Time limit: 0
Quiz-summary
0 of 40 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
Information
Good luck !
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 40 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- Answered
- Review
-
Question 1 of 40
1. Question
1 pointsThe buffers for packet processing and the running configuration file are temporarily stored in which type of router memory?Correct
Incorrect
Hint
RAM provides temporary storage for the running IOS, the running configuration file, the IP routing table, ARP table, and buffers for packet processing. In contrast, permanent storage of the IOS is provided by flash. NVRAM provides permanent storage of the startup configuration file, and ROM.provides permanent storage of the router bootup instructions and a limited IOS. -
Question 2 of 40
2. Question
1 pointsHow does implementing STP allow for a scalable network design?Correct
Incorrect
Hint
Spanning Tree Protocol (STP) supports the design of a scalable network by preventing Layer 2 loops where redundant switch paths are implemented. -
Question 3 of 40
3. Question
1 pointsA home user is looking for an ISP connection that provides high speed digital transmission over regular phone lines. What ISP connection type should be used?Correct
Incorrect
-
Question 4 of 40
4. Question
1 pointsWhat is a characteristic of a default static route? Correct
Incorrect
Hint
A default static route is a route that matches all packets. It identifies the gateway IP address to which the router sends all IP packets for which the router does not have a learned or static route. A default static route is simply a static route with 0.0.0.0/0 as the destination IPv4 address. Configuring a default static route creates a gateway of last resort. -
Question 5 of 40
5. Question
1 pointsWhich three pairs of trunking modes will establish a functional trunk link between two Cisco switches? (Choose three.)Correct
Incorrect
Hint
If a trunk is in dynamic desirable on either side of a trunk link, a trunk will form. The other trunking combinations will not form trunk links. -
Question 6 of 40
6. Question
1 pointsOn which switch interface would an administrator configure an IP address so that the switch can be managed remotely?Correct
Incorrect
Hint
Interface VLAN 1 is a virtual interface on a switch, called SVI (switch virtual interface). Configuring an IP address on the default SVI, interface VLAN 1, will allow a switch to be accessed remotely. The VTY line must also be configured to allow remote access, but an IP address cannot be configured on this line. -
Question 7 of 40
7. Question
1 pointsWhich statement describes a route that has been learned dynamically?Correct
Incorrect
-
Question 8 of 40
8. Question
1 pointsRefer to the exhibit. Which switch will be the root bridge after the election process is complete?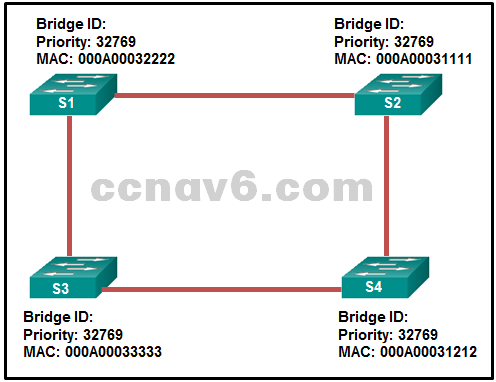 Correct
Correct
Incorrect
Hint
The root bridge is determined by the lowest bridge ID, which consists of the priority value and the MAC address. Because the priority values of all of the switches are identical, the MAC address is used to determine the root bridge. Because S2 has the lowest MAC address, S2 becomes the root bridge. -
Question 9 of 40
9. Question
1 pointsWhat three application layer protocols are part of the TCP/IP protocol suite? (Choose three.)Correct
Incorrect
Hint
DNS, DHCP, and FTP are all application layer protocols in the TCP/IP protocol suite. ARP and PPP are network access layer protocols, and NAT is an internet layer protocol in the TCP/IP protocol suite. -
Question 10 of 40
10. Question
1 pointsIn addition to the cable length, what two factors could interfere with the communication carried over UTP cables? (Choose two.)Correct
Incorrect
Hint
Copper media is widely used in network communications. However, copper media is limited by distance and signal interference. Data is transmitted on copper cables as electrical pulses. The electrical pulses are susceptible to interference from two sources: Electromagnetic interference (EMI) or radio frequency interference (RFI) – EMI and RFI signals can distort and corrupt the data signals being carried by copper media. Crosstalk – Crosstalk is a disturbance caused by the electric or magnetic fields of a signal on one wire interfering with the signal in an adjacent wire. -
Question 11 of 40
11. Question
