A router has learned three possible routes that could be used to reach a destination network. One route is from EIGRP and has a composite metric of 20514560. Another route is from OSPF with a metric of 782. The last is from RIPv2 and has a metric of …
Which identification number is valid for an extended ACL? A. 1 B. 64 C. 99 D. 100* E. 299 F. 1099 Which statement about named ACLs is true? A. They support standard and extended ACLs.* B. They are used to filter usernames and passwords for Telnet and SSH. …
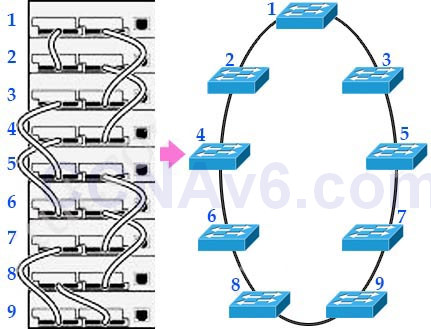
Which option is a benefit of switch stacking? A. It provides redundancy with no impact on resource usage. B. It simplifies adding and removing hosts. C. It supports better performance of high-needs applications. D. It provides higher port density with better resource usage.* Which two options describe benefits …
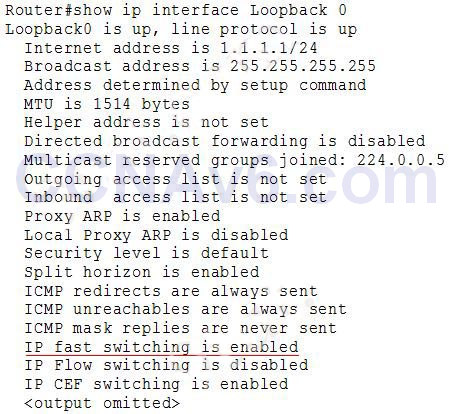
Which step in the router boot process searches for an IOS image to load into the router? A. bootstrap* B. POST C. mini-IOS D. ROMMON mode If a router has four interfaces and each interface is connected to four switches, how many broadcast domains are present on the …
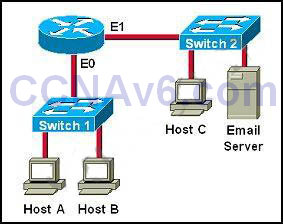
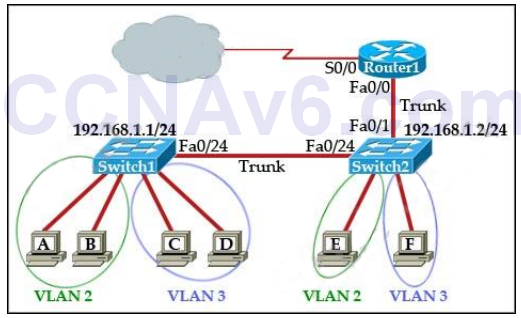
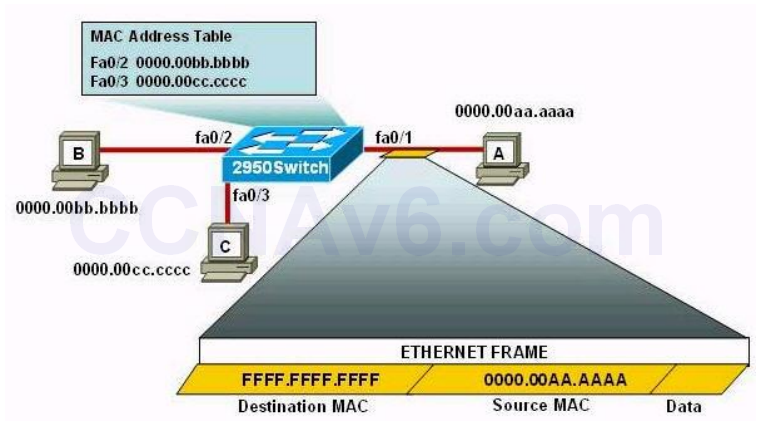
Which type of device can be replaced by the use of subinterfaces for VLAN routing? A. Layer 2 bridge B. Layer 2 switch C. Layer 3 switch* D. router Which technology can enable multiple VLANs to communicate with one another? A. inter-VLAN routing using a Layer 3 switch* …
Refer to the exhibit. While troubleshooting a switch, you executed the “show interface port-channel 1 etherchannel” command and it returned this output. Which information is provided by the Load value? A. the percentage of use of the link B. the preference of the link C. the session count …
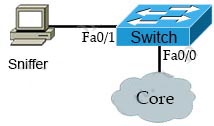
Which feature can you use to monitor traffic on a switch by replicating it to another port or ports on the same switch? A. copy run start B. traceroute C. the ICMP Echo IP SLA D. SPAN*
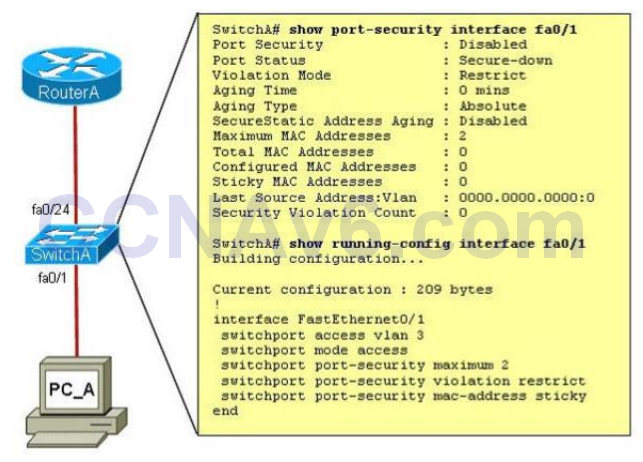
Which port security mode can assist with troubleshooting by keeping count of violations? A. access B. protect C. restrict* D. shutdown Which port security violation mode allows traffic from valid mac address to pass but block traffic from invalid MAC address? A. protect* B. shutdown C. shutdown vlan …
A network administrator needs to configure port security on a switch. Which two statements are true? (Choose two) A. The network administrator can apply port security to dynamic access ports B. The network administrator can configure static secure or sticky secure mac addresses in the voice vlan. C. …
Which protocol supports sharing the VLAN configuration between two or more switches? A. multicast B. STP C. VTP* D. split-horizon How to enable VLANs automatically across multiple switches? A. Configure VLAN B. Confiture NTP C. Configure each VLAN D. Configure VTP* Which VTP mode can not make a …