4.4.2 Packet Tracer – VTP Configuration Answers
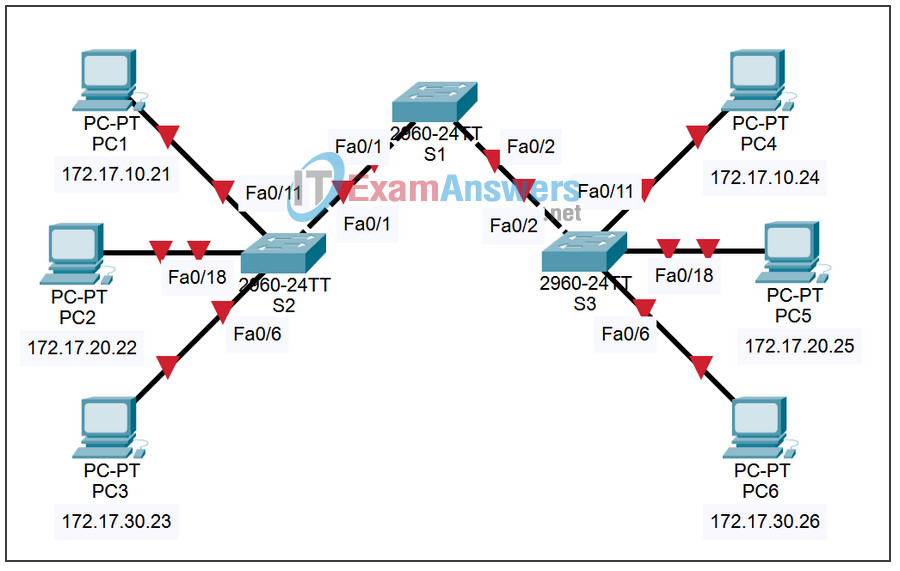
Topology
Addressing Table
| Device | Interface | IP Address | Subnet Mask |
|---|---|---|---|
| S1 | VLAN 99 | 172.31.99.11 | 255.255.255.0 |
| S2 | VLAN 99 | 172.31.99.12 | 255.255.255.0 |
| S3 | VLAN 99 | 172.31.99.13 | 255.255.255.0 |
| PC1 | NIC | 172.31.10.1 | 255.255.255.0 |
| PC2 | NIC | 172.31.20.1 | 255.255.255.0 |
| PC3 | NIC | 172.31.30.1 | 255.255.255.0 |
| PC4 | NIC | 172.31.10.2 | 255.255.255.0 |
| PC5 | NIC | 172.31.20.2 | 255.255.255.0 |
| PC6 | NIC | 172.31.30.2 | 255.255.255.0 |
Port Assignments (S2 and S3)
| Ports | Assignment | Network |
|---|---|---|
| Fa0/1 – 0/5 | 802.1q Trunks | |
| Fa0/6 – 0/10 | VLAN 30 – Administration | 172.31.30.0 /24 |
| Fa0/11 – 0/17 | VLAN 10 – Engineering | 172.31.10.0 /24 |
| Fa0/18 – 0/24 | VLAN 20 – Sales | 172.31.20.0 /24 |
| None | VLAN 99 – Network Mgmt | 172.31.99.0 /24 |
Learning Objectives
Upon completion of this lab, you will be able to:
- Cable a network according to the topology diagram.
- Erase the startup configuration and reload a switch to the default state.
- Perform basic configuration tasks on a switch.
- Configure VLAN Trunking Protocol (VTP) on all switches.
- Enable trunking on inter-switch connections.
- Verify trunk configuration.
- Modify VTP modes and observe the impact.
- Create VLANs on the VTP server, and distribute this VLAN information to switches in the network.
- Explain the differences in operation between VTP transparent mode, server mode, and client mode.
- Assign switch ports to the VLANs.
- Save the VLAN configuration.
Task 1: Prepare the Network
Step 1: Cable a network that is similar to the one in the topology diagram.
You can use any current switch in your lab as long as it has the required interfaces shown in the topology diagram. The output shown in this lab is based on 2960 switches. Other switch types may produce different output. If you are using older switches, then some commands may be different or unavailable.
Set up console connections to all three switches.
