Time limit: 0
Quiz-summary
0 of 53 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
Information
Good Luck For You!
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 53 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- Answered
- Review
-
Question 1 of 53
1. Question
1 pointsWhich two components of a WAN would more likely be used by an ISP? (Choose two.)Correct
Incorrect
Hint
The central office (CO), also known as the point of presence (POP), houses the service provider equipment. The toll network contains communication equipment that is used to span the WAN provider network. The customer premises equipment (CPE) and data terminal equipment (DTE) are commonly located at the customer site. The demarcation point delineates where the ISP equipment and wiring ends and the customer responsibility begins. The demarcation point is located inside the customer building. -
Question 2 of 53
2. Question
1 pointsWhat are two advantages of packet switching over circuit switching? (Choose two.)Correct
Incorrect
Hint
The setting up of a dedicated circuit through the service provider network between each pair of communicating nodes, and fewer delays in the data communications processes are advantages of circuit-switched networks. -
Question 3 of 53
3. Question
1 pointsWhat are two common types of circuit-switched WAN technologies? (Choose two.)Correct
Incorrect
Hint
ISDN and PSTN are the most common circuit-switched technologies. Circuit-switched networks form a dedicated circuit or channel before communication occurs. -
Question 4 of 53
4. Question
1 pointsUnder which two categories of WAN connections does Frame Relay fit? (Choose two.)Correct
Incorrect
Hint
A packet-switched private infrastructure like Frame Relay is a lower cost alternative to expensive leased lines. -
Question 5 of 53
5. Question
1 pointsWhich WAN technology is capable of transferring voice and video traffic by utilizing a fixed payload of 48 bytes for every frame?Correct
Incorrect
Hint
ATM cells always have a fixed length of 53 bytes. The ATM cell contains a 5-byte ATM header followed by 48 bytes of ATM payload. -
Question 6 of 53
6. Question
1 pointsWhich type of long distance telecommunication technology provides point-to-point connections and cellular access?Correct
Incorrect
Hint
WiMax towers are capable of connection to other WiMax towers by means of line-of-sight microwave links or they can provide cellular access to devices. Municipal Wi-Fi satellite technology and mobile broadband do not provide long distance point-to-point technology while providing mobile device access. -
Question 7 of 53
7. Question
1 pointsA small law firm wants to connect to the Internet at relatively high speed but with low cost. In addition, the firm prefers that the connection be through a dedicated link to the service provider. Which connection type should be selected?Correct
Incorrect
Hint
Both DSL and cable connections can provide relative high speed Internet connections with reasonable cost. Whereas DSL subscribers establish individual links to the service provider, local cable service subscribers (in the neighborhood) share the same cable bandwidth. As more users join the cable service, available bandwidth may be below the expected rate. Both leased line and ISDN connections are dedicated links from the customer to the service provider, but they are more expensive than either DSL or cable services. -
Question 8 of 53
8. Question
1 pointsRefer to the exhibit. What type of Layer 2 encapsulation will be used for connection D on the basis of this configuration on a newly installed router: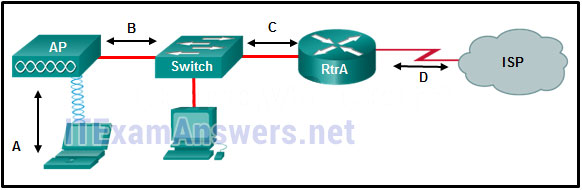 RtrA(config)# interface serial0/0/0
RtrA(config-if)# ip address 128.107.0.2 255.255.255.252