1 pointsWhich information does a switch use to keep the MAC address table information current?Correct
Incorrect
Hint
To maintain the MAC address table, the switch uses the source MAC address of the incoming packets and the port that the packets enter. The destination address is used to select the outgoing port. -
Question 12 of 40
12. Question
1 pointsA network engineer has been tasked with connecting two large autonomous systems (AS) together over the Internet. Which routing protocol should be selected?Correct
Incorrect
Hint
Large companies commonly interconnect multiple autonomous systems using an EGP. Border Gateway Protocol (BGP) is an EGP and is the routing protocol used by routers on the Internet. -
Question 13 of 40
13. Question
1 pointsWhat important information is examined in the Ethernet frame header by a Layer 2 device in order to forward the data onward?Correct
Incorrect
Hint
The Layer 2 device, such as a switch, uses the destination MAC address to determine which path (interface or port) should be used to send the data onward to the destination device. -
Question 14 of 40
14. Question
1 pointsWhat are two reasons to implement passive interfaces in the EIGRP configuration of a Cisco router? (Choose two.)Correct
Incorrect
Hint
Two primary reasons for implementing passive interfaces in EIGRP routing are to suppress unnecessary update traffic, such as when an interface is a LAN interface with no other routers connected, and to increase security controls, such as preventing unknown rogue routing devices from receiving EIGRP updates. -
Question 15 of 40
15. Question
1 pointsWhich two functions are primary functions of a router? (Choose two.)Correct
Incorrect
-
Question 16 of 40
16. Question
1 pointsWhich two devices allow hosts on different VLANs to communicate with each other? (Choose two.)Correct
Incorrect
Hint
Members of different VLANs are on separate networks. For devices on separate networks to be able to communicate, a Layer 3 device, such as a router or Layer 3 switch, is necessary. -
Question 17 of 40
17. Question
1 pointsAn EIGRP router loses the route to a network. Its topology table contains two feasible successors to the same network. What action will the router take?Correct
Incorrect
Hint
Because EIGRP uses the DUAL algorithm, the router is able to maintain information on all potential loop-free backup routes. In the event of the failure of a routing table entry, the router immediately inserts the best backup route into the routing table. -
Question 18 of 40
18. Question
1 pointsWhat three blocks of addresses are defined by RFC 1918 for private network use? (Choose three.)Correct
Incorrect
Hint
RFC 1918, Address Allocation for Private Internets, defines three blocks of IPv4 address for private networks that should not be routable on the public Internet. 10.0.0.0/8 172.16.0.0/12 192.168.0.0/16 -
Question 19 of 40
19. Question
1 pointsWhich two pieces of information are required when creating a standard access control list? (Choose two.)Correct
Incorrect
Hint
Standard ACLs can be numbered 1 to 99 and 1300 to 1999. Standard IP ACLs filter only on the source IP address. -
Question 20 of 40
20. Question
1 pointsWhich criterion is preferred by the router to choose a router ID?Correct
Incorrect
Hint
The preferred order of criteria for Cisco routers to identify the router ID is: an explicitly configured router using the router-id rid command; the IP address of any configured loopback interface; and the IP address of any active interface on the router (it does not have to be an OSPF-enabled interface). -
Question 21 of 40
21. Question
1 pointsA network administrator is entering the command ipv6 unicast-routing to start configuring DHCPv6 operation on a router. Which statement describes the function of this command?Correct
Incorrect
Hint
The ipv6 unicast-routing command is required to enable IPv6 routing on a router. This command is not necessary for the router to be a stateless or stateful DHCPv6 server, but is required for sending ICMPv6 RA messages. -
Question 22 of 40
22. Question
1 pointsWhat three services are provided by the transport layer? (Choose three.)Correct
Incorrect
Hint
The transport layer is responsible for tracking digital conversations between a source application and a destination application through the use of port numbers. Two protocols that operate at the transport layer are TCP and UDP. TCP can provide reliability by establishing a connection, maintaining flow control, and error recovery. -
