Operating Systems Basics – 1.5.2 Quiz: The Windows Operating System
1. What is the function of the kernel of an operating system?
- It provides a user interface that allows users to request a specific task.
- The kernel links the hardware drivers with the underlying electronics of a computer.
- It is an application that allows the initial configuration of a Cisco device.
- The kernel provisions hardware resources to meet software requirements.
Explanation: Operating systems function with a shell, a kernel, and the hardware. The shell interfaces with the users, allowing them to request specific tasks from the device. The kernel provisions resources from the hardware to meet software requirements. The hardware functions by using drivers and their underlying electronics. The hardware represents the physical components of the device.
2. What technology was created to replace the BIOS program on modern personal computer motherboards?
Explanation: As of 2015, most personal computer motherboards are shipped with UEFI as the replacement for the BIOS program.
3. What term is used to describe a logical drive that can be formatted to store data?
- partition
- track
- cluster
- volume
- sector
Explanation: Hard disk drives are organized by several physical and logical structures. Partitions are logical portions of the disk that can be formatted to store data. Partitions consist of tracks, sectors, and clusters. Tracks are concentric rings on the disk surface. Tracks are divided into sectors and multiple sectors are combined logically to form clusters.
4. Which command is used to manually query a DNS server to resolve a specific host name?
- tracert
- ipconfig / displaydns
- nslookup
- net
Explanation: The nslookup command was created to allow a user to manually query a DNS server to resolve a given host name. The ipconfig /displaydns command only displays previously resolved DNS entries. The tracert command was created to examine the path that packets take as they cross a network and can resolve a hostname by automatically querying a DNS server. The net command is used to manage network computers, servers, printers, and network drives.
5. Which user account should be used only to perform system management and not as the account for regular use?
- administrator
- power user
- standard user
- guest
Explanation: The administrator account is used to manage the computer and is very powerful. Best practices recommend that it be used only when it is needed to avoid accidentally performing significant changes to the system.
6. What utility is used to show the system resources consumed by each user?
- Task Manager
- User Accounts
- Event Viewer
- Device Manager
Explanation: The Windows Task Manager utility includes a Users tab from which the system resources consumed by each user can be displayed.
7. When a user makes changes to the settings of a Windows system, where are these changes stored?
- win.ini
- boot.ini
- Control Panel
- Registry
Explanation: The registry contains information about applications, users, hardware, network settings, and file types. The registry also contains a unique section for every user, which contains the settings configured by that particular user.
8. For security reasons a network administrator needs to ensure that local computers cannot ping each other. Which settings can accomplish this task?
- file system settings
- MAC address settings
- firewall settings
- smartcard settings
Explanation: Smartcard and file system settings do not affect network operation. MAC address settings and filtering may be used to control device network access but cannot be used to filter different data traffic types.
9. A user creates a file with .ps1 extension in Windows. What type of file is it?
- PowerShell documentation
- PowerShell cmdlet
- PowerShell script
- PowerShell function
Explanation: The types of commands that PowerShell can execute include the following:
- cmdlets – perform an action and return an output or object to the next command that will be executed
- PowerShell scripts – files with a .ps1 extension that contain PowerShell commands that are executed
- PowerShell functions – pieces of code that can be referenced in a script
10. What is the purpose of the cd∖ command?
- changes directory to the root directory
- changes directory to the next lower directory
- changes directory to the next highest directory
- changes directory to the previous directory
Explanation: CLI commands are typed into the Command Prompt window of the Windows operating system. The cd∖ command is used to change the directory to the Windows root directory.
11. A security incident has been filed and an employee believes that someone has been on the computer since the employee left last night. The employee states that the computer was turned off before the employee left for the evening. The computer is running slowly and applications are acting strangely. Which Microsoft Windows tool would be used by the security analyst to determine if and when someone logged on to the computer after working hours?