RtrA(config-if)# no shutdown Correct
RtrA(config)# interface serial0/0/0
RtrA(config-if)# ip address 128.107.0.2 255.255.255.252
RtrA(config-if)# no shutdown Correct
Incorrect
Hint
HDLC is the default encapsulation method on Cisco router serial interfaces. If no other encapsulation is configured, the interface will default to HDLC. -
Question 9 of 53
9. Question
1 pointsWhich two protocols in combination should be used to establish a link with secure authentication between a Cisco and a non-Cisco router? (Choose two.)Correct
Incorrect
Hint
On a Cisco router the version of HDLC used is proprietary. Therefore, with a link between a Cisco and a non-Cisco router, PPP should be used. Of the two authentication types that PPP supports (PAP and CHAP), CHAP is more secure. -
Question 10 of 53
10. Question
1 pointsWhich statement is true about NCP?Correct
Incorrect
-
Question 11 of 53
11. Question
1 pointsRefer to the exhibit. Which three steps are required to configure Multilink PPP on the HQ router? (Choose three.)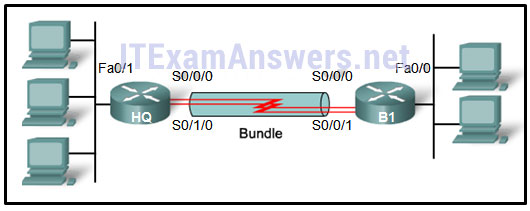 Correct
Correct
Incorrect
Hint
PPP multilink spreads traffic across bundled physical WAN links. To configure PPP multilink on a router, creating the multilink bundle begins with creation of the multilink interface. The serial interfaces are the WAN links in the exhibit and must be assigned to the multilink bundle. The serial interfaces must also be enabled for PPP encapsulation to become part of the multilink group. -
Question 12 of 53
12. Question
1 pointsA network engineer is troubleshooting the failure of CHAP authentication over a PPP WAN link between two routers. When CHAP authentication is not included as part of the interface configuration on both routers, communication across the link is successful. What could be causing CHAP to fail?Correct
Incorrect
Hint
The secret password configured on each router must be the same for successful CHAP authentication. A different hostname is expected to be configured on each router, and the username configured on each router must match the hostname of the other router for successful CHAP authentication. The DCE interface clock rate is configured because communication across the link is successful when CHAP is not configured. -
Question 13 of 53
13. Question
1 pointsWhich statement describes the difference between CHAP and PAP in PPP authentication?Correct
Incorrect
Hint
Another difference between PAP and CHAP is that CHAP sends periodic challenges whereas PAP only authenticates one time. -
Question 14 of 53
14. Question
1 pointsA technician at a remote location is troubleshooting a router and has emailed partial debug command output to a network engineer at the central office. The message that is received by the engineer only contains a number of LCP messages that relate to a serial interface. Which WAN protocol is being used on the link?Correct
Incorrect
Hint
LCP (Link Control Protocol) is a component of PPP. -
Question 15 of 53
15. Question
1 pointsWhich DSL technology provides higher downstream bandwidth to the user than upstream bandwidth?Correct
Incorrect
Hint
ADSL provides higher downstream bandwidth to the user than upload bandwidth. SDSL provides the same capacity in both directions. TDMA and CDMA are not DSL technologies. -
Question 16 of 53
16. Question
1 pointsWhich communication protocol allows the creation of a tunnel through the DSL connection between the customer router and the ISP router to send PPP frames?Correct
Incorrect
Hint
PPPoE, Point-to-Point Protocol over Ethernet, creates a tunnel through the DSL connection for the purpose of transmitting serial data up and down a wide frequency band and allows multiple subscribers connected to the network to transmit and receive concurrently. -