Question 23 of 40
23. Question
1 pointsWhich TCP/IP model layer is closest to the end user?Correct
Incorrect
Hint
End users use applications to interact with and use the network. The application layer of the TCP/IP model is closest to the end user. Application layer protocols are used to communicate and exchange messages with other network devices and applications. The layers of the TCP/IP model are from top to bottom (memory aid – ATIN): application, transport, internet, network access -
Question 24 of 40
24. Question
1 pointsWhen applied to a router, which command would help mitigate brute-force password attacks against the router?Correct
Incorrect
Hint
The login block-for command sets a limit on the maximum number of failed login attempts allowed within a defined period of time. If this limit is exceeded, no further logins are allowed for the specified period of time. This helps to mitigate brute-force password cracking since it will significantly increase the amount of time required to crack a password. The exec-timeout command specifies how long the session can be idle before the user is disconnected. The service password-encryption command encrypts the passwords in the running configuration. The banner motd command displays a message to users who are logging in to the device. -
Question 25 of 40
25. Question
1 pointsWhich circumstance would result in an enterprise deciding to implement a corporate WAN?Correct
Incorrect
Hint
WANs cover a greater geographic area than LANs do, so having employees distributed across many locations would require the implementation of WAN technologies to connect those locations. Customers will access corporate web services via a public WAN that is implemented by a service provider, not by the enterprise itself. When employee numbers grow, the LAN has to expand as well. A WAN is not required unless the employees are in remote locations. LAN security is not related to the decision to implement a WAN. -
Question 26 of 40
26. Question
1 pointsA corporation is searching for an easy and low cost solution to provide teleworkers with a secure connection to headquarters. Which solution should be selected?Correct
Incorrect
Hint
A remote access VPN over the Internet is an appropriate solution to meet the requirement for secure connections to individual teleworkers. Site-to-site VPNs are used to connect between offices. Leased lines are very expensive for multiple teleworkers. A dial-up connection is very slow and the corporation needs to maintain a facility (a bank of access servers) to handle multiple simultaneous dial-up connections. -
Question 27 of 40
27. Question
1 pointsWhich three statements are true about PPP? (Choose three.)Correct
Incorrect
Hint
PP is an encapsulation standard for transporting IP traffic over point-to-point synchronous and asynchronous links. PPP uses LCP to establish, configure, and test Layer 2 connections and also to negotiate authentication, compression, and error detection. -
Question 28 of 40
28. Question
1 pointsA network administrator is configuring a PPP link with the commands: R1(config-if)# encapsulation ppp R1(config-if)# ppp quality 70 What is the effect of these commands?Correct
Incorrect
Hint
LCP provides an option to monitor the link quality. The command ppp quality percentage ensures that the link meets the quality requirement set; otherwise the link closes down. -
Question 29 of 40
29. Question
1 pointsWhat is the protocol that provides ISPs the ability to send PPP frames over DSL networks?Correct
Incorrect
Hint
PPPoE was developed as a solution for ISPs that wanted to the benefits of PPP connections over their DSL networks. Point-to-Point Protocol over Ethernet, PPPoE, allows PPP frames to be encapsulated and sent over Ethernet. -
Question 30 of 40
30. Question
1 pointsRefer to the exhibit. All routers are successfully running the BGP routing protocol. How many routers must use EBGP in order to share routing information across the autonomous systems?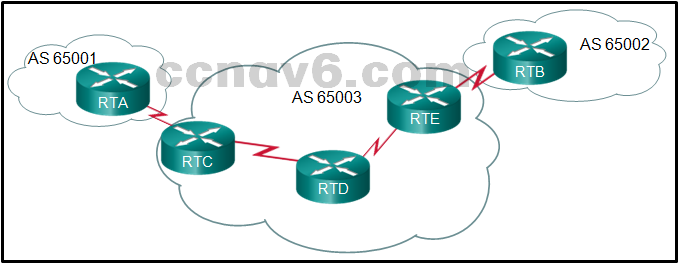 Correct
Correct
Incorrect
Hint
External BGP (EBGP) is used between routers that must communicate with routers that are in a different autonomous system (AS). -
Question 31 of 40
31. Question
1 pointsWhich three values or sets of values are included when creating an extended access control list entry? (Choose three.)Correct
Incorrect
