Time limit: 0
Quiz-summary
0 of 146 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- 143
- 144
- 145
- 146
Information
Good luck for you!
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- 143
- 144
- 145
- 146
- Answered
- Review
-
Question 1 of 146
1. Question
1 pointsWhich statement best describes a WAN?Correct
Incorrect
-
Question 2 of 146
2. Question
1 pointsConnecting offices at different locations using the Internet can be economical for a business. What are two important business policy issues that should be addressed when using the Internet for this purpose? (Choose two.)Correct
Incorrect
-
Question 3 of 146
3. Question
1 pointsWhat is a disadvafntage of a packet-switched network compared to a circuit-switched network?Correct
Incorrect
-
Question 4 of 146
4. Question
1 pointsA company is considering updating the campus WAN connection. Which two WAN options are examples of the private WAN architecture? (Choose two.)Correct
Incorrect
-
Question 5 of 146
5. Question
1 pointsWhich statement describes a characteristic of dense wavelength division multiplexing (DWDM)?Correct
Incorrect
-
Question 6 of 146
6. Question
1 pointsWhich WAN technology can serve as the underlying network to carry multiple types of network traffic such as IP, ATM, Ethernet, and DSL?Correct
Incorrect
-
Question 7 of 146
7. Question
1 pointsWhich two WAN technologies are more likely to be used by a business than by teleworkers or home users? (Choose two.)Correct
Incorrect
-
Question 8 of 146
8. Question
1 pointsThe security policy in a company specifies that the staff in the sales department must use a VPN to connect to the corporate network to access the sales data when they travel to meet customers. What component is needed by the sales staff to establish a remote VPN connection?Correct
Incorrect
-
Question 9 of 146
9. Question
1 pointsHow many DS0 channels are bundled to produce a 1.544 Mbps T1 line?Correct
Incorrect
-
Question 10 of 146
10. Question
1 pointsWhat function is provided by Multilink PPP?Correct
Incorrect
-
Question 11 of 146
11. Question
1 pointsRefer to the exhibit. A network administrator is configuring the PPP link between the routers R1 and R2. However, the link cannot be established. Based on the partial output of the show running-config command, what is the cause of the problem?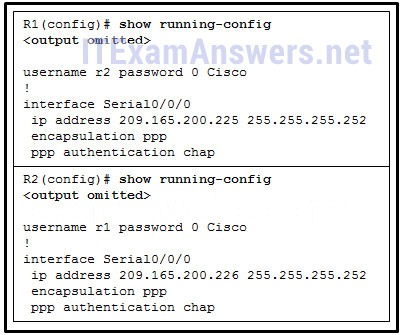 Correct
Correct
Incorrect
-
Question 12 of 146
12. Question
1 pointsRefer to the exhibit. A network administrator has configured routers RTA and RTB, but cannot ping from serial interface to serial interface. Which layer of the OSI model is the most likely cause of the problem?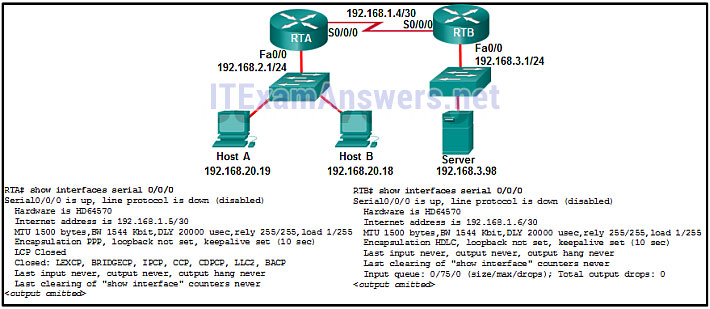 Correct
Correct
Incorrect
-
Question 13 of 146
13. Question
1 pointsWhat advantage does DSL have compared to cable technology?Correct
Incorrect
-
Question 14 of 146
14. Question
1 pointsWhich broadband technology would be best for a user that needs remote access when traveling in mountains and at sea?Correct
Incorrect
-
Question 15 of 146
15. Question
1 pointsWhich technology requires the use of PPPoE to provide PPP connections to customers?Correct
Incorrect
-
Question 16 of 146
16. Question
1 pointsRefer to the exhibit. What is the network administrator verifying when issuing the show ip interface brief command on R1 in respect to the PPPoE connection to R2?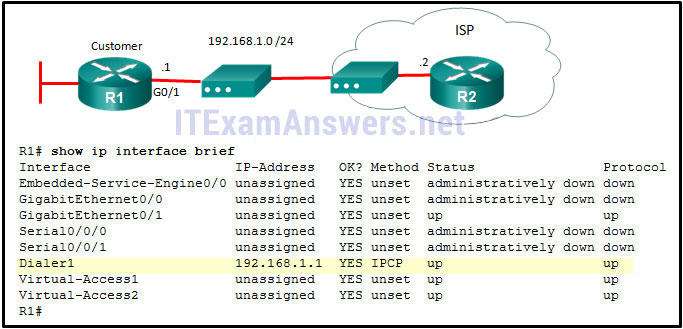 Correct
Correct
Incorrect
-
Question 17 of 146
17. Question
1 pointsWhich technology creates a mapping of public IP addresses for remote tunnel spokes in a DMVPN configuration?Correct
Incorrect
-
Question 18 of 146
18. Question
1 pointsWhat is the purpose of the generic routing encapsulation tunneling protocol?Correct
Incorrect
-
Question 19 of 146
19. Question