Question 17 of 53
17. Question
1 pointsWhich group of APIs are used by an SDN controller to communicate with various applications?Correct
Incorrect
Hint
Software defined networking (SDN) is a network architecture developed to virtualize the network. SDN moves the control plane from each network device to a central network controller. The SDN controller uses northbound APIs to communicate with the upstream applications. It also uses southbound APIs to define the behavior of the downstream virtual switches and routers. -
Question 18 of 53
18. Question
1 pointsWhich two technologies are core components of Cisco ACI architecture? (Choose two.)Correct
Incorrect
Hint
The Cisco ACI architecture contains three core components: Application Network Profile (ANP) – An ANP is a collection of end-point groups (EPG), their connections, and the policies that define those connections. Application Policy Infrastructure Controller (APIC) – APIC is a centralized software controller that manages and operates a scalable ACI clustered fabric. Cisco Nexus 9000 Series switches – Provides an application-aware switching fabric and works with an APIC to manage the virtual and physical network infrastructure. OpenFlow enabled switches are required in SDN implementation. Both Interface to the Routing System (I2RS) and Transparent Interconnection of Lots of Links (TRILL) are different approaches developed for network virtualization. -
Question 19 of 53
19. Question
1 pointsTwo corporations have just completed a merger. The network engineer has been asked to connect the two corporate networks without the expense of leased lines. Which solution would be the most cost effective method of providing a proper and secure connection between the two corporate networks?Correct
Incorrect
Hint
The site-to-site VPN is an extension of a classic WAN network that provides a static interconnection of entire networks. Frame Relay would be a better choice than leased lines, but would be more expensive than implementing site-to-site VPNs. The other options refer to remote access VPNs which are better suited for connecting users to the corporate network versus interconnecting two or more networks. -
Question 20 of 53
20. Question
1 pointsWhen GRE is configured on a router, what do the tunnel source and tunnel destination addresses on the tunnel interface refer to?Correct
Incorrect
Hint
A site-to-site VPN is established with a GRE tunnel. It does not link two LANs, but rather it extends the reach of a single LAN across a WAN. Tunnel interfaces are configured on routers at each end of the VPN, not in the intermediate routers. -
Question 21 of 53
21. Question
1 pointsOpen the PT Activity. Perform the tasks in the activity instructions and then answer the question. What problem is preventing the hosts from communicating across the VPN tunnel?Correct
Incorrect
Hint
The IP address of the tunnel interface on B-Gateway is incorrect. It should be in the 172.16.1.0/24 network. Changing this address will bring up the tunnel interfaces and allow the hosts to ping each other. -
Question 22 of 53
22. Question
1 pointsWhich routing protocol is used to exchange routing information between autonomous systems on the Internet?Correct
Incorrect
Hint
Exterior routing protocols exchange routing information between autonomous systems. BGP is the only exterior routing protocol in use today on the Internet. -
Question 23 of 53
23. Question
1 pointsThe graphic shows four autonomous systems (AS). AS 65002 is connected to AS 65003 and to AS 65004. AS 65003 is connected only to AS 65002. AS 65004 is connected to AS 65002 and AS 65005. AS 65005 is connected to AS 65003 and to the Internet.Refer to the exhibit. For which autonomous system would running BGP not be appropriate?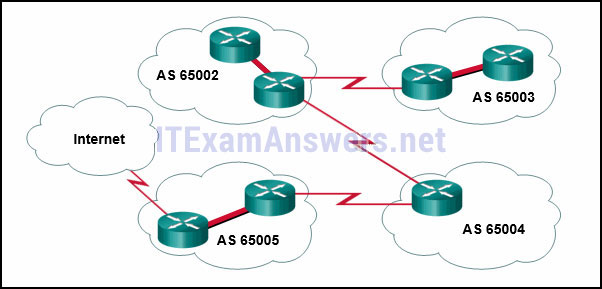 Correct