Step 2: Clear any existing configurations on the switches.
Erase existing configurations, VLANs, and reload the switch. Use the show vlan command to confirm that only default VLANs exist and that all ports are assigned to VLAN 1.
S1#show vlan VLAN Name Status Ports ---- -------------------------------- --------- ----------------------------- 1 default active Fa0/1, Fa0/2, Fa0/3, Fa0/4 Fa0/5, Fa0/6, Fa0/7, Fa0/8 Fa0/9, Fa0/10, Fa0/11, Fa0/12 Fa0/13, Fa0/14, Fa0/15,Fa0/16 Fa0/17, Fa0/18, Fa0/19,Fa0/20 Fa0/21, Fa0/22, Fa0/23,Fa0/24 Gig1/1, Gig1/2 1002 fddi-default active 1003 token-ring-default active 1004 fddinet-default active 1005 trnet-default active
Step 3: Disable all ports by using the shutdown command.
S1(config)#interface range fa0/1-24 S1(config-if-range)#shutdown S1(config-if-range)#interface range gi0/1-2 S1(config-if-range)#shutdown S2(config)#interface range fa0/1-24 S2(config-if-range)#shutdown S2(config-if-range)#interface range gi0/1-2 S2(config-if-range)#shutdown S3(config)#interface range fa0/1-24 S3(config-if-range)#shutdown S3(config-if-range)#interface range gi0/1-2 S3(config-if-range)#shutdown
Step 4: Re-enable the user ports on S2 and S3 and put those ports in access mode. Refer to the topology diagram to determine which ports are connected to end-user devices.
S2(config)#interface fa0/6 S2(config-if)#switchport mode access S2(config-if)#no shutdown S2(config-if)#interface fa0/11 S2(config-if)#switchport mode access S2(config-if)#no shutdown S2(config-if)#interface fa0/18 S2(config-if)#switchport mode access S2(config-if)#no shutdown S3(config)#interface fa0/6 S3(config-if)#switchport mode access S3(config-if)#no shutdown S3(config-if)#interface fa0/11 S3(config-if)#switchport mode access S3(config-if)#no shutdown S3(config-if)#interface fa0/18 S3(config-if)#switchport mode access S3(config-if)#no shutdown
Task 2: Perform Basic Switch Configurations.
Configure the S1, S2, and S3 switches according to the following guidelines and save all your configurations:
- Configure the switch hostname as indicated on the topology.
- Disable DNS lookup.
- Configure an EXEC mode password of class.
- Configure a password of cisco for console connections.
- Configure a password of cisco for vty connections.
Output for S1 shown
Switch>enable Switch#configure terminal Enter configuration commands, one per line. End with CNTL/Z. Switch(config)#hostname S1 S1(config)#enable secret class S1(config)#no ip domain-lookup S1(config)#line console 0 S1(config-line)#password cisco S1(config-line)#login S1(config-line)#line vty 0 15 S1(config-line)#password cisco S1(config-line)#login S1(config-line)#end %SYS-5-CONFIG_I: Configured from console by console S1#copy running-config startup-config Destination filename [startup-config]? Building configuration... [OK]
Task 3: Configure the Ethernet Interfaces on the Host PCs
Configure the Ethernet interfaces of PC1 through PC6 with the IP addresses indicated in the addressing table at the beginning of the lab.
Task 4: Configure VTP on the Switches
VTP allows the network administrator to control the instances of VLANs on the network by creating VTP domains. Within each VTP domain, one or more switches are configured as VTP servers. VLANs are then created on the VTP server and pushed to the other switches in the domain. Common VTP configuration tasks are operating mode, domain, and password. In this lab, you will be configuring S1 as a VTP server, with S2 and S3 configured as VTP clients.
Step 1: Check the current VTP settings on the three switches.
