Author: IT Administrator
3.5.5 Packet Tracer – Investigate the TCP/IP and OSI Models in Action (Instructor Version) Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy only. Objectives Part 1: Examine HTTP Web Traffic Part 2: Display Elements of the TCP/IP Protocol Suite Background …
The ping command can be used to test connectivity to another device on the network or a website on the internet. Click Play in the figure to view a video demonstration using the ping command to test connectivity to a switch and to another PC. Follow Along in …
In the previous topic, you implemented basic connectivity by configuring IP addressing on switches and PCs. Then you verified your configurations and connectivity, because, what is the point of configuring a device if you do not verify that the configuration is working? You will continue this process in …
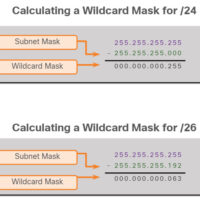
The Wildcard Mask The wildcard mask is typically the inverse of the subnet mask configured on that interface. In a subnet mask, binary 1 is equal to a match and binary 0 is not a match. In a wildcard mask, the reverse is true, as shown in here: …
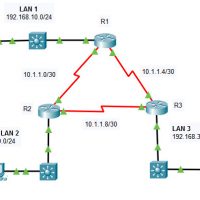
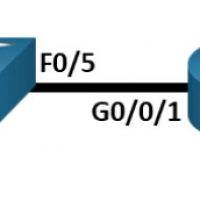
2.2.13 Packet Tracer – Point-to-Point Single-Area OSPFv2 Configuration (Instructor Version) Instructor Note: Red font color or green highlights indicate text that appears in the instructor copy only. Addressing Table Device Interface IP Address Subnet Mask R1 G0/0/0 192.168.10.1 /24 S0/1/0 10.1.1.1 /30 S0/1/1 10.1.1.5 /30 R2 G0/0/0 192.168.20.1 …
CCNA Cyber Ops introduces the core security concepts and skills needed to monitor, detect, analyze and respond to cybercrime, cyber espionage, insider threats, advanced persistent threats, regulatory requirements, and other cybersecurity issues facing organizations. It emphasizes the practical application of the skills needed to maintain and ensure security …
CCNA Cybersecurity Operations v1.1 Skills Assessment Introduction Working as the security analyst for ACME Inc., you notice a number of events on the SGUIL dashboard. Your task is to analyze these events, learn more about them, and decide if they indicate malicious activity. You will have access to …
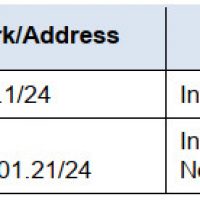
1.6.2 Lab – Configure Basic Router Settings Topology Addressing Table Device Interface IP Address / Prefix Default Gateway R1 G0/0/0 192.168.0.1 /24 N/A 2001:db8:acad::1 /64 fe80::1 G0/0/1 192.168.1.1 /24 2001:db8:acad:1::1 /64 fe80::1 Loopback0 10.0.0.1 /24 2001:db8:acad:2::1 /64 fe80::1 PC-A NIC 192.168.1.10 /24 192.168.1.1 fe80::1 NIC 2001:db8:acad:1::10 /64 PC-B …
The switch attempts to automatically boot by using information in the BOOT environment variable. If this variable is not set, the switch attempts to load and execute the first executable file it can find. On Catalyst 2960 Series switches, the image file is normally contained in a directory …
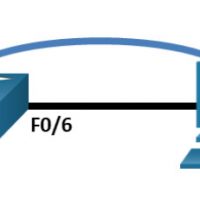
Lab – Basic Switch Configuration Topology Addressing Table Device Interface IP Address / Prefix S1 VLAN 99 192.168.1.2 /24 2001:db8:acad::2 /64 fe80::2 PC-A NIC 192.168.1.10 /24 2001:db8:acad:3 /64 fe80::3 Objectives Part 1: Cable the Network and Verify the Default Switch Configuration Part 2: Configure Basic Network Device Settings …