop (also referred to as a subscriber line) is the physical link or circuit that connects from the demarcation point of the customer premises to the edge of the carrier or telecommunications service provider’s network. Therefore a modem terminates an analog local loop is correct.

-
Question 6 of 555
6. Question
Refer to the exhibit. Refer to the exhibit. After HostA pings HostB, which entry will be in the ARP cache of HostA to support this transmission?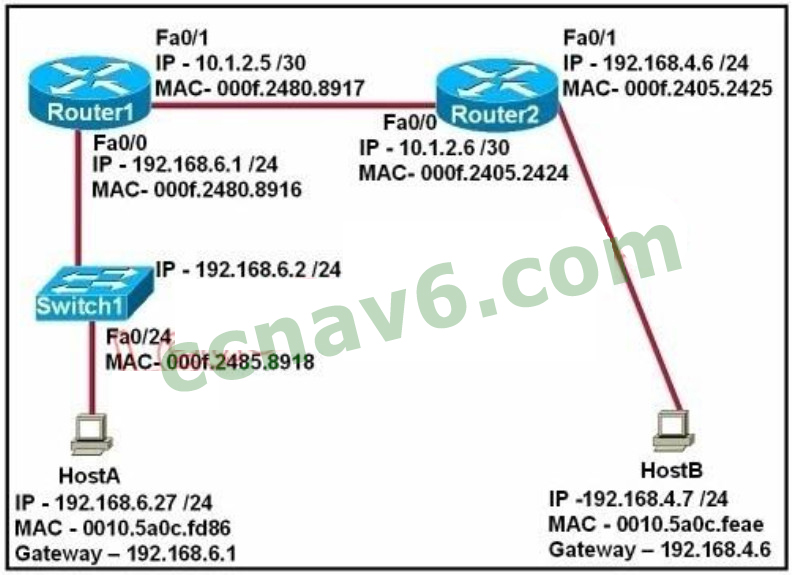 Correct
Correct
Incorrect
Hint
Explanation: When a host needs to reach a device on another subnet, the ARP cache entry will be that of the Ethernet address of the local router (default gateway) for the physical MAC address. The destination IP address will not change, and will be that of the remote host (HostB) -
Question 7 of 555
7. Question
A network administrator is verifying the configuration of a newly installed host by establishing an FTP connection to a remote server. What is the highest layer of the protocol stack that the network administrator is using for this operation?Correct
Incorrect
Hint
FTP belongs to Application layer and it is also the highest layer of the OSI model -
Question 8 of 555
8. Question
A network interface port has collision detection and carrier sensing enabled on a shared twisted pair network. From this statement, what is known about the network interface port?Correct
Incorrect
Hint
Explanation: Modern Ethernet networks built with switches and full-duplex connections no longer utilize CSMA/CD. CSMA/CD is only used in obsolete shared media Ethernet (which uses repeater or hub). -
Question 9 of 555
9. Question
A receiving host computes the checksum on a frame and determines that the frame is damaged. The frame is then discarded. At which OSI layer did this happen?Correct
Incorrect
Hint
The Data Link layer provides the physical transmission of the data and handles error notification, network topology, and flow control. The Data Link layer formats the message into pieces, each called a data frame, and adds a customized header containing the hardware destination and source address. Protocols Data Unit (PDU) on Datalink layer is called frame. According to this question the frame is damaged and discarded which will happen at the Data Link layer. -
Question 10 of 555
10. Question
Which of the following correctly describe steps in the OSI data encapsulation process? (Choose two.)Correct
Incorrect
Hint
The Application Layer (Layer 7) refers to communications services to applications and is the interface between the network and the application. Examples include. Telnet, HTTP, FTP, Internet browsers, NFS, SMTP gateways, SNMP, X.400 mail, and FTAM. The Presentation Layer (Layer 6) defining data formats, such as ASCII text, EBCDIC text, binary, BCD, and JPEG. Encryption also is defined as a presentation layer service. Examples include. JPEG, ASCII, EBCDIC, TIFF, GIF, PICT, encryption, MPEG, and MIDI. The Session Layer (Layer 5) defines how to start, control, and end communication sessions. This includes the control and management of multiple bidirectional messages so that the application can be notified if only some of a series of messages are completed. This allows the presentation layer to have a seamless view of an incoming stream of data. The presentation layer can be presented with data if all flows occur in some cases. Examples include. RPC, SQL, NFS, NetBios names, AppleTalk ASP, and DECnet SCP The Transport Layer (Layer 4) defines several functions, including the choice of protocols. The most important Layer 4 functions are error recovery and flow control. The transport layer may provide for retransmission, i.e., error recovery, and may use flow control to prevent unnecessary congestion by attempting to send data at a rate that the network can accommodate, or it might not, depending on the choice of protocols. Multiplexing of incoming data for different flows to applications on the same host is also performed. Reordering of the incoming data stream when packets arrive out of order is included. Examples include. TCP, UDP, and SPX. The Network Layer (Layer 3) defines end-to-end delivery of packets and defines logical addressing to accomplish this. It also defines how routing works and how routes are learned; and how to fragment a packet into smaller packets to accommodate media with smaller maximum transmission unit sizes. Examples include. IP, IPX, AppleTalk DDP, and ICMP. Both IP and IPX define logical addressing, routing, the learning of routing information, and end-to-end delivery rules. The IP and IPX protocols most closely match the OSI network layer (Layer 3) and are called Layer 3 protocols because their functions most closely match OSI’s Layer 3. The Data Link Layer (Layer 2) is concerned with getting data across one particular link or medium. The data link protocols define delivery across an individual link. These protocols are necessarily concerned with the type of media in use. Examples includE. IEEE 802.3/802.2, HDLC, Frame Relay, PPP, FDDI, ATM, and IEEE 802.5/802.2. -
Question 11 of 555
11. Question
Refer to the graphic. Host A is communicating with the server. What will be the source MAC address of the frames received by Host A from the server?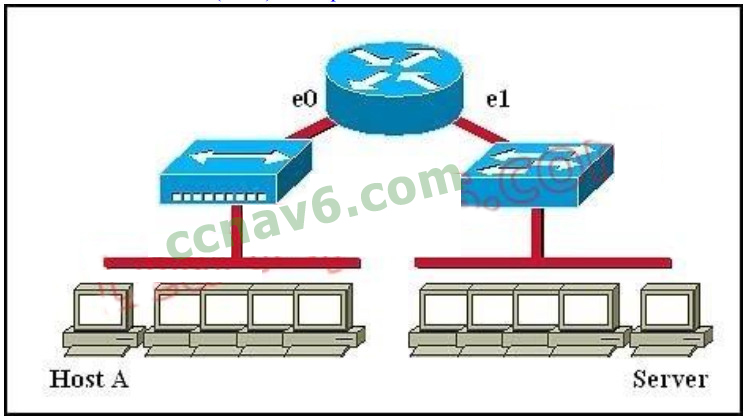 Correct
Correct
Incorrect
Hint
Whereas switches can only examine and forward packets based on the contents of the MAC header, routers can look further into the packet to discover the network for which a packet is destined. Routers make forwarding decisions based on the packet’s network-layer header (such as an IPX header or IP header). These network-layer headers contain source and destination network addresses. Local devices address packets to the router’s MAC address in the MAC header. After receiving the packets, the router must perform the following steps: 1. Check the incoming packet for corruption, and remove the MAC header . The router checks the packet for MAC-layer errors. The router then strips off the MAC header and examines the network- layer header to determine what to do with the packet. 2. Examine the age of the packet. The router must ensure that the packet has not come too far to be forwarded. For example, IPX headers contain a hop count. By default, 15 hops is the maximum number of hops (or routers) that a packet can cross. If a packet has a hop count of 15, the router discards the packet. IP headers contain a Time to Live (TTL) value. Unlike the IPX hop count, which increments as the packet is forwarded through each router, the IP TTL value decrements as the IP packet is forwarded through each router. If an IP packet has a TTL value of 1, the router discards the packet. A router cannot decrement the TTL value to 1 and then forward the packet. 3. Determine the route to the destination. Routers maintain a routing table that lists available networks, the direction to the desired network (the outgoing interface number), and the distance to those networks. After determining which direction to forward the packet, the router must build a new header. (If you want to read the IP routing tables on a Windows 95/98 workstation, type ROUTE PRINT in the DOS box.) 4. Build the new MAC header and forward the packet. Finally, the router builds a new MAC header for the packet. The MAC header includes the router’s MAC address and the final destination’s MAC address or the MAC address of the next router in the path. -
Question 12 of 555
12. Question
Refer to the exhibit. What two results would occur if the hub were to be replaced with a switch that is configured with one Ethernet VLAN? (Choose two.) Correct
Correct
Incorrect
Hint
Explanation: Basically, a collision domain is a network segment that allows normal network traffic to flow back and forth. In the old days of hubs, this meant you had a lot of collisions, and the old CSMA/CD would be working overtime to try to get those packets re-sent every time there was a collision on the wire (since ethernet allows only one host to be transmitting at once without there being a traffic jam). With switches, you break up collision domains by switching packets bound for other collision domains. These days, since we mostly use switches to connect computers to the network, you generally have one collision domain to a PC. Broadcast domains are exactly what they imply: they are network segments that allow broadcasts to be sent across them. Since switches and bridges allow for broadcast traffic to go unswitched, broadcasts can traverse collision domains freely. Routers, however, don’t allow broadcasts through by default, so when a broadcast hits a router (or the perimeter of a VLAN), it doesn’t get forwarded. The simple way to look at it is this way: switches break up collision domains, while routers (and VLANs) break up collision domains and broadcast domains. Also, a broadcast domain can contain multiple collision domains, but a collision domain can never have more than one broadcast domain associated with it. Collision Domain: A group of Ethernet or Fast Ethernet devices in a CSMA/CD LAN that are connected by repeaters and compete for access on the network. Only one device in the collision domain may transmit at any one time, and the other devices in the domain listen to the network in order to avoid data collisions. A collision domain is sometimes referred to as an Ethernet segment. Broadcast Domain: Broadcasting sends a message to everyone on the local network (subnet). An example for Broadcasting would be DHCP Request from a Client PC. The Client is asking for a IP Address, but the client does not know how to reach the DHCP Server. So the client sends a DHCP Discover packet to EVERY PC in the local subnet (Broadcast). But only the DHCP Server will answer to the Request. How to count them? Broadcast Domain: No matter how many hosts or devices are connected together, if they are connected with a repeater, hub, switch or bridge, all these devices are in ONE Broadcast domain (assuming a single VLAN). A Router is used to separate Broadcast-Domains (we could also call them Subnets – or call them VLANs). So, if a router stands between all these devices, we have TWO broadcast domains. Collision Domain: Each connection from a single PC to a Layer 2 switch is ONE Collision domain. For example, if 5 PCs are connected with separate cables to a switch, we have 5 Collision domains. If this switch is connected to another switch or a router, we have one collision domain more. If 5 Devices are connected to a Hub, this is ONE Collision Domain. Each device that is connected to a Layer 1 device (repeater, hub) will reside in ONE single collision domain. -
Question 13 of 555
13. Question
Which three statements accurately describe Layer 2 Ethernet switches? (Choose three.)Correct
Incorrect
Hint
Microsegmentation is a network design (functionality) where each workstation or device on a network gets its own dedicated segment (collision domain) to the switch. Each network device gets the full bandwidth of the segment and does not have to share the segment with other devices. Microsegmentation reduces and can even eliminate collisions because each segment is its own collision domain -> . Note: Microsegmentation decreases the number of collisions but it increases the number of collision domains. -
Question 14 of 555
14. Question
Where does routing occur within the DoD TCP/IP reference model?Correct
Incorrect
-
Question 15 of 555
15. Question
Refer to exhibit: Which destination addresses will be used by Host A to send data to Host C? (Choose two.)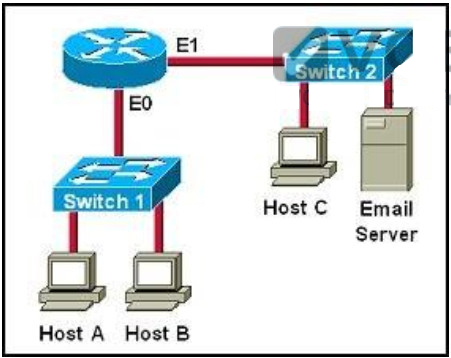 Correct
Correct
Incorrect
Hint
While transferring data through many different networks, the source and destination IP addresses are not changed. Only the source and destination MAC addresses are changed. So in this case Host A will use the IP address of Host C and the MAC address of E0 interface to send data. When the router receives this data, it replaces the source MAC address with it own E1 interface’s MAC address and replaces the destination MAC address with Host C’s MAC address before sending to Host C. -
Question 16 of 555
16. Question
For what two purposes does the Ethernet protocol use physical addresses? (Choose two.)Correct
Incorrect
Hint
Physical addresses or MAC addresses are used to identify devices at layer 2. MAC addresses are only used to communicate on the same network. To communicate on different network we have to use Layer 3 addresses (IP addresses) -> B is not correct. Layer 2 frame and Layer 3 packet can be recognized via headers. Layer 3 packet also contains physical address -> On Ethernet, each frame has the same priority to transmit by default -> All devices need a physical address to identify itself. If not, they can not communicate -> -
Question 17 of 555
17. Question
Refer to the exhibit. Based on the information given, which switch will be elected root bridge and why?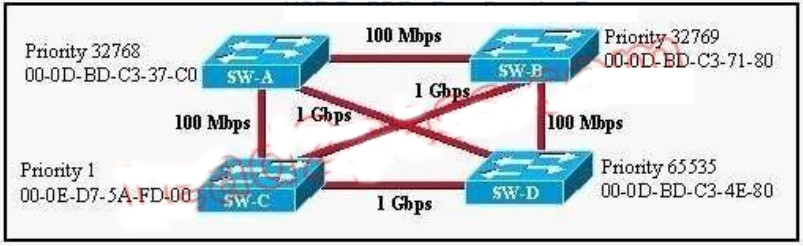 Correct
Correct
Incorrect
Hint
To elect the root bridge in the LAN, first check the priority value. The switch having the lowest priority will win the election process. If Priority Value is the same then it checks the MAC Address; the switch having the lowest MAC Address will become the root bridge. In this case, switch C has the lowest MAC Address so it becomes the root bridge. -
Question 18 of 555
18. Question
Refer to the exhibit. Switch-1 needs to send data to a host with a MAC address of 00b0.d056.efa4. What will Switch-1 do with this data?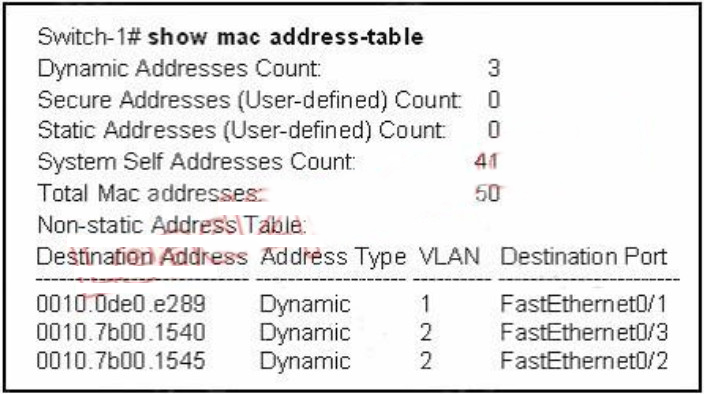 Correct
Correct
Incorrect
Hint
This question tests the operating principles of the Layer 2 switch. Check the MAC address table of Switch1 and find that the MAC address of the host does not exist in the table. Switch1 will flood the data out all of its ports except the port from which the data originated to determine which port the host is located in. Switches work as follows: In output there is no MAC address of give host so switch floods to all ports except the source port. -
Question 19 of 555
19. Question
What value is primarily used to determine which port becomes the root port on each nonroot switch in a spanning-tree topology?Correct
Incorrect
Hint
The path cost to the root bridge is the most important value to determine which port will become the root port on each non-root switch. In particular, the port with lowest cost to the root bridge will become root port (on non-root switch). -
Question 20 of 555
20. Question
What is the function of the command switchport trunk native vlan 999 on a Cisco Catalyst switch?Correct
Incorrect
Hint
Configuring the Native VLAN for Untagged Traffic A trunk port configured with 802.1Q tagging can receive both tagged and untagged traffic. By default, the switch forwards untagged traffic in the native VLAN configured for the port. The native VLAN is VLAN 1 by default. -
Question 21 of 555
21. Question
Which two protocols are used by bridges and/or switches to prevent loops in a layer 2 network? (Choose two.)Correct
Incorrect
Hint
This question is to examine the STP protocol. STP (802.1d) is used to prevent Layer 2 loops. 802.1q is a Frame Relay protocol which belongs to VLAN. SAP is a concept of the OSI model. -
Question 22 of 555
22. Question
Which switch would STP choose to become the root bridge in the selection process?Correct
Incorrect
-
Question 23 of 555
23. Question
A switch is configured with all ports assigned to vlan 2 with full duplex FastEthernet to segment existing departmental traffic. What is the effect of adding switch ports to a new VLAN on the switch?Correct
Incorrect
Hint
Each VLAN creates its own broadcast domain. Since this is a full duplex switch, each port is a separate collision domain. -
Question 24 of 555
24. Question
What are three benefits of implementing VLANs? (Choose three.)Correct
Incorrect
Hint
Benefits of VLANs VLAN is a network structure which allows users to communicate while in different locations by sharing one multicast domain and a single broadcast. They provide numerous networking benefits and have become popular in the market. For instance, it helps reduce administrative costs when users are geographically dispersed. 1. Inexpensive The popularity of VLANs is due to the fact that changes, adds, and moves can be attained simply by making necessary configurations on the VLAN port. Time-consuming, re-addressing, and host reconfigurations is now a thing of the past, because network configuration can be made at ease when need arises. 2. Better management A VLAN typically solve the scalability issues that exist in a large network by breaking the main domain into several VLAN groups or smaller broadcast configurations, thereby encourage better control of multicast traffic as well as broadcast domains. 3. Improves network security High-security can be positioned in different VLAN groups to ensure that non-members cannot receive their broadcasts. On the other hand, a router is added and workgroups relocated into centralized locations. 4. Enhances performance A more efficient use of bandwidth can be achieved allowing many logical networks to use the same network infrastructure. 5. Segment multiple networks VLANs are typically used to achieve multiple purposes. They are popularly used to reduce broadcast traffic. Each VLAN creates a separate, smaller broadcast domain. 6. Better administration VLANs facilitate grouping of multiple geographical stations. When VLAN users move to another physical location, the network does not have to be configured. -
Question 25 of 555
25. Question
Which IEEE standard protocol is initiated as a result of successful DTP completion in a switch over Fast Ethernet?Correct
Incorrect
Hint
Dynamic Trunking Protocol (DTP) is a Cisco proprietary protocol for negotiating trunking on a link between two devices and for negotiating the type of trunking encapsulation (802.1Q) to be used. -
Question 26 of 555
26. Question
Which of the following are benefits of VLANs? (Choose three.)Correct
Incorrect
Hint
When using VLAN the number and size of collision domains remain the same -> VLANs allow to group users by function, not by location or geography -> . VLANs help minimize the incorrect configuration of VLANs so it enhances the security of the network -> . VLAN increases the size of broadcast domains but does not decrease the number of collision domains -> VLANs increase the number of broadcast domains while decreasing the size of the broadcast domains which increase the utilization of the links. It is also a big advantage of VLAN -> . VLANs are useful but they are more complex and need more administration -> -
Question 27 of 555
27. Question
Refer to the exhibit. A technician has installed SwitchB and needs to configure it for remote access from the management workstation connected to SwitchA. Which set of commands is required to accomplish this task?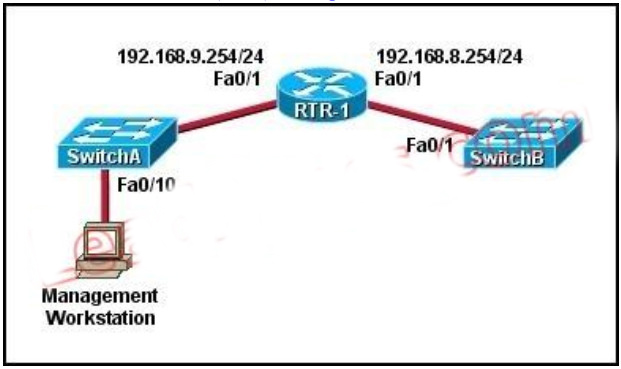 Correct
Correct
Incorrect
Hint
To remote access to SwitchB, it must have a management IP address on a VLAN on that switch. Traditionally, we often use VLAN 1 as the management VLAN (but in fact it is not secure). In the exhibit, we can recognize that the Management Workstation is in a different subnet from the SwitchB. For intersubnetwork communication to occur, you must configure at least one default gateway. This default gateway is used to forward traffic originating from the switch only, not to forward traffic sent by devices connected to the switch. -
Question 28 of 555
28. Question
In an Ethernet network, under what two scenarios can devices transmit? (Choose two.)Correct
Incorrect
Hint
Ethernet network is a shared environment so all devices have the right to access to the medium. If more than one device transmits simultaneously, the signals collide and can not reach the destination. If a device detects another device is sending, it will wait for a specified amount of time before attempting to transmit. When there is no traffic detected, a device will transmit its message. While this transmission is occurring, the device continues to listen for traffic or collisions on the LAN. After the message is sent, the device returns to its default listening mode. -
Question 29 of 555
29. Question
Which two states are the port states when RSTP has converged? (Choose two.)Correct
Incorrect
Hint
http://www.cisco.com/en/US/tech/tk389/tk621/technologies_white_paper09186a0080094cfa.shtml #states -
Question 30 of 555
30. Question
Which two commands can be used to verify a trunk link configuration status on a given Cisco switch interface? (Choose two.)Correct
Incorrect
-
Question 31 of 555
31. Question
Correct
Incorrect
Hint
Only router can break up broadcast domains so in the exhibit there are 2 broadcast domains: from e0 interface to the left is a broadcast domain and from e1 interface to the right is another broadcast domain ->. Both router and switch can break up collision domains so there is only 1 collision domain on the left of the router (because hub doesn’t break up collision domain) and there are 6 collision domains on the right of the router (1 collision domain from e1 interface to the switch + 5 collision domains for 5 PCs in Production) -> -
Question 32 of 555
32. Question
Which command enables RSTP on a switch?Correct
Incorrect
Hint
Ethernet network is a shared environment so all devices have the right to access to the medium. If more than one device transmits simultaneously, the signals collide and can not reach the destination. If a device detects another device is sending, it will wait for a specified amount of time before attempting to transmit. When there is no traffic detected, a device will transmit its message. While this transmission is occurring, the device continues to listen for traffic or collisions on the LAN. After the message is sent, the device returns to its default listening mode. -
Question 33 of 555
33. Question
Refer to the exhibit. All switch ports are assigned to the correct VLANs, but none of the hosts connected to SwitchA can communicate with hosts in the same VLAN connected to SwitchB. Based on the output shown, what is the most likely problem?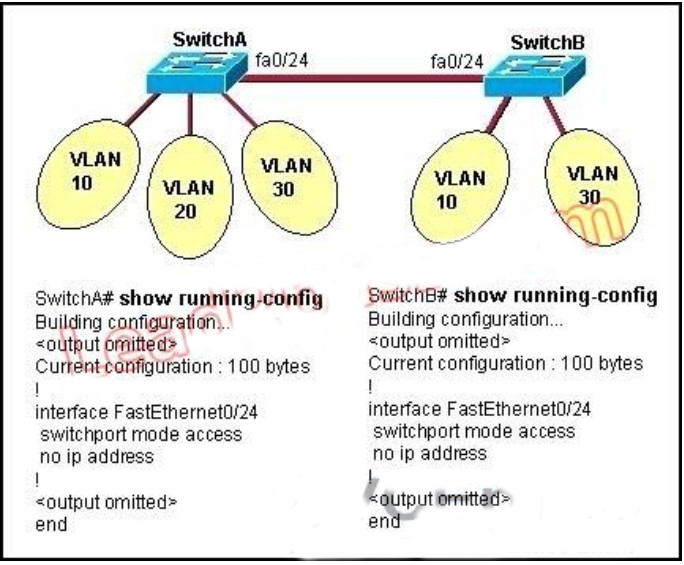 Correct
Correct
Incorrect
Hint
In order to pass traffic from VLANs on different switches, the connections between the switches must be configured as trunk ports. -
Question 34 of 555
34. Question
What is the function of the command switchport trunk native vlan 999 on a Cisco Catalyst switch?Correct
Incorrect
Hint
Configuring the Native VLAN for Untagged Traffic A trunk port configured with 802.1Q tagging can receive both tagged and untagged traffic. By default, the switch forwards untagged traffic in the native VLAN configured for the port. The native VLAN is VLAN 1 by default. -
Question 35 of 555
35. Question
Refer to the exhibit. Given the output shown from this Cisco Catalyst 2950, what is the reason that interface FastEthernet 0/10 is not the root port for VLAN 2?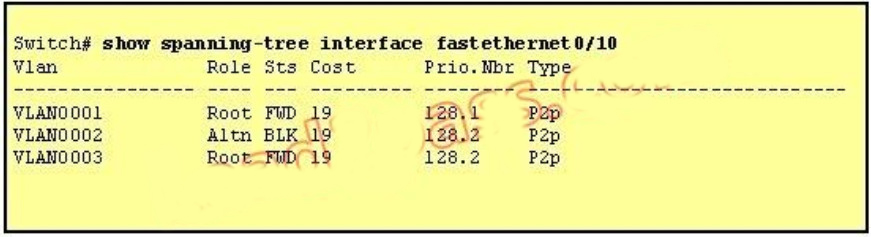 Correct
Correct
Incorrect
Hint
Since the port is in the blocked status, we must assume that there is a shorter path to the root bridge elsewhere. -
Question 36 of 555
36. Question
Why will a switch never learn a broadcast address?Correct
Incorrect
Hint
Switches dynamically learn MAC addresses based on the source MAC addresses that it sees, and since a broadcast is never the source, it will never learn the broadcast address. -
Question 37 of 555
37. Question
Correct
Incorrect
Hint
The root bridge is determined by the lowest bridge ID, and this switch has a bridge ID priority of 32768, which is higher than the roots priority of 20481. -
Question 38 of 555
38. Question
Which two link protocols are used to carry multiple VLANs over a single link? (Choose two.)Correct
Incorrect
Hint
Cisco switches can use two different encapsulation types for trunks, the industry standard 802.1q or the Cisco proprietary ISL. Generally, most network engineers prefer to use 802.1q since it is standards based and will interoperate with other vendors. -
Question 39 of 555
39. Question
Assuming the default switch configuration, which VLAN range can be added, modified, and removed on a Cisco switch?Correct
Incorrect
Hint
VLAN 1 is the default VLAN on Cisco switch. It always exists and can not be added, modified or removed. VLANs 1002-1005 are default VLANs for FDDI & Token Ring and they can’t be deleted or used for Ethernet. -
Question 40 of 555
40. Question
Which statement about VLAN operation on Cisco Catalyst switches is true?Correct
Incorrect
Hint
Each VLAN resides in its own broadcast domain, so incoming frames with unknown destinations are only transmitted to ports that reside in the same VLAN as the incoming frame. -
Question 41 of 555
41. Question
Refer to the topology shown in the exhibit. Which ports will be STP designated ports if all the links are operating at the same bandwidth? (Choose three.)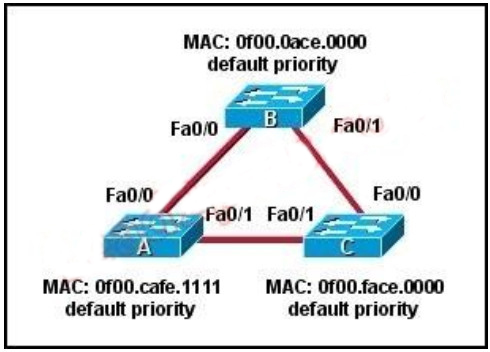 Correct
Correct
Incorrect
Hint
This question is to check the spanning tree election problem. 1. First, select the root bridge, which can be accomplished by comparing the bridge ID, the smallest will be selected. Bridge-id= bridge priority + MAC address. The three switches in the figure all have the default priority, so we should compare the MAC address, it is easy to find that SwitchB is the root bridge. 2. Select the root port on the non-root bridge, which can be completed through comparing root path cost. The smallest will be selected as the root port. 3. Next, select the Designated Port. First, compare the path cost, if the costs happen to be the same, then compare the BID, still the smallest will be selected. Each link has a DP. Based on the exhibit above, we can find DP on each link. The DP on the link between SwitchA and SwitchC is SwitchA’Fa0/1, because it has the smallest MAC address. -
Question 42 of 555
42. Question
Refer to the exhibit. How should the FastEthernet0/1 ports on the 2950 model switches that are shown in the exhibit be configured to allow connectivity between all devices? Correct
Correct
Incorrect
Hint
IN order for multiple VLANs to cross switches, the connection between the switches must be a trunk. The “switchport mode trunk” command is all that is needed, the individual VLANs should not be listed over that trunk interface. -
Question 43 of 555
43. Question
Which three statements about RSTP are true? (Choose three.)Correct
Incorrect
Hint
One big disadvantage of STP is the low convergence which is very important in switched network. To overcome this problem, in 2001, the IEEE with document 802.1w introduced an evolution of the Spanning Tree Protocol: Rapid Spanning Tree Protocol (RSTP), which significantly reduces the convergence time after a topology change occurs in the network. While STP can take 30 to 50 seconds to transit from a blocking state to a forwarding state, RSTP is typically able to respond less than 10 seconds of a physical link failure. RSTP works by adding an alternative port and a backup port compared to STP. These ports are allowed to immediately enter the forwarding state rather than passively wait for the network to converge. RSTP bridge port roles: * Root port – A forwarding port that is the closest to the root bridge in terms of path cost * Designated port – A forwarding port for every LAN segment * Alternate port – A best alternate path to the root bridge. This path is different than using the root port. The alternative port moves to the forwarding state if there is a failure on the designated port for the segment. * Backup port – A backup/redundant path to a segment where another bridge port already connects. The backup port applies only when a single switch has two links to the same segment (collision domain). To have two links to the same collision domain, the switch must be attached to a hub. * Disabled port – Not strictly part of STP, a network administrator can manually disable a port -
Question 44 of 555
44. Question
Refer to the exhibit. A frame on VLAN 1 on switch S1 is sent to switch S2 where the frame is received on VLAN 2. What causes this behavior?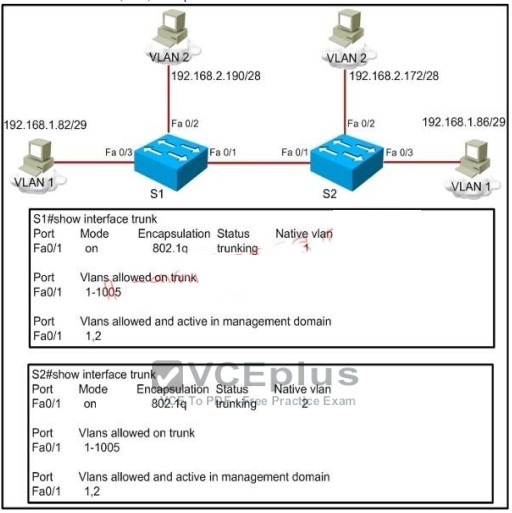 Correct
Correct
Incorrect
Hint
Untagged frames are encapsulated with the native VLAN. In this case, the native VLANs are different so although S1 will tag it as VLAN 1 it will be received by S2. -
Question 45 of 555
45. Question
At which layer of the OSI model is RSTP used to prevent loops?Correct
Incorrect
Hint
RSTP and STP operate on switches and are based on the exchange of Bridge Protocol Data Units (BPDUs) between switches. One of the most important fields in BPDUs is the Bridge Priority in which the MAC address is used to elect the Root Bridge -> RSTP operates at Layer 2 ?Data Link layer -> . -
Question 46 of 555
46. Question
What does a Layer 2 switch use to decide where to forward a received frame?Correct
Incorrect
Hint
When a frame is received, the switch looks at the destination hardware address and finds the interface if it is in its MAC address table. If the address is unknown, the frame is broadcast on all interfaces except the one it was received on. -
Question 47 of 555
47. Question
Correct
Incorrect
Hint
Only non-root bridge can have root port. Fa0/11 is the root port so we can confirm this switch is not the root bridge -> From the output we learn this switch is running Rapid STP, not PVST -> 0017.596d.1580 is the MAC address of this switch, not of the root bridge. The MAC address of the root bridge is 0017.596d.2a00 -> All of the interface roles of the root bridge are designated. SwitchA has one Root port and 1 Alternative port so it is not the root bridge. -
Question 48 of 555
48. Question
Which two benefits are provided by creating VLANs? (Choose two.)Correct
Incorrect
Hint
A VLAN is a switched network that is logically segmented on an organizational basis, by functions, project teams, or applications rather than on a physical or geographical basis. Security: VLANs also improve security by isolating groups. High-security users can be grouped into a VLAN, possible on the same physical segment, and no users outside that VLAN can communicate with them LAN Segmentation VLANs allow logical network topologies to overlay the physical switched infrastructure such that any arbitrary collection of LAN ports can be combined into an autonomous user group or community of interest. The technology logically segments the network into separate Layer 2 broadcast domains whereby packets are switched between ports designated to be within the same VLAN. By containing traffic originating on a particular LAN only to other LANs in the same VLAN, switched virtual networks avoid wasting bandwidth -
Question 49 of 555
49. Question
Which command can be used from a PC to verify the connectivity between hosts that connect through a switch in the same LAN?Correct
Incorrect
Hint
ICMP pings are used to verify connectivity between two IP hosts. Traceroute is used to verify the router hop path traffic will take but in this case since the hosts are in the same LAN there will be no router hops involved. -
Question 50 of 555
50. Question
Based on the network shown in the graphic. Which option contains both the potential networking problem and the protocol or setting that should be used to prevent the problem?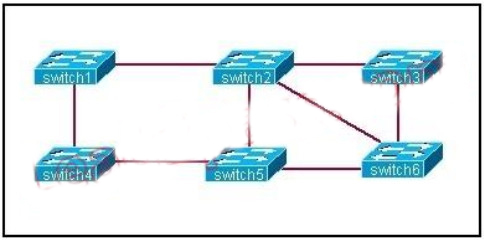 Correct
Correct
Incorrect
Hint
The Spanning-Tree Protocol (STP) prevents loops from being formed when switches or bridges are interconnected via multiple paths. Spanning-Tree Protocol implements the 802.1D IEEE algorithm by exchanging BPDU messages with other switches to detect loops, and then removes the loop by shutting down selected bridge interfaces. This algorithm guarantees that there is one and only one active path between two network devices -
Question 51 of 555
51. Question
Refer to the exhibit. Which two statements are true about interVLAN routing in the topology that is shown in the exhibit? (Choose two.)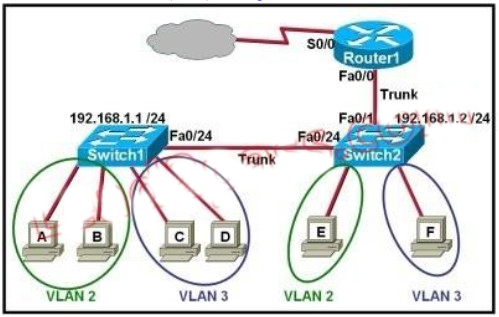 Correct
Correct
Incorrect
-
Question 52 of 555
52. Question
Which two of these are characteristics of the 802.1Q protocol? (Choose two.)Correct
Incorrect
Hint
802.1Q protocol, or Virtual Bridged Local Area Networks protocol, mainly stipulates the realization of the VLAN. 802.1Q is a standardized relay method that inserts 4 bytes field into the original Ethernet frame and re-calculate the FCS. 802.1Q frame relay supports two types of frame: marked and non-marked. Non-marked frame carries no VLAN identification information. -
Question 53 of 555
53. Question
Refer to the exhibit. Each of these four switches has been configured with a hostname, as well as being configured to run RSTP. No other configuration changes have been made. Which three of these show the correct RSTP port roles for the indicated switches and interfaces? (Choose three.)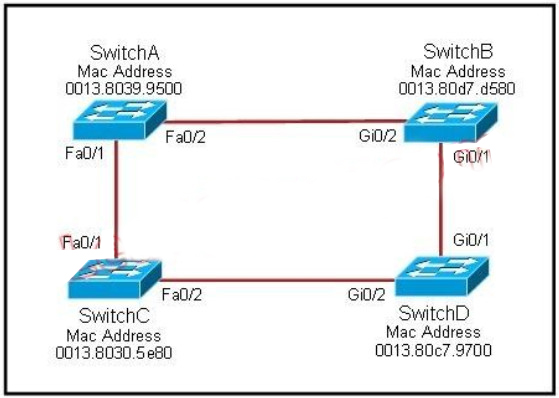 Correct
Correct
Incorrect
Hint
The question says "no other configuration changes have been made" so we can understand these switches have the same bridge priority. Switch C has lowest MAC address so it will become root bridge and 2 of its ports (Fa0/1 & Fa0/2) will be designated ports. Because SwitchC is the root bridge so the 2 ports nearest SwitchC on SwitchA (Fa0/1) and SwitchD (Gi0/2) will be root ports.. Now we come to the most difficult part of this question: SwitchB must have a root port so which port will it choose? To answer this question we need to know about STP cost and port cost. In general, "cost" is calculated based on bandwidth of the link. The higher the bandwidth on a link, the lower the value of its cost. Below are the cost values you should memorize: SwitchB will choose the interface with lower cost to the root bridge as the root port so we must calculate the cost on interface Gi0/1 & Gi0/2 of SwitchB to the root bridge. This can be calculated from the "cost to the root bridge" of each switch because a switch always advertises its cost to the root bridge in its BPDU. The receiving switch will add its local port cost value to the cost in the BPDU. One more thing to notice is that a root bridge always advertises the cost to the root bridge (itself) with an initial value of 0.
Now let's have a look at the topology again
SwitchB will choose the interface with lower cost to the root bridge as the root port so we must calculate the cost on interface Gi0/1 & Gi0/2 of SwitchB to the root bridge. This can be calculated from the "cost to the root bridge" of each switch because a switch always advertises its cost to the root bridge in its BPDU. The receiving switch will add its local port cost value to the cost in the BPDU. One more thing to notice is that a root bridge always advertises the cost to the root bridge (itself) with an initial value of 0.
Now let's have a look at the topology again
 SwitchC advertises its cost to the root bridge with a value of 0. Switch D adds 4 (the cost value of 1Gbps link) and advertises this value (4) to SwitchB. SwitchB adds another 4 and learns that it can reach SwitchC via Gi0/1 port with a total cost of 8. The same process happens for SwitchA
and SwitchB learns that it can reach SwitchC via Gi0/2 with a total cost of 23 -> Switch B chooses Gi0/1 as its root port -> Now our last task is to identify the port roles of the ports between SwitchA & SwitchB. It is rather
easy as the MAC address of SwitchA is lower than that of SwitchB so Fa0/2 of SwitchA will be designated port while Gi0/2 of SwitchB will be alternative port.
Below summaries all the port roles of these switches:
SwitchC advertises its cost to the root bridge with a value of 0. Switch D adds 4 (the cost value of 1Gbps link) and advertises this value (4) to SwitchB. SwitchB adds another 4 and learns that it can reach SwitchC via Gi0/1 port with a total cost of 8. The same process happens for SwitchA
and SwitchB learns that it can reach SwitchC via Gi0/2 with a total cost of 23 -> Switch B chooses Gi0/1 as its root port -> Now our last task is to identify the port roles of the ports between SwitchA & SwitchB. It is rather
easy as the MAC address of SwitchA is lower than that of SwitchB so Fa0/2 of SwitchA will be designated port while Gi0/2 of SwitchB will be alternative port.