1 pointsRefer to the exhibit. What is used to exchange routing information between routers within each AS?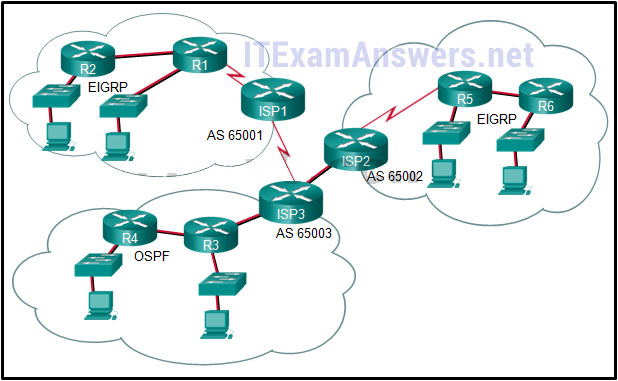 Correct
Correct
Incorrect
-
Question 20 of 146
20. Question
1 pointsWhich IPv4 address range covers all IP addresses that match the ACL filter specified by 172.16.2.0 with wildcard mask 0.0.1.255?Correct
Incorrect
-
Question 21 of 146
21. Question
1 pointsRefer to the exhibit. A named access list called chemistry_block has been written to prevent users on the Chemistry Network and public Internet from access to Records Server. All other users within the school should have access to this server. The list contains the following statements: deny 172.16.102.0 0.0.0.255 172.16.104.252 0.0.0.0 permit 172.16.0.0 0.0.255.255 172.16.104.252 0.0.0.0 Which command sequence will place this list to meet these requirements?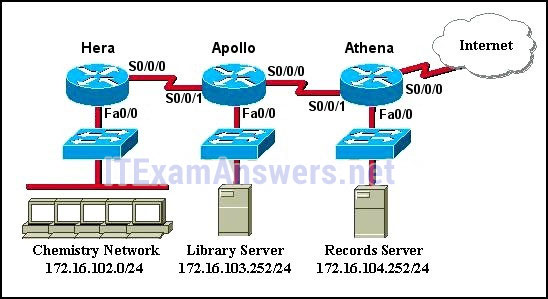 Correct
Correct
Incorrect
-
Question 22 of 146
22. Question
1 pointsWhat guideline is generally followed about the placement of extended access control lists?Correct
Incorrect
-
Question 23 of 146
23. Question
1 pointsIn the creation of an IPv6 ACL, what is the purpose of the implicit final command entries, permit icmp any any nd-na and permit icmp any any nd-ns?Correct
Incorrect
-
Question 24 of 146
24. Question
1 pointsA network administrator is testing IPv6 connectivity to a web server. The network administrator does not want any other host to connect to the web server except for the one test computer. Which type of IPv6 ACL could be used for this situation?Correct
Incorrect
-
Question 25 of 146
25. Question
1 pointsRefer to the exhibit. The IPv6 access list LIMITED_ACCESS is applied on the S0/0/0 interface of R1 in the inbound direction. Which IPv6 packets from the ISP will be dropped by the ACL on R1?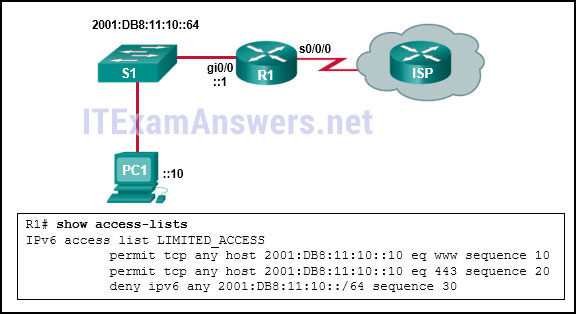 Correct
Correct
Incorrect
-
Question 26 of 146
26. Question
1 pointsWhat is a secure configuration option for remote access to a network device?Correct
Incorrect
-
Question 27 of 146
27. Question
1 pointsWhat protocol should be disabled to help mitigate VLAN attacks?Correct
Incorrect
-
Question 28 of 146
28. Question
1 pointsWhich term describes the role of a Cisco switch in the 802.1X port-based access control?Correct
Incorrect
-
Question 29 of 146
29. Question
1 pointsWhat two protocols are supported on Cisco devices for AAA communications? (Choose two.)Correct
Incorrect
-
Question 30 of 146
30. Question
1 pointsIn configuring SNMPv3, what is the purpose of creating an ACL?Correct
Incorrect
-
Question 31 of 146
31. Question
1 pointsRefer to the exhibit. What feature does an SNMP manager need in order to be able to set a parameter on switch ACSw1?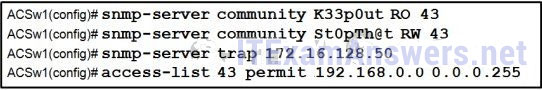 Correct
Correct
Incorrect
-
Question 32 of 146
32. Question
1 pointsWhich Cisco feature sends copies of frames entering one port to a different port on the same switch in order to perform traffic analysis?Correct
Incorrect
-
Question 33 of 146
33. Question
1 pointsWhat are two characteristics of video traffic? (Choose two.)Correct
Incorrect
-
Question 34 of 146
34. Question
1 pointsWhich QoS mechanism allows delay-sensitive data, such as voice, to be sent first before packets in other queues are sent?Correct
Incorrect
-
Question 35 of 146
35. Question
1 pointsRefer to the exhibit. As traffic is forwarded out an egress interface with QoS treatment, which congestion avoidance technique is used?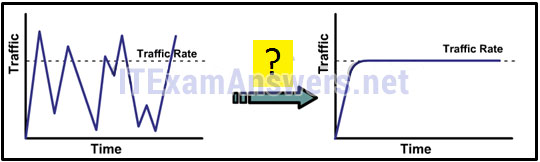 Correct
Correct
Incorrect
-
Question 36 of 146
36. Question
1 pointsWhich type of QoS marking is applied to Ethernet frames?Correct
Incorrect
-
Question 37 of 146
37. Question
1 pointsWhat is the function of a QoS trust boundary?Correct
Incorrect
-
Question 38 of 146
38. Question