S1#show vtp status
VTP Version : 2
Configuration Revision : 0
Maximum VLANs supported locally : 255
Number of existing VLANs : 5
VTP Operating Mode : Server
VTP Domain Name :
VTP Pruning Mode : Disabled
VTP V2 Mode : Disabled
VTP Traps Generation : Disabled
MD5 digest : 0x57 0xCD 0x40 0x65 0x63 0x59 0x47 0xBD
Configuration last modified by 0.0.0.0 at 0-0-00 00:00:00
Local updater ID is 0.0.0.0 (no valid interface found)
S2#show vtp status
VTP Version : 2
Configuration Revision : 0
Maximum VLANs supported locally : 255
Number of existing VLANs : 5
VTP Operating Mode : Server
VTP Domain Name :
VTP Pruning Mode : Disabled
VTP V2 Mode : Disabled
VTP Traps Generation : Disabled
MD5 digest : 0x57 0xCD 0x40 0x65 0x63 0x59 0x47 0xBD
Configuration last modified by 0.0.0.0 at 0-0-00 00:00:00
Local updater ID is 0.0.0.0 (no valid interface found)
S3#show vtp status
VTP Version : 2
Configuration Revision : 0
Maximum VLANs supported locally : 255
Number of existing VLANs : 5
VTP Operating Mode : Server
VTP Domain Name :
VTP Pruning Mode : Disabled
VTP V2 Mode : Disabled
VTP Traps Generation : Disabled
MD5 digest : 0x57 0xCD 0x40 0x65 0x63 0x59 0x47 0xBD
Configuration last modified by 0.0.0.0 at 0-0-00 00:00:00
What is the current (default) VTP operating mode on the switches?
Server
What is the configuration revision on S1 and S2?
0
Step 2: Configure the operating mode, the domain name, and VTP password on all three switches.
Set the VTP domain name to access and the VTP password to lab4 on all three switches. Configure S1 in server mode, S2 in client mode, and S3 in transparent mode.
S1(config)#vtp mode server Device mode already VTP SERVER. S1(config)#vtp domain access Changing VTP domain name from NULL to access S1(config)#vtp password lab4 Setting device VLAN database password to lab4 S1(config)#end S2(config)#vtp mode client Setting device to VTP CLIENT mode S2(config)#vtp domain access Changing VTP domain name from NULL to access S2(config)#vtp password lab4 Setting device VLAN database password to lab4 S2(config)#end S3(config)#vtp mode transparent Setting device to VTP TRANSPARENT mode. S3(config)#vtp domain access Changing VTP domain name from NULL to access S3(config)#vtp password lab4 Setting device VLAN database password to lab4 S3(config)#end
Note: The VTP domain name can be learned by a client switch from a server switch, but only if the client switch domain is in the null state. It does not learn a new name if one has been previously set. For that reason, it is good practice to manually configure the domain name on all switches to ensure that the domain name is configured correctly. Switches in different VTP domains do not exchange VLAN information. Recall that VTP domain names and passwords are case-sensitive.
Step 3: Configure trunking and the native VLAN for the trunking ports on all three switches.
Configure ports Fa0/1 through Fa0/5 in trunking mode. Configure VLAN 99 as the native VLAN for these trunks. You can use the interface range command to simplify this task. Do not forget to enable the trunk interfaces.
S1(config)#interface range fa0/1-5 S1(config-if-range)#switchport mode trunk S1(config-if-range)#switchport trunk native vlan 99 S1(config-if-range)#no shutdown S1(config-if-range)#end S2(config)# interface range fa0/1-5 S2(config-if-range)#switchport mode trunk S2(config-if-range)#switchport trunk native vlan 99 S2(config-if-range)#no shutdown S2(config-if-range)#end S3(config)# interface range fa0/1-5 S3(config-if-range)#switchport mode trunk S3(config-if-range)#switchport trunk native vlan 99 S3(config-if-range)#no shutdown S3(config-if-range)#end
Step 4: Configure port security on the S2 and S3 access ports.
Configure ports Fa0/6, Fa0/11, and Fa0/18 on S2 and S3 so that they allow a maximum of two hosts to connect to these ports and learn the MAC addresses of the hosts dynamically.