Below summaries all the port roles of these switches:
 + DP: Designated Port (forwarding state)
+ RP: Root Port (forwarding state)
+ DP: Designated Port (forwarding state)
+ RP: Root Port (forwarding state) -
Question 54 of 555
54. Question
What is one benefit of PVST+?Correct
Incorrect
Hint
The PVST+ provides Layer 2 load-balancing for the VLAN on which it runs. You can create different logical topologies by using the VLANs on your network to ensure that all of your links are used but that no one link is oversubscribed. Each instance of PVST+ on a VLAN has a single root switch. This root switch propagates the spanning-tree information associated with that VLAN to all other switches in the network. Because each switch has the same information about the network, this process ensures that the network topology is maintained and optimized per VLAN. http://www.cisco.com/en/US/docs/switches/lan/catalyst3750x_3560x/software/release/12.2_55_se/configuration/guide/swstp.html -
Question 55 of 555
55. Question
Refer to the exhibit. The network administrator normally establishes a Telnet session with the switch from host A . However, host A is unavailable. The administrator's attempt to telnet to the switch from host B fails, but pings to the other two hosts are successful. What is the issue?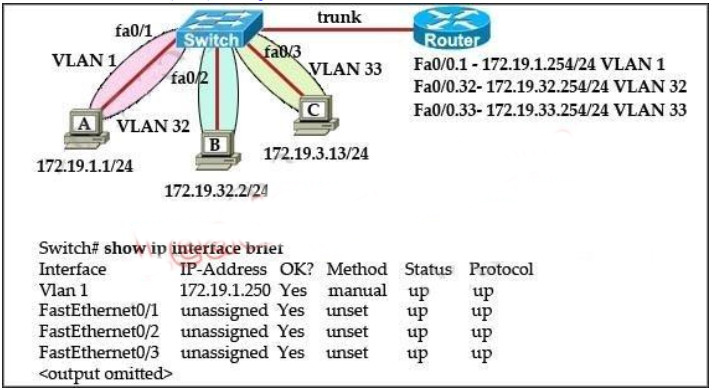 Correct
Correct
Incorrect
Hint
Ping was successful form host B to other hosts because of intervlan routing configured on router. But to manage switch via telnet the VLAN32 on the switch needs to be configured interface vlan32 along with ip address and its appropriate default-gateway address. Since VLAN1 interface is already configure on switch Host A was able to telnet switch. -
Question 56 of 555
56. Question
Which are valid modes for a switch port used as a VLAN trunk? (Choose three.)Correct
Incorrect
-
Question 57 of 555
57. Question
Refer to the exhibit. Which switch provides the spanning-tree designated port role for the network segment that services the printers?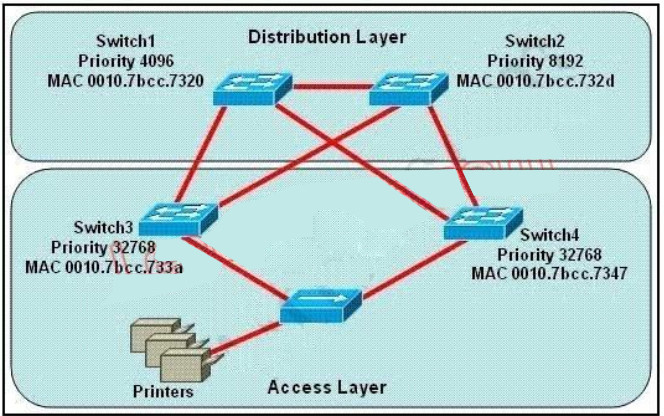 Correct
Correct
Incorrect
Hint
Printers are connected by hubs. Decide the switch that provides the spanning-tree designated port role between Switch3 and Switch4. They have the same priority 32768. Compare their MAC addresses. Switch3 with a smaller MAC address will provide a designated port for printers. -
Question 58 of 555
58. Question
Refer to Exhibit. How many broadcast domains are shown in the graphic assuming only the default VLAN is configured on the switches?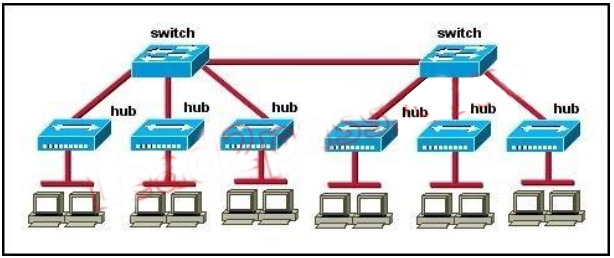 Correct
Correct
Incorrect
Hint
Only router can break up broadcast domains but in this exhibit no router is used so there is only 1 broadcast domain. For your information, there are 7 collision domains in this exhibit (6 collision domains between hubs & switches + 1 collision between the two switches). -
Question 59 of 555
59. Question
Which three of these statements regarding 802.1Q trunking are correct? (Choose three.)Correct
Incorrect
Hint
By default, 802.1Q trunk defined Native VLAN in order to forward unmarked frame. Switches can forward Layer 2 frame from Native VLAN on unmarked trunks port. Receiver switches will transmit all unmarked packets to Native VLAN. Native VLAN is the default VLAN configuration of port. Note for the 802.1Q trunk ports between two devices, the same Native VLAN configuration is required on both sides of the link. If the Native VLAN in 802.1Q trunk ports on same trunk link is properly configured, it could lead to layer 2 loops. The 802.1Q trunk link transmits VLAN information through Ethernet. -
Question 60 of 555
60. Question
Refer to the exhibit. The output that is shown is generated at a switch. Which three statements are true? (Choose three.)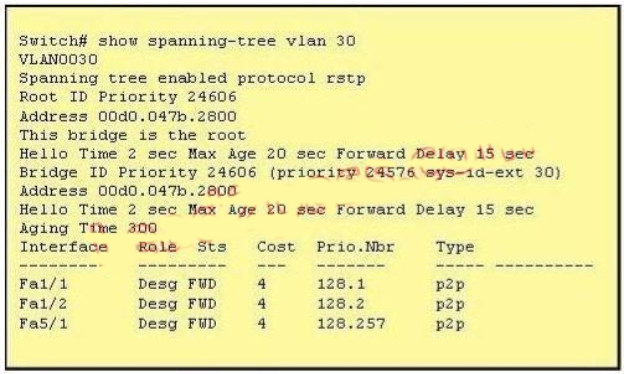 Correct
Correct
Incorrect
Hint
From the output, we see that all ports are in Designated role (forwarding state). The command "show spanning-tree vlan 30 only shows us information about VLAN 30. We don't know how many VLAN exists in this switch -> The bridge priority of this switch is 24606 which is lower than the default value bridge priority 32768 -> . All three interfaces on this switch have the connection type "p2p", which means Point-to-point environment ?not a shared media >; The only thing we can specify is this switch is the root bridge for VLAN 3o but we can not guarantee it is also the root bridge for other VLANs -> -
Question 61 of 555
61. Question
Refer to the exhibit. At the end of an RSTP election process, which access layer switch port will assume the discarding role?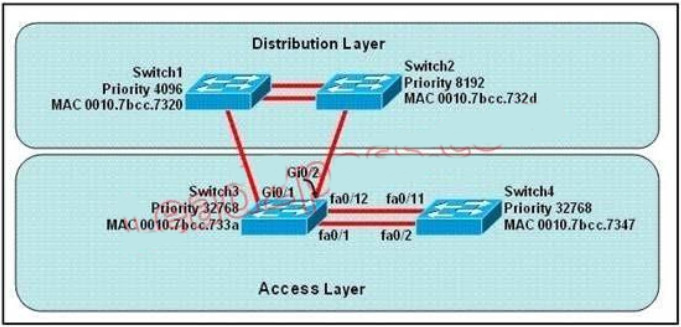 Correct
Correct
Incorrect
Hint
In this question, we only care about the Access Layer switches (Switch3 & 4). Switch 3 has a lower bridge ID than Switch 4 (because the MAC of Switch3 is smaller than that of Switch4) so both ports of Switch3 will be in forwarding state. The alternative port will surely belong to Switch4. Switch4 will need to block one of its ports to avoid a bridging loop between the two switches. But how does Switch4 select its blocked port? Well, the answer is based on the BPDUs it receives from Switch3. A BPDU is superior than another if it has: 1. A lower Root Bridge ID 2. A lower path cost to the Root 3. A lower Sending Bridge ID 4. A lower Sending Port ID These four parameters are examined in order. In this specific case, all the BPDUs sent by Switch3 have the same Root Bridge ID, the same path cost to the Root and the same Sending Bridge ID. The only parameter left to select the best one is the Sending Port ID (Port ID = port priority + port index). In this case the port priorities are equal because they use the default value, so Switch4 will compare port index values, which are unique to each port on the switch, and because Fa0/12 is inferior to Fa0/1, Switch4 will select the port connected with Fa0/1 (of Switch3) as its root port and block the other port -> Port fa0/11 of Switch4 will be blocked (discarding role). -
Question 62 of 555
62. Question
Which term describes a spanning-tree network that has all switch ports in either the blocking or fowarding state?Correct
Incorrect
Hint
Spanning Tree Protocol convergence (Layer 2 convergence) happens when bridges and switches have transitioned to either the forwarding or blocking state. When layer 2 is converged, root bridge is elected and all port roles (Root, Designated and Non-Designated) in all switches are selected. -
Question 63 of 555
63. Question
What are the possible trunking modes for a switch port? (Choose three.)Correct
Incorrect
-
Question 64 of 555
64. Question
Which two of these statements regarding RSTP are correct? (Choose two.)Correct
Incorrect
Hint
When network topology changes, rapid spanning tree protocol (IEEE802.1W, referred to as RSTP) will speed up significantly the speed to re-calculate spanning tree. RSTP not only defines the role of other ports: alternative port and backup port, but also defines status of 3 ports: discarding status, learning status, forwarding status. RSTP is 802.1D standard evolution, not revolution. It retains most of the parameters, and makes no changes. -
Question 65 of 555
65. Question
Correct
Incorrect
Hint
Carefully observe the information given after command show. Fa0/1 is connected to Switch2, seven MAC addresses correspond to Fa0/1, and these MAC are in different VLAN. From this we know that Fa0/1 is the trunk interface. From the information given by show cdp neighbors we find that there is no Fa0/5 in CDP neighbor. However, F0/5 corresponds to two MAC addresses in the same VLAN. Thus we know that Fa0/5 is connected to a Hub. Based on the output shown, there are multiple MAC addresses from different VLANs attached to the FastEthernet 0/1 interface. Only trunks are able to pass information from devices in multiple VLANs. -
Question 66 of 555
66. Question
Three switches are connected to one another via trunk ports. Assuming the default switch configuration, which switch is elected as the root bridge for the spanning-tree instance of VLAN 1?Correct
Incorrect
Hint
Each switch in your network will have a Bridge ID Priority value, more commonly referred to as a BID. This BID is a combination of a default priority value and the switch's MAC address, with the priority value listed first. The lowest BID will win the election process. For example, if a Cisco switch has the default priority value of 32,768 and a MAC address of 11- 22-33-44-55-66, the BID would be 32768:11-22-33-44-55-66. Therefore, if the switch priority is left at the default, the MAC address is the deciding factor in the root bridge election. -
Question 67 of 555
67. Question
What are three advantages of VLANs? (Choose three.)Correct
Incorrect
Hint
VLAN technology is often used in practice, because it can better control layer2 broadcast to improve network security. This makes network more flexible and scalable. Packet filtering is a function of firewall instead of VLAN. -
Question 68 of 555
68. Question
Which two benefits are provided by using a hierarchical addressing network addressing scheme? (Choose two.)Correct
Incorrect
Hint
Here are some of the benefits of hierarchical addressing: Reference: http://www.ciscopress.com/articles/article.asp?p=174107 -
Question 69 of 555
69. Question
What is the alternative notation for the IPv6 address B514:82C3:0000:0000:0029:EC7A:0000:EC72?Correct
Incorrect
Hint
There are two ways that an IPv6 address can be additionally compressed: compressing leading zeros and substituting a group of consecutive zeros with a single double colon (::). Both of these can be used in any number of combinations to notate the same address. It is important to note that the double colon (::) can only be used once within a single IPv6 address notation. So, the extra 0's can only be compressed once. -
Question 70 of 555
70. Question
Refer to the diagram. All hosts have connectivity with one another. Which statements describe the addressing scheme that is in use in the network? (Choose three.)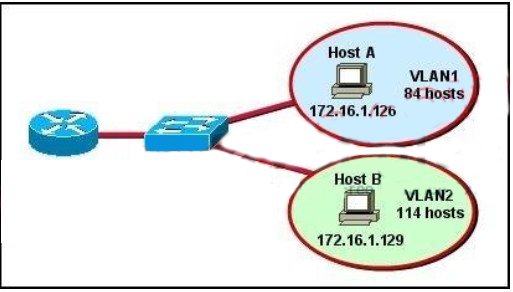 Correct
Correct
Incorrect
Hint
The subnet mask in use is 255.255.255.128: This is subnet mask will support up to 126 hosts, which is needed. The IP address 172.16.1.25 can be assigned to hosts in VLAN1: The usable host range in this subnet is 172.16.1.1-172.16.1.126 The LAN interface of the router is configured with multiple IP addresses: The router will need 2 subinterfaces for the single physical interface, one with an IP address that belongs in each VLAN -
Question 71 of 555
71. Question
Which two statements describe characteristics of IPv6 unicast addressing? (Choose two.)Correct
Incorrect
-
Question 72 of 555
72. Question
The network administrator has been asked to give reasons for moving from IPv4 to IPv6. What are two valid reasons for adopting IPv6 over IPv4? (Choose two.)Correct
Incorrect
Hint
IPv6 does not use broadcasts, and autoconfiguration is a feature of IPV6 that allows for hosts to automatically obtain an IPv6 address. -
Question 73 of 555
73. Question
An administrator must assign static IP addresses to the servers in a network. For network 192.168.20.24/29, the router is assigned the first usable host address while the sales server is given the last usable host address. Which of the following should be entered into the IP properties box for the sales server?Correct
Incorrect
Hint
For the 192.168.20.24/29 network, the usable hosts are 192.168.24.25 (router) ?192.168.24.30 (used for the sales server). -
Question 74 of 555
74. Question
Which subnet mask would be appropriate for a network address range to be subnetted for up to eight LANs, with each LAN containing 5 to 26 hosts?Correct
Incorrect
Hint
For a class C network, a mask of 255.255.255.224 will allow for up to 8 networks with 32 IP addresses each (30 usable). -
Question 75 of 555
75. Question
How many bits are contained in each field of an IPv6 address?Correct
Incorrect
Hint
An IPv6 address is represented as eight groups of four hexadecimal digits, each group representing 16 bits (two octets). The groups are separated by colons (:). An example of an IPv6 address is 2001:0db8:85a3:0000:0000:8a2e:0370:7334. -
Question 76 of 555
76. Question
What are three approaches that are used when migrating from an IPv4 addressing scheme to an IPv6 scheme. (Choose three.)Correct
Incorrect
Hint
Several methods are used terms of migration including tunneling, translators, and dual stack. Tunnels are used to carry one protocol inside another, while translators simply translate IPv6 packets into IPv4 packets. Dual stack uses a combination of both native IPv4 and IPv6. With dual stack, devices are able to run IPv4 and IPv6 together and if IPv6 communication is possible that is the preferred protocol. Hosts can simultaneously reach IPv4 and IPv6 content. -
Question 77 of 555
77. Question
Refer to the exhibit. In this VLSM addressing scheme, what summary address would be sent from router A?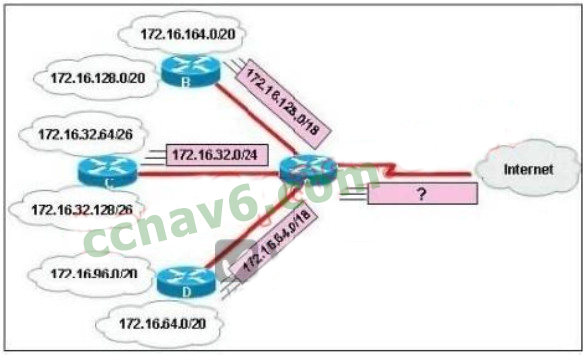 Correct
Correct
Incorrect
Hint
Router A receives 3 subnets: 172.16.64.0/18, 172.16.32.0/24 and 172.16.128.0/18. All these 3 subnets have the same form of 172.16.x.x so our summarized subnet must be also in that form -> Only A, B or . The smallest subnet mask of these 3 subnets is /18 so our summarized subnet must also have its subnet mask equal or smaller than /18. -> Only answer A has these 2 conditions -> . -
Question 78 of 555
78. Question
How is an EUI-64 format interface ID created from a 48-bit MAC address?Correct
Incorrect
Hint
The modified EUI-64 format interface identifier is derived from the 48-bit link-layer (MAC) address by inserting the hexadecimal number FFFE between the upper three bytes (OUI field) and the lower three bytes (serial number) of the link layer address. -
Question 79 of 555
79. Question
Refer to the exhibit. What is the most efficient summarization that R1 can use to advertise its networks to R2?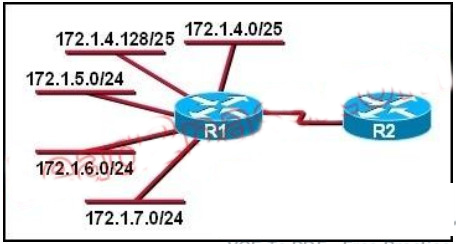 Correct
Correct
Incorrect
Hint
The 172.1.4.0/22 subnet encompasses all routes from the IP range 172.1.4.0 ?172.1.7.255. -
Question 80 of 555
80. Question
Which option is a valid IPv6 address?Correct
Incorrect
Hint
An IPv6 address is represented as eight groups of four hexadecimal digits, each group representing 16 bits (two octets). The groups are separated by colons (:). An example of an IPv6 address is 2001:0db8:85a3:0000:0000:8a2e:0370:7334. The leading 0's in a group can be collapsed using ::, but this can only be done once in an IP address. -
Question 81 of 555
81. Question
Which three are characteristics of an IPv6 anycast address? (Choose three.)Correct
Incorrect
Hint
A new address type made specifically for IPv6 is called the Anycast Address. These IPv6 addresses are global addresses, these addresses can be assigned to more than one interface unlike an IPv6 unicast address. Anycast is designed to send a packet to the nearest interface that is apart of that anycast group. The sender creates a packet and forwards the packet to the anycast address as the destination address which goes to the nearest router. The nearest router or interface is found by using the metric of a routing protocol currently running on the network. However in a LAN setting the nearest interface is found depending on the order the neighbors were learned. The anycast packet in a LAN setting forwards the packet to the neighbor it learned about first. -
Question 82 of 555
82. Question
A national retail chain needs to design an IP addressing scheme to support a nationwide network. The company needs a minimum of 300 sub-networks and a maximum of 50 host addresses per subnet. Working with only one Class B address, which of the following subnet masks will support an appropriate addressing scheme? (Choose two.)Correct
Incorrect
Hint
Subnetting is used to break the network into smaller more efficient subnets to prevent excessive rates of Ethernet packet collision in a large network. Such subnets can be arranged hierarchically, with the organization's network address space (see also Autonomous System) partitioned into a tree-like structure. Routers are used to manage traffic and constitute borders between subnets. A routing prefix is the sequence of leading bits of an IP address that precede the portion of the address used as host identifier. In IPv4 networks, the routing prefix is often expressed as a "subnet mask", which is a bit mask covering the number of bits used in the prefix. An IPv4 subnet mask is frequently expressed in quad-dotted decimal representation, e.g., 255.255.255.0 is the subnet mask for the 192.168.1.0 network with a 24-bit routing prefix (192.168.1.0/24). -
Question 83 of 555
83. Question
Refer to the exhibit. A network administrator is adding two new hosts to Switch A . Which three values could be used for the configuration of these hosts? (Choose three.) Correct
Correct
Incorrect
-
Question 84 of 555
84. Question
Which IPv6 address is the all-router multicast group?Correct
Incorrect
Hint
Well-known IPv6 multicast addresses: Address Description ff02::1 All nodes on the local network segment ff02::2 All routers on the local network segment -
Question 85 of 555
85. Question
Refer to the exhibit. Which address range efficiently summarizes the routing table of the addresses for router Main? Correct
Correct
Incorrect
Hint
The 172.16.0.0./20 network is the best option as it includes all networks from 172.16.0.0 - 172.16.16.0 and does it more efficiently than the /16 and /18 subnets. The /21 subnet will not include all the other subnets in this one single summarized address. -
Question 86 of 555
86. Question
Which IPv6 address is valid?Correct
Incorrect
Hint
An IPv6 address is represented as eight groups of four hexadecimal digits, each group representing 16 bits (two octets). The groups are separated by colons (:). An example of an IPv6 address is 2001:0db8:85a3:0000:0000:8a2e:0370:7334. The leading 0's in a group can be collapsed using ::, but this can only be done once in an IP address. -
Question 87 of 555
87. Question
Which command can you use to manually assign a static IPv6 address to a router interface?Correct
Incorrect
Hint
To assign an IPv6 address to an interface, use the "ipv6 address" command and specify the IP address you wish to use. -
Question 88 of 555
88. Question
Which of these represents an IPv6 link-local address?Correct
Incorrect
Hint
In the Internet Protocol Version 6 (IPv6), the address block fe80::/10 has been reserved for linklocal unicast addressing. The actual link local addresses are assigned with the prefix fe80::/64. They may be assigned by automatic (stateless) or stateful (e.g. manual) mechanisms. -
Question 89 of 555
89. Question
The network administrator is asked to configure 113 point-to-point links. Which IP addressing scheme defines the address range and subnet mask that meet the requirement and waste the fewest subnet and host addresses?Correct
Incorrect
Hint
We need 113 point-to-point links which equal to 113 sub-networks < 128 so we need to borrow 7 bits (because 2^7 = 128). The network used for point-to-point connection should be /30. So our initial network should be 30 ?7 = 23. So 10.10.0.0/23 is the correct answer. You can understand it more clearly when writing it in binary form: /23 = 1111 1111.1111 1110.0000 0000 /30 = 1111 1111.1111 1111.1111 1100 (borrow 7 bits) -
Question 90 of 555
90. Question
A Cisco router is booting and has just completed the POST process. It is now ready to find and load an IOS image. What function does the router perform next?Correct
Incorrect
Hint
Default (normal) Boot SequencePower on Router - Router does POST - Bootstrap starts IOS load - Check configuration registerto see what mode the router should boot up in (usually 0x2102 to read startup-config in NVRAM / or 0x2142 to start in "setup-mode") - check the startup-config file in NVRAM for boot-system commands - load IOS from Flash. -
Question 91 of 555
91. Question
Correct
Incorrect
Hint
The Maximum Transmission Unit (MTU) defines the maximum Layer 3 packet (in bytes) that the layer can pass onwards. -
Question 92 of 555
92. Question
On a corporate network, hosts on the same VLAN can communicate with each other, but they are unable to communicate with hosts on different VLANs. What is needed to allow communication between the VLANs?Correct
Incorrect
Hint
Different VLANs can't communicate with each other , they can communicate with the help of Layer3 router. Hence , it is needed to connect a router to a switch , then make the sub-interface on the router to connect to the switch, establishing Trunking links to achieve communications of devices which belong to different VLANs. When using VLANs in networks that have multiple interconnected switches, you need to use VLAN trunking between the switches. With VLAN trunking, the switches tag each frame sent between switches so that the receiving switch knows to what VLAN the frame belongs. End user devices connect to switch ports that provide simple connectivity to a single VLAN each. The attached devices are unaware of any VLAN structure. By default, only hosts that are members of the same VLAN can communicate. To change this and allow inter-VLAN communication, you need a router or a layer 3 switch. Here is the example of configuring the router for inter-vlan communication RouterA(config)#int f0/0.1 RouterA(config-subif)#encapsulation ? dot1Q IEEE 802.1Q Virtual LAN RouterA(config-subif)#encapsulation dot1Q or isl VLAN ID RouterA(config-subif)# ip address x.x.x.x y.y.y.y -
Question 93 of 555
93. Question
Which command displays CPU utilization?Correct
Incorrect
Hint
The "show process" (in fact, the full command is "show processes") command gives us lots of information about each process but in fact it is not easy to read. Below shows the output of this command (some next pages are omitted) A more friendly way to check the CPU utilization is the command "show processes cpu history", in which the total CPU usage on the router over a period of time: one minute, one hour, and 72 hours are clearly shown:
A more friendly way to check the CPU utilization is the command "show processes cpu history", in which the total CPU usage on the router over a period of time: one minute, one hour, and 72 hours are clearly shown:
 + The Y-axis of the graph is the CPU utilization.+ The X-axis of the graph is the increment within the period displayed in the graph
For example, from the last graph (last 72 hours) we learn that the highest CPU utilization within 72 hours is 37% about six hours ago.
+ The Y-axis of the graph is the CPU utilization.+ The X-axis of the graph is the increment within the period displayed in the graph
For example, from the last graph (last 72 hours) we learn that the highest CPU utilization within 72 hours is 37% about six hours ago. -
Question 94 of 555
94. Question
What two things will a router do when running a distance vector routing protocol? (Choose two.)Correct
Incorrect
Hint
Distance means how far and Vector means in which direction. Distance Vector routing protocols pass periodic copies of routing table to neighbor routers and accumulate distance vectors. In distance vector routing protocols, routers discover the best path to destination from each neighbor. The routing updates proceed step by step from router to router. -
Question 95 of 555
95. Question
Which command is used to display the collection of OSPF link states?Correct
Incorrect
Hint
The "show ip ospf database" command displays the link states. Here is an example: Here is the lsa database on R2. R2#show ip ospf database OSPF Router with ID (2.2.2.2) (Process ID 1) Router Link States (Area 0) Link ID ADV Router Age Seq# Checksum Link count2.2.2.2 2.2.2.2 793 0x80000003 0x004F85 210.4.4.4 10.4.4.4 776 0x80000004 0x005643 1111.111.111.111 111.111.111.111 755 0x80000005 0x0059CA 2133.133.133.133 133.133.133.133 775 0x80000005 0x00B5B1 2 Net Link States (Area 0) Link ID ADV Router Age Seq# Checksum10.1.1.1 111.111.111.111 794 0x80000001 0x001E8B10.2.2.3 133.133.133.133 812 0x80000001 0x004BA910.4.4.1 111.111.111.111 755 0x80000001 0x007F1610.4.4.3 133.133.133.133 775 0x80000001 0x00C31F -
Question 96 of 555
96. Question
Refer to the exhibit. The technician wants to upload a new IOS in the router while keeping the existing IOS. What is the maximum size of an IOS file that could be loaded if the original IOS is also kept in flash?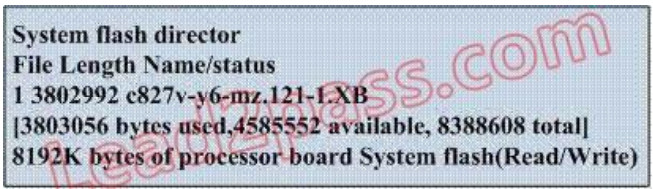 Correct
Correct
Incorrect
Hint
In this example, there are a total of 8 MB, but 3.8 are being used already, so another file as large as 4MB can be loaded in addition to the original file. -
Question 97 of 555
97. Question
If IP routing is enabled, which two commands set the gateway of last resort to the default gateway? (Choose two.)Correct
Incorrect
Hint
Both the "ip default-network" and "ip route 0.0.0.0 0.0.0.0 (next hop)" commands can be used to set the default gateway in a Cisco router. -
Question 98 of 555
98. Question
Refer to the exhibit. The two exhibited devices are the only Cisco devices on the network. The serial network between the two devices has a mask of 255.255.255.252. Given the output that is shown, what three statements are true of these devices? (Choose three.)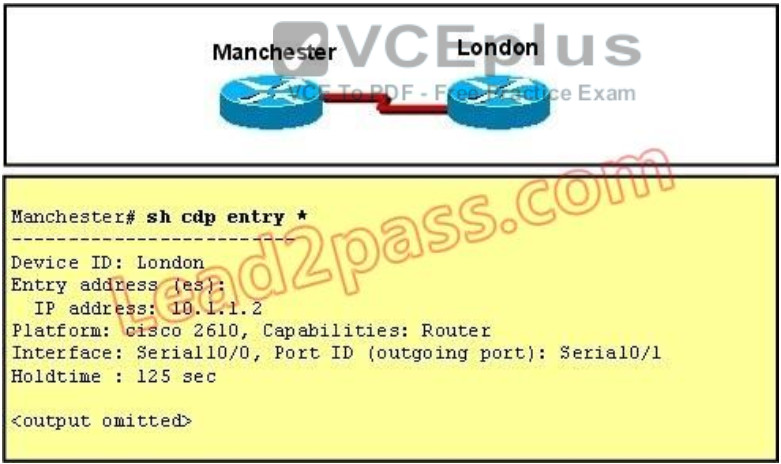 Correct
Correct
Incorrect
Hint
From the output, we learn that the IP address of the neighbor router is 10.1.1.2 and the question stated that the subnet mask of the network between two router is 255.255.255.252. Therefore there are only 2 available hosts in this network (22 ?2 = 2). So we can deduce the ip address (of the serial interface) of Manchester router is 10.1.1.1 -> The platform of the neighbor router is cisco 2610, as shown in the output -> Maybe the most difficult choice of this question is the answer E or F. Please notice that "Interface" refers to the local port on the local router, in this case it is the port of Manchester router, and "Port ID (outgoing port)" refers to the port on the neighbor router. -
Question 99 of 555
99. Question
Which parameter would you tune to affect the selection of a static route as a backup, when a dynamic protocol is also being used?Correct
Incorrect
Hint
By default the administrative distance of a static route is 1, meaning it will be preferred over all dynamic routing protocols. If you want to have the dynamic routing protocol used and have the static route be used only as a backup, you need to increase the AD of the static route so that it is higher than the dynamic routing protocol. -
Question 100 of 555
100. Question
Refer to the exhibit. A network associate has configured OSPF with the command: City(config-router)# network 192.168.12.64 0.0.0.63 area 0 After completing the configuration, the associate discovers that not all the interfaces are participating in OSPF. Which three of the interfaces shown in the exhibit will participate in OSPF according to this configuration statement? (Choose three.)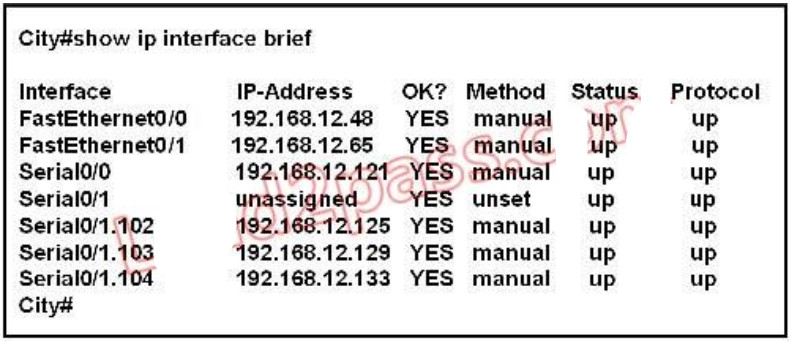 Correct
Correct
Incorrect
Hint
The "network 192.168.12.64 0.0.0.63 equals to network 192.168.12.64/26. This network has: + Increment: 64 (/26= 1111 1111.1111 1111.1111 1111.1100 0000) + Network address: 192.168.12.64 + Broadcast address: 192.168.12.127 Therefore all interface in the range of this network will join OSPF -
Question 101 of 555
101. Question
Refer to the exhibit. The Lakeside Company has the internetwork in the exhibit. The administrator would like to reduce the size of the routing table on the Central router. Which partial routing table entry in the Central router represents a route summary that represents the LANs in Phoenix but no additional subnets?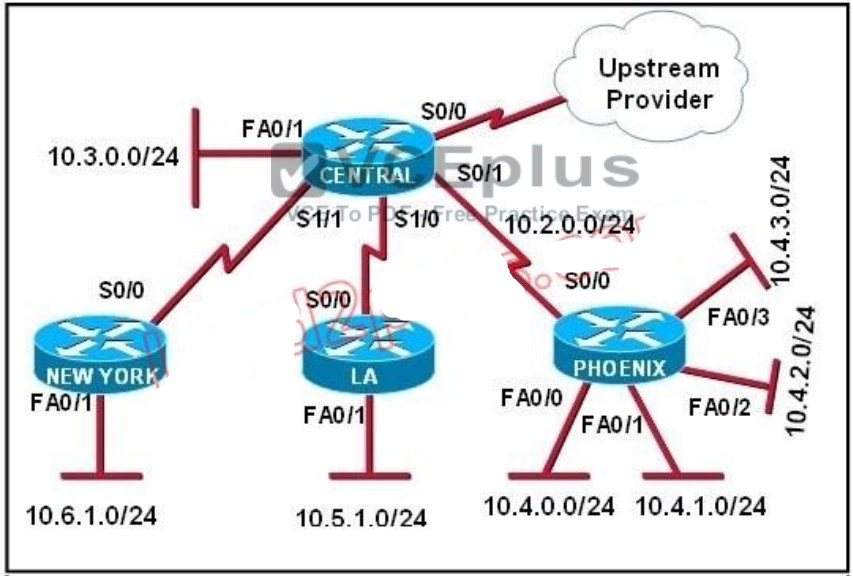 Correct
Correct
Incorrect
Hint
The 10.4.0.0/22 route includes 10.4.0.0/24, 10.4.1.0/24, 10.4.2.0/24 and 10.4.3.0/24 only. -
Question 102 of 555
102. Question
Refer to the graphic. A static route to the 10.5.6.0/24 network is to be configured on the HFD router. Which commands will accomplish this? (Choose two.) Correct
Correct
Incorrect
Hint
The simple syntax of static route: ip route destination-network-address subnet-mask {next-hop-IP-address | exit-interface} + destination-network-address: destination network address of the remote network + subnet mask: subnet mask of the destination network + next-hop-IP-address: the IP address of the receiving interface on the next-hop router + exit-interface: the local interface of this router where the packets will go out In the statement "ip route 10.5.6.0 255.255.255.0 fa0/0: + 10.5.6.0 255.255.255.0: the destination network +fa0/0: the exit-interface -
Question 103 of 555
103. Question
Before installing a new, upgraded version of the IOS, what should be checked on the router, and which command should be used to gather this information? (Choose two.)Correct
Incorrect
Hint
When upgrading new version of the IOS we need to copy the IOS to the Flash so first we have to check if the Flash has enough memory or not. Also running the new IOS may require more RAM than the older one so we should check the available RAM too. We can check both with the "show version" command. -
Question 104 of 555
104. Question
Which command reveals the last method used to powercycle a router?Correct
Incorrect
-
Question 105 of 555
105. Question
Which command would you use on a Cisco router to verify the Layer 3 path to a host?Correct
Incorrect
Hint
In computing, traceroute is a computer network diagnostic tool for displaying the route (path) and measuring transit delays of packets across an Internet Protocol (IP) network. The history of the route is recorded as the round-trip times of the packets received from each successive host (remote node) in the route (path); the sum of the mean times in each hop indicates the total time spent to establish the connection. Traceroute proceeds unless all (three) sent packets are lost more than twice, then the connection is lost and the route cannot be evaluated. Ping, on the other hand, only computes the final round-trip times from the destination point. -
Question 106 of 555
106. Question
What information does a router running a link-state protocol use to build and maintain its topological database? (Choose two.)Correct
Incorrect
Hint
Neighbor discovery is the first step in getting a link state environment up and running. In keeping with the friendly neighbor terminology, a Hello protocol is used for this step. The protocol will define a Hello packet format and a procedure for exchanging the packets and processing the information the packets contain. After the adjacencies are established, the routers may begin sending out LSAs. As the term flooding implies, the advertisements are sent to every neighbor. In turn, each received LSA is copied and forwarded to every neighbor except the one that sent the LSA. -
Question 107 of 555
107. Question
Which statements describe the routing protocol OSPF? (Choose three.)Correct
Incorrect
Hint
The OSPF protocol is based on link-state technology, which is a departure from the Bellman-Ford vector based algorithms used in traditional Internet routing protocols such as RIP. OSPF has introduced new concepts such as authentication of routing updates, Variable Length Subnet Masks (VLSM), route summarization, and so forth. OSPF uses flooding to exchange link-state updates between routers. Any change in routing information is flooded to all routers in the network. Areas are introduced to put a boundary on the explosion of link-state updates. Flooding and calculation of the Dijkstra algorithm on a router is limited to changes within an area. -
Question 108 of 555
108. Question
Refer to the exhibit. A network administrator configures a new router and enters the copy startupconfig running-config command on the router. The network administrator powers down the router and sets it up at a remote location. When the router starts, it enters the system configuration dialog as shown. What is the cause of the problem?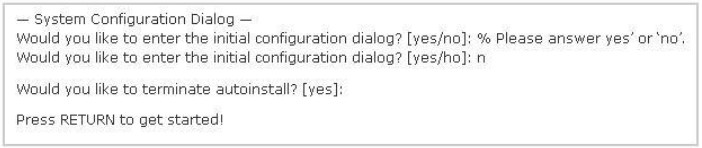 Correct
Correct
Incorrect
Hint
The "System Configuration Dialog" appears only when no startup configuration file is found. The network administrator has made a mistake because the command "copy startup-config runningconfig" will copy the startup config (which is empty) over the running config (which is configured by the administrator). So everything configured was deleted. Note: We can tell the router to ignore the start-up configuration on the next reload by setting the register to 0?142. This will make the "System Configuration Dialog" appear at the next reload. -
Question 109 of 555
109. Question
Correct
Incorrect
Hint
This question is to examine the show int command. According to the information provided in the exhibit, we can know that the data link protocol used in this network is the Frame Relay protocol. "LMI enq sent..." -
Question 110 of 555
110. Question
What is the default administrative distance of OSPF?Correct
Incorrect
Hint
Administrative distance is the feature that routers use in order to select the best path when there are two or more different routes to the same destination from two different routing protocols. Administrative distance defines the reliability of a routing protocol. Each routing protocol is prioritized in order of most to least reliable (believable) with the help of an administrative distance value. Default Distance Value Table This table lists the administrative distance default values of the protocols that Cisco supports: Route Source Default Distance Values Connected interface Static route Enhanced Interior Gateway Routing Protocol (EIGRP) summary route External Border Gateway Protocol (BGP) Internal EIGRP IGRP OSPF Intermediate System-to-Intermediate System (IS-IS) Routing Information Protocol (RIP) Exterior Gateway Protocol (EGP) On Demand Routing (ODR) External EIGRP Internal BGP Unknown -
Question 111 of 555
111. Question
Which characteristics are representative of a link-state routing protocol? (Choose three.)Correct
Incorrect
Hint
Each of routers running link-state routing protocol learns paths to all the destinations in its "area" so we can say although it is a bit unclear. Link-state routing protocols generate routing updates only (not the whole routing table) when a change occurs in the network topology so Link-state routing protocol like OSPF uses Dijkstra algorithm to calculate the shortest path -> . Unlike Distance vector routing protocol (which utilizes frequent periodic updates), link-state routing protocol utilizes event-triggered updates (only sends update when a change occurs) -> -
Question 112 of 555
112. Question
Refer to the exhibit. Based on the exhibited routing table, how will packets from a host within the 192.168.10.192/26 LAN be forwarded to 192.168.10.1?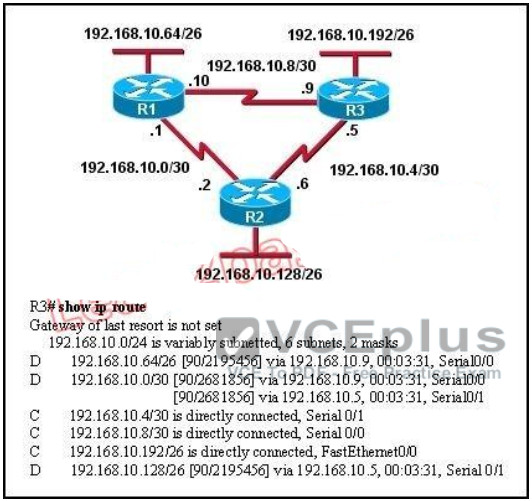 Correct
Correct
Incorrect
Hint
From the routing table we learn that network 192.168.10.0/30 is learned via 2 equal-cost paths (192.168.10.9 &192.168.10.5) -> traffic to this network will be load-balancing. -
Question 113 of 555
113. Question
Refer to the exhibit. C-router is to be used as a "router-on-a-stick" to route between the VLANs. All the interfaces have been properly configured and IP routing is operational. The hosts in the VLANs have been configured with the appropriate default gateway. What is true about this configuration?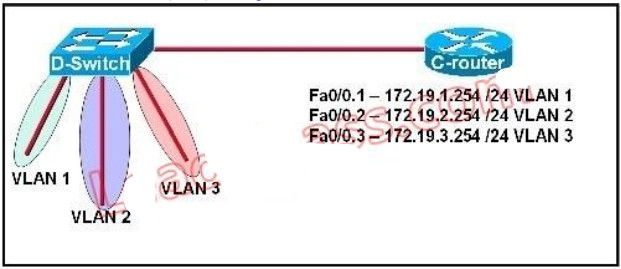 Correct
Correct
Incorrect
Hint
Since all the same router (C-router) is the default gateway for all three VLANs, all traffic destined to a different VLA will be sent to the C-router. The C-router will have knowledge of all three networks since they will appear as directly connected in the routing table. Since the C-router already knows how to get to all three networks, no routing protocols need to be configured. -
Question 114 of 555
114. Question
Which command would you configure globally on a Cisco router that would allow you to view directly connected Cisco devices?Correct
Incorrect
Hint
CDP is enabled on Cisco routers by default. If you prefer not to use the CDP capability, disable it with the no cdp run command. In order to reenable CDP, use the cdp run command in global configuration mode. The "cdp enable" command is an interface command, not global. -
Question 115 of 555
115. Question
Refer to the exhibit. Why is flash memory erased prior to upgrading the IOS image from the TFTP server?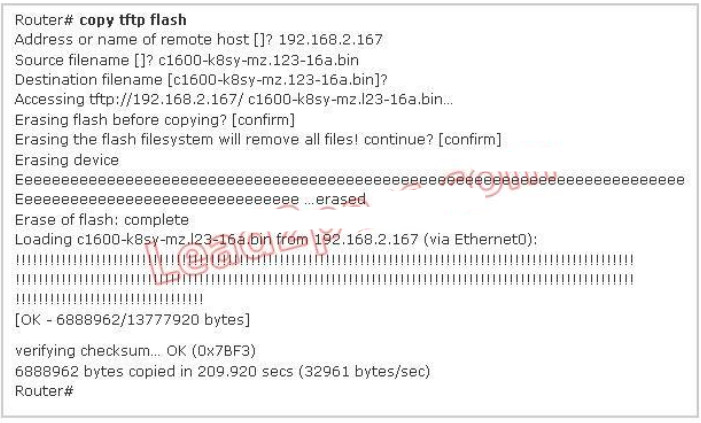 Correct
Correct
Incorrect
Hint
During the copy process, the router asked "Erasing flash before copying? [confirm]" and the administrator confirmed (by pressing Enter) so the flash was deleted. Note: In this case, the flash has enough space to copy a new IOS without deleting the current one. The current IOS is deleted just because the administrator wants to do so. If the flash does not have enough space you will see an error message like this: %Error copying tftp://192.168.2.167/ c1600-k8sy-mz.l23-16a.bin (Not enough space on device) -
Question 116 of 555
116. Question
Refer to the exhibit. According to the routing table, where will the router send a packet destined for 10.1.5.65?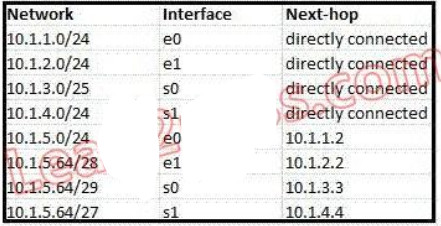 Correct
Correct
Incorrect
Hint
The destination IP address 10.1.5.65 belongs to 10.1.5.64/28, 10.1.5.64/29 & 10.1.5.64/27 subnets but the "longest prefix match" algorithm will choose the most specific subnet mask -> the prefix "/29 will be chosen to route the packet. Therefore the next-hop should be 10.1.3.3 -> . -
Question 117 of 555
117. Question
Refer to the exhibit. Which address and mask combination represents a summary of the routes learned by EIGRP?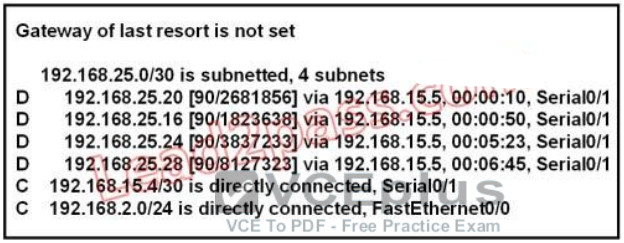 Correct
Correct
Incorrect
Hint