1 pointsA vibration sensor on an automated production line detects an unusual condition. The sensor communicates with a controller that automatically shuts down the line and activates an alarm. What type of communication does this scenario represent?Correct
Incorrect
-
Question 39 of 146
39. Question
1 pointsWhich pillar of the Cisco IoT System allows data to be analyzed and managed at the location where it is generated?Correct
Incorrect
-
Question 40 of 146
40. Question
1 pointsWhich Cloud computing service would be best for a new organization that cannot afford physical servers and networking equipment and must purchase network services on-demand?Correct
Incorrect
-
Question 41 of 146
41. Question
1 pointsA data center has recently updated a physical server to host multiple operating systems on a single CPU. The data center can now provide each customer with a separate web server without having to allocate an actual discrete server for each customer. What is the networking trend that is being implemented by the data center in this situation?Correct
Incorrect
-
Question 42 of 146
42. Question
1 pointsWhat is used to pre-populate the adjacency table on Cisco devices that use CEF to process packets?Correct
Incorrect
-
Question 43 of 146
43. Question
1 pointsWhich component of the ACI architecture translates application policies into network programming?Correct
Incorrect
-
Question 44 of 146
44. Question
1 pointsWhich two pieces of information should be included in a logical topology diagram of a network? (Choose two.)Correct
Incorrect
-
Question 45 of 146
45. Question
1 pointsWhich network performance statistics should be measured in order to verify SLA compliance?Correct
Incorrect
-
Question 46 of 146
46. Question
1 pointsWhich feature sends simulated data across the network and measures performance between multiple network locations?Correct
Incorrect
-
Question 47 of 146
47. Question
1 pointsWhich troubleshooting tool would a network administrator use to check the Layer 2 header of frames that are leaving a particular host?Correct
Incorrect
-
Question 48 of 146
48. Question
1 pointsRefer to the exhibit. A network administrator is troubleshooting the OSPF network. The 10.10.0.0/16 network is not showing up in the routing table of Router1. What is the probable cause of this problem?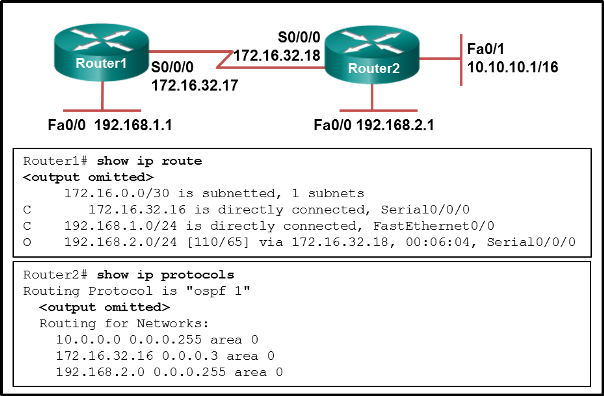 Correct
Correct
Incorrect
-
Question 49 of 146
49. Question
1 pointsRefer to the exhibit. A user turns on a PC after it is serviced and calls the help desk to report that the PC seems unable to reach the Internet. The technician asks the user to issue the arp –a and ipconfig commands. Based on the output, what are two possible causes of the problem? (Choose two.)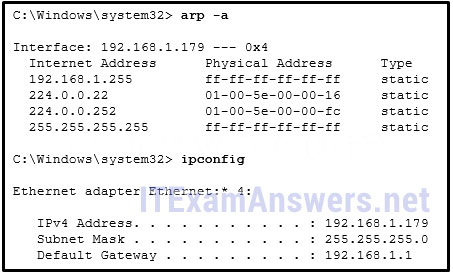 Correct
Correct
Incorrect
-
Question 50 of 146
50. Question
1 pointsMatch OoS techniques with the description. (Not all options are used.) Which circumstance would result in an enterprise deciding to implement a corporate WAN?Correct
Incorrect
-
Question 51 of 146
51. Question
1 pointsWhat are two types of WAN providers? (Choose two.)Correct
Incorrect
-
Question 52 of 146
52. Question
1 pointsWhich two types of devices are specific to WAN environments and are not found on a LAN? (Choose two.)Correct
Incorrect
-
Question 53 of 146
53. Question
1 pointsWhat is a feature of dense wavelength-division multiplexing (DWDM) technology?Correct
Incorrect
-
Question 54 of 146
54. Question
1 pointsWhat is a disadvantage of ATM compared to Frame Relay?Correct
Incorrect
-
Question 55 of 146
55. Question
1 pointsWhich WAN solution uses labels to identify the path in sending packets through a provider network?Correct
Incorrect
-
Question 56 of 146
56. Question
1 pointsAn intercity bus company wants to offer constant Internet connectivity to the users traveling on the buses. Which two types of WAN infrastructure would meet the requirements? (Choose two.)Correct
Incorrect
