Time limit: 0
Quiz-summary
0 of 20 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
Information
Networking Basics Module 15 - 17 Checkpoint Test Online
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 20 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- Answered
- Review
-
Question 1 of 20
1. Question
1 pointsWhat information is used by TCP to reassemble and reorder received segments?Correct
Incorrect
Hint
At the transport layer, TCP uses the sequence numbers in the header of each TCP segment to reassemble the segments into the correct order. -
Question 2 of 20
2. Question
1 pointsA PC user issues the netstat command without any options. What is displayed as the result of this command?Correct
Incorrect
Hint
When used by itself (without any options), the netstat command will display all the active TCP connections that are available. -
Question 3 of 20
3. Question
1 pointsWhich action is performed by a client when establishing communication with a server via the use of UDP at the transport layer?Correct
Incorrect
Hint
Because a session does not have to be established for UDP, the client selects a random source port to begin a connection. The random port number selected is inserted into the source port field of the UDP header. -
Question 4 of 20
4. Question
1 pointsRefer to the exhibit. A TCP segment was sent by PC1 to the web server via port 80. Because of an unexpected network failure, the data was forwarded by R1 but was not received by R2. Which statement is correct about this scenario?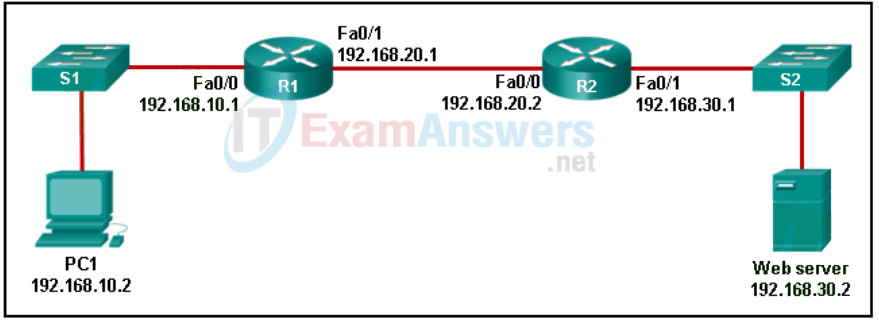 Correct
Correct
Incorrect
Hint
The TCP protocol works between end devices, not between each device on the network. Routers, switches, etc. do not participate in the packet recovery process. For each TCP segment (or group of segments) sent by a host, there is an acknowledgment. If the sender does not receive an acknowledgment within a period of time, the sender resends the segment. -
Question 5 of 20
5. Question
1 pointsA destination PC receives an email message with the sequence numbers on packets out of order. Which layer of the TCP/IP model is responsible for reassembling the packets of the message in the correct order?Correct
Incorrect
Hint
The transport layer of the TCP/IP model is responsible for ensuring that all packets in a message are received, reassembling the message in the correct order after all packets are received, and identifying which applications are sending and receiving network data. -
Question 6 of 20
6. Question
1 pointsA client device has initiated a secure HTTP request to a web browser. Which well-known port address number is associated with the destination address?Correct
Incorrect
Hint
Port numbers are used in TCP and UDP communications to differentiate between the various services running on a device. The well-known port number used by HTTPs is port 443. -
Question 7 of 20
7. Question
1 pointsWhat type of applications are best suited for using UDP?Correct
Incorrect
Hint
UDP is not a connection-oriented protocol and does not provide retransmission, sequencing, or flow control mechanisms. It provides basic transport layer functions with a much lower overhead than TCP. Lower overhead makes UDP suitable for applications which are sensitive to delay. -
Question 8 of 20
8. Question
1 pointsMatch the term to a function.Correct
Incorrect
Hint
Place the options in the following order:hosts a web page web server requests a web page web client used to create web pages HTML secure protocol that uses port 443 HTTPS protocol commonly used by a web browser HTTP -
Question 9 of 20
9. Question
1 pointsWhich three pieces of information are identified by a URL? (Choose three.)Correct
Incorrect
Hint
URLs are used to access specific content on a web server through a web browser. The URL identifies the protocol that is being used such as HTTP or FTP, the domain of the server, and the location of the resource on the server. -
Question 10 of 20
10. Question
1 pointsOpen the PT activity. Perform the tasks in the activity instructions and then answer the question. What is the application layer service being requested from Server0 by PC0?Correct
Incorrect
Hint
From the PDU, the destination port is 443, which means the service requested is HTTPS.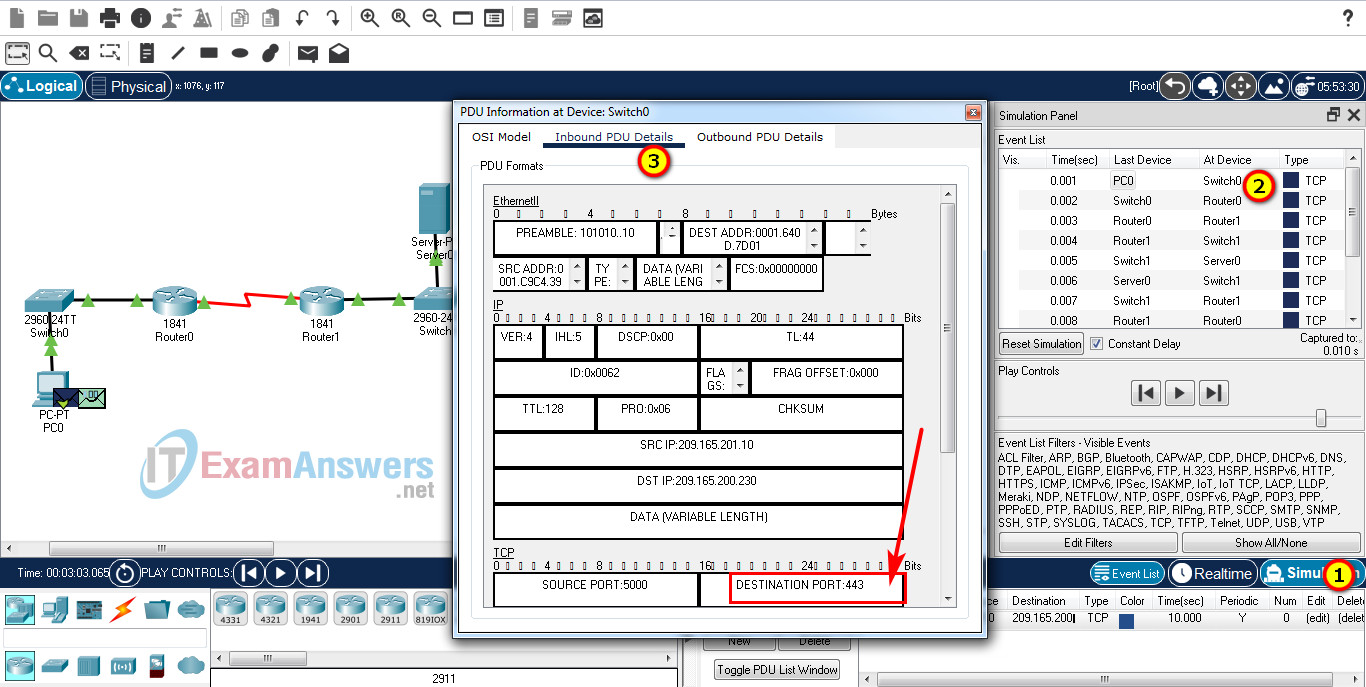
-
Question 11 of 20