The binary version of 20 is 10100. The binary version of 16 is 10000. The binary version of 24 is 11000. The binary version of 28 is 11100. The subnet mask is /28. The mask is 255.255.255.240. Note: From the output above, EIGRP learned 4 routes and we need to find out the summary of them: + 192.168.25.16 + 192.168.25.20 + 192.168.25.24 + 192.168.25.28 -> The increment should bE. 28 ?16 = 12 but 12 is not an exponentiation of 2 so we must choose 16 (24). Therefore the subnet mask is /28 (=1111 1111.1111 1111.1111 1111.11110000) = 255.255.255.240 So the best answer should be 192.168.25.16 255.255.255.240 -
Question 118 of 555
118. Question
Refer to the exhibit. Assuming that the entire network topology is shown, what is the operational status of the interfaces of R2 as indicated by the command output shown?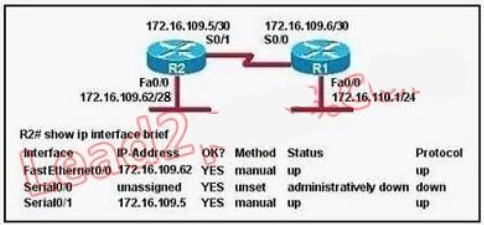 Correct
Correct
Incorrect
Hint
The output shown shows normal operational status of the router's interfaces. Serial0/0 is down because it has been disabled using the "shutdown" command. -
Question 119 of 555
119. Question
Which two locations can be configured as a source for the IOS image in the boot system command? (Choose two.)Correct
Incorrect
Hint
The following locations can be configured as a source for the IOS image: 1. + Flash (the default location) 2. + TFTP server 3. + ROM (used if no other source is found) -
Question 120 of 555
120. Question
Refer to the exhibit. Given the output for this command, if the router ID has not been manually set, what router ID will OSPF use for this router?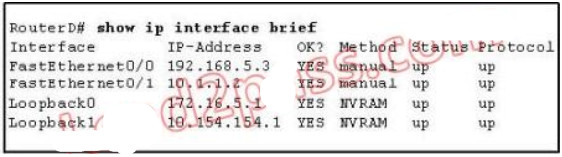 Correct
Correct
Incorrect
Hint
The highest IP address of all loopback interfaces will be chosen -> Loopback 0 will be chosen as the router ID. -
Question 121 of 555
121. Question
Which two statements describe the process identifier that is used in the command to configure OSPF on a router? (Choose two.) Router(config)# router ospf 1Correct
Incorrect
Hint
Multiple OSPF processes can be configured on a router using multiple process ID's. The valid process ID's are shown below: Edge-B(config)#router ospf ? <1-65535> Process ID -
Question 122 of 555
122. Question
Refer to the exhibit. What commands must be configured on the 2950 switch and the router to allow communication between host 1 and host 2? (Choose two.)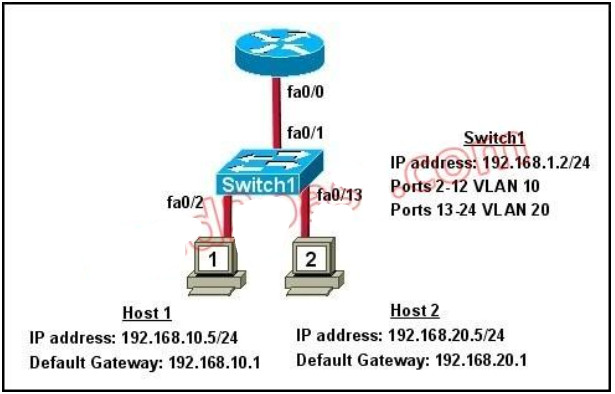 Correct
Correct
Incorrect
Hint
The router will need to use subinterfaces, where each subinterface is assigned a VLAN and IP address for each VLAN. On the switch, the connection to the router need to be configured as a trunk using the switchport mode trunk command and it will need a default gateway for VLAN 1. -
Question 123 of 555
123. Question
Refer to the exhibit. For what two reasons has the router loaded its IOS image from the location that is shown? (Choose two.)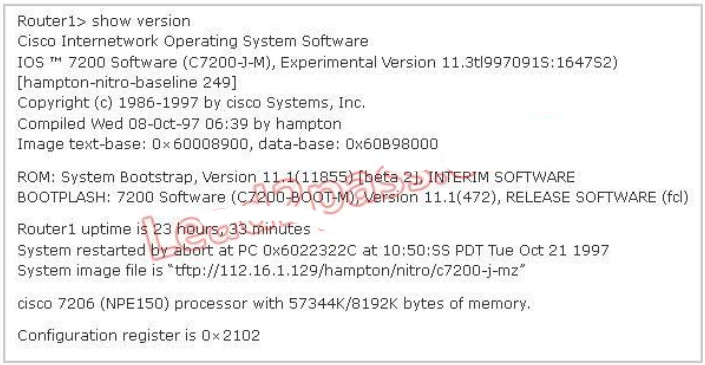 Correct
Correct
Incorrect
Hint
The loading sequence of CISCO IOS is as follows: Booting up the router and locating the Cisco IOS 1. POST (power on self test) 2. Bootstrap code executed 3. Check Configuration Register value (NVRAM) which can be modified using the config-register command 0 = ROM Monitor mode 1 = ROM IOS 2 - 15 = startup-config in NVRAM 4. Startup-config filE. Check for boot system commands (NVRAM) If boot system commands in startup-config a. Run boot system commands in order they appear in startup-config to locate the IOS b. [If boot system commands fail, use default fallback sequence to locate the IOS (Flash, TFTP, ROM)?] If no boot system commands in startup-config use the default fallback sequence in locating the IOS: a. Flash (sequential) b. TFTP server (netboot) c. ROM (partial IOS) or keep retrying TFTP depending upon router model 5. If IOS is loaded, but there is no startup-config file, the router will use the default fallback sequence for locating the IOS and then it will enter setup mode or the setup dialogue. -
Question 124 of 555
124. Question
Correct
Incorrect
Hint
When no startup configuration file is found in NVRAM, the System Configuration Dialog will appear to ask if we want to enter the initial configuration dialog or not. -
Question 125 of 555
125. Question
Which three elements must be used when you configure a router interface for VLAN trunking? (Choose three.)Correct
Incorrect
Hint
This scenario is commonly called a router on a stick. A short, well written article on this operation can be found here: http://www.thebryantadvantage.com/RouterOnAStickCCNACertificationExamTutorial.htm -
Question 126 of 555
126. Question
Which commands are required to properly configure a router to run OSPF and to add network 192.168.16.0/24 to OSPF area 0? (Choose two.)Correct
Incorrect
Hint
In the router ospf command, the ranges from 1 to 65535 so o is an invalid number -> but To configure OSPF, we need a wildcard in the "network" statement, not a subnet mask. We also need to assgin an area to this process -> . -
Question 127 of 555
127. Question
A router receives information about network 192.168.10.0/24 from multiple sources. What will the router consider the most reliable information about the path to that network?Correct
Incorrect
Hint
Explanation: When there is more than one way to reach a destination, it will choose the best one based on a couple of things. First, it will choose the route that has the longest match; meaning the most specific route. So, in this case the /24 routes will be chosen over the /16 routes. Next, from all the/24 routes it will choose the one with the lowest administrative distance. Directly connected routes have an AD of 1 so this will be the route chosen. -
Question 128 of 555
128. Question
What is the default maximum number of equal-cost paths that can be placed into the routing table of a Cisco OSPF router?Correct
Incorrect
Hint
maximum-paths (OSPF) To control the maximum number of parallel routes that Open Shortest Path First (OSPF) can support, use the maximum-paths command. Syntax Description maximum Maximum number of parallel routes that OSPF can install in a routing table. The range is from 1 to 16 routes. Command Default 8 paths -
Question 129 of 555
129. Question
Which command shows your active Telnet connections?Correct
Incorrect
Hint
The "show users" shows telnet/ssh connections to your router while "show sessions" shows telnet/ssh connections from your router (to other devices). The question asks about "your active Telnet connections", meaning connections from your router so the answer should be A. -
Question 130 of 555
130. Question
Correct
Incorrect
Hint
The "list 1 refers to the access-list number 1. -
Question 131 of 555
131. Question
Which type of EIGRP route entry describes a feasible successor?Correct
Incorrect
Hint
EIGRP uses the Neighbor Table to list adjacent routers. The Topology Table list all the learned routers to destination whilst the Routing Table contains the best route to a destination, which is known as the Successor. The Feasible Successor is a backup route to a destination which is kept in the Topology Table. -
Question 132 of 555
132. Question
Which statement describes the process of dynamically assigning IP addresses by the DHCP server?Correct
Incorrect
Hint
The DHCP lifecycle consists of the following: Release: The client may decide at any time that it no longer wishes to use the IP address it was assigned, and may terminate the lease, releasing the IP address. -
Question 133 of 555
133. Question
What are two benefits of using NAT? (Choose two.)Correct
Incorrect
Hint
By not revealing the internal Ip addresses, NAT adds some security to the inside network -> F is correct. NAT has to modify the source IP addresses in the packets -> E is not correct. Connection from the outside of the network through a "NAT" network is more difficult than a more network because IP addresses of inside hosts are hidden -> C is not correct. In order for IPsec to work with NAT we need to allow additional protocols, including Internet Key Exchange (IKE), Encapsulating Security Payload (ESP) and Authentication Header (AH) -> more complex -> A is not correct. By allocating specific public IP addresses to inside hosts, NAT eliminates the need to re-address the inside hosts -> B is correct. NAT does conserve addresses but not through host MAC-level multiplexing. It conserves addresses by allowing many private IP addresses to use the same public IP address to go to the Internet -> C is not correct. -
Question 134 of 555
134. Question
On which options are standard access lists based?Correct
Incorrect
Hint
Standard ACL's only examine the source IP address/mask to determine if a match is made. Extended ACL's examine the source and destination address, as well as port information. -
Question 135 of 555
135. Question
A network engineer wants to allow a temporary entry for a remote user with a specific username and password so that the user can access the entire network over the Internet. Which ACL can be used?Correct
Incorrect
Hint
We can use a dynamic access list to authenticate a remote user with a specific username and password. The authentication process is done by the router or a central access server such as a TACACS+ or RADIUS server. The configuration of dynamic ACL can be read here: http://www.cisco.com/en/US/tech/tk583/tk822/technologies_tech_note09186a0080094524.shtml -
Question 136 of 555
136. Question
How does a DHCP server dynamically assign IP addresses to hosts?Correct
Incorrect
Hint
DHCP works in a client/server mode and operates like any other client/server relationship. When a PC connects to a DHCP server, the server assigns or leases an IP address to that PC. The PC connects to the network with that leased IP address until the lease expires. The host must contact the DHCP server periodically to extend the lease. This lease mechanism ensures that hosts that move or power off do not hold onto addresses that they do not need. The DHCP server returns -
Question 137 of 555
137. Question
Correct
Incorrect
Hint
An address conflict occurs when two hosts use the same IP address. During address assignment, DHCP checks for conflicts using ping and gratuitous ARP. If a conflict is detected, the address is removed from the pool. The address will not be assigned until the administrator resolves the conflict. http://www.cisco.com/en/US/docs/ios/12_1/iproute/configuration/guide/1cddhcp.html -
Question 138 of 555
138. Question
Which two tasks does the Dynamic Host Configuration Protocol perform? (Choose two.)Correct
Incorrect
Hint
The Dynamic Host Configuration Protocol (DHCP) is a network protocol used to configure devices that are connected to a network (known as hosts) so they can communicate on that network using the Internet Protocol (IP). It involves clients and a server operating in a clientserver model. DHCP servers assigns IP addresses from a pool of addresses and also assigns other parameters such as DNS and default gateways to hosts. -
Question 139 of 555
139. Question
Correct
Incorrect
Hint
The "list 1 refers to the access-list number 1 -
Question 140 of 555
140. Question
When a DHCP server is configured, which two IP addresses should never be assignable to hosts? (Choose two.)Correct
Incorrect
Hint
Network or subnetwork IP address (for example 11.0.0.0/8 or 13.1.0.0/16) and broadcast address (for example 23.2.1.255/24) should never be assignable to hosts. When try to assign these addresses to hosts, you will receive an error message saying that they can't be assignable. -
Question 141 of 555
141. Question
Which two statements about static NAT translations are true? (Choose two.)Correct
Incorrect
Hint
Static NAT is to map a single outside IP address to a single inside IP address. This is typically done to allow incoming connections from the outside (Internet) to the inside. Since these are static, they are always present in the NAT table even if they are not actively in use. -
Question 142 of 555
142. Question
Which statement about access lists that are applied to an interface is true?Correct
Incorrect
Hint
We can have only 1 access list per protocol, per direction and per interface. It means: + We can not have 2 inbound access lists on an interface + We can have 1 inbound and 1 outbound access list on an interface -
Question 143 of 555
143. Question
Which item represents the standard IP ACL?Correct
Incorrect
Hint
The standard access lists are ranged from 1 to 99 and from 1300 to 1999 so only access list 50 is a standard access list. -
Question 144 of 555
144. Question
A network administrator is configuring ACLs on a Cisco router, to allow traffic from hosts on networks 192.168.146.0, 192.168.147.0, 192.168.148.0, and 192.168.149.0 only. Which two ACL statements, when combined, would you use to accomplish this task? (Choose two.)Correct
Incorrect
Hint
access-list 10 permit ip 192.168.146.0 0.0.1.255 will include the 192.168.146.0 and 192.168.147.0 subnets, while access-list 10 permit ip 192.168.148.0 0.0.1.255 will include -
Question 145 of 555
145. Question
What can be done to secure the virtual terminal interfaces on a router? (Choose two.)Correct
Incorrect
Hint
It is a waste to administratively shut down the interface. Moreover, someone can still access the virtual terminal interfaces via other interfaces -> We can not physically secure a virtual interface because it is "virtual" -> To apply an access list to a virtual terminal interface we must use the "access-class" command. The "access-group" command is only used to apply an access list to a physical interface -> C is not correct. The most simple way to secure the virtual terminal interface is to configure a username & password to prevent unauthorized login. -
Question 146 of 555
146. Question
Which two commands correctly verify whether port security has been configured on port FastEthernet 0/12 on a switch? (Choose two.)Correct
Incorrect
-
Question 147 of 555
147. Question
Refer to the exhibit. The following commands are executed on interface fa0/1 of 2950Switch. 2950Switch(config-if)# switchport port-security 2950Switch(config-if)# switchport port-security mac-address sticky 2950Switch(config-if)# switchport port-security maximum 1 The Ethernet frame that is shown arrives on interface fa0/1. What two functions will occur when this frame is received by 2950Switch? (Choose two.)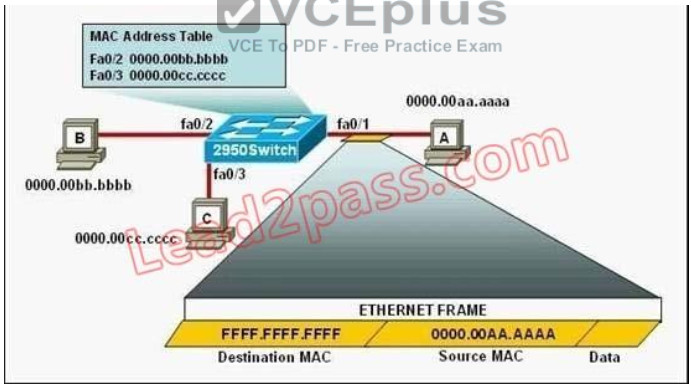 Correct
Correct
Incorrect
Hint
The configuration shown here is an example of port security, specifically port security using sticky addresses. You can use port security with dynamically learned and static MAC addresses to restrict a port's ingress traffic by limiting the MAC addresses that are allowed to send traffic into the port. When you assign secure MAC addresses to a secure port, the port does not forward ingress traffic that has source addresses outside the group of defined addresses. If you limit the number of secure MAC addresses to one and assign a single secure MAC address, the device attached to that port has the full bandwidth of the port. Port security with sticky MAC addresses provides many of the same benefits as port security with static MAC addresses, but sticky MAC addresses can be learned dynamically. Port security with sticky MAC addresses retains dynamically learned MAC addresses during a link-down condition. -
Question 148 of 555
148. Question
What will be the result if the following configuration commands are implemented on a Cisco switch? Switch(config-if)# switchport port-security Switch(config-if)# switchport port-security mac-address stickyCorrect
Incorrect
Hint
In the interface configuration mode, the command switchport port-security mac-address sticky enables sticky learning. When entering this command, the interface converts all the dynamic secure MAC addresses to sticky secure MAC addresses. -
Question 149 of 555
149. Question
The network administrator cannot connect to Switch1 over a Telnet session, although the hosts attached to Switch1 can ping the interface Fa0/0 of the router. Given the information in the graphic and assuming that the router and Switch2 are configured properly, which of the following commands should be issued on Switch1 to correct this problem?Correct
Incorrect
Hint
Since we know hosts can reach the router through the switch, we know that connectivity, duplex. Speed, etc. are good. However, for the switch itself to reach networks outside the local one, the ip default-gateway command must be used. -
Question 150 of 555
150. Question
Refer to the exhibit. Which of these statements correctly describes the state of the switch once the boot process has been completed?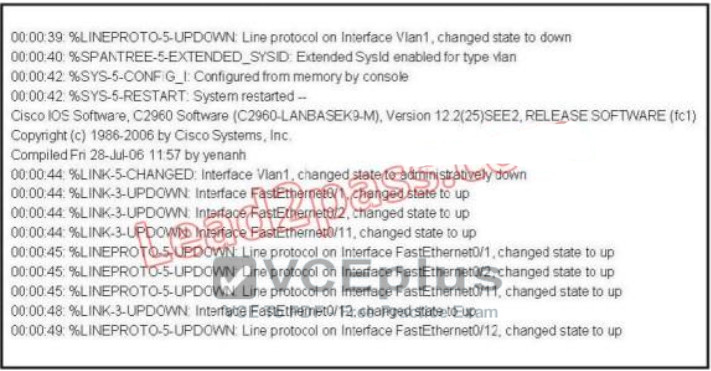 Correct
Correct
Incorrect
Hint
Notice the line, which says "Interface VLAN1, changed state to administratively down". This shows that VLAN1 is shut down. Hence remote management of this switch is not possible unless VLAN1 is brought back up. Since VLAN1 is the only interface shown in the output, you have to assume that no other VLAN interface has been configured with an IP Address. -
Question 151 of 555
151. Question
Refer to exhibit. A network administrator cannot establish a Telnet session with the indicated router. What is the cause of this failure?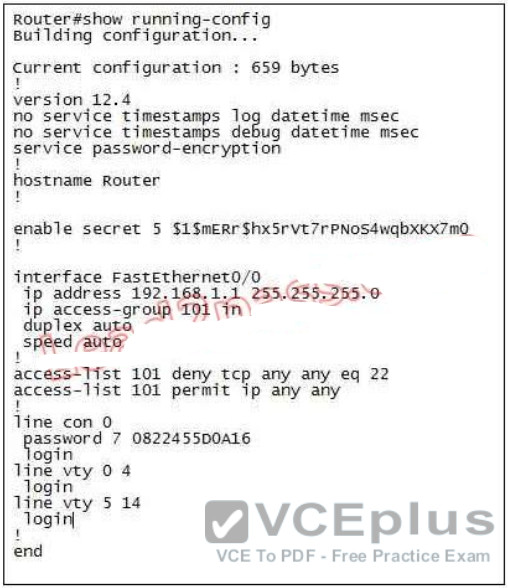 Correct
Correct
Incorrect
Hint
The login keyword has been set, but not password. This will result in the "password required, but none set" message to users trying to telnet to this router. -
Question 152 of 555
152. Question
Refer to the exhibit. When running EIGRP, what is required for RouterA to exchange routing updates with RouterC?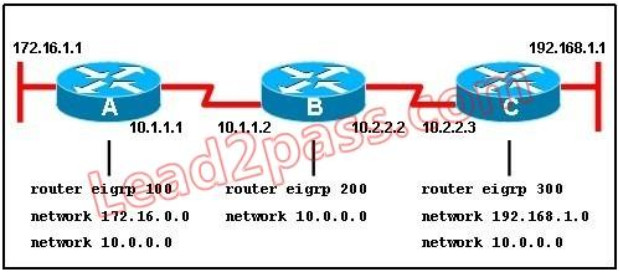 Correct
Correct
Incorrect
Hint
This question is to examine the understanding of the interaction between EIGRP routers. The following information must be matched so as to create neighborhood. EIGRP routers to establish, must match the following information: 1. AS Number; 2. K value. -
Question 153 of 555
153. Question
A router has two Fast Ethernet interfaces and needs to connect to four VLANs in the local network. How can you accomplish this task, using the fewest physical interfaces and without decreasing network performance?Correct
Incorrect
Hint
A router on a stick allows you to use sub-interfaces to create multiple logical networks on a single physical interface. -
Question 154 of 555
154. Question
Users on the 172.17.22.0 network cannot reach the server located on the 172.31.5.0 network. The network administrator connected to router Coffee via the console port, issued the show ip route command, and was able to ping the server.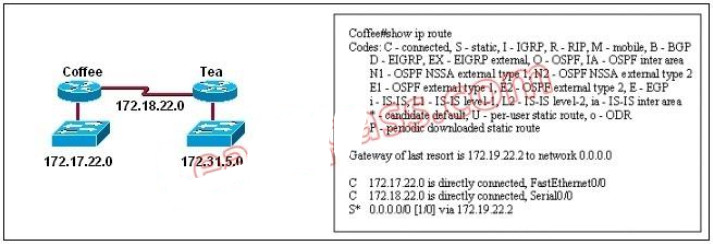 Based on the output of the show ip route command and the topology shown in the graphic, what is the cause of the failure? Correct
Based on the output of the show ip route command and the topology shown in the graphic, what is the cause of the failure? Correct
Incorrect
Hint
The default route or the static route was configured with incorrect next-hop ip address 172.19.22.2 The correct ip address will be 172.18.22.2 to reach server located on 172.31.5.0 network. Ip route 0.0.0.0 0.0.0.0 172.18.22.2 -
Question 155 of 555
155. Question
A network administrator is trying to add a new router into an established OSPF network. The networks attached to the new router do not appear in the routing tables of the other OSPF routers. Given the information in the partial configuration shown below, what configuration error is causing this problem? Router(config)# router ospf 1 Router(config-router)# network 10.0.0.0 255.0.0.0 area 0Correct
Incorrect
Hint
When configuring OSPF, the mask used for the network statement is a wildcard mask similar to an access list. In this specific example, the correct syntax would have been "network 10.0.0.0 0.0.0.255 area 0." -
Question 156 of 555
156. Question
Which Cisco Catalyst feature automatically disables the port in an operational PortFast upon receipt of a BPDU?Correct
Incorrect
Hint
We only enable PortFast feature on access ports (ports connected to end stations). But if someone does not know he can accidentally plug that port to another switch and a loop may occur when BPDUs are being transmitted and received on these ports. With BPDU Guard, when a PortFast receives a BPDU, it will be shut down to prevent a loop. -
Question 157 of 555
157. Question
When you are troubleshooting an ACL issue on a router, which command would you use to verify which interfaces are affected by the ACL?Correct
Incorrect
Hint
Incorrect answer: show ip access-lists does not show interfaces affected by an ACL. -
Question 158 of 555
158. Question
Host 1 is trying to communicate with Host 2. The e0 interface on Router C is down. Which of the following are true? (Choose two.)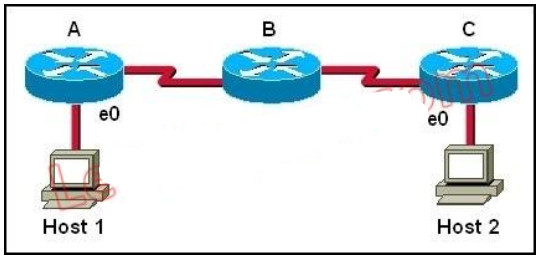 Correct
Correct
Incorrect
Hint
Host 1 is trying to communicate with Host 2. The e0 interface on Router C is down. Router C will send ICMP packets to inform Host 1 that Host 2 cannot be reached. -
Question 159 of 555
159. Question
Refer to the exhibit. When running EIGRP, what is required for RouterA to exchange routing updates with RouterC? Correct
Correct
Incorrect
Hint
This question is to examine the understanding of the interaction between EIGRP routers. The following information must be matched so as to create neighborhood. EIGRP routers to establish, must match the following information: 1. AS Number; 2. K value. -
Question 160 of 555
160. Question
Cisco Catalyst switches CAT1 and CAT2 have a connection between them using ports FA0/13. An 802.1Q trunk is configured between the two switches. On CAT1, VLAN 10 is chosen as native, but on CAT2 the native VLAN is not specified. What will happen in this scenario?Correct
Incorrect
Hint
A "native VLAN mismatch" error will appear by CDP if there is a native VLAN mismatch on an 802.1Q link. "VLAN mismatch" can cause traffic from one vlan to leak into another vlan. -
Question 161 of 555
161. Question
Refer to the exhibit. A network technician is asked to design a small network with redundancy. The exhibit represents this design, with all hosts configured in the same VLAN. What conclusions can be made about this design?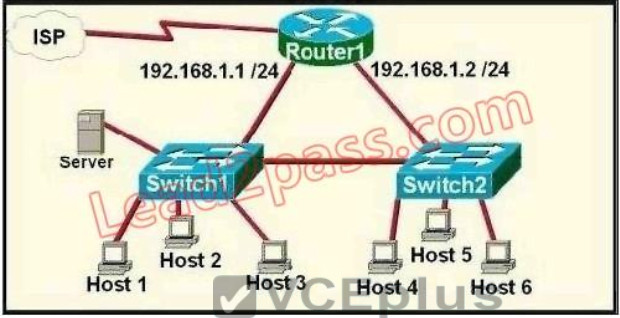 Correct
Correct
Incorrect
Hint
Each interface on a router must be in a different network. If two interfaces are in the same network, the router will not accept it and show error when the administrator assigns it. -
Question 162 of 555
162. Question
Refer to the exhibit. A technician is troubleshooting host connectivity issues on the switches. The hosts in VLANs 10 and 15 on Sw11 are unable to communicate with hosts in the same VLANs on Sw12. Hosts in the Admin VLAN are able to communicate. The port-to-VLAN assignments are identical on the two switches. What could be the problem?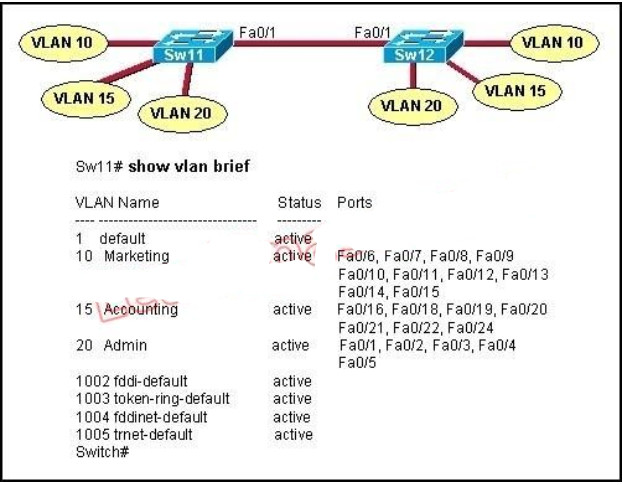 Correct
Correct
Incorrect
Hint
In order for hosts in the same VLAN to communicate with each other over multiple switches, those switches need to be configured as trunks on their connected interfaces so that they can pass traffic from multiple VLANs. -
Question 163 of 555
163. Question
Refer to the exhibit. The Bigtime router is unable to authenticate to the Littletime router. What is the cause of the problem?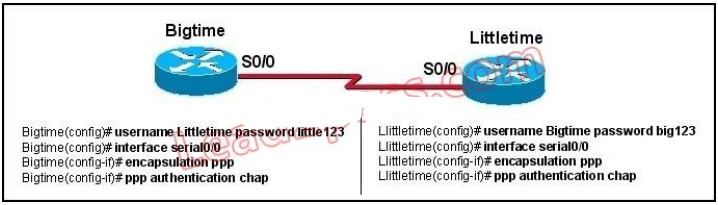 Correct
Correct
Incorrect
Hint
With CHAP authentication, the configured passwords must be identical on each router. Here, it is configured as little123 on one side and big123 on the other. -
Question 164 of 555
164. Question
Refer to the exhibit. Given this output for SwitchC, what should the network administrator's next action be?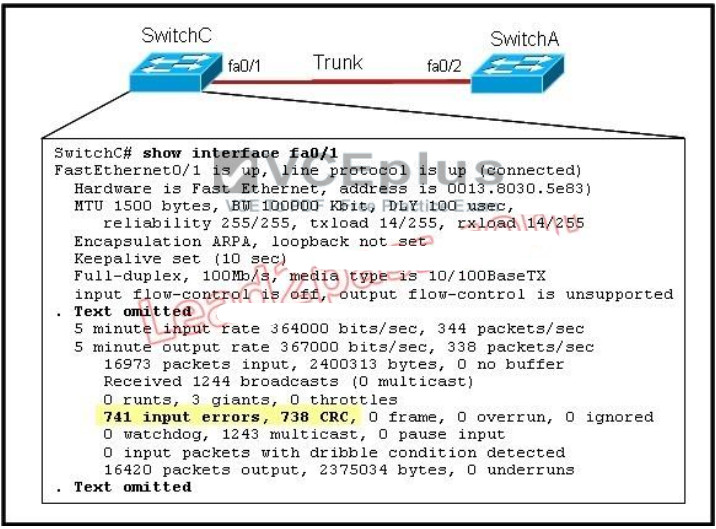 Correct
Correct
Incorrect
Hint
Here we can see that this port is configured for full duplex, so the next step would be to check the duplex setting of the port on the other switch. A mismatched trunk encapsulation would not result in input errors and CRC errors. -
Question 165 of 555
165. Question
What will happen if a private IP address is assigned to a public interface connected to an ISP?Correct
Incorrect
Hint
Private RFC 1918 IP addresses are meant to be used by organizations locally within their own network only, and can not be used globally for Internet use. -
Question 166 of 555
166. Question
Refer to the exhibit. An attempt to deny web access to a subnet blocks all traffic from the subnet. Which interface command immediately removes the effect of ACL 102?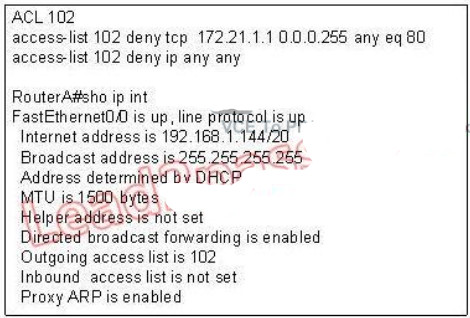 Correct
Correct
Incorrect
Hint
Explanation: Now let's find out the range of the networks on serial link: For the network 192.168.1.62/27: Increment: 32 Network address: 192.168.1.32 Broadcast address: 192.168.1.63 For the network 192.168.1.65/27: Increment: 32 Network address: 192.168.1.64 Broadcast address: 192.168.1.95 -> These two IP addresses don't belong to the same network and they can't see each other -
Question 167 of 555
167. Question
Which router IOS commands can be used to troubleshoot LAN connectivity problems? (Choose three.)Correct
Incorrect
Hint
Ping, show ip route, and show interfaces are all valid troubleshooting IOS commands. Tracert, ipconfig, and winipcfg are PC commands, not IOS. -
Question 168 of 555
168. Question
A network administrator is troubleshooting the OSPF configuration of routers R1 and R2. The routers cannot establish an adjacency relationship on their common Ethernet link.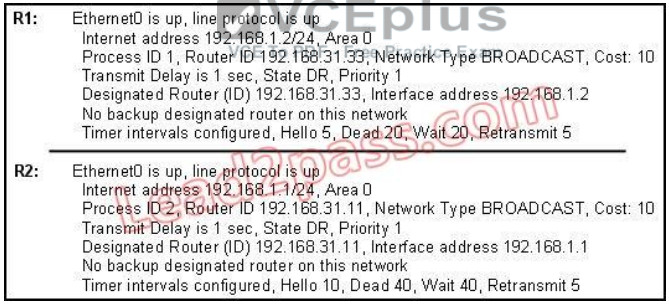 The graphic shows the output of the show ip ospf interface e0 command for routers R1 and R2. Based on the information in the graphic, what is the cause of this problem? Correct
The graphic shows the output of the show ip ospf interface e0 command for routers R1 and R2. Based on the information in the graphic, what is the cause of this problem? Correct
Incorrect
Hint
In OSPF, the hello and dead intervals must match and here we can see the hello interval is set to 5 on R1 and 10 on R2. The dead interval is also set to 20 on R1 but it is 40 on R2. -
Question 169 of 555
169. Question
In which circumstance are multiple copies of the same unicast frame likely to be transmitted in a switched LAN?Correct
Incorrect
Hint
If we connect two switches via 2 or more links and do not enable STP on these switches then a loop (which creates multiple copies of the same unicast frame) will occur. It is an example of an improperly implemented redundant topology. -
Question 170 of 555
170. Question
VLAN 3 is not yet configured on your switch. What happens if you set the switchport access vlan 3 command in interface configuration mode?Correct
Incorrect
Hint
The "switchport access vlan 3" will put that interface as belonging to VLAN 3 while also updated the VLAN database automatically to include VLAN 3. -
Question 171 of 555
171. Question
A network administrator is troubleshooting an EIGRP problem on a router and needs to confirm the IP addresses of the devices with which the router has established adjacency. The retransmit interval and the queue counts for the adjacent routers also need to be checked. What command will display the required information?Correct
Incorrect
-
Question 172 of 555
172. Question
Refer to the graphic. R1 is unable to establish an OSPF neighbor relationship with R3. What are possible reasons for this problem? (Choose two.)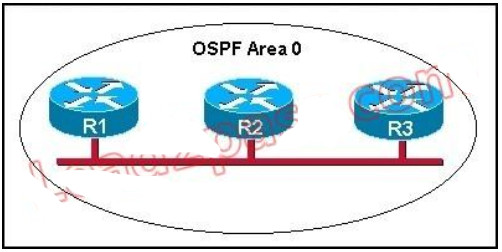 Correct
Correct
Incorrect
Hint
This question is to examine the conditions for OSPF to create neighborhood. So as to make the two routers become neighbors, each router must be matched with the following items: 1. The area ID and its types; 2. Hello and failure time interval timer; 3. OSPF Password (Optional); -
Question 173 of 555
173. Question
Refer to the exhibit. The network shown in the diagram is experiencing connectivity problems. Which of the following will correct the problems? (Choose two.)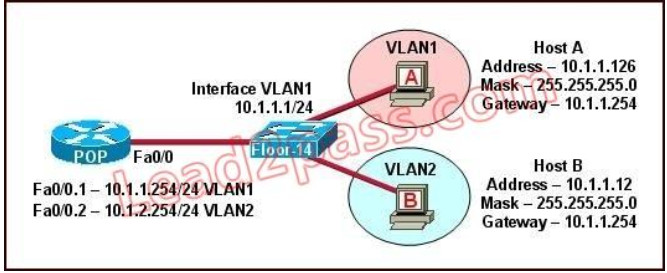 Correct
Correct
Incorrect
Hint
The switch 1 is configured with two VLANs: VLAN1 and VLAN2. The IP information of member Host A in VLAN1 is as follows: Address : 10.1.1.126 Mask : 255.255.255.0 Gateway : 10.1.1.254 The IP information of member Host B in VLAN2 is as follows: Address : 10.1.1.12 Mask : 255.255.255.0 Gateway : 10.1.1.254 The configuration of sub-interface on router 2 is as follows: Fa0/0.1 -- 10.1.1.254/24 VLAN1 Fa0/0.2 -- 10.1.2.254/24 VLAN2 It is obvious that the configurations of the gateways of members in VLAN2 and the associated network segments are wrong. The layer3 addressing information of Host B should be modified as follows: Address : 10.1.2.X Mask : 255.255.255.0 -
Question 174 of 555
174. Question
Refer to the exhibit. A problem with network connectivity has been observed. It is suspected that the cable connected to switch port Fa0/9 on Switch1 is disconnected. What would be an effect of this cable being disconnected?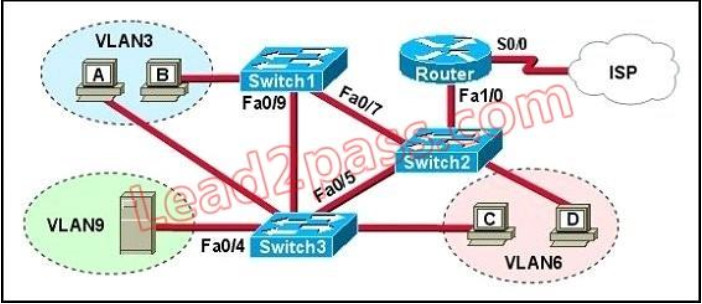 Correct
Correct
Incorrect
Hint
Spanning-Tree Protocol (STP) is a Layer 2 protocol that utilizes a special-purpose algorithm to discover physical loops in a network and effect a logical loop-free topology. STP creates a loopfree tree structure consisting of leaves and branches that span the entire Layer 2 network. The actual mechanics of how bridges communicate and how the STP algorithm works will be discussed at length in the following topics. Note that the terms bridge and switch are used interchangeably when discussing STP. In addition, unless otherwise indicated, connections between switches are assumed to be trunks. -
Question 175 of 555
175. Question
Refer to the exhibit. HostA cannot ping HostB. Assuming routing is properly configured, what is the cause of this problem?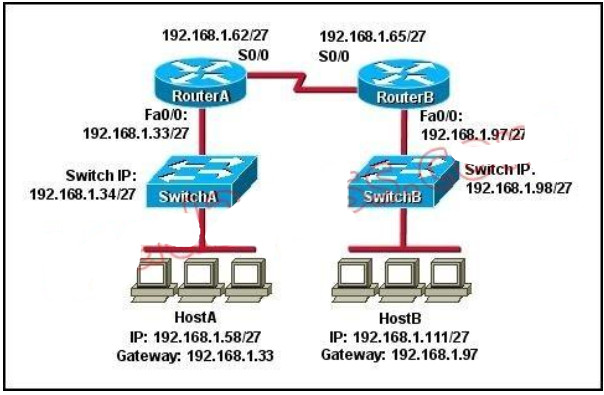 Correct
Correct
Incorrect
Hint
Now let's find out the range of the networks on serial link: For the network 192.168.1.62/27: Increment: 32 Network address: 192.168.1.32 Broadcast address: 192.168.1.63 For the network 192.168.1.65/27: Increment: 32 Network address: 192.168.1.64 Broadcast address: 192.168.1.95 -> These two IP addresses don't belong to the same network and they can't see each other -
Question 176 of 555
176. Question
Which port state is introduced by Rapid-PVST?Correct
Incorrect
Hint
Explanation: PVST+ is based on IEEE802.1D Spanning Tree Protocol (STP). But PVST+ has only 3 port states (discarding, learning and forwarding) while STP has 5 port states (blocking, listening, learning, forwarding and disabled). So discarding is a new port state in PVST+. -
Question 177 of 555
177. Question
Refer to the exhibit. The two connected ports on the switch are not turning orange or green. What would be the most effective steps to troubleshoot this physical layer problem? (Choose three.) Correct
Correct
Incorrect
Hint
The ports on the switch are not up indicating it is a layer 1 (physical) problem so we should check cable type, power and how they are plugged in. -
Question 178 of 555
178. Question
Refer to the exhibit. A network administrator attempts to ping Host2 from Host1 and receives the results that are shown. What is the problem?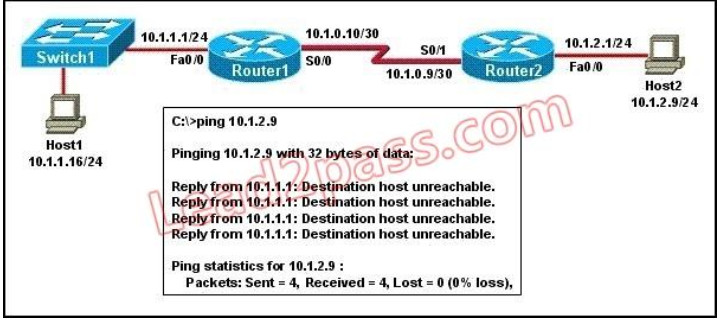 Correct
Correct
Incorrect
Hint
Host1 tries to communicate with Host2. The message destination host unreachable from Router1 indicates that the problem occurs when the data is forwarded from Host1 to Host2. According to the topology, we can infer that The link between Router1 and Router2 is down. -
Question 179 of 555
179. Question
Refer to the exhibit. Hosts in network 192.168.2.0 are unable to reach hosts in network 192.168.3.0. Based on the output from RouterA, what are two possible reasons for the failure? (Choose two.)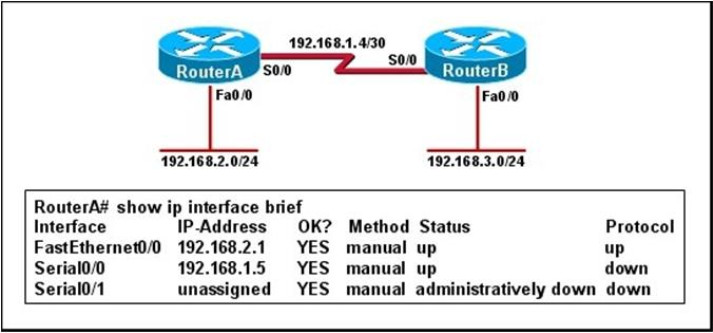 Correct
Correct
Incorrect
Hint
From the output we can see that there is a problem with the Serial 0/0 interface. It is enabled, but the line protocol is down. The could be a result of mismatched encapsulation or the interface not receiving a clock signal from the CSU/DSU. -
Question 180 of 555
180. Question
Refer to the exhibit. An administrator pings the default gateway at 10.10.10.1 and sees the output as shown. At which OSI layer is the problem?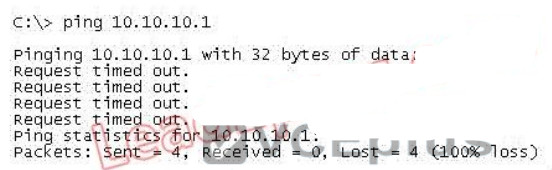 Correct
Correct
Incorrect
Hint
The command ping uses ICMP protocol, which is a network layer protocol used to propagate control message between host and router. The command ping is often used to verify the network connectivity, so it works at the network layer. -
Question 181 of 555
181. Question
Which statement is correct regarding the operation of DHCP?Correct
Incorrect
Hint
An address conflict occurs when two hosts use the same IP address. During address assignment, DHCP checks for conflicts using ping and gratuitous ARP. If a conflict is detected, the address is removed from the pool. The address will not be assigned until the administrator resolves the conflict. http://www.cisco.com/en/US/docs/ios/12_1/iproute/configuration/guide/1cddhcp.html -
Question 182 of 555
182. Question
Refer to the exhibit. Statements A, B, C, and D of ACL 10 have been entered in the shown order and applied to interface E0 inbound, to prevent all hosts (except those whose addresses are the first and last IP of subnet 172.21.1.128/28) from accessing the network. But as is, the ACL does not restrict anyone from the network. How can the ACL statements be re-arranged so that the system works as intended?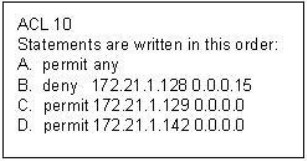 Correct
Correct
Incorrect
Hint
Routers go line by line through an access list until a match is found and then will not look any further, even if a more specific of better match is found later on in the access list. So, it it best to begin with the most specific entries first, in this cast the two hosts in line C and D. Then, include the subnet (B) and then finally the rest of the traffic (A) -
Question 183 of 555
183. Question
The output of the show frame-relay pvc command shows "PVC STATUS = INACTIVE". What does this mean?Correct
Incorrect
Hint
The PVC STATUS displays the status of the PVC. The DCE device creates and sends the report to the DTE devices. There are 4 statuses: + ACTIVE: the PVC is operational and can transmit data + INACTIVE: the connection from the local router to the switch is working, but the connection to the remote router is not available + DELETED: the PVC is not present and no LMI information is being received from the Frame Relay switch + STATIC: the Local Management Interface (LMI) mechanism on the interface is disabled (by using the "no keepalive" command). This status is rarely seen so it is ignored in some books. -
Question 184 of 555
184. Question
Which command is used to enable CHAP authentication, with PAP as the fallback method, on a serial interface?Correct
Incorrect
Hint
This command tells the router to first use CHAP and then go to PAP if CHAP isn't available. -
Question 185 of 555
185. Question
Which protocol is an open standard protocol framework that is commonly used in VPNs, to provide secure end-to-end communications?Correct
Incorrect
Hint
IPSec is a framework of open standards that provides data confidentiality, data integrity, and data authentication between participating peers at the IP layer. IPSec can be used to protect one or more data flows between IPSec peers. -
Question 186 of 555
186. Question
At which layer of the OSI model does PPP perform?Correct
Incorrect
Hint
The Point-to-Point Protocol (PPP) provides a standard method for transporting multi-protocol datagrams over point-to-point links. PPP was originally emerged as an encapsulation protocol for transporting IP traffic between two peers. It is a data link layer protocol (layer 2 in the OSI model ) -
Question 187 of 555
187. Question
The command frame-relay map ip 10.121.16.8 102 broadcast was entered on the router. Which of the following statements is true concerning this command?Correct
Incorrect
Hint
Broadcast is added to the configurations of the frame relay, so the PVC supports broadcast, allowing the routing protocol updates that use the broadcast update mechanism to be forwarded across itself. -
Question 188 of 555
188. Question
Which two options are valid WAN connectivity methods? (Choose two.)Correct
Incorrect
Hint
The Point-to-Point Protocol (PPP) provides a standard method for transporting multi-protocol datagrams over point-to-point links. PPP was originally emerged as an encapsulation protocol for transporting IP traffic between two peers. It is a data link layer protocol used for WAN connections. DSL is also considered a WAN connection, as it can be used to connect networks, typically when used with VPN technology. -
Question 189 of 555
189. Question
Which Layer 2 protocol encapsulation type supports synchronous and asynchronous circuits and has built-in security mechanisms?Correct
Incorrect
Hint
PPP: Provides router-to-router and host-to-network connections over synchronous and asynchronous circuits. PPP was designed to work with several network layer protocols, including IP. PPP also has built-in security mechanisms, such as Password Authentication Protocol (PAP) and Challenge Handshake Authentication Protocol (CHAP). -
Question 190 of 555
190. Question
Which encapsulation type is a Frame Relay encapsulation type that is supported by Cisco routers?Correct
Incorrect
Hint
Cisco supports two Frame Relay encapsulation types: the Cisco encapsulation and the IETF Frame Relay encapsulation, which is in conformance with RFC 1490 and RFC 2427. The former is often used to connect two Cisco routers while the latter is used to connect a Cisco router to a non-Cisco router. You can test with your Cisco router when typing the command Router(configif)# encapsulation frame-relay ? on a WAN link. Below is the output of this command (notice Cisco is the default encapsulation so it is not listed here, just press Enter to use it). Note: Three LMI options are supported by Cisco routers are ansi, Cisco, and Q933a. They represent the ANSI Annex D, Cisco, and ITU Q933-A (Annex A) LMI types, respectively. HDLC is a WAN protocol same as Frame-Relay and PPP so it is not a Frame Relay encapsulation type.