-
Question 57 of 146
57. Question
1 pointsWhat device is needed at a central office to aggregate many digital subscriber lines from customers?Correct
Incorrect
-
Question 58 of 146
58. Question
1 pointsA corporation is searching for an easy and low cost solution to provide teleworkers with a secure connection to headquarters. Which solution should be selected?Correct
Incorrect
-
Question 59 of 146
59. Question
1 pointsWhat is the maximum number of DS0 channels in a 1.544 Mbps T1 line?Correct
Incorrect
-
Question 60 of 146
60. Question
1 pointsRefer to the exhibit. What type of Layer 2 encapsulation will be used for RtrA connection D if it is left to the default and the router is a Cisco router?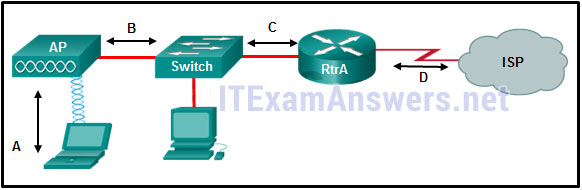 Correct
Correct
Incorrect
-
Question 61 of 146
61. Question
1 pointsWhich two functions are provided by the NCP during a PPP connection? (Choose two.)Correct
Incorrect
-
Question 62 of 146
62. Question
1 pointsWhat PPP information will be displayed if a network engineer issues the show ppp multilink command on Cisco router?Correct
Incorrect
-
Question 63 of 146
63. Question
1 pointsRefer to the exhibit. Which statement describes the status of the PPP connection?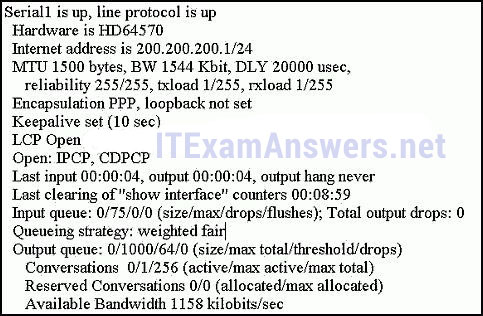 Correct
Correct
Incorrect
-
Question 64 of 146
64. Question
1 pointsA network administrator is configuring a PPP link with the commands: R1(config-if)# encapsulation ppp R1(config-if)# ppp quality 70 What is the effect of these commands?Correct
Incorrect
-
Question 65 of 146
65. Question
1 pointsHow does virtualization help with disaster recovery within a data center?Correct
Incorrect
-
Question 66 of 146
66. Question
1 pointsWhich broadband solution is appropriate for a home user who needs a wired connection not limited by distance?Correct
Incorrect
-
Question 67 of 146
67. Question
1 pointsWhat is the protocol that provides ISPs the ability to send PPP frames over DSL networks?Correct
Incorrect
-
Question 68 of 146
68. Question
1 pointsIn software defined network architecture, what function is removed from network devices and performed by an SDN controller?Correct
Incorrect
-
Question 69 of 146
69. Question
1 pointsWhat would a network administrator expect the routing table of stub router R1 to look like if connectivity to the ISP was established via a PPPoE configuration?Correct
Incorrect
-
Question 70 of 146
70. Question
1 pointsWhat is a benefit of implementing a Dynamic Multipoint VPN network design?Correct
Incorrect
-
Question 71 of 146
71. Question
1 pointsWhich remote access implementation scenario will support the use of generic routing encapsulation tunneling?Correct
Incorrect
-
Question 72 of 146
72. Question
1 pointsRefer to the exhibit. All routers are successfully running the BGP routing protocol. How many routers must use EBGP in order to share routing information across the autonomous systems?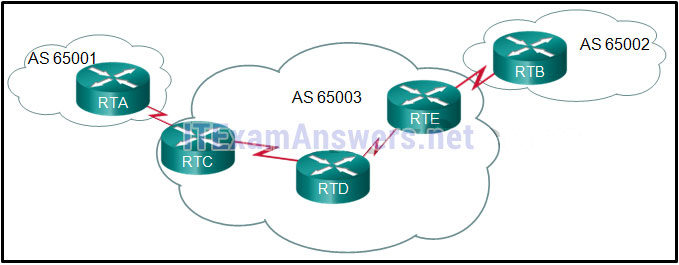 Correct
Correct
Incorrect
-
Question 73 of 146
73. Question
1 pointsWhich statement describes a characteristic of standard IPv4 ACLs?Correct
Incorrect
-
Question 74 of 146
74. Question
1 pointsWhich three values or sets of values are included when creating an extended access control list entry? (Choose three.)Correct
Incorrect
-
Question 75 of 146
75. Question
1 pointsRefer to the exhibit. A router has an existing ACL that permits all traffic from the 172.16.0.0 network. The administrator attempts to add a new ACE to the ACL that denies packets from host 172.16.0.1 and receives the error message that is shown in the exhibit. What action can the administrator take to block packets from host 172.16.0.1 while still permitting all other traffic from the 172.16.0.0 network?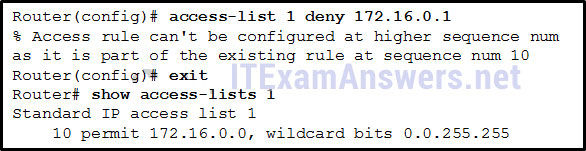 Correct
Correct
Incorrect
-
Question 76 of 146
76. Question