Correct
Incorrect
Hint
It is appropriate to use BGP when an autonomous system is multihomed, or has more than one connection to another autonomous system or to the Internet. BGP is not appropriate for single-homed autonomous systems. Autonomous system 65003 is a single-homed AS because it is only connected to one other autonomous system, 65002. -
Question 24 of 53
24. Question
1 pointsWhat two functions describe uses of an access control list? (Choose two.)Correct
Incorrect
-
Question 25 of 53
25. Question
1 pointsA network administrator is explaining to a junior colleague the use of the lt and gt keywords when filtering packets using an extended ACL. Where would the lt or gt keywords be used?Correct
Incorrect
Hint
The lt and gt keywords are used for defining a range of port numbers that are less than a particular port number or greater than a particular port number. -
Question 26 of 53
26. Question
1 pointsRefer to the exhibit. A router has an existing ACL that permits all traffic from the 172.16.0.0 network. The administrator attempts to add a new ACE to the ACL that denies packets from host 172.16.0.1 and receives the error message that is shown in the exhibit. What action can the administrator take to block packets from host 172.16.0.1 while still permitting all other traffic from the 172.16.0.0 network?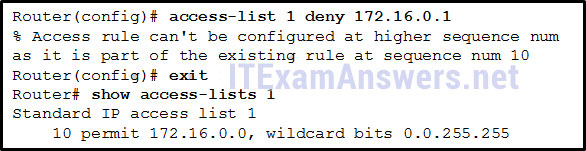 Correct
Correct
Incorrect
Hint
Because the new deny ACE is a host address that falls within the existing 172.16.0.0 network that is permitted, the router rejects the command and displays an error message. For the new deny ACE to take effect, it must be manually configured by the administrator with a sequence number that is less than 10. -
Question 27 of 53
27. Question
1 pointsWhich three implicit access control entries are automatically added to the end of an IPv6 ACL? (Choose three.)Correct
Incorrect
Hint
All IPv6 ACLs automatically include two implicit permit statements; permit icmp any any nd-ns and permit icmp any any nd-na. These statements allow the router interface to perform neighbor discovery operations. There is also an implicit deny ipv6 any any automatically included at the very end of any IPv6 ACL that blocks all IPv6 packets not otherwise permitted. -
Question 28 of 53
28. Question
1 pointsWhich statement describes a difference between the operation of inbound and outbound ACLs?Correct
Incorrect
Hint
With an inbound ACL, incoming packets are processed before they are routed. With an outbound ACL, packets are first routed to the outbound interface, then they are processed. Thus processing inbound is more efficient from the router perspective. The structure, filtering methods, and limitations (on an interface, only one inbound and one outbound ACL can be configured) are the same for both types of ACLs. -
Question 29 of 53
29. Question
1 pointsWhat is the result of a DHCP starvation attack?Correct
Incorrect
Hint
DCHP starvation attacks are launched by an attacker with the intent to create a DoS for DHCP clients. To accomplish this goal, the attacker uses a tool that sends many DHCPDISCOVER messages to lease the entire pool of available IP addresses, thus denying them to legitimate hosts. -
Question 30 of 53
30. Question
1 pointsWhat is a recommended best practice when dealing with the native VLAN?Correct
Incorrect
Hint
Port security cannot be enabled on a trunk and trunks are the only types of ports that have a native VLAN. Even though turning DTP off on a trunk is a best practice, it does not have anything to do with native VLAN risks. To prevent security breaches that take advantage of the native VLAN, place the native VLAN in an unused VLAN other than VLAN 1. The management VLAN should also be an unused VLAN that is different from the native VLAN and something other than VLAN 1. -