Note: Three LMI options are supported by Cisco routers are ansi, Cisco, and Q933a. They represent the ANSI Annex D, Cisco, and ITU Q933-A (Annex A) LMI types, respectively. HDLC is a WAN protocol same as Frame-Relay and PPP so it is not a Frame Relay encapsulation type. -
Question 191 of 555
191. Question
RouterA is unable to reach RouterB. Both routers are running IOS version 12.0. After reviewing the command output and graphic, what is the most likely cause of the problem?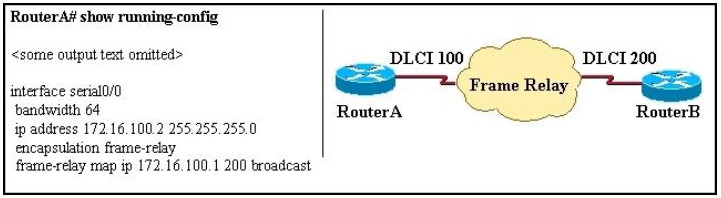 Correct
Correct
Incorrect
Hint
First we have to say this is an unclear question and it is wrong. The “frame-relay map ip” statement is correct thus none of the four answers above is correct. But we guess there is a typo in the output. Maybe the “ip address 172.16.100.2 255.255.0.0 command should be “ip address 172.16.100.1 255.255.0.0. -
Question 192 of 555
192. Question
Refer to the exhibit. What is the meaning of the term dynamic as displayed in the output of the show frame-relay map command shown?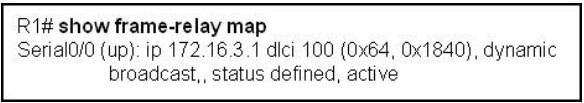 Correct
Correct
Incorrect
Hint
Inverse Address Resolution Protocol (Inverse ARP) was developed to provide a mechanism for dynamic DLCI to Layer 3 address maps. Inverse ARP works much the same way Address Resolution Protocol (ARP) works on a LAN. However, with ARP, the device knows the Layer 3 IP address and needs to know the remote data link MAC address. With Inverse ARP, the router knows the Layer 2 address which is the DLCI, but needs to know the remote Layer 3 IP address. When using dynamic address mapping, Inverse ARP requests a next-hop protocol address for each active PVC. Once the requesting router receives an Inverse ARP response, it updates its DLCI-to-Layer 3 address mapping table. Dynamic address mapping is enabled by default for all protocols enabled on a physical interface. If the Frame Relay environment supports LMI autosensing and Inverse ARP, dynamic address mapping takes place automatically. Therefore, no static address mapping is required. -
Question 193 of 555
193. Question
A network administrator needs to configure a serial link between the main office and a remote location. The router at the remote office is a non-Cisco router. How should the network administrator configure the serial interface of the main office router to make the connection?Correct
Incorrect
Hint
With serial point to point links there are two options for the encapsulation. The default, HDLC, is Cisco proprietary and works only with other Cisco routers. The other option is PPP which is standards based and supported by all vendors. -
Question 194 of 555
194. Question
What are three reasons that an organization with multiple branch offices and roaming users might implement a Cisco VPN solution instead of point-to-point WAN links? (Choose three.)Correct
Incorrect
Hint
IPsec offer a number of advantages over point to point WAN links, particularly when multiple locations are involved. These include reduced cost, increased security since all traffic is encrypted, and increased scalability as s single WAN link can be used to connect to all locations in a VPN, where as a point to point link would need to be provisioned to each location. -
Question 195 of 555
195. Question
Which two statistics appear in show frame-relay map output? (Choose two.)Correct
Incorrect
Hint
Sample "show frame-relay map" output: R1#sh frame mapSerial0/0 (up): ip 10.4.4.1 dlci 401(0x191,0x6410), dynamic,broadcast,, status defined, activeSerial0/0 (up): ip 10.4.4.3 dlci 403(0x193,0x6430), dynamic,broadcast,, status defined, activeSerial0/0 (up): ip 10.4.4.4 dlci 401(0x191,0x6410), static,CISCO, status defined, active -
Question 196 of 555
196. Question
Users have been complaining that their Frame Relay connection to the corporate site is very slow. The network administrator suspects that the link is overloaded.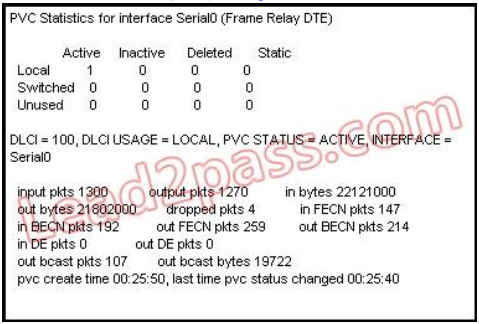 Based on the partial output of the Router# show frame relay pvc command shown in the graphic, which output value indicates to the local router that traffic sent to the corporate site is experiencing congestion? Correct
Based on the partial output of the Router# show frame relay pvc command shown in the graphic, which output value indicates to the local router that traffic sent to the corporate site is experiencing congestion? Correct
Incorrect
Hint
If device A is sending data to device B across a Frame Relay infrastructure and one of the intermediate Frame Relay switches encounters congestion, congestion being full buffers, oversubscribed port, overloaded resources, etc, it will set the BECN bit on packets being returned to the sending device and the FECN bit on the packets being sent to the receiving device. -
Question 197 of 555
197. Question
Which command allows you to verify the encapsulation type (CISCO or IETF) for a Frame Relay link?Correct
Incorrect
Hint
When connecting Cisco devices with non-Cisco devices, you must use IETF4 encapsulation on both devices. Check the encapsulation type on the Cisco device with the show frame-relay map exec command. -
Question 198 of 555
198. Question
It has become necessary to configure an existing serial interface to accept a second Frame Relay virtual circuit. Which of the following procedures are required to accomplish this task? (Choose three.)Correct
Incorrect
Hint
For multiple PVC's on a single interface, you must use subinterfaces, with each subinterface configured for each PVC. Each subinterface will then have its own IP address, and no IP address will be assigned to the main interface. -
Question 199 of 555
199. Question
What occurs on a Frame Relay network when the CIR is exceeded?Correct
Incorrect
Hint
Committed information rate (CIR): The minimum guaranteed data transfer rate agreed to by the Frame Relay switch. Frames that are sent in excess of the CIR are marked as discard eligible (DE) which means they can be dropped if the congestion occurs within the Frame Relay network. Note: In the Frame Relay frame format, there is a bit called Discard eligible (DE) bit that is used to identify frames that are first to be dropped when the CIR is exceeded. -
Question 200 of 555
200. Question
Which two statements about using the CHAP authentication mechanism in a PPP link are true? (Choose two.)Correct
Incorrect
Hint
CHAP is an authentication scheme used by Point to Point Protocol (PPP) servers to validate the identity of remote clients. CHAP periodically verifies the identity of the client by using a three-way handshake. This happens at the time of establishing the initial link (LCP), and may happen again at any time afterwards. The verification is based on a shared secret (such as the client user's password). -
Question 201 of 555
201. Question
Correct
Incorrect
Hint
DLCI-Data Link Connection Identifier Bits: The DLCI serves to identify the virtual connection so that the receiving end knows which information connection a frame belongs to. Note that this DLCI has only local significance. Frame Relay is strictly a Layer 2 protocol suite. -
Question 202 of 555
202. Question
What is the result of issuing the frame-relay map ip 192.168.1.2 202 broadcast command?Correct
Incorrect
Hint
This command identifies the DLCI that should be used for all packets destined to the 192.168.1.2 address. In this case, DLCI 202 should be used. -
Question 203 of 555
203. Question
Which PPP subprotocol negotiates authentication options?Correct
Incorrect
Hint
The PPP Link Control Protocol (LCP) is documented in RFC 1661. LPC negotiates link and PPP parameters to dynamically configure the data link layer of a PPP connection. Common LCP options include the PPP MRU, the authentication protocol, compression of PPP header fields, callback, and multilink options. -
Question 204 of 555
204. Question
What are two characteristics of Frame Relay point-to-point subinterfaces? (Choose two.)Correct
Incorrect
Hint
Subinterfaces are used for point to point frame relay connections, emulating virtual point to point leased lines. Each subinterface requires a unique IP address/subnet. Remember, you can not assign multiple interfaces in a router that belong to the same IP subnet. -
Question 205 of 555
205. Question
What command is used to verify the DLCI destination address in a Frame Relay static configuration?Correct
Incorrect
Hint
Sample "show frame-relay map" output: R1#sh frame mapSerial0/0 (up): ip 10.4.4.1 dlci 401(0x191,0x6410), dynamic,broadcast,, status defined, activeSerial0/0 (up): ip 10.4.4.3 dlci 403(0x193,0x6430), dynamic,broadcast,, status defined, activeSerial0/0 (up): ip 10.4.4.4 dlci 401(0x191,0x6410), static,CISCO, status defined, active -
Question 206 of 555
206. Question
What is the purpose of Inverse ARP?Correct
Incorrect
Hint
Dynamic address mapping relies on the Frame Relay Inverse Address Resolution Protocol (Inverse ARP), defined by RFC 1293, to resolve a next hop network protocol (IP) address to a local DLCI value. The Frame Relay router sends out Inverse ARP requests on its Frame Relay PVC to discover the protocol address of the remote device connected to the Frame Relay network. The responses to the Inverse ARP requests are used to populate an address-to-DLCI mapping table on the Frame Relay router or access server. The router builds and maintains this address-to- DLCI mapping table, which contains all resolved Inverse ARP requests, including both dynamic and static mapping entries. -
Question 207 of 555
207. Question
Two routers named Atlanta and Brevard are connected via their serial interfaces as illustrated, but they are unable to communicate. The Atlanta router is known to have the correct configuration.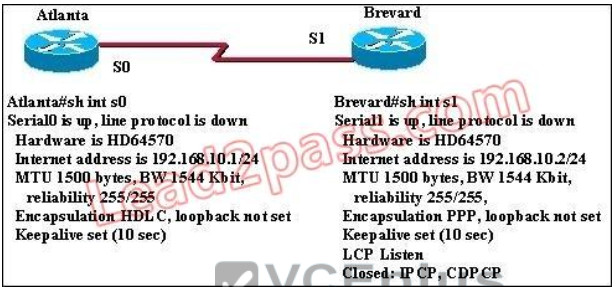 Given the partial configurations, identify the fault on the Brevard router that is causing the lack of connectivity. Correct
Given the partial configurations, identify the fault on the Brevard router that is causing the lack of connectivity. Correct
Incorrect
Hint
The correct explanation should be that the Atlanta router is usng HDLC while the Brevard is using PPP. These need to match on both ends. -
Question 208 of 555
208. Question
Refer to the exhibit. The company uses EIGRP as the routing protocol. What path will packets take from a host on the 192.168.10.192/26 network to a host on the LAN attached to router R1?
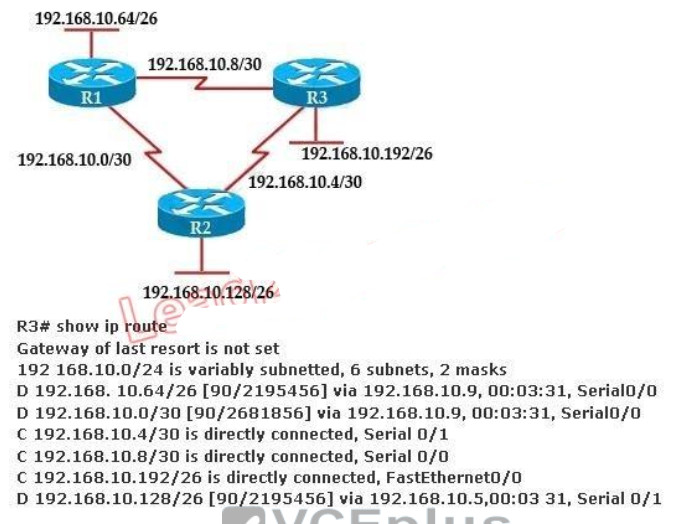 Correct
Correct
Incorrect
Hint
Host on the LAN attached to router R1 belongs to 192.168.10.64/26 subnet. From the output of the routing table of R3 we learn this network can be reach via 192.168.10.9, which is an IP address in 192.168.10.8/30 network (the network between R1 & R3) -> packets destined for 192.168.10.64 will be routed from R3 -> R1 -> LAN on R1. -
Question 209 of 555
209. Question
How does using the service password-encryption command on a router provide additional security?Correct
Incorrect
Hint
By using this command, all the (current and future) passwords are encrypted. This command is primarily useful for keeping unauthorized individuals from viewing your password in your configuration file -
Question 210 of 555
210. Question
Refer to the exhibit. Switch port FastEthernet 0/24 on ALSwitch1 will be used to create an IEEE 802.1Q-compliant trunk to another switch. Based on the output shown, what is the reason the trunk does not form, even though the proper cabling has been attached?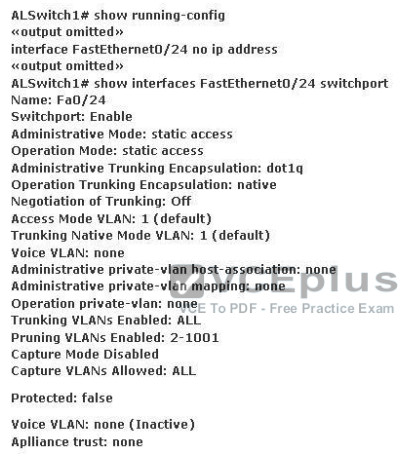 Correct
Correct
Incorrect
Hint
According to the output shown the switchport (layer 2 Switching) is enabled and the port is in access mode. To make a trunk link the port should configured as a trunk port, not an access port, by using the following command: (Config-if)#switchport mode trunk -
Question 211 of 555
211. Question
Refer to the exhibit. In the Frame Relay network, which IP addresses would be assigned to the interfaces with point-to- point PVCs?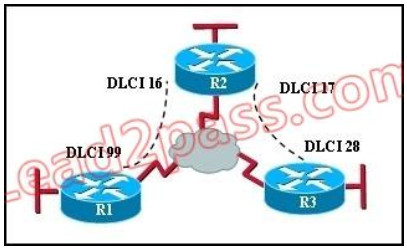 Correct
Correct
Incorrect
Hint
With point to point PVC, each connection needs to be in a separate subnet. The R2-R1 connection (DLCI 16 to 99) would have each router within the same subnet. Similarly, the R3-R1 connection would also be in the same subnet, but it must be in a different one than the R2-R1 connection. -
Question 212 of 555
212. Question
Refer to the exhibit. A new subnet with 60 hosts has been added to the network. Which subnet address should this network use to provide enough usable addresses while wasting the fewest addresses? Correct
Correct
Incorrect
Hint
A subnet with 60 host is 2*2*2*2*2*2 = 64 -2 == 62 6 bits needed for hosts part. Therefore subnet bits are 2 bits (8-6) in fourth octet. 8bits+ 8bits+ 8bits + 2bits = /26 /26 bits subnet is 24bits + 11000000 = 24bits + 192 256 -192 = 64 0 - 63 64 - 127 -
Question 213 of 555
213. Question
Refer to the exhibit. All of the routers in the network are configured with the ip subnet-zero command. Which network addresses should be used for Link A and Network A? (Choose two.)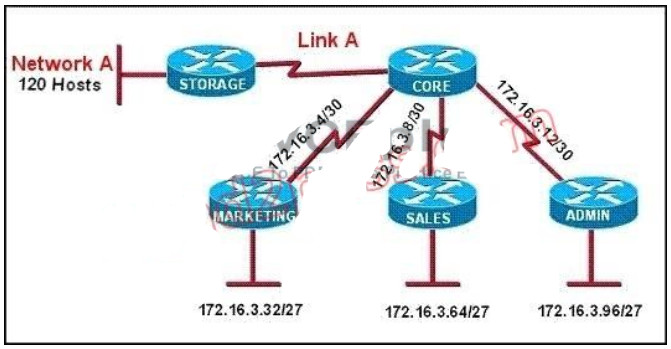 Correct
Correct
Incorrect
Hint
Only a /30 is needed for the point to point link and sine the use of the ip subnet-zero was used, 172.16.3.0/30 is valid. Also, a /25 is required for 120 hosts and again 172.16.3.128/25 is the best, valid option -
Question 214 of 555
214. Question
A router has learned three possible routes that could be used to reach a destination network. One route is from EIGRP and has a composite metric of 20514560. Another route is from OSPF with a metric of 782. The last is from RIPv2 and has a metric of 4. Which route or routes will the router install in the routing table?Correct
Incorrect
Hint
When one route is advertised by more than one routing protocol, the router will choose to use the routing protocol which has lowest Administrative Distance. The Administrative Distances of popular routing protocols are listed below:
-
Question 215 of 555
215. Question
A network administrator needs to allow only one Telnet connection to a router. For anyone viewing the configuration and issuing the show run command, the password for Telnet access should be encrypted. Which set of commands will accomplish this task?Correct
Incorrect
Hint
Only one VTY connection is allowed which is exactly what's requested. Incorrect answer: command. line vty0 4 would enable all 5 vty connections. -
Question 216 of 555
216. Question
Refer to the exhibit. The speed of all serial links is E1 and the speed of all Ethernet links is 100 Mb/s. A static route will be established on the Manchester router to direct traffic toward the Internet over the most direct path available. What configuration on the Manchester router will establish a route toward the Internet for traffic that originates from workstations on the Manchester LAN?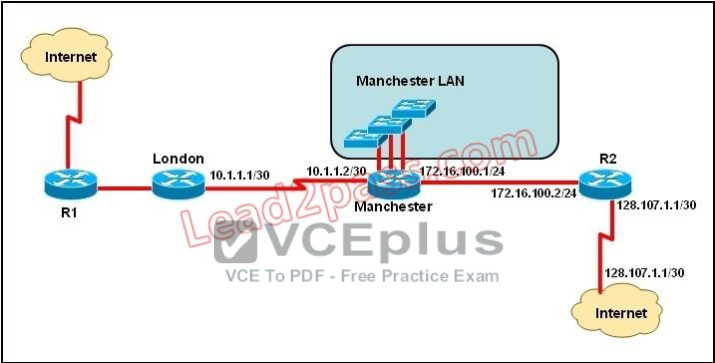 Correct
Correct
Incorrect
Hint
Explanation: We use default routing to send packets with a remote destination network not in the routing table to the next-hop router. You should generally only use default routing on stub networks--those with only one exit path out of the network. According to exhibit, all traffic towards Internet that originates from workstations should forward to Router R1. Syntax for default route is: ip route. -
Question 217 of 555
217. Question
Refer to the exhibit. The network administrator must establish a route by which London workstations can forward traffic to the Manchester workstations. What is the simplest way to accomplish this?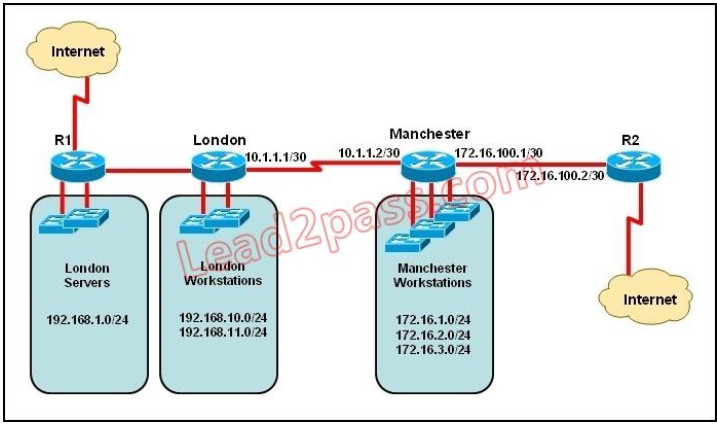 Correct
Correct
Incorrect
Hint
This static route will allow for communication to the Manchester workstations and it is better to use this more specific route than a default route as traffic destined to the Internet will then not go out the London Internet connection. -
Question 218 of 555
218. Question
Refer to the exhibit. The network administrator requires easy configuration options and minimal routing protocol traffic. What two options provide adequate routing table information for traffic that passes between the two routers and satisfy the requests of the network administrator? (Choose two.)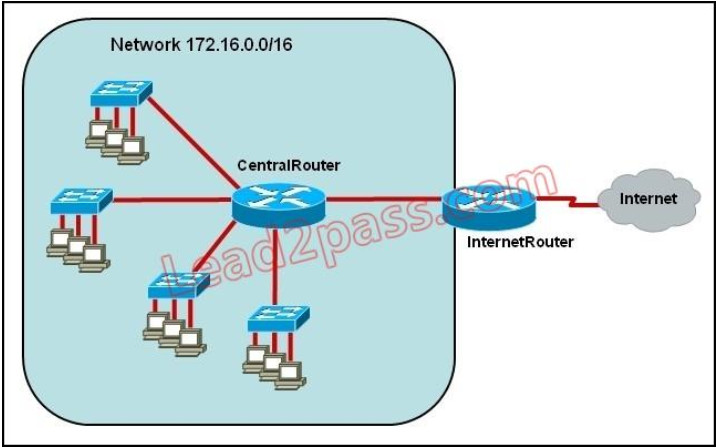 Correct
Correct
Incorrect
Hint
The use of static routes will provide the necessary information for connectivity while producing no routing traffic overhead. -
Question 219 of 555
219. Question
What is the effect of using the service password-encryption command?Correct
Incorrect
Hint
Enable vty, console, AUX passwords are configured on the Cisco device. Use the show run command to show most passwords in clear text. If the service password-encryption is used, all the passwords are encrypted. As a result, the security of device access is improved. -
Question 220 of 555
220. Question
Refer to the exhibit. What is the effect of the configuration that is shown?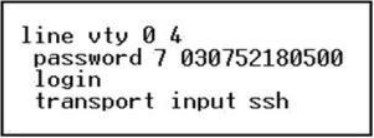 Correct
Correct
Incorrect
Hint
Secure Shell (SSH) is a protocol which provides a secure remote access connection to network devices. Communication between the client and server is encrypted in both SSH version 1 and SSH version 2. If you want to prevent non-SSH connections, add the "transport input ssh" command under the lines to limit the router to SSH connections only. Straight (non-SSH) Telnets are refused. www.cisco.com/warp/public/707/ssh.shtml -
Question 221 of 555
221. Question
Refer to the exhibit. What is the reason that the interface status is "administratively down, line protocol down"?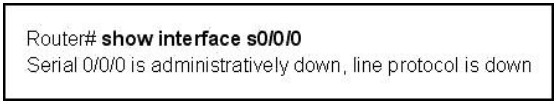 Correct
Correct
Incorrect
Hint
Interface can be enabled or disabled with shutdown/no shutdown command. If you interface is down, it will display administratively down status. You can bring up an interface having administratively down interface using no shutdown command. -
Question 222 of 555
222. Question
Refer to the exhibit. A junior network administrator was given the task of configuring port security on SwitchA to allow only PC_A to access the switched network through port fa0/1. If any other device is detected, the port is to drop frames from this device. The administrator configured the interface and tested it with successful pings from PC_A to RouterA, and then observes the output from these two show commands. Which two of these changes are necessary for SwitchA to meet the requirements? (Choose two.)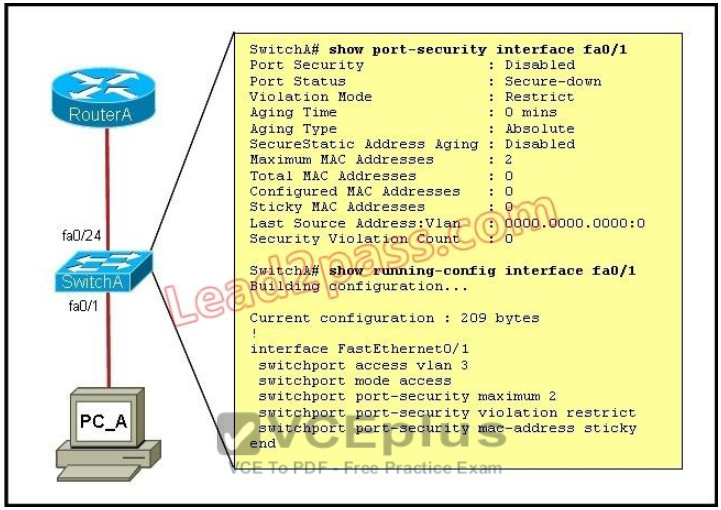 Correct
Correct
Incorrect
Hint
From the output we can see that port security is disabled so this needs to be enabled. Also, the maximum number of devices is set to 2 so this needs to be just one if we want the single host to have access and nothing else. -
Question 223 of 555
223. Question
Refer to the exhibit. When running OSPF, what would cause router A not to form an adjacency with router B?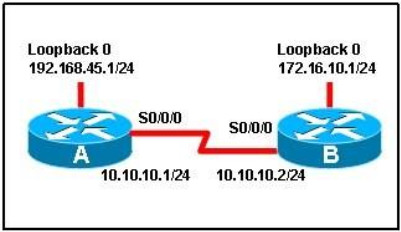 Correct
Correct
Incorrect
Hint
To form an adjacency (become neighbor), router A & B must have the same Hello interval, Dead interval and AREA number.s -
Question 224 of 555
224. Question
Which two of these statements are true of IPv6 address representation? (Choose two.)Correct
Incorrect
Hint
Leading zeros in IPv6 are optional do that 05C7 equals 5C7 and 0000 equals 0 -> D is not correct. -
Question 225 of 555
225. Question
Which set of commands is recommended to prevent the use of a hub in the access layer?Correct
Incorrect
Hint
This question is to examine the layer 2 security configuration. In order to satisfy the requirements of this question, you should perform the following configurations in the interface mode: First, configure the interface mode as the access mode Second, enable the port security and set the maximum number of connections to 1. -
Question 226 of 555
226. Question
What is known as "one-to-nearest" addressing in IPv6?Correct
Incorrect
Hint
IPv6 Anycast addresses are used for one-to-nearest communication, meaning an Anycast address is used by a device to send data to one specific recipient (interface) that is the closest out of a group of recipients (interfaces). -
Question 227 of 555
227. Question
What is the first 24 bits in a MAC address called?Correct
Incorrect
Hint
An Organizationally Unique Identifier (OUI) is a 24-bit number that uniquely identifies a vendor, manufacturer, or other organization globally or worldwide. They are used as the first 24 nits of the MAC address to uniquely identify a particular piece of equipment. -
Question 228 of 555
228. Question
Refer to the exhibit. Which subnet mask will place all hosts on Network B in the same subnet with the least amount of wasted addresses? Correct
Correct
Incorrect
Hint
310 hosts < 512 = 29 -> We need a subnet mask of 9 bits 0 -> 1111 1111.1111 1111.1111 1110.0000 0000 -> 255.255.254.0 -
Question 229 of 555
229. Question
Refer to the exhibit. What is the most appropriate summarization for these routes?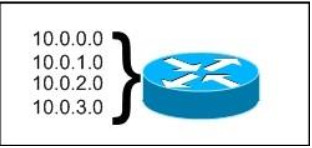 Correct
Correct
Incorrect
Hint
The 10.0.0.0/22 subnet mask will include the 10.0.0.0, 10.0.1.0, 10.0.2.0, and 10.0.3.0 networks, and only those four networks. -
Question 230 of 555
230. Question
What is the difference between a CSU/DSU and a modem?Correct
Incorrect
Hint
CSU/DSU is used to convert digital signals from a router to a network circuit such as a T1, while a modem is used to convert digital signals over a regular POTS line. -
Question 231 of 555
231. Question
Which two are features of IPv6? (Choose two.)Correct
Incorrect
Hint
IPv6 addresses are classified by the primary addressing and routing methodologies common in networkinG. unicast addressing, anycast addressing, and multicast addressing. -
Question 232 of 555
232. Question
Which two are advantages of static routing when compared to dynamic routing? (Choose two.)Correct
Incorrect
-
Question 233 of 555
233. Question
A network administrator needs to configure port security on a switch. Which two statements are true? (Choose two.)Correct
Incorrect
Hint
Follow these guidelines when configuring port security: + Port security can only be configured on static access ports, trunk ports, or 802.1Q tunnel ports. + A secure port cannot be a dynamic access port. + A secure port cannot be a destination port for Switched Port Analyzer (SPAN). + A secure port cannot belong to a Fast EtherChannel or Gigabit EtherChannel port group. + You cannot configure static secure or sticky secure MAC addresses on a voice VLAN. + When you enable port security on an interface that is also configured with a voice VLAN, you must set the maximum allowed secure addresses on the port to at least two. + If any type of port security is enabled on the access VLAN, dynamic port security is automatically enabled on the voice VLAN. + When a voice VLAN is configured on a secure port that is also configured as a sticky secure port, all addresses seen on the voice VLAN are learned as dynamic secure addresses, and all addresses seen on the access VLAN (to which the port belongs) are learned as sticky secure addresses. + The switch does not support port security aging of sticky secure MAC addresses. + The protect and restrict options cannot be simultaneously enabled on an interface. http://www.cisco.com/en/US/docs/switches/lan/catalyst3550/software/release/12.1_19_ea1/configuration/guide/swtrafc.html -
Question 234 of 555
234. Question
What are three features of the IPv6 protocol? (Choose three.)Correct
Incorrect
Hint
An important feature of IPv6 is that it allows plug and play option to the network devices by allowing them to configure themselves independently. It is possible to plug a node into an IPv6 network without requiring any human intervention. This feature was critical to allow network connectivity to an increasing number of mobile devices. This is accomplished by autoconfiguration. IPv6 does not implement traditional IP broadcast, i.e. the transmission of a packet to all hosts on the attached link using a special broadcast address, and therefore does not define broadcast addresses. In IPv6, the same result can be achieved by sending a packet to the link-local all nodes multicast group at address ff02::1, which is analogous to IPv4 multicast to address 224.0.0.1. -
Question 235 of 555
235. Question
Which command enables IPv6 forwarding on a Cisco router?Correct
Incorrect
Hint
to enable IPv6 routing on the Cisco router use the following command:ipv6 unicast-routing
If this command is not recognized, your version of IOS does not support IPv6. -
Question 236 of 555
236. Question
Which command encrypts all plaintext passwords?Correct
Incorrect
Hint
The "service password-encryption" command allows you to encrypt all passwords on your router so they can not be easily guessed from your running-config. This command uses a very weak encryption because the router has to be very quickly decode the passwords for its operation. It is meant to prevent someone from looking over your shoulder and seeing the password, that is all. This is configured in global configuration mode. -
Question 237 of 555
237. Question
You have been asked to come up with a subnet mask that will allow all three web servers to be on the same network while providing the maximum number of subnets. Which network address and subnet mask meet this requirement?Correct
Incorrect
Hint
A subnet mask of 255.255.255.248 will allow for up to 6 hosts to reside in this network. A subnet mask of 255.255.255.252 will allow for only 2 usable IP addresses, since we can not use the network or broadcast address -
Question 238 of 555
238. Question
Given an IP address 172.16.28.252 with a subnet mask of 255.255.240.0, what is the correct network address?Correct
Incorrect
Hint
For this example, the network range is 172.16.16.1 - 172.16.31.254, the network address is 172.16.16.0 and the broadcast IP address is 172.16.31.255. -
Question 239 of 555
239. Question
Which IPv6 address is the equivalent of the IPv4 interface loopback address 127.0.0.1?Correct
Incorrect
Hint
In IPv6 the loopback address is written as, This is a 128bit number, with the first 127 bits being '0' and the 128th bit being '1'. It's just a single address, so could also be written as ::1/128. -
Question 240 of 555
240. Question
You are working in a data center environment and are assigned the address range 10.188.31.0/23. You are asked to develop an IP addressing plan to allow the maximum number of subnets with as many as 30 hosts each. Which IP address range meets these requirements?Correct
Incorrect
Hint
Each subnet has 30 hosts < 32 = 25 so we need a subnet mask which has at least 5 bit 0s -> /27. Also the question requires the maximum number of subnets (which minimum the number of hosts- per-subnet) so /27 is the best choice -> . -
Question 241 of 555
241. Question
Which parameter or parameters are used to calculate OSPF cost in Cisco routers?Correct
Incorrect
Hint
The well-known formula to calculate OSPF cost is Cost = 108 / Bandwidth -
Question 242 of 555
242. Question
Why do large OSPF networks use a hierarchical design? (Choose three.)Correct
Incorrect
Hint
OSPF implements a two-tier hierarchical routing model that uses a core or backbone tier known as area zero (0). Attached to that backbone via area border routers (ABRs) are a number of secondary tier areas. The hierarchical approach is used to achieve the following: Rapid convergence because of link and/or switch failures Deterministic traffic recovery Scalable and manageable routing hierarchy, reduced routing overhead. -
Question 243 of 555
243. Question
Hotspot Question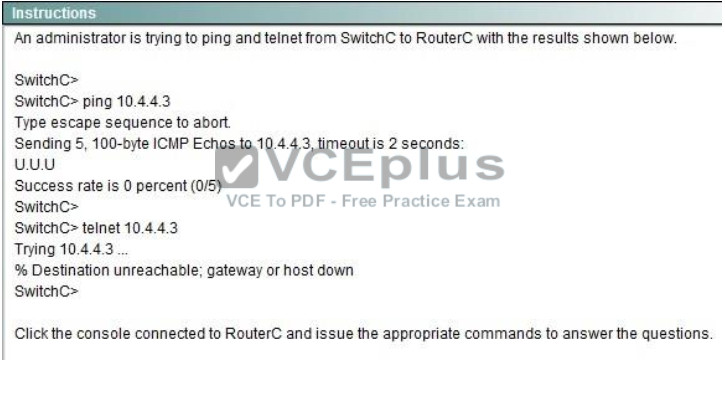
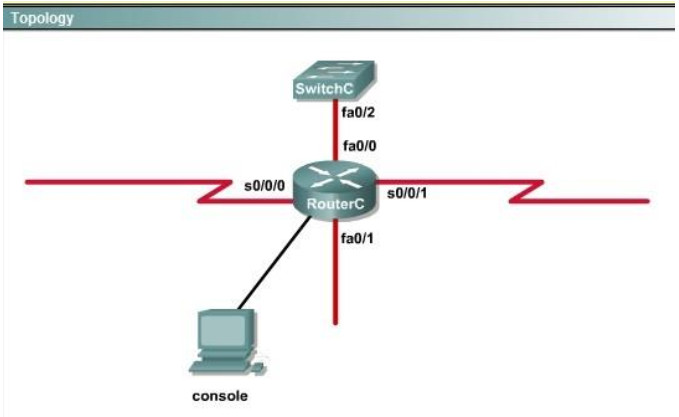

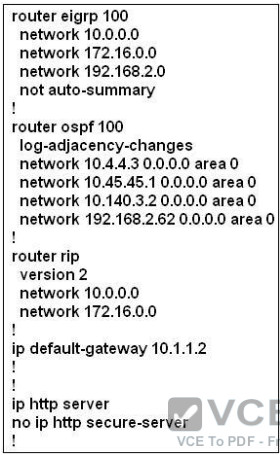
 What would be the effect of issuing the command ip access-group 114 in to the fa0/0 interface? Correct
What would be the effect of issuing the command ip access-group 114 in to the fa0/0 interface? Correct
Incorrect
Hint
From the output of access-list 114: access-list 114 permit ip 10.4.4.0 0.0.0.255 any we can easily understand that this access list allows all traffic (ip) from 10.4.4.0/24 network -
Question 244 of 555
244. Question
Hotspot Question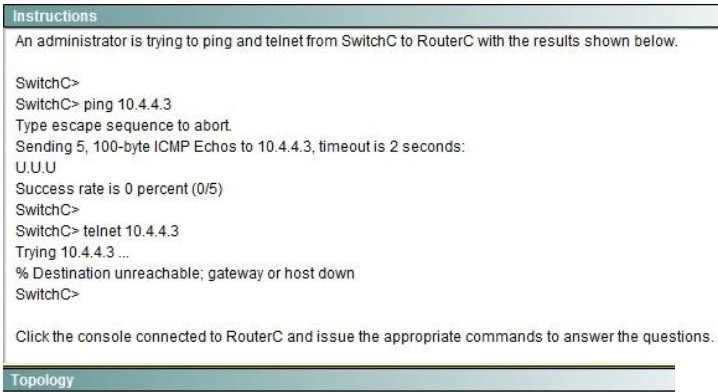
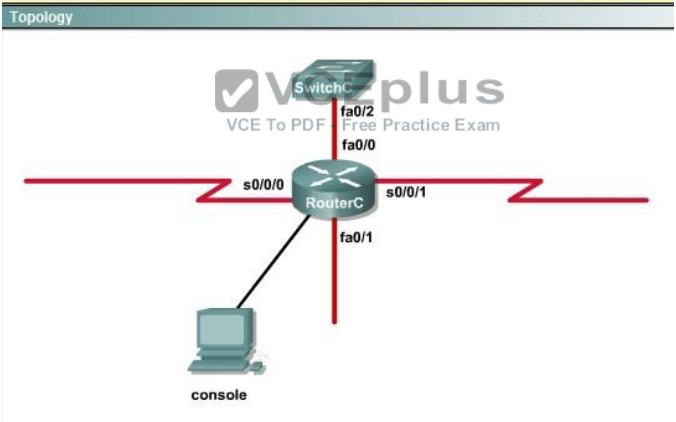

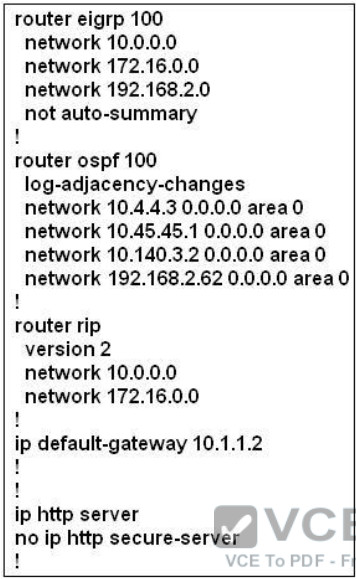
 What would be the effect of Issuing the command ip access-group 115 in on the s0/0/1 interface? Correct
What would be the effect of Issuing the command ip access-group 115 in on the s0/0/1 interface? Correct
Incorrect
Hint
First let's see what was configured on interface S0/0/1:
-
Question 245 of 555
245. Question
Refer to the exhibit. Based on the information given, which switch will be elected root bridge and why?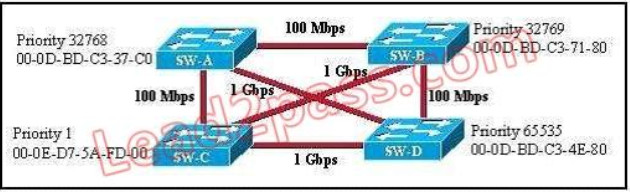 Correct
Correct
Incorrect
-
Question 246 of 555
246. Question
In a switched environment, what does the IEEE 802.1Q standard describe?Correct
Incorrect
Hint
A broadcast domain must sometimes exist on more than one switch in the network. To accomplish this, one switch must send frames to another switch and indicate which VLAN a particular frame belongs to. On Cisco switches, a trunk link is created to accomplish this VLAN identification. ISL and IEEE 802.1Q are different methods of putting a VLAN identifier in a Layer 2 frame. The IEEE 802.1Q protocol interconnects VLANs between multiple switches, routers, and servers. With 802.1Q, a network administrator can define a VLAN topology to span multiple physical devices. Cisco switches support IEEE 802.1Q for FastEthernet and Gigabit Ethernet interfaces. An 802.1Q trunk link provides VLAN identification by adding a 4-byte tag to an Ethernet Frame as it leaves a trunk port. -
Question 247 of 555
247. Question
What are three benefits of GLBP? (Choose three.)Correct
Incorrect
-
Question 248 of 555
248. Question
Which three statements about HSRP operation are true? (Choose three.)Correct
Incorrect
Hint
The virtual MAC address of HSRP version 1 is 0000.0C07.ACxx, where xx is the HSRP group number in hexadecimal based on the respective interface. For example, HSRP group 10 uses the HSRP virtual MAC address of 0000.0C07.AC0A. HSRP version 2 uses a virtual MAC address of 0000.0C9F.FXXX (XXX: HSRP group in hexadecimal) -
Question 249 of 555
249. Question
Which three statements about Syslog utilization are true? (Choose three.)Correct
Incorrect
-
Question 250 of 555
250. Question
A network administrator enters the following command on a router: logging trap 3. What are three message types that will be sent to the Syslog server? (Choose three.)Correct
Incorrect
-
Question 251 of 555
251. Question
What is the default Syslog facility level?Correct
Incorrect
-
Question 252 of 555
252. Question
What command instructs the device to timestamp Syslog debug messages in milliseconds?Correct
Incorrect
Hint
The "service timestamps debug" command configures the system to apply a time stamp to debugging messages. The time-stamp format for datetime is MMM DD HH:MM:SS, where MMM is the month, DD is the date, HH is the hour (in 24-hour notation), MM is the minute, and SS is the second. With the additional keyword msec, the system includes milliseconds in the time stamp, in the format HH:DD:MM:SS.mmm, where .mmm is milliseconds -
Question 253 of 555
253. Question
Refer to the exhibit. What is the cause of the Syslog output messages?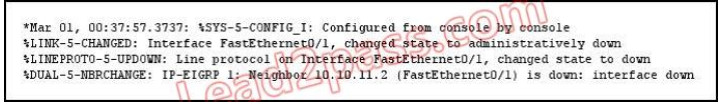 Correct
Correct
Incorrect
-
Question 254 of 555
254. Question
What are three components that comprise the SNMP framework? (Choose three.)Correct
Incorrect
-
Question 255 of 555
255. Question
What are three components that comprise the SNMP framework? (Choose three.)Correct
Incorrect
-
Question 256 of 555
256. Question
What SNMP message alerts the manager to a condition on the network?Correct
Incorrect
-
Question 257 of 555
257. Question
What authentication type is used by SNMPv2?Correct
Incorrect
-
Question 258 of 555
258. Question
Which three statements about the features of SNMPv2 and SNMPv3 are true? (Choose three.)Correct
Incorrect
-
Question 259 of 555
259. Question
What are three reasons to collect Netflow data on a company network? (Choose three.)Correct
Incorrect
-
Question 260 of 555
260. Question
What Netflow component can be applied to an interface to track IPv4 traffic?Correct
Incorrect
Hint
Flow monitors are the Flexible NetFlow component that is applied to interfaces to perform network traffic monitoring. Flow monitors consist of a record and a cache. You add the record to the flow monitor after you create the flow monitor. The flow monitor cache is automatically created at the time the flow monitor is applied to the first interface. Flow data is collected from the network traffic during the monitoring process based on the key and nonkey fields in the record, which is configured for the flow monitor and stored in the flow monitor cache. For example, the following example creates a flow monitor named FLOW-MONITOR-1 and enters Flexible NetFlow flow monitor configuration mode: Router(config)# flow monitor FLOW-MONITOR-1 Router(config-flow-monitor)# -
Question 261 of 555
261. Question
What Cisco IOS feature can be enabled to pinpoint an application that is causing slow network performance?Correct
Incorrect
-
Question 262 of 555
262. Question
What command visualizes the general NetFlow data on the command line?Correct
Incorrect
Hint
The "show ip cache flow" command displays a summary of the NetFlow
-
Question 263 of 555
263. Question
What are three values that must be the same within a sequence of packets for Netflow to consider them a network flow? (Choose three.)Correct
Incorrect
-
Question 264 of 555
264. Question
Refer to the exhibit. A network administrator is configuring an EtherChannel between SW1 and SW2. The SW1 configuration is shown. What is the correct configuration for SW2?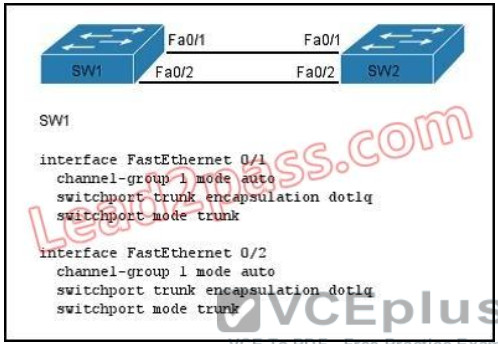 Correct
Correct
Incorrect
-
Question 265 of 555
265. Question
What are three factors a network administrator must consider before implementing Netflow in the network? (Choose three.)Correct
Incorrect
-
Question 266 of 555
266. Question
Which two statements about the OSPF Router ID are true? (Choose two.)Correct
Incorrect
-
Question 267 of 555
267. Question
What parameter can be different on ports within an EtherChannel?Correct
Incorrect
-
Question 268 of 555
268. Question
What are two benefits of using a single OSPF area network design? (Choose two.)Correct
Incorrect
-
Question 269 of 555
269. Question
Refer to the exhibit. What set of commands was configured on interface Fa0/3 to produce the given output?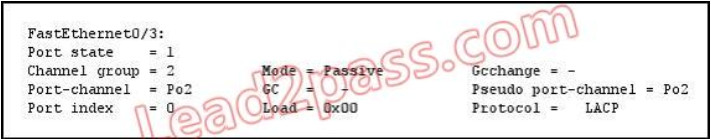 Correct
Correct
Incorrect
-
Question 270 of 555
270. Question
Refer to the exhibit. If the devices produced the given output, what is the cause of the EtherChannel problem?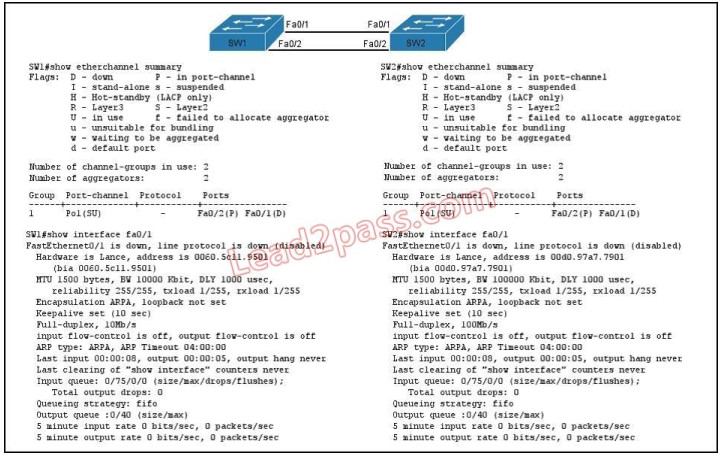 Correct
Correct
Incorrect
-
Question 271 of 555
271. Question
What are two enhancements that OSPFv3 supports over OSPFv2? (Choose two.)Correct
Incorrect
-
Question 272 of 555
272. Question
When a router undergoes the exchange protocol within OSPF, in what order does it pass through each state?Correct
Incorrect
-
Question 273 of 555
273. Question
A network administrator creates a layer 3 EtherChannel, bundling four interfaces into channel group 1. On what interface is the IP address configured?Correct
Incorrect
-
Question 274 of 555
274. Question
Refer to the exhibit. If the router Cisco returns the given output and has not had its router ID set manually, what value will OSPF use as its router ID?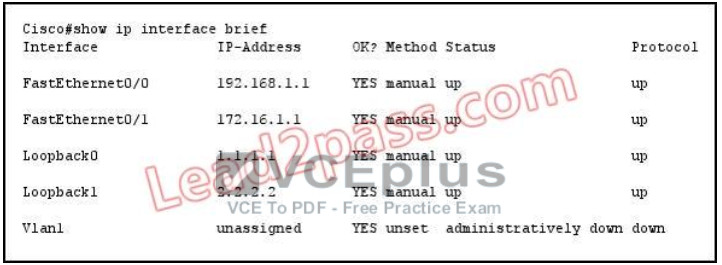 Correct
Correct
Incorrect
-
Question 275 of 555
275. Question
What command sequence will configure a router to run OSPF and add network 10.1.1.0 /24 to area 0?Correct
Incorrect
-
Question 276 of 555
276. Question
What OSPF command, when configured, will include all interfaces into area 0?Correct
Incorrect
-
Question 277 of 555
277. Question
Which statement describes the process ID that is used to run OSPF on a router?Correct
Incorrect
-
Question 278 of 555
278. Question
Which three are the components of SNMP? (Choose three)Correct
Incorrect
Hint
SNMP is an application-layer protocol that provides a message format for communication between SNMP managers and agents. SNMP provides a standardized framework and a common language used for the monitoring and management of devices in a network. The SNMP framework has three parts: + An SNMP manager + An SNMP agent + A Management Information Base (MIB) The SNMP manager is the system used to control and monitor the activities of network hosts using SNMP. The most common managing system is called a Network Management System (NMS). The term NMS can be applied to either a dedicated device used for network management, or the applications used on such a device. A variety of network management applications are available for use with SNMP. These features range from simple command-line applications to feature-rich graphical user interfaces (such as the CiscoWorks2000 line of products). The SNMP agent is the software component within the managed device that maintains the data for the device and reports these data, as needed, to managing systems. The agent and MIB reside on the routing device (router, access server, or switch). To enable the SNMP agent on a Cisco routing device, you must define the relationship between the manager and the agent. The Management Information Base (MIB) is a virtual information storage area for network management information, which consists of collections of managed objects -
Question 279 of 555
279. Question
What are the Popular destinations for syslog messages to be saved?Correct
Incorrect
Hint
By default, switches send the output from system messages and debug privileged EXEC commands to a logging process. The logging process controls the distribution of logging messages to various destinations, such as the logging buffer (on RAM), terminal lines (console terminal), or a UNIX syslog server, depending on your configuration. The process also sends messages to the console. Note: Syslog messages can be written to a file in Flash memory although it is not a popular place to use. We can configure this feature with the command logging file flash:filename. -
Question 280 of 555
280. Question
Syslog was configured with a level 3 trap. Which 4 types of logs would be generated (choose four)Correct
Incorrect
Hint
The Message Logging is divided into 8 levels as listed below: Level Keyword Description 0 emergencies System is unusable 1 alerts Immediate action is needed 2 critical Critical conditions exist 3 errors Error conditions exist 4 warnings Warning conditions exist 5 notification Normal, but significant, conditions exist 6 informational Informational messages 7 debugging Debugging messages The highest level is level 0 (emergencies). The lowest level is level 7. If you specify a level with the "logging console level" command, that level and all the higher levels will be displayed. For example, by using the "logging console warnings" command, all the logging of emergencies, alerts, critical, errors, warnings will be displayed. -
Question 281 of 555
281. Question
What are the benefit of using Netflow? (Choose three.)Correct
Incorrect
-
Question 282 of 555
282. Question
Which protocol can cause overload on a CPU of a managed device?Correct
Incorrect
Hint
Sometimes, messages like this might appear in the router console: %SNMP-3-CPUHOG: Processing [chars] of [chars] They mean that the SNMP agent on the device has taken too much time to process a request. You can determine the cause of high CPU use in a router by using the output of the show process cpu command. Note: A managed device is a part of the network that requires some form of monitoring and management (routers, switches, servers, workstations, printers...). -
Question 283 of 555
283. Question
What are the three things that the Netflow uses to consider the traffic to be in a same flow?Correct
Incorrect
Hint
What is an IP Flow? Each packet that is forwarded within a router or switch is examined for a set of IP packet attributes. These attributes are the IP packet identity or fingerprint of the packet and determine if the packet is unique or similar to other packets. Traditionally, an IP Flow is based on a set of 5 and up to 7 IP packet attributes. IP Packet attributes used by NetFlow: + IP source address + IP destination address + Source port + Destination port + Layer 3 protocol type + Class of Service + Router or switch interface -
Question 284 of 555
284. Question
What is the alert message generated by SNMP agents called ?Correct
Incorrect
Hint
A TRAP is a SNMP message sent from one application to another (which is typically on a remote host). Their purpose is merely to notify the other application that something has happened, has been noticed, etc. The big problem with TRAPs is that they're unacknowledged so you don't actually know if the remote application received your oh-so-important message to it. SNMPv2 PDUs fixed this by introducing the notion of an INFORM, which is nothing more than an acknowledged TRAP. -
Question 285 of 555
285. Question
Which three features are added in SNMPv3 over SNMPv2?Correct
Incorrect
-
Question 286 of 555
286. Question
In a GLBP network, who is responsible for the arp request?Correct
Incorrect
-
Question 287 of 555
287. Question
What levels will be trapped if the administrator executes the command router(config)# logging trap 4 (Choose four) ?Correct
Incorrect
Hint
The Message Logging is divided into 8 levels as listed below: Level Keyword Description 0 emergencies System is unusable 1 alerts Immediate action is needed 2 critical Critical conditions exist 3 errors Error conditions exist 4 warnings Warning conditions exist 5 notification Normal, but significant, conditions exist 6 informational Informational messages 7 debugging Debugging messages If you specify a level with the "logging trap level" command, that level and all the higher levels will be logged. For example, by using the "logging trap 4 command, all the logging of emergencies, alerts, critical, errors, warnings will be logged. -
Question 288 of 555
288. Question
Hotspot Question Refer to the topology. Your company has decided to connect the main office with three other remote branch offices using point-to-point serial links. You are required to troubleshoot and resolve OSPF neighbor adjacency issues between the main office and the routers located in the remote branch offices.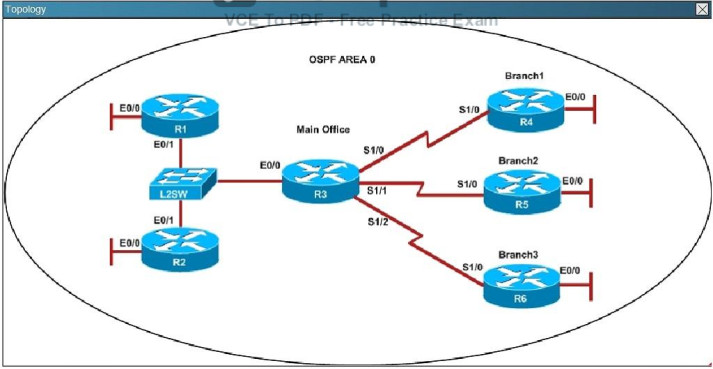 An OSPF neighbor adjacency is not formed between R3 in the main office and R4 in the Branchl office. What is causing the problem? Correct
An OSPF neighbor adjacency is not formed between R3 in the main office and R4 in the Branchl office. What is causing the problem? Correct
Incorrect
Hint
A show running-config command on R3 and R4 shows that R4 is incorrectly configured for area 2:
-
Question 289 of 555
289. Question
Hotspot Question Refer to the topology. Your company has decided to connect the main office with three other remote branch offices using point-to-point serial links. You are required to troubleshoot and resolve OSPF neighbor adjacency issues between the main office and the routers located in the remote branch offices.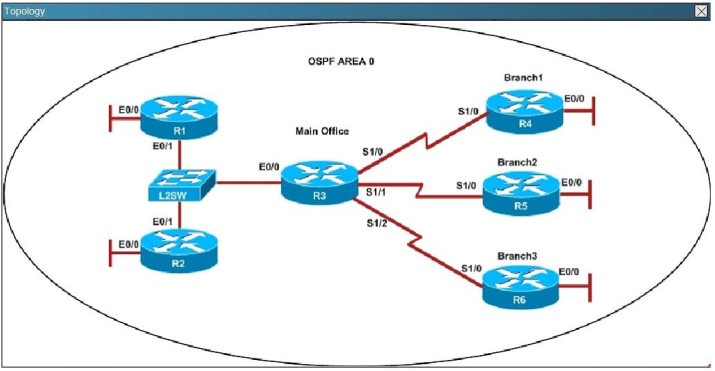 An OSPF neighbor adjacency is not formed between R3 in the main office and R5 in the Branch2 office. What is causing the problem? Correct
An OSPF neighbor adjacency is not formed between R3 in the main office and R5 in the Branch2 office. What is causing the problem? Correct
Incorrect
Hint
The "show ip ospf interface command on R3 and R5 shows that the hello and dead intervals do not match. They are 50 and 200 on R3 and 10 and 40 on R5.