S2(config)#interface fa0/6 S2(config-if)#switchport port-security S2(config-if)#switchport port-security maximum 2 S2(config-if)#switchport port-security mac-address sticky S2(config-if)#interface fa0/11 S2(config-if)#switchport port-security S2(config-if)#switchport port-security maximum 2 S2(config-if)#switchport port-security mac-address sticky S2(config-if)#interface fa0/18 S2(config-if)#switchport port-security S2(config-if)#switchport port-security maximum 2 S2(config-if)#switchport port-security mac-address sticky S2(config-if)#end S3(config)#interface fa0/6 S3(config-if)#switchport port-security S3(config-if)#switchport port-security maximum 2 S3(config-if)#switchport port-security mac-address sticky S3(config-if)#interface fa0/11 S3(config-if)#switchport port-security S3(config-if)#switchport port-security maximum 2 S3(config-if)#switchport port-security mac-address sticky S3(config-if)#interface fa0/18 S3(config-if)#switchport port-security S3(config-if)#switchport port-security maximum 2 S3(config-if)#switchport port-security mac-address sticky S3(config-if)#end
Step 5: Configure VLANs on the VTP server.
There are four VLANS required in this lab:
- VLAN 99 (network mgmt)
- VLAN 10(engineering)
- VLAN 20 (sales)
- VLAN 30 (administration)
Configure these VLANs only on the VTP server.
S1(config)#vlan 99 S1(config-vlan)#name management S1(config-vlan)#exit S1(config)#vlan 10 S1(config-vlan)#name engineering S1(config-vlan)#exit S1(config)#vlan 20 S1(config-vlan)#name sales S1(config-vlan)#exit S1(config)#vlan 30 S1(config-vlan)#name administration S1(config-vlan)#exit
When you are done, verify that all four VLANs have been created on S1.
Step 6: Check if the VLANs created on S1 have been distributed to S2 and S3.
Use the show vlan brief command on S2 and S3 to determine if the VTP server has pushed its VLAN configuration to all these switches.
S2#show vlan brief VLAN Name Status Ports ---- -------------------------------- --------- ----------------------------- 1 default active Fa0/1, Fa0/2, Fa0/4, Fa0/5 Fa0/6, Fa0/7, Fa0/8, Fa0/9 Fa0/10, Fa0/11, Fa0/12,Fa0/13 Fa0/14, Fa0/15, Fa0/16,Fa0/17 Fa0/18, Fa0/19, Fa0/20,Fa0/21 Fa0/22, Fa0/23, Fa0/24, Gi0/1 Gi0/2 10 engineering active 20 sales active 30 administration active 99 management active S3#show vlan brief VLAN Name Status Ports ---- -------------------------------- --------- ----------------------------- 1 default active Fa0/1, Fa0/2, Fa0/4, Fa0/5 Fa0/6, Fa0/7, Fa0/8, Fa0/9 Fa0/10, Fa0/11, Fa0/12,Fa0/13 Fa0/14, Fa0/15, Fa0/16,Fa0/17 Fa0/18, Fa0/19, Fa0/20,Fa0/21 Fa0/22, Fa0/23, Fa0/24, Gi0/1 Gi0/2 1002 fddi-default act/unsup 1003 token-ring-default act/unsup 1004 fddinet-default act/unsup 1005 trnet-default act/unsup
Are the same VLANs configured on all switches?
no
Explain why S2 and S3 have different VLAN configurations at this point.
S2 is in VTP client mode and accepts VLAN configurations advertised by a VTP server. S3 is in VTP transparent mode, so it forwards VTP advertisements but does not implement the advertised VLANs locally.
Step 7: Configure the management interface address on all three switches according to the addressing table at the beginning of the lab.
Assign these addresses to the network management VLAN (VLAN 99).
S1(config)#interface vlan 99 S1(config-if)#ip address 172.17.99.11 255.255.255.0 S1(config-if)#no shutdown S2(config)#interface vlan 99 S2(config-if)#ip address 172.17.99.12 255.255.255.0 S2(config-if)#no shutdown S3(config)#interface vlan 99 S3(config-if)#ip address 172.17.99.13 255.255.255.0 S3(config-if)#no shutdown
Verify that the switches are correctly configured by pinging between them. From S1, ping the management interface on S2 and S3. From S2, ping the management interface on S3.
Were the pings successful?
yes
If not, troubleshoot the switch configurations and resolve.
Step 8: Assign switch ports to VLANs.