Question 31 of 53
31. Question
1 pointsWhich management protocol can be used securely with Cisco devices to retrieve or write to variables in a MIB?Correct
Incorrect
-
Question 32 of 53
32. Question
1 pointsWhat are two benefits of using SNMP traps? (Choose two.)Correct
Incorrect
Hint
SNMP can be used to collect and store information about a device. SNMP managers can periodically poll SNMP agents for information stored in the MIB of the agent. To reduce the amount of polling and thus the load on the network and the SNMP agent, traps can be set on the agent that send information to the manager without the need for polling. -
Question 33 of 53
33. Question
1 pointsWhat is an advantage of SNMPv3 over SNMPv1 or SNMPv2?Correct
Incorrect
Hint
SNMPv3 provides for the authentication and encryption of network management and monitoring packets sent between a device and the SNMP manager(s). -
Question 34 of 53
34. Question
1 pointsWhat network monitoring tool copies traffic moving through one switch port, and sends the copied traffic to another switch port for analysis?Correct
Incorrect
Hint
The Switched Port Analyzer (SPAN) feature of Cisco switches allows traffic that is coming into or out of a switch port to be copied to a different port so that it can be collected and analyzed with network monitoring software. -
Question 35 of 53
35. Question
1 pointsRSPAN depends on which type of VLAN?Correct
Incorrect
Hint
Remote SPAN (RSPAN) allows source and destination ports to be in different switches. RSPAN uses two sessions. One session is used as the source and one session is used to copy or receive the traffic from a VLAN. The traffic for each RSPAN session is carried over trunk links in a user-specified RSPAN VLAN that is dedicated (for that RSPAN session) in all participating switches. -
Question 36 of 53
36. Question
1 pointsWhy is QoS an important issue in a converged network that combines voice, video, and data communications?Correct
Incorrect
Hint
Without any QoS mechanisms in place, time-sensitive packets, such as voice and video, will be dropped with the same frequency as email and web browsing traffic. -
Question 37 of 53
37. Question
1 pointsWhat are two characteristics of voice traffic? (Choose two.)Correct
Incorrect
Hint
Voice traffic does not consume much in the way of network resources, such as bandwidth. However, it is very sensitive to delay and dropped packets. For good voice quality, the amount of latency should be less than 150 milliseconds and packet loss less than 1%. -
Question 38 of 53
38. Question
1 pointsTrue or False. DiffServ is a QoS strategy that enforces end-to-end guarantees.Correct
Incorrect
Hint
Unlike IntServ which provides QoS guarantees through the use of a resource reservation mechanism, DiffServ cannot guarantee end-to-end QoS. With DiffServ, a QoS policy is applied and enforced on a hop-by-hop basis. -
Question 39 of 53
39. Question
1 pointsWhat QoS step must occur before packets can be marked?Correct
Incorrect
Hint
Traffic must be classified before it can be marked. After traffic has been marked, then actions can be taken to provide a specific level of service. -
Question 40 of 53
40. Question
1 pointsRefer to the exhibit. A network administrator has deployed QoS and has configured the network to mark traffic on the VoIP phones as well as the Layer 2 and Layer 3 switches. Where should initial marking occur to establish the trust boundary?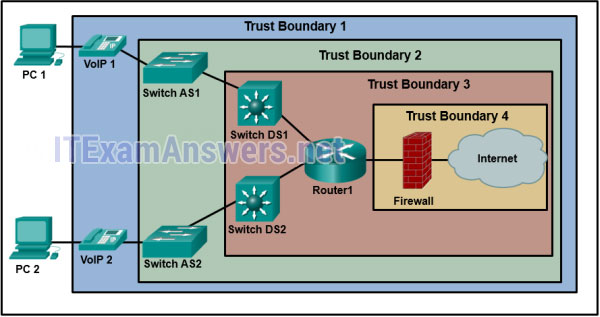 Correct
Correct
Incorrect
Hint