-
Question 290 of 555
290. Question
Hotspot Question Refer to the topology. Your company has decided to connect the main office with three other remote branch offices using point-to-point serial links. You are required to troubleshoot and resolve OSPF neighbor adjacency issues between the main office and the routers located in the remote branch offices.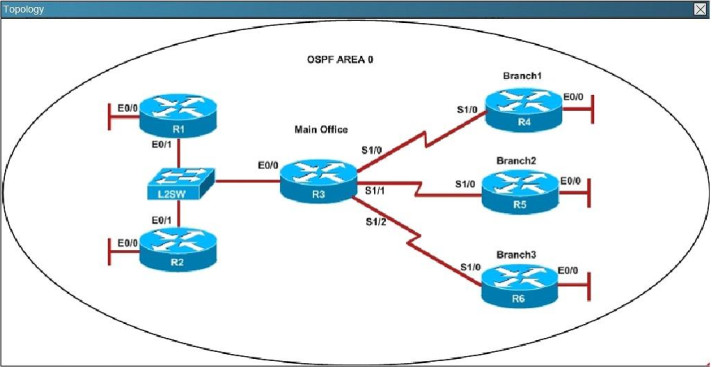 R1 does not form an OSPF neighbor adjacency with R2. Which option would fix the issue? Correct
R1 does not form an OSPF neighbor adjacency with R2. Which option would fix the issue? Correct
Incorrect
Hint
Looking at the configuration of R1, we see that R1 is configured with a hello interval of 25 on interface Ethernet 0/1 while R2 is left with the default of 10 (not configured).
-
Question 291 of 555
291. Question
Hotspot Question Refer to the topology. Your company has decided to connect the main office with three other remote branch offices using point-to-point serial links. You are required to troubleshoot and resolve OSPF neighbor adjacency issues between the main office and the routers located in the remote branch offices.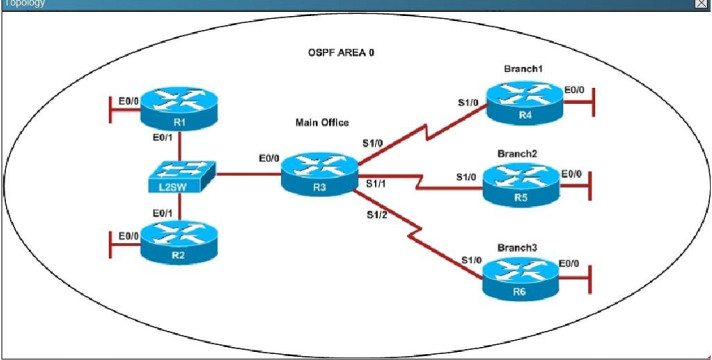 An OSPF neighbor adjacency is not formed between R3 in the main office and R6 in the Branch3 office. What is causing the problem? Correct
An OSPF neighbor adjacency is not formed between R3 in the main office and R6 in the Branch3 office. What is causing the problem? Correct
Incorrect
Hint
Using the show running-config command we see that R6 has been incorrectly configured with the same router ID as R3 under the router OSPF process.
-
Question 292 of 555
292. Question
Hotspot Question Refer to the topology. Your company has connected the routers R1. R2. and R3 with serial links. R2 and R3 are connected to the switches SW1 and SW2, respectively. SW1 and SW2 are also connected to the routers R4 and R5. The EIGRP routing protocol is configured. You are required to troubleshoot and resolve the EIGRP issues between the various routers. Use the appropriate show commands to troubleshoot the issues.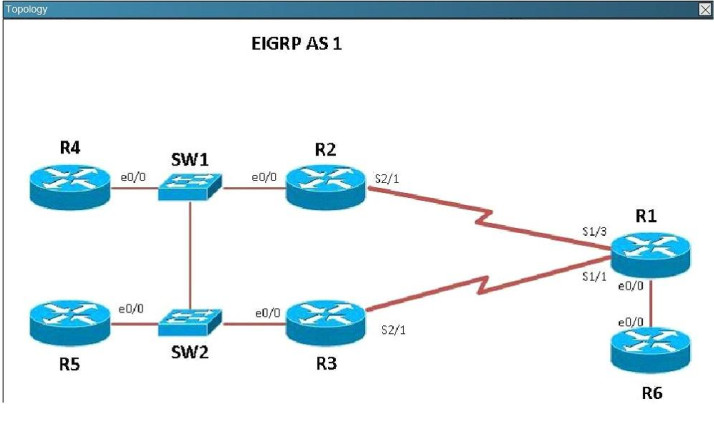 The loopback interfaces on R4 with the IP addresses of 10.4.4.4 /32, 10.4.4.5/32. and 10.4.4.6/32 are not appearing in the routing table of R5 Why are the interfaces missing? Correct
The loopback interfaces on R4 with the IP addresses of 10.4.4.4 /32, 10.4.4.5/32. and 10.4.4.6/32 are not appearing in the routing table of R5 Why are the interfaces missing? Correct
Incorrect
Hint
For an EIGRP neighbor to form, the following must match: - Neighbors must be in the same subnet- K values- AS numbers- Authentication method and key strings Here, we see that R4 is configured for EIGRP AS 2, when it should be AS 1.
-
Question 293 of 555
293. Question
Hotspot Question Refer to the topology. Your company has connected the routers R1. R2. and R3 with serial links. R2 and R3 are connected to the switches SW1 and SW2, respectively. SW1 and SW2 are also connected to the routers R4 and R5. The EIGRP routing protocol is configured. You are required to troubleshoot and resolve the EIGRP issues between the various routers. Use the appropriate show commands to troubleshoot the issues.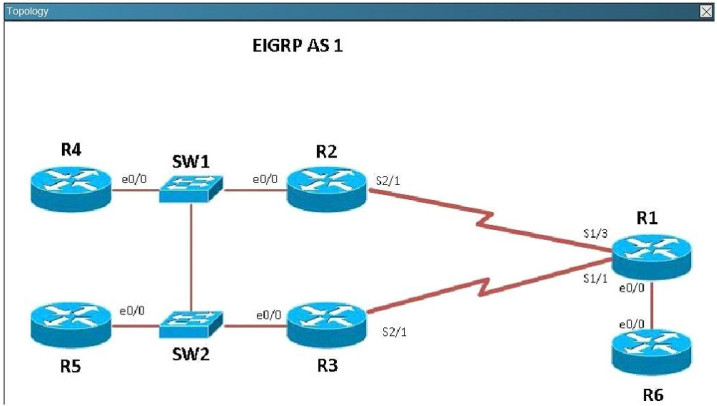 Which path does traffic take from R1 to R5? Correct
Which path does traffic take from R1 to R5? Correct
Incorrect
Hint
Using the "show ip int brief command" on R5 we can see the IP addresses assigned to this router. Then, using the "show ip route" command on R1 we can see that to reach 10.5.5.5 and 10.5.5.55 the preferred path is via Serial 1/3, which we see from the diagram is the link to R2.
-
Question 294 of 555
294. Question
Hotspot Question Refer to the topology. Your company has connected the routers R1. R2. and R3 with serial links. R2 and R3 are connected to the switches SW1 and SW2, respectively. SW1 and SW2 are also connected to the routers R4 and R5. The EIGRP routing protocol is configured. You are required to troubleshoot and resolve the EIGRP issues between the various routers. Use the appropriate show commands to troubleshoot the issues.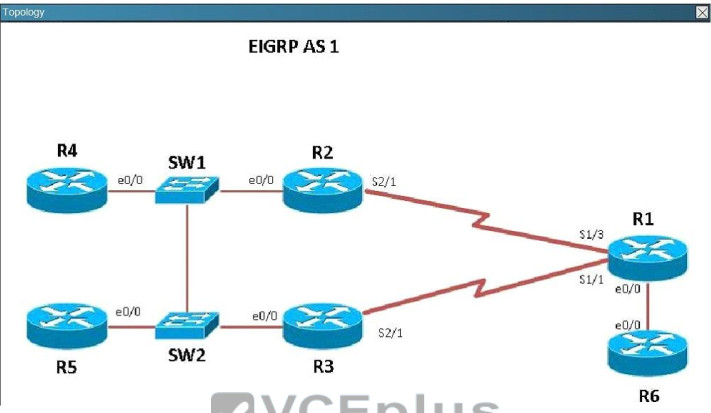 Router R6 does not form an EIGRP neighbor relationship correctly with router R1. What is the cause for this misconfiguration? Correct
Router R6 does not form an EIGRP neighbor relationship correctly with router R1. What is the cause for this misconfiguration? Correct
Incorrect
Hint
The link from R1 to R6 is shown below: As you can see, they are both using e0/0. The IP addresses are in the 192.168.16.0 network:
As you can see, they are both using e0/0. The IP addresses are in the 192.168.16.0 network:
 But when we look at the EIGRP configuration, the "network 192.168.16.0" command is missing on R6.
But when we look at the EIGRP configuration, the "network 192.168.16.0" command is missing on R6.
 Study the following output taken on R1:
R1# Ping 10.5.5.55 source 10.1.1.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 10.5.5.55, timeout is 2 seconds:
Packet sent with a source address of 10.1.1.1
.......
Success rate is 0 percent (0/5)
Study the following output taken on R1:
R1# Ping 10.5.5.55 source 10.1.1.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 10.5.5.55, timeout is 2 seconds:
Packet sent with a source address of 10.1.1.1
.......
Success rate is 0 percent (0/5) -
Question 295 of 555
295. Question
Hotspot Question Refer to the topology. Your company has connected the routers R1. R2. and R3 with serial links. R2 and R3 are connected to the switches SW1 and SW2, respectively. SW1 and SW2 are also connected to the routers R4 and R5. The EIGRP routing protocol is configured. You are required to troubleshoot and resolve the EIGRP issues between the various routers. Use the appropriate show commands to troubleshoot the issues.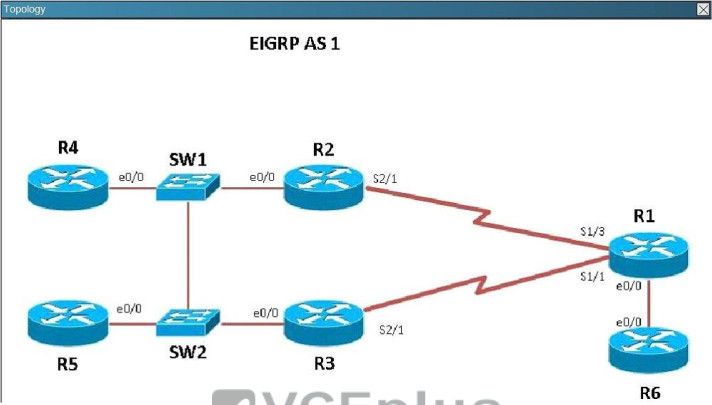 Why are the pings failing? Correct
Why are the pings failing? Correct
Incorrect
Hint
R5 does not have a route to the 10.1.1.1 network, which is the loopback0 IP address of R1. When looking at the EIGRP configuration on R1, we see that the 10.1.1.1 network statement is missing on R1.
-
Question 296 of 555
296. Question
What is a valid HSRP virtual MAC address?Correct
Incorrect
Hint
With HSRP, two or more devices support a virtual router with a fictitious MAC address and unique IP address. There are two version of HSRP. + With HSRP version 1, the virtual router's MAC address is 0000.0c07.ACxx , in which xx is the HSRP group. + With HSRP version 2, the virtual MAC address if 0000.0C9F.Fxxx, in which xxx is the HSRP group. Note: Another case is HSRP for IPv6, in which the MAC address range from 0005.73A0.0000 through 0005.73A0.0FFF. -
Question 297 of 555
297. Question
In GLBP, which router will respond to client ARP requests?Correct
Incorrect
Hint
One disadvantage of HSRP and VRRP is that only one router is in use, other routers must wait for the primary to fail because they can be used. However, Gateway Load Balancing Protocol (GLBP) can use of up to four routers simultaneously. In GLBP, there is still only one virtual IP address but each router has a different virtual MAC address. First a GLBP group must elect an Active Virtual Gateway (AVG). The AVG is responsible for replying ARP requests from hosts/clients. It replies with different virtual MAC addresses that correspond to different routers (known as Active Virtual Forwarders - AVFs) so that clients can send traffic to different routers in that GLBP group (load sharing). -
Question 298 of 555
298. Question
Which statement describes VRRP object tracking?Correct
Incorrect
Hint
Object tracking is the process of tracking the state of a configured object and uses that state to determine the priority of the VRRP router in a VRRP group -
Question 299 of 555
299. Question
What is a global command?Correct
Incorrect
Hint
When you enter global configuration mode and enter a command, it is applied to the running configuration file that is currently running in ram. The configuration of a global command affects the entire router. An example of a global command is one used for the hostname of the router. -
Question 300 of 555
300. Question
An administrator is unsuccessful in adding VLAN 50 to a switch. While troubleshooting the problem, the administrator views the output of the show vtp status command, which is displayed in the graphic. What commands must be issued on this switch to add VLAN 50 to the database? (Choose two.)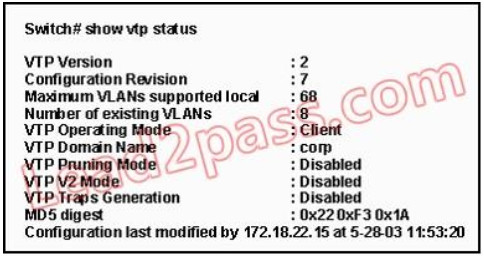 Correct
Correct
Incorrect
-
Question 301 of 555
301. Question
Which of the following IP addresses fall into the CIDR block of 115.64.4.0/22? (Choose three.)Correct
Incorrect
-
Question 302 of 555
302. Question
Which of the following are types of flow control? (Choose three.)Correct
Incorrect
-
Question 303 of 555
303. Question
Refer to the exhibit. After a RIP route is marked invalid on Router_1, how much time will elapse before that route is removed from the routing table?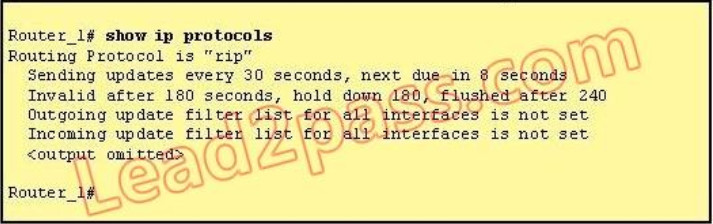 Correct
Correct
Incorrect
-
Question 304 of 555
304. Question
Refer to the exhibit. A network associate has configured the internetwork that is shown in the exhibit, but has failed to configure routing properly.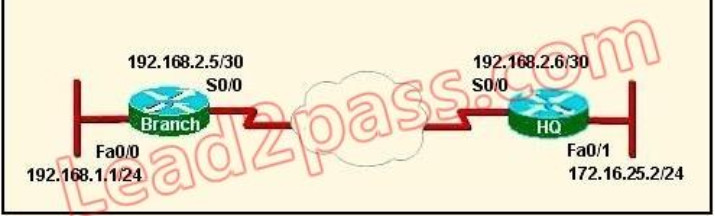 Which configuration will allow the hosts on the Branch LAN to access resources on the HQ LAN with the least impact on router processing and WAN bandwidth? Correct
Which configuration will allow the hosts on the Branch LAN to access resources on the HQ LAN with the least impact on router processing and WAN bandwidth? Correct
Incorrect
-
Question 305 of 555
305. Question
Which additional configuration step is necessary in order to connect to an access point that has SSID broadcasting disabled?Correct
Incorrect
-
Question 306 of 555
306. Question
What is one reason that WPA encryption is preferred over WEP?Correct
Incorrect
-
Question 307 of 555
307. Question
All WAN links inside the ABC University network use PPP with CHAP for authentication security. Which command will display the CHAP authentication process as it occur between two routers in the network?Correct
Incorrect
-
Question 308 of 555
308. Question
Refer to the exhibit. The network is converged. After link-state advertisements are received from Router_A, what information will Router_E contain in its routing table for the subnets 208.149.23.64 and 208.149.23.96?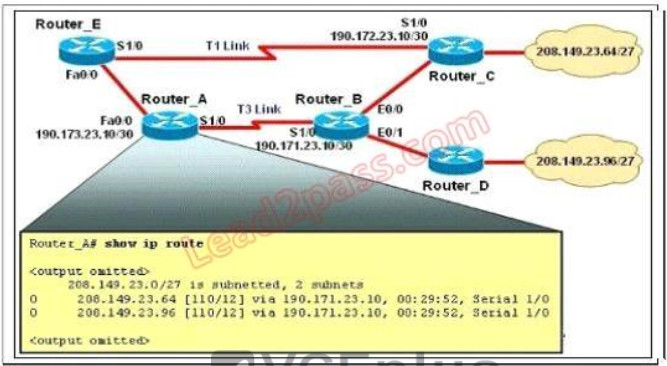 Correct
Correct
Incorrect
-
Question 309 of 555
309. Question
What are two characteristics of SSH? (Choose two.)Correct
Incorrect
-
Question 310 of 555
310. Question
Refer to the exhibit. The access list has been configured on the S0/0 interface of router RTB in the outbound direction. Which two packets, if routed to the interface, will be denied? (Choose two.) access-list 101 deny tcp 192.168.15.32 0.0.0.15 any eq telnet access-list 101 permit ip any any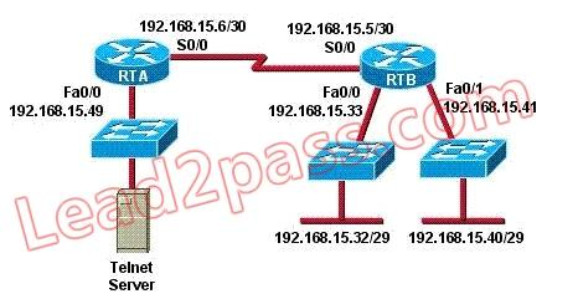 Correct
Correct
Incorrect
-
Question 311 of 555
311. Question
Refer to the graphic. It has been decided that Workstation 1 should be denied access to Server1. Which of the following commands are required to prevent only Workstation 1 from accessing Server1 while allowing all other traffic to flow normally? (Choose two.) Correct
Correct
Incorrect
-
Question 312 of 555
312. Question
An access list was written with the four statements shown in the graphic. Which single access list statement will combine all four of these statements into a single statement that will have exactly the same effect?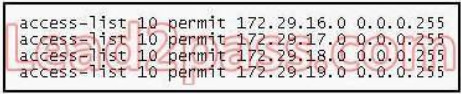 Correct
Correct
Incorrect
-
Question 313 of 555
313. Question
A network administrator wants to add a line to an access list that will block only Telnet access by the hosts on subnet 192.168.1.128/28 to the server at 192.168.1.5. What command should be issued to accomplish this task?Correct
Incorrect
-
Question 314 of 555
314. Question
As a network administrator, you have been instructed to prevent all traffic originating on the LAN from entering the R2 router. Which the following command would implement the access list on the interface of the R2 router? Correct
Correct
Incorrect
-
Question 315 of 555
315. Question
The access control list shown in the graphic has been applied to the Ethernet interface of router R1 using the ip access-group 101 in command. Which of the following Telnet sessions will be blocked by this ACL? (Choose two.)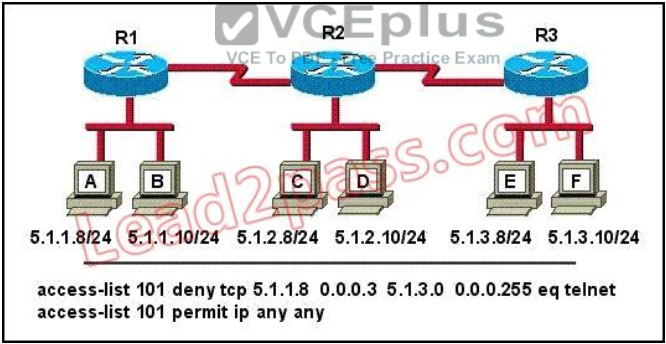 Correct
Correct
Incorrect
-
Question 316 of 555
316. Question
The following access list below was applied outbound on the E0 interface connected to the 192.169.1.8/29 LAN: access-list 135 deny tcp 192.169.1.8 0.0.0.7 eq 20 any access-list 135 deny tcp 192.169.1.8 0.0.0.7 eq 21 any How will the above access lists affect traffic?Correct
Incorrect
-
Question 317 of 555
317. Question
The following configuration line was added to router R1 Access-list 101 permit ip 10.25.30.0 0.0.0.255 any. What is the effect of this access list configuration?Correct
Incorrect
-
Question 318 of 555
318. Question
A default Frame Relay WAN is classified as what type of physical network?Correct
Incorrect
-
Question 319 of 555
319. Question
Which of the following are key characteristics of PPP? (Choose three.)Correct
Incorrect
-
Question 320 of 555
320. Question
How should a router that is being used in a Frame Relay network be configured to avoid split horizon issues from preventing routing updates?Correct
Incorrect
-
Question 321 of 555
321. Question
The Frame Relay network in the diagram is not functioning properly. What is the cause of the problem?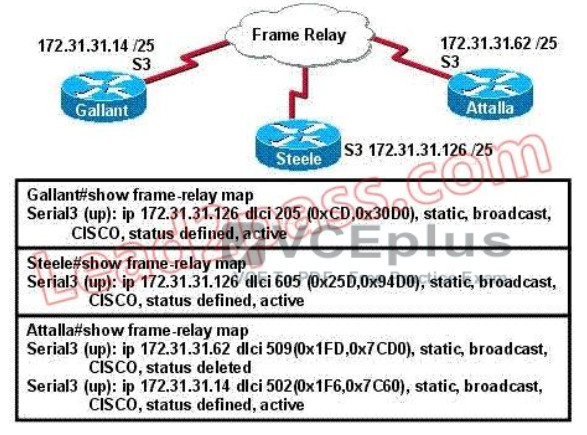 Correct
Correct
Incorrect
-
Question 322 of 555
322. Question
As a CCNA candidate, you must have a firm understanding of the IPv6 address structure. Refer to IPv6 address, could you tell me how many bits are included in each filed?Correct
Incorrect
-
Question 323 of 555
323. Question
Refer to the exhibit. How many broadcast domains exist in the exhibited topology?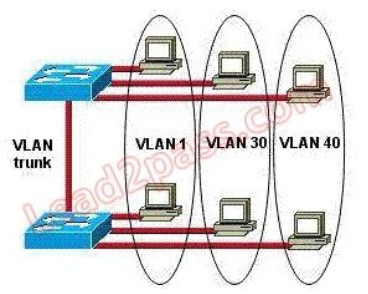 Correct
Correct
Incorrect
-
Question 324 of 555
324. Question
Refer to the exhibit. The network administrator has created a new VLAN on Switch1 and added host C and host D. The administrator has properly configured switch interfaces FastEthernet0/13 through FastEthernet0/14 to be members of the new VLAN. However, after the network administrator completed the configuration, host A could communicate with host B, but host A could not communicate with host C or host D. Which commands are required to resolve this problem?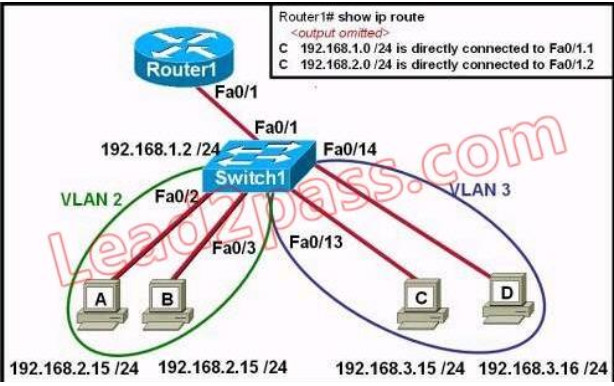 Correct
Correct
Incorrect
-
Question 325 of 555
325. Question
On a network of one department, there are four PCs connected to a switch, as shown in the following figure: After the Switch1 restarts. Host A ( the host on the left ) sends the first frame to Host C (the host on the right). What the first thing should the switch do?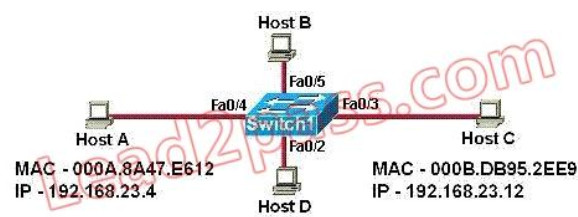 Correct
Correct
Incorrect
-
Question 326 of 555
326. Question
Refer to the exhibit. The network administrator is in a campus building distant from Building B. WANRouter is hosting a newly installed WAN link on interface S0/0. The new link is not functioning and the administrator needs to determine if the correct cable has been attached to the S0/0 interface. How can the administrator accurately verify the correct cable type on S0/0 in the most efficient manner?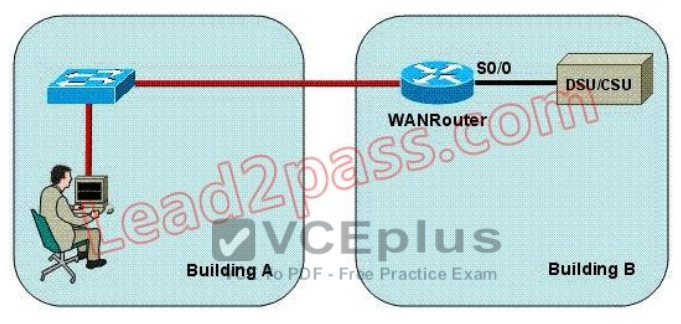 Correct
Correct
Incorrect
-
Question 327 of 555
327. Question
While troubleshooting a connectivity issue from a PC you obtain the following information:Local PC IP address: 10.0.0.35/24 Default Gateway: 10.0.0.1 Remote Sever: 10.5.75.250/24
You then conduct the following tests from the local PC:Ping 127.0.0.1 - Successful Ping 10.0.0.35 - Successful Ping 10.0.0.1 - Unsuccessful Ping 10.5.75.250 - Unsuccessful
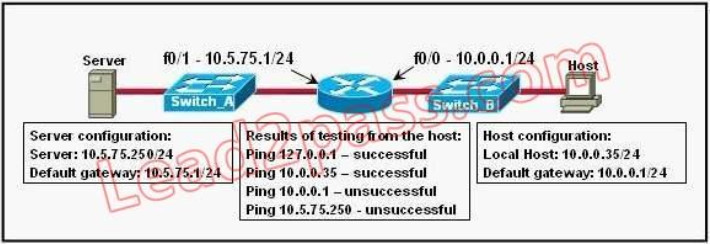 What is the underlying cause of this problem?
Correct
What is the underlying cause of this problem?
Correct
Incorrect
-
Question 328 of 555
328. Question
A network administrator is troubleshooting the OSPF configuration of routers R1 and R2. The routers cannot establish an adjacency relationship on their common Ethernet link. The graphic shows the output of the show ip ospf interface e0 command for routers R1 and R2.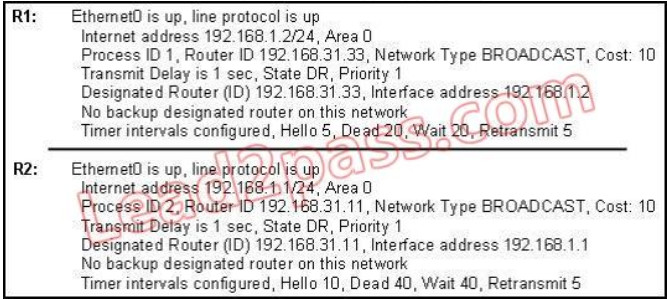 Based on the information in the graphic, what is the cause of this problem? Correct
Based on the information in the graphic, what is the cause of this problem? Correct
Incorrect
-
Question 329 of 555
329. Question
This graphic shows the results of an attempt to open a Telnet connection to router ACCESS1 from router Remote27.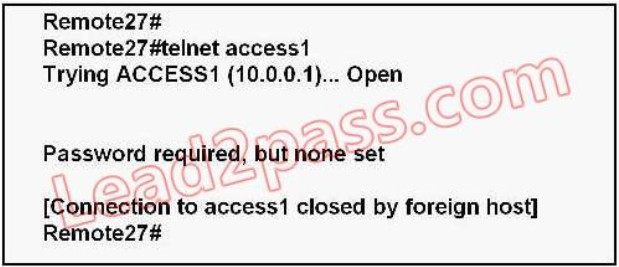 Which of the following command sequences will correct this problem? Correct
Which of the following command sequences will correct this problem? Correct
Incorrect
-
Question 330 of 555
330. Question
When upgrading the IOS image, the network administrator receives the exhibited error message.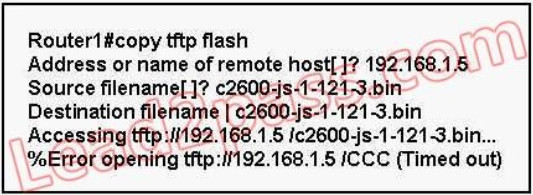 What could be the cause of this error? Correct
What could be the cause of this error? Correct
Incorrect
-
Question 331 of 555
331. Question
Refer to the exhibit, Host A pings interface S0/0 on router 3, what is the TTL value for that ping? Correct
Correct
Incorrect
-
Question 332 of 555
332. Question
Which statement is true, as relates to classful or classless routing?Correct
Incorrect
-
Question 333 of 555
333. Question
Refer to the exhibit. Why does the telnet connecting fail when a host attempts to connect a remote router?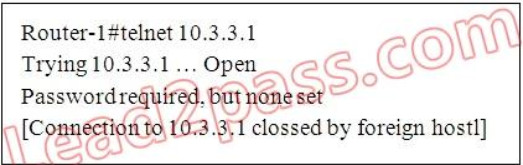 Correct
Correct
Incorrect
-
Question 334 of 555
334. Question
Which name describes an IPV6 host-enable tunneling technique that uses IPV4 UDP,does not require dedicated gateway tunnels,and can pass through existing IPV4 NAT gateways?Correct
Incorrect
-
Question 335 of 555
335. Question
Which pairing reflects a correct protocol-and-metric relationship?Correct
Incorrect
-
Question 336 of 555
336. Question
Refer to the exhibit, The VLAN configuration of S1 is not being in this VTP enabled environment. The VTP and uplink port configurations for each switch are displayed. Which two command sets, if issued, resolve this failure and allow VTP to operate as expected?(choose two)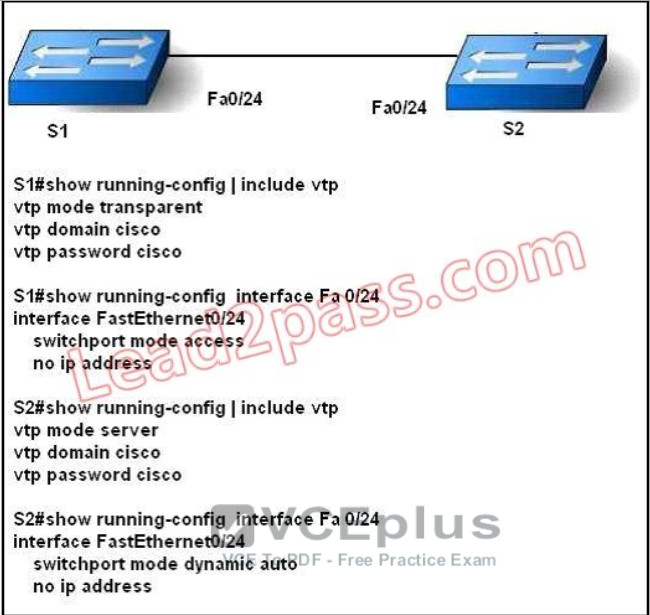 Correct
Correct
Incorrect
-
Question 337 of 555
337. Question
How are VTP advertisements delivered to switches across the network?Correct
Incorrect
-
Question 338 of 555
338. Question
Refer to the exhibit. What could be possible causes for the "Serial0/0 is down" interface status? (Choose two.)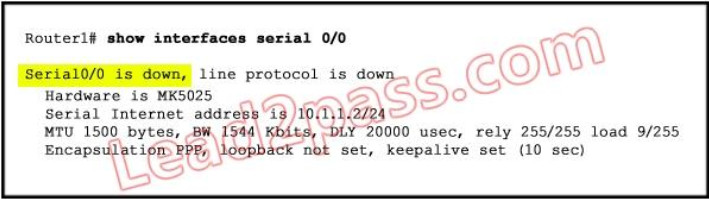 Correct
Correct
Incorrect
-
Question 339 of 555
339. Question
Refer to the exhibit. Which two statements are true about the loopback address that is configured on RouterB? (Choose two.)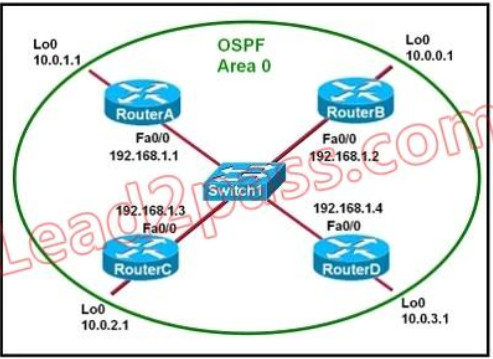 Correct
Correct
Incorrect
-
Question 340 of 555
340. Question
A network administrator is explaining VTP configuration to a new technician. What should the network administrator tell the new technician about VTP configuration? (Choose three.)Correct
Incorrect
-
Question 341 of 555
341. Question
Refer to the exhibit. Both switches are using a default configuration. Which two destination addresses will host 4 use to send data to host 1? (Choose two.) Correct
Correct
Incorrect
-
Question 342 of 555
342. Question
What are two reasons a network administrator would use CDP? (Choose two.)Correct
Incorrect
-
Question 343 of 555
343. Question
Refer to the exhibit. The router has been configured with these commands: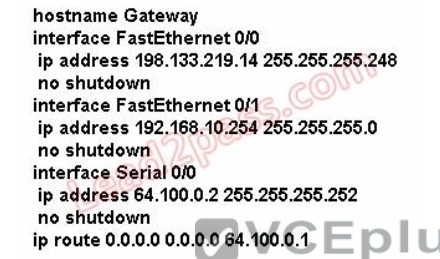 What are the two results of this configuration? (Choose two.)
What are the two results of this configuration? (Choose two.)