11. Question
1 pointsWhich number or set of numbers represents a socket?Correct
Incorrect
Hint
A socket is defined by the combination of an IP address and a port number, and uniquely identifies a particular communication. -
Question 12 of 20
12. Question
1 pointsA new employee is attempting to configure a cell phone to connect to the email server of the company. Which port number should be selected when using the IMAP4 protocol to access email messages stored on the local server?Correct
Incorrect
Hint
The IMAP4 protocol uses the TCP protocol with port 143 for accessing emails stored on a local server. -
Question 13 of 20
13. Question
1 pointsOpen the PT Activity. Perform the tasks in the activity instructions and then answer the question or complete the task. Capture traffic in simulation mode. What application layer service is PC-A requesting from the web server?Correct
Incorrect
Hint
When a client is initiating a request to open an FTP session, it does so by sending a packet to the FTP server with the destination port 21. -
Question 14 of 20
14. Question
1 pointsWhile a network security product is being deployed, a customizable list of allowable protocols is shown. Which three protocols should be allowed to provide for the use of email on a network? (Choose three.)Correct
Incorrect
Hint
The email protocols used on a network are SMTP, POP3, and IMAP4. SMTP is used to send messages to a local email server, whereas POP and IMAP are used to receive email. -
Question 15 of 20
15. Question
1 pointsMatch the command line utility with the description.Correct
Incorrect
Hint
Place the options in the following order:Displays the route taken to the destination. tracert Directly queries the name server for information on a destination domain. nslookup Tests connections to other IP hosts. ping Displays network connections. netstat Displays IP configuration information. ipconfig -
Question 16 of 20
16. Question
1 pointsMatch the command line utility with the function.Correct
Incorrect
Hint
Place the options in the following order:Use the ping command utility for IPv4 only. ping -4 Use the ping command utility for IPv6 only. ping -6 Use the ping command utility to resolve the address to the hostname. ping -a Use the ping command utility to continue pinging the target interface until manually stopped. ping -t -
Question 17 of 20
17. Question
1 pointsWhat is a function of the tracert command that differs from the ping command when they are used on a workstation?Correct
Incorrect
Hint
The tracert command sends three pings to each hop (router) in the path toward the destination and displays the domain name and IP address of hops from their responses. Because tracert uses the ping command, the travel time is the same as a standalone ping command. The primary function of a standalone ping command is to test the connectivity between two hosts. -
Question 18 of 20
18. Question
1 pointsA technician is troubleshooting a network where it is suspected that a defective node in the network path is causing packets to be dropped. The technician only has the IP address of the end point device and does not have any details of the intermediate devices. What command can the technician use to identify the faulty node?Correct
Incorrect
Hint
The ping command is used to verify connectivity to a device,the commands ipconfig /flushdns will cause the adapter to flush the DNS cache, while ipconfig / displaydns will result in the display of the DNS information in the cache. -
Question 19 of 20
19. Question
1 pointsWhich statement describes the use of the ping command?Correct
Incorrect
Hint
The ping command is used to test end-to-end connectivity between the source and destination IP address. It measures the time it takes a test message to make a round trip between the two end points. However, if the message does not reach the destination, or in the case of delays, there is no way to determine where the problem is located. -
Question 20 of 20
20. Question
1 pointsA computer has been assigned an IP address of 169.254.33.16. What command initiates the process of requesting a new IP address?Correct
Incorrect
Hint
Forcing a PC to release its DHCP binding allows a new DHCP request operation to occur. The net, tracert, and nslookup commands do not have any effect on DHCP configurations.
