Modules 1 – 4: Securing Networks Group Exam Answers Network Security ( Version 1) – Network Security 1.0 Modules 1-4: Securing Networks Group Exam Answers 1. An administrator defined a local user account with a secret password on router R1 for use with SSH. Which three additional steps …
1. Each day, a security analyst spends time examining logs and events from different systems and applications to quickly detect security threats. What function of the Security Information Event Management (SIEM) technology does this action represent? aggregation correlation retention forensic analysis 2. Which network security tool can detect …
1. Which two statements are true about ASA standard ACLs? (Choose two.) They identify only the destination IP address. They are the most common type of ACL. They are applied to interfaces to control traffic. They specify both the source and destination MAC address. They are typically only …
1. What is a characteristic of ASA security levels? An ACL needs to be configured to explicitly permit traffic from an interface with a lower security level to an interface with a higher security level. Each operational interface must have a name and be assigned a security level …
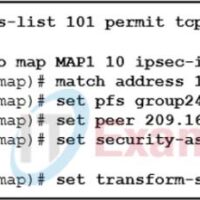
1. What is defined by an ISAKMP policy? the security associations that IPsec peers are willing to use the IP addresses of IPsec peers access lists that identify interesting traffic the preshared keys that will be exchanged between IPsec peers 2. Which are the five security associations to …
1. A network administrator is planning a VPN tunnel. Why would the engineer select main mode for IKE Phase 1? It requires less configuration. It is the industry standard. It is quicker. It is more secure. 2. What are the two types of VPN connections? (Choose two.) site-to-site …
1. What are the two important components of a public key infrastructure (PKI) used in network security? (Choose two.) digital certificates pre-shared key generation intrusion prevention system certificate authority symmetric encryption algorithms 2. What is the purpose of code signing? integrity of source .EXE files data encryption source …
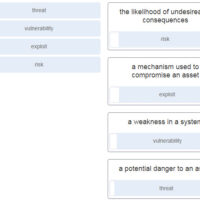
1. Which security function is provided by encryption algorithms? confidentiality key management authorization integrity 2. Which type of cryptographic key would be used when connecting to a secure website? symmetric keys digital signatures DES key hash keys 3. What do most cryptographic system attacks seek to target? user …
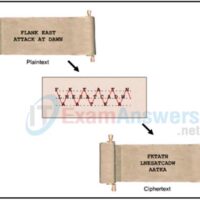
1. Refer to the exhibit. Which type of cipher method is depicted? stream cipher substitution cipher transposition cipher Caesar cipher 2. What are two objectives of ensuring data integrity? (Choose two.) Access to the data is authenticated. Data is unaltered during transit. Data is available all the time. …
1. What is the only type of traffic that is forwarded by a PVLAN protected port to other protected ports? broadcast control user management 2. A network administrator is configuring DAI on a switch with the command ip arp inspection validate src-mac. What is the purpose of this …