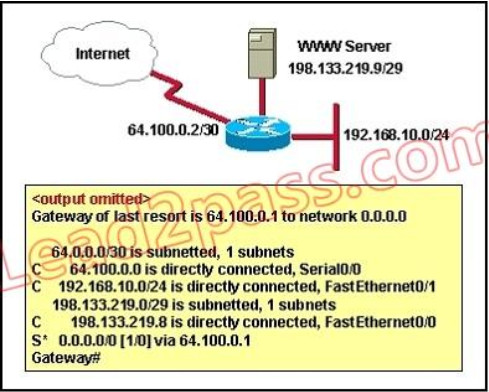 Correct
Correct
Incorrect
-
Question 344 of 555
344. Question
A company is installing IP phones. The phones and office computers connect to the same device. To ensure maximum throughput for the phone data, the company needs to make sure that the phone traffic is on a different network from that of the office computer data traffic. What is the best network device to which to directly connect the phones and computers, and what technology should be implemented on this device? (Choose two.)Correct
Incorrect
-
Question 345 of 555
345. Question
What are two benefits of using VTP in a switching environment? (Choose two.)Correct
Incorrect
-
Question 346 of 555
346. Question
Which two statements are true about the command ip route 172.16.3.0 255.255.255.0 192.168.2.4? (Choose two.)Correct
Incorrect
-
Question 347 of 555
347. Question
What are two advantages of Layer 2 Ethernet switches over hubs? (Choose two.)Correct
Incorrect
-
Question 348 of 555
348. Question
Refer to the exhibit. A network associate needs to configure the switches and router in the graphic so that the hosts in VLAN3 and VLAN4 can communicate with the enterprise server in VLAN2. Which two Ethernet segments would need to be configured as trunk links? (Choose two.)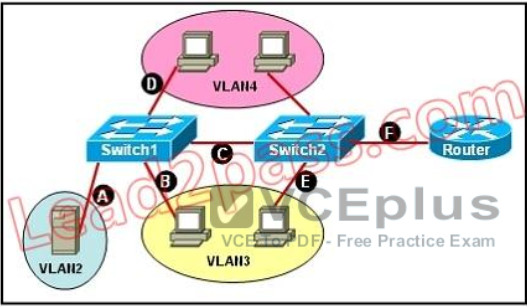 Correct
Correct
Incorrect
-
Question 349 of 555
349. Question
Which two values are used by Spanning Tree Protocol to elect a root bridge? (Choose two.)Correct
Incorrect
-
Question 350 of 555
350. Question
Refer to the exhibit. The networks connected to router R2 have been summarized as a 192.168.176.0/21 route and sent to R1. Which two packet destination addresses will R1 forward to R2? (Choose two.)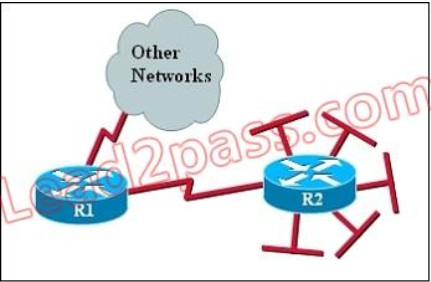 Correct
Correct
Incorrect
-
Question 351 of 555
351. Question
Which three statements are typical characteristics of VLAN arrangements? (Choose three.)Correct
Incorrect
-
Question 352 of 555
352. Question
Refer to the exhibit. Which three statements are true about how router JAX will choose a path to the 10.1.3.0/24 network when different routing protocols are configured? (Choose three.)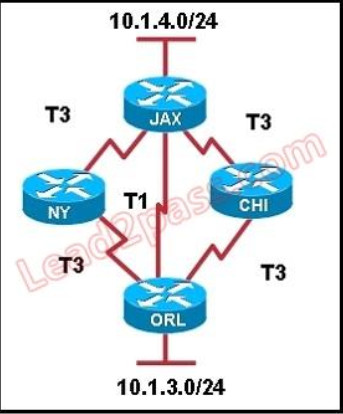 Correct
Correct
Incorrect
-
Question 353 of 555
353. Question
Switch ports operating in which two roles will forward traffic according to the IEEE 802.1w standard? (Choose two.)Correct
Incorrect
-
Question 354 of 555
354. Question
Refer to the exhibit. Given the output shown from this Cisco Catalyst 2950, what is the most likely reason that interface FastEthernet 0/10 is not the root port for VLAN 2?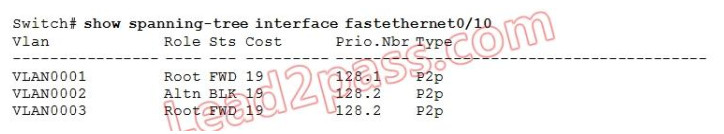 Correct
Correct
Incorrect
-
Question 355 of 555
355. Question
Refer to the exhibit. This command is executed on 2960Switch: 2960Switch(config)# mac-address-table static 0000.00aa.aaaa vlan 10 interface fa0/1 Which two of these statements correctly identify results of executing the command? (Choose two.)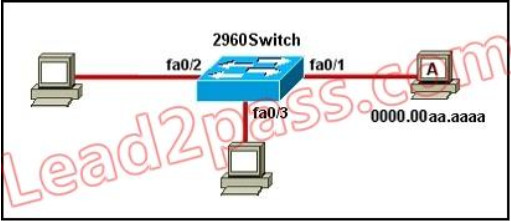 Correct
Correct
Incorrect
-
Question 356 of 555
356. Question
Which of the following describes the roles of devices in a WAN? (Choose three.)Correct
Incorrect
-
Question 357 of 555
357. Question
What are two characteristics of Telnet? (Choose two.)Correct
Incorrect
-
Question 358 of 555
358. Question
What are two security appliances that can be installed in a network? (Choose two.)Correct
Incorrect
-
Question 359 of 555
359. Question
Assuming a subnet mask of 255.255.248.0, three of the following addresses are valid host addresses. Which are these addresses? (Choose three.)Correct
Incorrect
-
Question 360 of 555
360. Question
Refer to the exhibit. A network technician is unable to ping from R1 to R2. What will help correct the problem?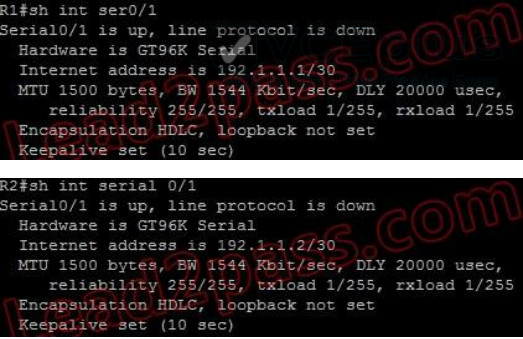 Correct
Correct
Incorrect
-
Question 361 of 555
361. Question
Refer to the exhibit. Which two statements are true of the interface configuration? (Choose two.)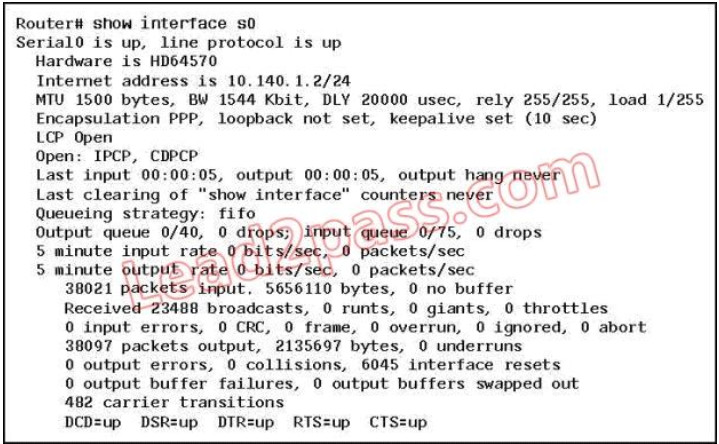 Correct
Correct
Incorrect
-
Question 362 of 555
362. Question
Refer to the exhibit. What does the address 192.168.2.167 represent?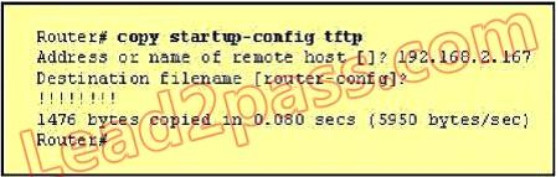 Correct
Correct
Incorrect
-
Question 363 of 555
363. Question
Refer to the exhibit. A technician is troubleshooting a host connectivity problem. The host is unable to ping a server connected to Switch_A. Based on the results of the testing, what could be the problem?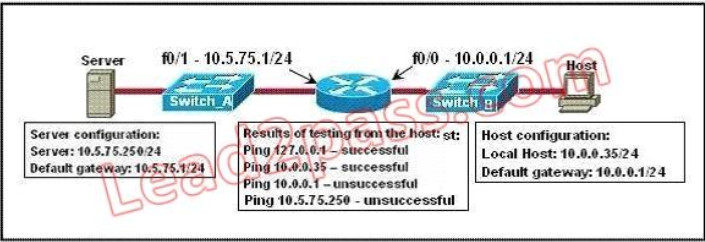 Correct
Correct
Incorrect
-
Question 364 of 555
364. Question
In which situation would the use of a static route be appropriate?Correct
Incorrect
-
Question 365 of 555
365. Question
An administrator issues the show ip interface s0/0 command and the output displays that interface Serial0/0 is up, line protocol is up What does "line protocol is up" specifically indicate about the interface?Correct
Incorrect
-
Question 366 of 555
366. Question
Which three statements are correct about RIP version 2? (Choose three)Correct
Incorrect
-
Question 367 of 555
367. Question
How can an administrator determine if a router has been configured when it is first powered up?Correct
Incorrect
-
Question 368 of 555
368. Question
A network administrator receives an error message while trying to configure the Ethernet interface of a router with IP address 10.24.24.24/29. Which statement explains the reason for this issue?Correct
Incorrect
-
Question 369 of 555
369. Question
Which address is the IPv6 all-RIP-routers multicast group address that is used by RIPng as the destination address for RIP updates?Correct
Incorrect
-
Question 370 of 555
370. Question
If all OSPF routers in a single area are configured with the same priority value, what value does a router use for the OSPF router ID in the absence of a loopback interface?Correct
Incorrect
-
Question 371 of 555
371. Question
The OSPF Hello protocol performs which of the following tasks? (Choose two.)Correct
Incorrect
-
Question 372 of 555
372. Question
The network administrator of the Oregon router adds the following command to the router configuration: ip route 192.168.12.0 255.255.255.0 172.16.12.1. What are the results of adding this command? (Choose two.)Correct
Incorrect
-
Question 373 of 555
373. Question
A network administrator is planning a network installation for a large organization. The design requires 100 separate subnetworks, so the company has acquired a Class B network address. What subnet mask will provide the 100 subnetworks required, if 500 usable host addresses are required per subnet?Correct
Incorrect
-
Question 374 of 555
374. Question
Refer to Exhibit. Based on the network shown in the graphic which option contains both the potential networking problem and the protocol or setting that should be used to prevent the problem? Correct
Correct
Incorrect
-
Question 375 of 555
375. Question
Which of the following services use UDP? (Choose three.)Correct
Incorrect
-
Question 376 of 555
376. Question
Refer to the exhibit. Which two statements are true based the output of the show frame-relay lmi command issued on the Branch router? (Choose two.)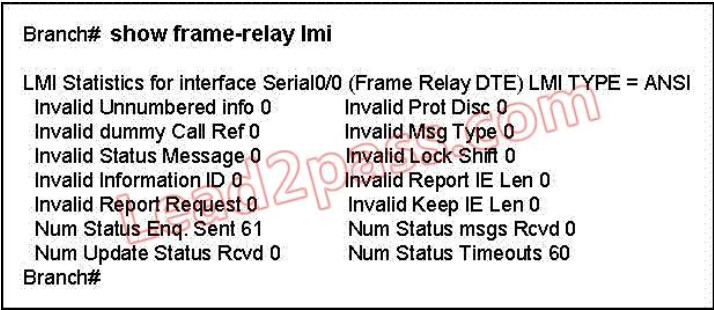 Correct
Correct
Incorrect
-
Question 377 of 555
377. Question
What are two recommended ways of protecting network device configuration files from outside network security threats? (Choose two.)Correct
Incorrect
-
Question 378 of 555
378. Question
Refer to the exhibit. The switches on a campus network have been interconnected as shown. All of the switches are running Spanning Tree Protocol with its default settings. Unusual traffic patterns are observed and it is discovered that Switch9 is the root bridge. Which change will ensure that Switch1 will be selected as the root bridge instead of Switch9?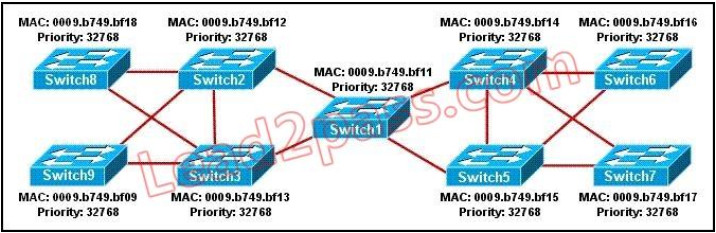 Correct
Correct
Incorrect
-
Question 379 of 555
379. Question
The Company WAN is migrating from RIPv1 to RIPv2. Which three statements are correct about RIP version 2? (Choose three)Correct
Incorrect
-
Question 380 of 555
380. Question
If a router has four interfaces and each interface is connected to four switches, how many broadcast domains are present on the router?Correct
Incorrect
-
Question 381 of 555
381. Question
Which command can you use to set the hostname on a switch?Correct
Incorrect
-
Question 382 of 555
382. Question
If the primary root bridge experiences a power loss, which switch takes over?Correct
Incorrect
-
Question 383 of 555
383. Question
Which IPv6 header field is equivalent to the TTL?Correct
Incorrect
-
Question 384 of 555
384. Question
Which two statements about the tunnel mode ipv6ip command are true? (Choose two.)Correct
Incorrect
-
Question 385 of 555
385. Question
What is the correct routing match to reach 172.16.1.5/32?Correct
Incorrect
-
Question 386 of 555
386. Question
Which step in the router boot process searches for an IOS image to load into the router?Correct
Incorrect
-
Question 387 of 555
387. Question
Which command can you enter to route all traffic that is destined for 192.168.0.0/20 to a specific interface?Correct
Incorrect
-
Question 388 of 555
388. Question
Which technology allows a large number of private IP addresses to be represented by a smaller number of public IP addresses?Correct
Incorrect
-
Question 389 of 555
389. Question
What is the effect of the overload keyword in a static NAT translation configuration?Correct
Incorrect
-
Question 390 of 555
390. Question
Which protocol advertises a virtual IP address to facilitate transparent failover of a Cisco routing device?Correct
Incorrect
-
Question 391 of 555
391. Question
What are three broadband wireless technologies? (Choose three.)Correct
Incorrect
-
Question 392 of 555
392. Question
Which condition indicates that service password-encryption is enabled?Correct
Incorrect
-
Question 393 of 555
393. Question
Which two spanning-tree port states does RSTP combine to allow faster convergence? (Choose two.)Correct
Incorrect
-
Question 394 of 555
394. Question
Which technology can enable multiple VLANs to communicate with one another?Correct
Incorrect
-
Question 395 of 555
395. Question
In which three ways is an IPv6 header simpler than an IPv4 header? (Choose three.)Correct
Incorrect
-
Question 396 of 555
396. Question
Which feature builds a FIB and an adjacency table to expedite packet forwarding?Correct
Incorrect
-
Question 397 of 555
397. Question
What is the purpose of the POST operation on a router?Correct
Incorrect
-
Question 398 of 555
398. Question
Which command can you enter to set the default route for all traffic to an interface?Correct
Incorrect
-
Question 399 of 555
399. Question
Which two types of NAT addresses are used in a Cisco NAT device? (Choose two.)Correct
Incorrect
-
Question 400 of 555
400. Question
What is the danger of the permit any entry in a NAT access list?Correct
Incorrect
-
Question 401 of 555
401. Question
Which protocol is the Cisco proprietary implementation of FHRP?Correct
Incorrect
-
Question 402 of 555
402. Question
Which two statements about late collisions are true? (Choose two.)Correct
Incorrect
-
Question 403 of 555
403. Question
Which three characteristics are representative of a link-state routing protocol? (Choose three.)Correct
Incorrect
-
Question 404 of 555
404. Question
Refer to the exhibit. What is the effect of the given configuration?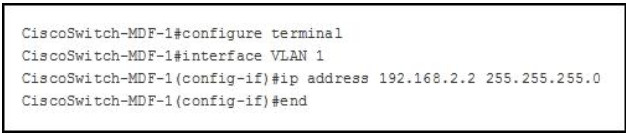 Correct
Correct
Incorrect
-
Question 405 of 555
405. Question
Which command can you enter to view the ports that are assigned to VLAN 20?Correct
Incorrect
-
Question 406 of 555
406. Question
If primary and secondary root switches with priority 16384 both experience catastrophic losses, which tertiary switch can take over?Correct
Incorrect
-
Question 407 of 555
407. Question
Which two statements about IPv6 and routing protocols are true? (Choose two.)Correct
Incorrect
-
Question 408 of 555
408. Question
Which two features can dynamically assign IPv6 addresses? (Choose two.)Correct
Incorrect
-
Question 409 of 555
409. Question
Which command can you enter to configure a local username with an encrypted password and EXEC mode user privileges?Correct
Incorrect
-
Question 410 of 555
410. Question
Which three commands can you use to set a router boot image? (Choose three.)Correct
Incorrect
-
Question 411 of 555
411. Question
Which three statements about static routing are true? (Choose three.)Correct
Incorrect
-
Question 412 of 555
412. Question
Which type of address is the public IP address of a NAT device?Correct
Incorrect
-
Question 413 of 555
413. Question
Which command can you enter to display the hits counter for NAT traffic?Correct
Incorrect
-
Question 414 of 555
414. Question
Which standards-based First Hop Redundancy Protocol is a Cisco supported alternative to Hot Standby Router Protocol?Correct
Incorrect
-
Question 415 of 555
415. Question
What are two reasons that duplex mismatches can be difficult to diagnose? (Choose two.)Correct
Incorrect
-
Question 416 of 555
416. Question
Which command can you execute to set the user inactivity timer to 10 seconds?Correct
Incorrect
-
Question 417 of 555
417. Question
Which command sequence can you enter to create VLAN 20 and assign it to an interface on a switch?Correct
Incorrect
-
Question 418 of 555
418. Question
Which spanning-tree protocol rides on top of another spanning-tree protocol?Correct
Incorrect
-
Question 419 of 555
419. Question
Which two statements about IPv6 router advertisement messages are true? (Choose two.)Correct
Incorrect
-
Question 420 of 555
420. Question
Which three statements about IPv6 prefixes are true? (Choose three.)Correct
Incorrect
-
Question 421 of 555
421. Question
After you configure the Loopback0 interface, which command can you enter to verify the status of the interface and determine whether fast switching is enabled?Correct
Incorrect
-
Question 422 of 555
422. Question
Which three statements about link-state routing are true? (Choose three.)Correct
Incorrect
-
Question 423 of 555
423. Question
Which NAT function can map multiple inside addresses to a single outside address?Correct
Incorrect
-
Question 424 of 555
424. Question
What is the first step in the NAT configuration process?Correct
Incorrect
-
Question 425 of 555
425. Question
What are two requirements for an HSRP group? (Choose two.)Correct
Incorrect
-
Question 426 of 555
426. Question
Which two commands can you enter to verify that a configured NetFlow data export is operational? (Choose two.)Correct
Incorrect
-
Question 427 of 555
427. Question
What are three characteristics of satellite Internet connections? (Choose three.)Correct
Incorrect
-
Question 428 of 555
428. Question
Which command sets and automatically encrypts the privileged enable mode password?Correct
Incorrect
-
Question 429 of 555
429. Question
The enable secret command is used to secure access to which CLI mode?Correct
Incorrect
-
Question 430 of 555
430. Question
The enable secret command is used to secure access to which CLI mode?Correct
Incorrect
-
Question 431 of 555
431. Question
Refer to the exhibit. What is the result of setting the no login command?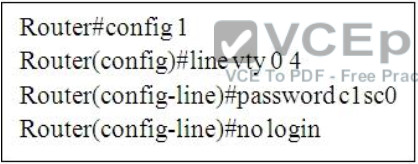 Correct
Correct
Incorrect
-
Question 432 of 555
432. Question
Which option describes a difference between EIGRP for IPv4 and IPv6?Correct
Incorrect
Hint
Router ID - Both EIGRP for IPv4 and EIGRP for IPv6 use a 32-bit number for the EIGRP router ID. The 32-bit router ID is represented in dotted-decimal notation and is commonly referred to as an IPv4 address. If the EIGRP for IPv6 router has not been configured with an IPv4 address, the eigrp router-id command must be used to configure a 32-bit router ID. The process for determining the router ID is the same for both EIGRP for IPv4 and IPv6. -
Question 433 of 555
433. Question
What is the best way to verify that a host has a path to other hosts in different networks?Correct
Incorrect
Hint
Ping is a tool that helps to verify IP-level connectivity; PathPing is a tool that detects packet loss over multiple-hop trips. When troubleshooting, the ping command is used to send an ICMP Echo Request to a target host name or IP address. Use Ping whenever you want to verify that a host computer can send IP packets to a destination host. You can also use the Ping tool to isolate network hardware problems and incompatible configurations. If you call ipconfig /all and receive a response, there is no need to ping the loopback address and your own IP address -- Ipconfig has already done so in order to generate the report. It is best to verify that a route exists between the local computer and a network host by first using ping and the IP address of the network host to which you want to connect. The command syntax is: ping < IP address > Perform the following steps when using Ping: Ping the loopback address to verify that TCP/IP is installed and configured correctly on the local computer. ping 127.0.0.1 If the loopback step fails, the IP stack is not responding. This might be because the TCP drivers are corrupted, the network adapter might not be working, or another service is interfering with IP. Ping the IP address of the local computer to verify that it was added to the network correctly. Note that if the routing table is correct, this simply forwards the packet to the loopback address of 127.0.0.1. ping < IP address of local host > Ping the IP address of the default gateway to verify that the default gateway is functioning and that you can communicate with a local host on the local network. ping < IP address of default gateway > Ping the IP address of a remote host to verify that you can communicate through a router. ping < IP address of remote host > Ping the host name of a remote host to verify that you can resolve a remote host name. ping < Host name of remote host > Run a PathPing analysis to a remote host to verify that the routers on the way to the destination are operating correctly. pathping < IP address of remote host > -
Question 434 of 555
434. Question
If host Z needs to send data through router R1 to a storage server, which destination MAC address does host Z use to transmit packets?Correct
Incorrect
-
Question 435 of 555
435. Question
Hotspot Questions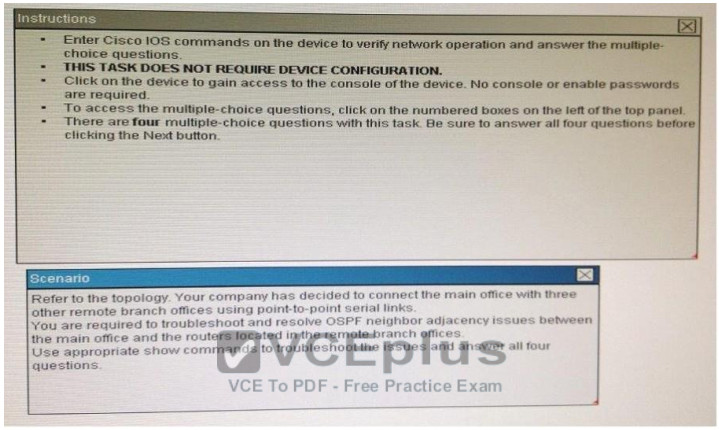
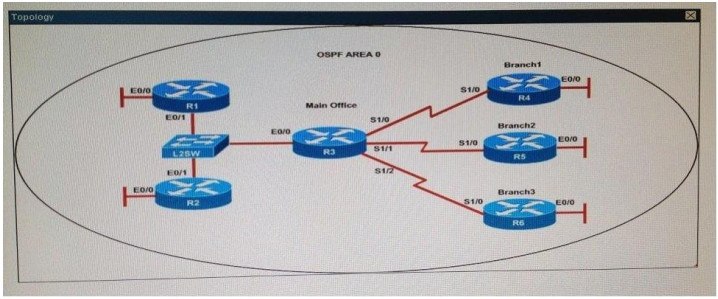 R1# show running-config
interface Loopback0
description ***Loopback***
ip address 192.168.1.1 255.255.255.255
ip ospf 1 area 0
!
interface Ethernet0/0
description **Connected to R1-LAN**
ip address 10.10.110.1 255.255.255.0
ip ospf 1 area 0
!
interface Ethernet0/1
description **Connected to L2SW**
ip address 10.10.230.1 255.255.255.0
ip ospf hello-interval 25
ip ospf 1 area 0
!
log-adjacency-changes
R2# show running-config
R2
!
interface Loopback0
description **Loopback**
ip address 192.168.2.2 255.255.255.255
ip ospf 2 area 0
!
interface Ethernet0/0
description **Connected to R2-LAN**
ip address 10.10.120.1 255.255.255.0
ip ospf 2 area 0
!
interface Ethernet0/1
description **Connected to L2SW**
ip address 10.10.230.2 255.255.255.0
ip ospf 2 area 0
!
router ospf 2
log-adjacency-changes
R3# show running-config
R3
username R6 password CISCO36
!
interface Loopback0
description **Loopback**
ip address 192.168.3.3 255.255.255.255
ip ospf 3 area 0
!
interface Ethernet0/0
description **Connected to L2SW**
ip address 10.10.230.3 255.255.255.0
ip ospf 3 area 0
!
interface Serial1/0
description **Connected to R4-Branch1 office**
ip address 10.10.240.1 255.255.255.252
encapsulation ppp
ip ospf 3 area 0
!
interface Serial1/1
description **Connected to R5-Branch2 office**
ip address 10.10.240.5 255.255.255.252
encapsulation ppp
ip ospf hello-interval 50
ip ospf 3 area 0
!
interface Serial1/2
description **Connected to R6-Branch3 office**
ip address 10.10.240.9 255.255.255.252
encapsulation ppp
ip ospf 3 area 0
ppp authentication chap
!
router ospf 3
router-id 192.168.3.3
!
R4# show running-config
R4
!
interface Loopback0
description **Loopback**
ip address 192.168.4.4 255.255.255.255
ip ospf 4 area 2
!
interface Ethernet0/0
ip address 172.16.113.1 255.255.255.0
ip ospf 4 area 2
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.2 255.255.255.252
encapsulation ppp
ip ospf 4 area 2
!
router ospf 4
log-adjacency-changes
R5# show running-config
R5
!
interface Loopback0
description **Loopback**
ip address 192.168.5.5 255.255.255.255
ip ospf 5 area 0
!
interface Ethernet0/0
ip address 172.16.114.1 255.255.255.0
ip ospf 5 area 0
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.6 255.255.255.252
encapsulation ppp
ip ospf 5 area 0
!
router ospf 5
log-adjacency-changes
R6# show running-config
R6
username R3 password CISCO36
!
interface Loopback0
description **Loopback**
ip address 192.168.6.6 255.255.255.255
ip ospf 6 area 0
!
interface Ethernet0/0
ip address 172.16.115.1 255.255.255.0
ip ospf 6 area 0
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.10 255.255.255.252
encapsulation ppp
ip ospf 6 area 0
ppp authentication chap
!
router ospf 6
router-id 192.168.3.3
!
An OSPF neighbor adjacency is not formed between R3 in the main office and R6 in the Branch3 office. What is causing the problem? Correct
R1# show running-config
interface Loopback0
description ***Loopback***
ip address 192.168.1.1 255.255.255.255
ip ospf 1 area 0
!
interface Ethernet0/0
description **Connected to R1-LAN**
ip address 10.10.110.1 255.255.255.0
ip ospf 1 area 0
!
interface Ethernet0/1
description **Connected to L2SW**
ip address 10.10.230.1 255.255.255.0
ip ospf hello-interval 25
ip ospf 1 area 0
!
log-adjacency-changes
R2# show running-config
R2
!
interface Loopback0
description **Loopback**
ip address 192.168.2.2 255.255.255.255
ip ospf 2 area 0
!
interface Ethernet0/0
description **Connected to R2-LAN**
ip address 10.10.120.1 255.255.255.0
ip ospf 2 area 0
!
interface Ethernet0/1
description **Connected to L2SW**
ip address 10.10.230.2 255.255.255.0
ip ospf 2 area 0
!
router ospf 2
log-adjacency-changes
R3# show running-config
R3
username R6 password CISCO36
!
interface Loopback0
description **Loopback**
ip address 192.168.3.3 255.255.255.255
ip ospf 3 area 0
!
interface Ethernet0/0
description **Connected to L2SW**
ip address 10.10.230.3 255.255.255.0
ip ospf 3 area 0
!
interface Serial1/0
description **Connected to R4-Branch1 office**
ip address 10.10.240.1 255.255.255.252
encapsulation ppp
ip ospf 3 area 0
!
interface Serial1/1
description **Connected to R5-Branch2 office**
ip address 10.10.240.5 255.255.255.252
encapsulation ppp
ip ospf hello-interval 50
ip ospf 3 area 0
!
interface Serial1/2
description **Connected to R6-Branch3 office**
ip address 10.10.240.9 255.255.255.252
encapsulation ppp
ip ospf 3 area 0
ppp authentication chap
!
router ospf 3
router-id 192.168.3.3
!
R4# show running-config
R4
!
interface Loopback0
description **Loopback**
ip address 192.168.4.4 255.255.255.255
ip ospf 4 area 2
!
interface Ethernet0/0
ip address 172.16.113.1 255.255.255.0
ip ospf 4 area 2
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.2 255.255.255.252
encapsulation ppp
ip ospf 4 area 2
!
router ospf 4
log-adjacency-changes
R5# show running-config
R5
!
interface Loopback0
description **Loopback**
ip address 192.168.5.5 255.255.255.255
ip ospf 5 area 0
!
interface Ethernet0/0
ip address 172.16.114.1 255.255.255.0
ip ospf 5 area 0
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.6 255.255.255.252
encapsulation ppp
ip ospf 5 area 0
!
router ospf 5
log-adjacency-changes
R6# show running-config
R6
username R3 password CISCO36
!
interface Loopback0
description **Loopback**
ip address 192.168.6.6 255.255.255.255
ip ospf 6 area 0
!
interface Ethernet0/0
ip address 172.16.115.1 255.255.255.0
ip ospf 6 area 0
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.10 255.255.255.252
encapsulation ppp
ip ospf 6 area 0
ppp authentication chap
!
router ospf 6
router-id 192.168.3.3
!
An OSPF neighbor adjacency is not formed between R3 in the main office and R6 in the Branch3 office. What is causing the problem? Correct
Incorrect
-
Question 436 of 555
436. Question
Hotspot Questions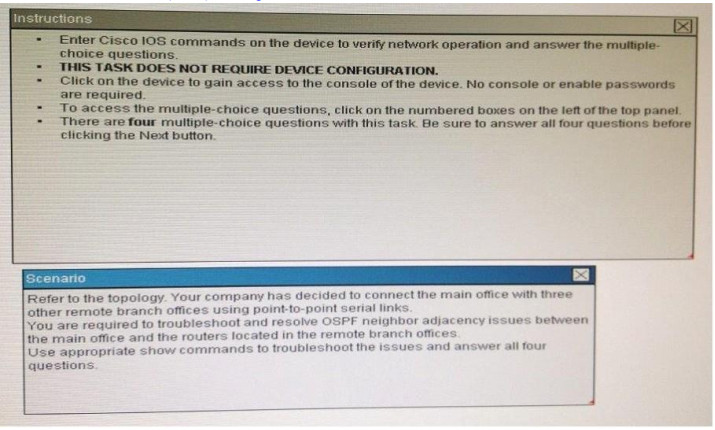
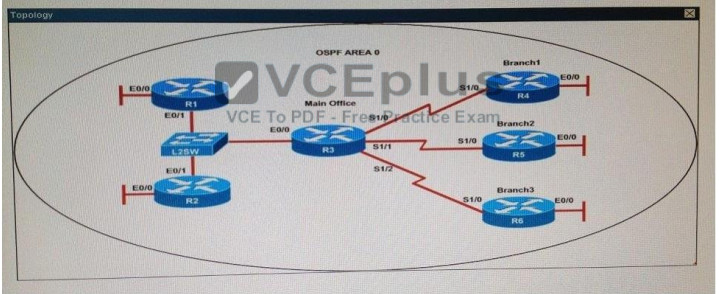 R1# show running-config
interface Loopback0
description ***Loopback***
ip address 192.168.1.1 255.255.255.255
ip ospf 1 area 0
!
interface Ethernet0/0
description **Connected to R1-LAN**
ip address 10.10.110.1 255.255.255.0
ip ospf 1 area 0
!
interface Ethernet0/1
description **Connected to L2SW**
ip address 10.10.230.1 255.255.255.0
ip ospf hello-interval 25
ip ospf 1 area 0
!
log-adjacency-changes
R2# show running-config
R2
!
interface Loopback0
description **Loopback**
ip address 192.168.2.2 255.255.255.255
ip ospf 2 area 0
!
interface Ethernet0/0
description **Connected to R2-LAN**
ip address 10.10.120.1 255.255.255.0
ip ospf 2 area 0
!
interface Ethernet0/1
description **Connected to L2SW**
ip address 10.10.230.2 255.255.255.0
ip ospf 2 area 0
!
router ospf 2
log-adjacency-changes
R3# show running-config
R3
username R6 password CISCO36
!
interface Loopback0
description **Loopback**
ip address 192.168.3.3 255.255.255.255
ip ospf 3 area 0
!
interface Ethernet0/0
description **Connected to L2SW**
ip address 10.10.230.3 255.255.255.0
ip ospf 3 area 0
!
interface Serial1/0
description **Connected to R4-Branch1 office**
ip address 10.10.240.1 255.255.255.252
encapsulation ppp
ip ospf 3 area 0
!
interface Serial1/1
description **Connected to R5-Branch2 office**
ip address 10.10.240.5 255.255.255.252
encapsulation ppp
ip ospf hello-interval 50
ip ospf 3 area 0
!
interface Serial1/2
description **Connected to R6-Branch3 office**
ip address 10.10.240.9 255.255.255.252
encapsulation ppp
ip ospf 3 area 0
ppp authentication chap
!
router ospf 3
router-id 192.168.3.3
!
R4# show running-config
R4
!
interface Loopback0
description **Loopback**
ip address 192.168.4.4 255.255.255.255
ip ospf 4 area 2
!
interface Ethernet0/0
ip address 172.16.113.1 255.255.255.0
ip ospf 4 area 2
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.2 255.255.255.252
encapsulation ppp
ip ospf 4 area 2
!
router ospf 4
log-adjacency-changes
R5# show running-config
R5
!
interface Loopback0
description **Loopback**
ip address 192.168.5.5 255.255.255.255
ip ospf 5 area 0
!
interface Ethernet0/0
ip address 172.16.114.1 255.255.255.0
ip ospf 5 area 0
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.6 255.255.255.252
encapsulation ppp
ip ospf 5 area 0
!
router ospf 5
log-adjacency-changes
R6# show running-config
R6
username R3 password CISCO36
!
interface Loopback0
description **Loopback**
ip address 192.168.6.6 255.255.255.255
ip ospf 6 area 0
!
interface Ethernet0/0
ip address 172.16.115.1 255.255.255.0
ip ospf 6 area 0
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.10 255.255.255.252
encapsulation ppp
ip ospf 6 area 0
ppp authentication chap
!
router ospf 6
router-id 192.168.3.3
!
An OSPF neighbor adjacency is not formed between R3 in the main office and R4 in the Branch1 office. What is causing the problem? Correct
R1# show running-config
interface Loopback0
description ***Loopback***
ip address 192.168.1.1 255.255.255.255
ip ospf 1 area 0
!
interface Ethernet0/0
description **Connected to R1-LAN**
ip address 10.10.110.1 255.255.255.0
ip ospf 1 area 0
!
interface Ethernet0/1
description **Connected to L2SW**
ip address 10.10.230.1 255.255.255.0
ip ospf hello-interval 25
ip ospf 1 area 0
!
log-adjacency-changes
R2# show running-config
R2
!
interface Loopback0
description **Loopback**
ip address 192.168.2.2 255.255.255.255
ip ospf 2 area 0
!
interface Ethernet0/0
description **Connected to R2-LAN**
ip address 10.10.120.1 255.255.255.0
ip ospf 2 area 0
!
interface Ethernet0/1
description **Connected to L2SW**
ip address 10.10.230.2 255.255.255.0
ip ospf 2 area 0
!
router ospf 2
log-adjacency-changes
R3# show running-config
R3
username R6 password CISCO36
!
interface Loopback0
description **Loopback**
ip address 192.168.3.3 255.255.255.255
ip ospf 3 area 0
!
interface Ethernet0/0
description **Connected to L2SW**
ip address 10.10.230.3 255.255.255.0
ip ospf 3 area 0
!
interface Serial1/0
description **Connected to R4-Branch1 office**
ip address 10.10.240.1 255.255.255.252
encapsulation ppp
ip ospf 3 area 0
!
interface Serial1/1
description **Connected to R5-Branch2 office**
ip address 10.10.240.5 255.255.255.252
encapsulation ppp
ip ospf hello-interval 50
ip ospf 3 area 0
!
interface Serial1/2
description **Connected to R6-Branch3 office**
ip address 10.10.240.9 255.255.255.252
encapsulation ppp
ip ospf 3 area 0
ppp authentication chap
!
router ospf 3
router-id 192.168.3.3
!
R4# show running-config
R4
!
interface Loopback0
description **Loopback**
ip address 192.168.4.4 255.255.255.255
ip ospf 4 area 2
!
interface Ethernet0/0
ip address 172.16.113.1 255.255.255.0
ip ospf 4 area 2
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.2 255.255.255.252
encapsulation ppp
ip ospf 4 area 2
!
router ospf 4
log-adjacency-changes
R5# show running-config
R5
!
interface Loopback0
description **Loopback**
ip address 192.168.5.5 255.255.255.255
ip ospf 5 area 0
!
interface Ethernet0/0
ip address 172.16.114.1 255.255.255.0
ip ospf 5 area 0
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.6 255.255.255.252
encapsulation ppp
ip ospf 5 area 0
!
router ospf 5
log-adjacency-changes
R6# show running-config
R6
username R3 password CISCO36
!
interface Loopback0
description **Loopback**
ip address 192.168.6.6 255.255.255.255
ip ospf 6 area 0
!
interface Ethernet0/0
ip address 172.16.115.1 255.255.255.0
ip ospf 6 area 0
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.10 255.255.255.252
encapsulation ppp
ip ospf 6 area 0
ppp authentication chap
!
router ospf 6
router-id 192.168.3.3
!
An OSPF neighbor adjacency is not formed between R3 in the main office and R4 in the Branch1 office. What is causing the problem? Correct
Incorrect
-
Question 437 of 555
437. Question
Hotspot Questions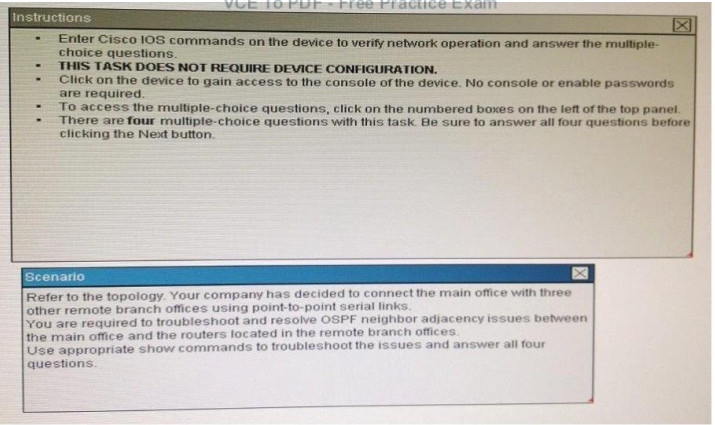
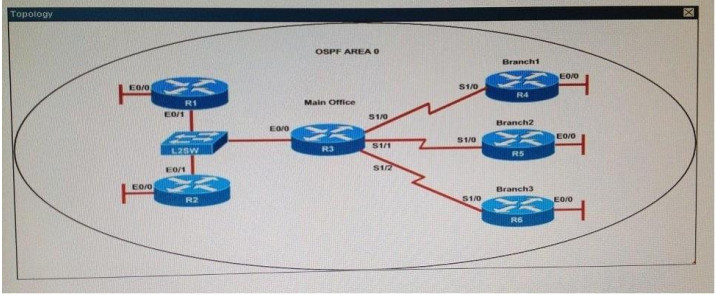 R1# show running-config
interface Loopback0
description ***Loopback***
ip address 192.168.1.1 255.255.255.255
ip ospf 1 area 0
!
interface Ethernet0/0
description **Connected to R1-LAN**
ip address 10.10.110.1 255.255.255.0
ip ospf 1 area 0
!
interface Ethernet0/1
description **Connected to L2SW**
ip address 10.10.230.1 255.255.255.0
ip ospf hello-interval 25
ip ospf 1 area 0
!
log-adjacency-changes
R2# show running-config
R2
!
interface Loopback0
description **Loopback**
ip address 192.168.2.2 255.255.255.255
ip ospf 2 area 0
!
interface Ethernet0/0
description **Connected to R2-LAN**
ip address 10.10.120.1 255.255.255.0
ip ospf 2 area 0
!
interface Ethernet0/1
description **Connected to L2SW**
ip address 10.10.230.2 255.255.255.0
ip ospf 2 area 0
!
router ospf 2
log-adjacency-changes
R3# show running-config
R3
username R6 password CISCO36
!
interface Loopback0
description **Loopback**
ip address 192.168.3.3 255.255.255.255
ip ospf 3 area 0
!
interface Ethernet0/0
description **Connected to L2SW**
ip address 10.10.230.3 255.255.255.0
ip ospf 3 area 0
!
interface Serial1/0
description **Connected to R4-Branch1 office**
ip address 10.10.240.1 255.255.255.252
encapsulation ppp
ip ospf 3 area 0
!
interface Serial1/1
description **Connected to R5-Branch2 office**
ip address 10.10.240.5 255.255.255.252
encapsulation ppp
ip ospf hello-interval 50
ip ospf 3 area 0
!
interface Serial1/2
description **Connected to R6-Branch3 office**
ip address 10.10.240.9 255.255.255.252
encapsulation ppp
ip ospf 3 area 0
ppp authentication chap
!
router ospf 3
router-id 192.168.3.3
!
R4# show running-config
R4
!
interface Loopback0
description **Loopback**
ip address 192.168.4.4 255.255.255.255
ip ospf 4 area 2
!
interface Ethernet0/0
ip address 172.16.113.1 255.255.255.0
ip ospf 4 area 2
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.2 255.255.255.252
encapsulation ppp
ip ospf 4 area 2
!
router ospf 4
log-adjacency-changes
R5# show running-config
R5
!
interface Loopback0
description **Loopback**
ip address 192.168.5.5 255.255.255.255
ip ospf 5 area 0
!
interface Ethernet0/0
ip address 172.16.114.1 255.255.255.0
ip ospf 5 area 0
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.6 255.255.255.252
encapsulation ppp
ip ospf 5 area 0
!
router ospf 5
log-adjacency-changes
R6# show running-config
R6
username R3 password CISCO36
!
interface Loopback0
description **Loopback**
ip address 192.168.6.6 255.255.255.255
ip ospf 6 area 0
!
interface Ethernet0/0
ip address 172.16.115.1 255.255.255.0
ip ospf 6 area 0
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.10 255.255.255.252
encapsulation ppp
ip ospf 6 area 0
ppp authentication chap
!
router ospf 6
router-id 192.168.3.3
!
R1 does not form an OSPF neighbor adjacency with R2. Which option would fix the issue? Correct
R1# show running-config
interface Loopback0
description ***Loopback***
ip address 192.168.1.1 255.255.255.255
ip ospf 1 area 0
!
interface Ethernet0/0
description **Connected to R1-LAN**
ip address 10.10.110.1 255.255.255.0
ip ospf 1 area 0
!
interface Ethernet0/1
description **Connected to L2SW**
ip address 10.10.230.1 255.255.255.0
ip ospf hello-interval 25
ip ospf 1 area 0
!
log-adjacency-changes
R2# show running-config
R2
!
interface Loopback0
description **Loopback**
ip address 192.168.2.2 255.255.255.255
ip ospf 2 area 0
!
interface Ethernet0/0
description **Connected to R2-LAN**
ip address 10.10.120.1 255.255.255.0
ip ospf 2 area 0
!
interface Ethernet0/1
description **Connected to L2SW**
ip address 10.10.230.2 255.255.255.0
ip ospf 2 area 0
!
router ospf 2
log-adjacency-changes
R3# show running-config
R3
username R6 password CISCO36
!
interface Loopback0
description **Loopback**
ip address 192.168.3.3 255.255.255.255
ip ospf 3 area 0
!
interface Ethernet0/0
description **Connected to L2SW**
ip address 10.10.230.3 255.255.255.0
ip ospf 3 area 0
!
interface Serial1/0
description **Connected to R4-Branch1 office**
ip address 10.10.240.1 255.255.255.252
encapsulation ppp
ip ospf 3 area 0
!
interface Serial1/1
description **Connected to R5-Branch2 office**
ip address 10.10.240.5 255.255.255.252
encapsulation ppp
ip ospf hello-interval 50
ip ospf 3 area 0
!
interface Serial1/2
description **Connected to R6-Branch3 office**
ip address 10.10.240.9 255.255.255.252
encapsulation ppp
ip ospf 3 area 0
ppp authentication chap
!
router ospf 3
router-id 192.168.3.3
!
R4# show running-config
R4
!
interface Loopback0
description **Loopback**
ip address 192.168.4.4 255.255.255.255
ip ospf 4 area 2
!
interface Ethernet0/0
ip address 172.16.113.1 255.255.255.0
ip ospf 4 area 2
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.2 255.255.255.252
encapsulation ppp
ip ospf 4 area 2
!
router ospf 4
log-adjacency-changes
R5# show running-config
R5
!
interface Loopback0
description **Loopback**
ip address 192.168.5.5 255.255.255.255
ip ospf 5 area 0
!
interface Ethernet0/0
ip address 172.16.114.1 255.255.255.0
ip ospf 5 area 0
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.6 255.255.255.252
encapsulation ppp
ip ospf 5 area 0
!
router ospf 5
log-adjacency-changes
R6# show running-config
R6
username R3 password CISCO36
!
interface Loopback0
description **Loopback**
ip address 192.168.6.6 255.255.255.255
ip ospf 6 area 0
!
interface Ethernet0/0
ip address 172.16.115.1 255.255.255.0
ip ospf 6 area 0
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.10 255.255.255.252
encapsulation ppp
ip ospf 6 area 0
ppp authentication chap
!
router ospf 6
router-id 192.168.3.3
!