Traffic should be classified and marked as close to its source as possible. The trust boundary identifies at which device marked traffic should be trusted. Traffic marked on VoIP phones would be considered trusted as it moves into the enterprise network. -
Question 41 of 53
41. Question
1 pointsWhich IoT pillar provides the infrastructure for application mobility?Correct
Incorrect
Hint
Providing the infrastructure for application hosting and application mobility between cloud and fog computing is the function of the application enablement platform pillar. -
Question 42 of 53
42. Question
1 pointsWhat are three abstraction layers of a computer system? (Choose three.)Correct
Incorrect
Hint
Abstraction layers help describe network protocols within the architecture of a computer system. Each layer uses programming code to interface with the layers above and below. The following abstraction layers make up a computer system: Hardware Firmware Assembler Kernel OS Services -
Question 43 of 53
43. Question
1 pointsUsers are reporting longer delays in authentication and in accessing network resources during certain time periods of the week. What kind of information should network engineers check to find out if this situation is part of a normal network behavior?Correct
Incorrect
Hint
The network engineers should first establish that the reported performance of the network is in fact abnormal. This is done by referring to the documented network performance baseline.Once it has been verified that the network is not having a proper performance, then specific troubleshooting processes can be applied. -
Question 44 of 53
44. Question
1 pointsA user is unable to connect to the Internet. The network administrator decides to use the top-down troubleshooting approach. Which action should the administrator perform first?Correct
Incorrect
Hint
The top-down troubleshooting method starts with the applications and moves down through the layers of the OSI model until the cause of the problem is identified. Using a web brwoser to test DNS resolution is a troubleshooting step at the application layer. -
Question 45 of 53
45. Question
1 pointsHow do network administrators use IP SLAs to monitor a network and to detect a network failure early?Correct
Incorrect
Hint
The Cisco IOS IP Service Level Agreements (SLAs) feature is a useful tool to discover a network failure. Network administrators use IP SLAs to simulate network data and IP services to collect network performance information in real time. The results can help network administrators detect signs of network issues in the early stages. -
Question 46 of 53
46. Question
1 pointsWhat are two examples of network problems that are found at the data link layer? (Choose two.)Correct
Incorrect
Hint
Both encapsulation and framing errors are network problems that are associated with the data link layer. Electromagnetic interference, incorrect interface clock rates, and late collisions and jabber are indications of physical layer problems. -
Question 47 of 53
47. Question
1 pointsThe output of the show ip interface brief command indicates that Serial0/0/0 is up but the line protocol is down. What are two possible causes for the line protocol being in the down state? (Choose two.)Correct
Incorrect
Hint
A router interface may experience Layer 2 issues such as framing problems, keepalives not received but expected, and encapsulation problems. The status of the interface that is experiencing Layer 2 problems would indicate line protocol down. -
Question 48 of 53
48. Question
1 pointsRefer to the exhibit. A small office uses an ISR to provide connectivity for both wired and wireless computers. One day, a sales person who is using a laptop cannot connect to Server1 through the wireless network. A network technician attempts to determine if the problem is on the wireless or the wired network. The technician pings successfully from the wireless laptop to the default gateway IP address on the ISR. What should be the next troubleshooting step?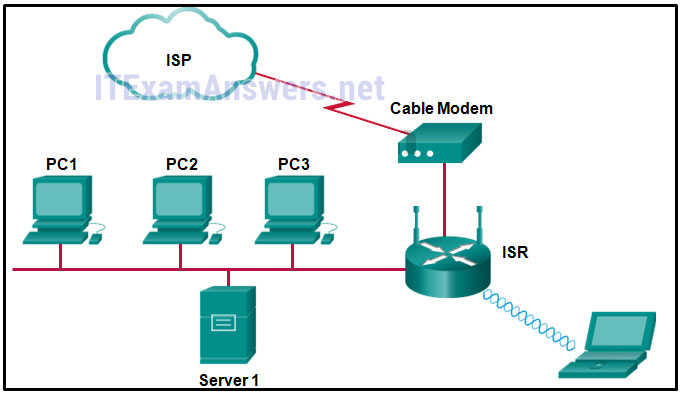 Correct