Refer to the port assignment table at the beginning of the lab to assign ports to VLANs. Use the interface range command to simplify this task. Note that port assignments are not configured through VTP. Port assignments must be configured on each switch manually or dynamically using a VMPS server. The commands are shown for S3 only, but both S2 and S1 switches should be similarly configured. Save the configuration when you are done.
S3(config)#interface range fa0/6-10 S3(config-if-range)#switchport access vlan 30 S3(config-if-range)#interface range fa0/11-17 S3(config-if-range)#switchport access vlan 10 S3(config-if-range)#interface range fa0/18-24 S3(config-if-range)#switchport access vlan 20 S3(config-if-range)#end S3#copy running-config startup-config Destination filename [startup-config]? [enter] Building configuration... [OK] S3#
Step 9: Verify that the trunks are operating correctly.
From PC1, attempt to ping PC4, PC5, and PC6.
Were any of the pings successful?
yes, the pings to PC4 were successful
Why did some of the pings fail?
The hosts are in different VLANs.
Which hosts could be reached from PC3?
PC6 only
Task 5: Configure VTP Pruning on the Switches
VTP pruning allows a VTP server to suppress IP broadcast traffic for specific VLANs to switches that do not have any ports in that VLAN. By default, all unknown unicasts and broadcasts in a VLAN are flooded over the entire VLAN. All switches in the network receive all broadcasts, even in situations in which few users are connected in that VLAN. VTP pruning eliminates or prunes this unnecessary traffic. Pruning saves LAN bandwidth because broadcasts do not have to be sent to switches that do not need them.
Configure pruning on the server switch, which is then pushed to client switches. However, because S3 is in transparent mode, VTP pruning must be configured locally on that switch as well.
Confirm the VTP pruning configuration on each switch using the show vtp status command. VTP pruning mode should show “Enabled” on each switch.
S1#show vtp status VTP Version : 2 Configuration Revision : 17 Maximum VLANs supported locally : 255 Number of existing VLANs : 9 VTP Operating Mode : Server VTP Domain Name : access VTP Pruning Mode : Enabled <output omitted>
Task 6: Clean Up
Erase the configurations and reload the switches. Disconnect and store the cabling. For PC hosts that are normally connected to other networks (such as the school LAN or to the Internet), reconnect the appropriate cabling and restore the TCP/IP settings.
Final Configurations
S1 Configuration
hostname S1
enable secret class
no ip domain-lookup
!
interface FastEthernet0/1
switchport trunk native vlan 99
switchport mode trunk
!
interface FastEthernet0/2
switchport trunk native vlan 99
switchport mode trunk
!
interface FastEthernet0/3
switchport trunk native vlan 99
switchport mode trunk
!
interface FastEthernet0/4
switchport trunk native vlan 99
switchport mode trunk
!
interface FastEthernet0/5
switchport trunk native vlan 99
switchport mode trunk
!
interface FastEthernet0/6
shutdown
!
<output omitted – FastEthernet 0/7 through 0/24 are the same as FastEthernet
0/6>
!
interface GigabitEthernet0/1
shutdown
!
interface GigabitEthernet0/2
shutdown
!
interface Vlan1
no ip address
shutdown
!
interface Vlan99
ip address 172.17.99.11 255.255.255.0
no shutdown
!
line con 0
password cisco
login
line vty 0
no login
line vty 1 4
password cisco
login
line vty 5 15
password cisco
login
!
end
S2 Configuration
hostname S2
!
enable secret class
!
no ip domain-lookup
!
interface FastEthernet0/1
switchport trunk native vlan 99
switchport mode trunk
!
interface FastEthernet0/2
switchport trunk native vlan 99
switchport mode trunk
!
interface FastEthernet0/3
switchport trunk native vlan 99
switchport mode trunk
!
interface FastEthernet0/4
switchport trunk native vlan 99
switchport mode trunk
!
interface FastEthernet0/5
switchport trunk native vlan 99
switchport mode trunk
!
interface FastEthernet0/6
switchport access vlan 30
s
switchport port-security maximum 2
witchport mode access
switchport port-security
switchport port-security mac-address sticky
!
interface FastEthernet0/7
switchport access vlan 30
shutdown
!
interface FastEthernet0/8
switchport access vlan 30
shutdown
!
interface FastEthernet0/9
switchport access vlan 30
shutdown
!