1 pointsWhich three implicit access control entries are automatically added to the end of an IPv6 ACL? (Choose three.)Correct
Incorrect
-
Question 77 of 146
77. Question
1 pointsThe computers used by the network administrators for a school are on the 10.7.0.0/27 network. Which two commands are needed at a minimum to apply an ACL that will ensure that only devices that are used by the network administrators will be allowed Telnet access to the routers? (Choose two.)Correct
Incorrect
-
Question 78 of 146
78. Question
1 pointsA network administrator is adding ACLs to a new IPv6 multirouter environment. Which IPv6 ACE is automatically added implicitly at the end of an ACL so that two adjacent routers can discover each other?Correct
Incorrect
-
Question 79 of 146
79. Question
1 pointsWhat would be the primary reason an attacker would launch a MAC address overflow attack?Correct
Incorrect
-
Question 80 of 146
80. Question
1 pointsWhat are three of the six core components in the Cisco IoT system? (Choose three.)Correct
Incorrect
-
Question 81 of 146
81. Question
1 pointsWhat security countermeasure is effective for preventing CAM table overflow attacks?Correct
Incorrect
-
Question 82 of 146
82. Question
1 pointsWhich SNMP feature provides a solution to the main disadvantage of SNMP polling?Correct
Incorrect
-
Question 83 of 146
83. Question
1 pointsWhen SNMPv1 or SNMPv2 is being used, which feature provides secure access to MIB objects?Correct
Incorrect
-
Question 84 of 146
84. Question
1 pointsWhat two are added in SNMPv3 to address the weaknesses of previous versions of SNMP? (Choose two.)Correct
Incorrect
-
Question 85 of 146
85. Question
1 pointsWhich queuing mechanism supports user-defined traffic classes?Correct
Incorrect
-
Question 86 of 146
86. Question
1 pointsWhich field is used to mark Layer 2 Ethernet frames for QoS treatment?Correct
Incorrect
-
Question 87 of 146
87. Question
1 pointsWhat is an example of cloud computing?Correct
Incorrect
-
Question 88 of 146
88. Question
1 pointsWhich type of resources are required for a Type 1 hypervisor?Correct
Incorrect
-
Question 89 of 146
89. Question
1 pointsA network technician made a configuration change on the core router in order to solve a problem. However, the problem is not solved. Which step should the technician take next?Correct
Incorrect
-
Question 90 of 146
90. Question
1 pointsA user reports that when the corporate web page URL is entered on a web browser, an error message indicates that the page cannot be displayed. The help-desk technician asks the user to enter the IP address of the web server to see if the page can be displayed. Which troubleshooting method is being used by the technician?Correct
Incorrect
-
Question 91 of 146
91. Question
1 pointsWhat is a primary function of the Cisco IOS IP Service Level Agreements feature?Correct
Incorrect
-
Question 92 of 146
92. Question
1 pointsWhich IOS log message level indicates the highest severity level?Correct
Incorrect
-
Question 93 of 146
93. Question
1 pointsWhich symptom is an example of network issues at the network layer?Correct
Incorrect
-
Question 94 of 146
94. Question
1 pointsRefer to the exhibit. H1 can only ping H2, H3, and the Fa0/0 interface of router R1. H2 and H3 can ping H4 and H5. Why might H1 not be able to successfully ping H4 and H5? Correct
Correct
Incorrect
-
Question 95 of 146
95. Question
1 pointsRefer to the exhibit. On the basis of the output, which two statements about network connectivity are correct? (Choose two.)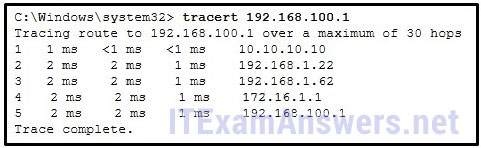 Correct
Correct
Incorrect
-
Question 96 of 146
96. Question
1 pointsFill in the blanks. Use dotted decimal format.- The wildcard mask that is associated with 128.165.216.0/23 is (0.0.1.255)
Correct
Incorrect
-
Question 97 of 146
97. Question