Correct
Incorrect
-
Question 49 of 53
49. Question
1 pointsRefer to the exhibit. A ping from R1 to 10.1.1.2 is successful, but a ping from R1 to any address in the 192.168.2.0 network fails. What is the cause of this problem?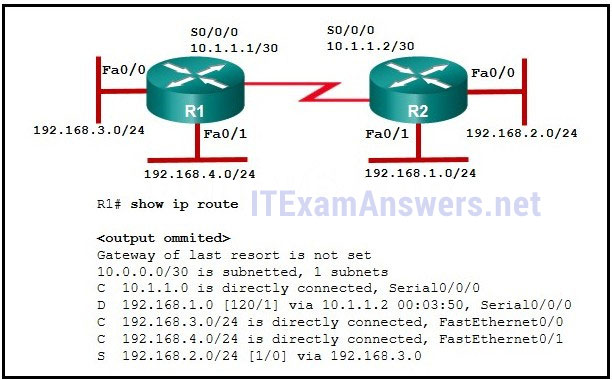 Correct
Correct
Incorrect
-
Question 50 of 53
50. Question
1 pointsWhich feature is unique to IPv6 ACLs when compared to those of IPv4 ACLs?Correct
Incorrect
Hint
One of the major differences between IPv6 and IPv4 ACLs are two implicit permit statements at the end of any IPv6 ACL. These two permit statements allow neighbor discovery operations to function on the router interface. -
Question 51 of 53
51. Question
1 pointsQuestion as presented: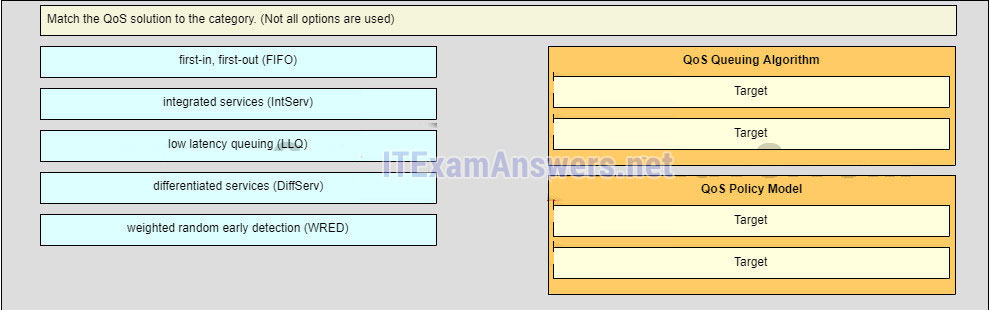
Sort elements
- first-in, first-out (FIFO)
- low latency queuing (LLC)
- integrated services (IntServ)
- differentiated services (DiffServ)
- weighted random early detection (WRED)
-
Qos Queuing Algorithm (A)
-
Qos Queuing Algorithm (B)
-
Qos policy Model (A)
-
Qos policy Model (B)
Correct
Incorrect
-
Question 52 of 53
52. Question
1 pointsQuestion as presented: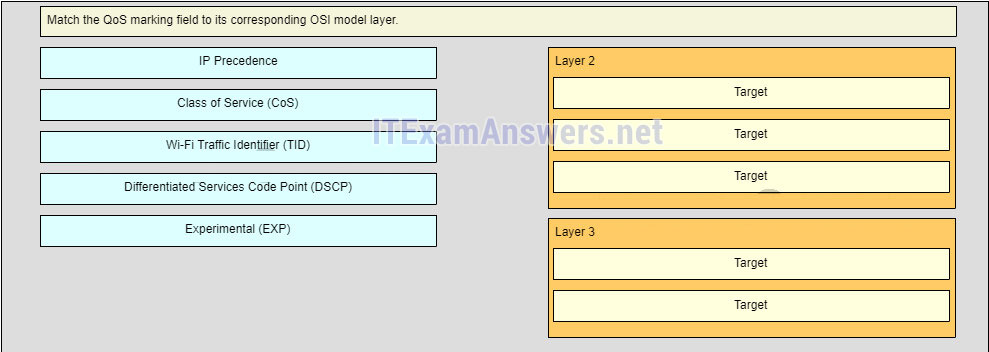
Sort elements
- Experimental (EXP)
- Class of Service (CoS)
- Wi-fi Traffic Identifier (TID)
- IP Precedence
- Differentiated Services Code Point (DSCP)
-
Layer 2 (A)
-
Layer 2 (B)
-
Layer 2 (C)
-
Layer 3 (A)
-
Layer 3 (B)
Correct
Incorrect
-
Question 53 of 53
53. Question
1 pointsOpen the PT Activity. Perform the tasks in the activity instructions and then answer the question. A user reports that PC0 cannot visit the web server www.server.com. Troubleshoot the network configuration to identify the problem. What are three configuration issues that are causing the problem? (Choose three.)Correct
Incorrect
Hint
On SW1, where VLANs are implemented, each port should be assigned to a proper VLAN. The physical interface on Branch must be activated to maintain the link status between Branch and various VLANs on SW1. In order to allow communication to remote networks, proper routing must be configured on both Branch and HQ routers.

Refer to the exhibit. A network administrator has configured router Edge_Router as shown in the output. Connectivity is failing between Edge_Router and a non-Cisco router running Frame Relay. What should be done to repair this Layer 2 connectivity?
i217792v1n1_217792.png
1. Issue the ietf keyword when enabling Frame Relay on interface serial 0/1/0.
2. Issue the broadcast keyword when performing static mapping on interface serial 0/1/0.
3. Correct the IP address used in the frame-relay map command.
4. Issue the frame-relay lmi-type ansi command on interface serial 0/1/0.
5. Modify the OSPF process-id from 10 to 1.
Correct answer is:
2) Issue the ietf keyword when enabling Frame Relay on interface serial 0/1/0.
Which three statements are true regarding the Frame Relay LMI? (Choose three.)
1. The LMI provides a virtual circuit (VC) status mechanism.
2. The LMI type must always be manually configured.
3. The available LMI types are CHAP and PAP.
4. The LMI types supported by Cisco routers are CISCO and IETF.
5. The LMI type configured on the router must match the one used on the Frame Relay switch.
6. The LMI uses reserved DLCIs to exchange messages between the DTE and DCE.
Correct answers are:
1) The LMI provides a virtual circuit (VC) status mechanism.
5) The LMI type configured on the router must match the one used on the Frame Relay switch.
6) The LMI uses reserved DLCIs to exchange messages between the DTE and DCE.