interface FastEthernet0/10
switchport access vlan 30
shutdown
!
interface FastEthernet0/11
switchport access vlan 10
switchport mode access
switchport port-security
switchport port-security maximum 2
switchport port-security mac-address sticky
!
interface FastEthernet0/12
switchport access vlan 10
shutdown
!
interface FastEthernet0/13
switchport access vlan 10
shutdown
!
interface FastEthernet0/14
switchport access vlan 10
shutdown
!
interface FastEthernet0/15
switchport access vlan 10
shutdown
!
interface FastEthernet0/16
switchport access vlan 10
shutdown
!
interface FastEthernet0/17
switchport access vlan 10
shutdown
!
interface FastEthernet0/18
switchport access vlan 20
switchport mode access
switchport port-security
switchport port-security maximum 2
switchport port-security mac-address sticky
!
interface FastEthernet0/19
switchport access vlan 20
shutdown
!
interface FastEthernet0/20
switchport access vlan 20
shutdown
!
interface FastEthernet0/21
switchport access vlan 20
shutdown
!
interface FastEthernet0/22
switchport access vlan 20
shutdown
!
interface FastEthernet0/23
switchport access vlan 20
shutdown
!
interface FastEthernet0/24
switchport access vlan 20
shutdown
!
interface GigabitEthernet0/1
shutdown
!
interface GigabitEthernet0/2
switchport mode trunk
!
interface Vlan1
no ip address
no ip route-cache
!
interface Vlan99
ip address 172.17.99.12 255.255.255.0
no shutdown
!
ip http server
!
line con 0
exec-timeout 0 0
password cisco
logging synchronous
login
line vty 0 4
password cisco
login
line vty 5 15
password cisco
S3 Configuration
hostname S3
!
enable secret class
!
no ip domain-lookup
!
vtp domain access
vtp mode transparent
!
vlan 10
name faculty/staff
!
vlan 20
name students
!
vlan 30
name guest
!
vlan 99
name mangement
!
interface FastEthernet0/1
switchport trunk native vlan 99
switchport mode trunk
!
interface FastEthernet0/2
switchport trunk native vlan 99
switchport mode trunk
interface FastEthernet0/3
switchport trunk native vlan 99
switchport mode trunk
interface FastEthernet0/4
switchport trunk native vlan 99
switchport mode trunk
interface FastEthernet0/5
switchport trunk native vlan 99
switchport mode trunk
!
interface FastEthernet0/6
switchport access vlan 30
switchport mode access
switchport port-security
switchport port-security maximum 2
switchport port-security mac-address sticky
!
interface FastEthernet0/7
switchport access vlan 30
interface FastEthernet0/8
switchport access vlan 30
interface FastEthernet0/9
switchport access vlan 30
interface FastEthernet0/10
switchport access vlan 30
!
interface FastEthernet0/11
switchport access vlan 10
switchport mode access
switchport port-security
switchport port-security maximum 2
switchport port-security mac-address sticky
!
interface FastEthernet0/12
switchport access vlan 10
interface FastEthernet0/13
switchport access vlan 10
interface FastEthernet0/14
switchport access vlan 10
interface FastEthernet0/15
switchport access vlan 10
interface FastEthernet0/16
switchport access vlan 10
interface FastEthernet0/17
switchport access vlan 10
!
interface FastEthernet0/18
switchport access vlan 20
switchport mode access
switchport port-security
switchport port-security maximum 2
switchport port-security mac-address sticky
!
interface FastEthernet0/19
switchport access vlan 20
interface FastEthernet0/20
switchport access vlan 20
interface FastEthernet0/21
switchport access vlan 20
interface FastEthernet0/22
switchport access vlan 20
interface FastEthernet0/23
switchport access vlan 20
interface FastEthernet0/24
switchport access vlan 20
!
interface GigabitEthernet0/1
!
interface GigabitEthernet0/2
!
interface Vlan1
no ip address
no ip route-cache
shutdown
!
interface Vlan99
ip address 172.17.99.13 255.255.255.0
no shutdown
!
line con 0
password cisco
login
line vty 0 4
password cisco
login
line vty 5 15
password cisco
login
end