-
Question 32 of 40
32. Question
1 pointsWhich pillar of the Cisco IoT System allows data to be analyzed and managed at the location where it is generated?Correct
Incorrect
Hint
The Cisco IoT System consists of six pillars to describe foundational elements, (1) network connectivity, (2) fog computing, (3) security (cyber and physical), (4) data analytics, (5) management and automation, and (6) an application enablement platform. The fog computing pillar covers software and hardware that extends IoT applications to the network edge. -
Question 33 of 40
33. Question
1 pointsWhat two protocols are supported on Cisco devices for AAA communications? (Choose two.)Correct
Incorrect
Hint
Two AAA protocols are supported on Cisco devices, TACACS+ and RADIUS. Hot Standby Router Protocol (HSRP) is used on Cisco routers to allow for gateway redundancy. Link Layer Discovery Protocol (LLDP) is a protocol for neighbor discovery. VLAN trunking protocol (VTP) is used on Cisco switches to manage VLANs on a VTP-enabled server switch. -
Question 34 of 40
34. Question
1 pointsWhat guideline is generally followed about the placement of extended access control lists?Correct
Incorrect
Hint
ACLs should be placed where they have the greatest impact. The recommendation for the placement of extended ACLs is as close as possible to the source of traffic to be filtered. Whereas standard ACLs should be placed as close to the destination as possible. -
Question 35 of 40
35. Question
1 pointsWhat network monitoring tool copies traffic moving through one switch port, and sends the copied traffic to another switch port for analysis?Correct
Incorrect
Hint
The Switched Port Analyzer (SPAN) feature of Cisco switches allows traffic that is coming into or out of a switch port to be copied to a different port so that it can be collected and analyzed with network monitoring software. -
Question 36 of 40
36. Question
1 pointsWhich type of QoS marking is applied to Ethernet frames?Correct
Incorrect
Hint
The class of service (CoS) marking allows a Layer 2 Ethernet frame to be marked with eight levels of priority (values 0–7). This marking can be used by QoS-enabled network devices to provide preferential traffic treatment. -
Question 37 of 40
37. Question
1 pointsUsers are reporting longer delays in authentication and in accessing network resources during certain time periods of the week. What kind of information should network engineers check to find out if this situation is part of a normal network behavior?Correct
Incorrect
Hint
The network engineers should first establish that the reported performance of the network is in fact abnormal. This is done by referring to the documented network performance baseline.Once it has been verified that the network is not having a proper performance, then specific troubleshooting processes can be applied. -
Question 38 of 40
38. Question
1 pointsWhich feature sends simulated data across the network and measures performance between multiple network locations?Correct
Incorrect
Hint
IP SLAs use generated traffic to measure network performance between two locations, two network devices, or through multiple network paths. IP SLAs are useful in providing data related to network performance and in troubleshooting congestion-related issues. -
Question 39 of 40
39. Question
1 pointsQuestion as presented: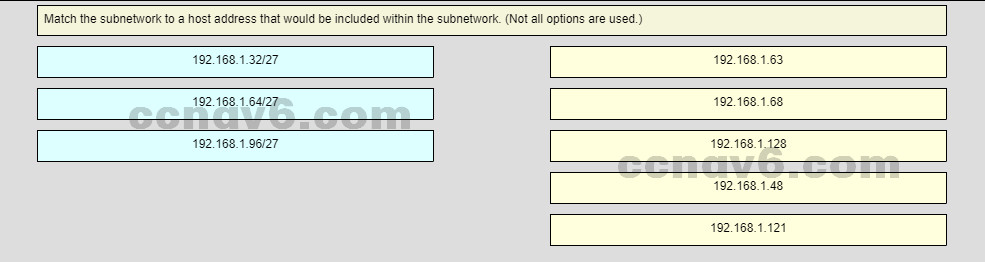
Sort elements
- 192.168.1.48
- 192.168.1.68
- 193.168.1.121
- 192.168.1.63
- 192.168.1.128
-
Subnet 192.168.1.32/27
-
Subnet 192.168.1.64/27
-
Subnet 192.168.1.96/27
Correct
Incorrect
Hint
Subnet 192.168.1.32/27 will have a valid host range from 192.168.1.33 – 192.168.1.62 with the broadcast address as 192.168.1.63 Subnet 192.168.1.64/27 will have a valid host range from 192.168.1.65 – 192.168.1.94 with the broadcast address as 192.168.1.95 Subnet 192.168.1.96/27 will have a valid host range from 192.168.1.97 – 192.168.1.126 with the broadcast address as 192.168.1.127 -
Question 40 of 40
40. Question
1 pointsuestion as presented: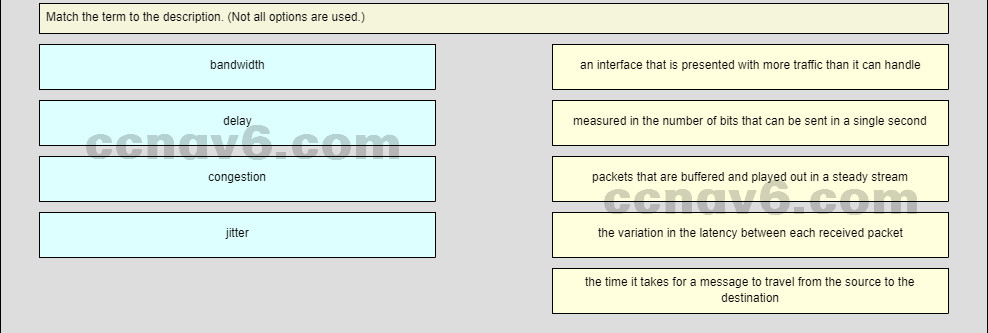
Sort elements
- measured in the number of bits that can be send in a single second
- the time it takes for a message to travel from from the source to be destination
- an interface that is presented with more traffic that can be handle
- packets that are buffered and played out in steady tream
-
bandwidch
-
delay
-
congrestion
Correct
Incorrect