1 pointsMatch the characteristic to the appropriate authentication protocol. (Not all options are used.)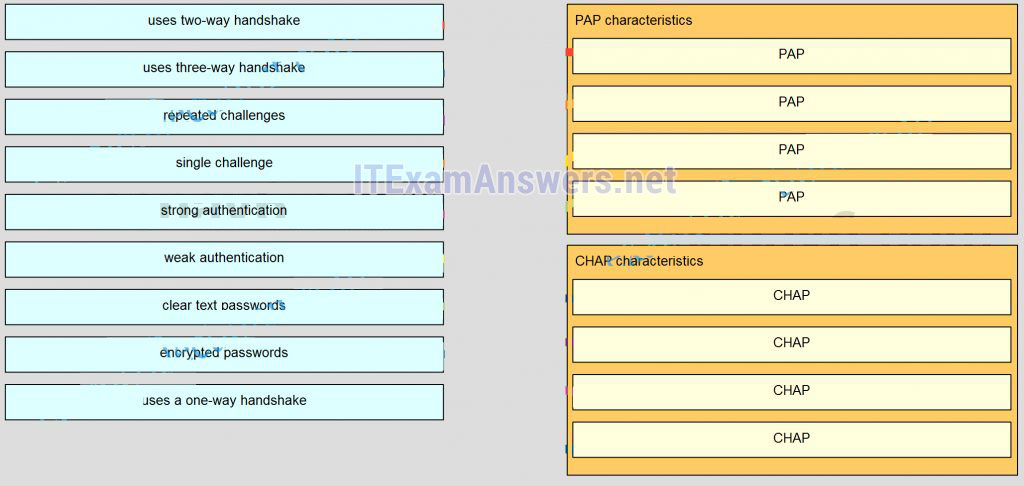
Sort elements
- uses two-way handshake
- single challenge
- weak authentication
- clear text passwords
- uses three-way handshake
- repeated challenge
- strong authentication
- encrypted passwords
- use a one-way handshake
-
PAP characteristics (1)
-
PAP characteristics (2)
-
PAP characteristics (3)
-
PAP characteristics (4)
-
CHAP characteristics (1)
-
CHAP characteristics (2)
-
CHAP characteristics (3)
-
CHAP characteristics (4)
Correct
Incorrect
-
Question 98 of 146
98. Question
1 pointsMatch the term to the description. (Not all options are used.)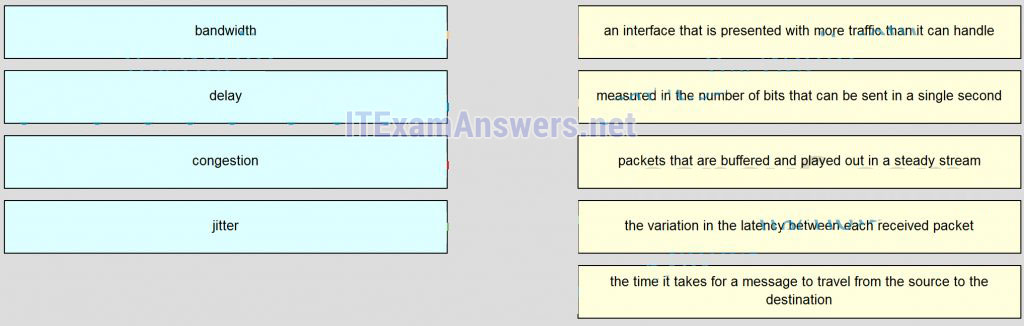
Sort elements
- measured in the number of bits that can be sent in a single second
- the time it takes for a message to travel from the source to the dextination
- an interface that is presented with more traffic than it can be handle
- the variation in the latency between each received packet
- packets that are buffered and played out in a steady stream
-
bandwidth
-
delay
-
congestion
-
jitter
Correct
Incorrect
-
Question 99 of 146
99. Question
1 pointsWhat is a primary difference between a company LAN and the WAN services that it uses?Correct
Incorrect
-
Question 100 of 146
100. Question
1 pointsTo which two layers of the OSI model do WAN technologies provide services? (Choose two.)Correct
Incorrect
-
Question 101 of 146
101. Question
1 pointsWhich two technologies are private WAN technologies? (Choose two.)Correct
Incorrect
-
Question 102 of 146
102. Question
1 pointsWhich WAN technology can switch any type of payload based on labels?Correct
Incorrect
-
Question 103 of 146
103. Question
1 pointsWhat technology can be used to create a private WAN via satellite communications?Correct
Incorrect
-
Question 104 of 146
104. Question
1 pointsWhich public WAN access technology utilizes copper telephone lines to provide access to subscribers that are multiplexed into a single T3 link connection?Correct
Incorrect
-
Question 105 of 146
105. Question
1 pointsHow many DS0 channels are bounded to produce a 1.544 Mb/s DS1 line?Correct
Incorrect
-
Question 106 of 146
106. Question
1 pointsRefer to the exhibit. Communication between two peers has failed. Based on the output that is shown, what is the most likely cause?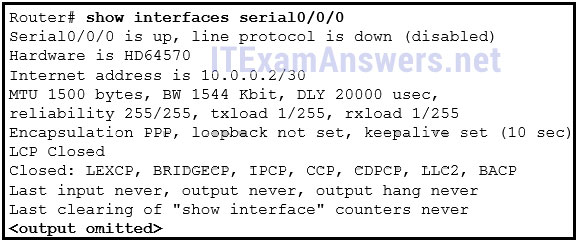 Correct
Correct
Incorrect
-
Question 107 of 146
107. Question
1 pointsRefer to the exhibit. Which type of Layer 2 encapsulation used for connection D requires Cisco routers?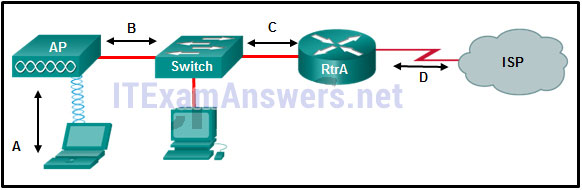 Correct
Correct
Incorrect
-
Question 108 of 146
108. Question
1 pointsWhich three statements are true about PPP? (Choose three.)Correct
Incorrect
-
Question 109 of 146
109. Question
1 pointsA network administrator is evaluating authentication protocols for a PPP link. Which three factors might lead to the selection of CHAP over PAP as the authentication protocol? (Choose three.)Correct
Incorrect
-
Question 110 of 146
110. Question
1 pointsWhich cellular or mobile wireless standard is considered a fourth generation technology?Correct
Incorrect
-
Question 111 of 146
111. Question
1 pointsA company is looking for the least expensive broadband solution that provides at least 10 Mb/s download speed. The company is located 5 miles from the nearest provider. Which broadband solution would be appropriate?Correct
Incorrect
-
Question 112 of 146
112. Question
1 pointsWhich technology can ISPs use to periodically challenge broadband customers over DSL networks with PPPoE?Correct
Incorrect
-
Question 113 of 146
113. Question
1 pointsWhat are the three core components of the Cisco ACI architecture? (Choose three.)Correct
Incorrect
-
Question 114 of 146
114. Question
1 pointsWhich statement describes a feature of site-to-site VPNs?Correct
Incorrect