R1 does not form an OSPF neighbor adjacency with R2. Which option would fix the issue? Correct
Incorrect
-
Question 438 of 555
438. Question
Hotspot Questions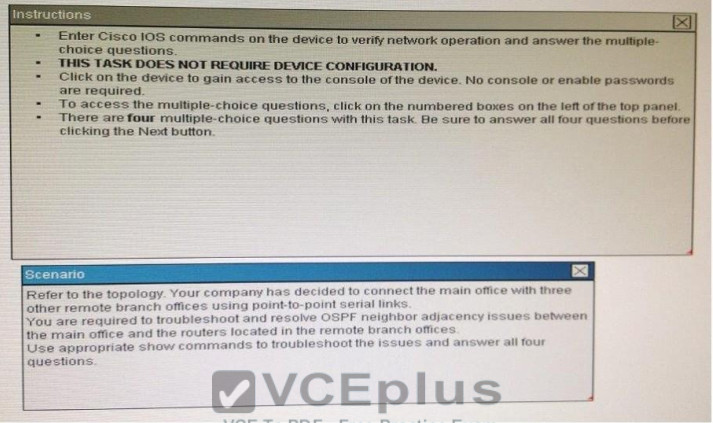
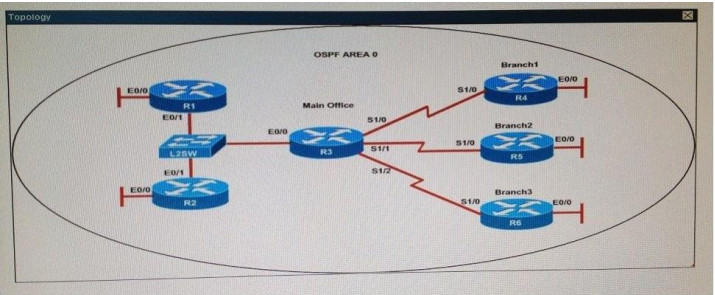 R1# show running-config
interface Loopback0
description ***Loopback***
ip address 192.168.1.1 255.255.255.255
ip ospf 1 area 0
!
interface Ethernet0/0
description **Connected to R1-LAN**
ip address 10.10.110.1 255.255.255.0
ip ospf 1 area 0
!
interface Ethernet0/1
description **Connected to L2SW**
ip address 10.10.230.1 255.255.255.0
ip ospf hello-interval 25
ip ospf 1 area 0
!
log-adjacency-changes
R2# show running-config
R2
!
interface Loopback0
description **Loopback**
ip address 192.168.2.2 255.255.255.255
ip ospf 2 area 0
!
interface Ethernet0/0
description **Connected to R2-LAN**
ip address 10.10.120.1 255.255.255.0
ip ospf 2 area 0
!
interface Ethernet0/1
description **Connected to L2SW**
ip address 10.10.230.2 255.255.255.0
ip ospf 2 area 0
!
router ospf 2
log-adjacency-changes
R3# show running-config
R3
username R6 password CISCO36
!
interface Loopback0
description **Loopback**
ip address 192.168.3.3 255.255.255.255
ip ospf 3 area 0
!
interface Ethernet0/0
description **Connected to L2SW**
ip address 10.10.230.3 255.255.255.0
ip ospf 3 area 0
!
interface Serial1/0
description **Connected to R4-Branch1 office**
ip address 10.10.240.1 255.255.255.252
encapsulation ppp
ip ospf 3 area 0
!
interface Serial1/1
description **Connected to R5-Branch2 office**
ip address 10.10.240.5 255.255.255.252
encapsulation ppp
ip ospf hello-interval 50
ip ospf 3 area 0
!
interface Serial1/2
description **Connected to R6-Branch3 office**
ip address 10.10.240.9 255.255.255.252
encapsulation ppp
ip ospf 3 area 0
ppp authentication chap
!
router ospf 3
router-id 192.168.3.3
!
R4# show running-config
R4
!
interface Loopback0
description **Loopback**
ip address 192.168.4.4 255.255.255.255
ip ospf 4 area 2
!
interface Ethernet0/0
ip address 172.16.113.1 255.255.255.0
ip ospf 4 area 2
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.2 255.255.255.252
encapsulation ppp
ip ospf 4 area 2
!
router ospf 4
log-adjacency-changes
R5# show running-config
R5
!
interface Loopback0
description **Loopback**
ip address 192.168.5.5 255.255.255.255
ip ospf 5 area 0
!
interface Ethernet0/0
ip address 172.16.114.1 255.255.255.0
ip ospf 5 area 0
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.6 255.255.255.252
encapsulation ppp
ip ospf 5 area 0
!
router ospf 5
log-adjacency-changes
R6# show running-config
R6
username R3 password CISCO36
!
interface Loopback0
description **Loopback**
ip address 192.168.6.6 255.255.255.255
ip ospf 6 area 0
!
interface Ethernet0/0
ip address 172.16.115.1 255.255.255.0
ip ospf 6 area 0
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.10 255.255.255.252
encapsulation ppp
ip ospf 6 area 0
ppp authentication chap
!
router ospf 6
router-id 192.168.3.3
!
An OSPF neighbor adjacency is not formed between R3 in the main office and R5 in the Branch2 office. What is causing the problem?
Correct
R1# show running-config
interface Loopback0
description ***Loopback***
ip address 192.168.1.1 255.255.255.255
ip ospf 1 area 0
!
interface Ethernet0/0
description **Connected to R1-LAN**
ip address 10.10.110.1 255.255.255.0
ip ospf 1 area 0
!
interface Ethernet0/1
description **Connected to L2SW**
ip address 10.10.230.1 255.255.255.0
ip ospf hello-interval 25
ip ospf 1 area 0
!
log-adjacency-changes
R2# show running-config
R2
!
interface Loopback0
description **Loopback**
ip address 192.168.2.2 255.255.255.255
ip ospf 2 area 0
!
interface Ethernet0/0
description **Connected to R2-LAN**
ip address 10.10.120.1 255.255.255.0
ip ospf 2 area 0
!
interface Ethernet0/1
description **Connected to L2SW**
ip address 10.10.230.2 255.255.255.0
ip ospf 2 area 0
!
router ospf 2
log-adjacency-changes
R3# show running-config
R3
username R6 password CISCO36
!
interface Loopback0
description **Loopback**
ip address 192.168.3.3 255.255.255.255
ip ospf 3 area 0
!
interface Ethernet0/0
description **Connected to L2SW**
ip address 10.10.230.3 255.255.255.0
ip ospf 3 area 0
!
interface Serial1/0
description **Connected to R4-Branch1 office**
ip address 10.10.240.1 255.255.255.252
encapsulation ppp
ip ospf 3 area 0
!
interface Serial1/1
description **Connected to R5-Branch2 office**
ip address 10.10.240.5 255.255.255.252
encapsulation ppp
ip ospf hello-interval 50
ip ospf 3 area 0
!
interface Serial1/2
description **Connected to R6-Branch3 office**
ip address 10.10.240.9 255.255.255.252
encapsulation ppp
ip ospf 3 area 0
ppp authentication chap
!
router ospf 3
router-id 192.168.3.3
!
R4# show running-config
R4
!
interface Loopback0
description **Loopback**
ip address 192.168.4.4 255.255.255.255
ip ospf 4 area 2
!
interface Ethernet0/0
ip address 172.16.113.1 255.255.255.0
ip ospf 4 area 2
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.2 255.255.255.252
encapsulation ppp
ip ospf 4 area 2
!
router ospf 4
log-adjacency-changes
R5# show running-config
R5
!
interface Loopback0
description **Loopback**
ip address 192.168.5.5 255.255.255.255
ip ospf 5 area 0
!
interface Ethernet0/0
ip address 172.16.114.1 255.255.255.0
ip ospf 5 area 0
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.6 255.255.255.252
encapsulation ppp
ip ospf 5 area 0
!
router ospf 5
log-adjacency-changes
R6# show running-config
R6
username R3 password CISCO36
!
interface Loopback0
description **Loopback**
ip address 192.168.6.6 255.255.255.255
ip ospf 6 area 0
!
interface Ethernet0/0
ip address 172.16.115.1 255.255.255.0
ip ospf 6 area 0
!
interface Serial1/0
description **Connected to R3-Main Branch office**
ip address 10.10.240.10 255.255.255.252
encapsulation ppp
ip ospf 6 area 0
ppp authentication chap
!
router ospf 6
router-id 192.168.3.3
!
An OSPF neighbor adjacency is not formed between R3 in the main office and R5 in the Branch2 office. What is causing the problem?
Correct
Incorrect
-
Question 439 of 555
439. Question
Hotspot Questions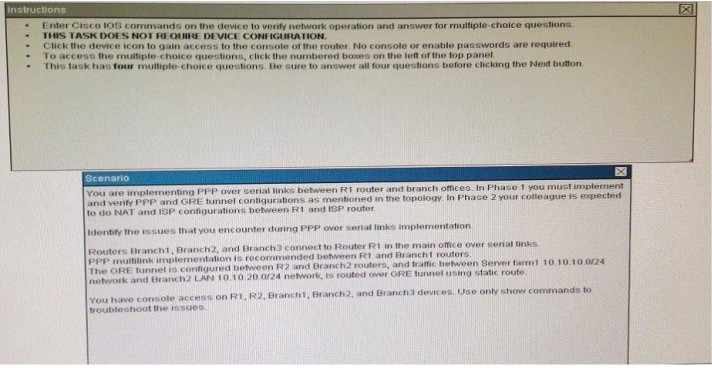
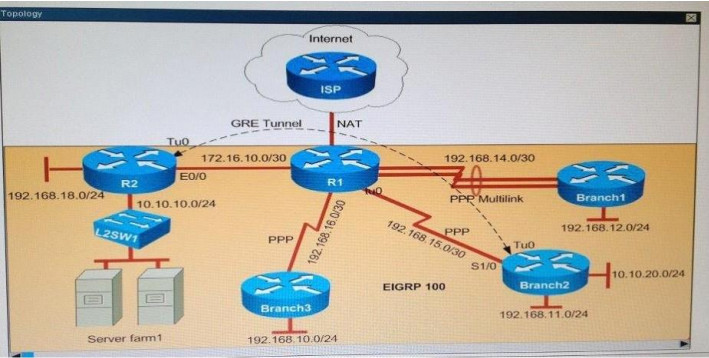 Why is the Branch2 network 10.1 0.20.0/24 unable to communicate with the Server farm1 network 10.1 0.10.0/24 over the GRE tunnel? Correct
Why is the Branch2 network 10.1 0.20.0/24 unable to communicate with the Server farm1 network 10.1 0.10.0/24 over the GRE tunnel? Correct
Incorrect
-
Question 440 of 555
440. Question
Hotspot Questions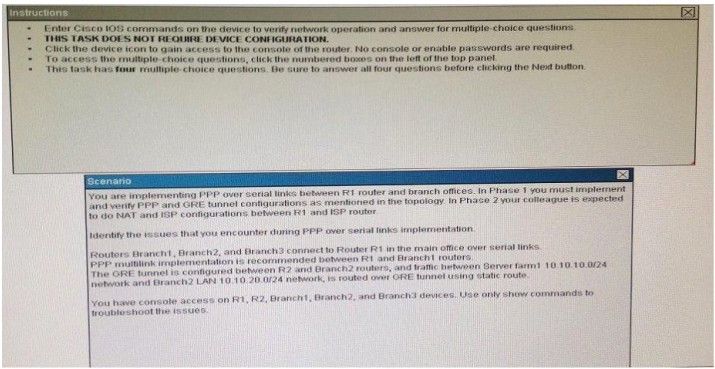
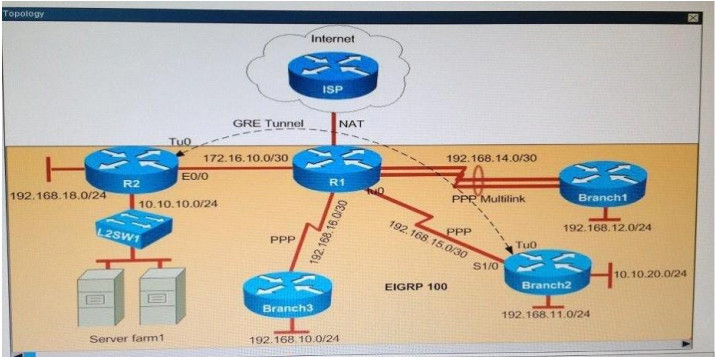 Why has the Branch3 router lost connectivity with R1? Use only show commands to troubleshoot because usage of the debug command is restricted on the Branch3 and R1 routers. Correct
Why has the Branch3 router lost connectivity with R1? Use only show commands to troubleshoot because usage of the debug command is restricted on the Branch3 and R1 routers. Correct
Incorrect
-
Question 441 of 555
441. Question
Hotspot Questions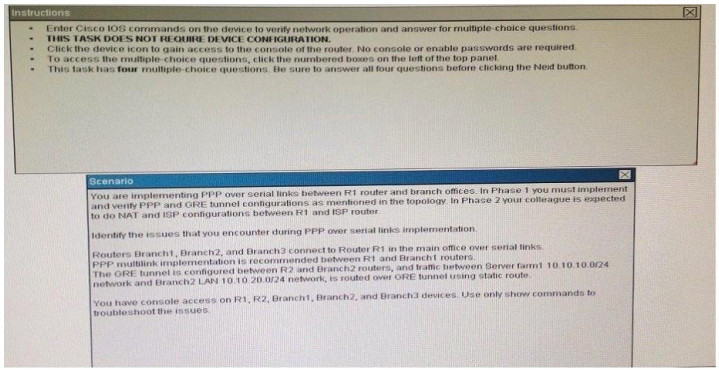
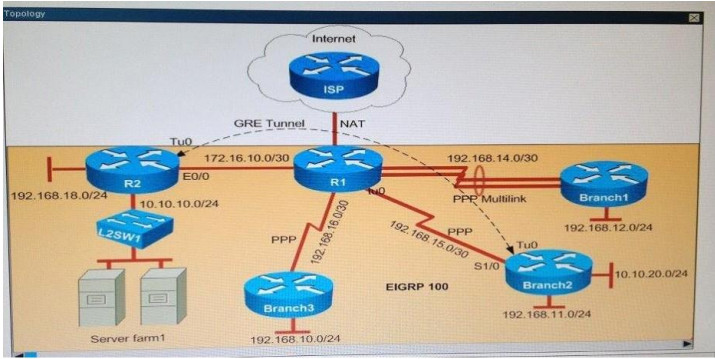 Which statement about the router configurations is correct? Correct
Which statement about the router configurations is correct? Correct
Incorrect
-
Question 442 of 555
442. Question
Hotspot Questions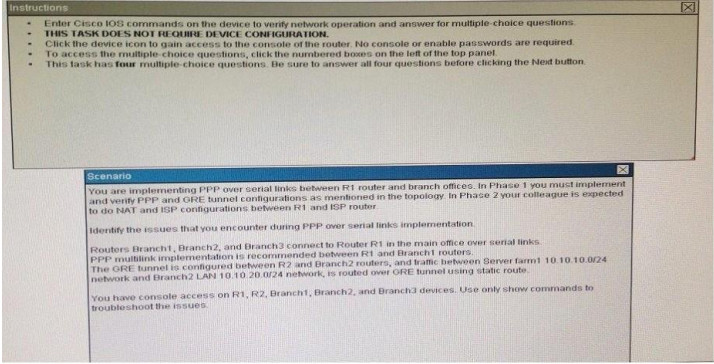
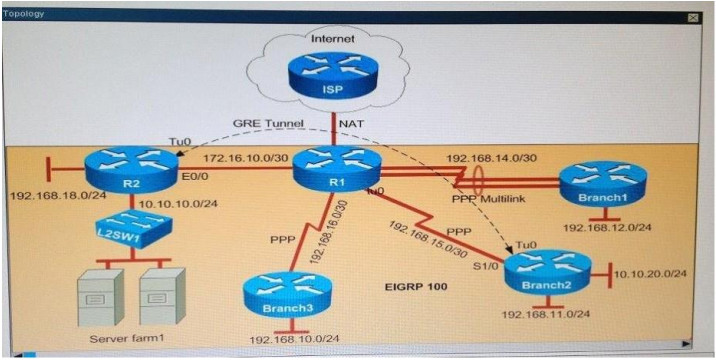 Why did Branch1 router lose WAN connectivity with R1 router? Correct
Why did Branch1 router lose WAN connectivity with R1 router? Correct
Incorrect
-
Question 443 of 555
443. Question
While you were troubleshooting a connection issue, a ping from one VLAN to another VLAN on the same switch failed. Which command verifies that IP routing is enabled on interfaces and the local VLANs are up?Correct
Incorrect
Hint
Initiate a ping from an end device in one VLAN to the interface VLAN on another VLAN in order to verify that the switch routes between VLANs. In this example, ping from VLAN 2 (10.1.2.1) to Interface VLAN 3 (10.1.3.1) or Interface VLAN 10 (10.1.10.1). If the ping fails, verify that IP routing is enabled and that the VLAN interfaces status is up with the show ip interface brief command. -
Question 444 of 555
444. Question
Which statement about DTP is true?Correct
Incorrect
Hint
Disabling Dynamic Trunking Protocol (DTP) Cisco's Dynamic Trunking Protocol can facilitate the automatic creation of trunks between two switches. When two connected ports are configured in dynamic mode, and at least one of the ports is configured as desirable, the two switches will negotiate the formation of a trunk across the link. DTP isn't to be confused with VLAN Trunking Protocol (VTP), although the VTP domain does come into play. DTP on the wire is pretty simple, essentially only advertising the VTP domain, the status of the interface, and it's DTP type. These packets are transmitted in the native (or access) VLAN every 60 seconds both natively and with ISL encapsulation (tagged as VLAN 1) when DTP is enabled.
DTP on the wire is pretty simple, essentially only advertising the VTP domain, the status of the interface, and it's DTP type. These packets are transmitted in the native (or access) VLAN every 60 seconds both natively and with ISL encapsulation (tagged as VLAN 1) when DTP is enabled. -
Question 445 of 555
445. Question
Which feature can you use to monitor traffic on a switch by replicating it to another port or ports on the same switch?Correct
Incorrect
Hint
A source port, also called a monitored port, is a switched or routed port that you monitor for network traffic analysis. In a single local SPAN session or RSPAN source session, you can monitor source port traffic, such as received (Rx), transmitted (Tx), or bidirectional (both). The switch supports any number of source ports (up to the maximum number of available ports on the switch) and any number of source VLANs. A source port has these characteristics: It can be any port type, such as EtherChannel, Fast Ethernet, Gigabit Ethernet, and so forth. It can be monitored in multiple SPAN sessions. It cannot be a destination port. Each source port can be configured with a direction (ingress, egress, or both) to monitor. For EtherChannel sources, the monitored direction applies to all physical ports in the group. Source ports can be in the same or different VLANs. For VLAN SPAN sources, all active ports in the source VLAN are included as source ports. -
Question 446 of 555
446. Question
Which two circumstances can cause collision domain issues on VLAN domain? (Choose two.)Correct
Incorrect
Hint
Collision Domains A collision domain is an area of a single LAN where end stations contend for access to the network because all end stations are connected to a shared physical medium. If two connected devices transmit onto the media at the same time, a collision occurs. When a collision occurs, a JAM signal is sent on the network, indicating that a collision has occurred and that devices should ignore any fragmented data associated with the collision. Both sending devices back off sending their data for a random amount and then try again if the medium is free for transmission. Therefore, collisions effectively delay transmission of data, lowering the effective throughput available to a device. The more devices that are attached to a collision domain, the greater the chances of collisions; this results in lower bandwidth and performance for each device attached to the collision domain. Bridges and switches terminate the physical signal path of a collision domain, allowing you to segment separate collision domains, breaking them up into multiple smaller pieces to provide more bandwidth per user within the new collision domains formed. -
Question 447 of 555
447. Question
What is a difference between TACACS+ and RADIUS in AAA?Correct
Incorrect
-
Question 448 of 555
448. Question
Which version of SNMP first allowed user-based access?Correct
Incorrect
-
Question 449 of 555
449. Question
Which IEEE standard does PVST+ use to tunnel information?Correct
Incorrect
-
Question 450 of 555
450. Question
Which option describes the purpose of traffic policing?Correct
Incorrect
Hint
Traffic policing allows you to control the maximum rate of traffic transmitted or received on an interface. Traffic policing is often configured on interfaces at the edge of a network to limit traffic into or out of the network. In most Traffic Policing configurations, traffic that falls within the rate parameters is transmitted, whereas traffic that exceeds the parameters is dropped or transmitted with a different priority. -
Question 451 of 555
451. Question
Which component of the Cisco SDN solution serves as the centralized management system?Correct
Incorrect
Hint
Cisco ACI is a comprehensive SDN architecture. This policy-based automation solution supports a business-relevant application policy language, greater scalability through a distributed enforcement system, and greater network visibility. These benefits are achieved through the storage, services, and security. -
Question 452 of 555
452. Question
What are two drawbacks of implementing a link-state routing protocol? (Choose two.)Correct
Incorrect
-
Question 453 of 555
453. Question
Which part of the PPPoE server configuration contains the information used to assign an IP address to a PPPoE client?Correct
Incorrect
Hint
PPPoE is configured as a point to point connection between two Ethernet ports. As a tunneling protocol, PPPoE is used as an effective foundation for the transport of IP packets at the network layer. IP is overlaid over a PPP connection and uses PPP as a virtual dial up connection between points on the network. From the user’s perspective, a PPPoE session is initiated by using connection software on the client machine or router. PPPoE session initiation involves the identification of the Media Access Control (MAC) address of the remote device. This process, also known as PPPoE discovery -
Question 454 of 555
454. Question
Which process is associated with spanning-tree convergence?Correct
Incorrect
Hint
Spanning Tree Protocol (STP) convergence (Layer 2 convergence) happens when bridges and switches have transitioned to either the forwarding or blocking state. When layer 2 is converged, Root Switch is elected and Root Ports, Designated Ports and Non-Designated ports in all switches are selected. At Converged condition, the Root Ports and the Designated ports are in forwarding state, and all other ports are in blocking state. -
Question 455 of 555
455. Question
Which option is the benefit of implementing an intelligent DNS for a cloud computing solution?Correct
Incorrect
-
Question 456 of 555
456. Question
Which protocol supports sharing the VLAN configuration between two or more switches?Correct
Incorrect
Hint
“VTP allows a network manager to configure a switch so that it will propagate VLAN configurations to other switches in the network” VTP minimizes misconfigurations and configuration inconsistencies that can cause problems, such as duplicate VLAN names or incorrect VLAN-type specifications. VTP helps you simplify management of the VLAN database across multiple switches. VTP is a Cisco-proprietary protocol and is available on most of the Cisco switches. -
Question 457 of 555
457. Question
How can you disable DTP on a switch port?Correct
Incorrect
-
Question 458 of 555
458. Question
Which two components are used to identify a neighbor in a BGP configuration? (Choose two.)Correct
Incorrect
Hint
Use the show ip bgp neighbors (registered customers only) command to display information about the TCP and Border Gateway Protocol (BGP) connections and verify if the BGP peer is established. The output of the show ip bgp neighbors command below shows the BGP state as ‘Established’, which indicates that the BGP peer relationship has been established successfully. R1-AGS# show ip bgp neighbors | include BGP BGP neighbor is 10.10.10.2, remote AS 400, internal link BGP version 4, remote router ID 2.2.2.2 BGP state = Established, up for 00:04:20 BGP table version 1, neighbor version 1 R1-AGS# The show ip bgp neighbors command has been used above with the modifier | include BGP. This makes the output more readable by filtering the the command output and displaying the relevant parts only. In addition, the show ip bgp summary (registered customers only) command can also be used to display the status of all BGP connections, as shown below. R1-AGS(9)# show ip bgp summary BGP router identifier 10.1.1.2, local AS number 400 BGP table version is 1, main routing table version 1 Neighbor V AS MsgRcvd MsgSent TblVer InQ OutQ Up/Down State/PfxRcd 10.10.10.2 4 400 3 3 1 0 0 00:00:26 0 -
Question 459 of 555
459. Question
Which type of interface can negotiate an IP address for a PPPoE client?Correct
Incorrect
-
Question 460 of 555
460. Question
What is the default VLAN on an access port?Correct
Incorrect
-
Question 461 of 555
461. Question
Which statement about QoS default behavior is true?Correct
Incorrect
Hint
Frames received from users in the administratively-defined VLANs are classified or tagged for transmission to other devices. Based on rules that you define, a unique identifier (the tag) is inserted in each frame header before it is forwarded. The tag is examined and understood by each device before any broadcasts or transmissions to other switches, routers, or end stations. When the frame reaches the last switch or router, the tag is removed before the frame is sent to the target end station. VLANs that are assigned on trunk or access ports without identification or a tag are called native or untagged frames. For IEEE 802.1Q frames with tag information, the priority value from the header frame is used. For native frames, the default priority of the input port is used. Each port on the switch has a single receive queue buffer (the ingress port) for incoming traffic. When an untagged frame arrives, it is assigned the value of the port as its port default priority. You assign this value by using the CLI or CMS. A tagged frame continues to use its assigned CoS value when it passes through the ingress port. -
Question 462 of 555
462. Question
Refer to the exhibit. While troubleshooting a switch, you executed the show interface port-channel 1 etherchannel command and it returned this output. Which information is provided by the Load value?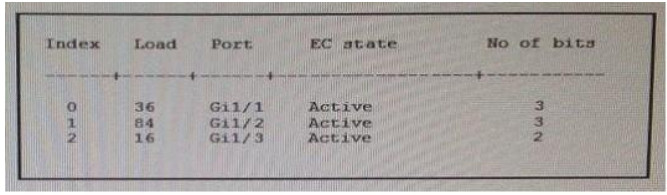 Correct
Correct
Incorrect
-
Question 463 of 555
463. Question
Which spanning-tree feature places a port immediately into a forwarding stated?Correct
Incorrect
Hint
PortFast causes a switch or trunk port to enter the spanning tree forwarding state immediately, bypassing the listening and learning states. You can use PortFast on switch or trunk ports that are connected to a single workstation, switch, or server to allow those devices to connect to the network immediately, instead of waiting for the port to transition from the listening and learning states to the forwarding state. -
Question 464 of 555
464. Question
Which protocol authenticates connected devices before allowing them to access the LAN?Correct
Incorrect
Hint
802.1X authentication involves three parties: a supplicant, an authenticator, and an authentication server. The supplicant is a client device (such as a laptop) that wishes to attach to the LAN/WLAN. The term ‘supplicant’ is also used interchangeably to refer to the software running on the client that provides credentials to the authenticator. The authenticator is a network device, such as an Ethernet switch or wireless access point; and the authentication server is typically a host running software supporting the RADIUS and EAP protocols. The authenticator acts like a security guard to a protected network. The supplicant (i.e., client device) is not allowed access through the authenticator to the protected side of the network until the supplicant’s identity has been validated and authorized. An analogy to this is providing a valid visa at the airport’s arrival immigration before being allowed to enter the country. With 802.1X port-based authentication, the supplicant provides credentials, such as user name/password or digital certificate, to the authenticator, and the authenticator forwards the credentials to the authentication server for verification. If the authentication server determines the credentials are valid, the supplicant (client device) is allowed to access resources located on the protected side of the network. -
Question 465 of 555
465. Question
Which identification number is valid for an extended ACL?Correct
Incorrect
-
Question 466 of 555
466. Question
Which two pieces of information are provided by the show controllers serial 0 command? (Choose two.)Correct
Incorrect
Hint
The show controller command provides hardware-related information useful to troubleshoot and diagnose issues with Cisco router interfaces. The Cisco 12000 Series uses a distributed architecture with a central command-line interface (CLI) at the Gigabit Route Processor (GRP) and a local CLI at each line card. -
Question 467 of 555
467. Question
Which EIGRP for IPv6 command can you enter to view the link-local addresses of the neighbors of a device?Correct
Incorrect
-
Question 468 of 555
468. Question
Which configuration can you apply to enable encapsulation on a subinterface?Correct
Incorrect
-
Question 469 of 555
469. Question
Which statement about slow inter VLAN forwarding is true?Correct
Incorrect
Hint
Common Causes of Slow IntraVLAN and InterVLAN Connectivity The symptoms of slow connectivity on a VLAN can be caused by multiple factors on different network layers. Commonly the network speed issue may be occurring on a lower level, but symptoms can be observed on a higher level as the problem masks itself under the term “slow VLAN”. To clarify, this document defines the following new terms: “slow collision domain”, “slow broadcast domain” (in other words, slow VLAN), and “slow interVLAN forwarding”. These are defined in the section Three Categories of Causes, below. In the following scenario (illustrated in the network diagram below), there is a Layer 3 (L3) switch performing interVLAN routing between the server and client VLANs. In this failure scenario, one server is connected to a switch, and the port duplex mode is configured half- duplex on the server side and full-duplex on the switch side. This misconfiguration results in a packet loss and slowness, with increased packet loss when higher traffic rates occur on the link where the server is connected. For the clients who communicate with this server, the problem looks like slow interVLAN forwarding because they do not have a problem communicating to other devices or clients on the same VLAN. The problem occurs only when communicating to the server on a different VLAN. Thus, the problem occurred on a single collision domain, but is seen as slow interVLAN forwarding. Three Categories of Causes
The causes of slowness can be divided into three categories, as follows:
Slow Collision Domain Connectivity
Collision domain is defined as connected devices configured in a half-duplex port configuration, connected to each other or a hub. If a device is connected to a switch port and full-duplex mode is configured, such a point-to-point connection is collisionless. Slowness on such a segment still can occur for different reasons.
Slow Broadcast Domain Connectivity (Slow VLAN)
Slow broadcast domain connectivity occurs when the whole VLAN (that is, all devices on the same VLAN) experiences slowness.
Slow InterVLAN Connectivity (Slow Forwarding Between VLANs) Slow interVLAN connectivity (slow forwarding between VLANs) occurs when there is no slowness on the local VLAN, but traffic needs to be forwarded to an alternate VLAN, and it is not forwarded at the expected rate.
Causes for Network Slowness
Packet Loss
In most cases, a network is considered slow when higher-layer protocols (applications) require extended time to complete an operation that typically runs faster. That slowness is caused by the loss of some packets on the network, which causes higher-level protocols like TCP or applications to time out and initiate retransmission.
Hardware Forwarding Issues With another type of slowness, caused by network equipment, forwarding (whether Layer 2 [L2] or L3) is performed slowly. This is due to a deviation from normal (designed) operation and switching to slow path forwarding. An example of this is when Multilayer Switching (MLS) on the switch forwards L3 packets between VLANs in the hardware, but due to misconfiguration, MLS is not functioning properly and forwarding is done by the router in the software (which drops the interVLAN forwarding rate significantly).
Three Categories of Causes
The causes of slowness can be divided into three categories, as follows:
Slow Collision Domain Connectivity
Collision domain is defined as connected devices configured in a half-duplex port configuration, connected to each other or a hub. If a device is connected to a switch port and full-duplex mode is configured, such a point-to-point connection is collisionless. Slowness on such a segment still can occur for different reasons.
Slow Broadcast Domain Connectivity (Slow VLAN)
Slow broadcast domain connectivity occurs when the whole VLAN (that is, all devices on the same VLAN) experiences slowness.
Slow InterVLAN Connectivity (Slow Forwarding Between VLANs) Slow interVLAN connectivity (slow forwarding between VLANs) occurs when there is no slowness on the local VLAN, but traffic needs to be forwarded to an alternate VLAN, and it is not forwarded at the expected rate.
Causes for Network Slowness
Packet Loss
In most cases, a network is considered slow when higher-layer protocols (applications) require extended time to complete an operation that typically runs faster. That slowness is caused by the loss of some packets on the network, which causes higher-level protocols like TCP or applications to time out and initiate retransmission.
Hardware Forwarding Issues With another type of slowness, caused by network equipment, forwarding (whether Layer 2 [L2] or L3) is performed slowly. This is due to a deviation from normal (designed) operation and switching to slow path forwarding. An example of this is when Multilayer Switching (MLS) on the switch forwards L3 packets between VLANs in the hardware, but due to misconfiguration, MLS is not functioning properly and forwarding is done by the router in the software (which drops the interVLAN forwarding rate significantly). -
Question 470 of 555
470. Question
Which statement about the IP SLAs ICMP Echo operation is true?Correct
Incorrect
Hint
This module describes how to configure an IP Service Level Agreements (SLAs) Internet Control Message Protocol (ICMP) Echo operation to monitor end-to-end response time between a Cisco router and devices using IPv4 or IPv6. ICMP Echo is useful for troubleshooting network connectivity issues. This module also demonstrates how the results of the ICMP Echo operation can be displayed and analyzed to determine how the network IP connections are performing. ICMP Echo Operation The ICMP Echo operation measures end-to-end response time between a Cisco router and any devices using IP. Response time is computed by measuring the time taken between sending an ICMP Echo request message to the destination and receiving an ICMP Echo reply. In the figure below ping is used by the ICMP Echo operation to measure the response time between the source IP SLAs device and the destination IP device. Many customers use IP SLAs ICMP-based operations, in-house ping testing, or ping-based dedicated probes for response time measurements. The IP SLAs ICMP Echo operation conforms to the same IETF specifications for ICMP ping testing and the two methods result in the same response times.
Configuring a Basic ICMP Echo Operation on the Source Device SUMMARY STEPS
1. enable
2. configure terminal
3. ip sla operation-number
4. icmp-echo {destination-ip-address | destination-hostname} [source-ip {ip-address | hostname} |
source-interface interface-name]
5. frequency seconds 6. end
The IP SLAs ICMP Echo operation conforms to the same IETF specifications for ICMP ping testing and the two methods result in the same response times.
Configuring a Basic ICMP Echo Operation on the Source Device SUMMARY STEPS
1. enable
2. configure terminal
3. ip sla operation-number
4. icmp-echo {destination-ip-address | destination-hostname} [source-ip {ip-address | hostname} |
source-interface interface-name]
5. frequency seconds 6. end -
Question 471 of 555
471. Question
Which option describes how a switch in rapid PVST+ mode responds to a topology change?Correct
Incorrect
Hint
Rapid PVST+This spanning-tree mode is the same as PVST+ except that is uses a rapid convergence based on the IEEE 802.1w standard. To provide rapid convergence, the rapid PVST+ immediately deletes dynamically learned MAC address entries on a per-port basis upon receiving a topology change. By contrast, PVST+ uses a short aging time for dynamically learned MAC address entries. The rapid PVST+ uses the same configuration as PVST+ (except where noted), and the switch needs only minimal extra configuration. The benefit of rapid PVST+ is that you can migrate a large PVST+ install base to rapid PVST+ without having to learn the complexities of the MSTP configuration and without having to reprovision your network. In rapid-PVST+ mode, each VLAN runs its own spanning-tree instance up to the maximum supported. -
Question 472 of 555
472. Question
Which type of topology is required by DMVPN?Correct
Incorrect
-
Question 473 of 555
473. Question
Refer to the exhibit. Router edge-1 is unable to establish OSPF neighbor adjacency with router ISP-1. Which two configuration changes can you make on edge-1 to allow the two routers to establish adjacency? (Choose two.)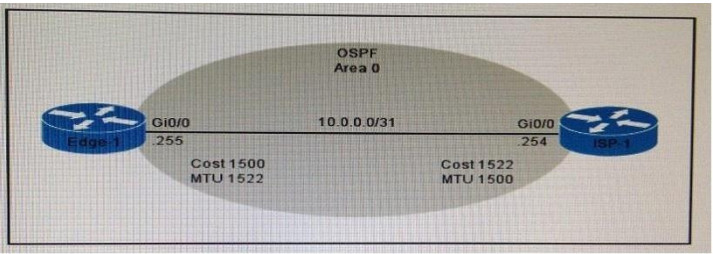 Correct
Correct
Incorrect
Hint
A situation can occur where the interface MTU is at a high value, for example 9000, while the real value of the size of packets that can be forwarded over this interface is 1500. If there is a mismatch on MTU on both sides of the link where OSPF runs, then the OSPF adjacency will not form because the MTU value is carried in the Database Description (DBD) packets and checked on the other side. -
Question 474 of 555
474. Question
Which statement about switch access ports is true?Correct
Incorrect
Hint
“If an access port receives a packet with an 802.1Q tag in the header other than the access VLAN value, that port drops the packet without learning its MAC source address.” -
Question 475 of 555
475. Question
Which option is a benefit of switch stacking?Correct
Incorrect
Hint
A stackable switch is a network switch that is fully functional operating standalone but which can also be set up to operate together with one or more other network switches, with this group of switches showing the characteristics of a single switch but having the port capacity of the sum of the combined switches. -
Question 476 of 555
476. Question
What is the first step you perform to configure an SNMPv3 user?Correct
Incorrect
Hint
The first task in configuring SNMPv3 is to define a view. To simplify things, we’ll create a view that allows access to the entire internet subtree: router(config)#snmp-server view readview internet included This command creates a view called readview. If you want to limit the view to the system tree, for example, replace internet with system. The included keyword states that the specified tree should be included in the view; use excluded if you wanted to exclude a certain subtree. Next, create a group that uses the new view. The following command creates a group called readonly ; v3 means that SNMPv3 should be used. The auth keyword specifies that the entity should authenticate packets without encrypting them; read readview says that the view named readview should be used whenever members of the readonly group access the router. router(config)#snmp-server group readonly v3 auth read readview. -
Question 477 of 555
477. Question
Which statement about named ACLs is true?Correct
Incorrect
Hint
Named Access Control Lists (ACLs) allows standard and extended ACLs to be given names instead of numbers. Unlike in numbered Access Control Lists (ACLs), we can edit Named Access Control Lists. Another benefit of using named access configuration mode is that you can add new statements to the access list, and insert them wherever you like. With the legacy syntax, you must delete the entire access list before reapplying it using the updated rules. -
Question 478 of 555
478. Question
Which two switch states are valid for 802.1w? (Choose two.)Correct
Incorrect
Hint
Port States There are only three port states left in RSTP that correspond to the three possible operational states. The 802.1D disabled, blocking, and listening states are merged into a unique 802.1w discarding state.