- Performance Monitor
- Task Manager
- PowerShell
- Event Viewer
Explanation: Event Viewer is used to investigate the history of application, security, and system events. Events show the date and time that the event occurred along with the source of the event. If a cybersecurity analyst has the address of the Windows computer targeted or the date and time that a security breach occurred, the analyst could use Event Viewer to document and prove what occurred on the computer.
12. What would be displayed if the netstat -abno command was entered on a Windows PC?
- all active TCP and UDP connections, their current state, and their associated process ID (PID)
- a local routing table
- only active TCP connections in an ESTABLISHED state
- only active UDP connections in an LISTENING state
Explanation: With the optional switch -abno, the netstat command will display all network connections together with associated running processes. It helps a user identify possible malware connections.
13. Which net command is used on a Windows PC to establish a connection to a shared directory on a remote server?
- net session
- net share
- net use
- net start
Explanation: The net command is a very important command in Windows. Some common net commands include the following:
- net accounts – sets password and logon requirements for users
- net session – lists or disconnects sessions between a computer and other computers on the network
- net share – creates, removes, or manages shared resources
- net start – starts a network service or lists running network services
- net stop – stops a network service
- net use – connects, disconnects, and displays information about shared network resources
- net view – shows a list of computers and network devices on the network
14. Which Windows tool can be used by a cybersecurity administrator to secure stand-alone computers that are not part of an active directory domain?
- Local Security Policy
- Windows Firewall
- Windows Defender
- PowerShell
Explanation: Windows systems that are not part of an Active Directory Domain can use the Windows Local Security Policy to enforce security settings on each stand-alone system.
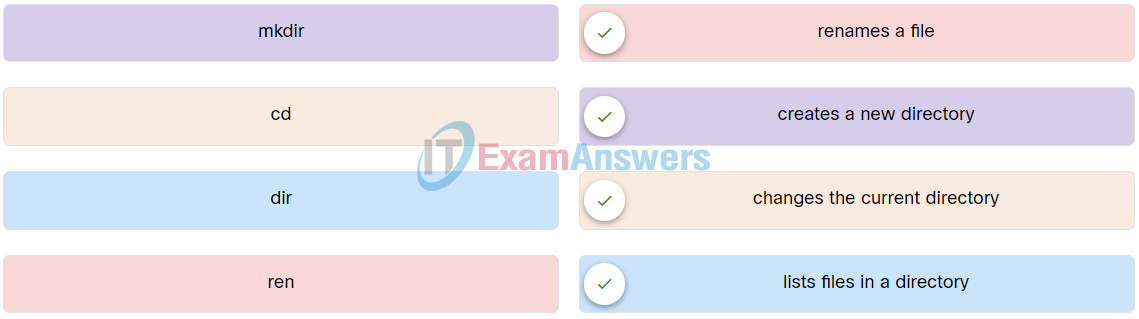
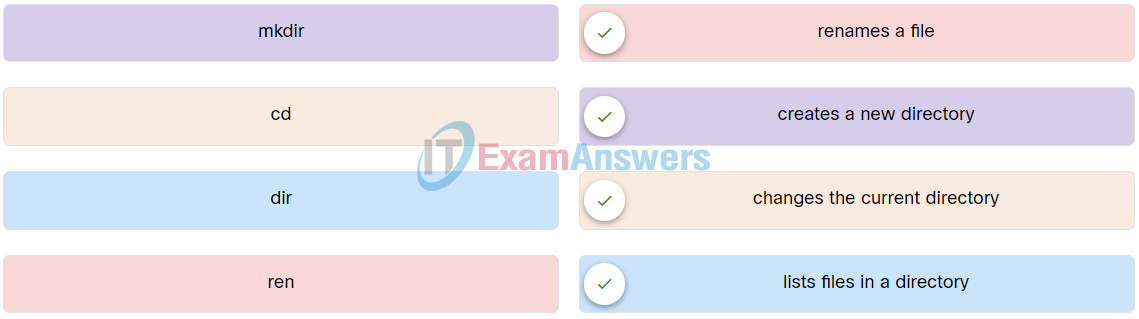
15. Match the Windows command to the description.