-
Question 115 of 146
115. Question
1 pointsWhat are three features of a GRE tunnel? (Choose three.)Correct
Incorrect
-
Question 116 of 146
116. Question
1 pointsRefer to the exhibit. What two commands are needed to complete the GRE tunnel configuration on router R1? (Choose two.)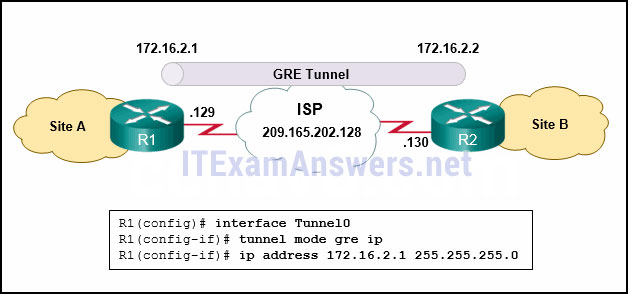 Correct
Correct
Incorrect
-
Question 117 of 146
117. Question
1 pointsWhat does BGP use to exchange routing updates with neighbors?Correct
Incorrect
-
Question 118 of 146
118. Question
1 pointsRefer to the exhibit. The network administrator that has the IP address of 10.0.70.23/25 needs to have access to the corporate FTP server (10.0.54.5/28). The FTP server is also a web server that is accessible to all internal employees on networks within the 10.x.x.x address. No other traffic should be allowed to this server. Which extended ACL would be used to filter this traffic, and how would this ACL be applied? (Choose two.)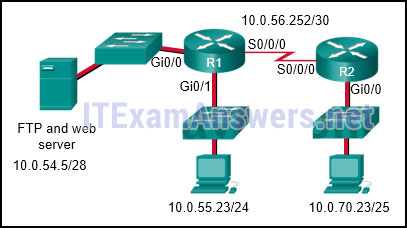 Correct
Correct
Incorrect
-
Question 119 of 146
119. Question
1 pointsRefer to the exhibit. What can be determined from this output? https://itexamanswers.net/wp-content/uploads/2016/02/i209869v1n1_209869.jpgCorrect
Incorrect
-
Question 120 of 146
120. Question
1 pointsWhat is the only type of ACL available for IPv6?Correct
Incorrect
-
Question 121 of 146
121. Question
1 pointsWhich IPv6 ACL command entry will permit traffic from any host to an SMTP server on network 2001:DB8:10:10::/64?Correct
Incorrect
-
Question 122 of 146
122. Question
1 pointsRefer to the exhibit. Considering how packets are processed on a router that is configured with ACLs, what is the correct order of the statements?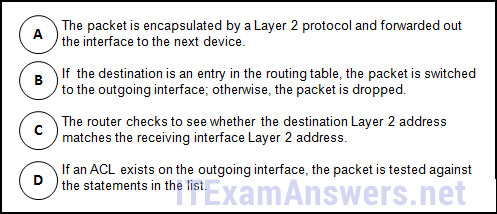 Correct
Correct
Incorrect
-
Question 123 of 146
123. Question
1 pointsWhich two hypervisors are suitable to support virtual machines in a data center? (Choose two.)Correct
Incorrect
-
Question 124 of 146
124. Question
1 pointsHow can DHCP spoofing attacks be mitigated?Correct
Incorrect
-
Question 125 of 146
125. Question
1 pointsWhat action can a network administrator take to help mitigate the threat of VLAN attacks?Correct
Incorrect
-
Question 126 of 146
126. Question
1 pointsWhich SNMP message type informs the network management system (NMS) immediately of certain specified events?Correct
Incorrect
-
Question 127 of 146
127. Question
1 pointsRefer to the exhibit. A SNMP manager is using the community string of snmpenable and is configured with the IP address 172.16.10.1. The SNMP manager is unable to read configuration variables on the R1 SNMP agent. What could be the problem?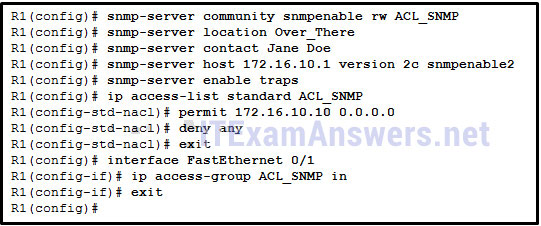 Correct
Correct
Incorrect
-
Question 128 of 146
128. Question
1 pointsRefer to the exhibit. Which SNMP authentication password must be used by the member of the ADMIN group that is configured on router R1?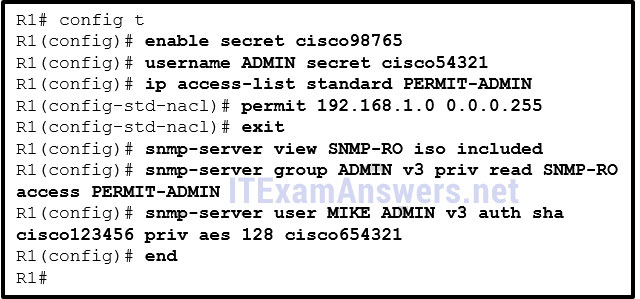 Correct
Correct
Incorrect
-
Question 129 of 146
129. Question
1 pointsA network administrator has noticed an unusual amount of traffic being received on a switch port that is connected to a college classroom computer. Which tool would the administrator use to make the suspicious traffic available for analysis at the college data center?Correct
Incorrect
-
Question 130 of 146
130. Question
1 pointsWhat network monitoring tool copies traffic moving through one switch port, and sends the copied traffic to another switch port for analysis?Correct
Incorrect
-
Question 131 of 146
131. Question
1 pointsVoice packets are being received in a continuous stream by an IP phone, but because of network congestion the delay between each packet varies and is causing broken conversations. What term describes the cause of this condition?Correct
Incorrect
-
Question 132 of 146
132. Question