-
Question 479 of 555
479. Question
Which statement about MPLS is true?Correct
Incorrect
Hint
MPLS belongs to the family of packet-switched networks. MPLS operates at a layer that is generally considered to lie between traditional definitions of OSI Layer 2 (data link layer) and Layer 3 (network layer), and thus is often referred to as a layer 2.5 protocol. -
Question 480 of 555
480. Question
Which Cisco platform can verify ACLs?Correct
Incorrect
-
Question 481 of 555
481. Question
Which three options are the HSRP states for a router? (Choose three.)Correct
Incorrect
Hint
HSRP States
-
Question 482 of 555
482. Question
You enter the show ipv6 route command on an OSPF device and the device displays a route. Which conclusion can you draw about the environment?Correct
Incorrect
-
Question 483 of 555
483. Question
Which NTP command configures the local device as an NTP reference clock source?Correct
Incorrect
-
Question 484 of 555
484. Question
Which routing protocol has the smallest default administrative distance?Correct
Incorrect
Hint
http://www.cisco.com/c/en/us/support/docs/ip/border-gateway-protocol-bgp/15986-admindistance.html Default Distance Value TableThis table lists the administrative distance default values of the protocols that Cisco supports: Route Source Default Distance Values Connected interface Static route Enhanced Interior Gateway Routing Protocol (EIGRP) summary route External Border Gateway Protocol (BGP) Internal EIGRP IGRP OSPF Intermediate System-to-Intermediate System (IS-IS) Routing Information Protocol (RIP) Exterior Gateway Protocol (EGP) On Demand Routing (ODR) External EIGRP Internal BGP Unknown* -
Question 485 of 555
485. Question
Which statement about static routes is true?Correct
Incorrect
Hint
Static routing can be used to define an exit point from a router when no other routes are available or necessary. This is called a default route. -
Question 486 of 555
486. Question
Under which circumstance should a network administrator implement one-way NAT?Correct
Incorrect
Hint
NAT operation is typically transparent to both the internal and external hosts. Typically the internal host is aware of the true IP address and TCP or UDP port of the external host. Typically the NAT device may function as the default gateway for the internal host. However the external host is only aware of the public IP address for the NAT device and the particular port being used to communicate on behalf of a specific internal host. NAT and TCP/UDP “Pure NAT”, operating on IP alone, may or may not correctly parse protocols that are totally concerned with IP information, such as ICMP, depending on whether the payload is interpreted by a host on the “inside” or “outside” of translation. As soon as the protocol stack is traversed, even with such basic protocols as TCP and UDP, the protocols will break unless NAT takes action beyond the network layer. IP packets have a checksum in each packet header, which provides error detection only for the header. IP datagrams may become fragmented and it is necessary for a NAT to reassemble these fragments to allow correct recalculation of higher-level checksums and correct tracking of which packets belong to which connection. The major transport layer protocols, TCP and UDP, have a checksum that covers all the data they carry, as well as the TCP/UDP header, plus a “pseudo-header” that contains the source and destination IP addresses of the packet carrying the TCP/UDP header. For an originating NAT to pass TCP or UDP successfully, it must recompute the TCP/UDP header checksum based on the translated IP addresses, not the original ones, and put that checksum into the TCP/UDP header of the first packet of the fragmented set of packets. The receiving NAT must recompute the IP checksum on every packet it passes to the destination host, and also recognize and recompute the TCP/UDP header using the retranslated addresses and pseudo-header. This is not a completely solved problem. One solution is for the receiving NAT to reassemble the entire segment and then recompute a checksum calculated across all packets. The originating host may perform Maximum transmission unit (MTU) path discovery to determine the packet size that can be transmitted without fragmentation, and then set the don’t fragment (DF) bit in the appropriate packet header field. Of course, this is only a one-way solution, because the responding host can send packets of any size, which may be fragmented before reaching the NAT. -
Question 487 of 555
487. Question
Which component of a routing table entry represents the subnet mask?Correct
Incorrect
Hint
IP Routing Table Entry TypesAn entry in the IP routing table contains the following information in the order presented: Network ID. The network ID or destination corresponding to the route. The network ID can be class-based, subnet, or supernet network ID, or an IP address for a host route. Network Mask. The mask that is used to match a destination IP address to the network ID. Next Hop. The IP address of the next hop. Interface. An indication of which network interface is used to forward the IP packet. Metric. A number used to indicate the cost of the route so the best route among possible multiple routes to the same destination can be selected. A common use of the metric is to indicate the number of hops (routers crossed) to the network ID. Routing table entries can be used to store the following types of routes: irectly Attached Network IDs. Routes for network IDs that are directly attached. For directly attached networks, the Next Hop field can be blank or contain the IP address of the interface on that network. Remote Network IDs. Routes for network IDs that are not directly attached but are available across other routers. For remote networks, the Next Hop field is the IP address of a local router in between the forwarding node and the remote network. Host Routes. A route to a specific IP address. Host routes allow routing to occur on a per- IP address basis. For host routes, the network ID is the IP address of the specified host and the network mask is 255.255.255.255. Default Route. The default route is designed to be used when a more specific network ID or host route is not found. The default route network ID is 0.0.0.0 with the network mask of 0.0.0.0. -
Question 488 of 555
488. Question
When a router makes a routing decision for a packet that is received from one network and destined to another, which portion of the packet does if replace?Correct
Incorrect
Hint
Router Switching Function (1.2.1.1)A primary function of a router is to forward packets toward their destination. This is accomplished by using a switching function, which is the process used by a router to accept a packet on one interface and forward it out of another interface. A key responsibility of the switching function is to encapsulate packets in the appropriate data link frame type for the outgoing data link. NOTE: In this context, the term “switching” literally means moving packets from source to destination and should not be confused with the function of a Layer 2 switch. After the router has determined the exit interface using the path determination function, the router must encapsulate the packet into the data link frame of the outgoing interface. What does a router do with a packet received from one network and destined for another network? The router performs the following three major steps: Step 1. De-encapsulates the Layer 3 packet by removing the Layer 2 frame header and trailer. Step 2. Examines the destination IP address of the IP packet to find the best path in the routing table. Step 3. If the router finds a path to the destination, it encapsulates the Layer 3 packet into a new Layer 2 frame and forwards the frame out the exit interface. -
Question 489 of 555
489. Question
On which type of device is every port in the same collision domain?Correct
Incorrect
Hint
Collision domainA collision domain is, as the name implies, a part of a network where packet collisions can occur. A collision occurs when two devices send a packet at the same time on the shared network segment. The packets collide and both devices must send the packets again, which reduces network efficiency. Collisions are often in a hub environment, because each port on a hub is in the same collision domain. By contrast, each port on a bridge, a switch or a router is in a separate collision domain. -
Question 490 of 555
490. Question
Which statement about routing protocols is true?Correct
Incorrect
Hint
Link State Routing Protocols Link state protocols are also called shortest-path-first protocols. Link state routing protocols have a complete picture of the network topology. Hence they know more about the whole network than any distance vector protocol. Three separate tables are created on each link state routing enabled router. One table is used to hold details about directly connected neighbors, one is used to hold the topology of the entire internetwork and the last one is used to hold the actual routing table. Link state protocols send information about directly connected links to all the routers in the network. Examples of Link state routing protocols include OSPF – Open Shortest Path First and IS-IS – Intermediate System to Intermediate System. There are also routing protocols that are considered to be hybrid in the sense that they use aspects of both distance vector and link state protocols. EIGRP – Enhanced Interior Gateway Routing Protocol is one of those hybrid routing protocols. -
Question 491 of 555
491. Question
Which technology supports the stateless assignment of IPv6 addresses?Correct
Incorrect
Hint
DHCPv6 Technology Overview IPv6 Internet Address Assignment Overview IPv6 has been developed with Internet Address assignment dynamics in mind. Being aware that IPv6 Internet addresses are 128 bits in length and written in hexadecimals makes automation of address-assignment an important aspect within network design. These attributes make it inconvenient for a user to manually assign IPv6 addresses, as the format is not naturally intuitive to the human eye. To facilitate address assignment with little or no human intervention, several methods and technologies have been developed to automate the process of address and configuration parameter assignment to IPv6 hosts. The various IPv6 address assignment methods are as follows: 1. Manual Assignment An IPv6 address can be statically configured by a human operator. However, manual assignment is quite open to errors and operational overhead due to the 128 bit length and hexadecimal attributes of the addresses, although for router interfaces and static network elements and resources this can be an appropriate solution. 2. Stateless Address Autoconfiguration (RFC2462) Stateless Address Autoconfiguration (SLAAC) is one of the most convenient methods to assign Internet addresses to IPv6 nodes. This method does not require any human intervention at all from an IPv6 user. If one wants to use IPv6 SLAAC on an IPv6 node, it is important that this IPv6 node is connected to a network with at least one IPv6 router connected. This router is configured by the network administrator and sends out Router Advertisement announcements onto the link. These announcements can allow the on-link connected IPv6 nodes to configure themselves with IPv6 address and routing parameters, as specified in RFC2462, without further human intervention. 3. Stateful DHCPv6 The Dynamic Host Configuration Protocol for IPv6 (DHCPv6) has been standardized by the IETF through RFC3315. DHCPv6 enables DHCP servers to pass configuration parameters, such as IPv6 network addresses, to IPv6 nodes. It offers the capability of automatic allocation of reusable network addresses and additional configuration flexibility. This protocol is a stateful counterpart to “IPv6 Stateless Address Autoconfiguration” (RFC 2462), and can be used separately, or in addition to the stateless autoconfiguration to obtain configuration parameters. 4. DHCPv6-PD DHCPv6 Prefix Delegation (DHCPv6-PD) is an extension to DHCPv6, and is specified in RFC3633. Classical DHCPv6 is typically focused upon parameter assignment from a DHCPv6 server to an IPv6 host running a DHCPv6 protocol stack. A practical example would be the stateful address assignment of “2001:db8::1” from a DHCPv6 server to a DHCPv6 client. DHCPv6-PD however is aimed at assigning complete subnets and other network and interface parameters from a DHCPv6-PD server to a DHCPv6-PD client. This means that instead of a single address assignment, DHCPv6-PD will assign a set of IPv6 “subnets”. An example could be the assignment of “2001:db8::/60” from a DHCPv6-PD server to a DHCPv6-PD client. This will allow the DHCPv6-PD client (often a CPE device) to segment the received address IPv6 address space, and assign it dynamically to its IPv6 enabled interfaces. 5. Stateless DHCPv6 Stateless DHCPv6 is a combination of “stateless Address Autoconfiguration” and “Dynamic Host Configuration Protocol for IPv6” and is specified by RFC3736. When using stateless- DHCPv6, a device will use Stateless Address Auto-Configuration (SLAAC) to assign one or more IPv6 addresses to an interface, while it utilizes DHCPv6 to receive “additional parameters” which may not be available through SLAAC. For example, additional parameters could include information such as DNS or NTP server addresses, and are provided in a stateless manner by DHCPv6. Using stateless DHCPv6 means that the DHCPv6 server does not need to keep track of any state of assigned IPv6 addresses, and there is no need for state refreshment as result. On network media supporting a large number of hosts associated to a single DHCPv6 server, this could mean a significant reduction in DHCPv6 messages due to the reduced need for address state refreshments. From Cisco IOS 12.4(15)T onwards the client can also receive timing information, in addition to the “additional parameters” through DHCPv6. This timing information provides an indication to a host when it should refresh its DHCPv6 configuration data. This behavior (RFC4242) is particularly useful in unstable environments where changes are likely to occur. -
Question 492 of 555
492. Question
Which feature allows a device to use a switch port that is configured for half-duplex to access the network?Correct
Incorrect
Hint
Ethernet began as a local area network technology that provided a half-duplex shared channel for stations connected to coaxial cable segments linked with signal repeaters. In this appendix, we take a detailed look at the half-duplex shared-channel mode of operation, and at the CSMA/CD mechanism that makes it work. In the original half-duplex mode, the CSMA/CD protocol allows a set of stations to compete for access to a shared Ethernet channel in a fair and equitable manner. The protocol’s rules determine the behavior of Ethernet stations, including when they are allowed to transmit a frame onto a shared Ethernet channel, and what to do when a collision occurs. Today, virtually all devices are connected to Ethernet switch ports over full-duplex media, such as twisted-pair cables. On this type of connection, assuming that both devices can support the full-duplex mode of operation and that Auto-Negotiation (AN) is enabled, the AN protocol will automatically select the highest-performance mode of operation supported by the devices at each end of the link. That will result in full-duplex mode for the vast majority of Ethernet connections with modern interfaces that support full duplex and AN. -
Question 493 of 555
493. Question
Which function enables an administrator to route multiple VLANs on a router?Correct
Incorrect
-
Question 494 of 555
494. Question
Which dynamic routing protocol uses only the hop count to determine the best path to a destination?Correct
Incorrect
-
Question 495 of 555
495. Question
What is one requirement for interfaces to run IPv6?Correct
Incorrect
Hint
To use IPv6 on your router, you must, at a minimum, enable the protocol and assign IPv6 addresses to your interfaces. -
Question 496 of 555
496. Question
Which destination IP address can a host use to send one message to multiple devices across different subnets?Correct
Incorrect
Hint
Multicast is a networking protocol where one host can send a message to a special multicast IP address and one or more network devices can listen for and receive those messages. Multicast works by taking advantage of the existing IPv4 networking infrastructure, and it does so in something of a weird fashion. As you read, keep in mind that things are a little confusing because multicast was “shoe-horned” in to an existing technology. For the rest of this article, let’s use the multicast IP address of 239.255.0.1. We’ll not worry about port numbers yet, but make a mental note that they are used in multicast. We’ll discuss that later. -
Question 497 of 555
497. Question
Which MTU size can cause a baby giant error?Correct
Incorrect
Hint
http://www.cisco.com/c/en/us/support/docs/switches/catalyst-4000-series-switches/29805- 175.html -
Question 498 of 555
498. Question
Which entity assigns IPv6 addresses to end users?Correct
Incorrect
-
Question 499 of 555
499. Question
Which option is the default switch port port-security violation mode?Correct
Incorrect
Hint
Shutdown–This mode is the default violation mode; when in this mode, the switch will automatically force the switchport into an error disabled (err-disable) state when a violation occurs. While in this state, the switchport forwards no traffic. The switchport can be brought out of this error disabled state by issuing the errdisable recovery cause CLI command or by disabling and reenabling the switchport. Shutdown VLAN–This mode mimics the behavior of the shutdown mode but limits the error disabled state the specific violating VLAN. -
Question 500 of 555
500. Question
Which statement about the inside interface configuration in a NAT deployment is true?Correct
Incorrect
Hint
This module describes how to configure Network Address Translation (NAT) for IP address conservation and how to configure inside and outside source addresses. This module also provides information about the benefits of configuring NAT for IP address conservation. NAT enables private IP internetworks that use nonregistered IP addresses to connect to the Internet. NAT operates on a device, usually connecting two networks, and translates the private (not globally unique) addresses in the internal network into legal addresses before packets are forwarded onto another network. NAT can be configured to advertise to the outside world only one address for the entire network. This ability provides additional security by effectively hiding the entire internal network behind that one address. NAT is also used at the enterprise edge to allow internal users access to the Internet and to allow Internet access to internal devices such as mail servers. -
Question 501 of 555
501. Question
Which value is indicated by the next hop in a routing table?Correct
Incorrect
Hint
The routing table contains network/next hop associations. These associations tell a router that a particular destination can be optimally reached by sending the packet to a specific router that represents the “next hop” on the way to the final destination. The next hop association can also be the outgoing or exit interface to the final destination. -
Question 502 of 555
502. Question
Which option is a valid hostname for a switch?Correct
Incorrect
-
Question 503 of 555
503. Question
Which component of the routing table ranks routing protocols according to their preferences?Correct
Incorrect
Hint
Administrative distance – This is the measure of trustworthiness of the source of the route. If a router learns about a destination from more than one routing protocol, administrative distance is compared and the preference is given to the routes with lower administrative distance. In other words, it is the believability of the source of the route. -
Question 504 of 555
504. Question
Which statement about unicast frame forwarding on a switch is true?Correct
Incorrect
-
Question 505 of 555
505. Question
Which statement about native VLAN traffic is true?Correct
Incorrect
-
Question 506 of 555
506. Question
Which route source code represents the routing protocol with a default administrative distance of 90 in the routing table?Correct
Incorrect
Hint
SStatic EEGP DEIGRP RRIP OOSPF Default Administrative distance of EIGRP protocol is 90 then answer is C. Default Distance Value TableThis table lists the administrative distance default values of the
protocols that Cisco supports:
Route Source
Default Distance Values
Connected interface
Static route
Enhanced Interior Gateway Routing Protocol (EIGRP) summary route External Border Gateway
Protocol (BGP)
Internal EIGRP
IGRP
OSPF
Intermediate System-to-Intermediate System (IS-IS) Routing Information Protocol (RIP)
Exterior Gateway Protocol (EGP)
On Demand Routing (ODR)
External EIGRP
Internal BGP
Unknown*
Default Distance Value TableThis table lists the administrative distance default values of the
protocols that Cisco supports:
Route Source
Default Distance Values
Connected interface
Static route
Enhanced Interior Gateway Routing Protocol (EIGRP) summary route External Border Gateway
Protocol (BGP)
Internal EIGRP
IGRP
OSPF
Intermediate System-to-Intermediate System (IS-IS) Routing Information Protocol (RIP)
Exterior Gateway Protocol (EGP)
On Demand Routing (ODR)
External EIGRP
Internal BGP
Unknown* -
Question 507 of 555
507. Question
Refer to the exhibit. Which statement describes the effect of this configuration?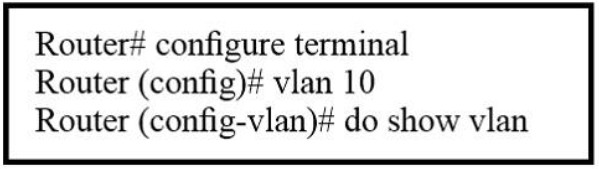 Correct
Correct
Incorrect
-
Question 508 of 555
508. Question
When enabled, which feature prevents routing protocols from sending hello messages on an interface’?Correct
Incorrect
Hint
You can use the passive-interface command in order to control the advertisement of routing information. The command enables the suppression of routing updates over some interfaces while it allows updates to be exchanged normally over other interfaces. With most routing protocols, the passive-interface command restricts outgoing advertisements only. But, when used with Enhanced Interior Gateway Routing Protocol (EIGRP), the effect is slightly different. This document demonstrates that use of the passive-interface command in EIGRP suppresses the exchange of hello packets between two routers, which results in the loss of their neighbor relationship. This stops not only routing updates from being advertised, but it also suppresses incoming routing updates. This document also discusses the configuration required in order to allow the suppression of outgoing routing updates, while it also allows incoming routing updates to be learned normally from the neighbor. -
Question 509 of 555
509. Question
Which device allows users to connect to the network using a single or double radio?Correct
Incorrect
-
Question 510 of 555
510. Question
Two hosts are attached to a switch with the default configuration. Which statement about the configuration is true?Correct
Incorrect
Hint
IP routing must be enables to allow the two hosts to communicate with each other with default configuration. http://www.cisco.com/c/en/us/support/docs/lan-switching/inter-vlan-routing/41860-howto-L3-intervlanrouting.html -
Question 511 of 555
511. Question
By default, how many MAC addresses are permitted to be learned on a switch port with port security enabled?Correct
Incorrect
-
Question 512 of 555
512. Question
Which statement about a router on a stick is true?Correct
Incorrect
Hint
https://www.freeccnaworkbook.com/workbooks/ccna/configuring-inter-vlan-routing-router-on-astick -
Question 513 of 555
513. Question
Which network topology allows all traffic to flow through a central hub?Correct
Incorrect
-
Question 514 of 555
514. Question
Which NAT type is used to translate a single inside address to a single outside address?Correct
Incorrect
Hint
Network address translation (NAT) is the process of modifying IP address information in IP packet headers while in transit across a traffic routing device. There are two different types of NAT: NAT PAT -
Question 515 of 555
515. Question
What is the default lease time for a DHCP binding?Correct
Incorrect
Hint
By default, each IP address assigned by a DHCP Server comes with a one- day lease, which is the amount of time that the address is valid. To change the lease value for an IP address, use the following command in DHCP pool configuration mode: -
Question 516 of 555
516. Question
Which RFC was created to alleviate the depletion of IPv4 public addresses?Correct
Incorrect
-
Question 517 of 555
517. Question
Which method does a connected trunk port use to tag VLAN traffic?Correct
Incorrect
Hint
http://www.cisco.com/c/en/us/support/docs/lan-switching/8021q/17056-741-4.html -
Question 518 of 555
518. Question
Configuration of which option is required on a Cisco switch for the Cisco IP phone to work?Correct
Incorrect
Hint
Configure the Switch Port to Carry Both Voice and Data TrafficWhen you connect an IP phone to a switch using a trunk link, it can cause high CPU utilization in the switches. As all the VLANs for a particular interface are trunked to the phone, it increases the number of STP instances the switch has to manage. This increases the CPU utilization. Trunking also causes unnecessary broadcast / multicast / unknown unicast traffic to hit the phone link. In order to avoid this, remove the trunk configuration and keep the voice and access VLAN configured along with Quality of Service (QoS). Technically, it is still a trunk, but it is called a Multi-VLAN Access Port (MVAP). Because voice and data traffic can travel through the same port, you should specify a different VLAN for each type of traffic. You can configure a switch port to forward voice and data traffic on different VLANs. Configure IP phone ports with a voice VLAN configuration. This configuration creates a pseudo trunk, but does not require you to manually prune the unnecessary VLANs. The voice VLAN feature enables access ports to carry IP voice traffic from an IP phone. The voice VLAN feature is disabled by default. The Port Fast feature is automatically enabled when voice VLAN is configured. When you disable voice VLAN, the Port Fast feature is not automatically disabled. -
Question 519 of 555
519. Question
Which NTP command configures the local device as an NTP reference clock source?Correct
Incorrect
-
Question 520 of 555
520. Question
Which routing protocol has the smallest default administrative distance?Correct
Incorrect
Hint
http://www.cisco.com/c/en/us/support/docs/ip/border-gateway-protocol-bgp/15986-admindistance.html Default Distance Value TableThis table lists the administrative distance default values of the protocols that Cisco supports: Route Source Default Distance Values Connected interface Static route Enhanced Interior Gateway Routing Protocol (EIGRP) summary route External Border Gateway Protocol (BGP) Internal EIGRP IGRP OSPF Intermediate System-to-Intermediate System (IS-IS) Routing Information Protocol (RIP) Exterior Gateway Protocol (EGP) On Demand Routing (ODR) External EIGRP Internal BGP Unknown* -
Question 521 of 555
521. Question
Which statement about static routes is true?Correct
Incorrect
Hint
Static routing can be used to define an exit point from a router when no other routes are available or necessary. This is called a default route. -
Question 522 of 555
522. Question
Under which circumstance should a network administrator implement one-way NAT?Correct
Incorrect
Hint
NAT operation is typically transparent to both the internal and external hosts. Typically the internal host is aware of the true IP address and TCP or UDP port of the external host. Typically the NAT device may function as the default gateway for the internal host. However the external host is only aware of the public IP address for the NAT device and the particular port being used to communicate on behalf of a specific internal host. NAT and TCP/UDP “Pure NAT”, operating on IP alone, may or may not correctly parse protocols that are totally concerned with IP information, such as ICMP, depending on whether the payload is interpreted by a host on the “inside” or “outside” of translation. As soon as the protocol stack is traversed, even with such basic protocols as TCP and UDP, the protocols will break unless NAT takes action beyond the network layer. IP packets have a checksum in each packet header, which provides error detection only for the header. IP datagrams may become fragmented and it is necessary for a NAT to reassemble these fragments to allow correct recalculation of higher-level checksums and correct tracking of which packets belong to which connection. The major transport layer protocols, TCP and UDP, have a checksum that covers all the data they carry, as well as the TCP/UDP header, plus a “pseudo-header” that contains the source and destination IP addresses of the packet carrying the TCP/UDP header. For an originating NAT to pass TCP or UDP successfully, it must recompute the TCP/UDP header checksum based on the translated IP addresses, not the original ones, and put that checksum into the TCP/UDP header of the first packet of the fragmented set of packets. The receiving NAT must recompute the IP checksum on every packet it passes to the destination host, and also recognize and recompute the TCP/UDP header using the retranslated addresses and pseudo-header. This is not a completely solved problem. One solution is for the receiving NAT to reassemble the entire segment and then recompute a checksum calculated across all packets. The originating host may perform Maximum transmission unit (MTU) path discovery to determine the packet size that can be transmitted without fragmentation, and then set the don’t fragment (DF) bit in the appropriate packet header field. Of course, this is only a one-way solution, because the responding host can send packets of any size, which may be fragmented before reaching the NAT. -
Question 523 of 555
523. Question
Which component of a routing table entry represents the subnet mask?Correct
Incorrect
Hint
IP Routing Table Entry TypesAn entry in the IP routing table contains the following information in the order presented: Network ID. The network ID or destination corresponding to the route. The network ID can be class-based, subnet, or supernet network ID, or an IP address for a host route. Network Mask. The mask that is used to match a destination IP address to the network ID. Next Hop. The IP address of the next hop. Interface. An indication of which network interface is used to forward the IP packet. Metric. A number used to indicate the cost of the route so the best route among possible multiple routes to the same destination can be selected. A common use of the metric is to indicate the number of hops (routers crossed) to the network ID. Routing table entries can be used to store the following types of routes: Directly Attached Network IDs. Routes for network IDs that are directly attached. For directly attached networks, the Next Hop field can be blank or contain the IP address of the interface on that network. Remote Network IDs. Routes for network IDs that are not directly attached but are available across other routers. For remote networks, the Next Hop field is the IP address of a local router in between the forwarding node and the remote network. Host Routes. A route to a specific IP address. Host routes allow routing to occur on a per- IP address basis. For host routes, the network ID is the IP address of the specified host and the network mask is 255.255.255.255. Default Route. The default route is designed to be used when a more specific network ID or host route is not found. The default route network ID is 0.0.0.0 with the network mask of 0.0.0.0. -
Question 524 of 555
524. Question
When a router makes a routing decision for a packet that is received from one network and destined to another, which portion of the packet does if replace?Correct
Incorrect
Hint
Router Switching Function (1.2.1.1)A primary function of a router is to forward packets toward their destination. This is accomplished by using a switching function, which is the process used by a router to accept a packet on one interface and forward it out of another interface. A key responsibility of the switching function is to encapsulate packets in the appropriate data link frame type for the outgoing data link. NOTE: In this context, the term “switching” literally means moving packets from source to destination and should not be confused with the function of a Layer 2 switch. After the router has determined the exit interface using the path determination function, the router must encapsulate the packet into the data link frame of the outgoing interface. What does a router do with a packet received from one network and destined for another network? The router performs the following three major steps: Step 1. De-encapsulates the Layer 3 packet by removing the Layer 2 frame header and trailer. Step 2. Examines the destination IP address of the IP packet to find the best path in the routing table. Step 3. If the router finds a path to the destination, it encapsulates the Layer 3 packet into a new Layer 2 frame and forwards the frame out the exit interface. -
Question 525 of 555
525. Question
On which type of device is every port in the same collision domain?Correct
Incorrect
Hint
Collision domainA collision domain is, as the name implies, a part of a network where packet collisions can occur. A collision occurs when two devices send a packet at the same time on the shared network segment. The packets collide and both devices must send the packets again, on a hub is in the same collision domain. By contrast, each port on a bridge, a switch or a router is in a separate collision domain. -
Question 526 of 555
526. Question
Which statement about routing protocols is true?Correct
Incorrect
Hint
Link State Routing Protocols Link state protocols are also called shortest-path-first protocols. Link state routing protocols have a complete picture of the network topology. Hence they know more about the whole network than any distance vector protocol. Three separate tables are created on each link state routing enabled router. One table is used to hold details about directly connected neighbors, one is used to hold the topology of the entire internetwork and the last one is used to hold the actual routing table. Link state protocols send information about directly connected links to all the routers in the network. Examples of Link state routing protocols include OSPF – Open Shortest Path First and IS-IS – Intermediate System to Intermediate System. There are also routing protocols that are considered to be hybrid in the sense that they use aspects of both distance vector and link state protocols. EIGRP – Enhanced Interior Gateway Routing Protocol is one of those hybrid routing protocols. -
Question 527 of 555
527. Question
Which technology supports the stateless assignment of IPv6 addresses?Correct
Incorrect
Hint
DHCPv6 Technology Overview IPv6 Internet Address Assignment Overview IPv6 has been developed with Internet Address assignment dynamics in mind. Being aware that IPv6 Internet addresses are 128 bits in length and written in hexadecimals makes automation of address-assignment an important aspect within network design. These attributes make it inconvenient for a user to manually assign IPv6 addresses, as the format is not naturally intuitive to the human eye. To facilitate address assignment with little or no human intervention, several configuration parameter assignment to IPv6 hosts. The various IPv6 address assignment methods are as follows: 1. Manual Assignment An IPv6 address can be statically configured by a human operator. However, manual assignment is quite open to errors and operational overhead due to the 128 bit length and hexadecimal attributes of the addresses, although for router interfaces and static network elements and resources this can be an appropriate solution. 2. Stateless Address Autoconfiguration (RFC2462) Stateless Address Autoconfiguration (SLAAC) is one of the most convenient methods to assign Internet addresses to IPv6 nodes. This method does not require any human intervention at all from an IPv6 user. If one wants to use IPv6 SLAAC on an IPv6 node, it is important that this IPv6 node is connected to a network with at least one IPv6 router connected. This router is configured These announcements can allow the on-link connected IPv6 nodes to configure themselves with IPv6 address and routing parameters, as specified in RFC2462, without further human intervention. 3. Stateful DHCPv6 The Dynamic Host Configuration Protocol for IPv6 (DHCPv6) has been standardized by the IETF through RFC3315. DHCPv6 enables DHCP servers to pass configuration parameters, such as IPv6 network addresses, to IPv6 nodes. It offers the capability of automatic allocation of reusable network addresses and additional configuration flexibility. This protocol is a stateful counterpart to “IPv6 Stateless Address Autoconfiguration” (RFC 2462), and can be used separately, or in addition to the stateless autoconfiguration to obtain configuration parameters. 4. DHCPv6-PD DHCPv6 Prefix Delegation (DHCPv6-PD) is an extension to DHCPv6, and is specified in RFC3633. Classical DHCPv6 is typically focused upon parameter assignment from a DHCPv6 server to an IPv6 host running a DHCPv6 protocol stack. A practical example would be the stateful address assignment of “2001:db8::1” from a DHCPv6 server to a DHCPv6 client. DHCPv6-PD however is aimed at assigning complete subnets and other network and interface parameters from a DHCPv6-PD server to a DHCPv6-PD client. This means that instead of a single address assignment, DHCPv6-PD will assign a set of IPv6 “subnets”. An example could be the assignment of “2001:db8::/60” from a DHCPv6-PD server to a DHCPv6-PD client. This will allow the DHCPv6-PD client (often a CPE device) to segment the received address IPv6 address space, and assign it dynamically to its IPv6 enabled interfaces. 5. Stateless DHCPv6 Stateless DHCPv6 is a combination of “stateless Address Autoconfiguration” and “Dynamic Host Configuration Protocol for IPv6” and is specified by RFC3736. When using stateless- DHCPv6, a device will use Stateless Address Auto-Configuration (SLAAC) to assign one or more IPv6 addresses to an interface, while it utilizes DHCPv6 to receive “additional parameters” which may not be available through SLAAC. For example, additional parameters could include information such as DNS or NTP server addresses, and are provided in a stateless manner by DHCPv6. Using stateless DHCPv6 means that the DHCPv6 server does not need to keep track of any state of assigned IPv6 addresses, and there is no need for state refreshment as result. On network media supporting a large number of hosts associated to a single DHCPv6 server, this could mean a significant reduction in DHCPv6 messages due to the reduced need for address state refreshments. From Cisco IOS 12.4(15)T onwards the client can also receive timing information, in addition to the “additional parameters” through DHCPv6. This timing information provides an indication to a host when it should refresh its DHCPv6 configuration data. This behavior (RFC4242) is particularly useful in unstable environments where changes are likely to occur. -
Question 528 of 555
528. Question
Which feature allows a device to use a switch port that is configured for half-duplex to access the network?Correct
Incorrect
Hint
Ethernet began as a local area network technology that provided a half-duplex shared channel for stations connected to coaxial cable segments linked with signal repeaters. In this appendix, we take a detailed look at the half-duplex shared-channel mode of operation, and at the CSMA/CD mechanism that makes it work. In the original half-duplex mode, the CSMA/CD protocol allows a set of stations to compete for access to a shared Ethernet channel in a fair and equitable manner. The protocol’s rules determine the behavior of Ethernet stations, including when they are allowed to transmit a frame onto a shared Ethernet channel, and what to do when a collision occurs. Today, virtually all devices are connected to Ethernet switch ports over full-duplex media, such as twisted-pair cables. On this type of connection, assuming that both devices can support the full-duplex mode of operation and that Auto-Negotiation (AN) is enabled, the AN protocol will automatically select the highest-performance mode of operation supported by the devices at each end of the link. That will result in full-duplex mode for the vast majority of Ethernet connections with modern interfaces that support full duplex and AN. -
Question 529 of 555
529. Question
Which function enables an administrator to route multiple VLANs on a router?Correct
Incorrect
-
Question 530 of 555
530. Question
Which dynamic routing protocol uses only the hop count to determine the best path to a destination?Correct
Incorrect
-
Question 531 of 555
531. Question
What is one requirement for interfaces to run IPv6?Correct
Incorrect
Hint
To use IPv6 on your router, you must, at a minimum, enable the protocol and assign IPv6 addresses to your interfaces. -
Question 532 of 555
532. Question
Which destination IP address can a host use to send one message to multiple devices across different subnets?Correct
Incorrect
Hint
Multicast is a networking protocol where one host can send a message to a special multicast IP address and one or more network devices can listen for and receive those messages. Multicast works by taking advantage of the existing IPv4 networking infrastructure, and it does so in something of a weird fashion. As you read, keep in mind that things are a little confusing use the multicast IP address of 239.255.0.1. We’ll not worry about port numbers yet, but make a mental note that they are used in multicast. We’ll discuss that later. -
Question 533 of 555
533. Question
Which MTU size can cause a baby giant error?Correct
Incorrect
Hint
http://www.cisco.com/c/en/us/support/docs/switches/catalyst-4000-series-switches/29805- 175.html -
Question 534 of 555
534. Question
Which entity assigns IPv6 addresses to end users?Correct
Incorrect
-
Question 535 of 555
535. Question
Which option is the default switch port port-security violation mode?Correct
Incorrect
Hint
Shutdown–This mode is the default violation mode; when in this mode, the switch will automatically force the switchport into an error disabled (err-disable) state when a violation occurs. While in this state, the switchport forwards no traffic. The switchport can be brought out of this error disabled state by issuing the errdisable recovery cause CLI command or by disabling and reenabling the switchport. Shutdown VLAN–This mode mimics the behavior of the shutdown mode but limits the error disabled state the specific violating VLAN. -
Question 536 of 555
536. Question
Which statement about the inside interface configuration in a NAT deployment is true?Correct
Incorrect
Hint
This module describes how to configure Network Address Translation (NAT) for IP address conservation and how to configure inside and outside source addresses. This module also provides information about the benefits of configuring NAT for IP address conservation. NAT enables private IP internetworks that use nonregistered IP addresses to connect to the Internet. NAT operates on a device, usually connecting two networks, and translates the private (not globally unique) addresses in the internal network into legal addresses before packets are forwarded onto another network. NAT can be configured to advertise to the outside world only one address for the entire network. This ability provides additional security by effectively hiding the entire internal network behind that one address. NAT is also used at the enterprise edge to allow internal users access to the Internet and to allow Internet access to internal devices such as mail servers. -
Question 537 of 555
537. Question
Which value is indicated by the next hop in a routing table?Correct
Incorrect
Hint
The routing table contains network/next hop associations. These associations tell a router that a particular destination can be optimally reached by sending the packet to a specific router that represents the “next hop” on the way to the final destination. The next hop association can also be the outgoing or exit interface to the final destination. -
Question 538 of 555
538. Question
Which option is a valid hostname for a switch?Correct
Incorrect
-
Question 539 of 555
539. Question
Which component of the routing table ranks routing protocols according to their preferences?Correct
Incorrect
Hint
Administrative distance – This is the measure of trustworthiness of the source of the route. If a router learns about a destination from more than one routing protocol, administrative distance is compared and the preference is given to the routes with lower administrative distance. In other words, it is the believability of the source of the route. -
Question 540 of 555
540. Question
Which statement about unicast frame forwarding on a switch is true?Correct
Incorrect
-
Question 541 of 555
541. Question
Which statement about native VLAN traffic is true?Correct
Incorrect
-
Question 542 of 555
542. Question
Which route source code represents the routing protocol with a default administrative distance of 90 in the routing table?Correct
Incorrect
Hint
SStatic EEGP DEIGRP RRIP OOSPF Default Administrative distance of EIGRP protocol is 90 then answer is C. Default Distance Value TableThis table lists the administrative distance default values of the
protocols that Cisco supports:
Route Source
Default Distance Values
Connected interface
Static route
Enhanced Interior Gateway Routing Protocol (EIGRP) summary route External Border Gateway
Protocol (BGP)
Internal EIGRP
IGRP
OSPF
Intermediate System-to-Intermediate System (IS-IS) Routing Information Protocol (RIP)
Exterior Gateway Protocol (EGP)
On Demand Routing (ODR)
External EIGRP
Internal BGP
Unknown*
Default Distance Value TableThis table lists the administrative distance default values of the
protocols that Cisco supports:
Route Source
Default Distance Values
Connected interface
Static route
Enhanced Interior Gateway Routing Protocol (EIGRP) summary route External Border Gateway
Protocol (BGP)
Internal EIGRP
IGRP
OSPF
Intermediate System-to-Intermediate System (IS-IS) Routing Information Protocol (RIP)
Exterior Gateway Protocol (EGP)
On Demand Routing (ODR)
External EIGRP
Internal BGP
Unknown*
-
Question 543 of 555
543. Question
Refer to the exhibit. Which statement describes the effect of this configuration?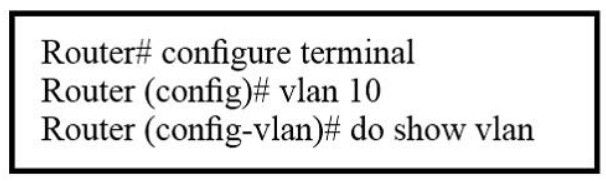 Correct
Correct
Incorrect
-
Question 544 of 555
544. Question
When enabled, which feature prevents routing protocols from sending hello messages on an interface’?Correct
Incorrect
Hint
You can use the passive-interface command in order to control the advertisement of routing information. The command enables the suppression of routing updates over some interfaces while it allows updates to be exchanged normally over other interfaces. With most routing protocols, the passive-interface command restricts outgoing advertisements only. But, when used with Enhanced Interior Gateway Routing Protocol (EIGRP), the effect is slightly different. This document demonstrates that use of the passive-interface command in EIGRP suppresses the exchange of hello packets between two routers, which results in the loss of their neighbor relationship. This stops not only routing updates from being advertised, but it also suppresses incoming routing updates. This document also discusses the configuration required in order to allow the suppression of outgoing routing updates, while it also allows incoming routing updates to be learned normally from the neighbor. -
Question 545 of 555
545. Question
Which device allows users to connect to the network using a single or double radio?Correct
Incorrect
-
Question 546 of 555
546. Question
Two hosts are attached to a switch with the default configuration. Which statement about the configuration is true?Correct
Incorrect
Hint
IP routing must be enables to allow the two hosts to communicate with each other with default configuration. http://www.cisco.com/c/en/us/support/docs/lan-switching/inter-vlan-routing/41860-howto-L3-intervlanrouting.html -
Question 547 of 555
547. Question
By default, how many MAC addresses are permitted to be learned on a switch port with port security enabled?Correct
Incorrect
-
Question 548 of 555
548. Question
Which statement about a router on a stick is true?Correct
Incorrect
Hint
https://www.freeccnaworkbook.com/workbooks/ccna/configuring-inter-vlan-routing-router-on-astick -
Question 549 of 555
549. Question
Which network topology allows all traffic to flow through a central hub?Correct
Incorrect
-
Question 550 of 555
550. Question
Which NAT type is used to translate a single inside address to a single outside address?Correct
Incorrect
Hint
Network address translation (NAT) is the process of modifying IP address information in IP packet headers while in transit across a traffic routing device. There are two different types of NAT: NAT PAT -
Question 551 of 555
551. Question
What is the default lease time for a DHCP binding?Correct
Incorrect
Hint
By default, each IP address assigned by a DHCP Server comes with a one- day lease, which is the amount of time that the address is valid. To change the lease value for an IP address, use the following command in DHCP pool configuration mode: -
Question 552 of 555
552. Question
Which RFC was created to alleviate the depletion of IPv4 public addresses?Correct
Incorrect
-
Question 553 of 555
553. Question
Which method does a connected trunk port use to tag VLAN traffic?Correct
Incorrect
Hint
http://www.cisco.com/c/en/us/support/docs/lan-switching/8021q/17056-741-4.html -
Question 554 of 555
554. Question
Configuration of which option is required on a Cisco switch for the Cisco IP phone to work?Correct
Incorrect
Hint
Configure the Switch Port to Carry Both Voice and Data TrafficWhen you connect an IP phone to a switch using a trunk link, it can cause high CPU utilization in the switches. As all the VLANs for a particular interface are trunked to the phone, it increases the number of STP instances the switch has to manage. This increases the CPU utilization. Trunking also causes unnecessary broadcast / multicast / unknown unicast traffic to hit the phone link. In order to avoid this, remove the trunk configuration and keep the voice and access VLAN configured along with Quality of Service (QoS). Technically, it is still a trunk, but it is called a Multi-VLAN Access Port (MVAP). Because voice and data traffic can travel through the same port, you should specify a different VLAN for each type of traffic. You can configure a switch port to forward voice and data traffic on different VLANs. Configure IP phone ports with a voice VLAN configuration. This configuration creates a pseudo trunk, but does not require you to manually prune the unnecessary VLANs. The voice VLAN feature enables access ports to carry IP voice traffic from an IP phone. The voice VLAN feature is disabled by default. The Port Fast feature is automatically enabled when voice VLAN is configured. When you disable voice VLAN, the Port Fast feature is not automatically disabled. -
Question 555 of 555
555. Question
Refer to the exhibit. What is the meaning of the output MTU 1500 bytes?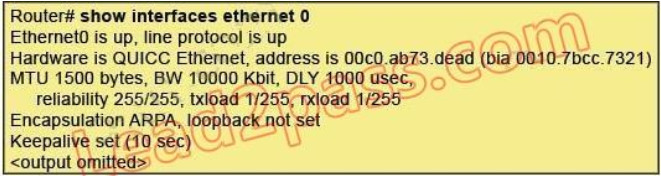 Correct
Correct
Incorrect
Hint
The Maximum Transmission Unit (MTU) defines the maximum Layer 3 packet (in bytes) that the layer can pass onwards.


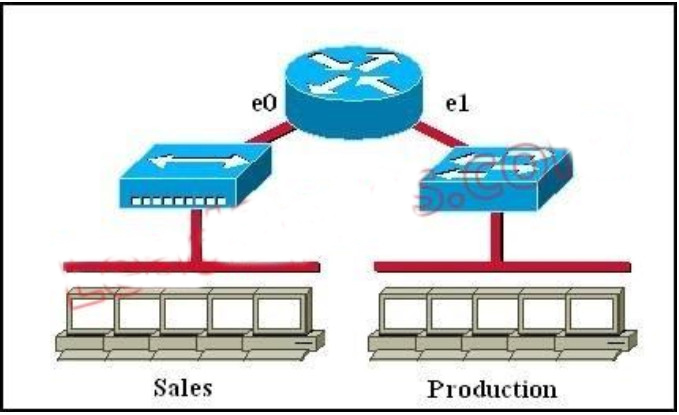
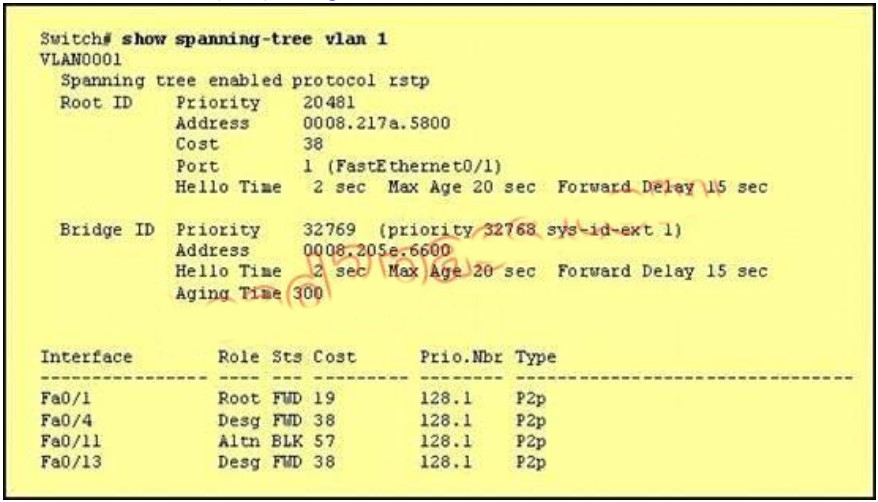
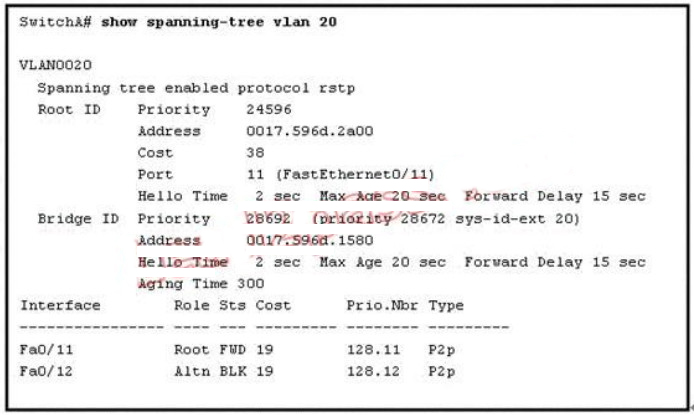
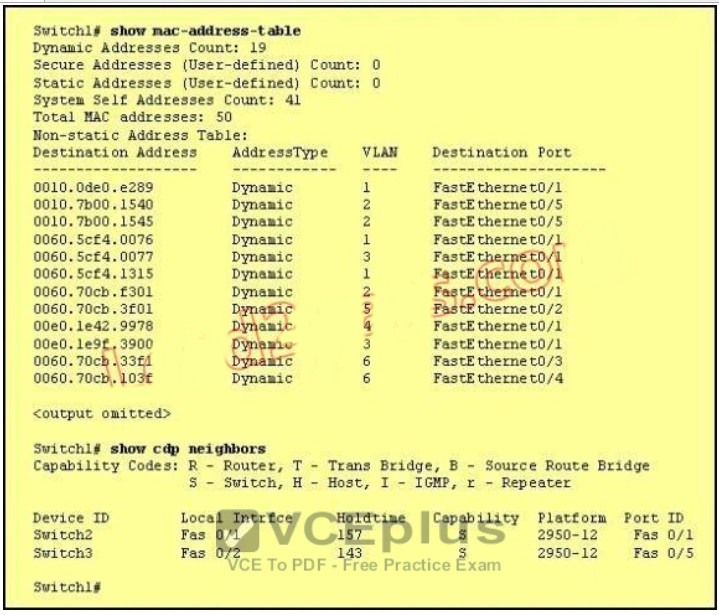

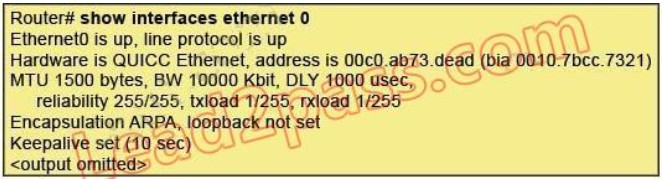

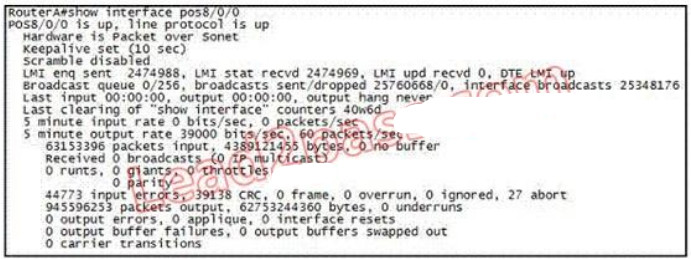
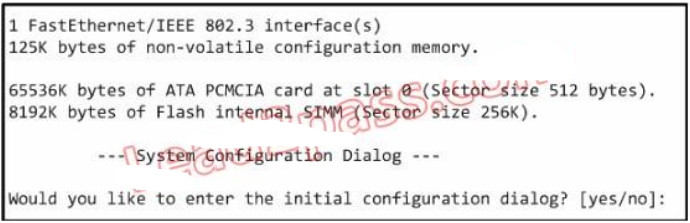
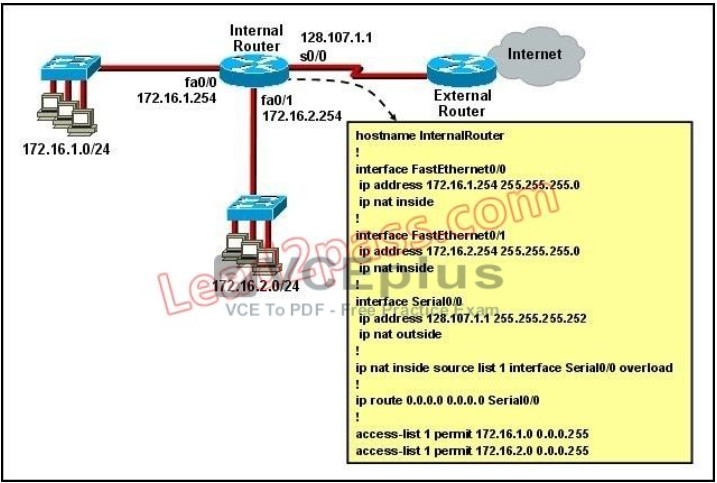
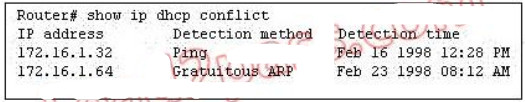
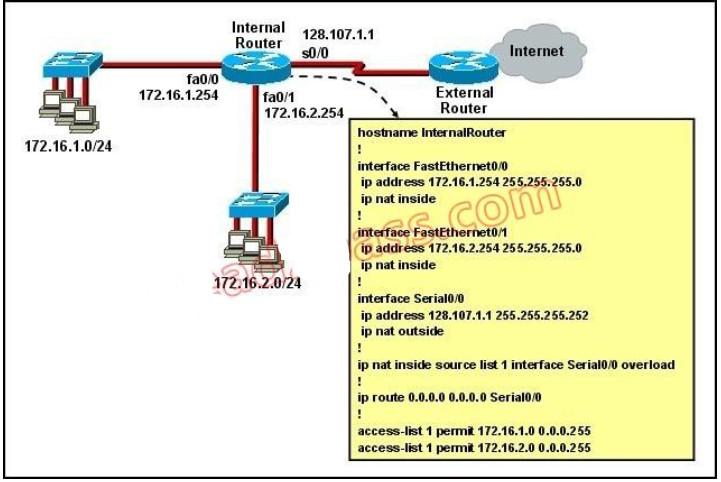


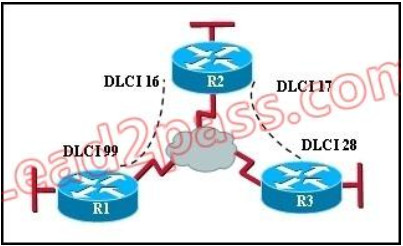
thanks is this valid
Thank you very much for sharing!!
how can I download and studying the material offline?
Thank you,
Very useful , I will do it later
is that those q in final exam