1 pointsWhat mechanism compensates for jitter in an audio stream by buffering packets and then replaying them outbound in a steady stream?Correct
Incorrect
-
Question 133 of 146
133. Question
1 pointsWhich type of network traffic cannot be managed using congestion avoidance tools?Correct
Incorrect
-
Question 134 of 146
134. Question
1 pointsA network administrator has moved the company intranet web server from a switch port to a dedicated router interface. How can the administrator determine how this change has affected performance and availability on the company intranet?Correct
Incorrect
-
Question 135 of 146
135. Question
1 pointsIn which stage of the troubleshooting process would ownership be researched and documented?Correct
Incorrect
-
Question 136 of 146
136. Question
1 pointsWhich troubleshooting approach is more appropriate for a seasoned network administrator rather than a less-experienced network administrator?Correct
Incorrect
-
Question 137 of 146
137. Question
1 pointsA router has been configured to use simulated network traffic in order to monitor the network performance between the router and a distant network device. Which command would display the results of this analysis?Correct
Incorrect
-
Question 138 of 146
138. Question
1 pointsWhich type of tool would an administrator use to capture packets that are going to and from a particular device?Correct
Incorrect
-
Question 139 of 146
139. Question
1 pointsRefer to the exhibit. Which two statements describe the results of entering these commands? (Choose two.)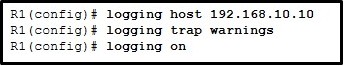 Correct
Correct
Incorrect
-
Question 140 of 146
140. Question
1 pointsRefer to the exhibit. A network administrator discovers that host A is having trouble with Internet connectivity, but the server farm has full connectivity. In addition, host A has full connectivity to the server farm. What is a possible cause of this problem? Correct
Correct
Incorrect
-
Question 141 of 146
141. Question
1 pointsMatch the operation to the appropriate QoS model.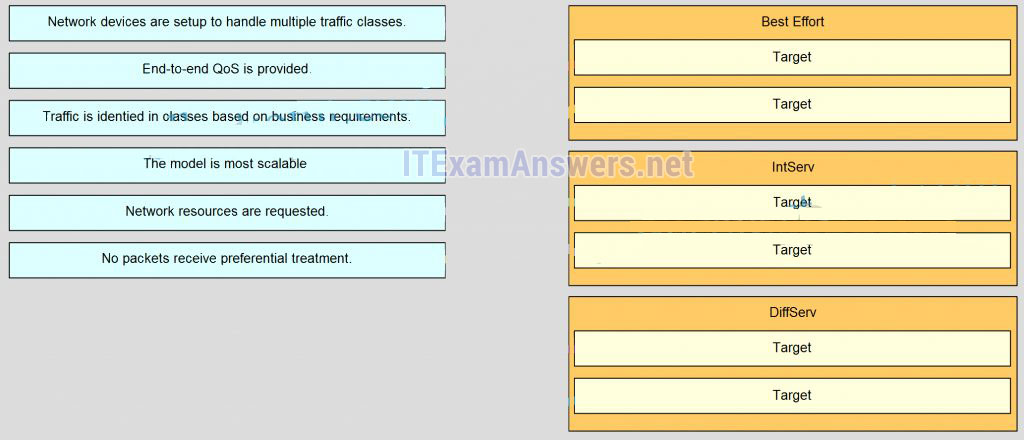
Sort elements
- The model is most scalable
- No packets receive preferential treatment
- End-to-end Qos is provided
- Network resources are requeted
- Network devices are setup to handle multiple traffic classes
- Traffic is identied in classes based on business reqirements
-
Best Offort
-
Best Offort
-
Intserv
-
Intserv
-
Diffserv
-
Diffserv
Correct
Incorrect
-
Question 142 of 146
142. Question
1 pointsMatch the cloud model with the description.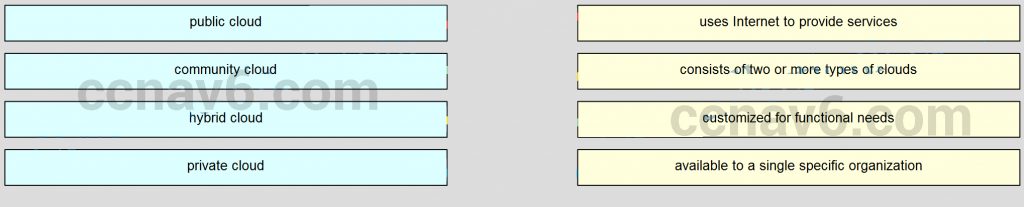
Sort elements
- use internet to provide services
- customized for functional needs
- consists of two or more types of cloud
- available to a single specific organization
-
public cloud
-
community cloud
-
hybrid cloud
-
private cloud
Correct
Incorrect
-
Question 143 of 146
143. Question
1 pointsMatch the cloud model with the description.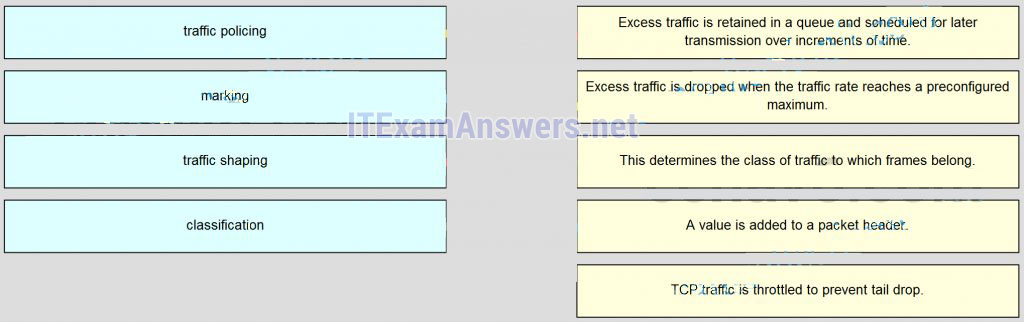
Sort elements
- Excess traffic is dropped when the traffic rate reaches a preconfigured maximum
- A value is added to a packet header
- Excess traffic is retained in a queue and scheduled for later transmission over increments of time
- This determines the class of traffic to which frames belong
- TCP traffic is throttled to prevent tail drop
-
traffic policing
-
marking
-
traffic shaping
-
classcification
Correct
Incorrect
-
Question 144 of 146
144. Question
1 pointsWhich two factors allow businesses to safely communicate and perform transactions using the Internet? (Choose two.)Correct
Incorrect
-
Question 145 of 146
145. Question
1 pointsWhat is the wildcard mask that is associated with the network 128.165.216.0/23?Correct
Incorrect
-
Question 146 of 146
146. Question
1 pointsWhat two features are added in SNMPv3 to address the weaknesses of previous versions of SNMP? (Choose two.)Correct
Incorrect
